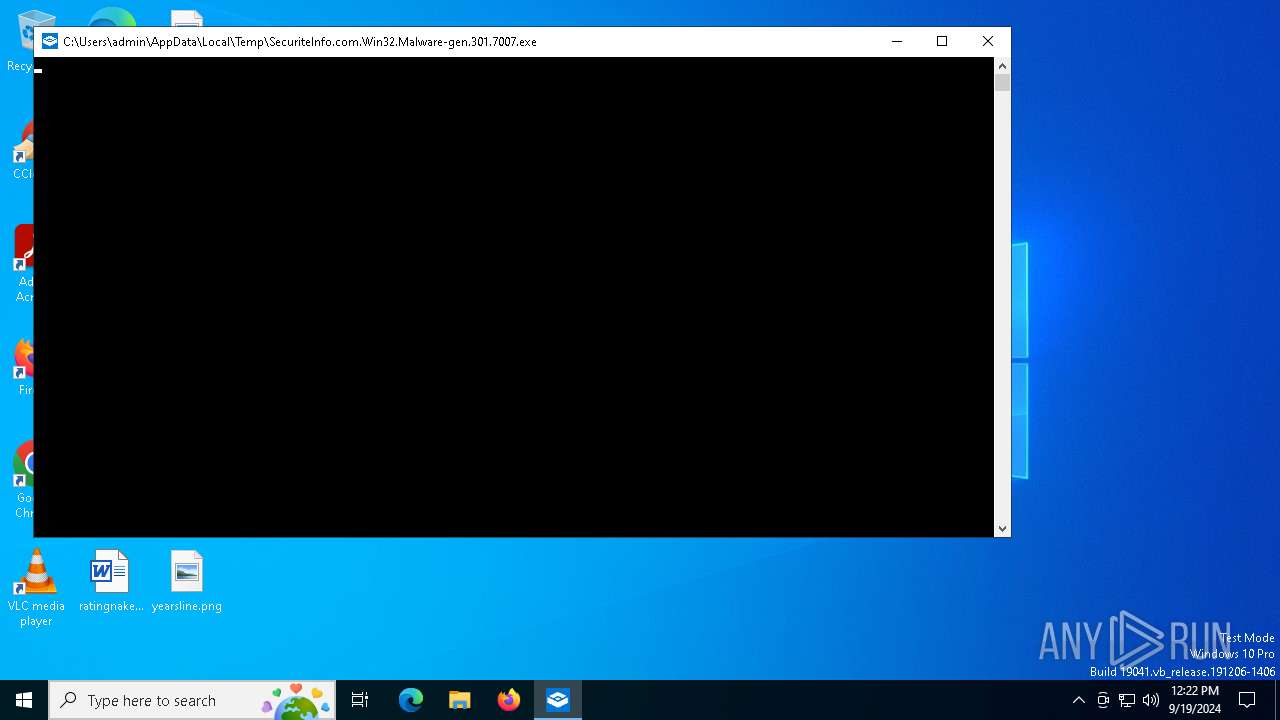
| File name: | SecuriteInfo.com.Win32.Malware-gen.301.7007 |
| Full analysis: | https://app.any.run/tasks/156f4355-6eba-4cdb-b726-da9a90929c3e |
| Verdict: | Malicious activity |
| Analysis date: | September 19, 2024, 12:22:24 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | F18E04E444196B02E1FF216A80C2379D |
| SHA1: | FDD1FC0FFB6F4CB9ACD27E4F7492006B18C9D871 |
| SHA256: | CDE29A4FD40C984D7201F1360CF2D489343732262326A08F1B0B92B35EE2CDB1 |
| SSDEEP: | 49152:imvsQWloSpZJxV/tQUGIls1eRn7vYxoOTToUG2:0QIez |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executable content was dropped or overwritten
- SecuriteInfo.com.Win32.Malware-gen.301.7007.exe (PID: 7012)
There is functionality for communication dyndns network (YARA)
- powershell.exe (PID: 7000)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (63.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (23.8) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.8) |
| .exe | | | Generic Win/DOS Executable (1.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2021:11:23 12:33:59+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 11 |
| CodeSize: | 6526976 |
| InitializedDataSize: | 272384 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x63b61e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows command line |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| FileDescription: | |
| FileVersion: | 0.0.0.0 |
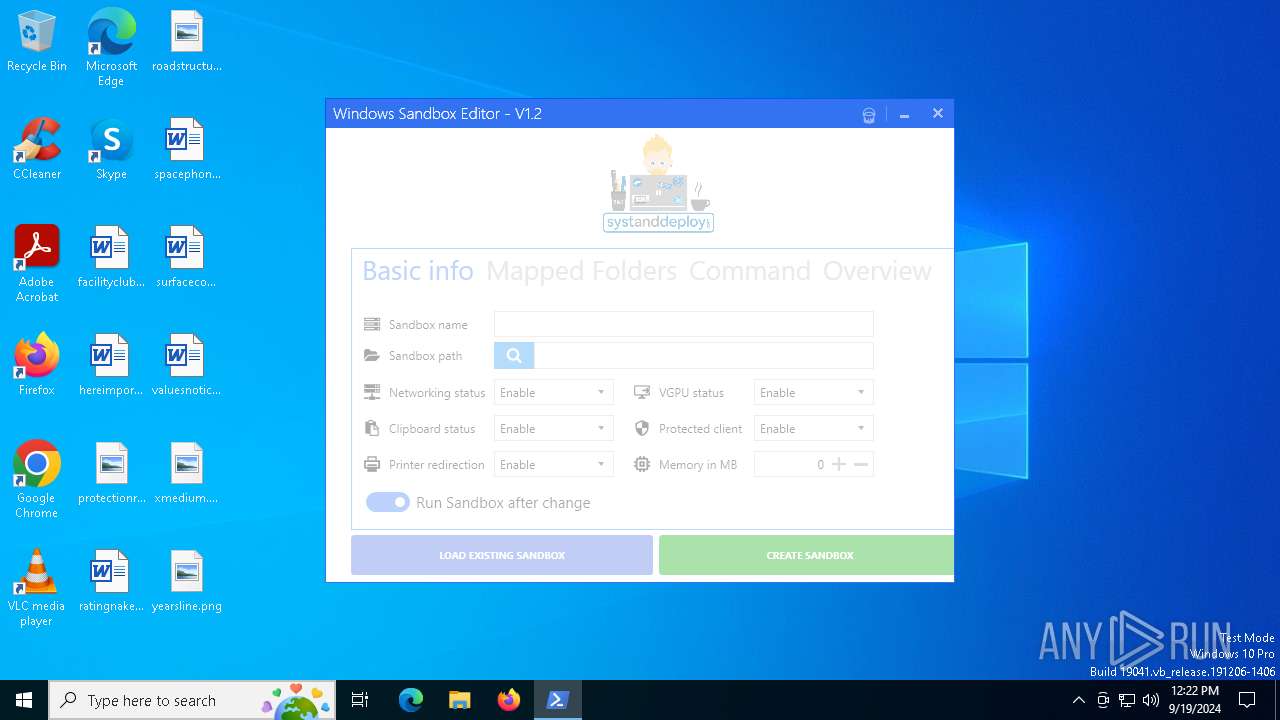
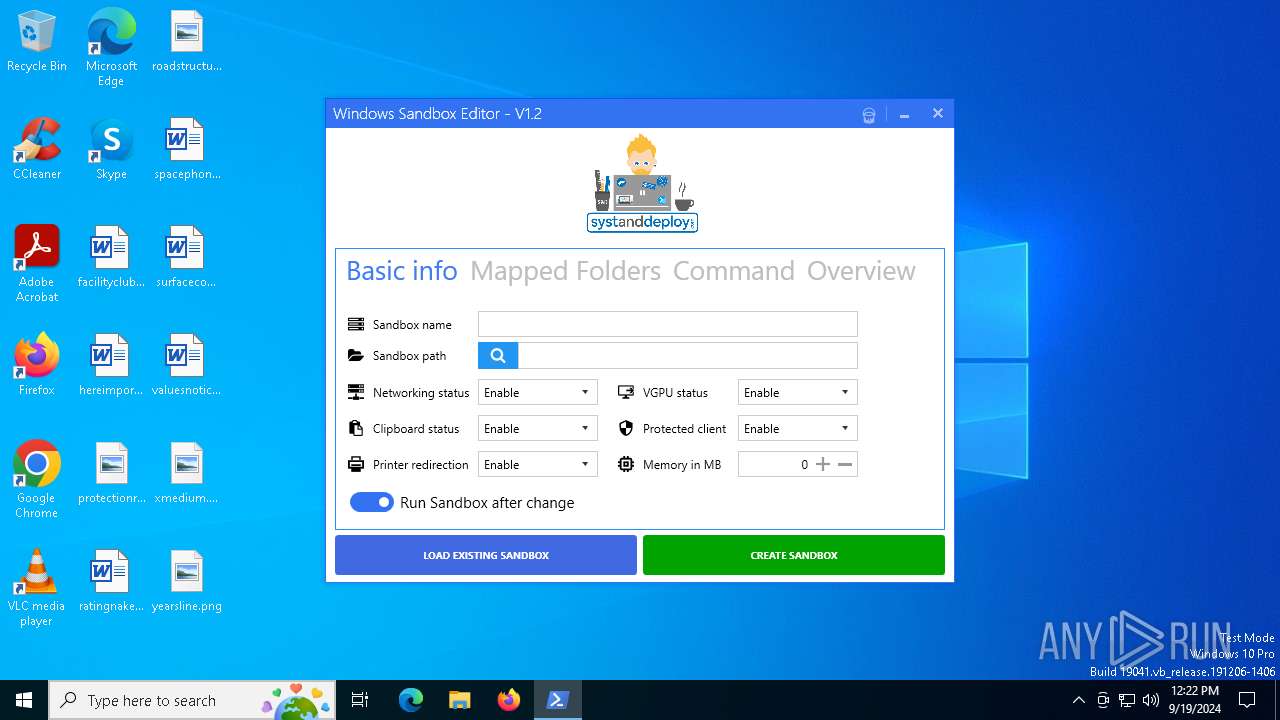
| InternalName: | sandbox_manager.exe |
| LegalCopyright: | |
| OriginalFileName: | sandbox_manager.exe |
| ProductVersion: | 0.0.0.0 |
| AssemblyVersion: | 0.0.0.0 |
Total processes
123
Monitored processes
3
