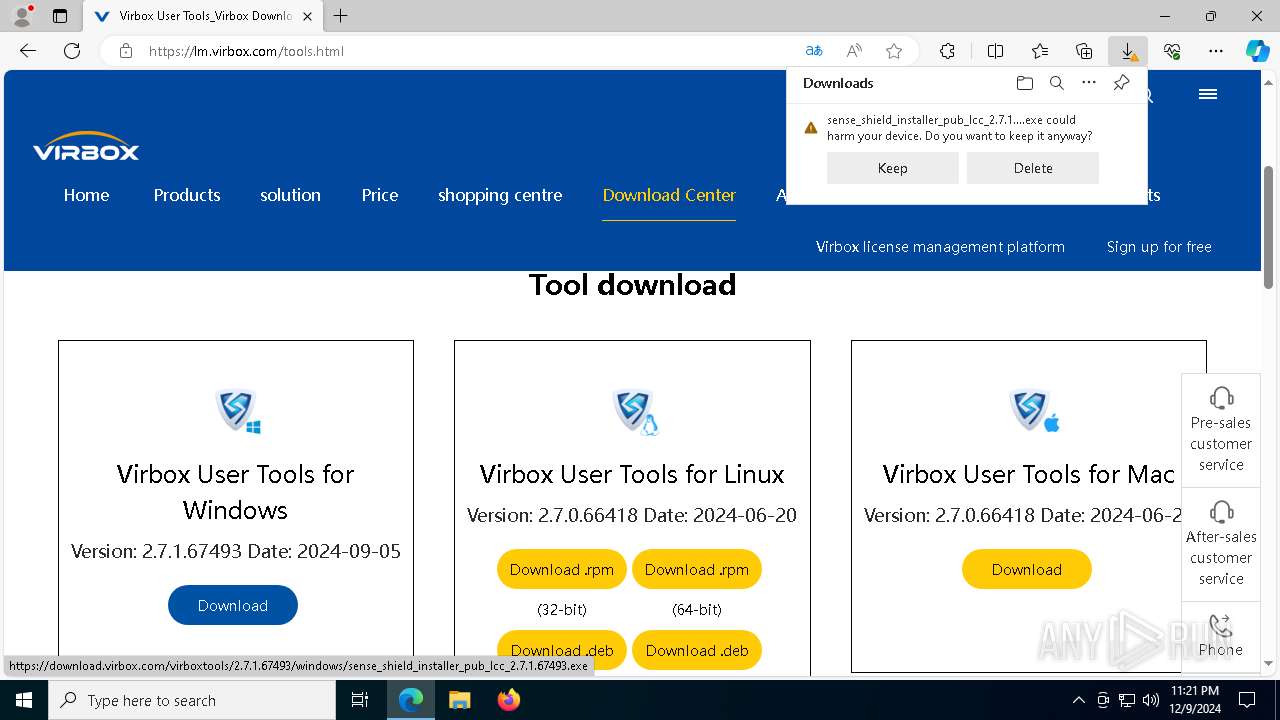
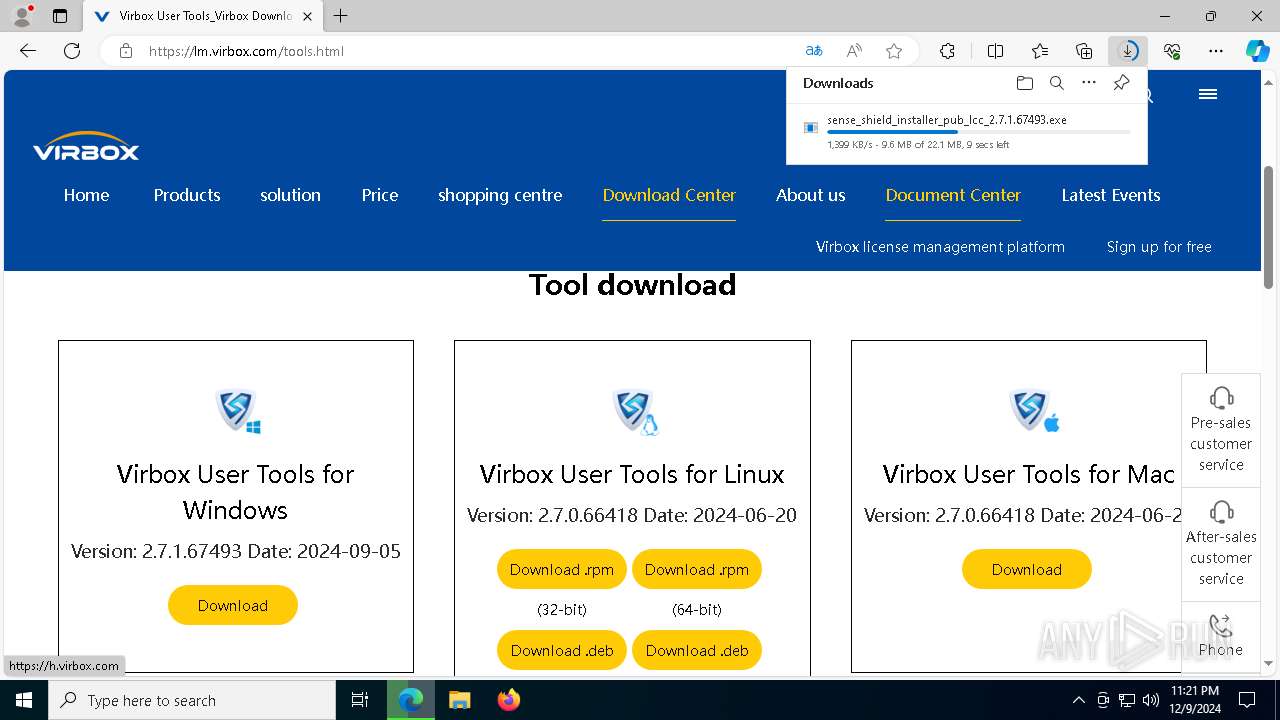
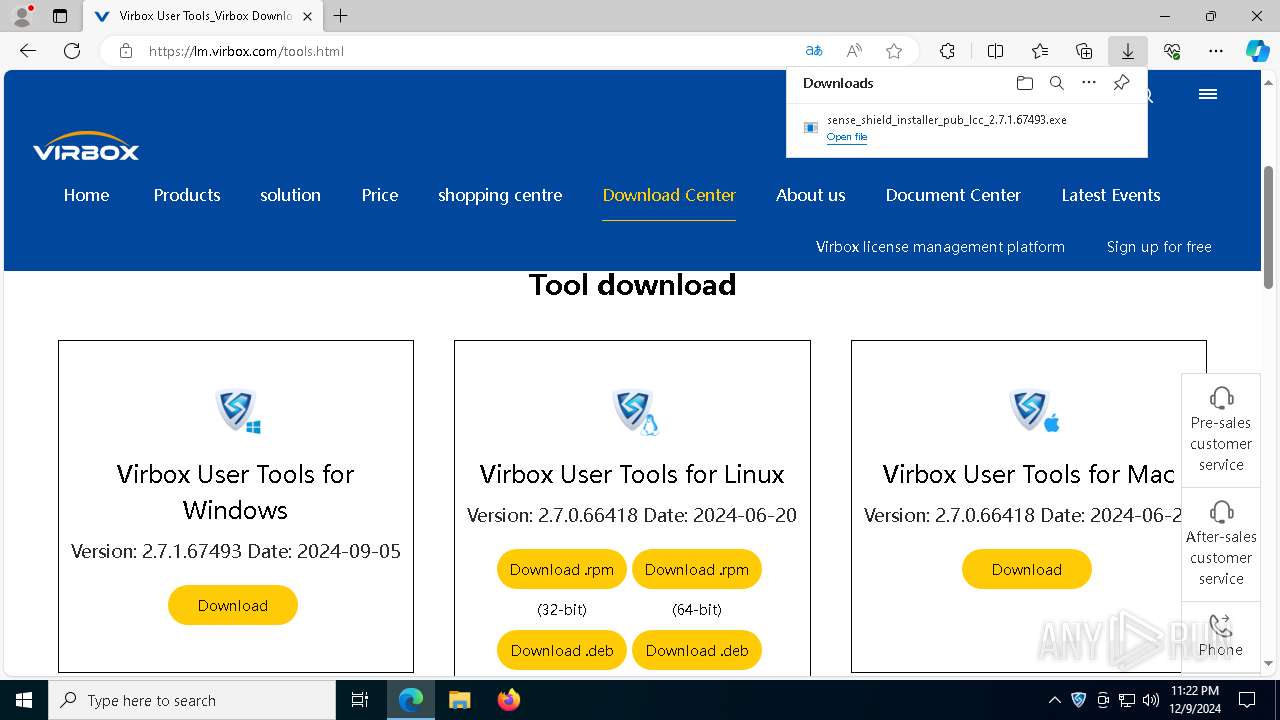
| URL: | https://lm.virbox.com/about/introduce.html |
| Full analysis: | https://app.any.run/tasks/abe06fba-6bcd-4699-b8ff-b9ae2e79b8a1 |
| Verdict: | Malicious activity |
| Analysis date: | December 09, 2024, 23:19:52 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | CD8028ED62DDB0799F4B7AC7996DA9F3 |
| SHA1: | 190F67AB5D6BB7DDC11CF63BC9A0E715A81638C1 |
| SHA256: | CDCD1E2909026844B91CFC1CF7501BCD5401CA79B5956080466B92E1F04D85CB |
| SSDEEP: | 3:N8ILTWDqxSIJ:2InWDqxN |
MALICIOUS
No malicious indicators.SUSPICIOUS
Malware-specific behavior (creating "System.dll" in Temp)
- sense_shield_installer_pub_lcc_2.7.1.67493.exe (PID: 3820)
Process drops legitimate windows executable
- sense_shield_installer_pub_lcc_2.7.1.67493.exe (PID: 3820)
Reads security settings of Internet Explorer
- sense_shield_installer_pub_lcc_2.7.1.67493.exe (PID: 3820)
Drops a system driver (possible attempt to evade defenses)
- sense_shield_installer_pub_lcc_2.7.1.67493.exe (PID: 3820)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 7076)
- cmd.exe (PID: 4724)
Starts CMD.EXE for commands execution
- sense_shield_installer_pub_lcc_2.7.1.67493.exe (PID: 3820)
Creates or modifies Windows services
- sense_shield_installer_pub_lcc_2.7.1.67493.exe (PID: 3820)
Uses SYSTEMINFO.EXE to read the environment
- cmd.exe (PID: 7076)
- cmd.exe (PID: 4724)
Connects to unusual port
- sssync.exe (PID: 5028)
The process drops C-runtime libraries
