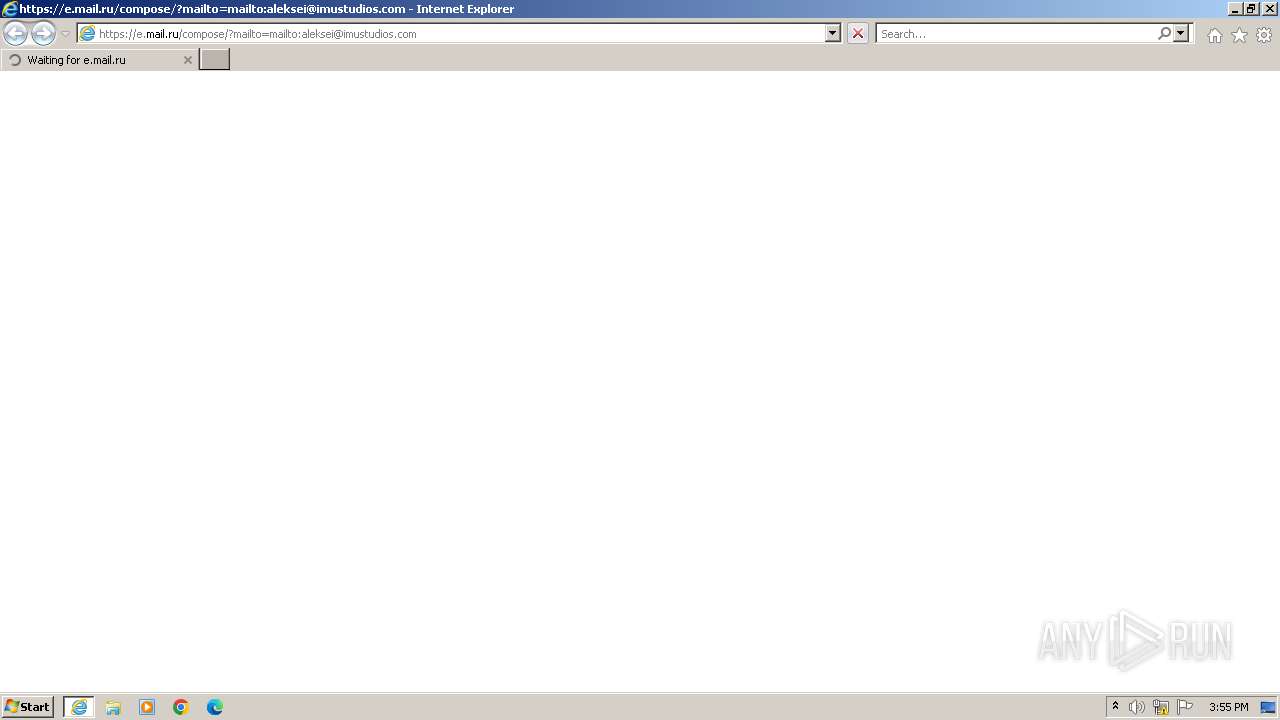
| URL: | https://e.mail.ru/compose/?mailto=mailto:aleksei@imustudios.com |
| Full analysis: | https://app.any.run/tasks/bc88d2db-9ac8-44c0-b150-3fc474096a29 |
| Verdict: | Malicious activity |
| Analysis date: | November 26, 2023, 15:54:57 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| SHA1: | 8D3AEB07F42FFCEA571C4180D7E7B7262649BBDB |
| SHA256: | CDDA9A06AE2856FDBC8836B3333F60EDCB090288AA0B31FED72E948EF2147887 |
| SSDEEP: | 3:N8SMo0WLlMWlJDRV4T:2/HVWlC |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- iexplore.exe (PID: 2876)
Reads the computer name
- wmpnscfg.exe (PID: 664)
Checks supported languages
- wmpnscfg.exe (PID: 664)
Manual execution by a user
- wmpnscfg.exe (PID: 664)
Reads the machine GUID from the registry
- wmpnscfg.exe (PID: 664)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
40
Monitored processes
3
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 664 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
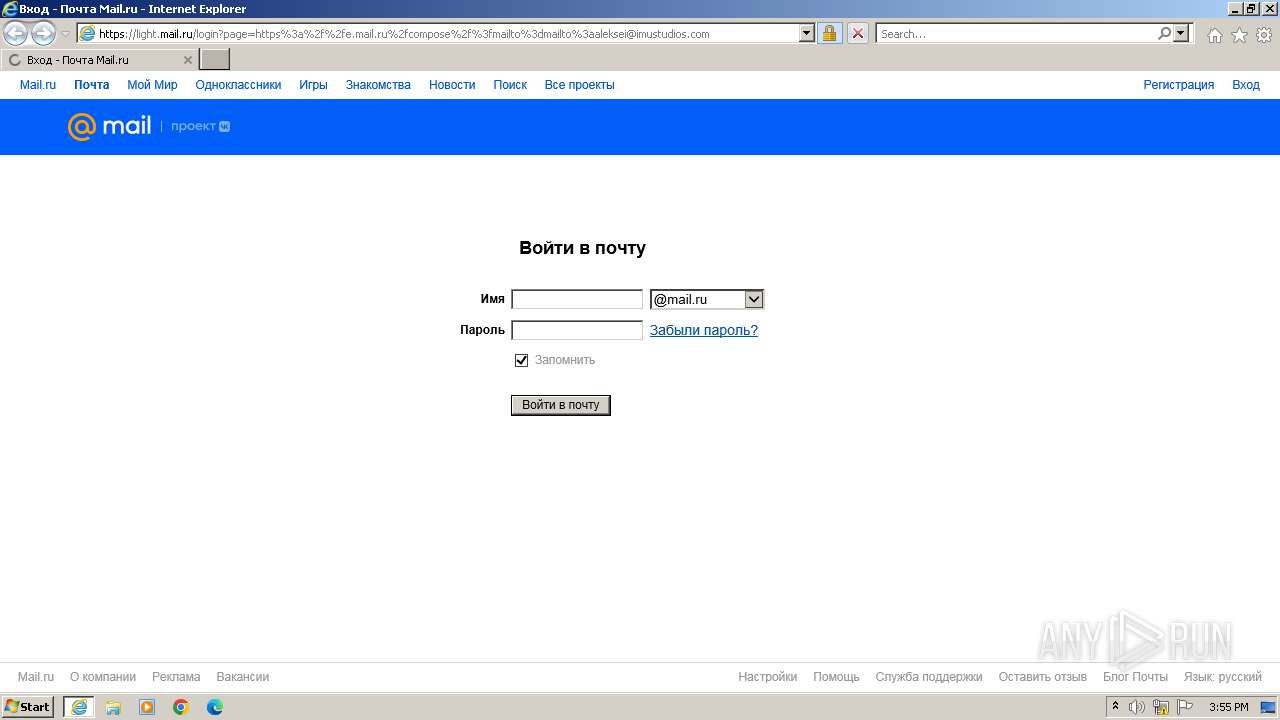
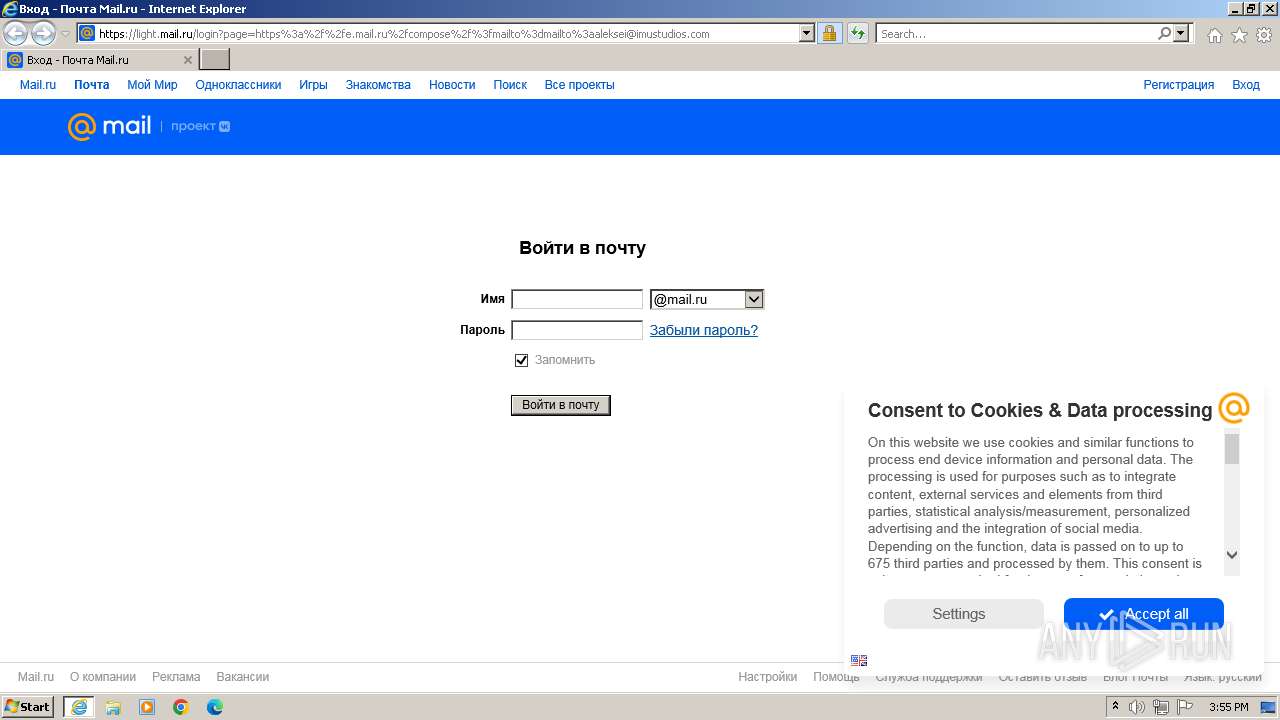
| 2876 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://e.mail.ru/compose/?mailto=mailto:aleksei@imustudios.com" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3376 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2876 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
18 004
Read events
17 917
Write events
82
Delete events
5
Modification events
| (PID) Process: | (2876) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (2876) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (2876) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (2876) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2876) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2876) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2876) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2876) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2876) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2876) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
0
Suspicious files
46
Text files
61
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3376 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:1BFE591A4FE3D91B03CDF26EAACD8F89 | SHA256:9CF94355051BF0F4A45724CA20D1CC02F76371B963AB7D1E38BD8997737B13D8 | |||
| 3376 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\DHUGUIJ6.txt | text | |
MD5:1FEBC6E4D2E8B61B9D3BB01C4BEC35AF | SHA256:170757303D97BCA9DAA9E175F2831102AAD70EDE93950E91AB1606D27759C091 | |||
| 3376 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\login[1].htm | html | |
MD5:8990584D449043E03EEBC9E0C09F4865 | SHA256:1FB545E633C40D437E4E6E2DBE121CB6D3BF4659E6FCCF9277E09CEBF097A61A | |||
| 3376 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\0DA515F703BB9B49479E8697ADB0B955_96EEC010953ED454BBCDFA69FC071E7C | binary | |
MD5:B2110FF441E787E0E13BEC4B354CA7C8 | SHA256:6D2DC77A7B7B6BE420A14BF309FCE2D7B61A5DAA0983F620199D09DF3A81DD16 | |||
| 3376 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:66592CEE9B63CFBA13BE1C99098F4A51 | SHA256:2FC4F42E5282A6B9F25B3A5579B8A4EF6BE1C5BEDB62C23B1D9FE418D5538B3E | |||
| 3376 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B039FEA45CB4CC4BBACFC013C7C55604_50D7940D5D3FEDD8634D83074C7A46A3 | binary | |
MD5:B20EA7EE4119DC560DAE6F1186809206 | SHA256:414FB66228997F7990E64D0FA19BEEED39CAD5DEAB1694A2BA63E055439804B4 | |||
| 3376 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\0DA515F703BB9B49479E8697ADB0B955_4136D3715888E22D65EBE484B233D81B | binary | |
MD5:DFD87C8FD6FF67FFD1BFD882E03A8DA2 | SHA256:E63514D3E4243A3A1D9D5EE15F9ED88383E8BCFDC897F34DB1702E036EBBEDAE | |||
| 3376 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\32EB332F23A238B0DC8C4A0D9C936056 | binary | |
MD5:F1EEA8225A0D781DD397134BFB0071FC | SHA256:8B797CBFD2119C94F6165BB5F96EA8A619CA328882CA28C637E57F0663CCD6BD | |||
| 3376 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\0DA515F703BB9B49479E8697ADB0B955_96EEC010953ED454BBCDFA69FC071E7C | binary | |
MD5:1B54E916764B515FC9C933473F89ECBE | SHA256:ED087FF53E484790B1726D2EE142B37FBB0D5B49C0F88A914CDB2B1BDAE13F28 | |||
| 3376 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\32EB332F23A238B0DC8C4A0D9C936056 | binary | |
MD5:C8D7A9060C812F7EC2278D5E56FE86D2 | SHA256:366A1A2B812C15D1E2DA7362F23594D12AB6DB7D50CD537522FFFEBBA1FF4E47 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
25
TCP/UDP connections
61
DNS requests
28
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3376 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?e925f9b3981bfc0f | unknown | compressed | 4.66 Kb | unknown |
3376 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?f2969c510caf3352 | unknown | compressed | 4.66 Kb | unknown |
3376 | iexplore.exe | GET | 200 | 151.101.66.133:80 | http://ocsp2.globalsign.com/rootr3/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBT1nGh%2FJBjWKnkPdZIzB1bqhelHBwQUj%2FBLf6guRSSuTVD6Y5qL3uLdG7wCDQHuXyId%2FGI71DM6hVc%3D | unknown | binary | 1.40 Kb | unknown |
3376 | iexplore.exe | GET | 200 | 151.101.130.133:80 | http://ocsp.globalsign.com/rootr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCDQHuXxad%2F5c1K2Rl1mo%3D | unknown | binary | 1.41 Kb | unknown |
3376 | iexplore.exe | GET | 200 | 151.101.130.133:80 | http://ocsp.globalsign.com/gsrsaovsslca2018/ME0wSzBJMEcwRTAJBgUrDgMCGgUABBRrcGT%2BanRD3C1tW3nsrKeuXC7DPwQU%2BO9%2F8s14Z6jeb48kjYjxhwMCs%2BsCDD%2F2jDCJa5FQkuK6Tw%3D%3D | unknown | binary | 1.40 Kb | unknown |
1080 | svchost.exe | GET | 304 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?8c278ce706dba7cc | unknown | — | — | unknown |
3376 | iexplore.exe | GET | 200 | 151.101.130.133:80 | http://ocsp.globalsign.com/rootr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEH1NQqkrQx1%2BZFPnwZqNWHc%3D | unknown | binary | 1.41 Kb | unknown |
3376 | iexplore.exe | GET | 200 | 151.101.66.133:80 | http://ocsp2.globalsign.com/rootr3/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBT1nGh%2FJBjWKnkPdZIzB1bqhelHBwQUj%2FBLf6guRSSuTVD6Y5qL3uLdG7wCDQHuXyI%2BPTVbmSvIKrQ%3D | unknown | binary | 1.40 Kb | unknown |
3376 | iexplore.exe | GET | 200 | 151.101.130.133:80 | http://ocsp.globalsign.com/gsrsaovsslca2018/ME0wSzBJMEcwRTAJBgUrDgMCGgUABBRrcGT%2BanRD3C1tW3nsrKeuXC7DPwQU%2BO9%2F8s14Z6jeb48kjYjxhwMCs%2BsCDFZ43noMCcDUxwQLHw%3D%3D | unknown | binary | 1.40 Kb | unknown |
3376 | iexplore.exe | GET | 200 | 151.101.130.133:80 | http://ocsp.globalsign.com/gsrsaovsslca2018/ME0wSzBJMEcwRTAJBgUrDgMCGgUABBRrcGT%2BanRD3C1tW3nsrKeuXC7DPwQU%2BO9%2F8s14Z6jeb48kjYjxhwMCs%2BsCDFwPfOXcb9eOnCF9aQ%3D%3D | unknown | binary | 1.40 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3376 | iexplore.exe | 217.69.139.216:443 | e.mail.ru | LLC VK | RU | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2588 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3376 | iexplore.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | EDGECAST | GB | whitelisted |
3376 | iexplore.exe | 151.101.130.133:80 | ocsp.globalsign.com | FASTLY | US | unknown |
3376 | iexplore.exe | 151.101.66.133:80 | ocsp.globalsign.com | FASTLY | US | unknown |
1080 | svchost.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | EDGECAST | GB | whitelisted |
3376 | iexplore.exe | 94.100.180.216:443 | e.mail.ru | LLC VK | RU | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
e.mail.ru |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.globalsign.com |
| whitelisted |
ocsp2.globalsign.com |
| whitelisted |
light.mail.ru |
| unknown |
imgs2.imgsmail.ru |
| unknown |
r.mradx.net |
| whitelisted |
img.imgsmail.ru |
| whitelisted |
rs.mail.ru |
| whitelisted |
www.tns-counter.ru |
| whitelisted |