| File name: | YandexPackLoader.exe |
| Full analysis: | https://app.any.run/tasks/6a911477-36a7-425b-a72a-3c570de04a87 |
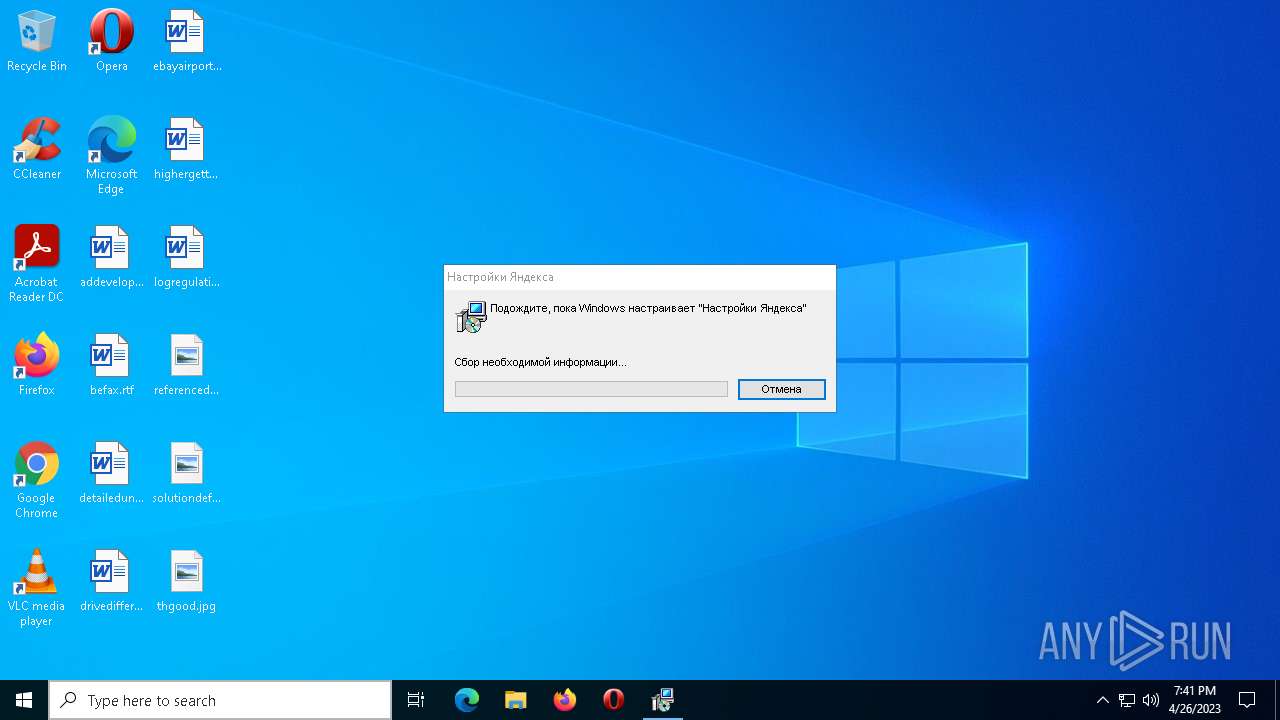
| Verdict: | Malicious activity |
| Analysis date: | April 26, 2023, 19:40:51 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 365E6A3DD47CFDB13E9A4A73D841F879 |
| SHA1: | 9100230BC2F8744FB0DCE6535CA3658C7DC1DF8B |
| SHA256: | CDECBF8D84BB7B5ED08948F9B6D3C9C1B97E7C38BDC636FDC75FE7CCA907A803 |
| SSDEEP: | 3072:+x3P/sUhfv9/d7HvEQC2mCE0KMlbq3dVCZbnKvg8t8xtbXe0GjuKnkNrin2j53:S3P/Fv9/d7PzqdCbnKxjUIn2j53 |
MALICIOUS
Scans artifacts that could help determine the target
- YandexPackLoader.exe (PID: 4100)
SUSPICIOUS
Process requests binary or script from the Internet
- YandexPackLoader.exe (PID: 4100)
Reads security settings of Internet Explorer
- YandexPackLoader.exe (PID: 4100)
Reads settings of System Certificates
- YandexPackLoader.exe (PID: 4100)
- msiexec.exe (PID: 4048)
Checks Windows Trust Settings
- YandexPackLoader.exe (PID: 4100)
- msiexec.exe (PID: 4048)
Reads the date of Windows installation
- YandexPackLoader.exe (PID: 4100)
Application launched itself
- YandexPackLoader.exe (PID: 4100)
Starts itself from another location
- Yandex.exe (PID: 6172)
- Yandex.exe (PID: 3900)
INFO
Create files in a temporary directory
- YandexPackLoader.exe (PID: 4100)
- YandexPackLoader.exe (PID: 4460)
- YandexPackSetup.exe (PID: 5032)
Reads the computer name
- YandexPackLoader.exe (PID: 4100)
- msiexec.exe (PID: 4048)
Checks supported languages
- YandexPackLoader.exe (PID: 4100)
- YandexPackLoader.exe (PID: 4460)
- YandexPackSetup.exe (PID: 5032)
- msiexec.exe (PID: 4048)
Checks proxy server information
- YandexPackLoader.exe (PID: 4100)
Reads the machine GUID from the registry
- YandexPackLoader.exe (PID: 4100)
- msiexec.exe (PID: 4048)
The process checks LSA protection
- YandexPackLoader.exe (PID: 4100)
- YandexPackSetup.exe (PID: 5032)
- msiexec.exe (PID: 4048)
Creates files or folders in the user directory
- YandexPackLoader.exe (PID: 4100)
Reads the software policy settings
- YandexPackLoader.exe (PID: 4100)
- msiexec.exe (PID: 4048)
Manual execution by a user
- {33CF3A51-9227-4AC0-9E69-968F0D03B750}.exe (PID: 6616)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| ProductVersion: | 0.1.0.32 |
|---|---|
| ProductName: | Setup Downloader |
| OriginalFileName: | WebDownloader.exe |
| LegalCopyright: | Copyright (C) 2015 Yandex LLC |
| InternalName: | download |
| FileVersion: | 0.1.0.32 |
| FileDescription: | Setup Downloader |
| CharacterSet: | Unicode |
| LanguageCode: | Russian |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x0017 |
| ProductVersionNumber: | 0.1.0.32 |
| FileVersionNumber: | 0.1.0.32 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 5.1 |
| ImageVersion: | - |
| OSVersion: | 5.1 |
| EntryPoint: | 0x8eb2 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 88576 |
| CodeSize: | 151040 |
| LinkerVersion: | 14 |
| PEType: | PE32 |
| ImageFileCharacteristics: | Executable, 32-bit |
| TimeStamp: | 2018:12:11 06:24:12+00:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 11-Dec-2018 06:24:12 |