- sense_shield_installer_pub_lcc_2.7.1.67493.exe (PID: 3820)
Executable content was dropped or overwritten
- sense_shield_installer_pub_lcc_2.7.1.67493.exe (PID: 3820)
Uses NETSH.EXE to add a firewall rule or allowed programs
- sense_shield_installer_pub_lcc_2.7.1.67493.exe (PID: 3820)
INFO
Checks supported languages
- identity_helper.exe (PID: 6532)
- sense_shield_installer_pub_lcc_2.7.1.67493.exe (PID: 3820)
- DriverEnvVerify.exe (PID: 5728)
- ss_monitor.exe (PID: 2088)
- ssclient.exe (PID: 1144)
- sssync.exe (PID: 5028)
- ss_config_merge.exe (PID: 540)
- InstWiz3.exe (PID: 4128)
- setup.exe (PID: 1344)
- setup.exe (PID: 6980)
- setup.exe (PID: 5752)
Reads the computer name
- identity_helper.exe (PID: 6532)
- ssclient.exe (PID: 1144)
- sssync.exe (PID: 5028)
- DriverEnvVerify.exe (PID: 5728)
- sense_shield_installer_pub_lcc_2.7.1.67493.exe (PID: 3820)
Executable content was dropped or overwritten
- msedge.exe (PID: 6352)
- msedge.exe (PID: 6056)
Creates files in the program directory
- sense_shield_installer_pub_lcc_2.7.1.67493.exe (PID: 3820)
- sssync.exe (PID: 5028)
- ssclient.exe (PID: 1144)
- DriverEnvVerify.exe (PID: 5728)
The process uses the downloaded file
- sense_shield_installer_pub_lcc_2.7.1.67493.exe (PID: 3820)
Application launched itself
- msedge.exe (PID: 6056)
Create files in a temporary directory
- sense_shield_installer_pub_lcc_2.7.1.67493.exe (PID: 3820)
Sends debugging messages
- sense_shield_installer_pub_lcc_2.7.1.67493.exe (PID: 3820)
Reads Environment values
- identity_helper.exe (PID: 6532)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
210
Monitored processes
79
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 512 | systeminfo | C:\Windows\SysWOW64\systeminfo.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Displays system information Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 540 | "C:\Program Files (x86)\senseshield\ss\service\ss_config_merge.exe" "config_http2https" "C:\ProgramData\senseshield\ss_service\ss_config.xml" | C:\Program Files (x86)\senseshield\ss\service\ss_config_merge.exe | — | sense_shield_installer_pub_lcc_2.7.1.67493.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 4294967295 Modules
| |||||||||||||||
| 624 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6756 --field-trial-handle=2504,i,5227140707095775160,12180023746449123213,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 628 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6688 --field-trial-handle=2504,i,5227140707095775160,12180023746449123213,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 648 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5984 --field-trial-handle=2504,i,5227140707095775160,12180023746449123213,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1016 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | sssync.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
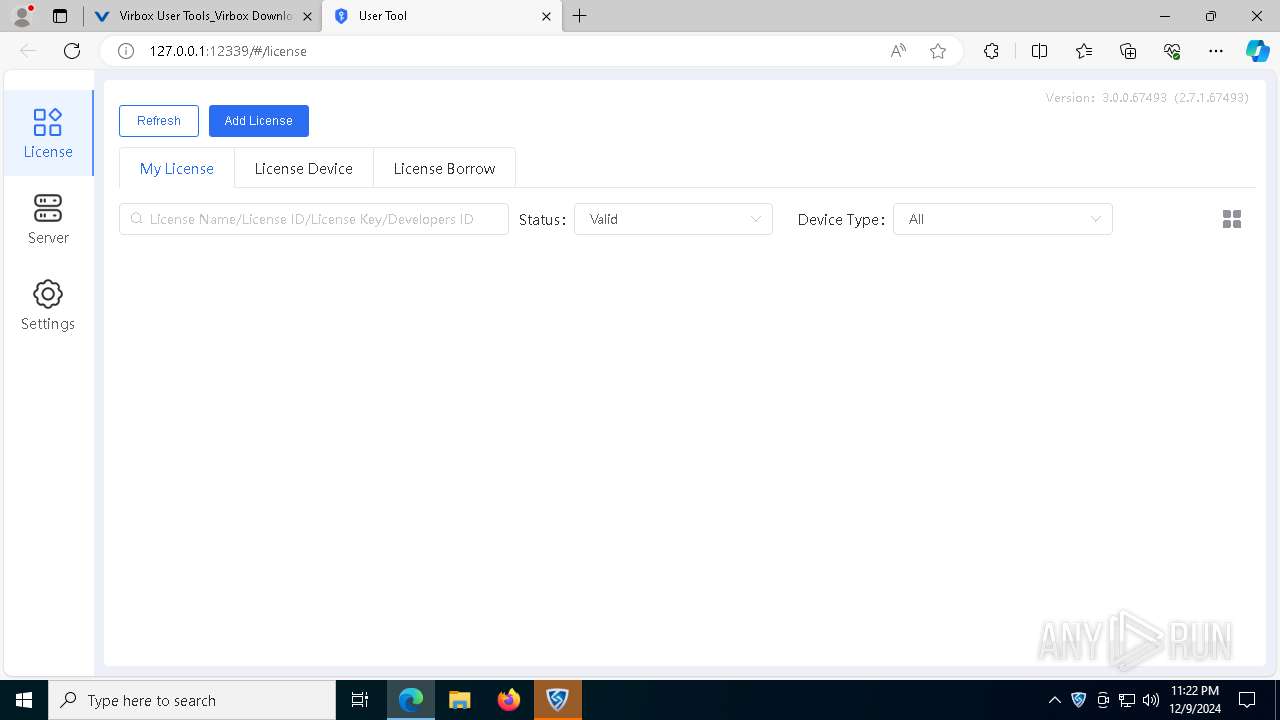
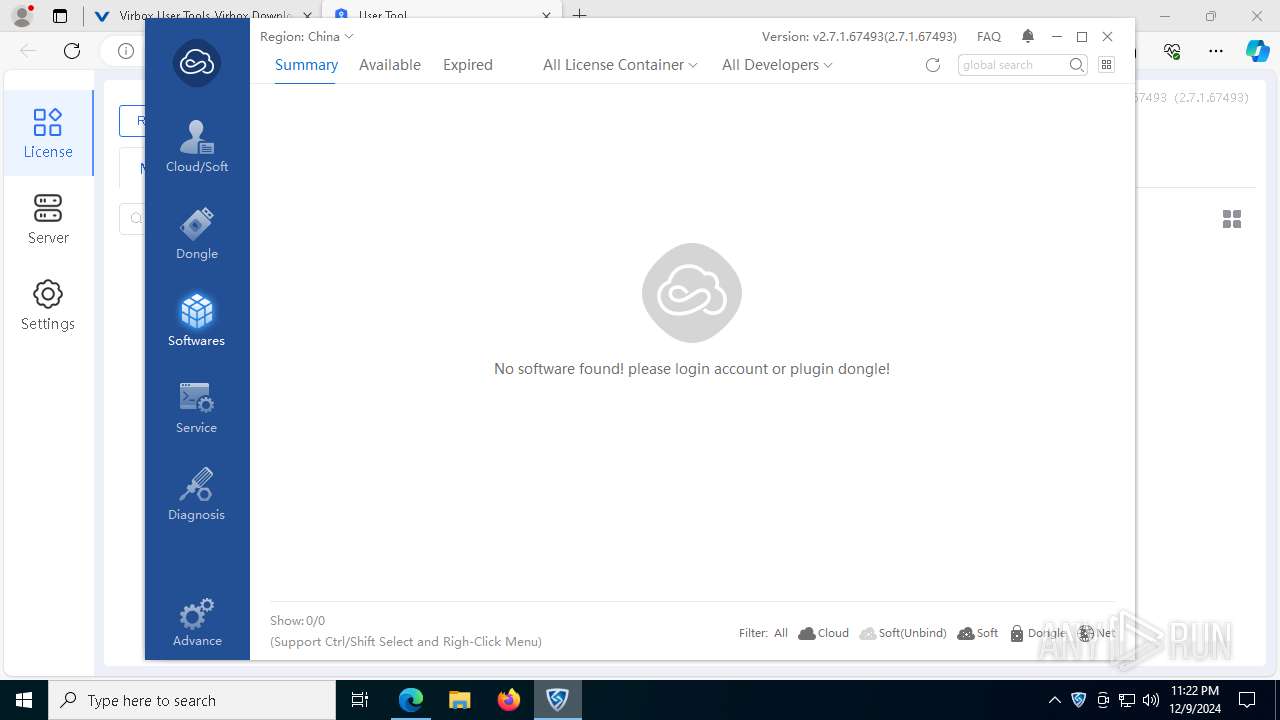
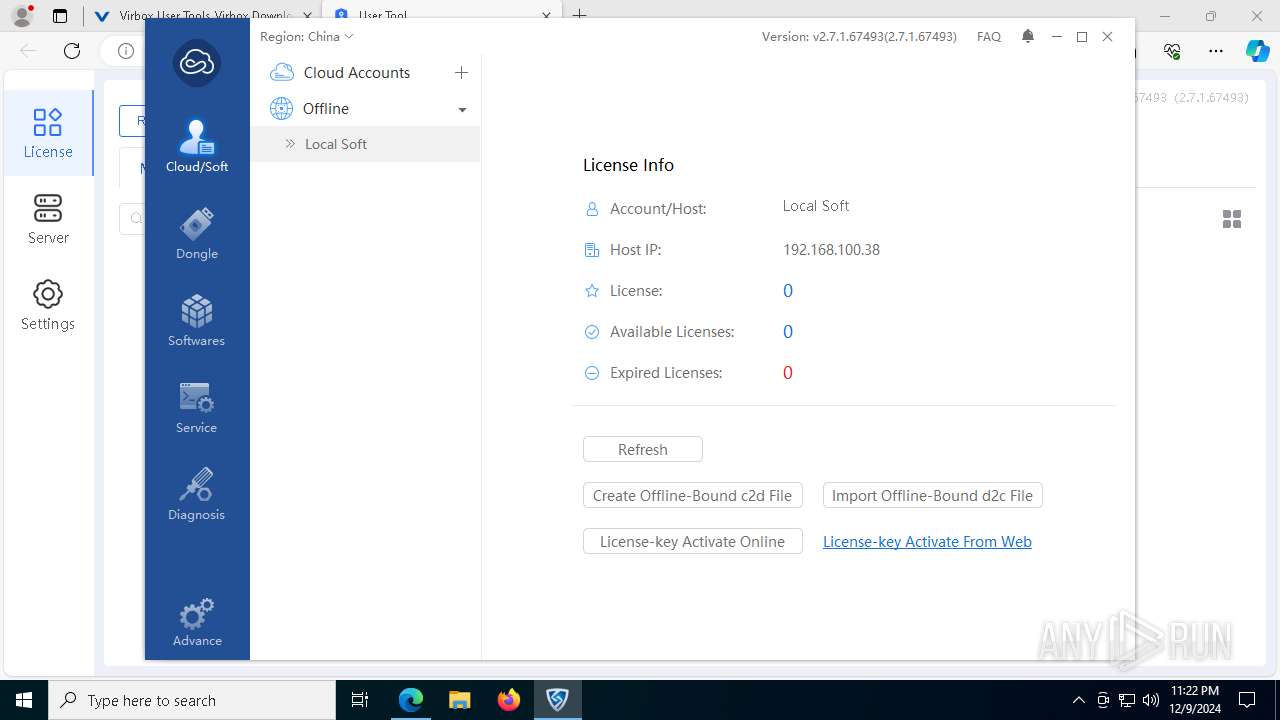
| 1144 | "C:\Program Files (x86)\senseshield\ss\tools\ssclient.exe" -hide | C:\Program Files (x86)\senseshield\ss\Tools\ssclient.exe | — | sense_shield_installer_pub_lcc_2.7.1.67493.exe | |||||||||||
User: admin Company: Beijing Senseshield Technology Co.,Ltd Integrity Level: HIGH Description: Virbox User Tool Modules
| |||||||||||||||
| 1344 | .\winlh64\setup -g "elite5.inf" | C:\Users\admin\AppData\Local\Temp\DriversTmp\user\Drivers\winlh64\setup.exe | — | sense_shield_installer_pub_lcc_2.7.1.67493.exe | |||||||||||
User: admin Integrity Level: HIGH Description: setuplh64 Application Exit code: 0 Version: 5.0.0.4 Modules
| |||||||||||||||
| 1512 | netsh advfirewall firewall add rule name="SenseShield Service" dir=out program="C:\Program Files (x86)\senseshield\ss\service\senseshield.exe" action=allow | C:\Windows\SysWOW64\netsh.exe | — | sense_shield_installer_pub_lcc_2.7.1.67493.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1988 | netsh advfirewall firewall add rule name="SenseShield Service" dir=in program="C:\Program Files (x86)\senseshield\ss\service\senseshield.exe" action=allow | C:\Windows\SysWOW64\netsh.exe | — | sense_shield_installer_pub_lcc_2.7.1.67493.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
16 886
Read events
16 828
Write events
57
Delete events
1
Modification events
| (PID) Process: | (6056) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6056) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6056) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6056) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6056) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: CF40D2E274872F00 | |||
| (PID) Process: | (6056) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 7D68DFE274872F00 | |||
| (PID) Process: | (6056) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328474 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {EF9F5881-F57D-4359-8CD3-6B417AC0A405} | |||
| (PID) Process: | (6056) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328474 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {9BE30AF3-DC42-4264-8AEF-8BF5CE96E5EC} | |||
| (PID) Process: | (6056) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328474 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {D815564E-9AA7-4C32-96CF-8497F08D9C6E} | |||
| (PID) Process: | (6056) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328474 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {631AEA36-6287-4F79-B967-A850C73AC1EA} | |||
Executable files
81
Suspicious files
423
Text files
138
Unknown types
13
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6056 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF135db3.TMP | — | |
MD5:— | SHA256:— | |||
| 6056 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6056 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF135dc3.TMP | — | |
MD5:— | SHA256:— | |||
| 6056 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF135dc3.TMP | — | |
MD5:— | SHA256:— | |||
| 6056 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6056 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6056 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF135e02.TMP | — | |
MD5:— | SHA256:— | |||
| 6056 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6056 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF135e11.TMP | — | |
MD5:— | SHA256:— | |||
| 6056 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
85
TCP/UDP connections
179
DNS requests
99
Threats
59
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 184.24.77.35:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5536 | svchost.exe | HEAD | 200 | 217.20.57.42:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1734256805&P2=404&P3=2&P4=V5LkQTAbpoytQt17QhSvzgYbse%2bXSoYbNWvkCIX1KB2iBhNKzWLEha3UmFcJ9PIvTMn28xAHFGb2oxcpZ5c5DQ%3d%3d | unknown | — | — | whitelisted |
1544 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
5536 | svchost.exe | GET | 206 | 217.20.57.42:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1734256805&P2=404&P3=2&P4=V5LkQTAbpoytQt17QhSvzgYbse%2bXSoYbNWvkCIX1KB2iBhNKzWLEha3UmFcJ9PIvTMn28xAHFGb2oxcpZ5c5DQ%3d%3d | unknown | — | — | whitelisted |
5536 | svchost.exe | GET | 206 | 217.20.57.42:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1734256805&P2=404&P3=2&P4=V5LkQTAbpoytQt17QhSvzgYbse%2bXSoYbNWvkCIX1KB2iBhNKzWLEha3UmFcJ9PIvTMn28xAHFGb2oxcpZ5c5DQ%3d%3d | unknown | — | — | whitelisted |
5536 | svchost.exe | GET | 206 | 217.20.57.42:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1734256805&P2=404&P3=2&P4=V5LkQTAbpoytQt17QhSvzgYbse%2bXSoYbNWvkCIX1KB2iBhNKzWLEha3UmFcJ9PIvTMn28xAHFGb2oxcpZ5c5DQ%3d%3d | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5536 | svchost.exe | GET | 206 | 217.20.57.42:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1734256805&P2=404&P3=2&P4=V5LkQTAbpoytQt17QhSvzgYbse%2bXSoYbNWvkCIX1KB2iBhNKzWLEha3UmFcJ9PIvTMn28xAHFGb2oxcpZ5c5DQ%3d%3d | unknown | — | — | whitelisted |
— | — | GET | 200 | 47.91.167.206:80 | http://47.91.167.206:80/ping.do | unknown | — | — | unknown |
5536 | svchost.exe | GET | 206 | 217.20.57.42:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1734256805&P2=404&P3=2&P4=V5LkQTAbpoytQt17QhSvzgYbse%2bXSoYbNWvkCIX1KB2iBhNKzWLEha3UmFcJ9PIvTMn28xAHFGb2oxcpZ5c5DQ%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5496 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5064 | SearchApp.exe | 2.16.204.161:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4712 | MoUsoCoreWorker.exe | 184.24.77.35:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 2.23.181.156:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
6352 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6056 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6352 | msedge.exe | 204.79.197.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6352 | msedge.exe | 13.107.246.45:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
lm.virbox.com |
| unknown |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6352 | msedge.exe | Misc activity | ET INFO DNS Query to Alibaba Cloud CDN Domain (aliyuncs .com) |
6352 | msedge.exe | Misc activity | ET INFO DNS Query to Alibaba Cloud CDN Domain (aliyuncs .com) |
6352 | msedge.exe | Misc activity | ET INFO Observed Alibaba Cloud CDN Domain (aliyuncs .com in TLS SNI) |
6352 | msedge.exe | Misc activity | ET INFO Observed Alibaba Cloud CDN Domain (aliyuncs .com in TLS SNI) |
6352 | msedge.exe | Misc activity | ET INFO DNS Query to Alibaba Cloud CDN Domain (aliyuncs .com) |
6352 | msedge.exe | Misc activity | ET INFO DNS Query to Alibaba Cloud CDN Domain (aliyuncs .com) |
6352 | msedge.exe | Misc activity | ET INFO Observed Alibaba Cloud CDN Domain (aliyuncs .com in TLS SNI) |
— | — | Misc activity | ET INFO DNS Query to Alibaba Cloud CDN Domain (aliyuncs .com) |
— | — | Misc activity | ET INFO DNS Query to Alibaba Cloud CDN Domain (aliyuncs .com) |
— | — | Misc activity | ET INFO Observed Alibaba Cloud CDN Domain (aliyuncs .com in TLS SNI) |
49 ETPRO signatures available at the full report
Process | Message |
|---|---|
sense_shield_installer_pub_lcc_2.7.1.67493.exe | _CallParameterCheck INST[1]=12
|
sense_shield_installer_pub_lcc_2.7.1.67493.exe | _CallParameterCheck INST[6]=32
|
sense_shield_installer_pub_lcc_2.7.1.67493.exe | _CallParameterCheck INST[3]=Monday
|
sense_shield_installer_pub_lcc_2.7.1.67493.exe | _CallParameterCheck INST[12]=0
|
sense_shield_installer_pub_lcc_2.7.1.67493.exe | _CallParameterCheck INST[9]=
|
sense_shield_installer_pub_lcc_2.7.1.67493.exe | _CallParameterCheck INST[10]=X64
|
sense_shield_installer_pub_lcc_2.7.1.67493.exe | _CallParameterCheck INST[7]=
|
sense_shield_installer_pub_lcc_2.7.1.67493.exe | _CallParameterCheck INST[11]=X64
|
sense_shield_installer_pub_lcc_2.7.1.67493.exe | _CallParameterCheck INST[0]=09
|
sense_shield_installer_pub_lcc_2.7.1.67493.exe | _CallParameterCheck INST[8]=
|