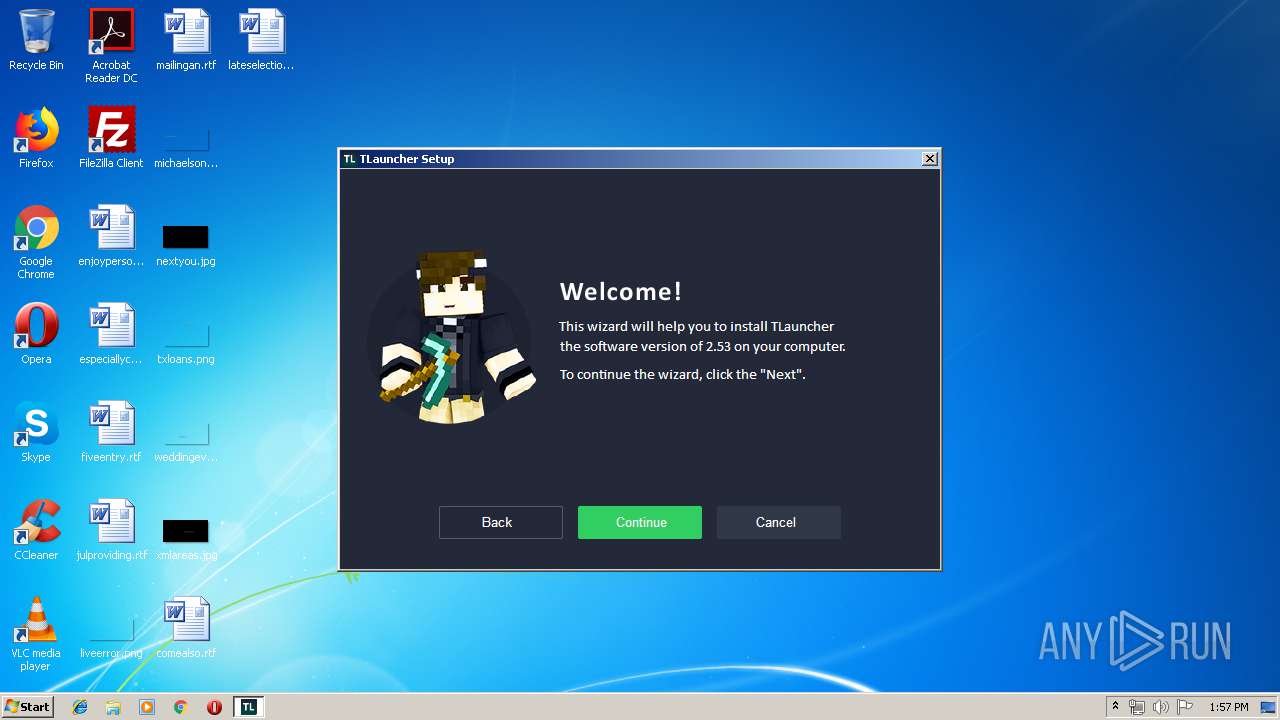
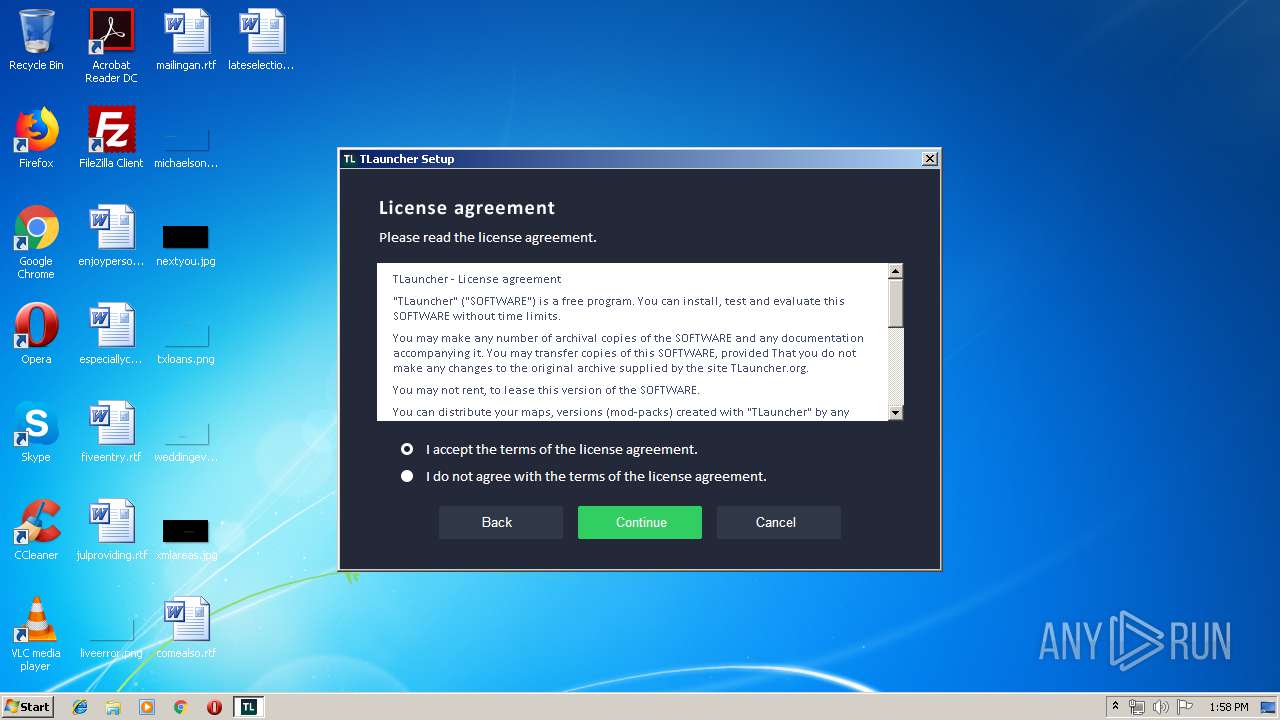
| File name: | minecraft-installer-0.5-ns.exe |
| Full analysis: | https://app.any.run/tasks/6b1f5d8a-559b-4da2-9e4a-f12182aaa43b |
| Verdict: | Malicious activity |
| Analysis date: | April 12, 2019, 12:57:32 |
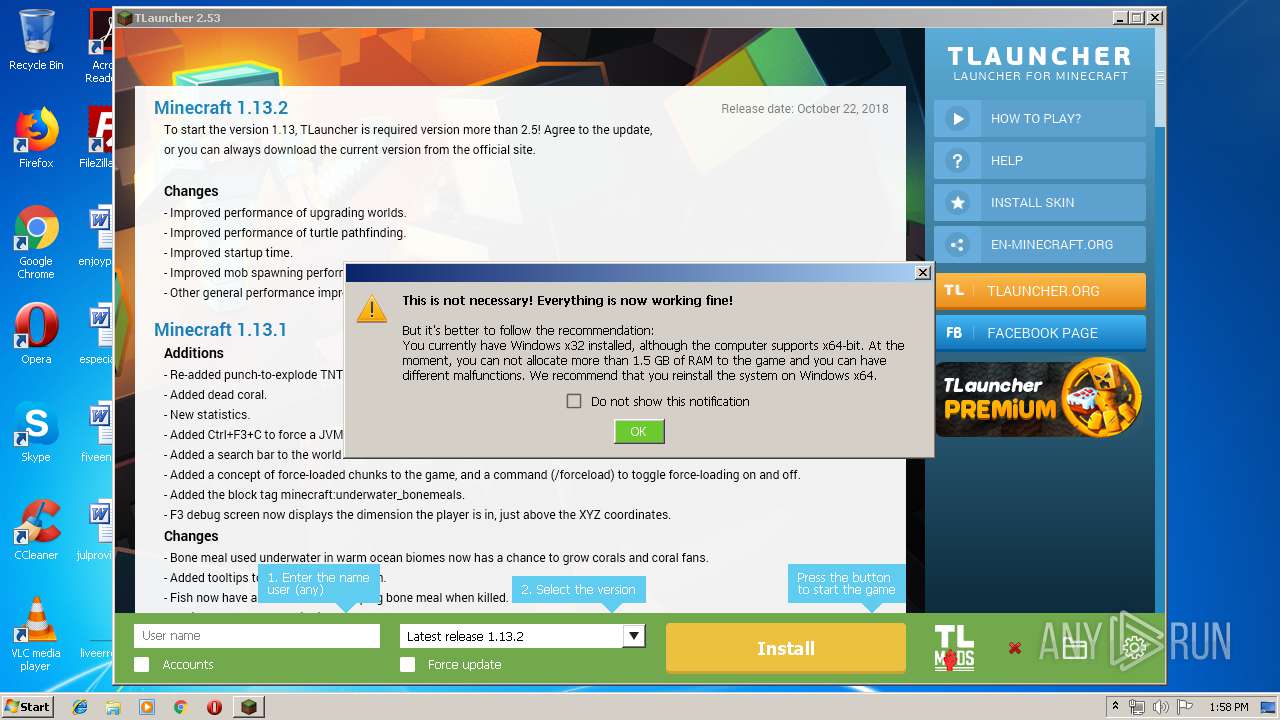
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 60646B9E51F333E56420932A8088FA47 |
| SHA1: | 0AA497230B3CC8E2327148E6A14B57B721FDCE8A |
| SHA256: | CDC241BEBC31FABA94C5AF81328E275C3CAC35AB8ED5CFA3591EED21099037B9 |
| SSDEEP: | 393216:hVjSHOf9fsD441ffz4e4oQL1fIiJbSmWIzAtdB7l+SMN3f/lk/l:LFF+1Hz4e4tgiJ+mlzuB7lpO3f/G/l |
MALICIOUS
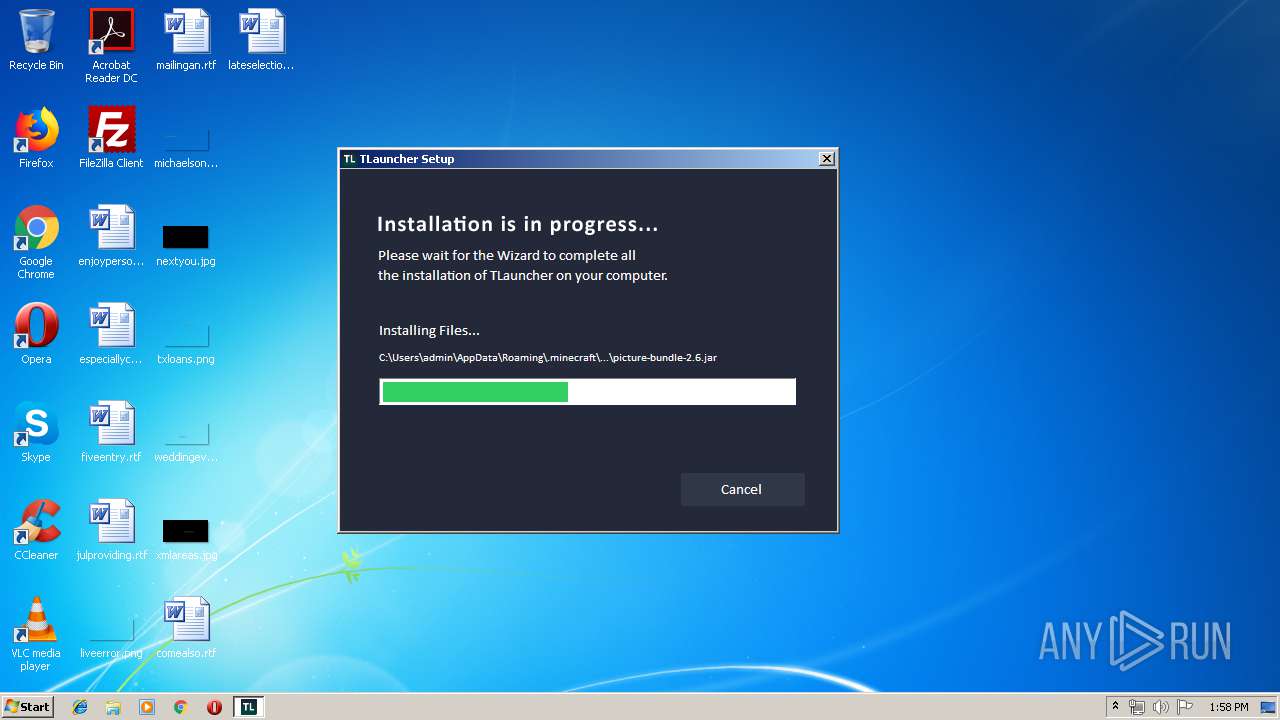
Loads dropped or rewritten executable
- irsetup.exe (PID: 2584)
Application was dropped or rewritten from another process
- irsetup.exe (PID: 2584)
- TLauncher.exe (PID: 2204)
SUSPICIOUS
Creates files in the user directory
- javaw.exe (PID: 2568)
- javaw.exe (PID: 116)
- irsetup.exe (PID: 2584)
Reads internet explorer settings
- irsetup.exe (PID: 2584)
Uses SYSTEMINFO.EXE to read environment
- cmd.exe (PID: 3904)
Executes JAVA applets
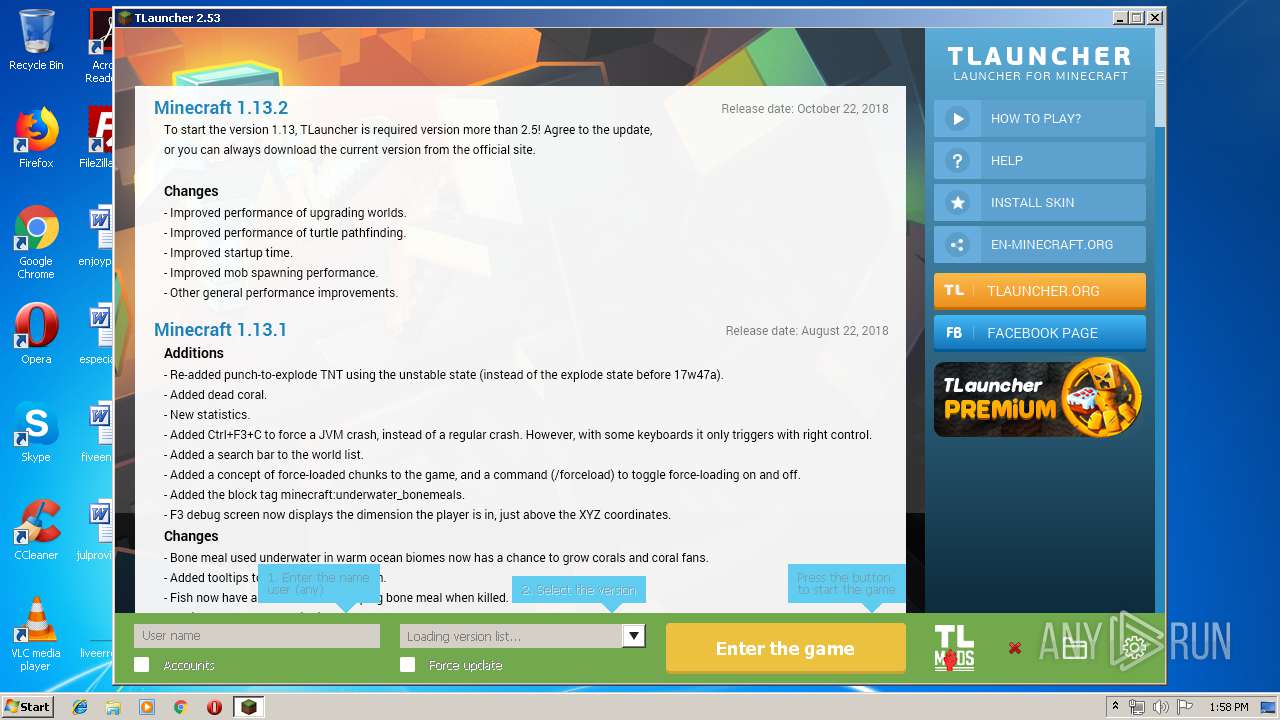
- TLauncher.exe (PID: 2204)
- javaw.exe (PID: 2568)
Executable content was dropped or overwritten
- minecraft-installer-0.5-ns.exe (PID: 1372)
- irsetup.exe (PID: 2584)
Starts CMD.EXE for commands execution
- javaw.exe (PID: 116)
Application launched itself
- javaw.exe (PID: 2568)
Starts application with an unusual extension
- cmd.exe (PID: 3904)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.8) |
|---|---|---|
| .exe | | | Win32 EXE Yoda's Crypter (36.4) |
| .dll | | | Win32 Dynamic Link Library (generic) (9) |
| .exe | | | Win32 Executable (generic) (6.1) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2015:02:09 22:57:00+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 22528 |
| InitializedDataSize: | 142336 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x29e1 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.5.0.0 |
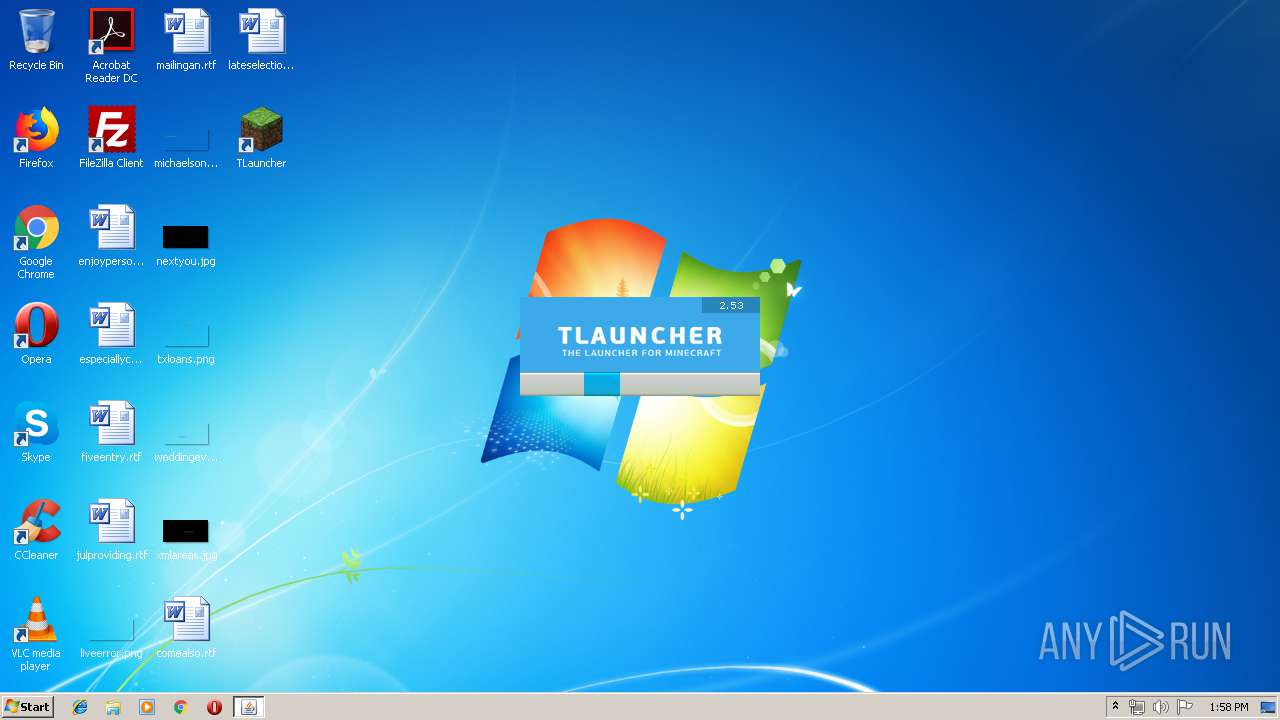
| ProductVersionNumber: | 2.53.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | ASCII |
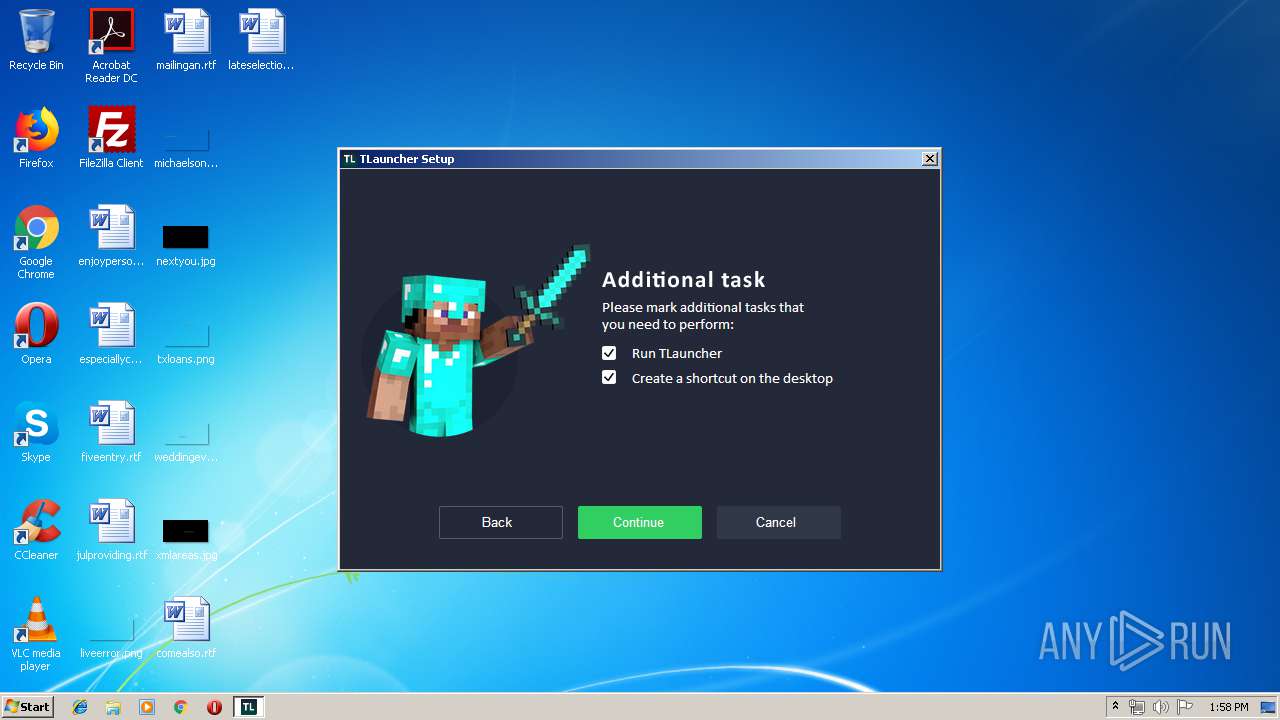
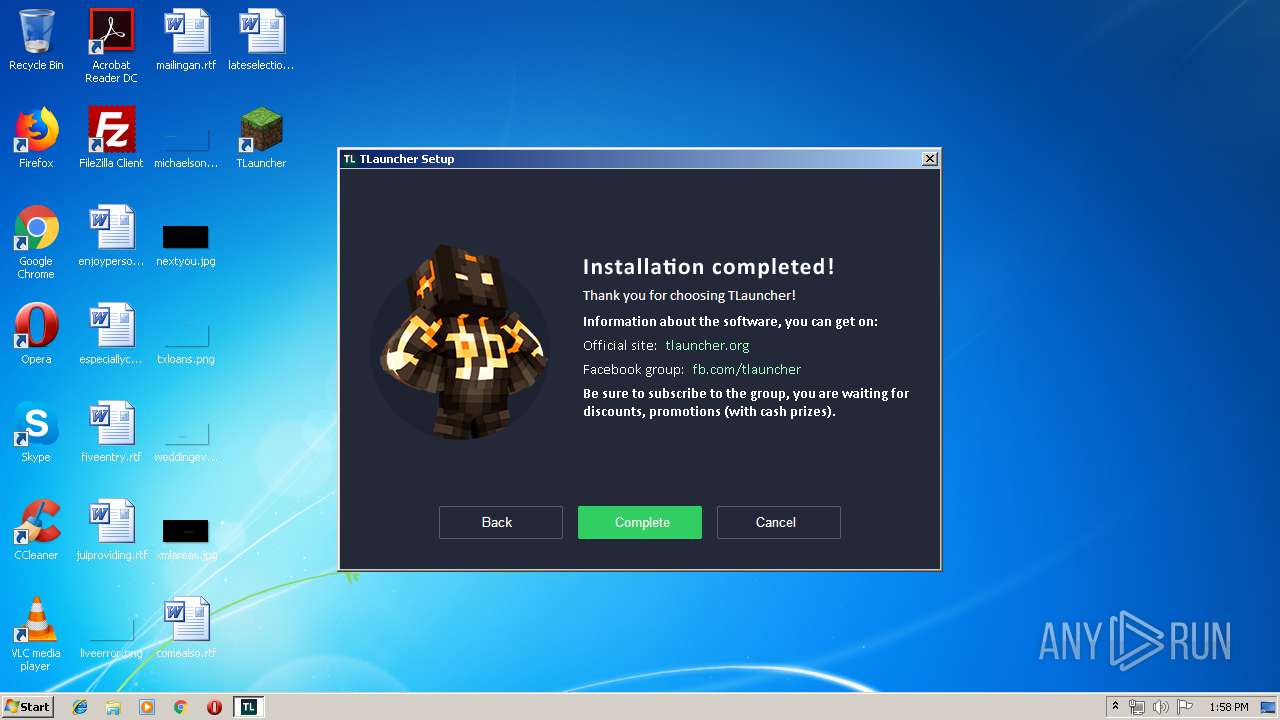
| Comments: | TLauncher Setup |
| CompanyName: | TLauncher Inc. |
| FileDescription: | TLauncher Setup |
| FileVersion: | 0.5.0.0 |
| InternalName: | TLauncher |
| LegalCopyright: | TLauncher Copyright © 2019 |
| LegalTrademarks: | TLauncher |
| OriginalFileName: | suf_launch.exe |
| ProductName: | TLauncher |
| ProductVersion: | 2.53.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 09-Feb-2015 21:57:00 |
| Detected languages: |
|
| Comments: | TLauncher Setup |
| CompanyName: | TLauncher Inc. |
| FileDescription: | TLauncher Setup |
| FileVersion: | 0.5.0.0 |
| InternalName: | TLauncher |
| LegalCopyright: | TLauncher Copyright © 2019 |
| LegalTrademarks: | TLauncher |
| OriginalFilename: | suf_launch.exe |
| ProductName: | TLauncher |
| ProductVersion: | 2.53.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 09-Feb-2015 21:57:00 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00005718 | 0x00005800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.45945 |
.rdata | 0x00007000 | 0x00002E82 | 0x00003000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.97533 |
.data | 0x0000A000 | 0x00001968 | 0x00000C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.58663 |
.rsrc | 0x0000C000 | 0x0001DDCC | 0x0001DE00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.50306 |
.reloc | 0x0002A000 | 0x00001092 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 3.7122 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.37661 | 1413 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 4.87454 | 67624 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 5.04321 | 16936 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 5.10433 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 5.15069 | 6760 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 5.24063 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
7 | 5.45174 | 2440 | Latin 1 / Western European | English - United States | RT_ICON |
8 | 5.39733 | 1720 | Latin 1 / Western European | English - United States | RT_ICON |
9 | 5.52276 | 1128 | Latin 1 / Western European | English - United States | RT_ICON |
101 | 2.9892 | 132 | Latin 1 / Western European | English - United States | RT_GROUP_ICON |
Imports
ADVAPI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
Total processes
43
Monitored processes
8
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 116 | "C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe" -Xmx384m -cp C:\Users\admin\AppData\Roaming\.minecraft\TLauncher.exe;C:\Users\admin\AppData\Roaming\.minecraft\tlauncher_libraries\com\google\inject\guice\4.1.0\guice-4.1.0.jar;C:\Users\admin\AppData\Roaming\.minecraft\tlauncher_libraries\com\google\inject\extentions\guice-assistedinject\4.1.0\guice-assistedinject-4.1.0.jar;C:\Users\admin\AppData\Roaming\.minecraft\tlauncher_libraries\javax\inject\javax.inject\1\javax.inject-1.jar;C:\Users\admin\AppData\Roaming\.minecraft\tlauncher_libraries\aopalliance\aopalliance\1.0\aopalliance-1.0.jar;C:\Users\admin\AppData\Roaming\.minecraft\tlauncher_libraries\com\google\guava\guava\19.0\guava-19.0.jar;C:\Users\admin\AppData\Roaming\.minecraft\tlauncher_libraries\org\apache\commons\commons-lang3\3.4\commons-lang3-3.4.jar;C:\Users\admin\AppData\Roaming\.minecraft\tlauncher_libraries\net\sf\jopt-simple\jopt-simple\4.9\jopt-simple-4.9.jar;C:\Users\admin\AppData\Roaming\.minecraft\tlauncher_libraries\log4j\log4j\1.2.17\log4j-1.2.17.jar;C:\Users\admin\AppData\Roaming\.minecraft\tlauncher_libraries\org\tukaani\xz\1.5\xz-1.5.jar;C:\Users\admin\AppData\Roaming\.minecraft\tlauncher_libraries\org\tlauncher\picture-bundle\2.6\picture-bundle-2.6.jar;C:\Users\admin\AppData\Roaming\.minecraft\tlauncher_libraries\org\tlauncher\skin-server-API\1.0\skin-server-API-1.0.jar;C:\Users\admin\AppData\Roaming\.minecraft\tlauncher_libraries\org\tlauncher\tlauncher-resource\1.4\tlauncher-resource-1.4.jar;C:\Users\admin\AppData\Roaming\.minecraft\tlauncher_libraries\com\github\junrar\junrar\0.7\junrar-0.7.jar;C:\Users\admin\AppData\Roaming\.minecraft\tlauncher_libraries\dnsjava\dnsjava\2.1.8\dnsjava-2.1.8.jar; org.tlauncher.tlauncher.rmo.TLauncher | C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe | javaw.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.920.14 Modules
| |||||||||||||||
| 1372 | "C:\Users\admin\AppData\Local\Temp\minecraft-installer-0.5-ns.exe" | C:\Users\admin\AppData\Local\Temp\minecraft-installer-0.5-ns.exe | explorer.exe | ||||||||||||
User: admin Company: TLauncher Inc. Integrity Level: MEDIUM Description: TLauncher Setup Exit code: 0 Version: 0.5.0.0 Modules
| |||||||||||||||
| 2204 | "C:\Users\admin\AppData\Roaming\.minecraft\TLauncher.exe" | C:\Users\admin\AppData\Roaming\.minecraft\TLauncher.exe | — | irsetup.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2568 | "C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe" -jar "C:\Users\admin\AppData\Roaming\.minecraft\TLauncher.exe" | C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe | — | TLauncher.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.920.14 Modules
| |||||||||||||||
| 2584 | "C:\Users\admin\AppData\Local\Temp\_ir_sf_temp_0\irsetup.exe" __IRAOFF:1884418 "__IRAFN:C:\Users\admin\AppData\Local\Temp\minecraft-installer-0.5-ns.exe" "__IRCT:1" "__IRTSS:0" "__IRSID:S-1-5-21-1302019708-1500728564-335382590-1000" | C:\Users\admin\AppData\Local\Temp\_ir_sf_temp_0\irsetup.exe | minecraft-installer-0.5-ns.exe | ||||||||||||
User: admin Company: Indigo Rose Corporation Integrity Level: MEDIUM Description: Setup Application Exit code: 0 Version: 9.5.0.0 Modules
| |||||||||||||||
| 3236 | systeminfo | C:\Windows\system32\systeminfo.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Displays system information Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3512 | chcp 437 | C:\Windows\system32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Change CodePage Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3904 | cmd.exe /C chcp 437 & systeminfo | C:\Windows\system32\cmd.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
1 207
Read events
1 189
Write events
18
Delete events
0
Modification events
| (PID) Process: | (1372) minecraft-installer-0.5-ns.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1372) minecraft-installer-0.5-ns.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2584) irsetup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2584) irsetup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (116) javaw.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: javaw.exe | |||
| (PID) Process: | (116) javaw.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3236) systeminfo.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3236) systeminfo.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\mlang.dll,-4386 |
Value: English (United States) | |||
Executable files
11
Suspicious files
8
Text files
47
Unknown types
12
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2584 | irsetup.exe | C:\Users\admin\AppData\Local\Temp\_ir_sf_temp_0\irsetup.dat | — | |
MD5:— | SHA256:— | |||
| 2584 | irsetup.exe | C:\Users\admin\AppData\Local\Temp\_ir_sf_temp_0\IRIMG4.PNG | image | |
MD5:B1DFDD85B72F53B816F8C90CECA50E3A | SHA256:7ED85E4ED5DC2B9C483352C8D11ABAE7986F95DE10227F08B38C447900913F45 | |||
| 2584 | irsetup.exe | C:\Users\admin\AppData\Local\Temp\_ir_sf_temp_0\IRIMG11.PNG | image | |
MD5:2EF3A0FA4D938CB9A2199EC63266D68F | SHA256:5D4E4944EEC91586EE8CA9581EE4812DA55EDB1C29211BC300782B7898B69C10 | |||
| 2584 | irsetup.exe | C:\Users\admin\AppData\Local\Temp\_ir_sf_temp_0\IRIMG5.PNG | image | |
MD5:37B63FD071F3842A72F6BBFDE1FA874F | SHA256:6AED00BA74EAA9E34B02C7FB5A72F66373B9AF0B81EED9CCDDAC2041AA38DC16 | |||
| 2584 | irsetup.exe | C:\Users\admin\AppData\Local\Temp\_ir_sf_temp_0\IRIMG7.PNG | image | |
MD5:EF83A9F2495D30212161BB240D507009 | SHA256:DC82D1221F1E54EDF3EEDD3F4F3951DC0BC89F4A1F28A4FC48726E41365739BE | |||
| 2584 | irsetup.exe | C:\Users\admin\AppData\Local\Temp\_ir_sf_temp_0\IRIMG3.PNG | image | |
MD5:681683E1791FC0266A147D3CB4F0B3D0 | SHA256:0786A8A620C6C5A8635581FA0D288C8F09B71995E751B9BB5BAA1AB5038460F0 | |||
| 2584 | irsetup.exe | C:\Users\admin\AppData\Local\Temp\_ir_sf_temp_0\IRIMG2.PNG | image | |
MD5:614FF28917089ED1801DC0B04EFB351B | SHA256:620CBF8EEC41DD22DECF03E724B62330AE5EFF314C5B2CFCC59AACEB9AECE3A3 | |||
| 2584 | irsetup.exe | C:\Users\admin\AppData\Local\Temp\_ir_sf_temp_0\IRIMG8.PNG | image | |
MD5:12B063B6191EFC007B1D17A85FC9D381 | SHA256:2AB3B7AEF2FDB563240D860237EF3CBA30BC81691DDBE04E1C77159EE56A3DA1 | |||
| 2584 | irsetup.exe | C:\Users\admin\AppData\Local\Temp\_ir_sf_temp_0\IRIMG13.PNG | image | |
MD5:01369F4200196DB7582A02F3E5C703CA | SHA256:58B5F9ECF64C8BE786335AD202C272496F5649D9CFD9DCABE457E481206E10D1 | |||
| 2584 | irsetup.exe | C:\Users\admin\AppData\Local\Temp\_ir_sf_temp_0\IRIMG14.PNG | image | |
MD5:F6743A15F600072331FF40A1797157B3 | SHA256:AC1F502BE7EAC20283C4BA4C6FF23E7E1E3146FC8BA7D3E3CA0AA3B5FE7DBF5B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
23
TCP/UDP connections
16
DNS requests
6
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
116 | javaw.exe | HEAD | 200 | 104.20.28.43:80 | http://repo.tlauncher.org/ | US | — | — | whitelisted |
116 | javaw.exe | HEAD | — | 104.20.28.43:80 | http://page.tlauncher.org/ | US | — | — | malicious |
116 | javaw.exe | GET | 200 | 104.20.28.43:80 | http://repo.tlauncher.org/update/downloads/configs/inner_servers.json | US | text | 2.16 Kb | whitelisted |
116 | javaw.exe | GET | 200 | 104.20.28.43:80 | http://repo.tlauncher.org/update/lch/update_2.0.json?version=2.53&client=aa7a4922-a6c2-4c51-97e7-cc5505cfe188 | US | text | 10.0 Kb | whitelisted |
116 | javaw.exe | GET | 200 | 104.20.29.43:80 | http://img.tlauncher.org/update/downloads/configs/client/images/tl-en-pe-news.png | US | image | 135 Kb | malicious |
116 | javaw.exe | GET | 200 | 104.20.29.43:80 | http://img.tlauncher.org/update/downloads/configs/client/images/icons/btn1.png | US | image | 206 b | malicious |
116 | javaw.exe | GET | 200 | 104.20.28.43:80 | http://repo.tlauncher.org/update/downloads/versions/new3/additional_assets.json | US | text | 182 Kb | whitelisted |
116 | javaw.exe | GET | 200 | 104.20.29.43:80 | http://img.tlauncher.org/update/downloads/configs/client/images/icons/btn2.png | US | image | 258 b | malicious |
116 | javaw.exe | GET | 200 | 104.20.29.43:80 | http://img.tlauncher.org/update/downloads/configs/client/style_new_bes_fontov.css | US | text | 6.21 Kb | malicious |
116 | javaw.exe | GET | 200 | 104.20.28.43:80 | http://repo.tlauncher.org/update/downloads/configs/client/eng.html | US | html | 10.6 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
116 | javaw.exe | 104.20.28.43:80 | page.tlauncher.org | Cloudflare Inc | US | shared |
116 | javaw.exe | 104.20.29.43:80 | page.tlauncher.org | Cloudflare Inc | US | shared |
116 | javaw.exe | 104.24.30.45:80 | ru-m.org | Cloudflare Inc | US | shared |
116 | javaw.exe | 104.20.28.43:443 | page.tlauncher.org | Cloudflare Inc | US | shared |
116 | javaw.exe | 54.192.92.122:443 | launchermeta.mojang.com | Amazon.com, Inc. | US | unknown |
116 | javaw.exe | 5.9.74.187:46150 | — | Hetzner Online GmbH | DE | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
page.tlauncher.org |
| malicious |
repo.tlauncher.org |
| whitelisted |
img.tlauncher.org |
| malicious |
launchermeta.mojang.com |
| whitelisted |
tlauncher.org |
| malicious |
ru-m.org |
| suspicious |