| Detected languages: |
|
| Debug artifacts: |
|
| FileDescription: | Setup Downloader |
| FileVersion: | 0.1.0.32 |
| InternalName: | download |
| LegalCopyright: | Copyright (C) 2015 Yandex LLC |
| OriginalFilename: | WebDownloader.exe |
| ProductName: | Setup Downloader |
| ProductVersion: | 0.1.0.32 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000108 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 11-Dec-2018 06:24:12 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00024D1C | 0x00024E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.63719 |
.rdata | 0x00026000 | 0x00009BD4 | 0x00009C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.96753 |
.data | 0x00030000 | 0x0000360C | 0x00000C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.64313 |
.gfids | 0x00034000 | 0x00000134 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 2.42235 |
.rsrc | 0x00035000 | 0x000067E8 | 0x00006800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.1595 |
.reloc | 0x0003C000 | 0x00001A18 | 0x00001C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.41306 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.31879 | 1235 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 1.53973 | 9832 | UNKNOWN | Russian - Russia | RT_ICON |
3 | 1.54324 | 4392 | UNKNOWN | Russian - Russia | RT_ICON |
4 | 1.70751 | 2488 | UNKNOWN | Russian - Russia | RT_ICON |
5 | 1.78405 | 1128 | UNKNOWN | Russian - Russia | RT_ICON |
107 | 2.81633 | 76 | UNKNOWN | Russian - Russia | RT_GROUP_ICON |
Imports
ADVAPI32.dll |
KERNEL32.dll |
OLEAUT32.dll |
SHELL32.dll |
Secur32.dll |
USER32.dll |
VERSION.dll |
WINTRUST.dll |
WS2_32.dll |
WTSAPI32.dll |
Total processes
139
Monitored processes
14
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1440 | C:\Users\admin\AppData\Local\Yandex\YaPin\Yandex.exe --silent --pin-taskbar=y --pin-desktop=n /pin-path="C:\Users\admin\AppData\Local\Yandex\YaPin\Yandex.lnk" --is-pinning | C:\Users\admin\AppData\Local\Temp\pin\explorer.exe | — | Yandex.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: YandexPin Exit code: 0 Version: 3.7.9.0 | |||||||||||||||
| 2160 | "C:\Users\admin\AppData\Local\Temp\6D30FD3B-7C6B-4A17-808F-5181242DDB1B\lite_installer.exe" --use-user-default-locale --silent --remote-url=http://downloader.yandex.net/downloadable_soft/browser/pseudoportal-ru/Yandex.exe --cumtom-welcome-page=https://browser.yandex.ru/promo/welcome_com/5/ --YABROWSER | C:\Users\admin\AppData\Local\Temp\6D30FD3B-7C6B-4A17-808F-5181242DDB1B\lite_installer.exe | — | msiexec.exe | |||||||||||
User: admin Company: Yandex Integrity Level: MEDIUM Description: YandexBrowserDownloader Exit code: 0 Version: 1.0.1.88 | |||||||||||||||
| 3260 | "C:\Users\admin\AppData\Local\Temp\C1A8B3FD-237C-4260-95C5-2701DB1BEB58\seederexe.exe" "--yqs=y" "--yhp=y" "--ilight=" "--oem=" "--nopin=n" "--pin_custom=n" "--pin_desktop=n" "--pin_taskbar=y" "--locale=us" "--browser=y" "--browser_default=" "--loglevel=trace" "--ess=" "--clids=C:\Users\admin\AppData\Local\Temp\clids-yasearch.xml" "--sender=C:\Users\admin\AppData\Local\Temp\DB3738DC-8C03-4B76-A8A8-B581FF5FF5E4\sender.exe" "--is_elevated=no" "--ui_level=3" "--good_token=x" "--no_opera=n" | C:\Users\admin\AppData\Local\Temp\C1A8B3FD-237C-4260-95C5-2701DB1BEB58\seederexe.exe | — | msiexec.exe | |||||||||||
User: admin Company: Yandex Integrity Level: MEDIUM Description: Browser Integration Module Exit code: 0 Version: 3.7.10.0 | |||||||||||||||
| 3900 | C:\Users\admin\AppData\Local\Yandex\YaPin\Yandex.exe --silent --pin-taskbar=y --pin-desktop=n /website-path="C:\Users\admin\AppData\Roaming\Microsoft\Internet Explorer\Quick Launch\User Pinned\Taskbar\Яндекс Маркет.website" /icon-path="C:\Users\admin\AppData\Local\MICROS~1\INTERN~1\Services\MARKET~1.ICO" /site-id="2AE68B04.8A85F169" | C:\Users\admin\AppData\Local\Yandex\YaPin\Yandex.exe | — | seederexe.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: YandexPin Exit code: 0 Version: 3.7.9.0 | |||||||||||||||
| 4048 | C:\WINDOWS\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4100 | "C:\Users\admin\AppData\Local\Temp\YandexPackLoader.exe" | C:\Users\admin\AppData\Local\Temp\YandexPackLoader.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Setup Downloader Exit code: 0 Version: 0.1.0.32 Modules
| |||||||||||||||
| 4460 | C:\Users\admin\AppData\Local\Temp\YandexPackLoader.exe --stat dwnldr/p=70510/cnt=0/dt=7/ct=1/rt=0 --dh 2392 --st 1682538112 | C:\Users\admin\AppData\Local\Temp\YandexPackLoader.exe | — | YandexPackLoader.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup Downloader Exit code: 0 Version: 0.1.0.32 Modules
| |||||||||||||||
| 4688 | C:\Users\admin\AppData\Local\Temp\DB3738DC-8C03-4B76-A8A8-B581FF5FF5E4\sender.exe --send "/status.xml?clid=2598005-830&uuid=82813a06-e6c8-4487-9802-8964760c89bb&vnt=Windows 10x64&file-no=8%0A10%0A11%0A12%0A13%0A15%0A16%0A17%0A18%0A20%0A21%0A22%0A25%0A28%0A36%0A38%0A40%0A42%0A43%0A54%0A58%0A59%0A89%0A102%0A103%0A123%0A124%0A125%0A129%0A" | C:\Users\admin\AppData\Local\Temp\DB3738DC-8C03-4B76-A8A8-B581FF5FF5E4\sender.exe | — | seederexe.exe | |||||||||||
User: admin Company: Yandex Integrity Level: MEDIUM Description: Yandex Statistics Exit code: 0 Version: 0.0.2.14 | |||||||||||||||
| 5032 | "C:\Users\admin\AppData\Local\Temp\7F4987FB1A6E43d69E3E94B29EB75926\YandexPackSetup.exe" /passive /msicl "VID=830 YABROWSER=y YAHOMEPAGE=y YAQSEARCH=y " | C:\Users\admin\AppData\Local\Temp\7F4987FB1A6E43d69E3E94B29EB75926\YandexPackSetup.exe | YandexPackLoader.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Software Installer Exit code: 0 Version: 3.0.5419.0 Modules
| |||||||||||||||
| 5764 | C:\Windows\syswow64\MsiExec.exe -Embedding AD46E15D40C580E3EC0EDBC458A7D581 | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
Total events
6 857
Read events
6 837
Write events
20
Delete events
0
Modification events
| (PID) Process: | (4100) YandexPackLoader.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (4100) YandexPackLoader.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (4100) YandexPackLoader.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (4100) YandexPackLoader.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (4100) YandexPackLoader.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (4100) YandexPackLoader.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
Executable files
0
Suspicious files
3
Text files
9
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5032 | YandexPackSetup.exe | C:\Users\admin\AppData\Local\Temp\{5B964E0E-B9A3-4276-9ED9-4D5A5720747A}\YandexSearch.msi | — | |
MD5:— | SHA256:— | |||
| 4048 | msiexec.exe | C:\WINDOWS\Installer\43fa96.msi | — | |
MD5:— | SHA256:— | |||
| 3260 | seederexe.exe | C:\Users\admin\AppData\Local\Temp\omnija-20234126.zip | — | |
MD5:— | SHA256:— | |||
| 3260 | seederexe.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\places.sqlite-20230426194154.463000.backup | — | |
MD5:— | SHA256:— | |||
| 3260 | seederexe.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\places.sqlite | — | |
MD5:— | SHA256:— | |||
| 3260 | seederexe.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\CURRENT | — | |
MD5:— | SHA256:— | |||
| 6616 | {33CF3A51-9227-4AC0-9E69-968F0D03B750}.exe | C:\Users\admin\AppData\Local\Temp\website.ico | — | |
MD5:— | SHA256:— | |||
| 4100 | YandexPackLoader.exe | C:\Users\admin\AppData\Local\Temp\7F4987FB1A6E43d69E3E94B29EB75926\seed.txt | text | |
MD5:141FDED8387B387998EEEDD6820F3EE3 | SHA256:1963B3E4A46541F0F31738C8D59E5FEF51345567539469A3C40AD57491A24E30 | |||
| 4100 | YandexPackLoader.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\AH8CR9J5\info[1].rss | xml | |
MD5:1624F4A1E637E4A958CA214764AD4D02 | SHA256:69E56887CAF622CDA9BA6380BFC46BC08BA2E80361D9B087B79BF12D40B07F75 | |||
| 3260 | seederexe.exe | C:\Users\admin\AppData\Local\Temp\8b8bfaeb-7e01-4ccd-891d-78d6ad33a6cc\market-32.png | image | |
MD5:05CDE36DE2B2E94D3322FBA16554FDE5 | SHA256:AE05465BFBCD33620690011C9D65E976AD4A5A5BEA10BF5770922ED565262EE9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
23
TCP/UDP connections
64
DNS requests
22
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4100 | YandexPackLoader.exe | GET | 302 | 5.45.205.245:80 | http://downloader.yandex.net/yandex-pack/downloader/info.rss | RU | — | — | whitelisted |
4100 | YandexPackLoader.exe | GET | 302 | 5.45.205.245:80 | http://downloader.yandex.net/yandex-pack/70510/YandexPackSetup.exe | RU | — | — | whitelisted |
4100 | YandexPackLoader.exe | GET | 200 | 149.5.241.41:80 | http://ext-cachev2-cogent01.cdn.yandex.net/download.yandex.ru/yandex-pack/downloader/info.rss?lid=1503 | US | xml | 267 b | whitelisted |
4100 | YandexPackLoader.exe | GET | 200 | 185.70.202.15:80 | http://ext-cachev2-itt03.cdn.yandex.net/downloader.yandex.net/yandex-pack/70510/YandexPackSetup.exe?lid=1529 | IT | executable | 10.1 Mb | whitelisted |
4100 | YandexPackLoader.exe | GET | 302 | 5.45.205.241:80 | http://download.yandex.ru/yandex-pack/downloader/info.rss | RU | — | — | whitelisted |
— | — | GET | — | 213.180.204.14:80 | http://clck.yandex.ru/click/dtype=stred/pid=12/cid=72435/path=dwnldr/p=70510/cnt=0/dt=7/ct=1/rt=1/imp=0/* | RU | — | — | whitelisted |
