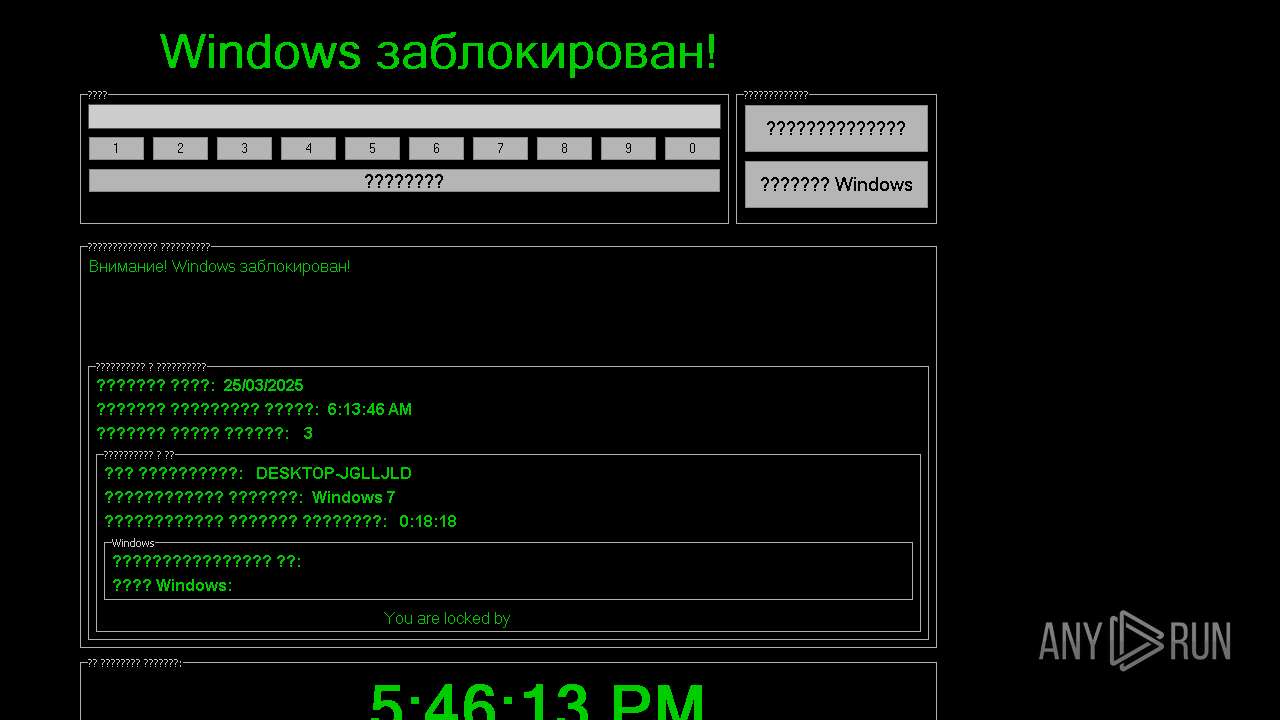
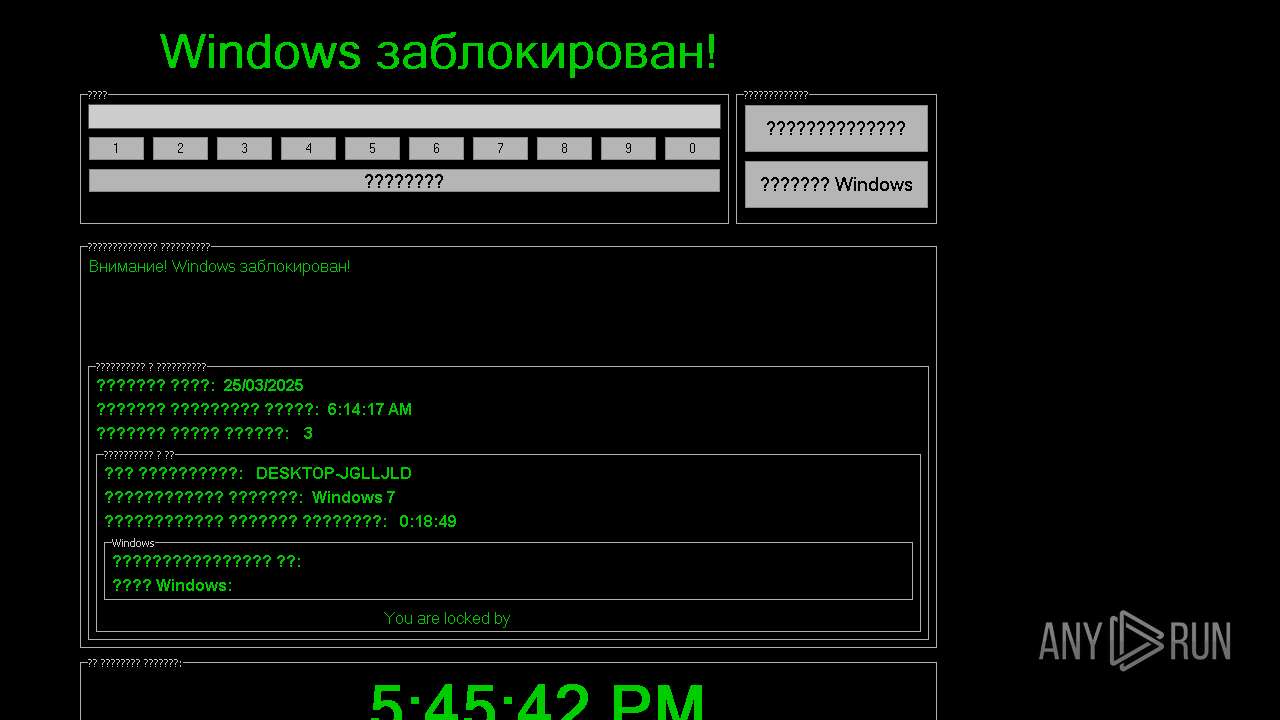
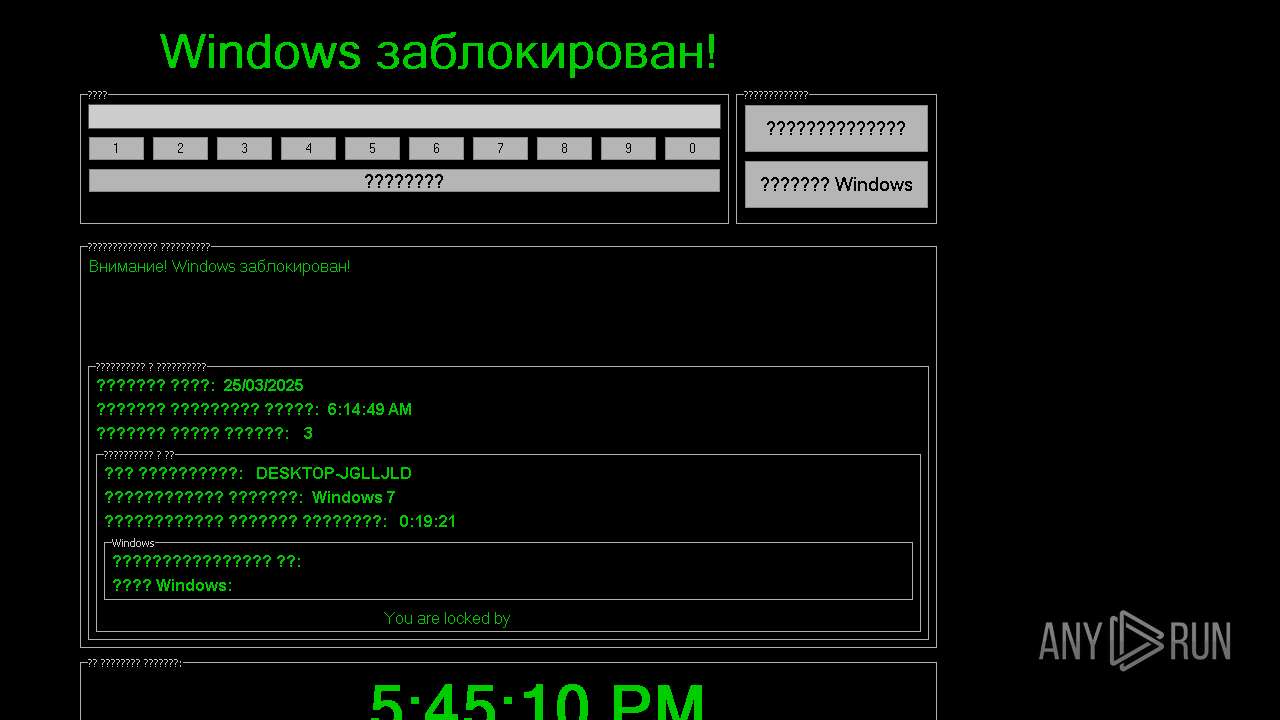
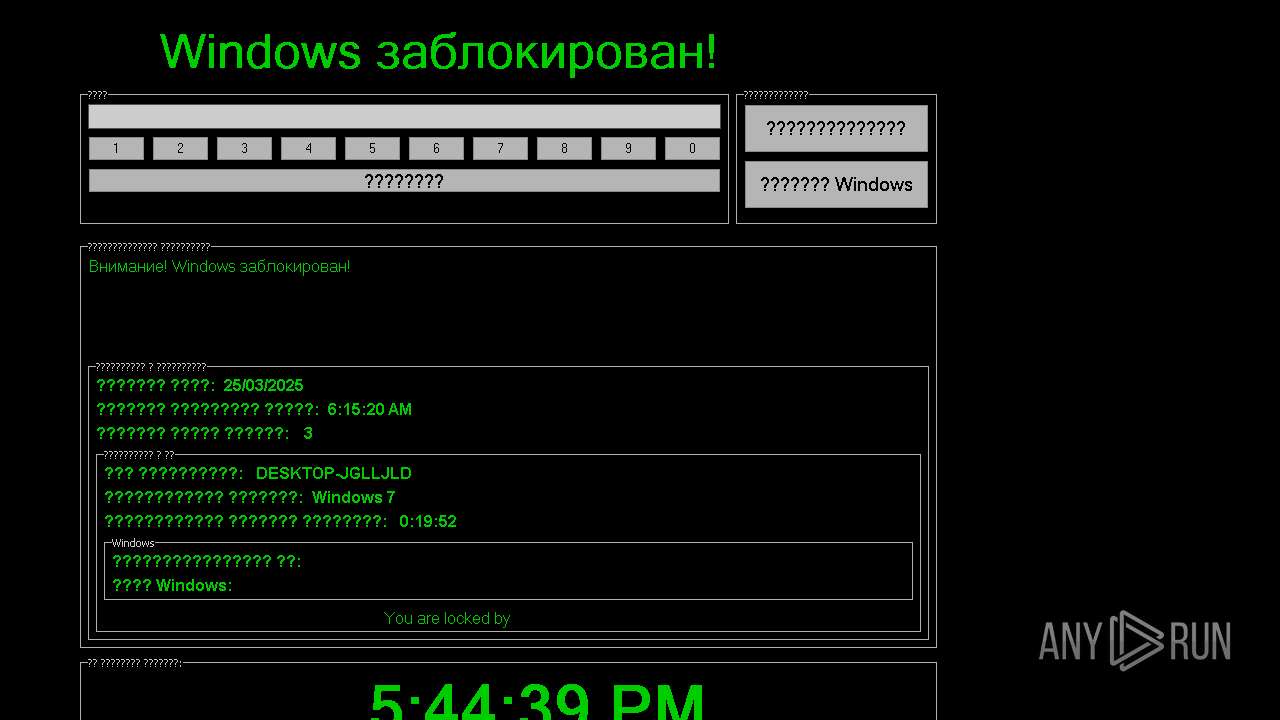
| File name: | 2025-03-25_eb6ead4a32baf0ed948d87eb83d081ff_darkgate_ransomlock |
| Full analysis: | https://app.any.run/tasks/576c0aa4-d483-4e84-8695-b2df9e3d2176 |
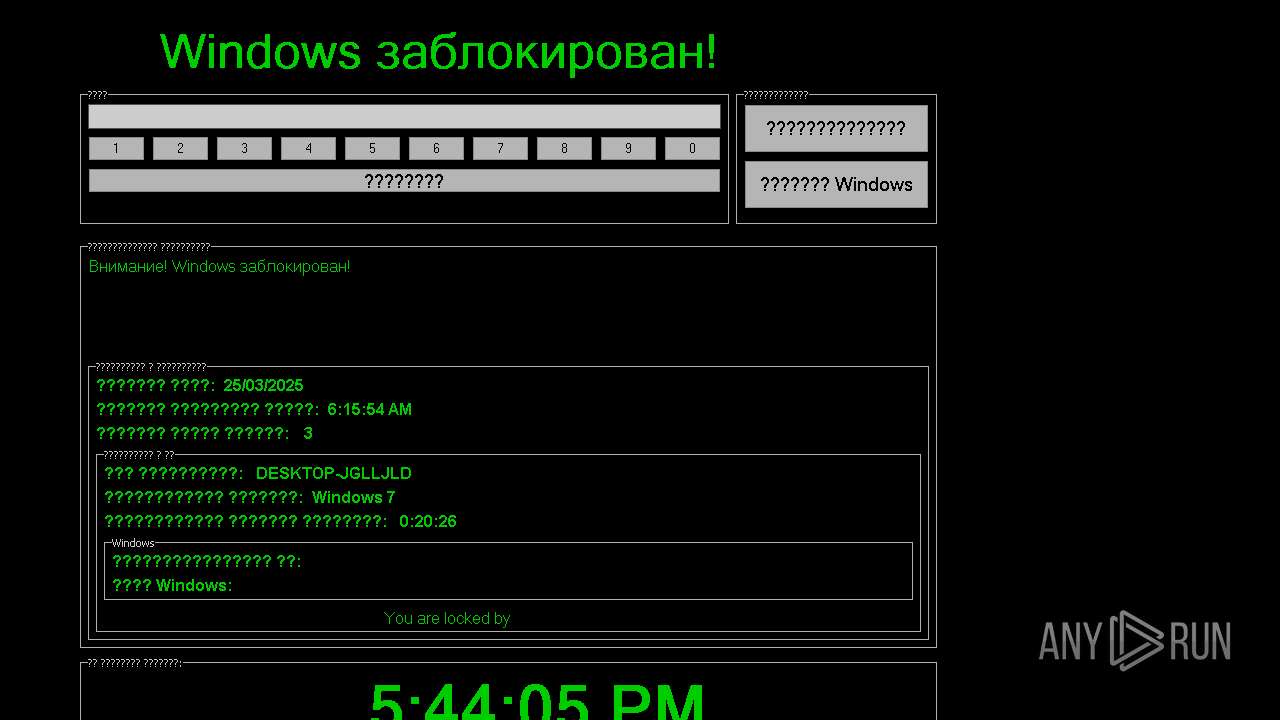
| Verdict: | Malicious activity |
| Analysis date: | March 25, 2025, 06:13:37 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 8 sections |
| MD5: | EB6EAD4A32BAF0ED948D87EB83D081FF |
| SHA1: | 504884473C373780FC9A576E727D54CC66A6270C |
| SHA256: | CDB360D1825942546837AE7CACF940C088FA13F2C95DED6CF17183C7B2B22AAD |
| SSDEEP: | 6144:f9AGg0HKSm76V9R63WN9tIzOdfQYnCMNZbtAhqTqBuweUc/m6Erfc2PZTTz22orq:WGgaW3Q/IzJ+JdeBugc/0zSff3 |
MALICIOUS
Changes the autorun value in the registry
- 2025-03-25_eb6ead4a32baf0ed948d87eb83d081ff_darkgate_ransomlock.exe (PID: 7828)
