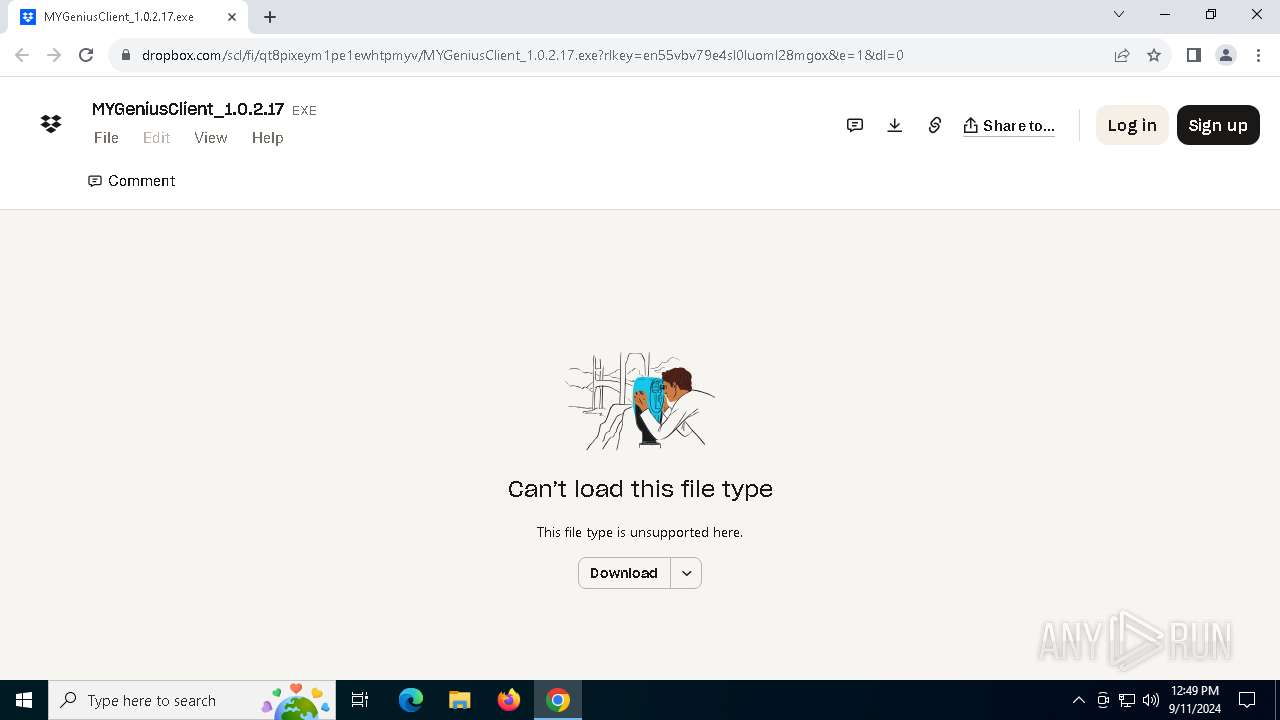
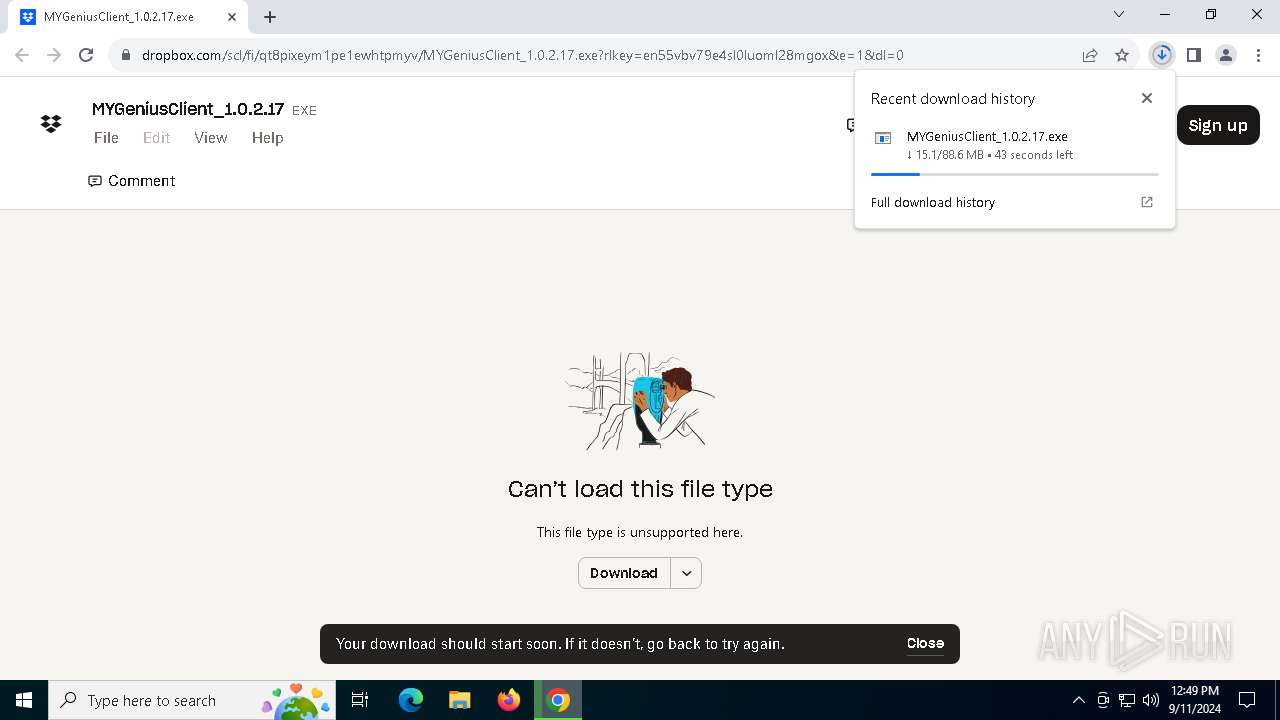
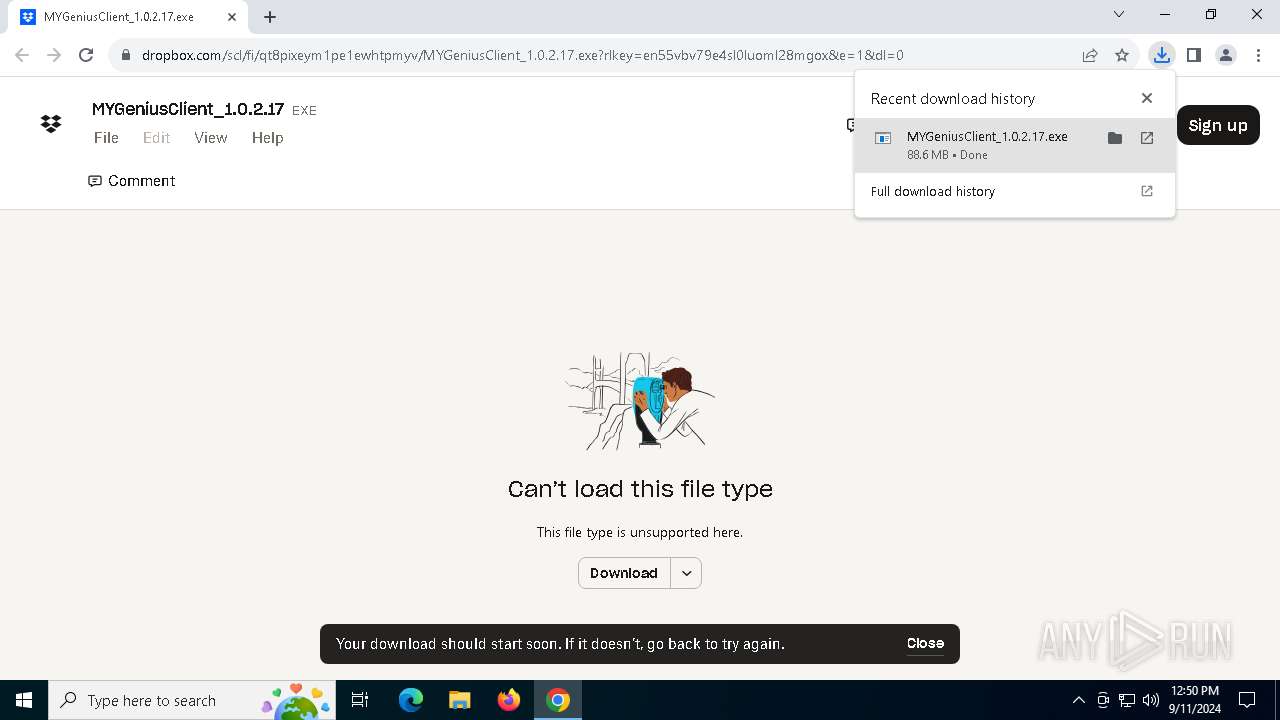
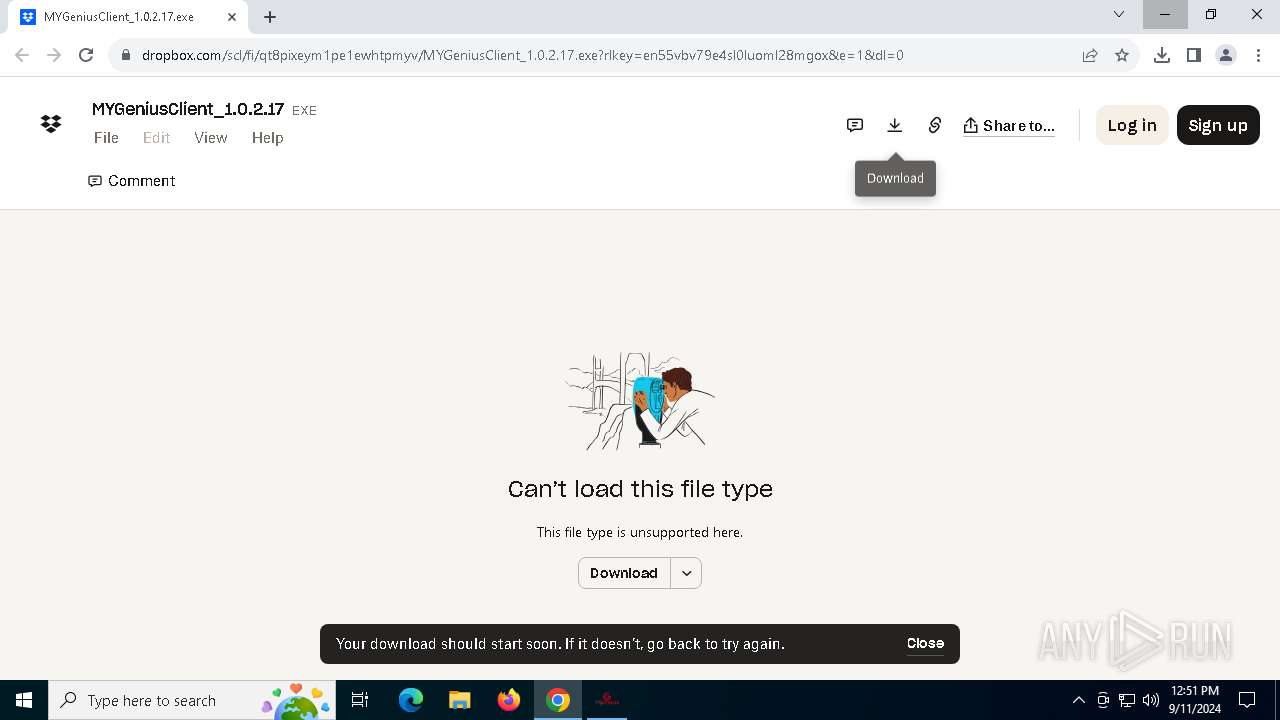
| URL: | https://www.dropbox.com/scl/fi/qt8pixeym1pe1ewhtpmyv/MYGeniusClient_1.0.2.17.exe?rlkey=en55vbv79e4sl0luoml28mgox&dl=0 |
| Full analysis: | https://app.any.run/tasks/7fc78d12-1c18-4b33-9f71-f4d4774efd8b |
| Verdict: | Malicious activity |
| Analysis date: | September 11, 2024, 12:49:00 |
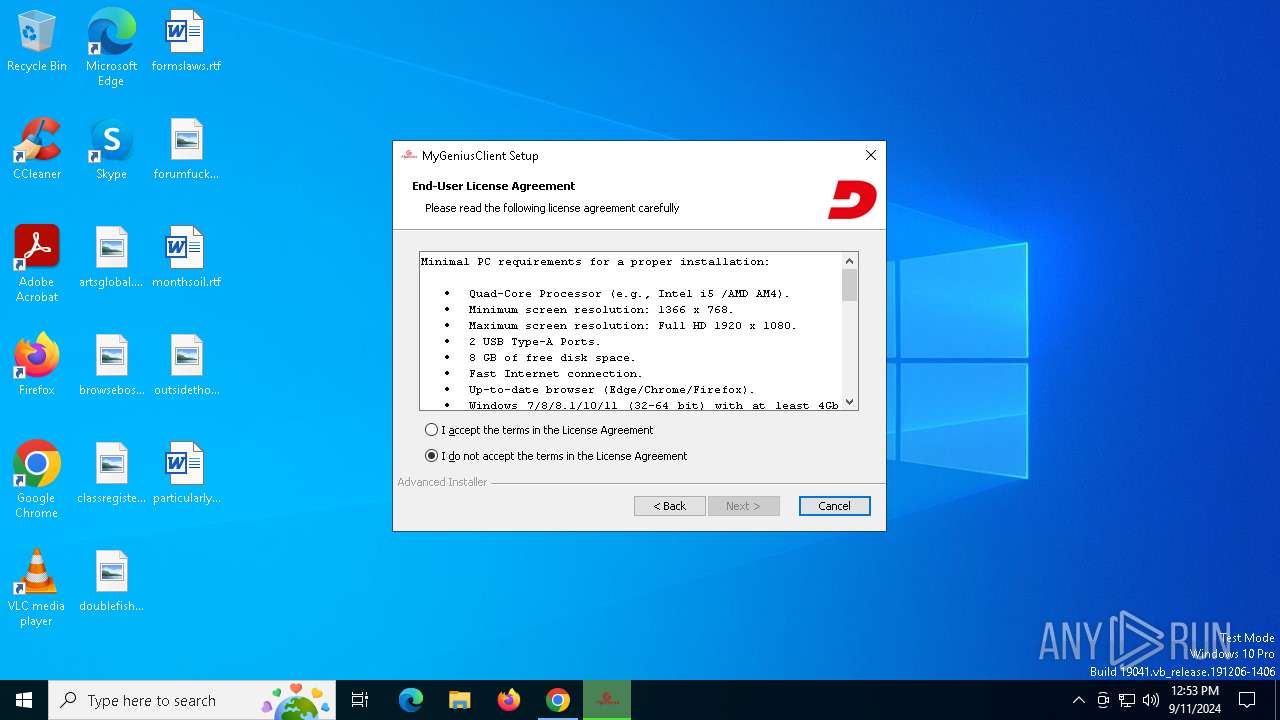
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 6AD13A2773E294597C728414AB637EF1 |
| SHA1: | 0180A3C1E036C90305A81CE6C8DEB16DE9266B49 |
| SHA256: | CDB88181DD17F71BC507002359927C1B59E65876DC4F8839526D1CBDE781B23C |
| SSDEEP: | 3:N8DSLcVHGkG6gY7AZ+Rbz88QWmJMAgUVXLqJxezSx8jacBS:2OLHk2YEZ2z88DzOVbqP+p3A |
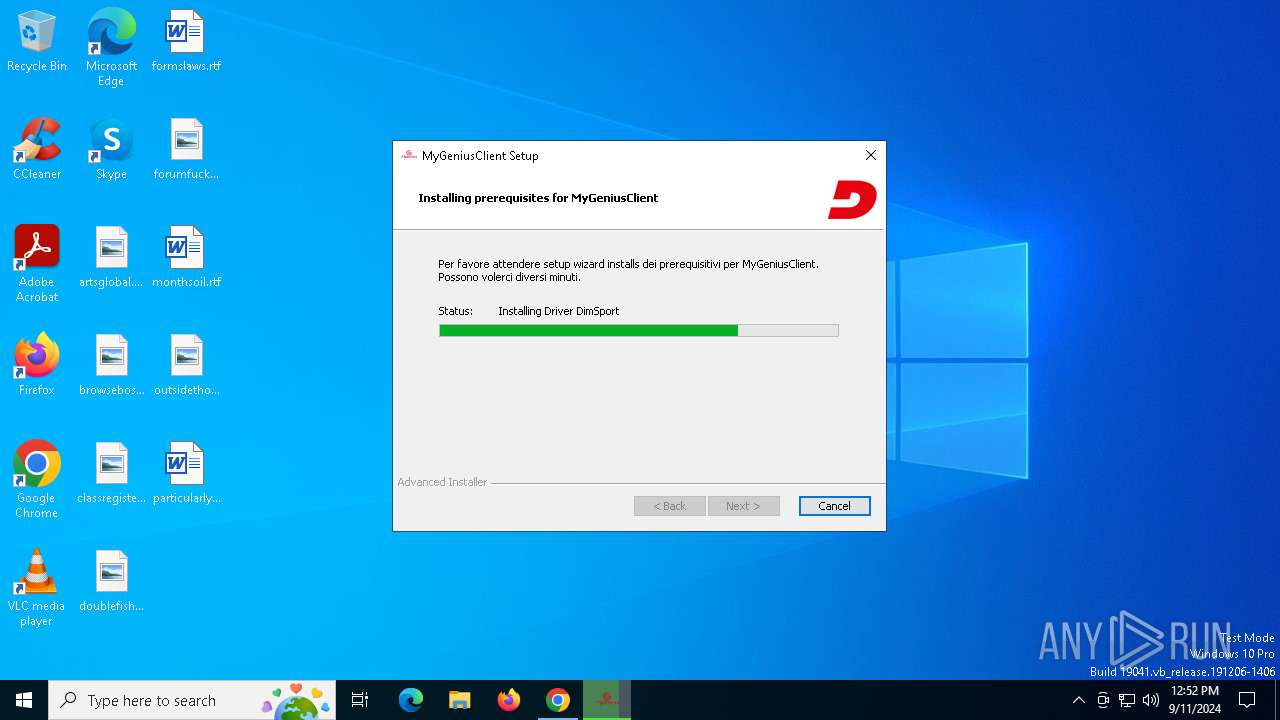
MALICIOUS
Changes the autorun value in the registry
- vcredist_x86_2005.exe (PID: 6492)
- VCREDI~3.EXE (PID: 400)
- vcredist_x64_2005.exe (PID: 6020)
- VCREDI~2.EXE (PID: 1344)
Gets a file object corresponding to the file in a specified path (SCRIPT)
- msiexec.exe (PID: 6424)
Deletes a file (SCRIPT)
- msiexec.exe (PID: 6424)
Changes powershell execution policy (AllSigned)
- aipackagechainer.exe (PID: 3700)
SUSPICIOUS
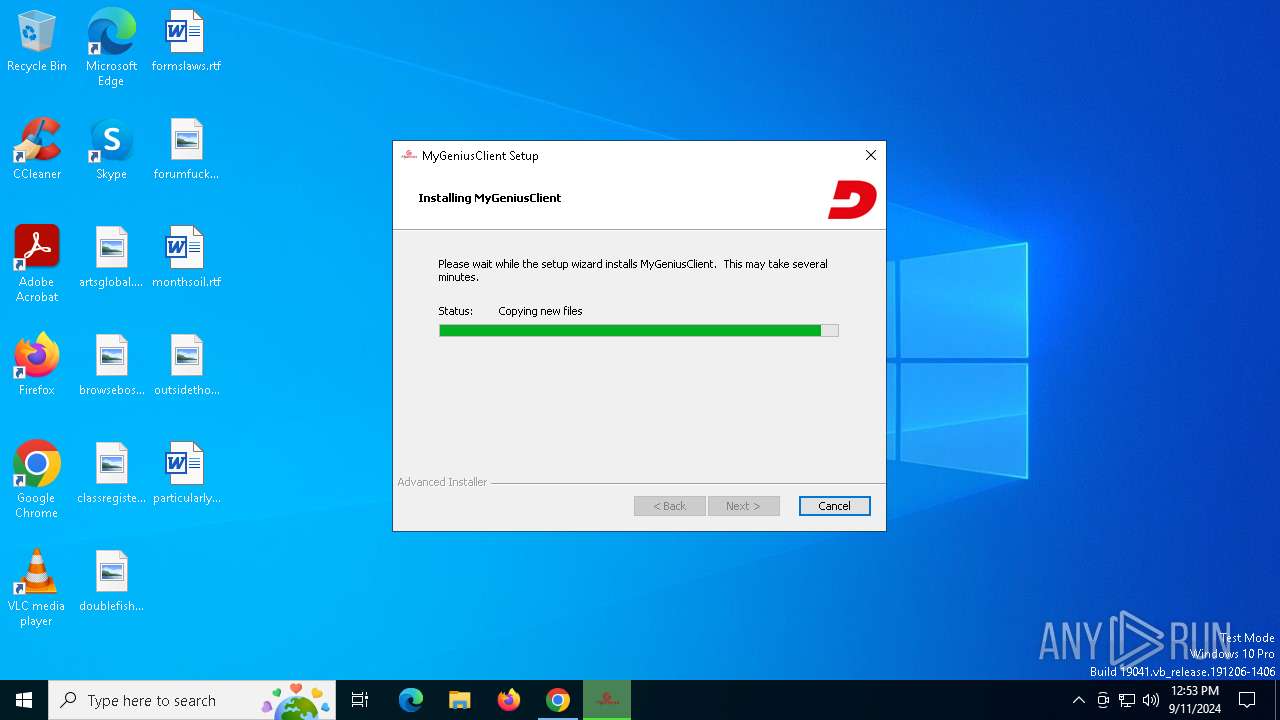
Executable content was dropped or overwritten
- MYGeniusClient_1.0.2.17.exe (PID: 1636)
- vcredist_x86_2005.exe (PID: 6492)
- VCREDI~3.EXE (PID: 400)
- TiWorker.exe (PID: 1280)
- VCREDI~2.EXE (PID: 1344)
- Install_Driver_64.exe (PID: 6268)
- vcredist_x64_2005.exe (PID: 6020)
- drvinst.exe (PID: 2228)
- drvinst.exe (PID: 7100)
- MYGeniusClient_1.0.2.17.exe (PID: 6128)
Reads the Windows owner or organization settings
- MYGeniusClient_1.0.2.17.exe (PID: 1636)
- msiexec.exe (PID: 1452)
- MYGeniusClient_1.0.2.17.exe (PID: 6128)
Reads security settings of Internet Explorer
- MYGeniusClient_1.0.2.17.exe (PID: 1636)
- msiexec.exe (PID: 6200)
- aipackagechainer.exe (PID: 3700)
- MYGeniusClient_1.0.2.17.exe (PID: 6128)
- MSIBC03.tmp (PID: 3996)
- DSUpdate.exe (PID: 6576)
- MyGeniusClient.exe (PID: 6516)
Process drops legitimate windows executable
- MYGeniusClient_1.0.2.17.exe (PID: 1636)
- vcredist_x86_2005.exe (PID: 6492)
- msiexec.exe (PID: 1452)
- TiWorker.exe (PID: 1280)
- vcredist_x64_2005.exe (PID: 6020)
- msiexec.exe (PID: 2264)
- Install_Driver_64.exe (PID: 6268)
- MYGeniusClient_1.0.2.17.exe (PID: 6128)
Starts a Microsoft application from unusual location
- VCREDI~3.EXE (PID: 400)
- VCREDI~2.EXE (PID: 1344)
- Install_Driver_64.exe (PID: 6268)
- Install_Driver_64.exe (PID: 5040)
Checks Windows Trust Settings
- MYGeniusClient_1.0.2.17.exe (PID: 1636)
- msiexec.exe (PID: 1452)
- drvinst.exe (PID: 7100)
- drvinst.exe (PID: 2228)
- MYGeniusClient_1.0.2.17.exe (PID: 6128)
Executes as Windows Service
- VSSVC.exe (PID: 2040)
The process drops C-runtime libraries
- msiexec.exe (PID: 1452)
- TiWorker.exe (PID: 1280)
Drops a system driver (possible attempt to evade defenses)
- msiexec.exe (PID: 2264)
- Install_Driver_64.exe (PID: 6268)
- drvinst.exe (PID: 7100)
- drvinst.exe (PID: 2228)
Creates FileSystem object to access computer's file system (SCRIPT)
- msiexec.exe (PID: 6200)
- msiexec.exe (PID: 6424)
Reads the date of Windows installation
- msiexec.exe (PID: 6200)
Creates files in the driver directory
- drvinst.exe (PID: 7100)
- drvinst.exe (PID: 2228)
- drvinst.exe (PID: 6164)
Creates a software uninstall entry
- Install_Driver_64.exe (PID: 6268)
Executing commands from a ".bat" file
- aipackagechainer.exe (PID: 3700)
- MYGeniusClient_1.0.2.17.exe (PID: 1636)
- cmd.exe (PID: 2228)
Creates/Modifies COM task schedule object
- msiexec.exe (PID: 5944)
- msiexec.exe (PID: 3800)
- msiexec.exe (PID: 6552)
The process hide an interactive prompt from the user
- aipackagechainer.exe (PID: 3700)
The process hides Powershell's copyright startup banner
- aipackagechainer.exe (PID: 3700)
Starts POWERSHELL.EXE for commands execution
- aipackagechainer.exe (PID: 3700)
Adds/modifies Windows certificates
- powershell.exe (PID: 3104)
The process executes Powershell scripts
- aipackagechainer.exe (PID: 3700)
Application launched itself
- MYGeniusClient_1.0.2.17.exe (PID: 1636)
- cmd.exe (PID: 2228)
Starts application with an unusual extension
- MYGeniusClient_1.0.2.17.exe (PID: 1636)
Uses ATTRIB.EXE to modify file attributes
- cmd.exe (PID: 2228)
Starts CMD.EXE for commands execution
- MYGeniusClient_1.0.2.17.exe (PID: 1636)
- cmd.exe (PID: 2228)
- aipackagechainer.exe (PID: 3700)
Reads the BIOS version
- DSUpdate.exe (PID: 6576)
- MyGeniusClient.exe (PID: 6516)
Reads Microsoft Outlook installation path
- DSUpdate.exe (PID: 6576)
There is functionality for sending ICMP (YARA)
- DSUpdate.exe (PID: 6576)
There is functionality for taking screenshot (YARA)
- MyGeniusClient.exe (PID: 6516)
Reads Internet Explorer settings
- DSUpdate.exe (PID: 6576)
Runs shell command (SCRIPT)
- msiexec.exe (PID: 6200)
INFO
Application launched itself
- chrome.exe (PID: 5088)
- msiexec.exe (PID: 1452)
Executable content was dropped or overwritten
- chrome.exe (PID: 5088)
- msiexec.exe (PID: 1452)
- msiexec.exe (PID: 2264)
- msiexec.exe (PID: 6424)
Reads Environment values
- MYGeniusClient_1.0.2.17.exe (PID: 1636)
- msiexec.exe (PID: 2264)
- msiexec.exe (PID: 6200)
- msiexec.exe (PID: 6424)
- aipackagechainer.exe (PID: 3700)
- msiexec.exe (PID: 2340)
- MYGeniusClient_1.0.2.17.exe (PID: 6128)
- msiexec.exe (PID: 2960)
The process uses the downloaded file
- chrome.exe (PID: 5088)
- chrome.exe (PID: 6312)
- MYGeniusClient_1.0.2.17.exe (PID: 1636)
- msiexec.exe (PID: 6200)
- aipackagechainer.exe (PID: 3700)
- powershell.exe (PID: 3104)
- MSIBC03.tmp (PID: 3996)
Reads the machine GUID from the registry
- MYGeniusClient_1.0.2.17.exe (PID: 1636)
- msiexec.exe (PID: 1452)
- drvinst.exe (PID: 7100)
- drvinst.exe (PID: 2228)
- Install_Driver_64.exe (PID: 6268)
- Install_Driver_64.exe (PID: 5040)
- MYGeniusClient_1.0.2.17.exe (PID: 6128)
- DSUpdate.exe (PID: 6576)
- MyGeniusClient.exe (PID: 6516)
Reads the computer name
- msiexec.exe (PID: 1452)
- MYGeniusClient_1.0.2.17.exe (PID: 1636)
- msiexec.exe (PID: 1448)
- vcredist_x86_2005.exe (PID: 6492)
- VCREDI~3.EXE (PID: 400)
- msiexec.exe (PID: 1132)
- VCREDI~2.EXE (PID: 1344)
- msiexec.exe (PID: 5048)
- msiexec.exe (PID: 2264)
- msiexec.exe (PID: 6200)
- Install_Driver_64.exe (PID: 6268)
- drvinst.exe (PID: 7100)
- vcredist_x64_2005.exe (PID: 6020)
- drvinst.exe (PID: 2228)
- Install_Driver_64.exe (PID: 5040)
- drvinst.exe (PID: 6164)
- msiexec.exe (PID: 6424)
- msiexec.exe (PID: 7068)
- aipackagechainer.exe (PID: 3700)
- msiexec.exe (PID: 2340)
- MYGeniusClient_1.0.2.17.exe (PID: 6128)
- msiexec.exe (PID: 2960)
- MSIBC03.tmp (PID: 3996)
- DSUpdate.exe (PID: 6576)
- MyGeniusClient.exe (PID: 6516)
Create files in a temporary directory
- MYGeniusClient_1.0.2.17.exe (PID: 1636)
- vcredist_x86_2005.exe (PID: 6492)
- VCREDI~3.EXE (PID: 400)
- vcredist_x64_2005.exe (PID: 6020)
- VCREDI~2.EXE (PID: 1344)
- msiexec.exe (PID: 2264)
- Install_Driver_64.exe (PID: 6268)
- msiexec.exe (PID: 6424)
- msiexec.exe (PID: 7068)
- MYGeniusClient_1.0.2.17.exe (PID: 6128)
- DSUpdate.exe (PID: 6576)
- aipackagechainer.exe (PID: 3700)
Checks supported languages
- msiexec.exe (PID: 1452)
- msiexec.exe (PID: 1448)
- vcredist_x86_2005.exe (PID: 6492)
- VCREDI~3.EXE (PID: 400)
- MYGeniusClient_1.0.2.17.exe (PID: 1636)
- msiexec.exe (PID: 1132)
- vcredist_x64_2005.exe (PID: 6020)
- VCREDI~2.EXE (PID: 1344)
- msiexec.exe (PID: 5048)
- msiexec.exe (PID: 2264)
- msiexec.exe (PID: 6200)
- Install_Driver_64.exe (PID: 6268)
- drvinst.exe (PID: 7100)
- drvinst.exe (PID: 2228)
- Install_Driver_64.exe (PID: 5040)
- msiexec.exe (PID: 6424)
- drvinst.exe (PID: 6164)
- msiexec.exe (PID: 7068)
- aipackagechainer.exe (PID: 3700)
- msiexec.exe (PID: 2340)
- MYGeniusClient_1.0.2.17.exe (PID: 6128)
- msiexec.exe (PID: 2960)
- MSIBC03.tmp (PID: 3996)
- DSUpdate.exe (PID: 6576)
- MyGeniusClient.exe (PID: 6516)
Checks proxy server information
- MYGeniusClient_1.0.2.17.exe (PID: 1636)
- msiexec.exe (PID: 6404)
- DSUpdate.exe (PID: 6576)
- MyGeniusClient.exe (PID: 6516)
Connects to unusual port
- chrome.exe (PID: 7040)
Process checks computer location settings
- MYGeniusClient_1.0.2.17.exe (PID: 1636)
- msiexec.exe (PID: 6200)
- aipackagechainer.exe (PID: 3700)
- MSIBC03.tmp (PID: 3996)
Creates files or folders in the user directory
- MYGeniusClient_1.0.2.17.exe (PID: 1636)
- msiexec.exe (PID: 6404)
- msiexec.exe (PID: 6424)
- DSUpdate.exe (PID: 6576)
- MyGeniusClient.exe (PID: 6516)
Reads the software policy settings
- MYGeniusClient_1.0.2.17.exe (PID: 1636)
- msiexec.exe (PID: 1452)
- msiexec.exe (PID: 6404)
- msiexec.exe (PID: 3540)
- drvinst.exe (PID: 7100)
- rundll32.exe (PID: 6032)
- drvinst.exe (PID: 2228)
- Install_Driver_64.exe (PID: 6268)
- Install_Driver_64.exe (PID: 5040)
- MYGeniusClient_1.0.2.17.exe (PID: 6128)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 6404)
- rundll32.exe (PID: 6032)
- msiexec.exe (PID: 3540)
Creates a software uninstall entry
- msiexec.exe (PID: 1452)
Sends debugging messages
- msiexec.exe (PID: 2264)
- msiexec.exe (PID: 7068)
- msiexec.exe (PID: 6424)
- msiexec.exe (PID: 3800)
- MyGeniusClient.exe (PID: 6516)
Adds/modifies Windows certificates
- drvinst.exe (PID: 7100)
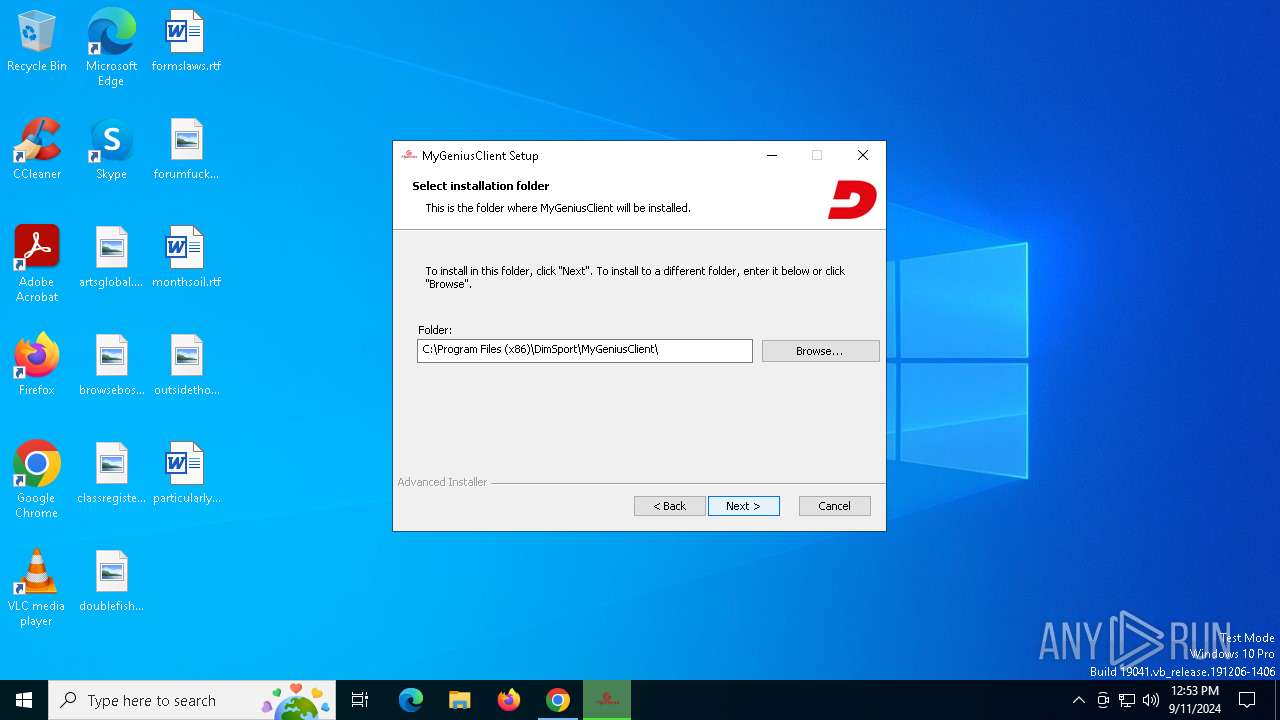
Creates files in the program directory
- Install_Driver_64.exe (PID: 6268)
- DSUpdate.exe (PID: 6576)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 3104)
Process checks whether UAC notifications are on
- DSUpdate.exe (PID: 6576)
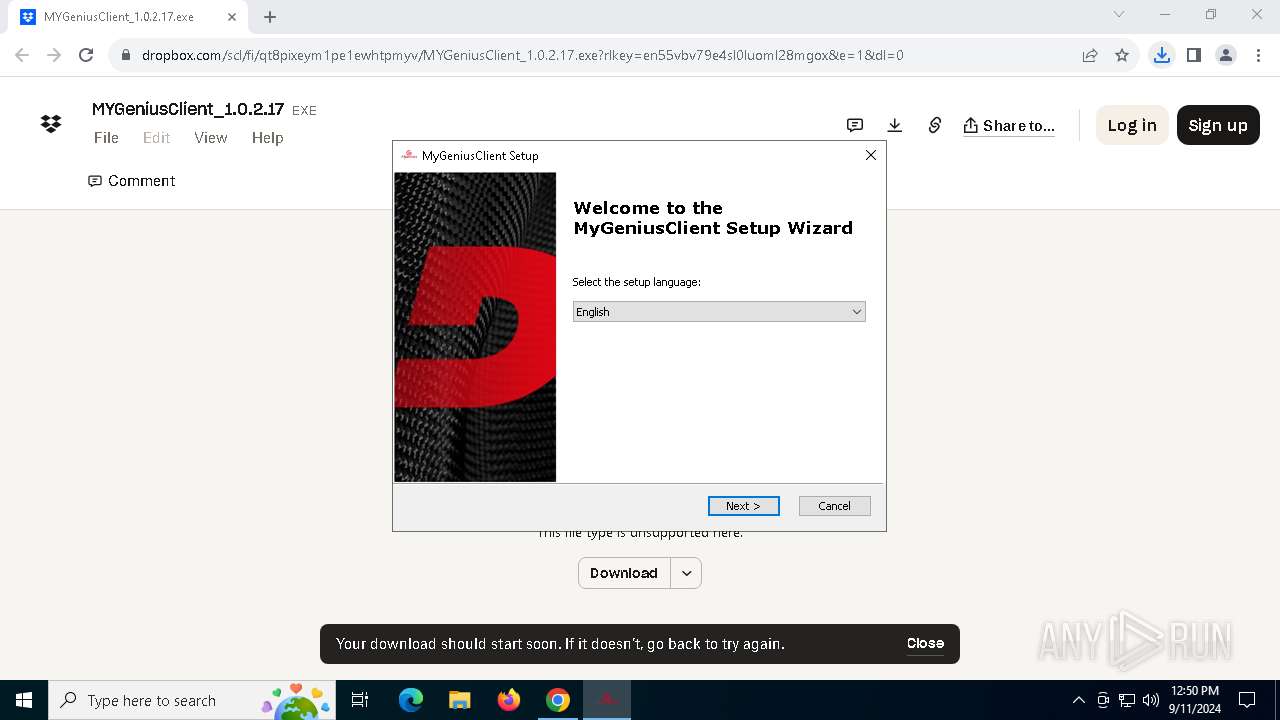
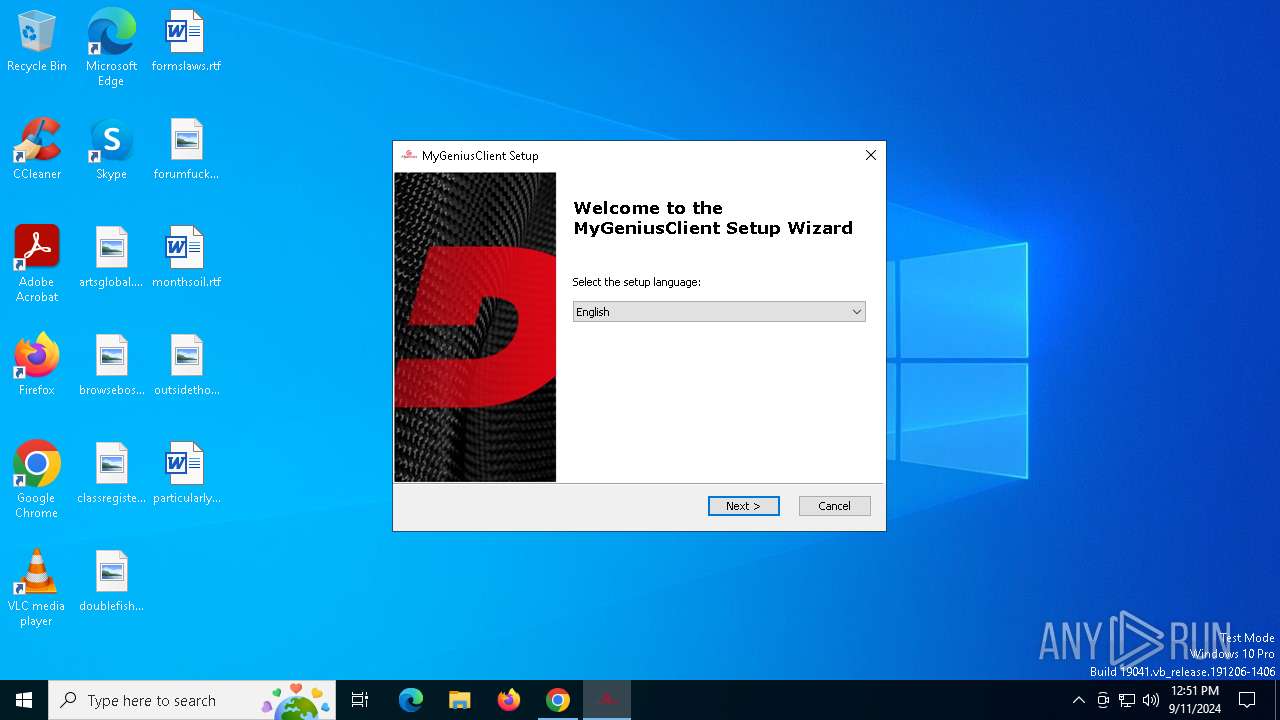
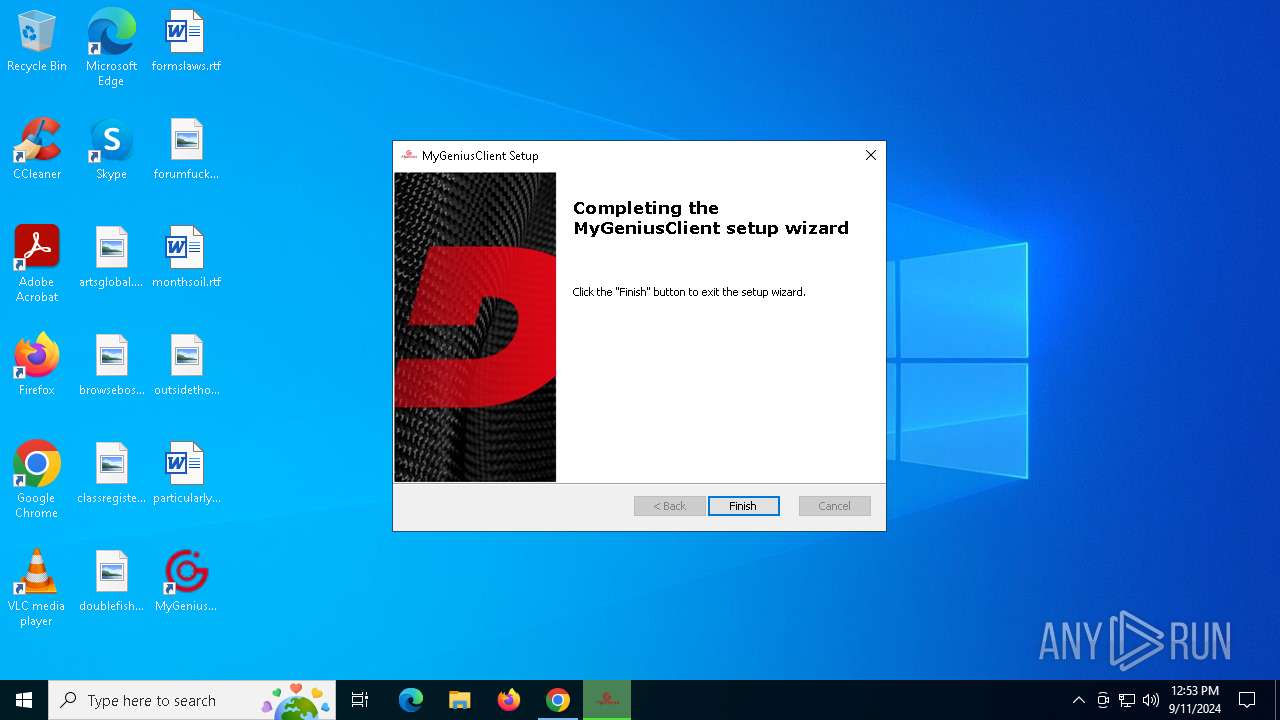
Manual execution by a user
- MyGeniusClient.exe (PID: 6516)
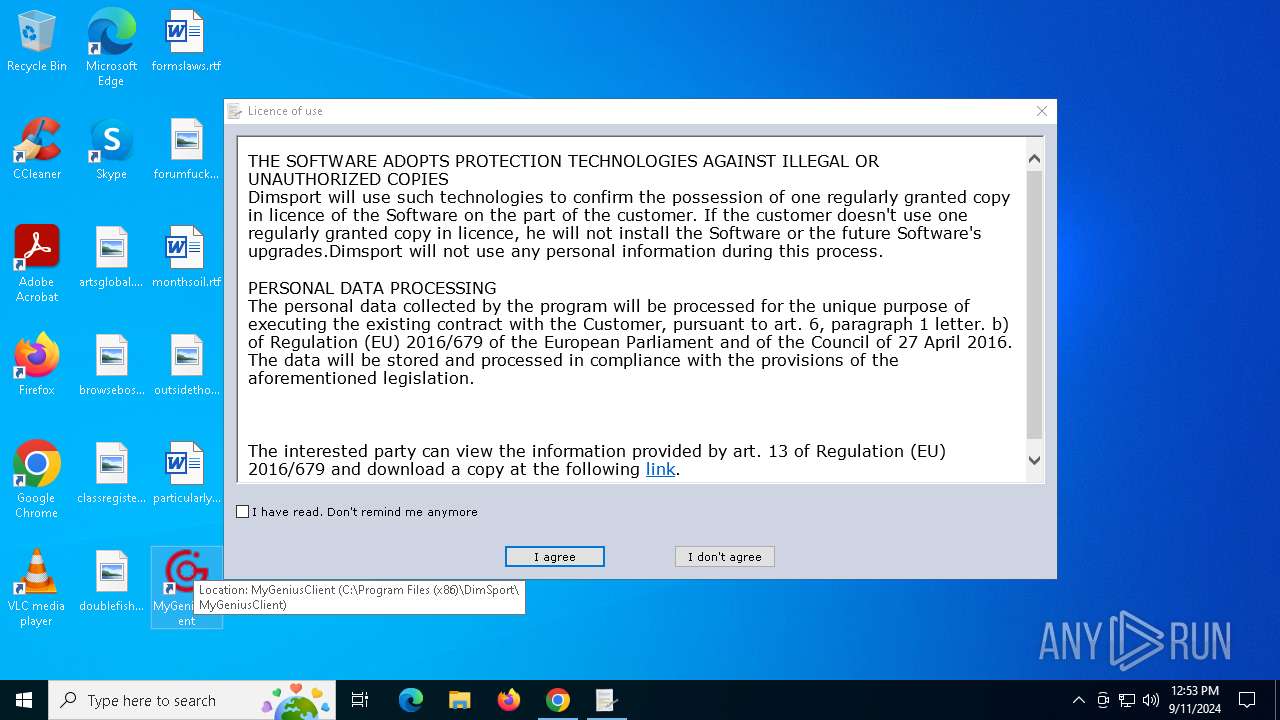
Themida protector has been detected
- DSUpdate.exe (PID: 6576)
Disables trace logs
- MyGeniusClient.exe (PID: 6516)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
213
Monitored processes
75
Malicious processes
14
Suspicious processes
8
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 232 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5520 --field-trial-handle=1964,i,18149701964777749624,6239346444090343510,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 368 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5204 --field-trial-handle=1964,i,18149701964777749624,6239346444090343510,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
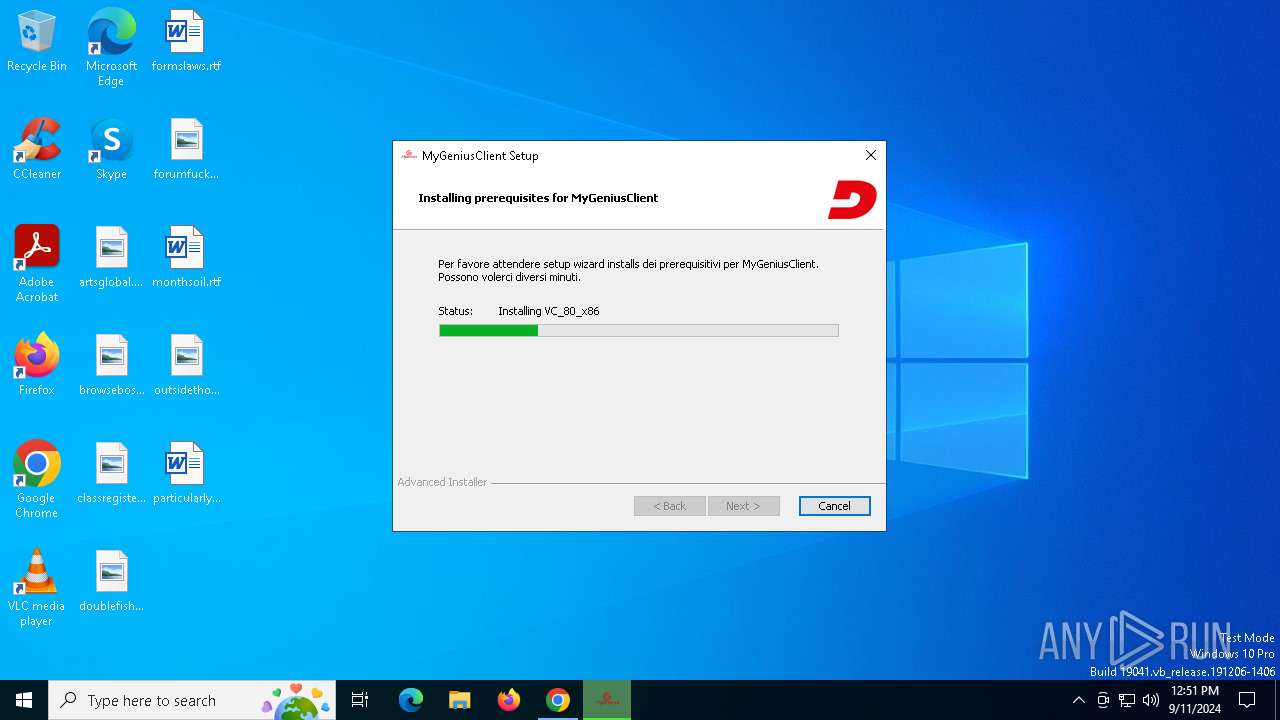
| 400 | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\VCREDI~3.EXE | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\VCREDI~3.EXE | vcredist_x86_2005.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: IExpress Setup Exit code: 0 Version: 2.0.50727.4053 Modules
| |||||||||||||||
| 508 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --mojo-platform-channel-handle=3052 --field-trial-handle=1964,i,18149701964777749624,6239346444090343510,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1132 | C:\Windows\syswow64\MsiExec.exe -Embedding D7FA8ABAD61C681DD1FB71F0B4135447 | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1280 | C:\WINDOWS\winsxs\amd64_microsoft-windows-servicingstack_31bf3856ad364e35_10.0.19041.3989_none_7ddb45627cb30e03\TiWorker.exe -Embedding | C:\Windows\WinSxS\amd64_microsoft-windows-servicingstack_31bf3856ad364e35_10.0.19041.3989_none_7ddb45627cb30e03\TiWorker.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Modules Installer Worker Exit code: 0 Version: 10.0.19041.3989 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1344 | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\VCREDI~2.EXE | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\VCREDI~2.EXE | vcredist_x64_2005.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: IExpress Setup Exit code: 0 Version: 2.0.50727.4053 Modules
| |||||||||||||||
| 1448 | C:\Windows\syswow64\MsiExec.exe -Embedding 111958BEBB8AACE77675CC2C393B0015 C | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1452 | C:\WINDOWS\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1636 | "C:\Users\admin\Downloads\MYGeniusClient_1.0.2.17.exe" | C:\Users\admin\Downloads\MYGeniusClient_1.0.2.17.exe | chrome.exe | ||||||||||||
User: admin Company: DimSport Integrity Level: HIGH Description: MyGeniusClient Installer Exit code: 0 Version: 1.0.2.11 Modules
| |||||||||||||||
Total events
80 354
Read events
77 628
Write events
2 484
Delete events
242
Modification events
| (PID) Process: | (5088) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (5088) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (5088) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (5088) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (5088) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (6312) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {2781761E-28E0-4109-99FE-B9D127C57AFE} {56FFCC30-D398-11D0-B2AE-00A0C908FA49} 0xFFFF |
Value: 0100000000000000D49105274904DB01 | |||
| (PID) Process: | (5088) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Common\Rlz\Events\C |
| Operation: | write | Name: | C1I |
Value: 1 | |||
| (PID) Process: | (5088) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Common\Rlz\Events\C |
| Operation: | write | Name: | C2I |
Value: 1 | |||
| (PID) Process: | (5088) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Common\Rlz\Events\C |
| Operation: | write | Name: | C7I |
Value: 1 | |||
| (PID) Process: | (5088) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Common\Rlz\Events\C |
| Operation: | write | Name: | C1S |
Value: 1 | |||
Executable files
263
Suspicious files
355
Text files
227
Unknown types
93
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5088 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5088 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5088 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5088 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5088 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF12b3b8.TMP | — | |
MD5:— | SHA256:— | |||
| 5088 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5088 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF12b3b8.TMP | — | |
MD5:— | SHA256:— | |||
| 5088 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5088 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF12b389.TMP | text | |
MD5:8F45965291AB2DA10EEB049FB6E917C6 | SHA256:8A0DE526945B27CDBBD87357C85FDDD37B572370F894CB0A5AC533FD465D2166 | |||
| 5088 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:FCE53E052E5CF7C20819320F374DEA88 | SHA256:CD95DE277E746E92CC2C53D9FC92A8F6F0C3EDFB7F1AD9A4E9259F927065BC89 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
39
TCP/UDP connections
97
DNS requests
70
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6864 | svchost.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1064 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4820 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7020 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acaldksiunzh56452py2db5mnbpa_120.0.6050.0/jamhcnnkihinmdlkakkaopbjbbcngflc_120.0.6050.0_all_dgzfpknn7v3zslsbhrwu6bt44e.crx3 | unknown | — | — | whitelisted |
7020 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acaldksiunzh56452py2db5mnbpa_120.0.6050.0/jamhcnnkihinmdlkakkaopbjbbcngflc_120.0.6050.0_all_dgzfpknn7v3zslsbhrwu6bt44e.crx3 | unknown | — | — | whitelisted |
7020 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acaldksiunzh56452py2db5mnbpa_120.0.6050.0/jamhcnnkihinmdlkakkaopbjbbcngflc_120.0.6050.0_all_dgzfpknn7v3zslsbhrwu6bt44e.crx3 | unknown | — | — | whitelisted |
7020 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acaldksiunzh56452py2db5mnbpa_120.0.6050.0/jamhcnnkihinmdlkakkaopbjbbcngflc_120.0.6050.0_all_dgzfpknn7v3zslsbhrwu6bt44e.crx3 | unknown | — | — | whitelisted |
7020 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acaldksiunzh56452py2db5mnbpa_120.0.6050.0/jamhcnnkihinmdlkakkaopbjbbcngflc_120.0.6050.0_all_dgzfpknn7v3zslsbhrwu6bt44e.crx3 | unknown | — | — | whitelisted |
7020 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acaldksiunzh56452py2db5mnbpa_120.0.6050.0/jamhcnnkihinmdlkakkaopbjbbcngflc_120.0.6050.0_all_dgzfpknn7v3zslsbhrwu6bt44e.crx3 | unknown | — | — | whitelisted |
7020 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acaldksiunzh56452py2db5mnbpa_120.0.6050.0/jamhcnnkihinmdlkakkaopbjbbcngflc_120.0.6050.0_all_dgzfpknn7v3zslsbhrwu6bt44e.crx3 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6864 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6776 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2120 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5088 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7040 | chrome.exe | 162.125.66.18:443 | www.dropbox.com | DROPBOX | DE | shared |
7040 | chrome.exe | 142.250.110.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
7040 | chrome.exe | 104.16.100.29:443 | cfl.dropboxstatic.com | CLOUDFLARENET | — | shared |
6864 | svchost.exe | 51.11.168.232:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | GB | whitelisted |
6864 | svchost.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.dropbox.com |
| shared |
accounts.google.com |
| whitelisted |
cfl.dropboxstatic.com |
| shared |
www.microsoft.com |
| whitelisted |
fp.dropbox.com |
| shared |
use1-turn.fpjs.io |
| unknown |
beacon.dropbox.com |
| whitelisted |
www.google.com |
| whitelisted |
Threats
Process | Message |
|---|---|
msiexec.exe | Logger::SetLogFile( C:\Users\admin\AppData\Roaming\Caphyon\Advanced Installer\AI_ResourceCleaner.log ) while OLD path is: |
msiexec.exe | Logger::SetLogFile( C:\Users\admin\AppData\Roaming\Caphyon\Advanced Installer\AI_ResourceCleaner.log ) while OLD path is: |
msiexec.exe | Logger::SetLogFile( C:\Users\admin\AppData\Roaming\Caphyon\Advanced Installer\AI_ResourceCleaner.log ) while OLD path is: |
msiexec.exe | Logger::SetLogFile( C:\Users\admin\AppData\Roaming\Caphyon\Advanced Installer\AI_ResourceCleaner.log ) while OLD path is: |
msiexec.exe | Logger::SetLogFile( C:\Users\admin\AppData\Roaming\Caphyon\Advanced Installer\AI_ResourceCleaner.log ) while OLD path is: |
msiexec.exe | Logger::SetLogFile( C:\Users\admin\AppData\Roaming\Caphyon\Advanced Installer\AI_ResourceCleaner.log ) while OLD path is: |
msiexec.exe | Logger::SetLogFile( C:\Users\admin\AppData\Roaming\Caphyon\Advanced Installer\AI_ResourceCleaner.log ) while OLD path is: |
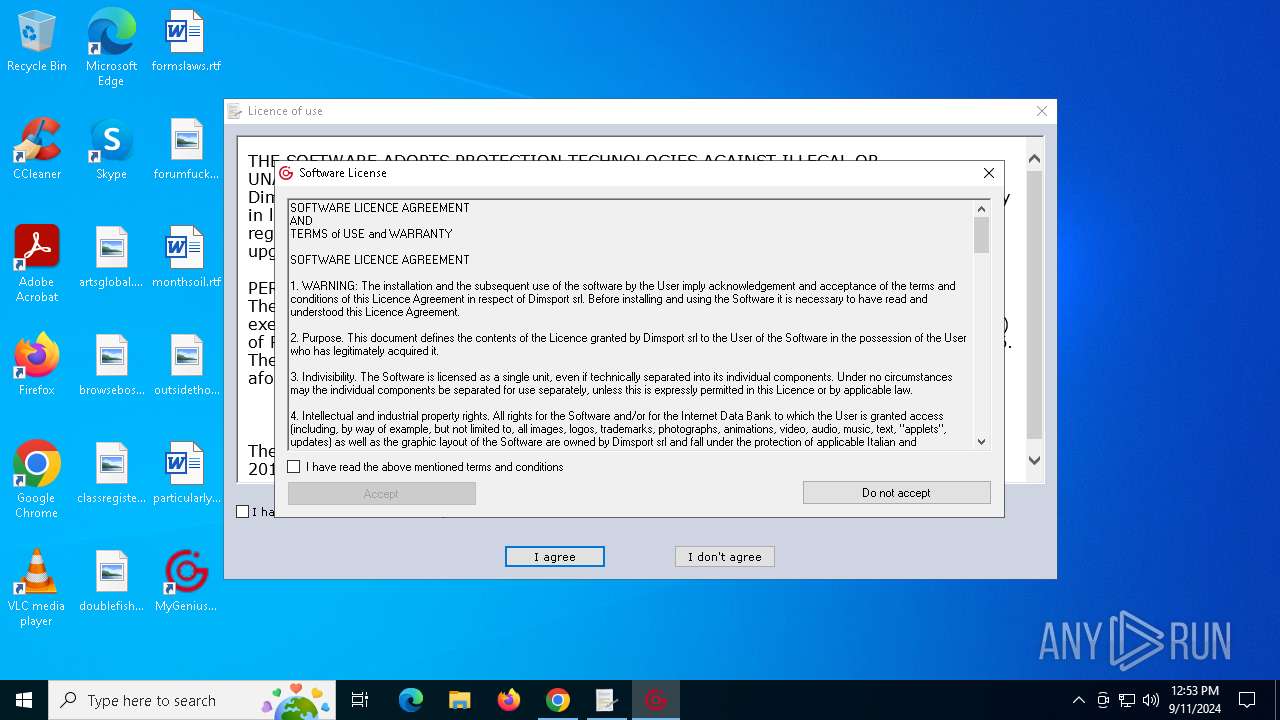
msiexec.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|
MyGeniusClient.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|
MyGeniusClient.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|