4100 | YandexPackLoader.exe | GET | 200 | 104.18.20.226:80 | http://ocsp.globalsign.com/codesigningrootr45/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQVFZP5vqhCrtRN5SWf40Rn6NM1IAQUHwC%2FRoAK%2FHg5t6W0Q9lWULvOljsCEHe9DgW3WQu2HUdhUx4%2Fde0%3D | US | der | 1.67 Kb | whitelisted |
4100 | YandexPackLoader.exe | GET | 200 | 104.18.20.226:80 | http://ocsp.globalsign.com/gsgccr45evcodesignca2020/ME0wSzBJMEcwRTAJBgUrDgMCGgUABBQaCbVYh07WONuW4e63Ydlu4AlbDAQUJZ3Q%2FFkJhmPF7POxEztXHAOSNhECDHkE0y50%2FEcrZsCKOA%3D%3D | US | der | 1.65 Kb | whitelisted |
— | — | GET | 200 | 149.5.241.43:80 | http://ext-cachev2-cogent03.cdn.yandex.net/downloader.yandex.net/downloadable_soft/browser/pseudoportal-ru/Yandex.exe?clid=2597987-830&ui={82813a06-e6c8-4487-9802-8964760c89bb}&lid=1503 | US | executable | 3.12 Mb | shared |
— | — | GET | 302 | 5.45.205.244:80 | http://downloader.yandex.net/downloadable_soft/browser/pseudoportal-ru/Yandex.exe?clid=2597987-830&ui={82813a06-e6c8-4487-9802-8964760c89bb} | RU | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4100 | YandexPackLoader.exe | 5.45.205.244:80 | downloader.yandex.net | YANDEX LLC | RU | whitelisted |
5952 | MoUsoCoreWorker.exe | 2.21.20.133:80 | — | Akamai International B.V. | DE | suspicious |
— | — | 20.190.160.22:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4736 | SearchApp.exe | 2.16.186.203:443 | — | Akamai International B.V. | DE | whitelisted |
— | — | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 2.18.233.62:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5952 | MoUsoCoreWorker.exe | 2.21.20.137:80 | — | Akamai International B.V. | DE | suspicious |
5756 | svchost.exe | 20.190.160.17:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4100 | YandexPackLoader.exe | 5.45.205.245:80 | downloader.yandex.net | YANDEX LLC | RU | whitelisted |
5756 | svchost.exe | 40.126.32.134:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
downloader.yandex.net |
| whitelisted |
officeclient.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
ext-cachev2-cogent01.cdn.yandex.net |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
login.live.com |
| whitelisted |
download.yandex.ru |
| whitelisted |
ext-cachev2-itt03.cdn.yandex.net |
| whitelisted |
ocsp.globalsign.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4100 | YandexPackLoader.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
— | — | Attempted Information Leak | ET POLICY curl User-Agent Outbound |
— | — | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
— | — | Misc activity | ET INFO EXE - Served Attached HTTP |
2 ETPRO signatures available at the full report
Process | Message |
|---|---|
YandexPackSetup.exe | IsAlreadyRun() In
|
YandexPackSetup.exe | IsAlreadyRun() In
|
YandexPackSetup.exe | IsAlreadyRun() Out : ret (BOOL) = 0
|
YandexPackSetup.exe | IsMSISrvFree() In |
YandexPackSetup.exe | IsMSISrvFree() : OpenMutex() err ret = 2
|
YandexPackSetup.exe | IsMSISrvFree() Out ret = 1
|
YandexPackSetup.exe | IsAlreadyRun() Out : ret (BOOL) = 0
|
YandexPackSetup.exe | IsMSISrvFree() In |
YandexPackSetup.exe | IsMSISrvFree() : OpenMutex() err ret = 2
|
YandexPackSetup.exe | IsMSISrvFree() Out ret = 1
|