Changes the login/logoff helper path in the registry
- 2025-03-25_eb6ead4a32baf0ed948d87eb83d081ff_darkgate_ransomlock.exe (PID: 7828)
SUSPICIOUS
There is functionality for taking screenshot (YARA)
- 2025-03-25_eb6ead4a32baf0ed948d87eb83d081ff_darkgate_ransomlock.exe (PID: 7828)
INFO
Checks supported languages
- 2025-03-25_eb6ead4a32baf0ed948d87eb83d081ff_darkgate_ransomlock.exe (PID: 7828)
Compiled with Borland Delphi (YARA)
- 2025-03-25_eb6ead4a32baf0ed948d87eb83d081ff_darkgate_ransomlock.exe (PID: 7828)
- slui.exe (PID: 2320)
Checks proxy server information
- slui.exe (PID: 2320)
Reads the software policy settings
- slui.exe (PID: 2320)
Reads the computer name
- 2025-03-25_eb6ead4a32baf0ed948d87eb83d081ff_darkgate_ransomlock.exe (PID: 7828)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Borland Delphi 7 (68.4) |
|---|---|---|
| .exe | | | Win32 Executable Borland Delphi 6 (27) |
| .exe | | | Win32 Executable Delphi generic (1.4) |
| .scr | | | Windows screen saver (1.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (0.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:19 22:22:17+00:00 |
| ImageFileCharacteristics: | Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 347648 |
| InitializedDataSize: | 97792 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x55d50 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
126
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2320 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7828 | "C:\Users\admin\Desktop\2025-03-25_eb6ead4a32baf0ed948d87eb83d081ff_darkgate_ransomlock.exe" | C:\Users\admin\Desktop\2025-03-25_eb6ead4a32baf0ed948d87eb83d081ff_darkgate_ransomlock.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 8120 | "C:\WINDOWS\SystemApps\Microsoft.Windows.Search_cw5n1h2txyewy\SearchApp.exe" -ServerName:CortanaUI.AppX8z9r6jm96hw4bsbneegw0kyxx296wr9t.mca | C:\Windows\SystemApps\Microsoft.Windows.Search_cw5n1h2txyewy\SearchApp.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Search application Exit code: 2147945463 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
3 382
Read events
3 379
Write events
3
Delete events
0
Modification events
| (PID) Process: | (7828) 2025-03-25_eb6ead4a32baf0ed948d87eb83d081ff_darkgate_ransomlock.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon |
| Operation: | write | Name: | Shell |
Value: C:\Users\admin\Desktop\2025-03-25_eb6ead4a32baf0ed948d87eb83d081ff_darkgate_ransomlock.exe | |||
| (PID) Process: | (7828) 2025-03-25_eb6ead4a32baf0ed948d87eb83d081ff_darkgate_ransomlock.exe | Key: | HKEY_CURRENT_USER\System\CurrentControlSet\Control\SafeBoot |
| Operation: | write | Name: | AlternateShell |
Value: C:\Users\admin\Desktop\2025-03-25_eb6ead4a32baf0ed948d87eb83d081ff_darkgate_ransomlock.exe | |||
| (PID) Process: | (7828) 2025-03-25_eb6ead4a32baf0ed948d87eb83d081ff_darkgate_ransomlock.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | write | Name: | userini |
Value: C:\Users\admin\Desktop\2025-03-25_eb6ead4a32baf0ed948d87eb83d081ff_darkgate_ransomlock.exe | |||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
19
DNS requests
5
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2564 | RUXIMICS.exe | GET | 200 | 23.53.40.176:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | POST | 500 | 40.91.76.224:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | xml | 512 b | whitelisted |
— | — | POST | 500 | 40.91.76.224:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | xml | 512 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2564 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2564 | RUXIMICS.exe | 23.53.40.176:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
7652 | slui.exe | 40.91.76.224:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2320 | slui.exe | 40.91.76.224:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |