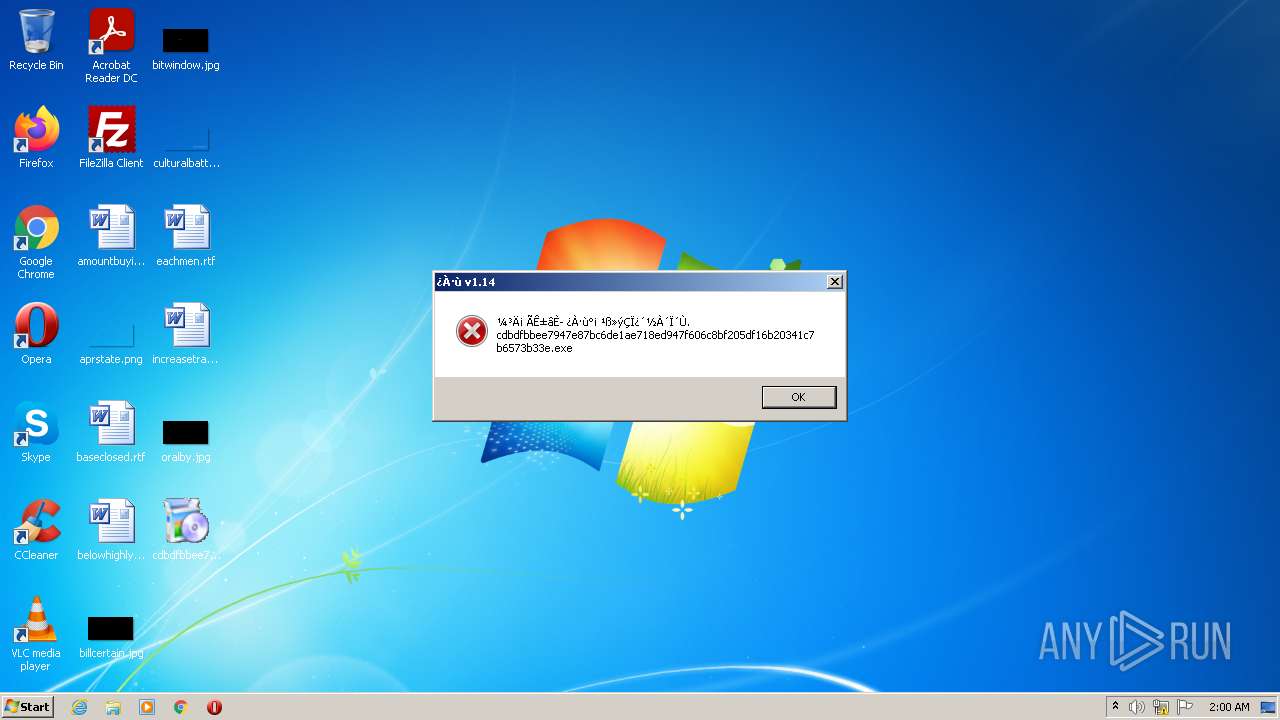
| File name: | cdbdfbbee7947e87bc6de1ae718ed947f606c8bf205df16b20341c7b6573b33e |
| Full analysis: | https://app.any.run/tasks/26d82130-5061-428a-8167-566c0078e448 |
| Verdict: | Malicious activity |
| Analysis date: | January 25, 2022, 01:59:35 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | 0485794F8C527BF33DF46D24A3F62B57 |
| SHA1: | 7A2A853695096CA4E8875C604C48A7E64EDDDDBB |
| SHA256: | CDBDFBBEE7947E87BC6DE1AE718ED947F606C8BF205DF16B20341C7B6573B33E |
| SSDEEP: | 3072:0C07Wd+hGSxRcb1u2IShYi40uy9WgxjKCxTJeEByK5TPdCiygD/Cg:Psxxi4KPLxXGEBj5dRy2X |
MALICIOUS
Changes settings of System certificates
- cdbdfbbee7947e87bc6de1ae718ed947f606c8bf205df16b20341c7b6573b33e.exe (PID: 1252)
SUSPICIOUS
Checks supported languages
- cdbdfbbee7947e87bc6de1ae718ed947f606c8bf205df16b20341c7b6573b33e.exe (PID: 1252)
Reads the computer name
- cdbdfbbee7947e87bc6de1ae718ed947f606c8bf205df16b20341c7b6573b33e.exe (PID: 1252)
Adds / modifies Windows certificates
- cdbdfbbee7947e87bc6de1ae718ed947f606c8bf205df16b20341c7b6573b33e.exe (PID: 1252)
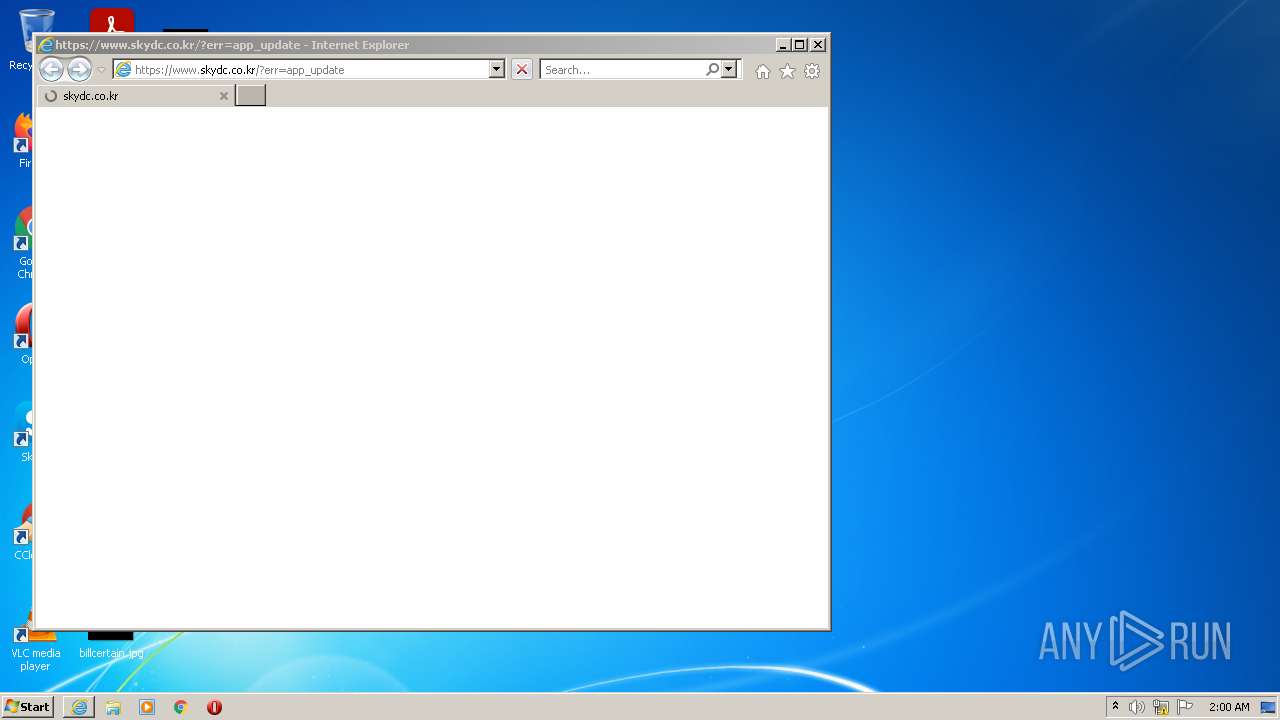
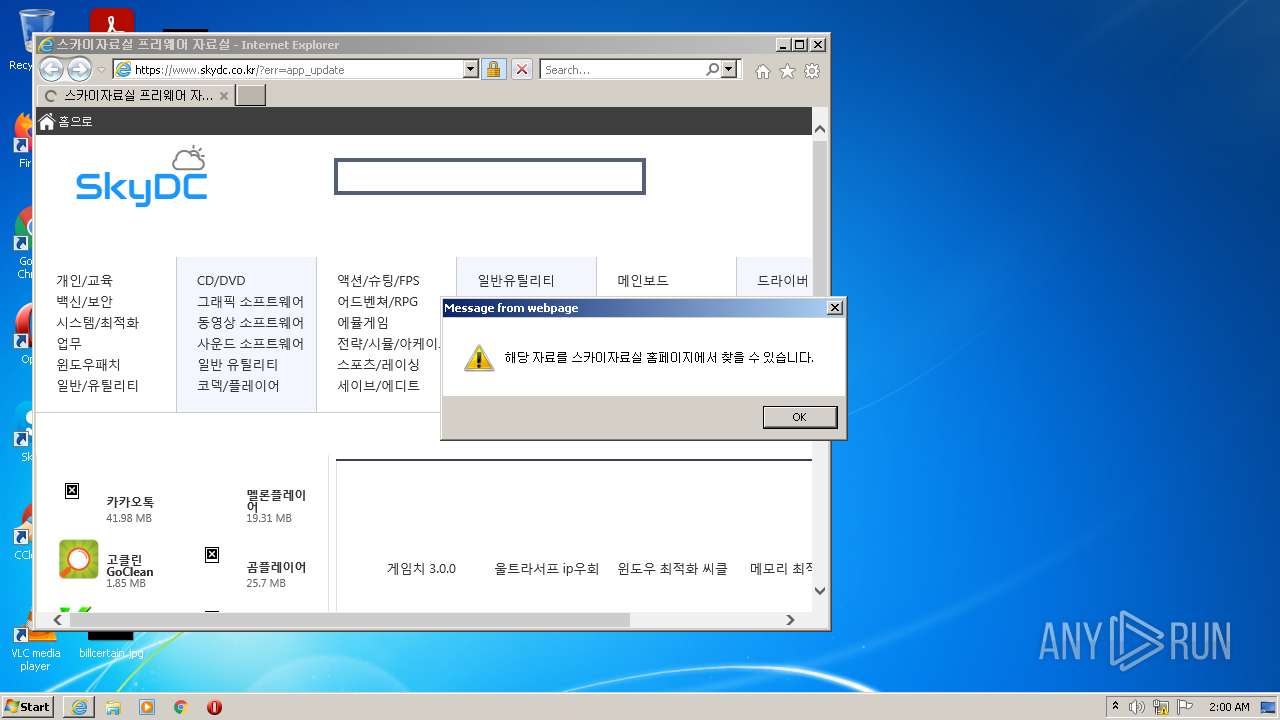
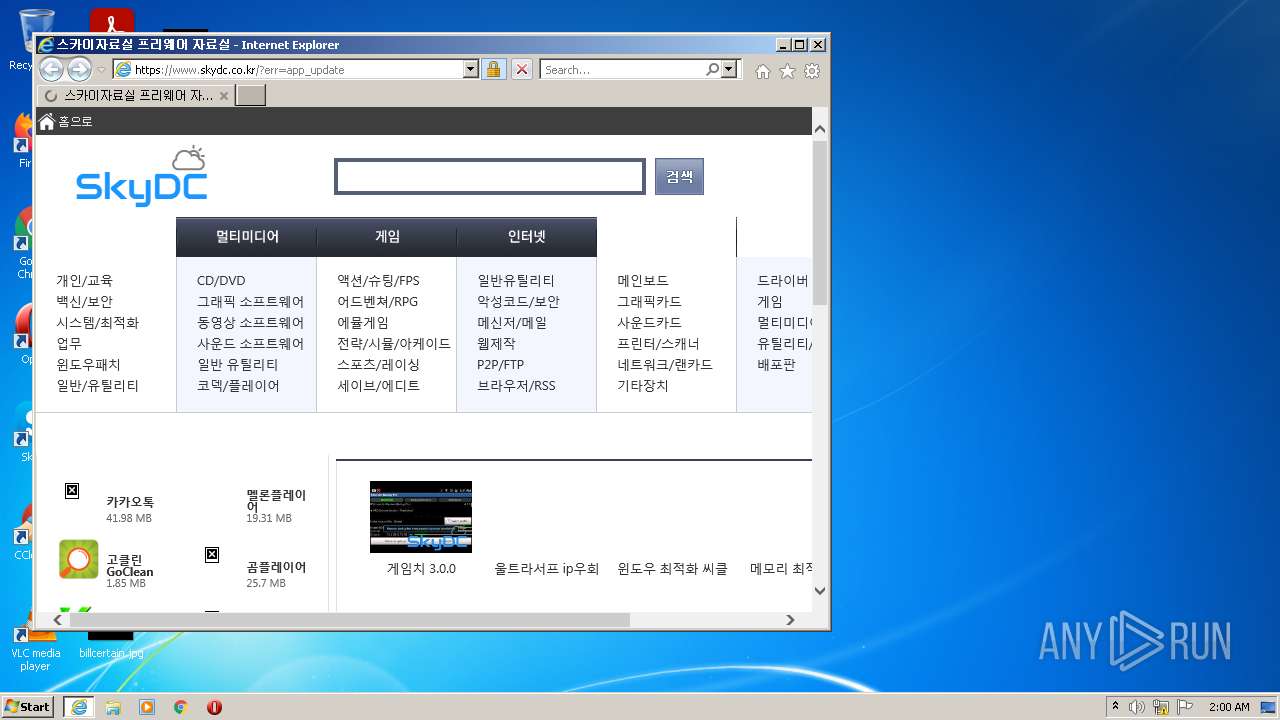
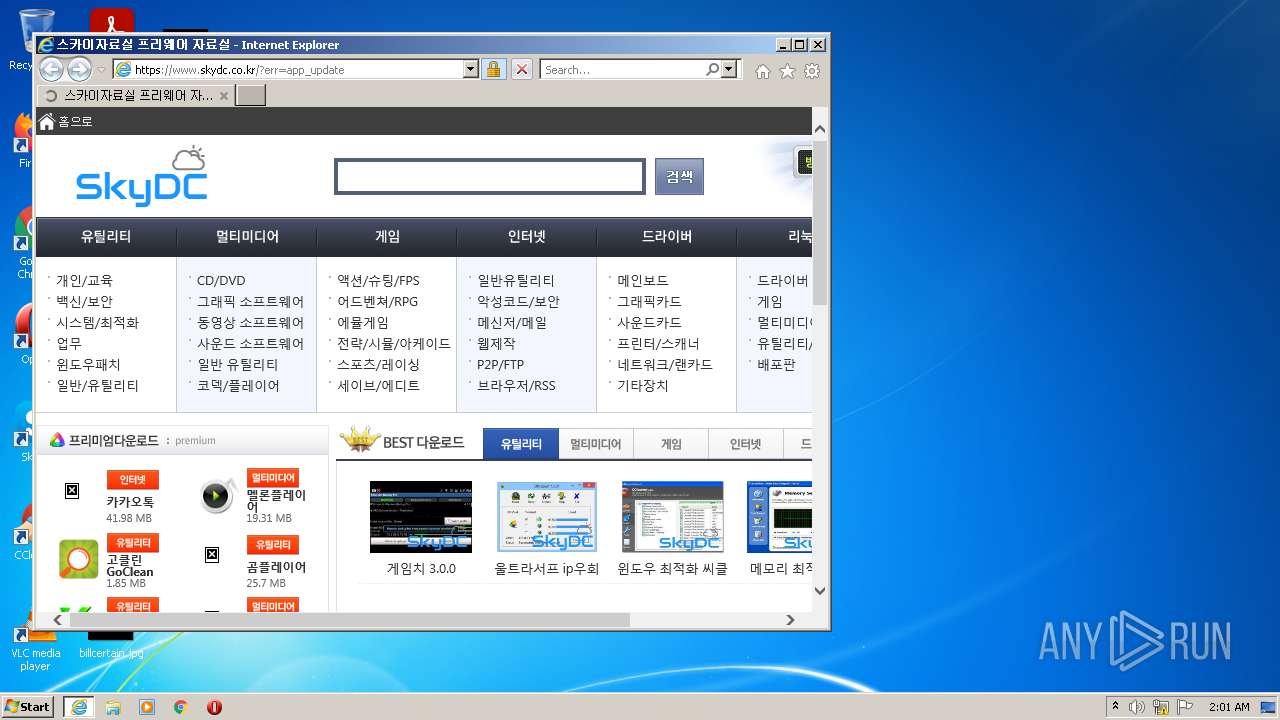
Starts Internet Explorer
- cdbdfbbee7947e87bc6de1ae718ed947f606c8bf205df16b20341c7b6573b33e.exe (PID: 1252)
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 1512)
INFO
Reads settings of System Certificates
- cdbdfbbee7947e87bc6de1ae718ed947f606c8bf205df16b20341c7b6573b33e.exe (PID: 1252)
- iexplore.exe (PID: 1512)
- iexplore.exe (PID: 3120)
Checks Windows Trust Settings
- cdbdfbbee7947e87bc6de1ae718ed947f606c8bf205df16b20341c7b6573b33e.exe (PID: 1252)
- iexplore.exe (PID: 3120)
- iexplore.exe (PID: 1512)
Checks supported languages
- iexplore.exe (PID: 3120)
- iexplore.exe (PID: 1512)
Reads the computer name
- iexplore.exe (PID: 3120)
- iexplore.exe (PID: 1512)
Application launched itself
- iexplore.exe (PID: 3120)
Changes internet zones settings
- iexplore.exe (PID: 3120)
Reads internet explorer settings
- iexplore.exe (PID: 1512)
Creates files in the user directory
- iexplore.exe (PID: 1512)
- iexplore.exe (PID: 3120)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3120)
Changes settings of System certificates
- iexplore.exe (PID: 3120)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (64.2) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.6) |
| .exe | | | Win32 Executable (generic) (10.6) |
| .exe | | | Generic Win/DOS Executable (4.7) |
| .exe | | | DOS Executable Generic (4.7) |
EXIF
EXE
| Subsystem: | Windows GUI |
|---|---|
| SubsystemVersion: | 4 |
| ImageVersion: | - |
| OSVersion: | 4 |
| EntryPoint: | 0x8c670 |
| UninitializedDataSize: | 397312 |
| InitializedDataSize: | 12288 |
| CodeSize: | 176128 |
| LinkerVersion: | 6 |
| PEType: | PE32 |
| TimeStamp: | 2020:03:16 03:23:30+01:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 16-Mar-2020 02:23:30 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 16-Mar-2020 02:23:30 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x00061000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x00062000 | 0x0002B000 | 0x0002AA00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.91407 |
.rsrc | 0x0008D000 | 0x00003000 | 0x00002E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.76824 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.0493 | 616 | UNKNOWN | Korean - Korea | RT_MANIFEST |
2 | 6.36668 | 2216 | UNKNOWN | Korean - Korea | RT_ICON |
3 | 6.39428 | 1128 | UNKNOWN | Korean - Korea | RT_ICON |
4 | 5.44828 | 1384 | UNKNOWN | Korean - Korea | RT_ICON |
5 | 0 | 1128 | UNKNOWN | Korean - Korea | RT_ICON |
6 | 0 | 1384 | UNKNOWN | Korean - Korea | RT_ICON |
7 | 0 | 1384 | UNKNOWN | Korean - Korea | RT_ICON |
8 | 0 | 1128 | UNKNOWN | Korean - Korea | RT_ICON |
9 | 0 | 1384 | UNKNOWN | Korean - Korea | RT_ICON |
10 | 0 | 2216 | UNKNOWN | Korean - Korea | RT_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.DLL |
OLEAUT32.dll |
OLEPRO32.DLL |
SHELL32.dll |
USER32.dll |
WININET.dll |
WINMM.dll |
Total processes
39
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1252 | "C:\Users\admin\Desktop\cdbdfbbee7947e87bc6de1ae718ed947f606c8bf205df16b20341c7b6573b33e.exe" | C:\Users\admin\Desktop\cdbdfbbee7947e87bc6de1ae718ed947f606c8bf205df16b20341c7b6573b33e.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1512 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3120 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3120 | "C:\Program Files\Internet Explorer\iexplore.exe" https://www.skydc.co.kr/?err=app_update | C:\Program Files\Internet Explorer\iexplore.exe | cdbdfbbee7947e87bc6de1ae718ed947f606c8bf205df16b20341c7b6573b33e.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
22 919
Read events
22 741
Write events
171
Delete events
7
Modification events
| (PID) Process: | (1252) cdbdfbbee7947e87bc6de1ae718ed947f606c8bf205df16b20341c7b6573b33e.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1252) cdbdfbbee7947e87bc6de1ae718ed947f606c8bf205df16b20341c7b6573b33e.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1252) cdbdfbbee7947e87bc6de1ae718ed947f606c8bf205df16b20341c7b6573b33e.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1252) cdbdfbbee7947e87bc6de1ae718ed947f606c8bf205df16b20341c7b6573b33e.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (1252) cdbdfbbee7947e87bc6de1ae718ed947f606c8bf205df16b20341c7b6573b33e.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000003B010000090000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A80164000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1252) cdbdfbbee7947e87bc6de1ae718ed947f606c8bf205df16b20341c7b6573b33e.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1252) cdbdfbbee7947e87bc6de1ae718ed947f606c8bf205df16b20341c7b6573b33e.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1252) cdbdfbbee7947e87bc6de1ae718ed947f606c8bf205df16b20341c7b6573b33e.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1252) cdbdfbbee7947e87bc6de1ae718ed947f606c8bf205df16b20341c7b6573b33e.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (1252) cdbdfbbee7947e87bc6de1ae718ed947f606c8bf205df16b20341c7b6573b33e.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Wpad\{362E934C-743B-4588-8259-D2482DB771A8} |
| Operation: | write | Name: | WpadDecisionReason |
Value: 1 | |||
Executable files
0
Suspicious files
21
Text files
162
Unknown types
15
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1252 | cdbdfbbee7947e87bc6de1ae718ed947f606c8bf205df16b20341c7b6573b33e.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\77EC63BDA74BD0D0E0426DC8F8008506 | binary | |
MD5:— | SHA256:— | |||
| 1252 | cdbdfbbee7947e87bc6de1ae718ed947f606c8bf205df16b20341c7b6573b33e.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 1252 | cdbdfbbee7947e87bc6de1ae718ed947f606c8bf205df16b20341c7b6573b33e.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\103621DE9CD5414CC2538780B4B75751 | binary | |
MD5:— | SHA256:— | |||
| 1252 | cdbdfbbee7947e87bc6de1ae718ed947f606c8bf205df16b20341c7b6573b33e.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\EC75D96F0A397C5B662465E6CA15FBF6 | der | |
MD5:— | SHA256:— | |||
| 1252 | cdbdfbbee7947e87bc6de1ae718ed947f606c8bf205df16b20341c7b6573b33e.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\EC75D96F0A397C5B662465E6CA15FBF6 | binary | |
MD5:— | SHA256:— | |||
| 1252 | cdbdfbbee7947e87bc6de1ae718ed947f606c8bf205df16b20341c7b6573b33e.exe | C:\Users\admin\AppData\Local\Temp\512F.tmp | text | |
MD5:— | SHA256:— | |||
| 1512 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\paging[1].css | text | |
MD5:— | SHA256:— | |||
| 1512 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | binary | |
MD5:— | SHA256:— | |||
| 1512 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | der | |
MD5:— | SHA256:— | |||
| 1512 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\CAF4703619713E3F18D8A9D5D88D6288_A7725538C46DE2D0088EE44974E2CEBA | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
17
TCP/UDP connections
200
DNS requests
30
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1512 | iexplore.exe | GET | 200 | 142.250.184.195:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | der | 1.41 Kb | whitelisted |
1512 | iexplore.exe | GET | 200 | 142.250.184.195:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | der | 724 b | whitelisted |
1512 | iexplore.exe | GET | 200 | 142.250.184.195:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQC2PrP09fGo%2BgoAAAABK3x6 | US | der | 472 b | whitelisted |
1512 | iexplore.exe | GET | 200 | 104.18.30.182:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | US | der | 471 b | whitelisted |
1512 | iexplore.exe | GET | 200 | 104.18.31.182:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEH1bUSa0droR23QWC7xTDac%3D | US | der | 727 b | whitelisted |
1512 | iexplore.exe | GET | 200 | 104.18.31.182:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEChOOcFLOG2InHKZ5YzQWlc%3D | US | der | 727 b | whitelisted |
1512 | iexplore.exe | GET | 200 | 2.16.107.96:80 | http://r3.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBRI2smg%2ByvTLU%2Fw3mjS9We3NfmzxAQUFC6zF7dYVsuuUAlA5h%2BvnYsUwsYCEgRto6LQXY4k5Ae7BzNpAgQBeA%3D%3D | unknown | der | 503 b | shared |
1512 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAVG%2Fhgj9%2BGUHaOfzhTEYXM%3D | US | der | 471 b | whitelisted |
3120 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA177el9ggmWelJjG4vdGL0%3D | US | der | 471 b | whitelisted |
1512 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://status.geotrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBR3enuod9bxDxzpICGW%2B2sabjf17QQUkFj%2FsJx1qFFUd7Ht8qNDFjiebMUCEAizz4BnNrkfMPE50Zfatds%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1252 | cdbdfbbee7947e87bc6de1ae718ed947f606c8bf205df16b20341c7b6573b33e.exe | 211.233.33.250:443 | skydc.co.kr | LG DACOM Corporation | KR | suspicious |
1252 | cdbdfbbee7947e87bc6de1ae718ed947f606c8bf205df16b20341c7b6573b33e.exe | 23.32.238.178:80 | ctldl.windowsupdate.com | XO Communications | US | suspicious |
1252 | cdbdfbbee7947e87bc6de1ae718ed947f606c8bf205df16b20341c7b6573b33e.exe | 23.32.238.201:80 | ctldl.windowsupdate.com | XO Communications | US | suspicious |
1512 | iexplore.exe | 211.233.33.250:443 | skydc.co.kr | LG DACOM Corporation | KR | suspicious |
1252 | cdbdfbbee7947e87bc6de1ae718ed947f606c8bf205df16b20341c7b6573b33e.exe | 2.16.107.115:80 | r3.o.lencr.org | Akamai International B.V. | — | malicious |
1512 | iexplore.exe | 104.109.70.229:443 | wcs.naver.net | Akamai International B.V. | NL | unknown |
1512 | iexplore.exe | 142.250.184.200:443 | www.googletagmanager.com | Google Inc. | US | suspicious |
1512 | iexplore.exe | 142.250.184.195:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
1512 | iexplore.exe | 69.16.175.42:443 | code.jquery.com | Highwinds Network Group, Inc. | US | malicious |
1512 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
skydc.co.kr |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
r3.o.lencr.org |
| shared |
www.skydc.co.kr |
| suspicious |
www.googletagmanager.com |
| whitelisted |
wcs.naver.net |
| whitelisted |
pds.skydc.co.kr |
| suspicious |
ocsp.pki.goog |
| whitelisted |
ocsp.digicert.com |
| whitelisted |