| File name: | Agent_Install (4).exe |
| Full analysis: | https://app.any.run/tasks/d2461237-9a0c-43a5-8bb6-41205a305af7 |
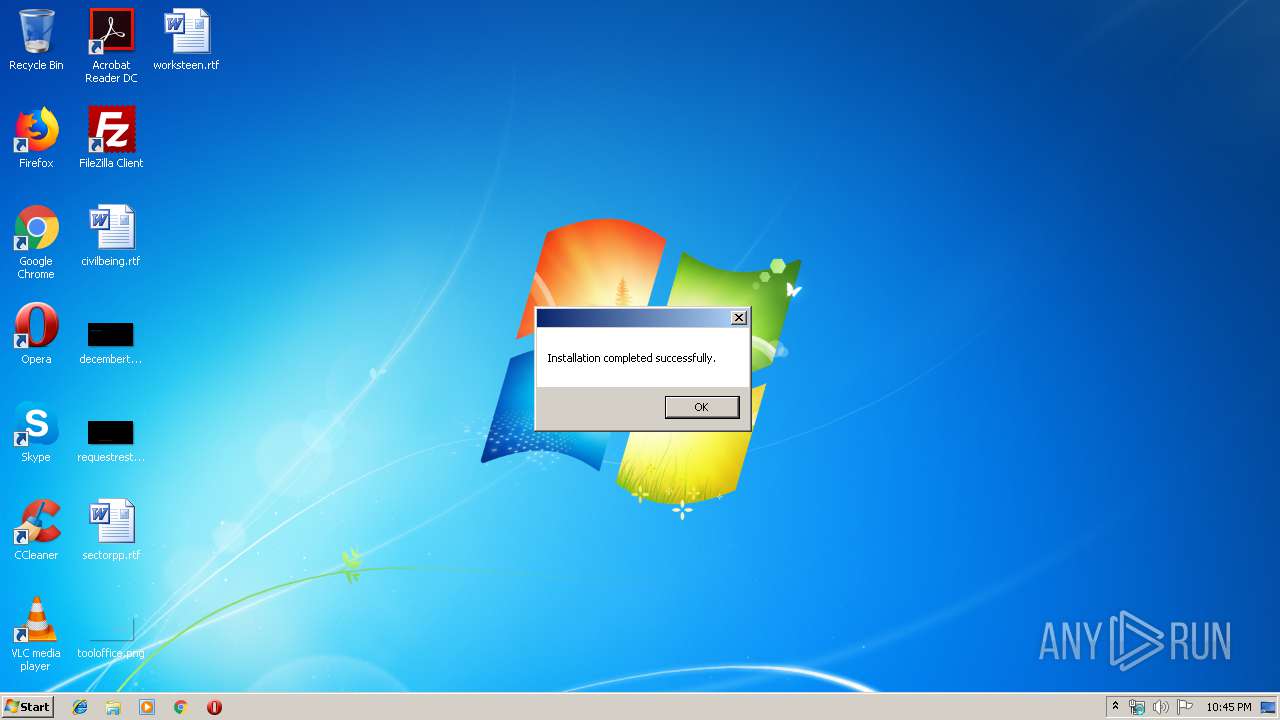
| Verdict: | Malicious activity |
| Analysis date: | September 18, 2019, 21:44:32 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 39F6918DB6453D74FD84B9CE64436EE6 |
| SHA1: | 5CB56882EAD9019D58B2CB202F805644E177542B |
| SHA256: | CDE2E4A5AA226304D358CC0A3177BC90A0F637B25026654B6560B0D75D117512 |
| SSDEEP: | 98304:SsiIeYADXOMekNLQdzzmEODQ6i19S8jJmVkzVz+aXamMdbxjiPiRD:Ssi9DVeGL4nTzjJmVeVzp3MdbxiPil |
MALICIOUS
Application was dropped or rewritten from another process
- Agent_Install (4).exe (PID: 2756)
- LabTechRemoteAgent.exe (PID: 2568)
- LTSVC.exe (PID: 2860)
- LTSvcMon.exe (PID: 2492)
- LTTray.exe (PID: 872)
- ScreenConnect.ClientService.exe (PID: 3944)
- ScreenConnect.WindowsClient.exe (PID: 3456)
- ScreenConnect.WindowsClient.exe (PID: 4072)
Loads dropped or rewritten executable
- Agent_Install (4).exe (PID: 2756)
- LTSvcMon.exe (PID: 2492)
- LTSVC.exe (PID: 2860)
- regsvr32.exe (PID: 2984)
- LTTray.exe (PID: 872)
- ScreenConnect.ClientService.exe (PID: 3944)
- ScreenConnect.WindowsClient.exe (PID: 3456)
- ScreenConnect.WindowsClient.exe (PID: 4072)
- rundll32.exe (PID: 3688)
Starts NET.EXE for service management
- MsiExec.exe (PID: 2808)
- CMD.exe (PID: 2772)
Changes the autorun value in the registry
- LabTechRemoteAgent.exe (PID: 2568)
Registers / Runs the DLL via REGSVR32.EXE
- LTSVC.exe (PID: 2860)
Changes settings of System certificates
- msiexec.exe (PID: 3628)
Starts NET.EXE to view/change shared resources
- LTSVC.exe (PID: 2860)
Loads the Task Scheduler COM API
- LTSVC.exe (PID: 2860)
SUSPICIOUS
Executed via COM
- DrvInst.exe (PID: 3160)
Executable content was dropped or overwritten
- Agent_Install (4).exe (PID: 3780)
- Agent_Install (4).exe (PID: 2756)
- LabTechRemoteAgent.exe (PID: 2568)
- msiexec.exe (PID: 3628)
- LTSVC.exe (PID: 2860)
Creates files in the program directory
- LabTechRemoteAgent.exe (PID: 2568)
Executed as Windows Service
- vssvc.exe (PID: 3792)
- LTSvcMon.exe (PID: 2492)
- LTSVC.exe (PID: 2860)
- ScreenConnect.ClientService.exe (PID: 3944)
Starts itself from another location
- Agent_Install (4).exe (PID: 2756)
Searches for installed software
- LabTechRemoteAgent.exe (PID: 2568)
- LTSVC.exe (PID: 2860)
Creates a software uninstall entry
- LabTechRemoteAgent.exe (PID: 2568)
Adds / modifies Windows certificates
- msiexec.exe (PID: 3628)
Creates files in the Windows directory
- msiexec.exe (PID: 3628)
- LTSvcMon.exe (PID: 2492)
- MsiExec.exe (PID: 2808)
- LTSVC.exe (PID: 2860)
- msiexec.exe (PID: 3300)
Reads Environment values
- LTSvcMon.exe (PID: 2492)
- LTSVC.exe (PID: 2860)
- ScreenConnect.WindowsClient.exe (PID: 4072)
Removes files from Windows directory
- LTSVC.exe (PID: 2860)
Creates COM task schedule object
- regsvr32.exe (PID: 2984)
Low-level read access rights to disk partition
- LTSVC.exe (PID: 2860)
Starts CMD.EXE for commands execution
- LTSVC.exe (PID: 2860)
Creates or modifies windows services
- LTSVC.exe (PID: 2860)
Uses NETSH.EXE for network configuration
- CMD.exe (PID: 2300)
- CMD.exe (PID: 1440)
- CMD.exe (PID: 3584)
- CMD.exe (PID: 2540)
- CMD.exe (PID: 3564)
- CMD.exe (PID: 2572)
- CMD.exe (PID: 2812)
- CMD.exe (PID: 560)
- CMD.exe (PID: 3232)
- CMD.exe (PID: 4076)
- CMD.exe (PID: 3156)
- CMD.exe (PID: 3688)
- CMD.exe (PID: 3384)
- CMD.exe (PID: 1144)
- CMD.exe (PID: 3880)
- CMD.exe (PID: 2736)
- CMD.exe (PID: 3108)
- CMD.exe (PID: 2720)
- CMD.exe (PID: 2796)
- CMD.exe (PID: 3724)
- CMD.exe (PID: 3020)
- CMD.exe (PID: 1432)
- CMD.exe (PID: 3396)
Uses NETSTAT.EXE to discover network connections
- cmd.exe (PID: 2608)
- cmd.exe (PID: 3804)
- cmd.exe (PID: 2276)
- cmd.exe (PID: 3188)
Uses TASKLIST.EXE to query information about running processes
- cmd.exe (PID: 2092)
Uses RUNDLL32.EXE to load library
- MsiExec.exe (PID: 1156)
Starts Microsoft Installer
- cmd.exe (PID: 772)
Modifies the open verb of a shell class
- msiexec.exe (PID: 3628)
Reads CPU info
- ScreenConnect.WindowsClient.exe (PID: 4072)
Executes PowerShell scripts
- LTSVC.exe (PID: 2860)
INFO
Low-level read access rights to disk partition
- vssvc.exe (PID: 3792)
Application launched itself
- msiexec.exe (PID: 3628)
Loads dropped or rewritten executable
- MsiExec.exe (PID: 2808)
- MsiExec.exe (PID: 3832)
Creates a software uninstall entry
- msiexec.exe (PID: 3628)
Creates files in the program directory
- msiexec.exe (PID: 3628)
Dropped object may contain Bitcoin addresses
- LTSVC.exe (PID: 2860)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:02:28 19:25:32+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 301568 |
| InitializedDataSize: | 161280 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x2e0c1 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 19.0.250.0 |
| ProductVersionNumber: | 19.0.250.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | ConnectWise, Inc. |
| FileDescription: | ConnectWise Automate Remote Agent |
| FileVersion: | 19.0.250 |
| InternalName: | setup |
| LegalCopyright: | Copyright (c) ConnectWise, Inc.. All rights reserved. |
| OriginalFileName: | LabTechRemoteAgent.exe |
| ProductName: | ConnectWise Automate Remote Agent |
| ProductVersion: | 19.0.250 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 28-Feb-2018 18:25:32 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | ConnectWise, Inc. |
| FileDescription: | ConnectWise Automate Remote Agent |
| FileVersion: | 19.0.250 |
| InternalName: | setup |
| LegalCopyright: | Copyright (c) ConnectWise, Inc.. All rights reserved. |
| OriginalFilename: | LabTechRemoteAgent.exe |
| ProductName: | ConnectWise Automate Remote Agent |
| ProductVersion: | 19.0.250 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000118 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 28-Feb-2018 18:25:32 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00049827 | 0x00049A00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.55956 |
.rdata | 0x0004B000 | 0x0001EB34 | 0x0001EC00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.11602 |
.data | 0x0006A000 | 0x00001740 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.12305 |
.wixburn8 | 0x0006C000 | 0x00000038 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.735162 |
.tls | 0x0006D000 | 0x00000009 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.gfids | 0x0006E000 | 0x000000E0 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 2.01067 |
.rsrc | 0x0006F000 | 0x00003A80 | 0x00003C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.52823 |
.reloc | 0x00073000 | 0x00003D8C | 0x00003E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.7698 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.30829 | 1234 | Latin 1 / Western European | English - United States | RT_MANIFEST |
Imports
ADVAPI32.dll |
Cabinet.dll (delay-loaded) |
GDI32.dll |
KERNEL32.dll |
OLEAUT32.dll |
RPCRT4.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
207
Monitored processes
115
Malicious processes
11
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 560 | "CMD.exe" /c netsh advfirewall firewall Delete rule name="AgentMonitor" | C:\Windows\system32\CMD.exe | — | LTSVC.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 772 | "C:\Windows\System32\cmd.exe" /c msiexec /i C:\Windows\LTSvc\packages\connectwisecontrol\CWControlClientInstaller.msi /quiet /qn /norestart /L*v C:\Windows\LTSvc\packages\connectwisecontrol\CWControlClientInstallLog.txt | C:\Windows\System32\cmd.exe | — | LTSVC.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 780 | netsh advfirewall firewall add rule name="AgentTray" dir=out action=allow program="C:\Windows\LTSvc\LTTray.exe" enable=yes | C:\Windows\system32\netsh.exe | — | CMD.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 872 | C:\Windows\LTSvc\LTTray.exe | C:\Windows\LTSvc\LTTray.exe | — | LTSVC.exe | |||||||||||
User: admin Company: LabTech Software Integrity Level: MEDIUM Description: LabTech Tray Exit code: 0 Version: 190.250.7181.27062 Modules
| |||||||||||||||
| 892 | "C:\Windows\system32\BCDedit.exe" /deletevalue SAFEBOOT | C:\Windows\system32\BCDedit.exe | — | LTSVC.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Boot Configuration Data Editor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 924 | netsh advfirewall firewall Delete rule name="Allow Local Redir" | C:\Windows\system32\netsh.exe | — | CMD.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Network Command Shell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 976 | C:\Windows\system32\net1 stop LTSvcMon | C:\Windows\system32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1016 | find /i "Listening" | C:\Windows\system32\find.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Find String (grep) Utility Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1080 | netsh advfirewall firewall Add rule name="Allow Tunnel StunRelay" dir=out protocol=udp localport=70-75 action=allow | C:\Windows\system32\netsh.exe | — | CMD.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1144 | "CMD.exe" /c netsh advfirewall firewall add rule name="AgentMonitor" dir=out action=allow program="C:\Windows\LTSvc\LTSVCmon.exe" enable=yes | C:\Windows\system32\CMD.exe | — | LTSVC.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
8 739
Read events
2 187
Write events
6 491
Delete events
61
Modification events
| (PID) Process: | (2756) Agent_Install (4).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Agent_Install (4)_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2756) Agent_Install (4).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Agent_Install (4)_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2756) Agent_Install (4).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Agent_Install (4)_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2756) Agent_Install (4).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Agent_Install (4)_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2756) Agent_Install (4).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Agent_Install (4)_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (2756) Agent_Install (4).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Agent_Install (4)_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (2756) Agent_Install (4).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Agent_Install (4)_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2756) Agent_Install (4).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Agent_Install (4)_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2756) Agent_Install (4).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Agent_Install (4)_RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2756) Agent_Install (4).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Agent_Install (4)_RASMANCS |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
Executable files
93
Suspicious files
23
Text files
270
Unknown types
27
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3780 | Agent_Install (4).exe | C:\Users\admin\AppData\Local\Temp\{23FFA80C-DA16-4687-9E28-3030C92D0B9E}\.cr\Agent_Install (4).exe | executable | |
MD5:56E602D0521EBF1EE0B6EE95C9799EAE | SHA256:4536F24F83BF6688B02522C3FADA20A46B37931C1FC87F64D2F9A1AED030BA20 | |||
| 2756 | Agent_Install (4).exe | C:\Users\admin\AppData\Local\Temp\{E01CA9B3-0C25-4710-8257-9474A1CC9827}\.ba\Microsoft.Deployment.Compression.Zip.dll | executable | |
MD5:6F5A5AE706F92397A95A308A2E98C699 | SHA256:DB6361F42349C9D75DA494D4710F83A482642B8CC49F6705942104F262654874 | |||
| 2756 | Agent_Install (4).exe | C:\Users\admin\AppData\Local\Temp\{E01CA9B3-0C25-4710-8257-9474A1CC9827}\.ba\BootstrapperCore.dll | executable | |
MD5:E1428889727D28B0246B51BE3AA5E29A | SHA256:747EC72EACF06257C0734FA9A808C68E5DB76EB8EA309849DBFBE4CA35972877 | |||
| 2756 | Agent_Install (4).exe | C:\Users\admin\AppData\Local\Temp\{E01CA9B3-0C25-4710-8257-9474A1CC9827}\.ba\RemoteAgentBootstrapper.dll | executable | |
MD5:CAE895EFB51F7AA1003F9B4ED178796E | SHA256:176CFCD01443E406A7B4C348CEF3D0DFE5686B943D3E91BE1FA1D419837F46BF | |||
| 2756 | Agent_Install (4).exe | C:\Users\admin\AppData\Local\Temp\{E01CA9B3-0C25-4710-8257-9474A1CC9827}\.ba\Microsoft.Deployment.WindowsInstaller.dll | executable | |
MD5:A4B0ED5683AB353C9570DEC295891C2B | SHA256:C73ADED9A76D875B8687D20D2464A4BFEFD15BD5DBEF3998C0B5A0EB9EDAC437 | |||
| 2756 | Agent_Install (4).exe | C:\Users\admin\AppData\Local\Temp\{E01CA9B3-0C25-4710-8257-9474A1CC9827}\.ba\Microsoft.Deployment.Resources.dll | executable | |
MD5:CD36AE3CADC62CB043525346D1819C28 | SHA256:B005392BCF602341F9A80A85BFDBDD6A5C14079F276A38D456B0D3977A3EAB15 | |||
| 2756 | Agent_Install (4).exe | C:\Users\admin\AppData\Local\Temp\{E01CA9B3-0C25-4710-8257-9474A1CC9827}\.ba\Microsoft.Deployment.WindowsInstaller.Package.dll | executable | |
MD5:68AD1792EB777C6808BD073582032B41 | SHA256:BD81F5D17551F576E5EF5B872F9ED87453C2B9D61CC17E71DDDD6A1D6CC97D8F | |||
| 2756 | Agent_Install (4).exe | C:\Users\admin\AppData\Local\Temp\{E01CA9B3-0C25-4710-8257-9474A1CC9827}\.ba\Microsoft.Deployment.Compression.dll | executable | |
MD5:9A7836B8F0633597F69CE1423960B4CE | SHA256:C19D43A2E6E5C4BAFDA562886583D10AA98A089D1C4875410FF2AE220BB8CF79 | |||
| 2756 | Agent_Install (4).exe | C:\Users\admin\AppData\Local\Temp\{E01CA9B3-0C25-4710-8257-9474A1CC9827}\.ba\Microsoft.Deployment.Compression.Cab.dll | executable | |
MD5:7FD91239792D625CCE5EBAF31FD2F4FE | SHA256:52D03290029ECCE3D68166DEBDC3589C79737BF3B0E87AB6183713D22E9F5A84 | |||
| 2756 | Agent_Install (4).exe | C:\Users\admin\AppData\Local\Temp\{E01CA9B3-0C25-4710-8257-9474A1CC9827}\.ba\winterop.dll | executable | |
MD5:7070236E82B6F9CD538AE8481A27311A | SHA256:9074BA23E6747E5FC3875111602D924EDE7BFE062F99FE4D7C838B8466CDA045 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
271
TCP/UDP connections
78
DNS requests
8
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2860 | LTSVC.exe | GET | 200 | 104.18.21.226:80 | http://ocsp2.globalsign.com/gsextendcodesignsha2g3/ME0wSzBJMEcwRTAJBgUrDgMCGgUABBQ3DAV9N6WelMGCzSTdNIqjdmfHiAQU3CxYLCpvNS2feZWoSF3EbT5Tv7kCDBWcvWHUaDWCegib0A%3D%3D | US | der | 1.55 Kb | whitelisted |
— | — | GET | 200 | 13.107.4.50:80 | http://ds.download.windowsupdate.com/v11/2/microsoftupdate/redir/v6-legacy-muauth.cab?1909182147 | US | compressed | 23.3 Kb | whitelisted |
— | — | HEAD | 200 | 93.184.221.240:80 | http://download.windowsupdate.com/v9/windowsupdate/redir/muv4wuredir.cab?1909182147 | US | — | — | whitelisted |
— | — | HEAD | 200 | 93.184.221.240:80 | http://download.windowsupdate.com/v9/windowsupdate/redir/muv4wuredir.cab?1909182147 | US | compressed | 23.0 Kb | whitelisted |
— | — | GET | 200 | 93.184.221.240:80 | http://download.windowsupdate.com/v9/windowsupdate/redir/muv4wuredir.cab?1909182147 | US | compressed | 23.0 Kb | whitelisted |
— | — | HEAD | 200 | 13.107.4.50:80 | http://ds.download.windowsupdate.com/v11/2/microsoftupdate/redir/v6-legacy-muredir.cab?1909182147 | US | compressed | 23.3 Kb | whitelisted |
— | — | HEAD | 200 | 13.107.4.50:80 | http://ds.download.windowsupdate.com/v11/2/microsoftupdate/redir/v6-legacy-muauth.cab?1909182147 | US | compressed | 23.3 Kb | whitelisted |
3964 | wmiprvse.exe | GET | 200 | 2.16.186.120:80 | http://crl.microsoft.com/pki/crl/products/microsoftrootcert.crl | unknown | der | 781 b | whitelisted |
— | — | GET | 200 | 13.107.4.50:80 | http://ds.download.windowsupdate.com/v11/2/microsoftupdate/redir/v6-legacy-muredir.cab?1909182147 | US | compressed | 22.9 Kb | whitelisted |
— | — | GET | 200 | 93.184.221.240:80 | http://download.windowsupdate.com/msdownload/update/common/2012/05/5574325_9c5797d0cd744ceb00b36ca6295f292c5cc30c2d.cab | US | compressed | 6.87 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2756 | Agent_Install (4).exe | 54.81.94.228:443 | trutech.hostedrmm.com | Amazon.com, Inc. | US | suspicious |
2860 | LTSVC.exe | 104.18.21.226:80 | ocsp2.globalsign.com | Cloudflare Inc | US | shared |
2860 | LTSVC.exe | 54.81.94.228:443 | trutech.hostedrmm.com | Amazon.com, Inc. | US | suspicious |
2860 | LTSVC.exe | 54.81.94.228:8040 | trutech.hostedrmm.com | Amazon.com, Inc. | US | suspicious |
3944 | ScreenConnect.ClientService.exe | 54.81.94.228:8041 | trutech.hostedrmm.com | Amazon.com, Inc. | US | suspicious |
— | — | 13.107.4.50:80 | ds.download.windowsupdate.com | Microsoft Corporation | US | whitelisted |
— | — | 40.91.124.111:443 | www.update.microsoft.com | Microsoft Corporation | US | unknown |
— | — | 93.184.221.240:80 | download.windowsupdate.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3964 | wmiprvse.exe | 2.16.186.120:80 | crl.microsoft.com | Akamai International B.V. | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
trutech.hostedrmm.com |
| suspicious |
ocsp2.globalsign.com |
| whitelisted |
download.windowsupdate.com |
| whitelisted |
ds.download.windowsupdate.com |
| whitelisted |
www.update.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3944 | ScreenConnect.ClientService.exe | Misc activity | APP [PTsecurity] ScreenConnect |
5 ETPRO signatures available at the full report