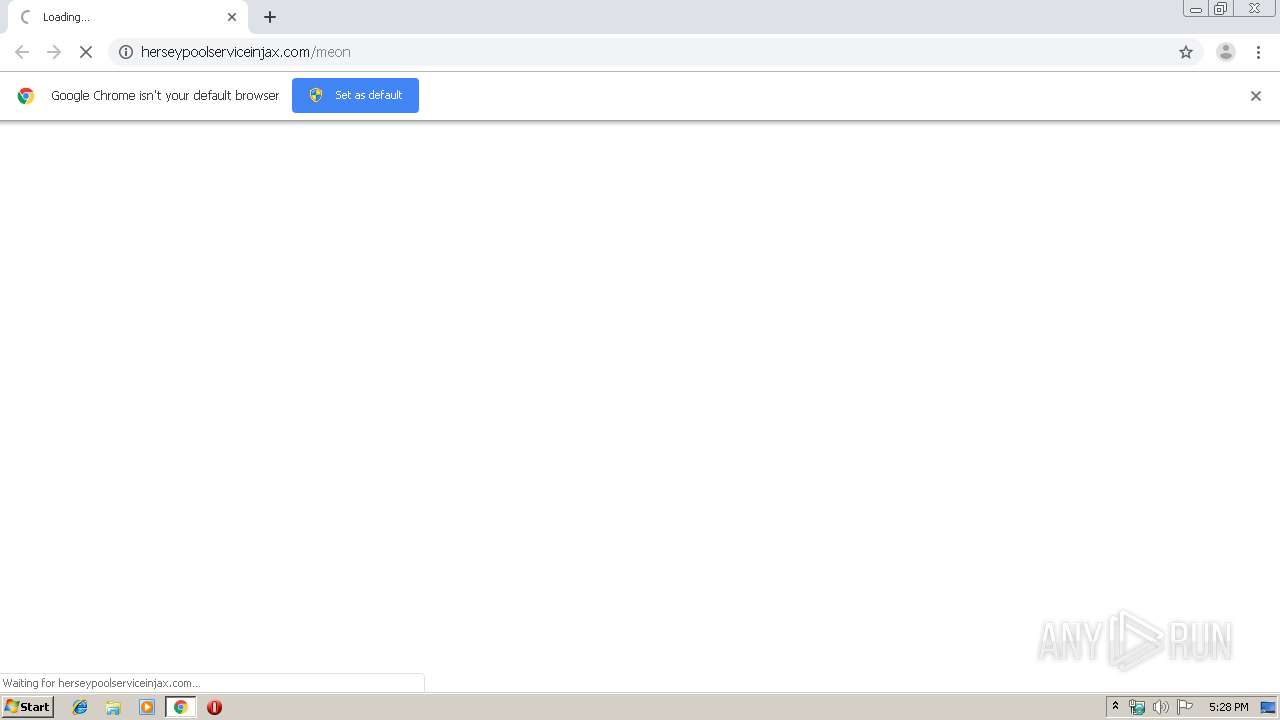
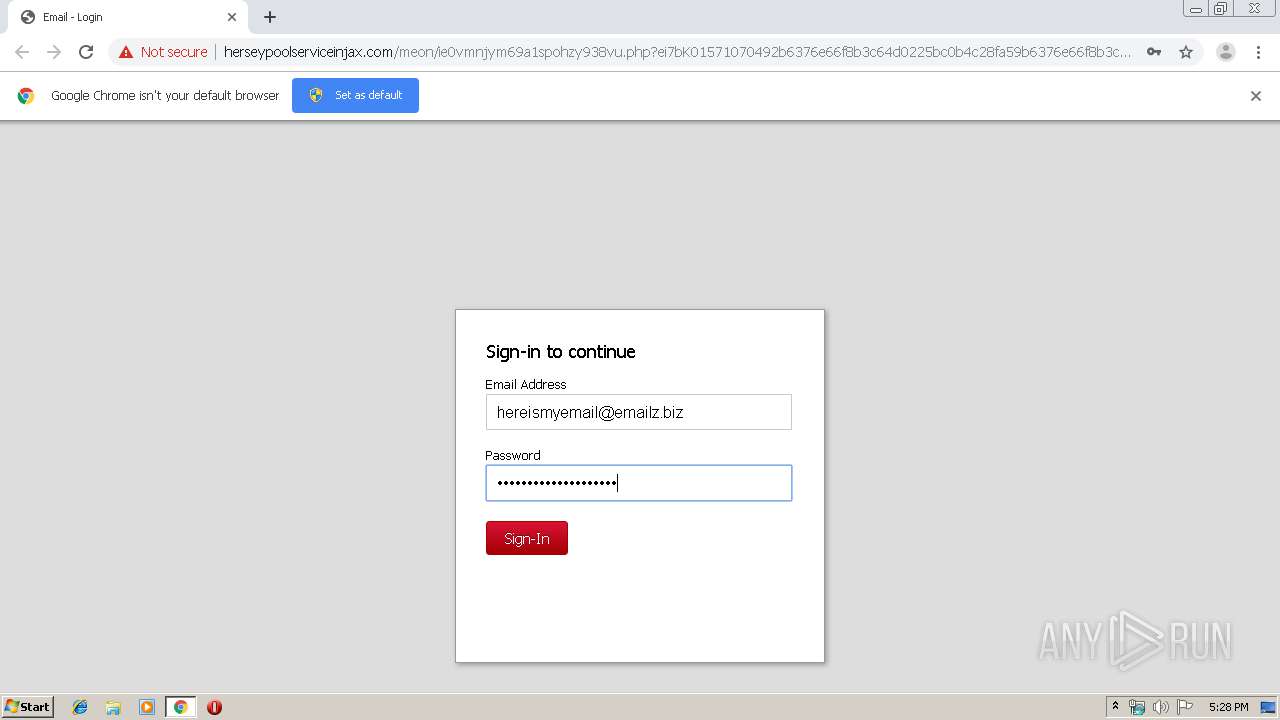
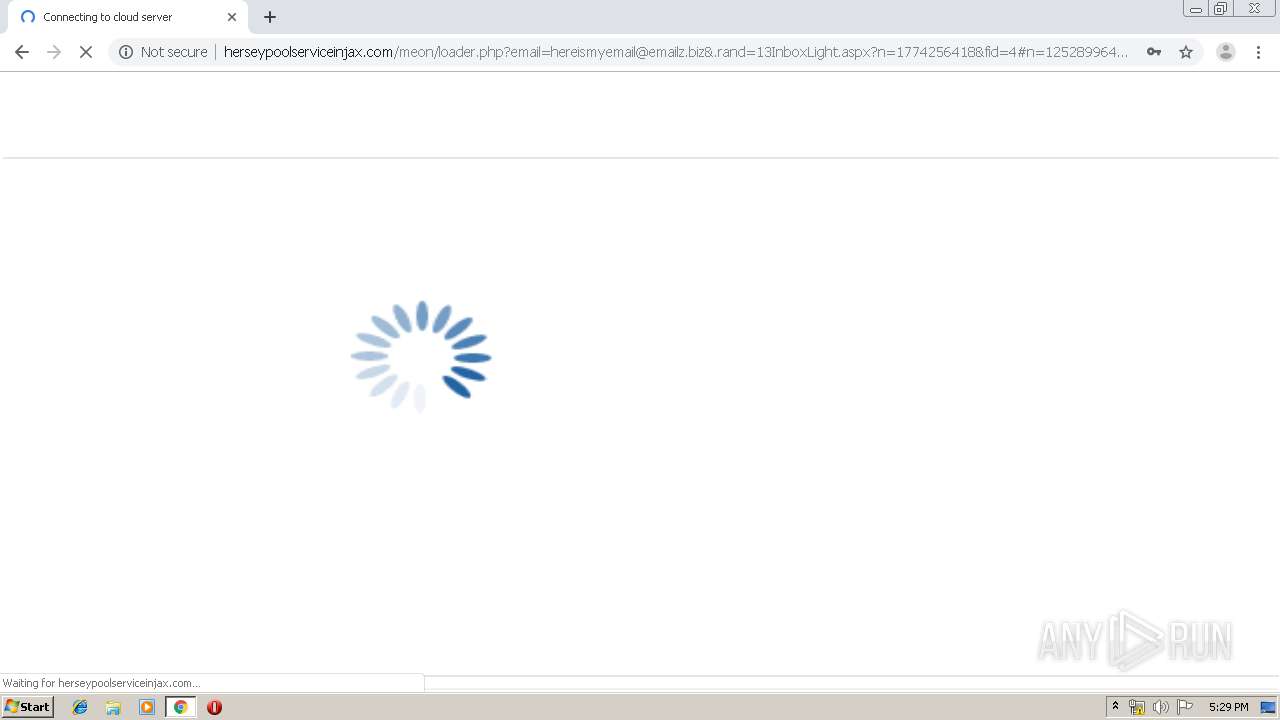
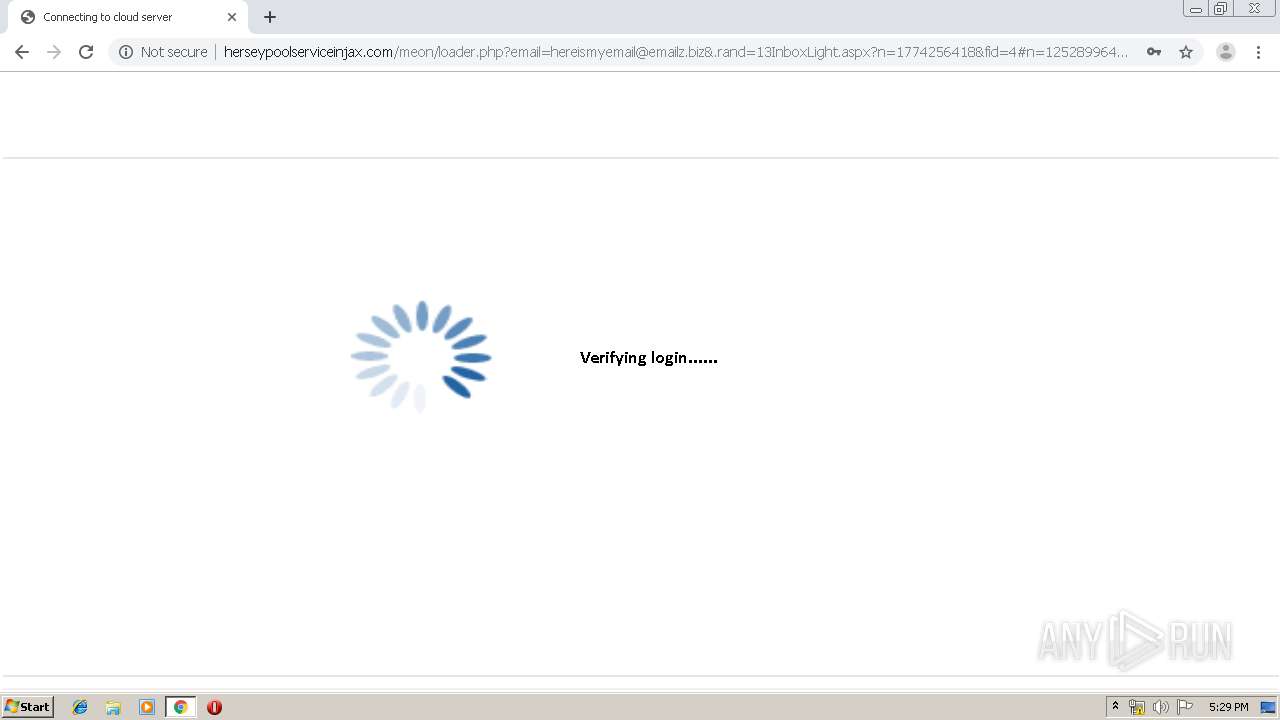
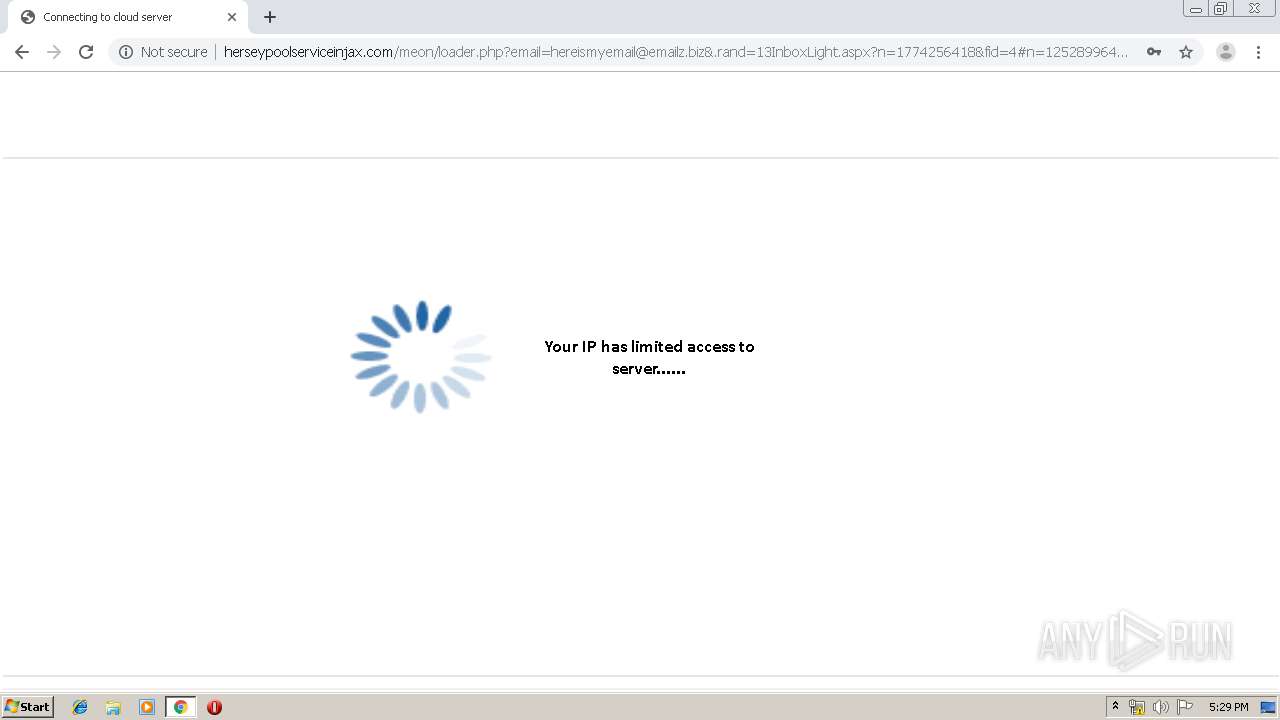
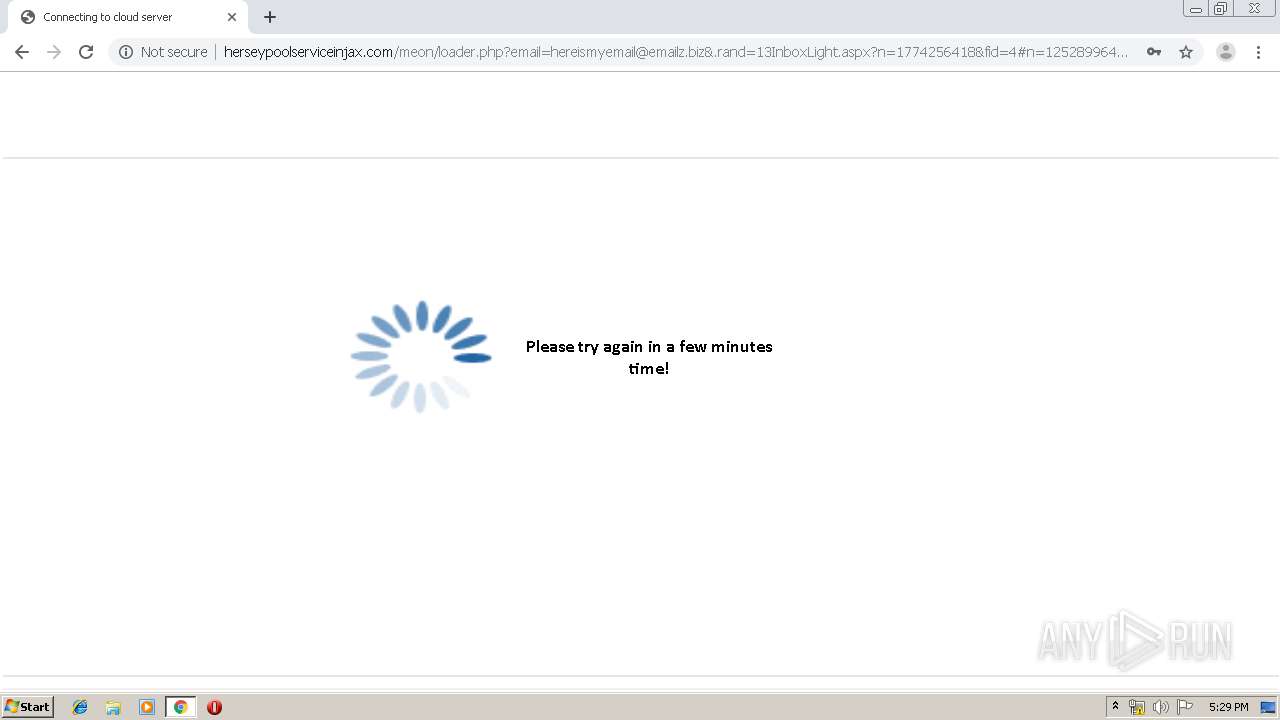
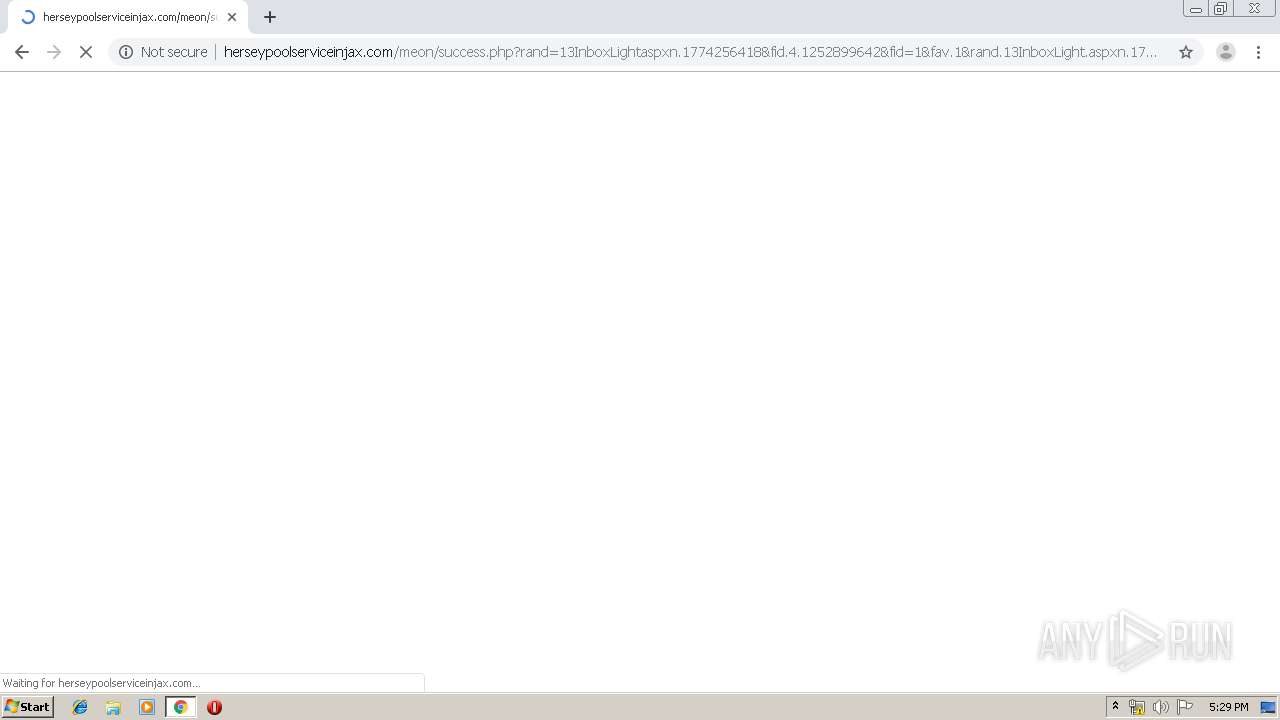
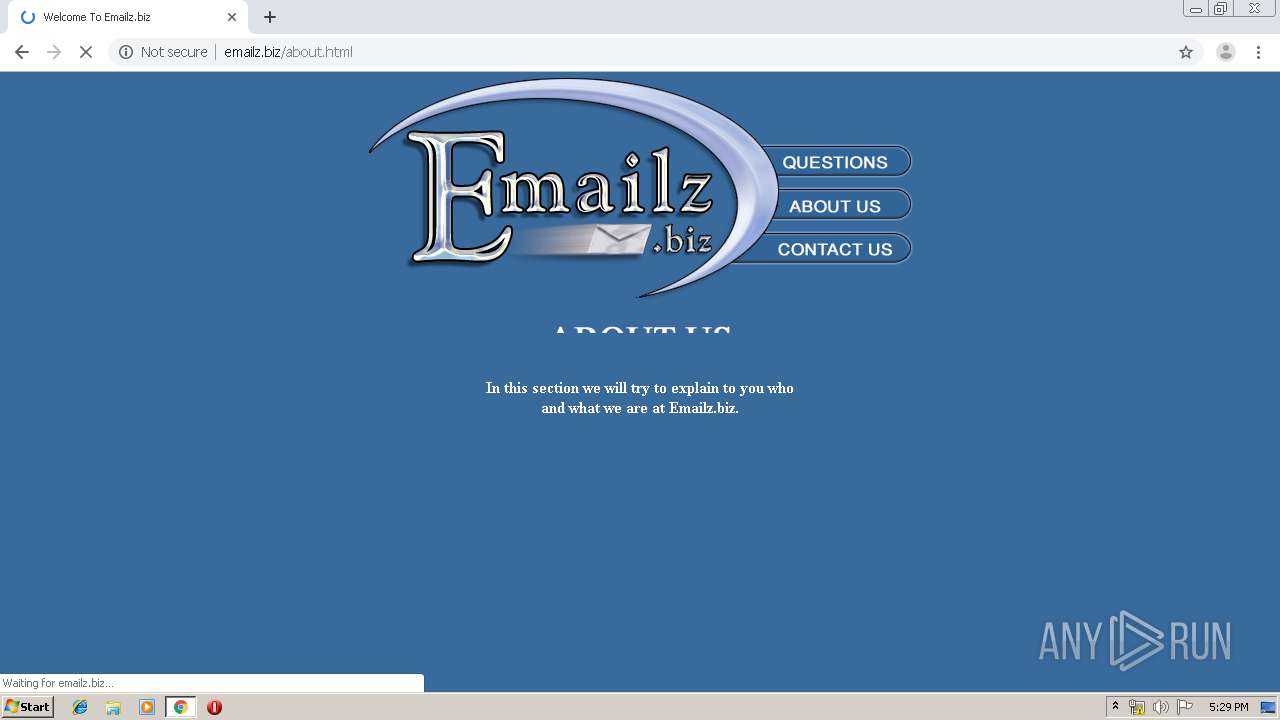
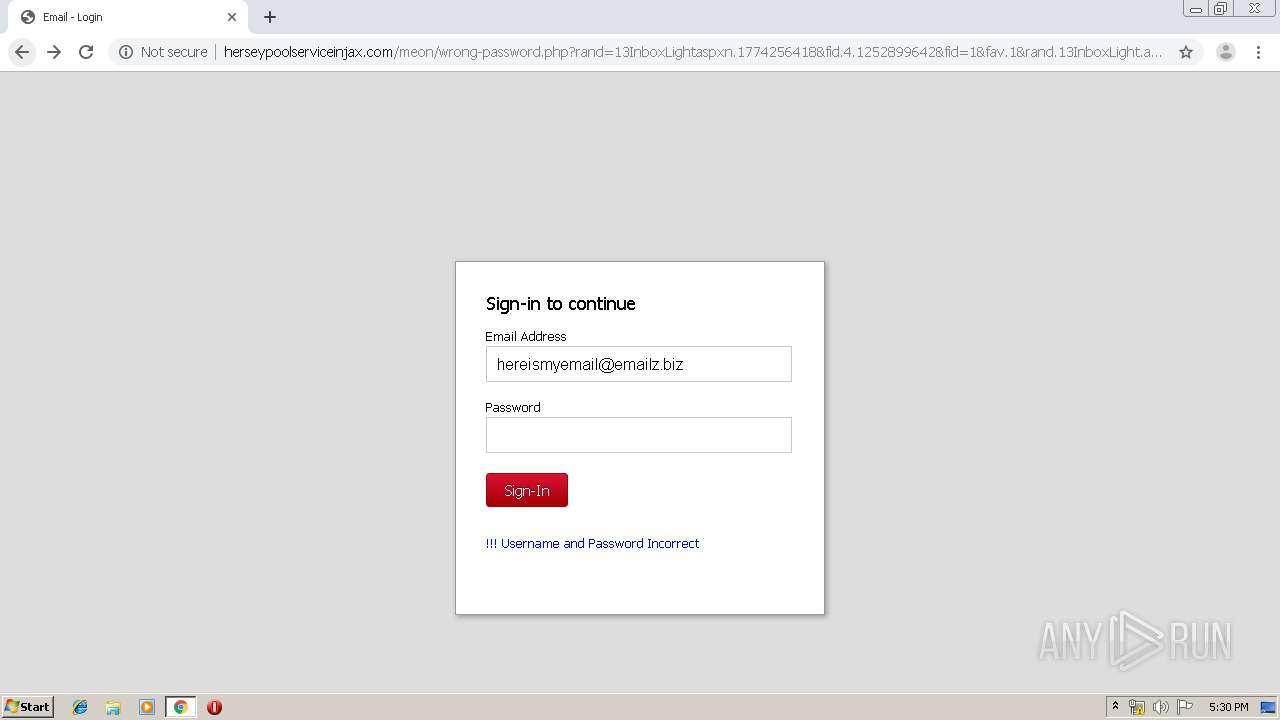
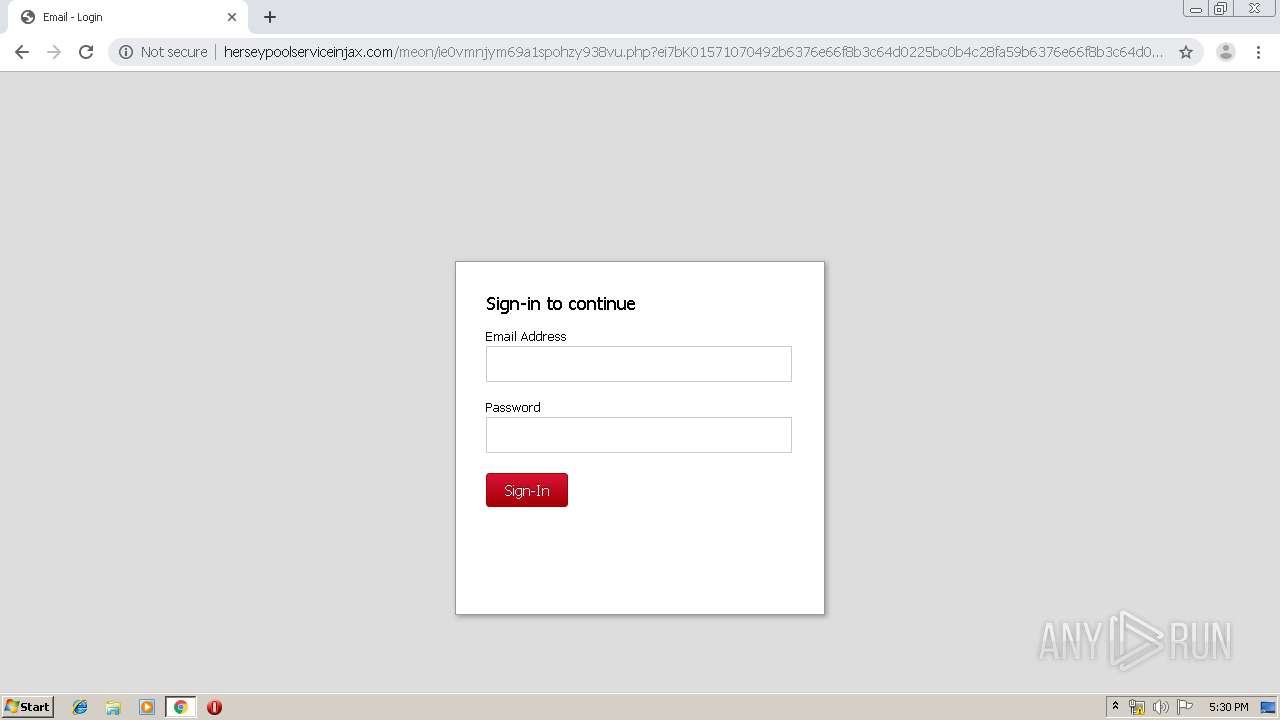
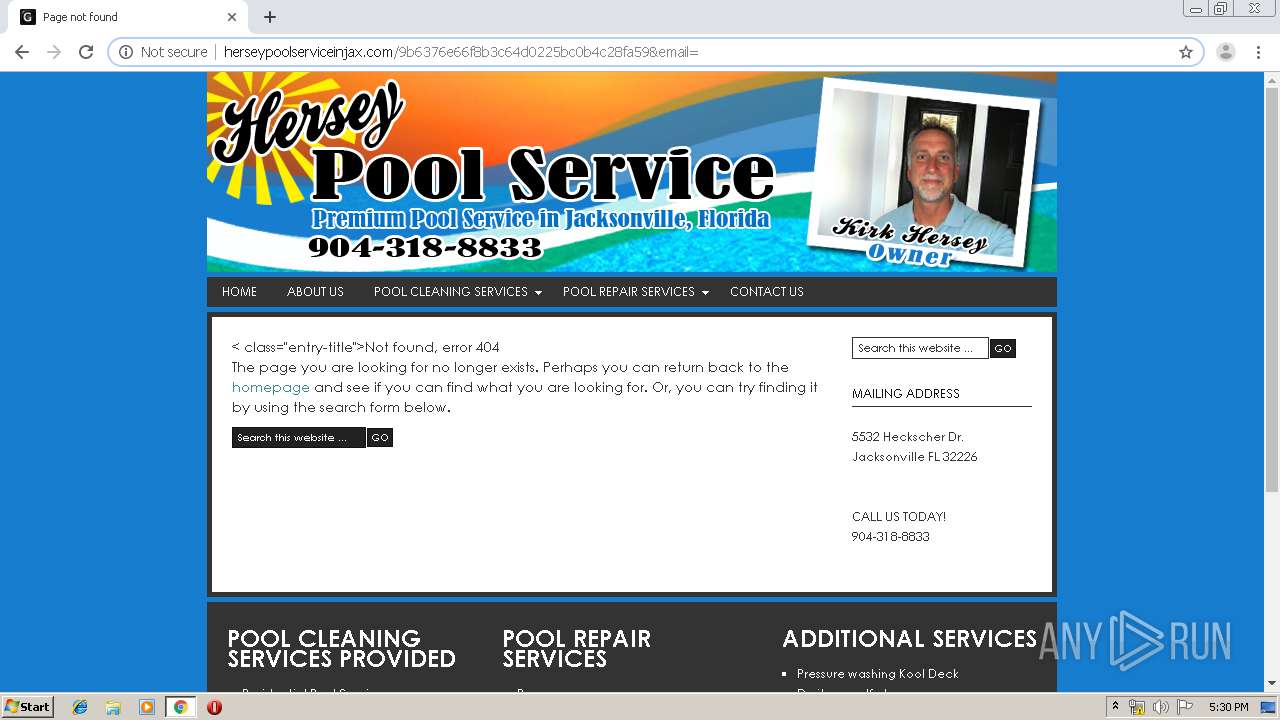
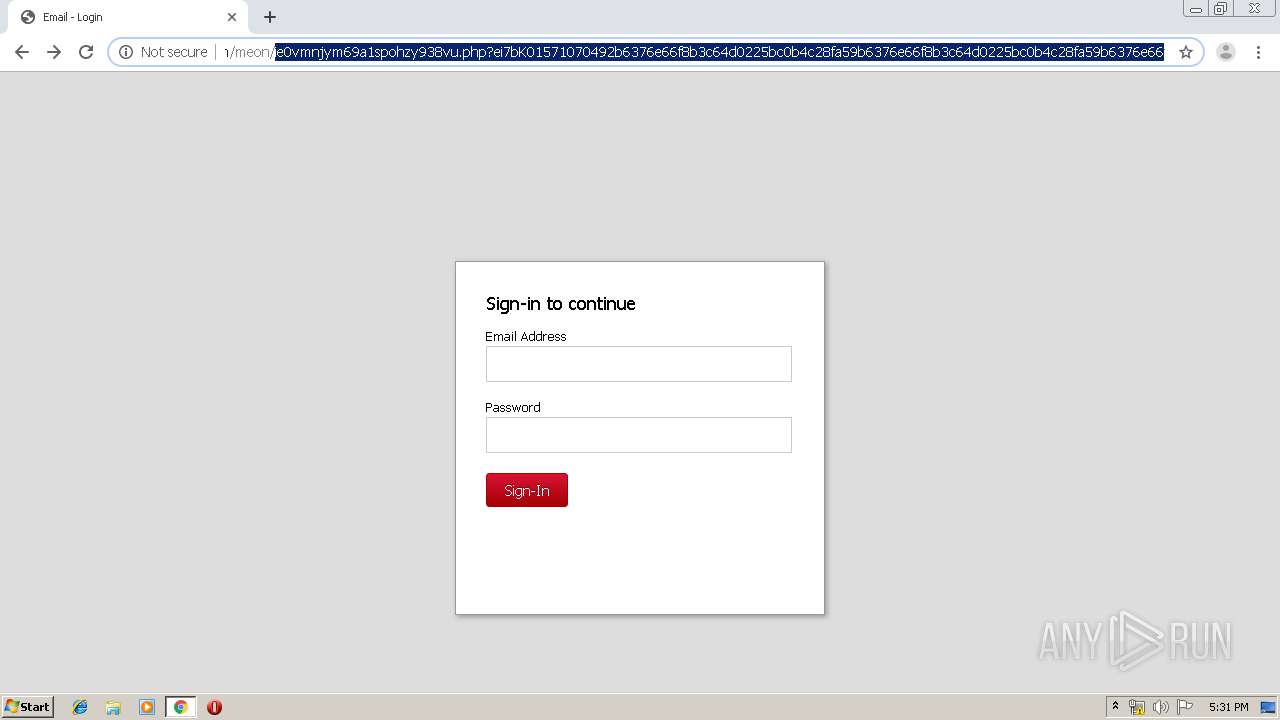
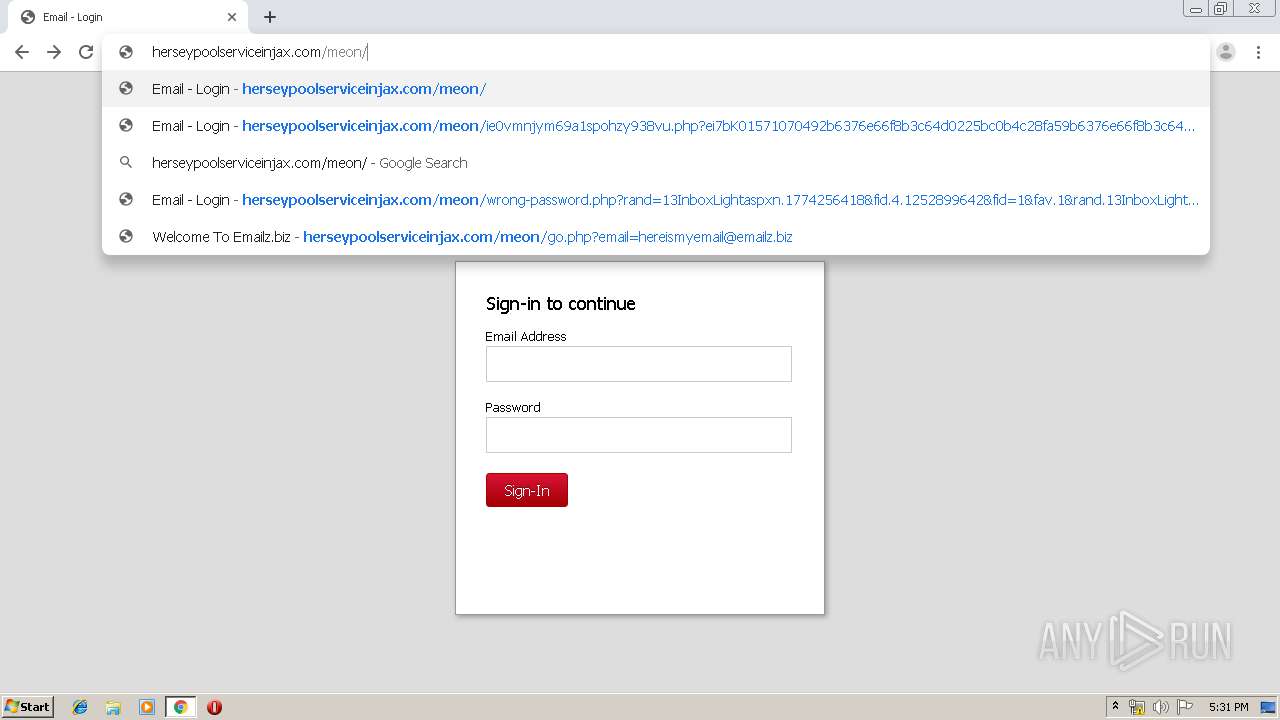
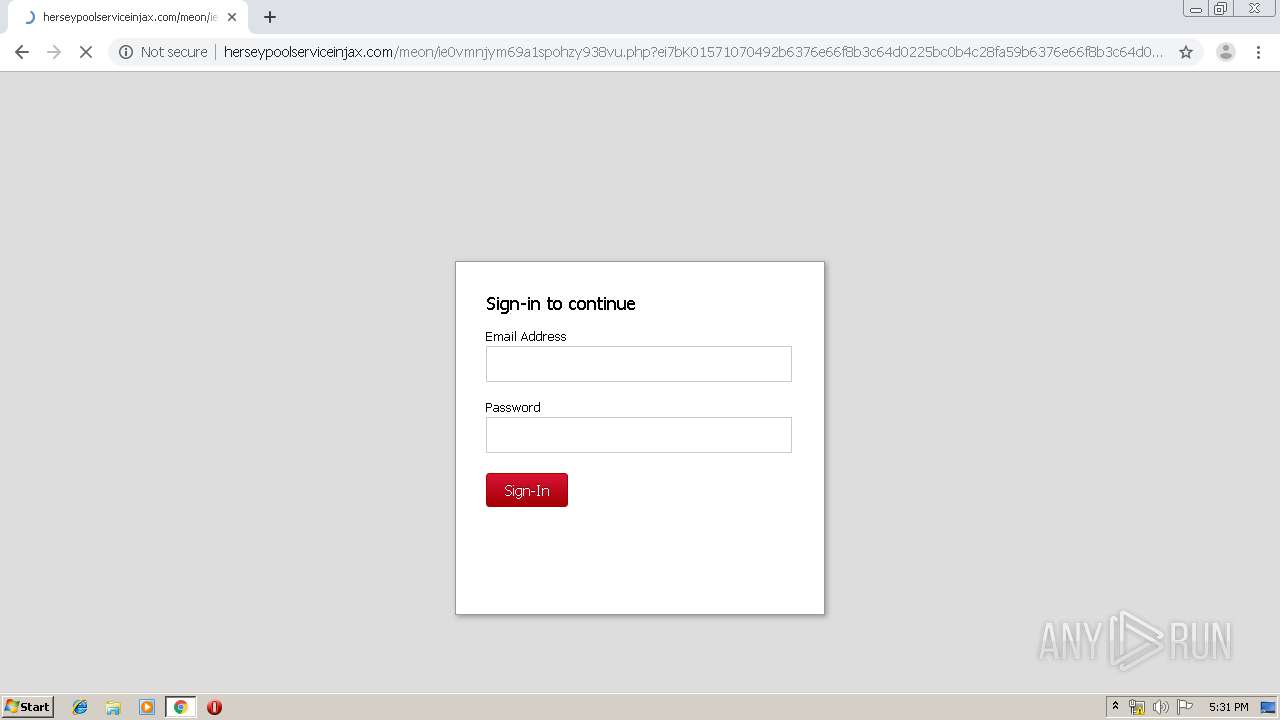
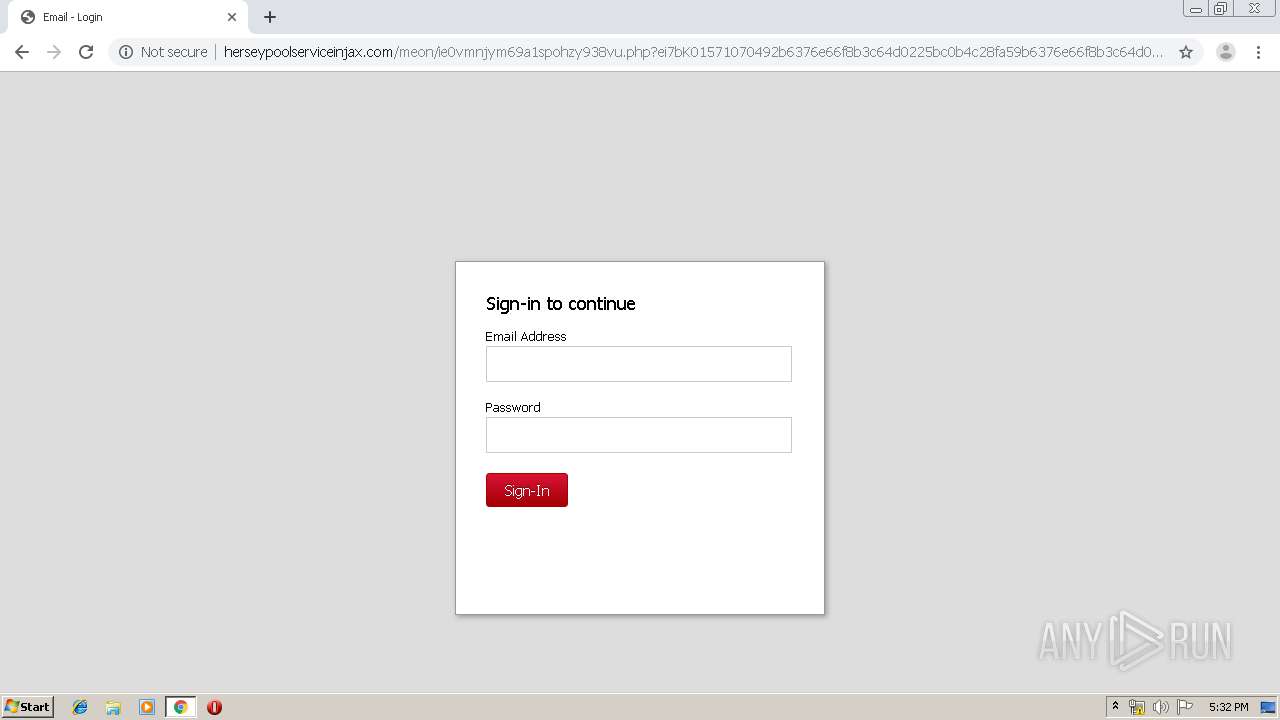
| URL: | http://herseypoolserviceinjax.com/meon |
| Full analysis: | https://app.any.run/tasks/1c4bf6f7-fd6c-4be7-9f17-f53115e060bd |
| Verdict: | Malicious activity |
| Analysis date: | October 14, 2019, 16:27:53 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 1D1DF02CF03DA8194A2333C2E2BD6CB6 |
| SHA1: | 4BB6248F799DBDBA59811953A0DA9A7287A666C1 |
| SHA256: | CDDF0144E433B1DE1E3F2D6C984017D63DD626DE550F59B21B2425BDD9026804 |
| SSDEEP: | 3:N1KWAG59T1E34Tn:CWooTn |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 1532)
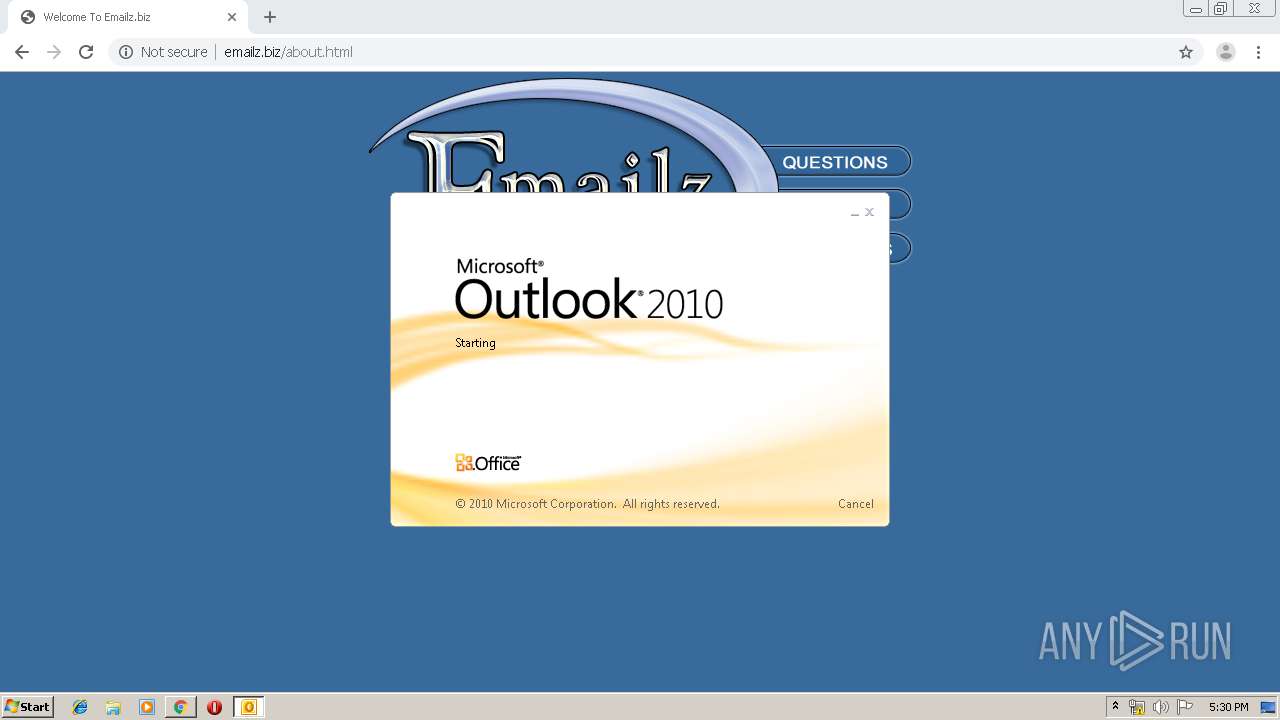
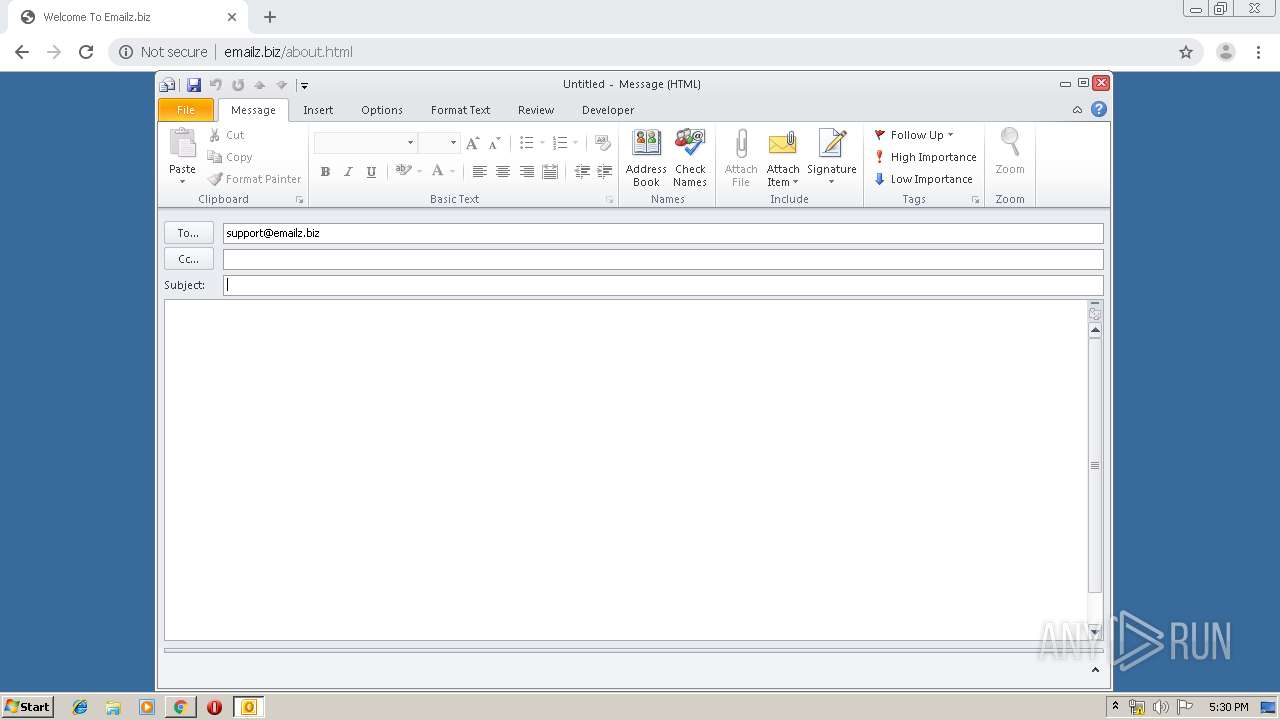
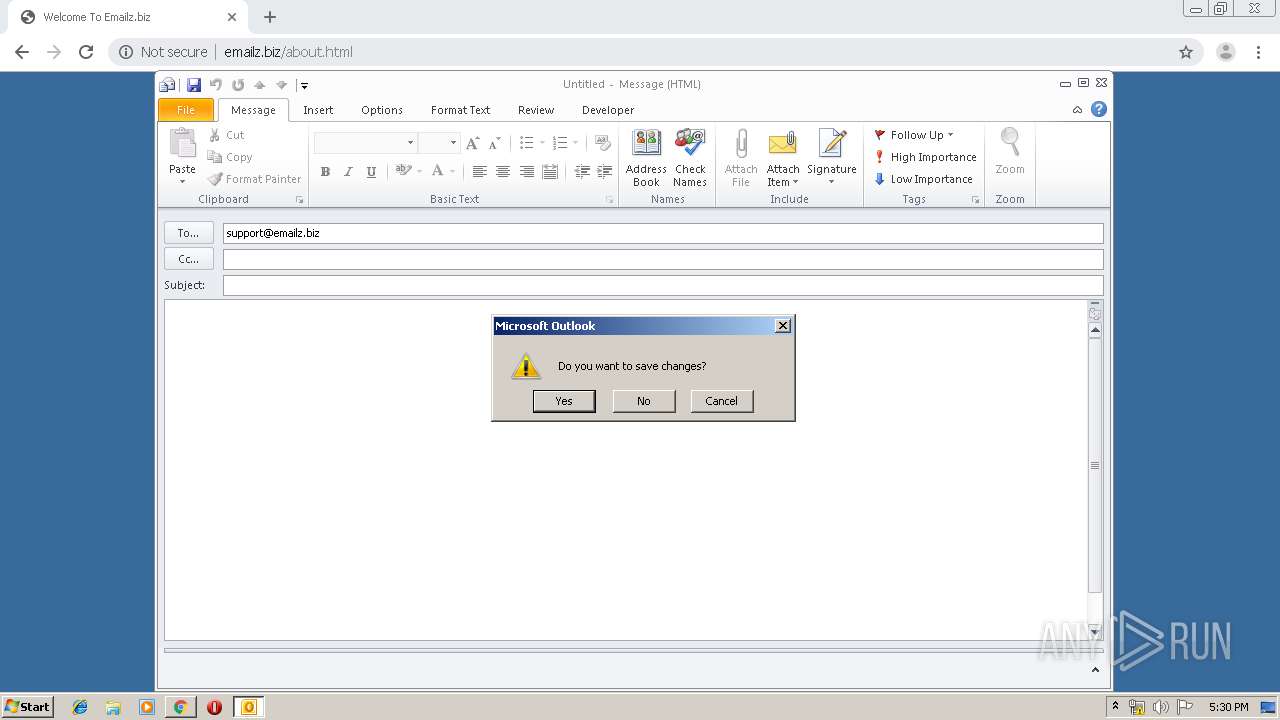
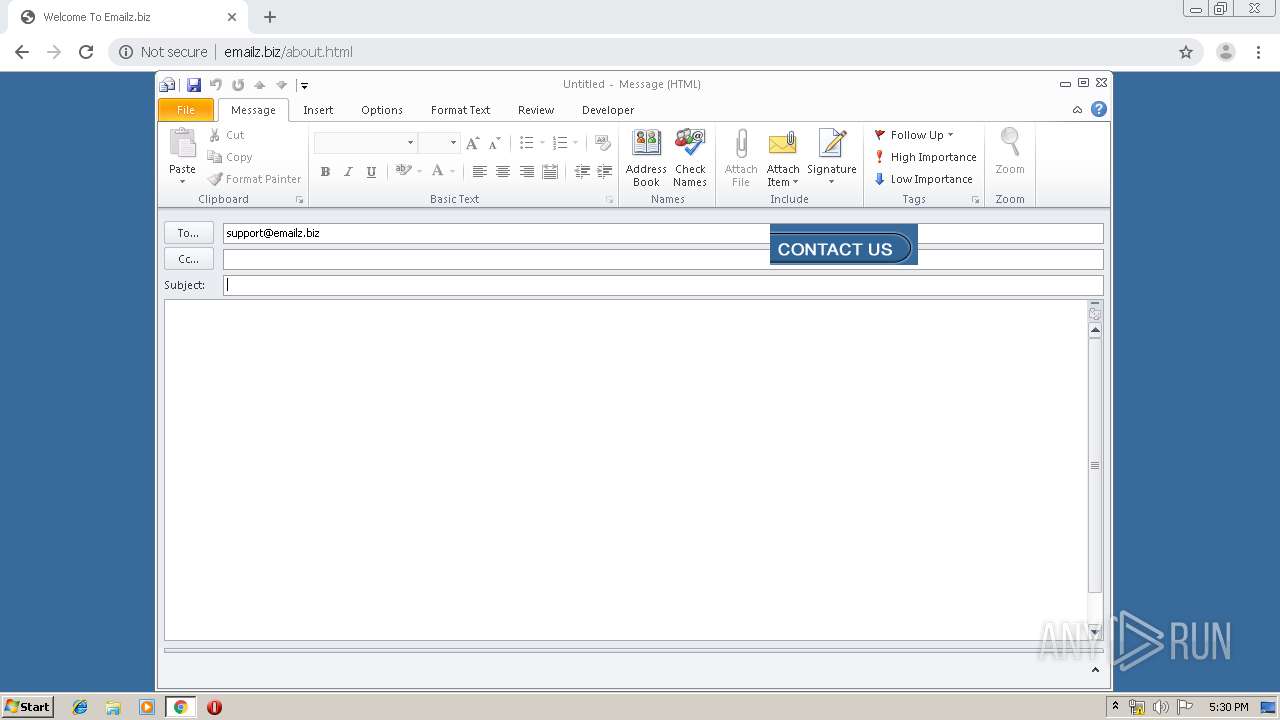
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 2468)
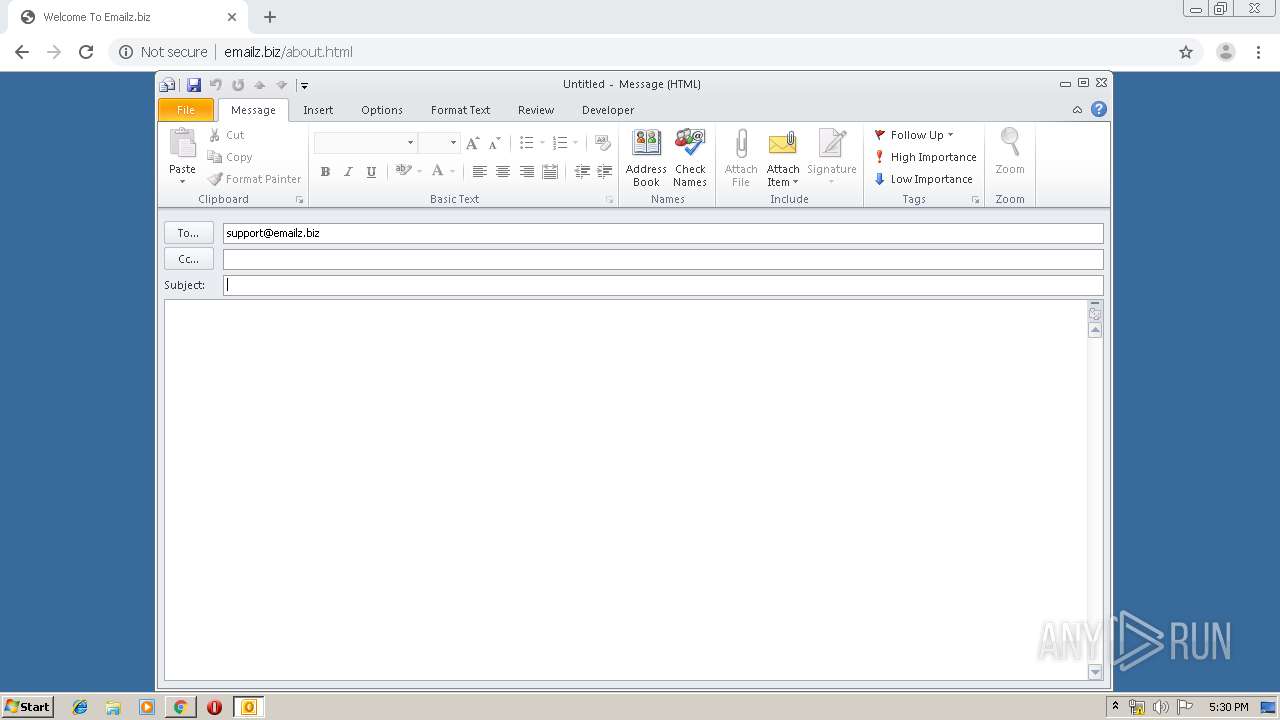
Creates files in the user directory
- OUTLOOK.EXE (PID: 2468)
INFO
Application launched itself
- chrome.exe (PID: 1532)
Reads the hosts file
- chrome.exe (PID: 1596)
- chrome.exe (PID: 1532)
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 2468)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
69
Monitored processes
30
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 940 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=920,314740921139912077,6852643483249543325,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=10224369274963961552 --mojo-platform-channel-handle=4024 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1532 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "http://herseypoolserviceinjax.com/meon" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1544 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=920,314740921139912077,6852643483249543325,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11830081070364113806 --mojo-platform-channel-handle=3980 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1596 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=920,314740921139912077,6852643483249543325,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=6305620532044550319 --mojo-platform-channel-handle=1584 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1636 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=920,314740921139912077,6852643483249543325,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=4765163541834390307 --mojo-platform-channel-handle=4304 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1756 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=920,314740921139912077,6852643483249543325,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=18012468246547611975 --mojo-platform-channel-handle=1036 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1884 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2928 --on-initialized-event-handle=312 --parent-handle=316 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2076 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=920,314740921139912077,6852643483249543325,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15477228118538691699 --mojo-platform-channel-handle=3508 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2192 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=920,314740921139912077,6852643483249543325,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4067188573591342353 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2236 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2196 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=920,314740921139912077,6852643483249543325,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=7128698006347615281 --mojo-platform-channel-handle=4308 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
1 680
Read events
1 431
Write events
224
Delete events
25
Modification events
| (PID) Process: | (1532) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1532) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1532) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1532) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1532) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1884) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 1532-13215544088813125 |
Value: 259 | |||
| (PID) Process: | (1532) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1532) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1532) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (1532) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
60
Text files
335
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1532 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\e86115d9-c7e6-4687-90a2-695e9dccc999.tmp | — | |
MD5:— | SHA256:— | |||
| 1532 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1532 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1532 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF39a4e5.TMP | text | |
MD5:— | SHA256:— | |||
| 1532 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1532 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1532 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1532 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 1532 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1532 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
68
TCP/UDP connections
68
DNS requests
22
Threats
11
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
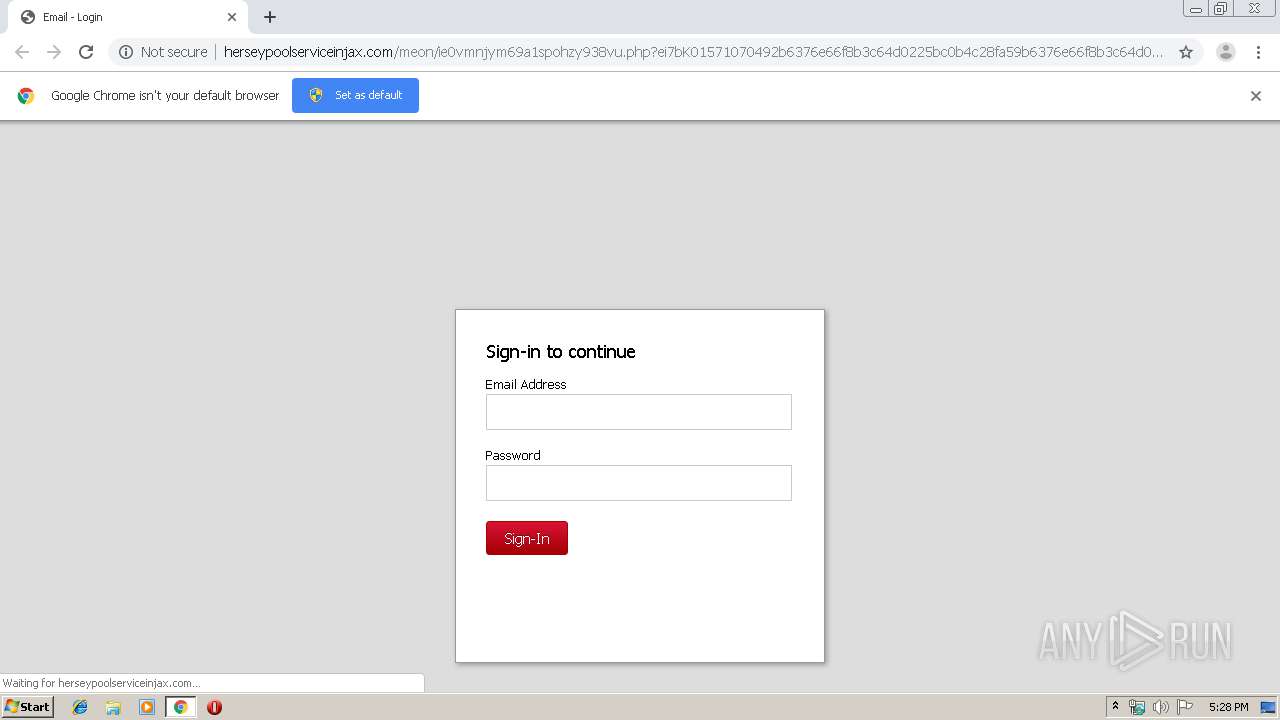
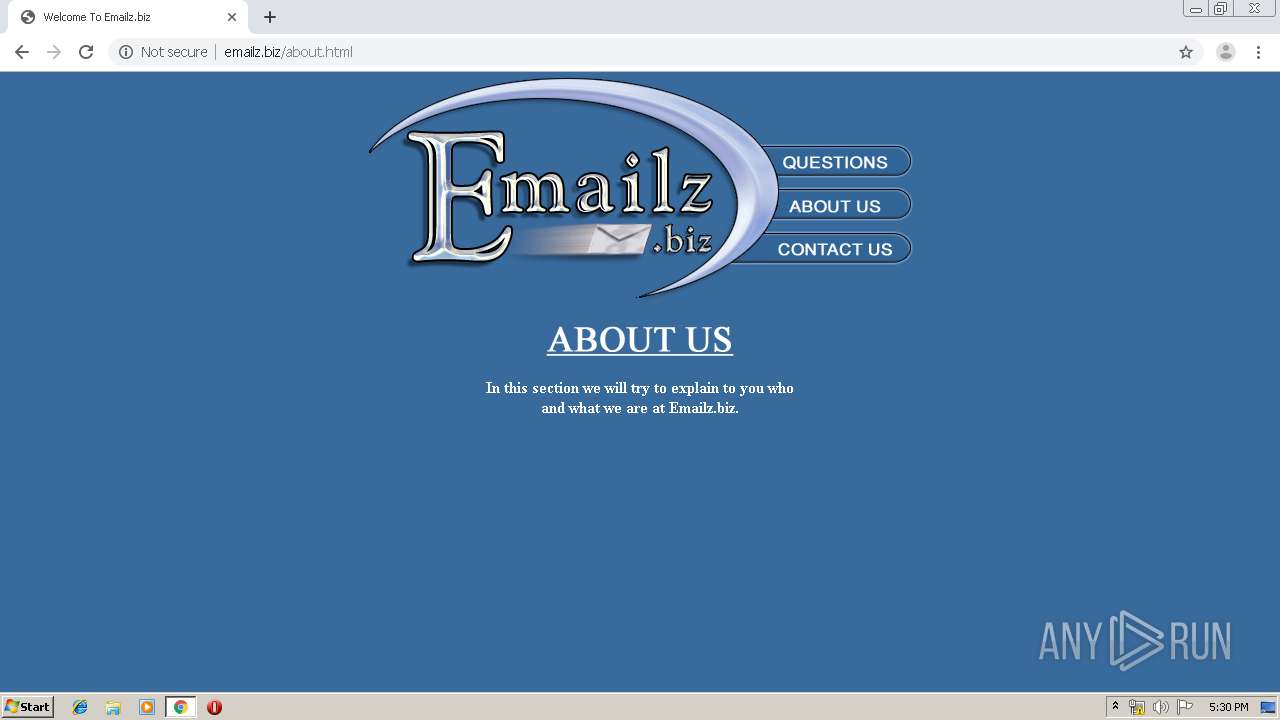
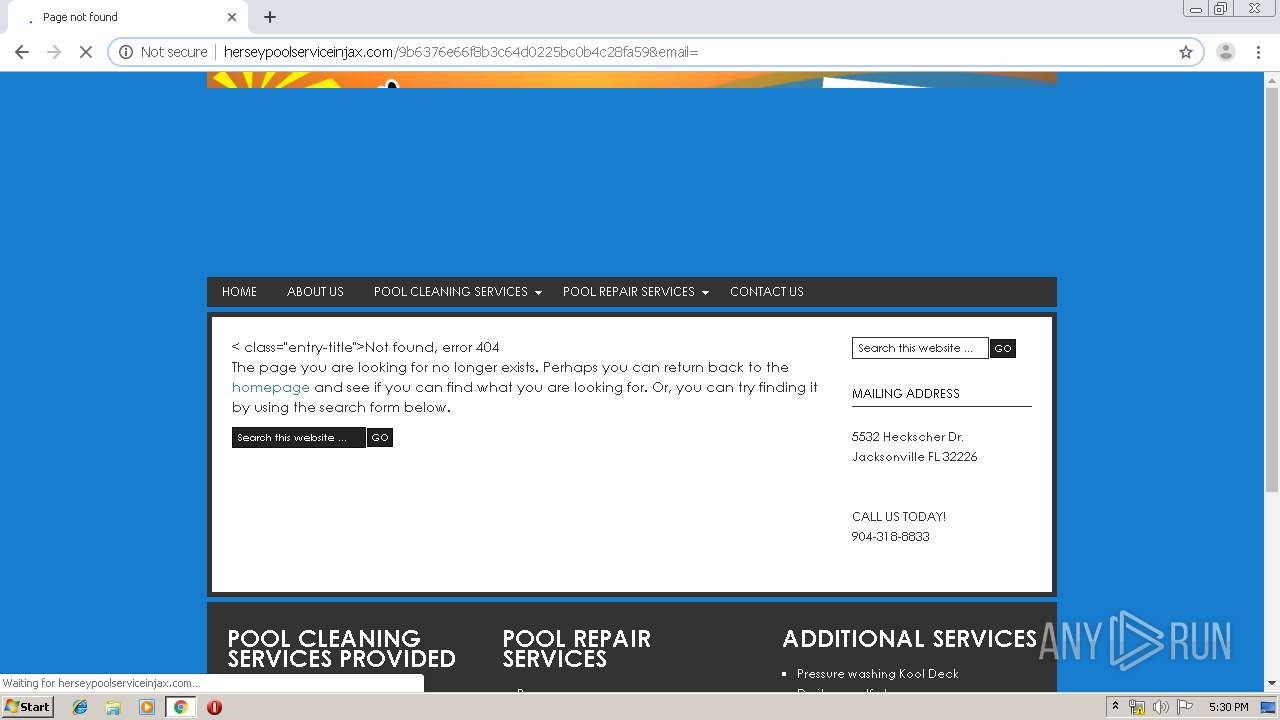
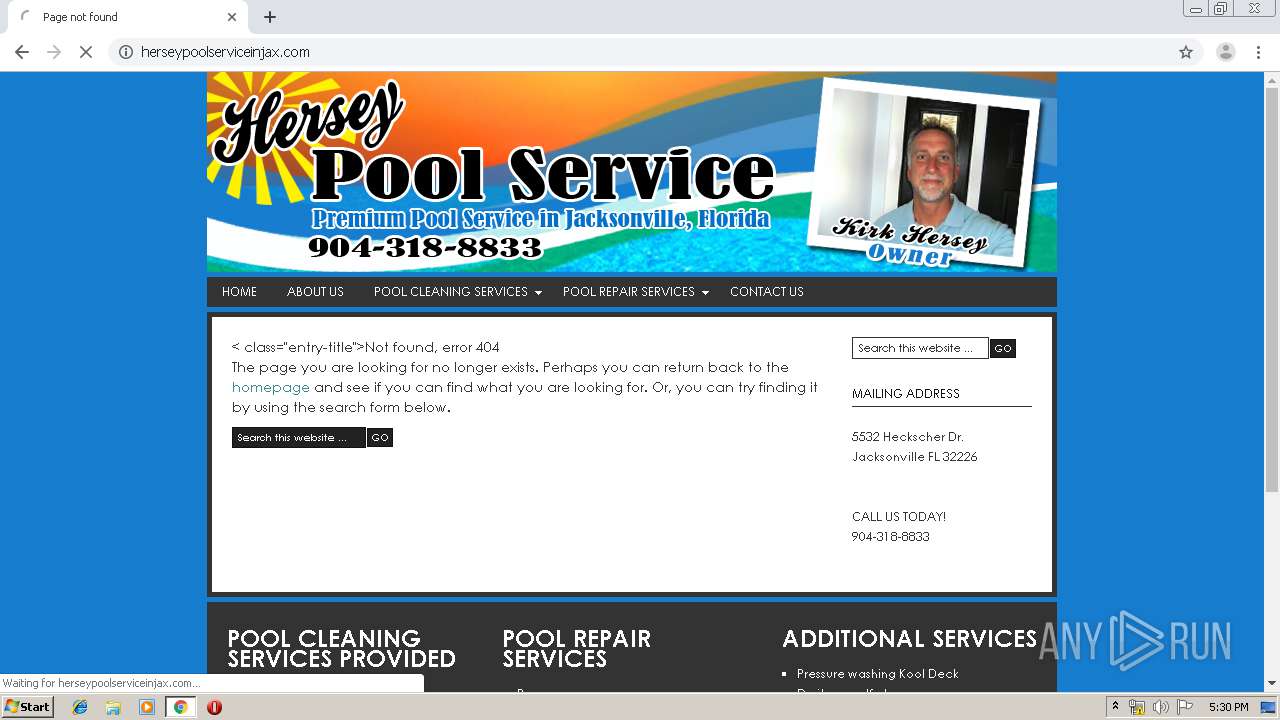
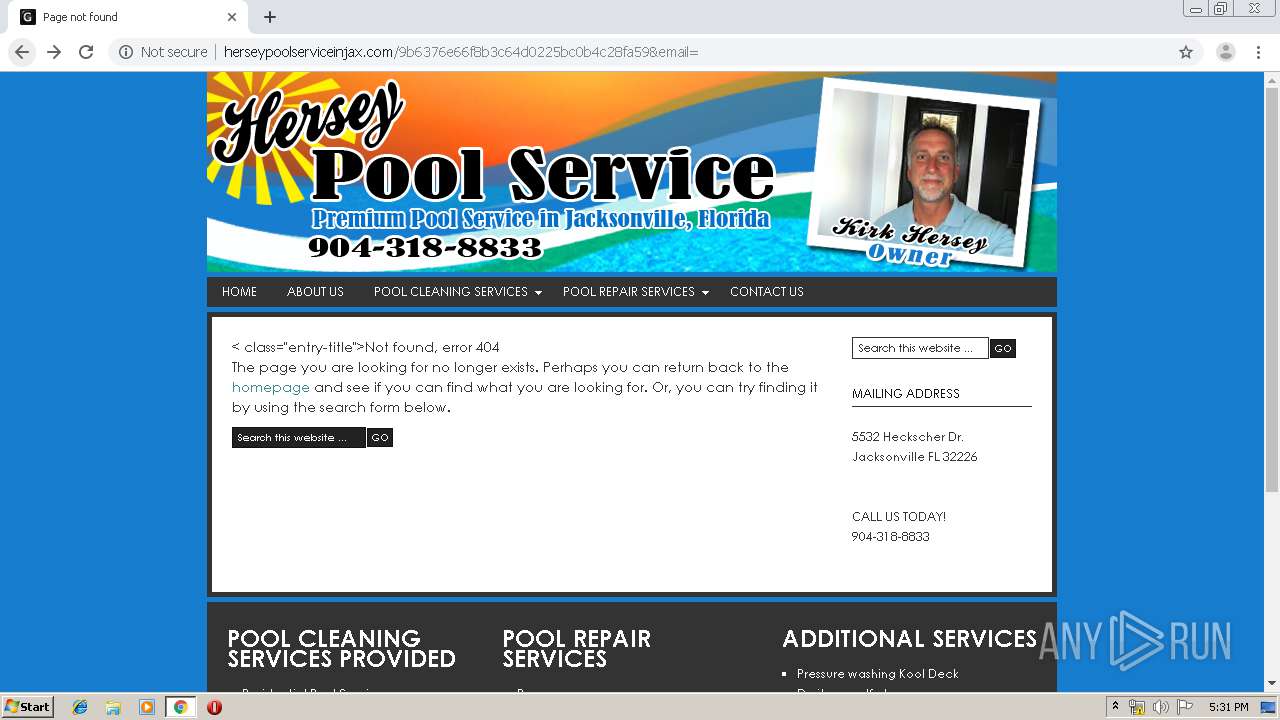
1596 | chrome.exe | GET | 302 | 72.52.229.85:80 | http://herseypoolserviceinjax.com/meon/ | US | html | 247 b | suspicious |
1596 | chrome.exe | GET | — | 72.52.229.85:80 | http://herseypoolserviceinjax.com/meon/js/login.js?2230 | US | — | — | suspicious |
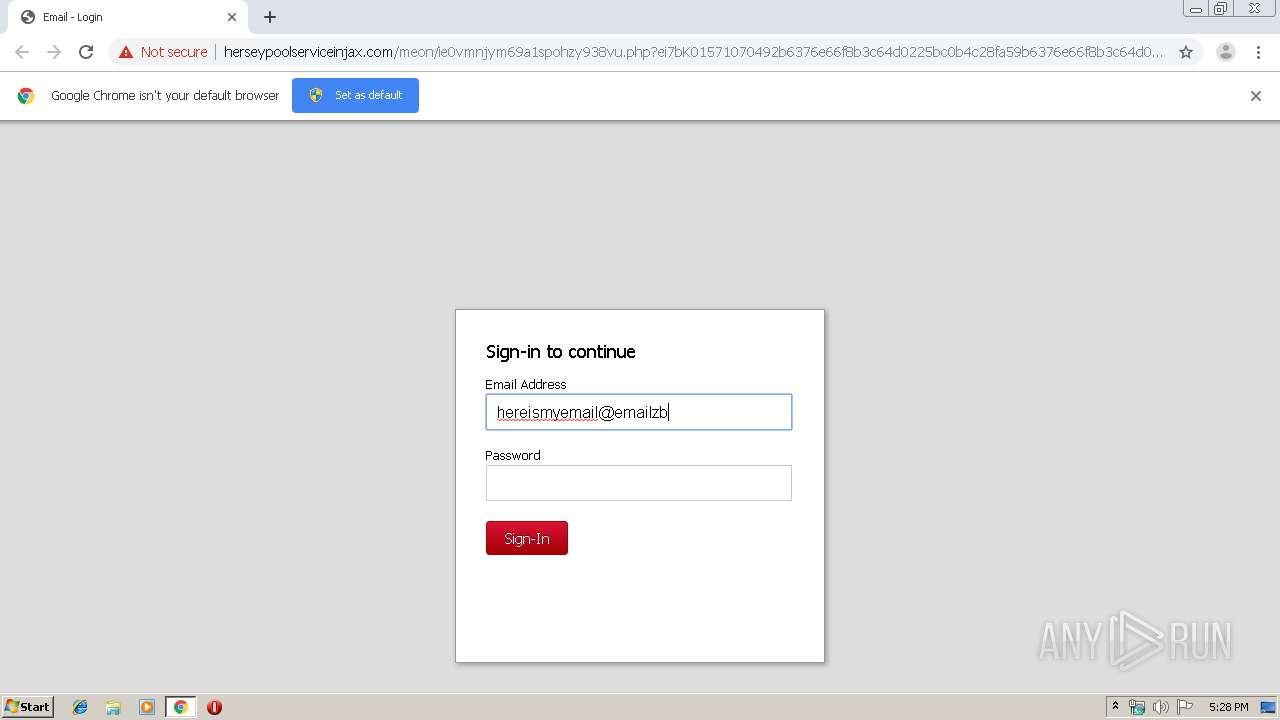
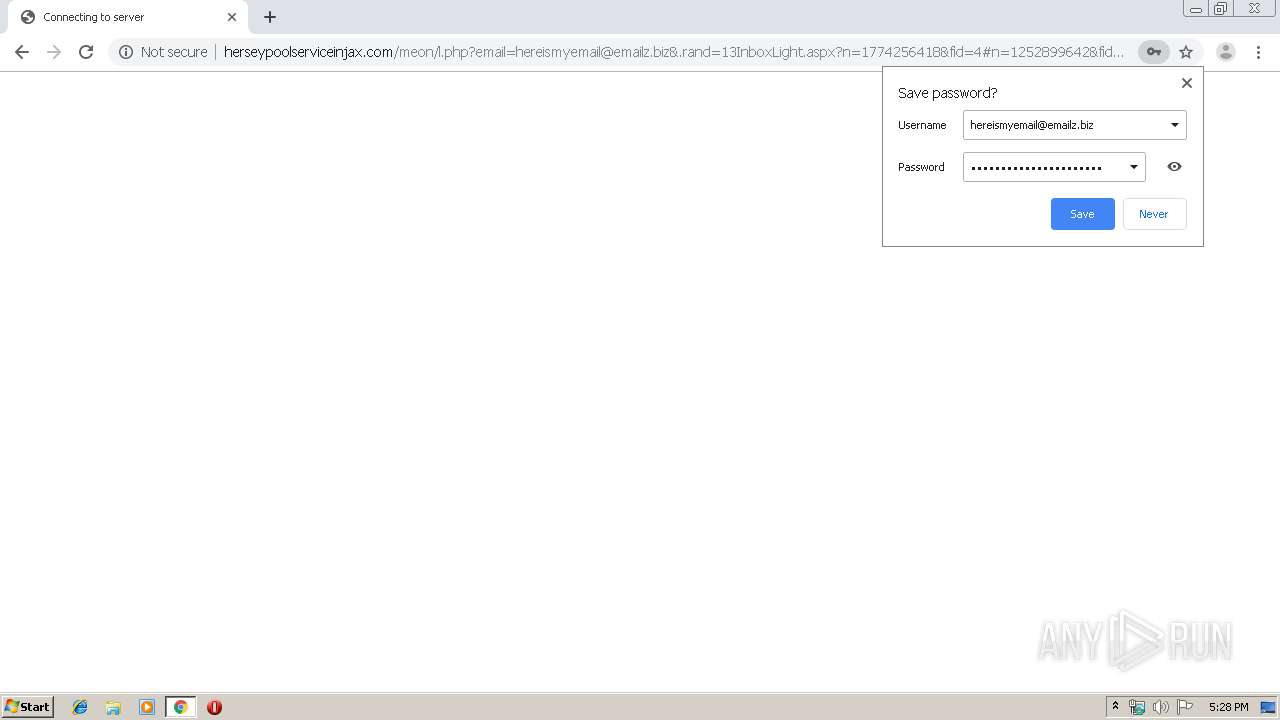
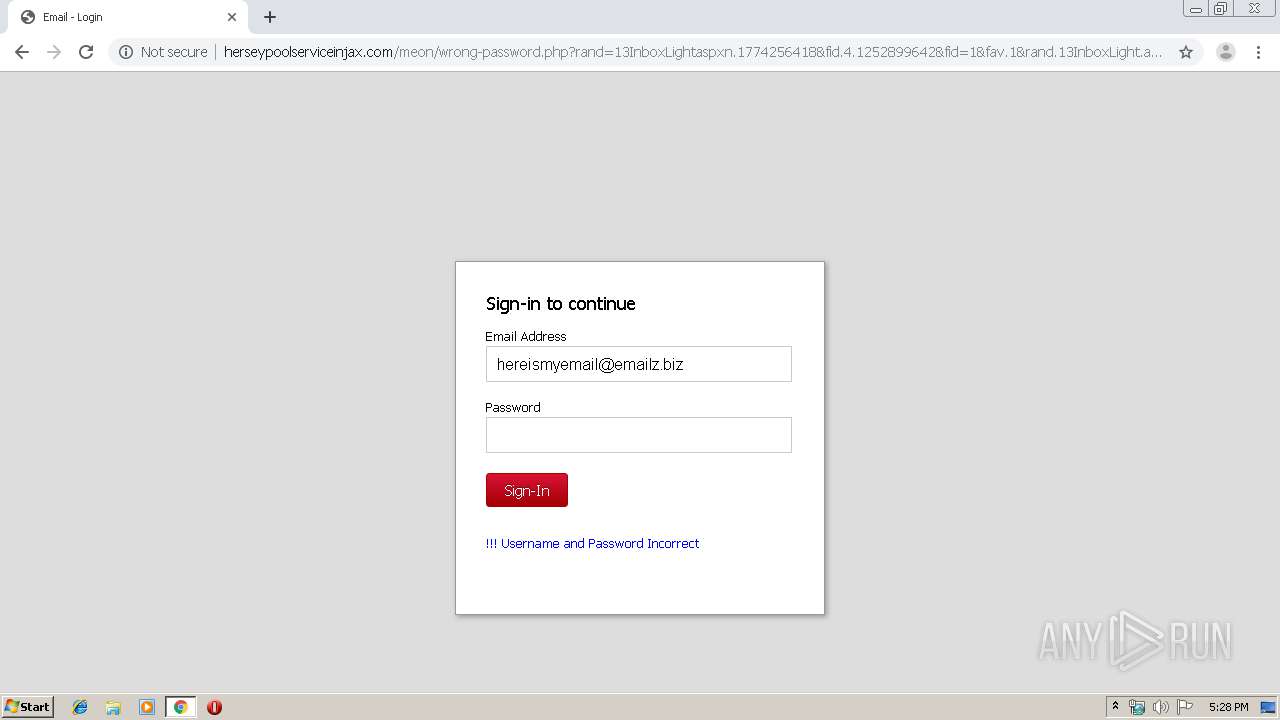
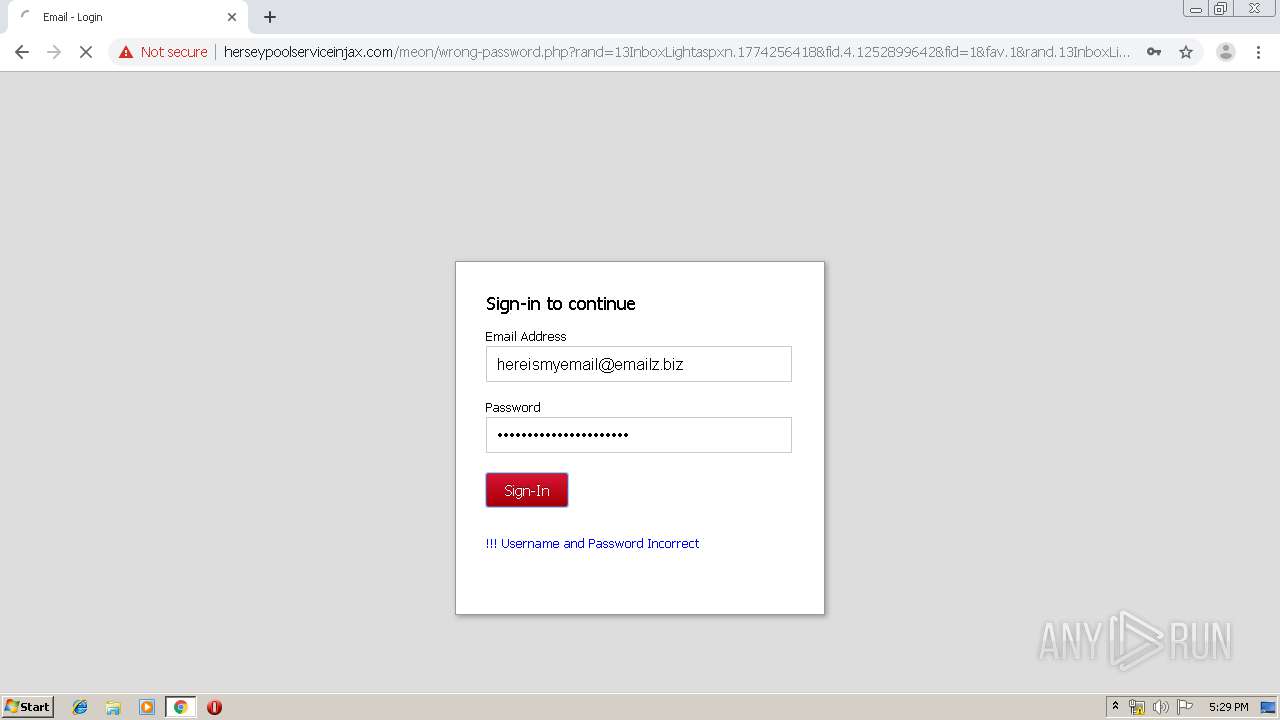
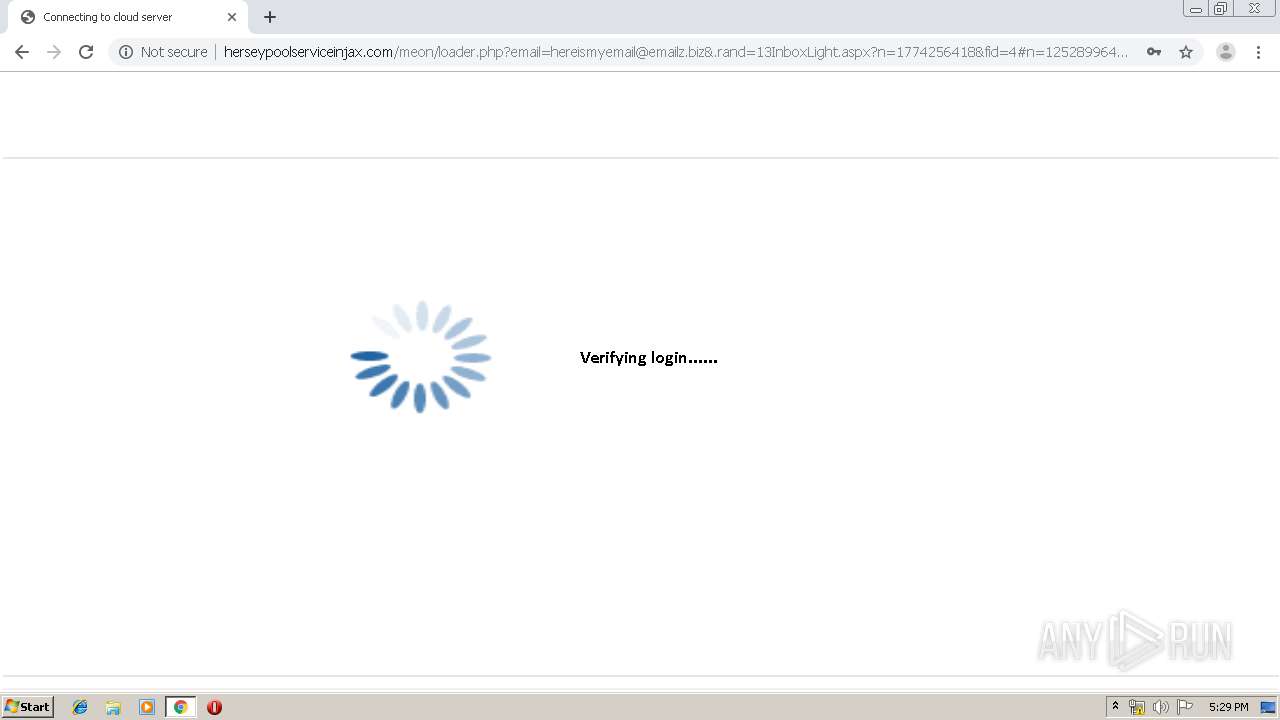
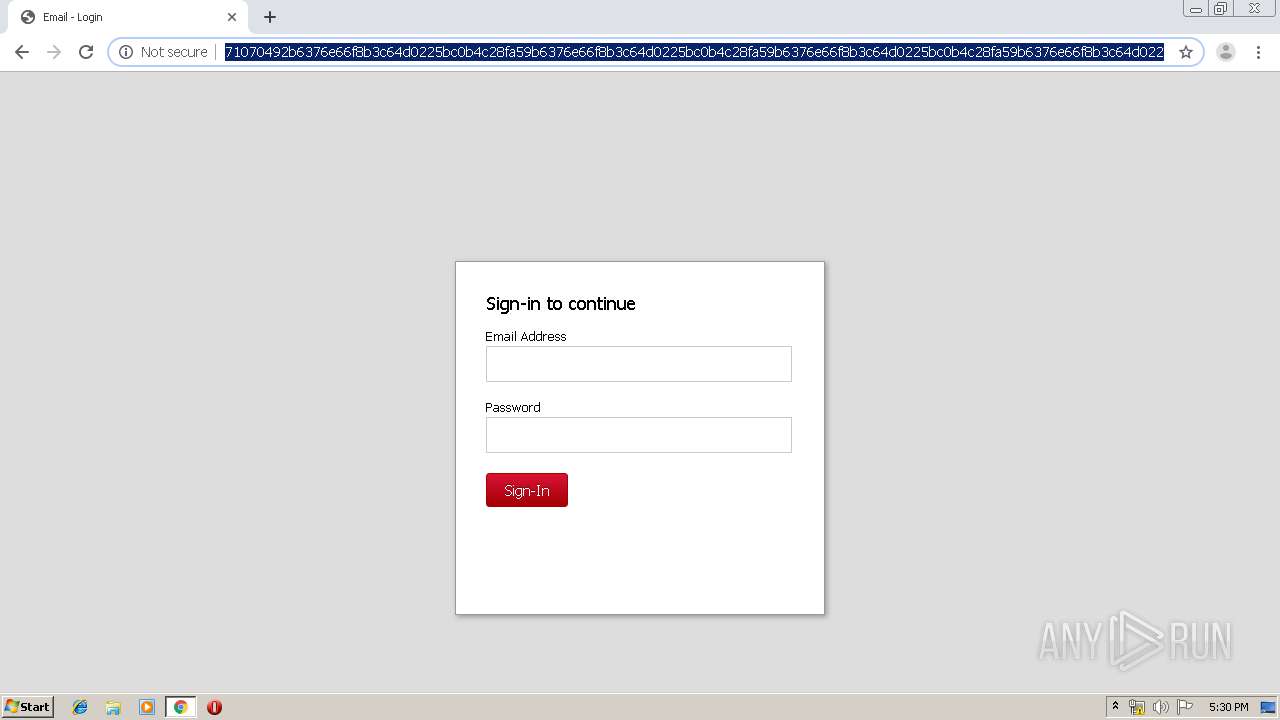
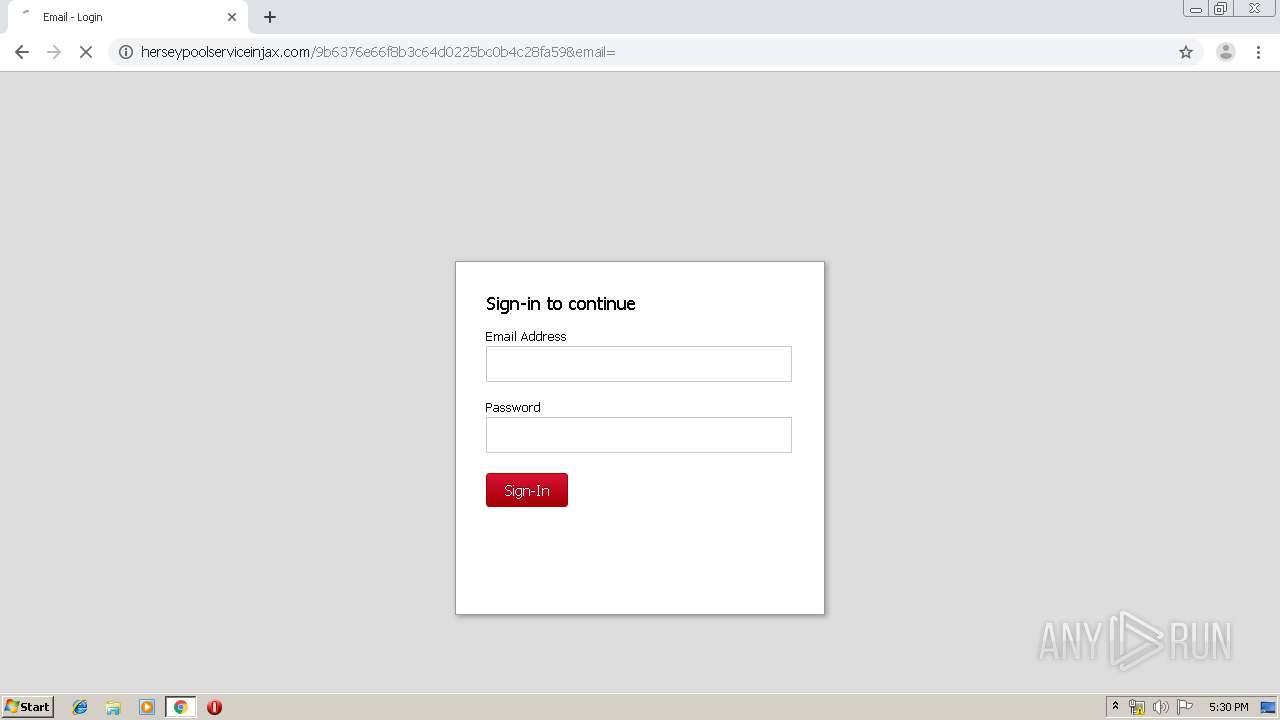
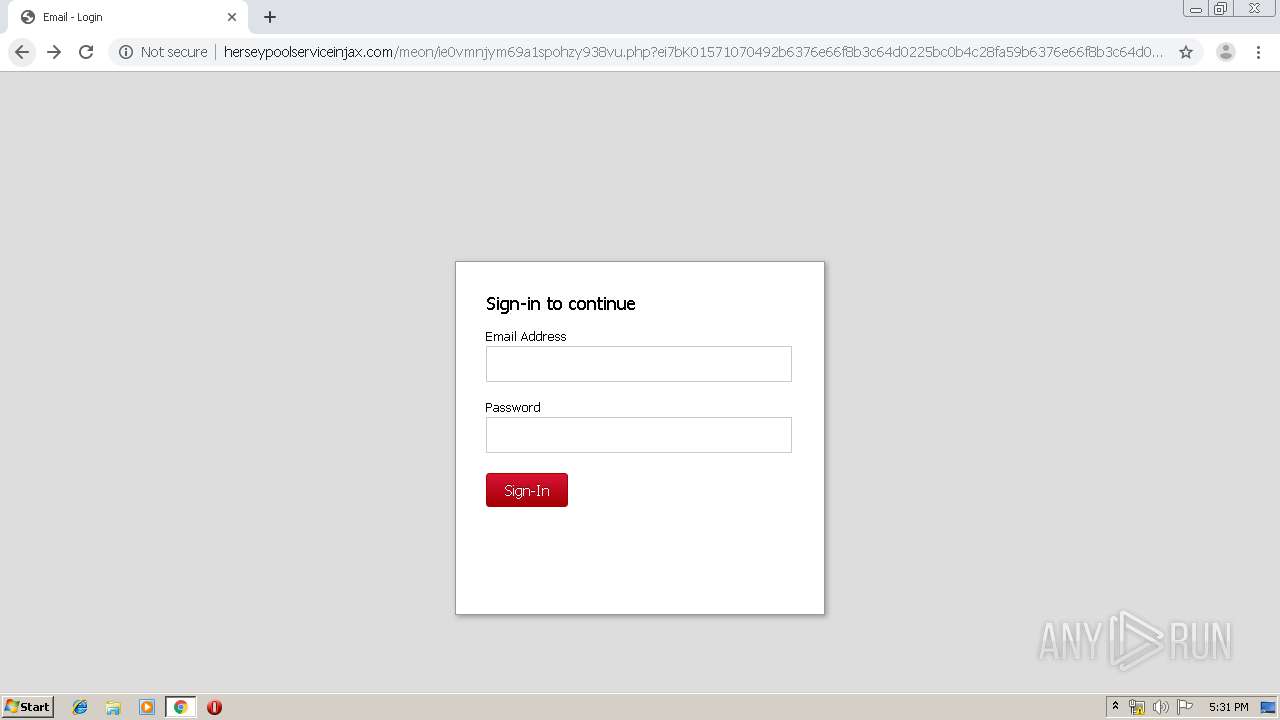
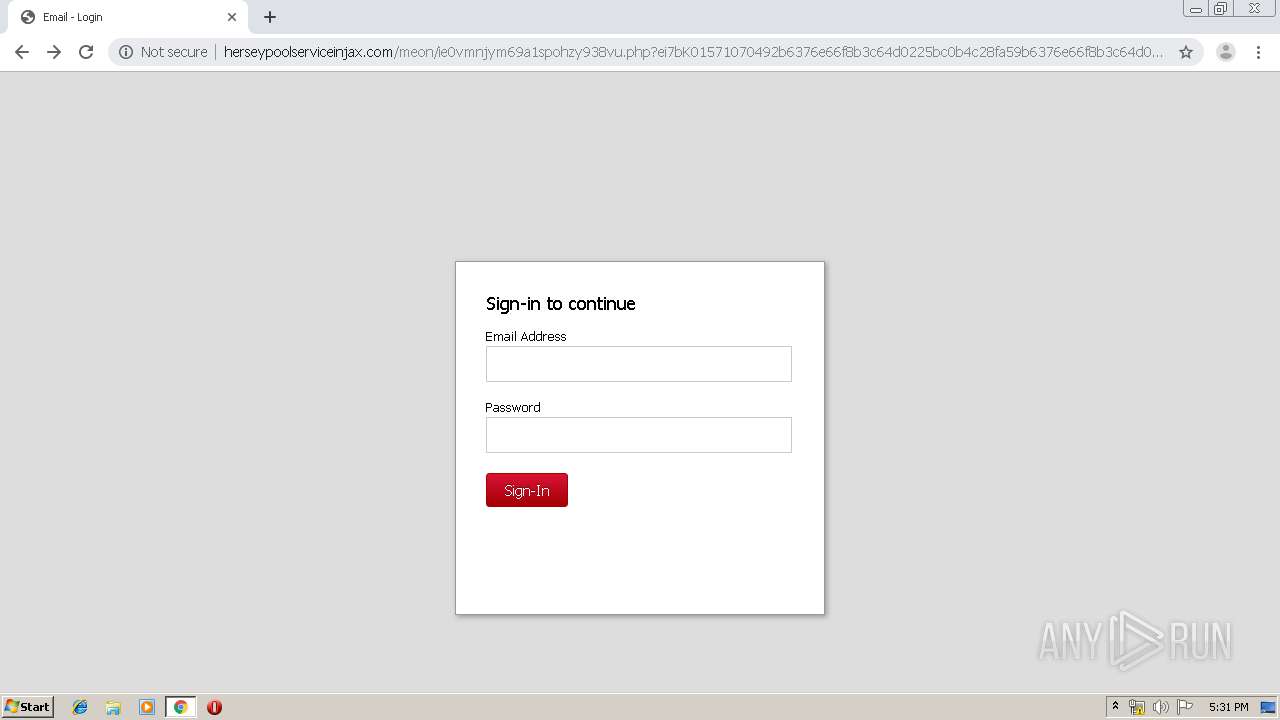
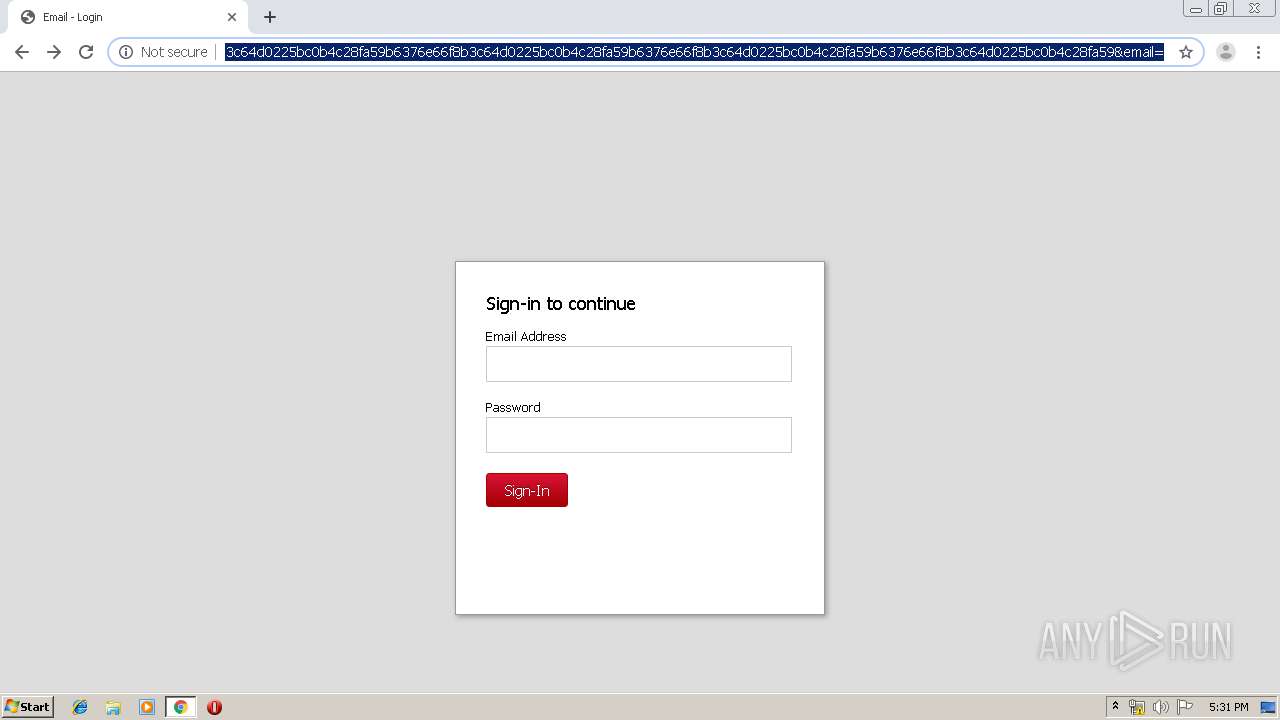
1596 | chrome.exe | POST | 302 | 72.52.229.85:80 | http://herseypoolserviceinjax.com/meon/login.php | US | — | — | suspicious |
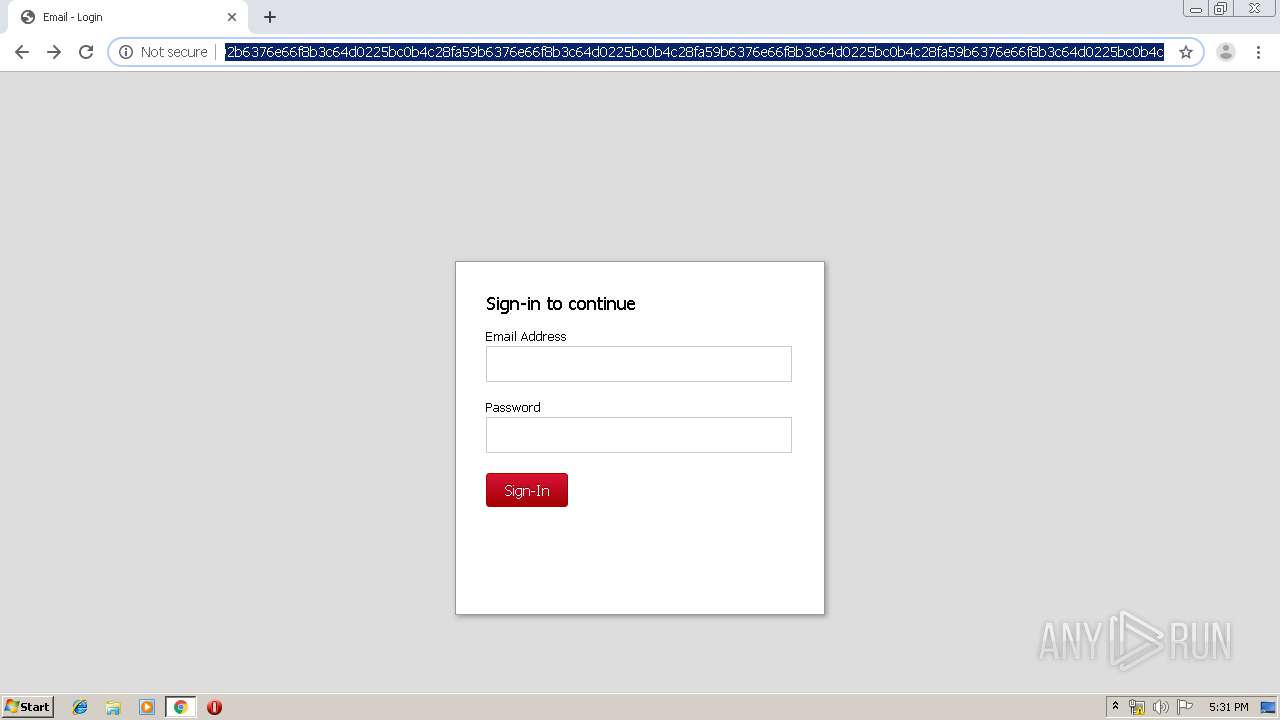
1596 | chrome.exe | GET | 200 | 72.52.229.85:80 | http://herseypoolserviceinjax.com/meon/ie0vmnjym69a1spohzy938vu.php?ei7bK01571070492b6376e66f8b3c64d0225bc0b4c28fa59b6376e66f8b3c64d0225bc0b4c28fa59b6376e66f8b3c64d0225bc0b4c28fa59b6376e66f8b3c64d0225bc0b4c28fa59b6376e66f8b3c64d0225bc0b4c28fa59&email= | US | html | 2.09 Kb | suspicious |
1596 | chrome.exe | GET | 301 | 72.52.229.85:80 | http://herseypoolserviceinjax.com/meon | US | html | 247 b | suspicious |
1596 | chrome.exe | GET | 200 | 72.52.229.85:80 | http://herseypoolserviceinjax.com/meon/loader.php?email=hereismyemail@emailz.biz&.rand=13InboxLight.aspx?n=1774256418&fid=4 | US | html | 1.71 Kb | suspicious |
1596 | chrome.exe | GET | — | 72.52.229.85:80 | http://herseypoolserviceinjax.com/meon/js/login.js?2230 | US | — | — | suspicious |
1596 | chrome.exe | GET | — | 72.52.229.85:80 | http://herseypoolserviceinjax.com/meon/favicon.ico | US | — | — | suspicious |
1596 | chrome.exe | GET | 200 | 72.52.229.85:80 | http://herseypoolserviceinjax.com/meon/l.php?email=hereismyemail@emailz.biz&.rand=13InboxLight.aspx?n=1774256418&fid=4 | US | html | 459 b | suspicious |
1596 | chrome.exe | GET | 200 | 72.52.229.85:80 | http://herseypoolserviceinjax.com/meon/success.php?rand=13InboxLightaspxn.1774256418&fid.4.1252899642&fid=1&fav.1&rand.13InboxLight.aspxn.1774256418&fid.1252899642&fid.1&fav.1&email=hereismyemail@emailz.biz&.rand=13InboxLight.aspx?n=1774256418&fid=4 | US | html | 1.17 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1596 | chrome.exe | 72.52.229.85:80 | herseypoolserviceinjax.com | Liquid Web, L.L.C | US | suspicious |
1596 | chrome.exe | 172.217.16.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
1596 | chrome.exe | 216.58.206.13:443 | accounts.google.com | Google Inc. | US | whitelisted |
1596 | chrome.exe | 172.217.18.10:80 | ajax.googleapis.com | Google Inc. | US | whitelisted |
1596 | chrome.exe | 172.217.18.164:443 | www.google.com | Google Inc. | US | whitelisted |
1596 | chrome.exe | 172.217.22.78:443 | clients1.google.com | Google Inc. | US | whitelisted |
1596 | chrome.exe | 172.217.18.174:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
1596 | chrome.exe | 172.217.18.163:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
1596 | chrome.exe | 173.194.138.200:80 | r3---sn-aigzrn7d.gvt1.com | Google Inc. | US | whitelisted |
1596 | chrome.exe | 216.58.208.33:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
herseypoolserviceinjax.com |
| suspicious |
accounts.google.com |
| shared |
ajax.googleapis.com |
| whitelisted |
www.google.com |
| malicious |
clients1.google.com |
| whitelisted |
clients2.google.com |
| whitelisted |
redirector.gvt1.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
r3---sn-aigzrn7d.gvt1.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1596 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY Http Client Body contains pass= in cleartext |
1596 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY Http Client Body contains pass= in cleartext |
1080 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .biz TLD |
8 ETPRO signatures available at the full report