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1860 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | SecuriteInfo.com.Win32.Malware-gen.301.7007.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7000 | "powershell.exe" -executionpolicy bypass -WindowStyle hidden -file "sandbox_manager.ps1" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | SecuriteInfo.com.Win32.Malware-gen.301.7007.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7012 | "C:\Users\admin\AppData\Local\Temp\SecuriteInfo.com.Win32.Malware-gen.301.7007.exe" | C:\Users\admin\AppData\Local\Temp\SecuriteInfo.com.Win32.Malware-gen.301.7007.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Exit code: 0 Version: 0.0.0.0 Modules
| |||||||||||||||
Total events
5 083
Read events
5 083
Write events
0
Delete events
0
Modification events
Executable files
3
Suspicious files
1
Text files
11
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7012 | SecuriteInfo.com.Win32.Malware-gen.301.7007.exe | C:\Users\admin\AppData\Local\Temp\Make-EXE0\Dialog.xaml | text | |
MD5:69C45B14B364C3A07E72819FF13FF11F | SHA256:71FB0D84601CFAA20343595A830CBFCC220E90537D7CD5512CF20C850BCC7235 | |||
| 7012 | SecuriteInfo.com.Win32.Malware-gen.301.7007.exe | C:\Users\admin\AppData\Local\Temp\Make-EXE0\PS1.png | image | |
MD5:A75FB8574D90B677B3AF147FE6CBA570 | SHA256:F54364C6EE16E1D6E7F5936BF03FAB7A3FF44EC962566212EB459C11DD6D4ED6 | |||
| 7000 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_oxwrlnoy.eci.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7012 | SecuriteInfo.com.Win32.Malware-gen.301.7007.exe | C:\Users\admin\AppData\Local\Temp\Make-EXE0\sandbox.ico | image | |
MD5:415BD9CF62CB98A78BB5674AEBAAF748 | SHA256:1F061C767BC44AB1D6EA4F4651953C3BC63A58D6B4715AD8E365A14ABEE13071 | |||
| 7012 | SecuriteInfo.com.Win32.Malware-gen.301.7007.exe | C:\Users\admin\AppData\Local\Temp\Make-EXE0\sandbox_manager.xaml | text | |
MD5:00404614E09C563555F6DD935ECF3D2F | SHA256:94F2DDED7DDEA823A4DE5B67CDFDBB65E9E954657438BE81699096C10A56FA4D | |||
| 7012 | SecuriteInfo.com.Win32.Malware-gen.301.7007.exe | C:\Users\admin\AppData\Local\Temp\Make-EXE0\System.Windows.Interactivity.dll | executable | |
MD5:580244BC805220253A87196913EB3E5E | SHA256:93FBC59E4880AFC9F136C3AC0976ADA7F3FAA7CACEDCE5C824B337CBCA9D2EBF | |||
| 7012 | SecuriteInfo.com.Win32.Malware-gen.301.7007.exe | C:\Users\admin\AppData\Local\Temp\Make-EXE0\MahApps.Metro.IconPacks.dll | executable | |
MD5:E2689EE8F7C54CE73D0EE6F8A22B76C8 | SHA256:D554299000017553CBA1152E44872F3D2327F81597D11B6B53BFFB5CCE399581 | |||
| 7012 | SecuriteInfo.com.Win32.Malware-gen.301.7007.exe | C:\Users\admin\AppData\Local\Temp\Make-EXE0\EXE.png | image | |
MD5:36934AFDEE94F9A3B90E36B2BB79CBE9 | SHA256:954A113C49A0F65DDA5D941EA162A71BDFAD55C2A35FDD214511390C4A9BC9E6 | |||
| 7012 | SecuriteInfo.com.Win32.Malware-gen.301.7007.exe | C:\Users\admin\AppData\Local\Temp\Make-EXE0\sandbox_manager.ps1 | text | |
MD5:6F5B3F4BCA2C6A02153E9AB81090AFA9 | SHA256:551906F63E1EA04B5ADDBA0A8D8C42C4446F1EA339D62CFF528B89EC2659A89E | |||
| 7012 | SecuriteInfo.com.Win32.Malware-gen.301.7007.exe | C:\Users\admin\AppData\Local\Temp\Make-EXE0\MahApps.Metro.dll | executable | |
MD5:A1B84E1D85EF46E744E0A492C73CEFA1 | SHA256:F1A8D821A17D9A38C878B6239F1C142F04495607AD17457022EF58796C127D51 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
24
DNS requests
12
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2120 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
3136 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
3136 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
1456 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
3004 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
2264 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2120 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 52.182.143.209:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
1456 | svchost.exe | 40.126.32.68:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1456 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |