| File name: | 215720°.msi |
| Full analysis: | https://app.any.run/tasks/55f9177a-91b3-4fc7-b80c-14ff95c0d24c |
| Verdict: | Malicious activity |
| Analysis date: | July 12, 2025, 17:38:11 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-msi |
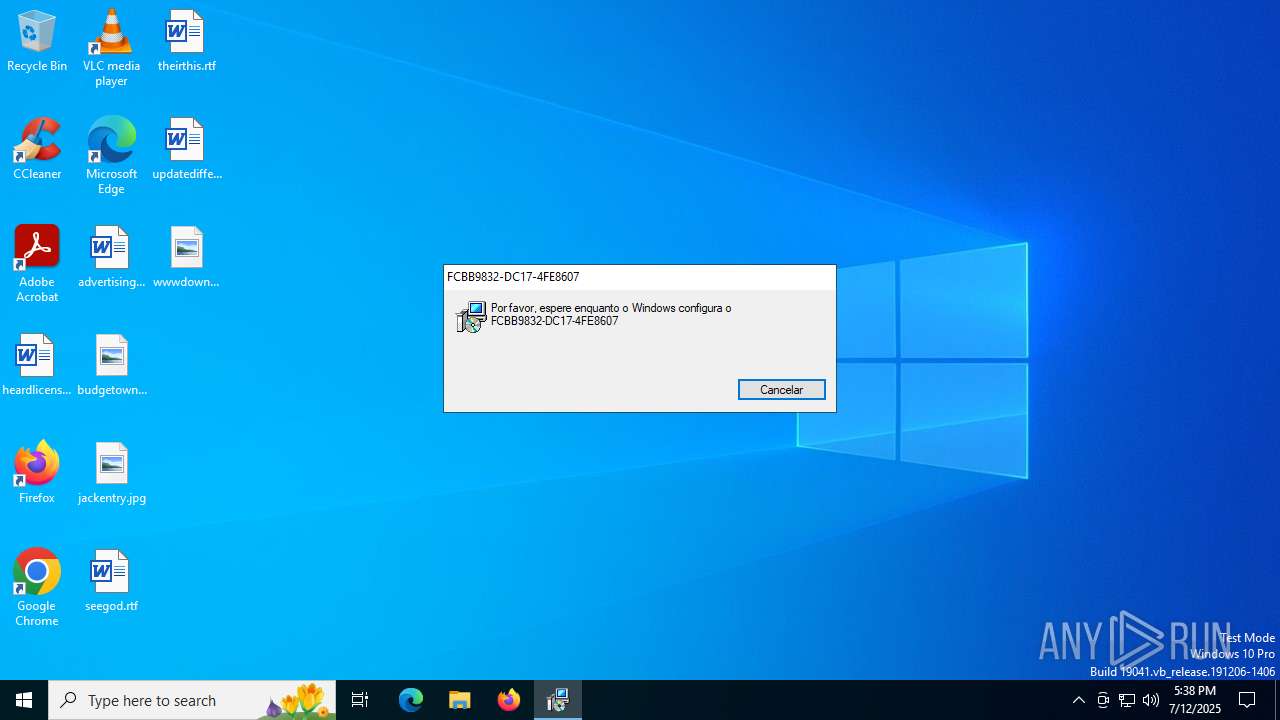
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 10.0, MSI Installer, Security: 0, Code page: 1252, Revision Number: {B089E0A0-6D63-4DE3-A4DB-E2DCD944488A}, Number of Words: 10, Subject: FCBB9832-DC17-4FE8607, Author: CBB9832-DC17-4FE8607, Name of Creating Application: FCBB9832-DC17-4FE8607, Template: ;1046, Comments: FCBB9832-DC17-4FE8607., Title: Installation Database, Keywords: Installer, MSI, Database, Create Time/Date: Fri Jul 11 11:20:02 2025, Last Saved Time/Date: Fri Jul 11 11:20:02 2025, Last Printed: Fri Jul 11 11:20:02 2025, Number of Pages: 450 |
| MD5: | DBB063BCB78E9B5DDD7C32B1498C75DC |
| SHA1: | 00C8300765882EC34DD7AAF7F6CA8316CC3B2B44 |
| SHA256: | CDAAE5CCAC423CE1B5CC018058A03133274B483624655D3D5164200061AF0EB7 |
| SSDEEP: | 98304:Y9ILo1kF8/t6PYAAcJYVDjFCRlWcDYEEWi: |
MALICIOUS
Changes the autorun value in the registry
- f4ZoAgmlYd7Vº.exe (PID: 4880)
SUSPICIOUS
Executes as Windows Service
- VSSVC.exe (PID: 6720)
Detects AdvancedInstaller (YARA)
- msiexec.exe (PID: 7104)
- msiexec.exe (PID: 1356)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 1356)
Application launched itself
- msiexec.exe (PID: 1356)
- f4ZoAgmlYd7Vº.exe (PID: 4880)
- f4ZoAgmlYd7Vº.exe (PID: 6412)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 536)
Connects to the server without a host name
- msiexec.exe (PID: 536)
- f4ZoAgmlYd7Vº.exe (PID: 4880)
Process drops legitimate windows executable
- msiexec.exe (PID: 536)
Likely accesses (executes) a file from the Public directory
- f4ZoAgmlYd7Vº.exe (PID: 1976)
- f4ZoAgmlYd7Vº.exe (PID: 4880)
- f4ZoAgmlYd7Vº.exe (PID: 5480)
- f4ZoAgmlYd7Vº.exe (PID: 6412)
Reads the date of Windows installation
- msiexec.exe (PID: 536)
INFO
An automatically generated document
- msiexec.exe (PID: 7104)
Checks supported languages
- msiexec.exe (PID: 1356)
- msiexec.exe (PID: 6664)
- msiexec.exe (PID: 536)
- f4ZoAgmlYd7Vº.exe (PID: 4880)
- f4ZoAgmlYd7Vº.exe (PID: 1976)
- f4ZoAgmlYd7Vº.exe (PID: 5480)
- f4ZoAgmlYd7Vº.exe (PID: 6412)
Create files in a temporary directory
- msiexec.exe (PID: 7104)
Reads the computer name
- msiexec.exe (PID: 1356)
- msiexec.exe (PID: 6664)
- msiexec.exe (PID: 536)
- f4ZoAgmlYd7Vº.exe (PID: 4880)
- f4ZoAgmlYd7Vº.exe (PID: 6412)
Manages system restore points
- SrTasks.exe (PID: 1132)
Reads Environment values
- msiexec.exe (PID: 6664)
- msiexec.exe (PID: 536)
Executable content was dropped or overwritten
- msiexec.exe (PID: 1356)
- msiexec.exe (PID: 536)
The sample compiled with english language support
- msiexec.exe (PID: 1356)
- msiexec.exe (PID: 536)
Checks proxy server information
- msiexec.exe (PID: 536)
- slui.exe (PID: 3788)
Creates files or folders in the user directory
- msiexec.exe (PID: 536)
Process checks computer location settings
- msiexec.exe (PID: 536)
Launching a file from a Registry key
- f4ZoAgmlYd7Vº.exe (PID: 4880)
Manual execution by a user
- f4ZoAgmlYd7Vº.exe (PID: 6412)
Reads the software policy settings
- slui.exe (PID: 3788)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Windows Installer (88.6) |
|---|---|---|
| .mst | | | Windows SDK Setup Transform Script (10) |
| .msi | | | Microsoft Installer (100) |
EXIF
FlashPix
| Security: | None |
|---|---|
| CodePage: | Windows Latin 1 (Western European) |
| RevisionNumber: | {B089E0A0-6D63-4DE3-A4DB-E2DCD944488A} |
| Words: | 10 |
| Subject: | FCBB9832-DC17-4FE8607 |
| Author: | CBB9832-DC17-4FE8607 |
| LastModifiedBy: | - |
| Software: | FCBB9832-DC17-4FE8607 |
| Template: | ;1046 |
| Comments: | FCBB9832-DC17-4FE8607. |
| Title: | Installation Database |
| Keywords: | Installer, MSI, Database |
| CreateDate: | 2025:07:11 11:20:02 |
| ModifyDate: | 2025:07:11 11:20:02 |
| LastPrinted: | 2025:07:11 11:20:02 |
| Pages: | 450 |
Total processes
151
Monitored processes
13
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 536 | C:\Windows\System32\MsiExec.exe -Embedding CF774B4FC1763C0FE4F36268606B5463 | C:\Windows\System32\msiexec.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1132 | C:\WINDOWS\system32\srtasks.exe ExecuteScopeRestorePoint /WaitForRestorePoint:11 | C:\Windows\System32\SrTasks.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Windows System Protection background tasks. Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1356 | C:\WINDOWS\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1948 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | SrTasks.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1976 | C:\Users\Public\f4ZoAgmlYd7V\f4ZoAgmlYd7Vº.exe --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=138.0.7204.97 --initial-client-data=0x178,0x17c,0x180,0x148,0x184,0x7536741c,0x75367428,0x75367434 | C:\Users\Public\f4ZoAgmlYd7V\f4ZoAgmlYd7Vº.exe | — | f4ZoAgmlYd7Vº.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 138.0.7204.97 Modules
| |||||||||||||||
| 3564 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3788 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4880 | "C:\Users\Public\f4ZoAgmlYd7V\f4ZoAgmlYd7Vº.exe" | C:\Users\Public\f4ZoAgmlYd7V\f4ZoAgmlYd7Vº.exe | msiexec.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 138.0.7204.97 Modules
| |||||||||||||||
| 5480 | C:\Users\Public\f4ZoAgmlYd7V\f4ZoAgmlYd7Vº.exe --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=138.0.7204.97 --initial-client-data=0x17c,0x180,0x184,0x158,0x188,0x7536741c,0x75367428,0x75367434 | C:\Users\Public\f4ZoAgmlYd7V\f4ZoAgmlYd7Vº.exe | — | f4ZoAgmlYd7Vº.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 138.0.7204.97 Modules
| |||||||||||||||
| 6412 | C:\Users\Public\f4ZoAgmlYd7V\f4ZoAgmlYd7Vº.exe | C:\Users\Public\f4ZoAgmlYd7V\f4ZoAgmlYd7Vº.exe | — | explorer.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 138.0.7204.97 Modules
| |||||||||||||||
Total events
7 070
Read events
6 861
Write events
191
Delete events
18
Modification events
| (PID) Process: | (1356) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 480000000000000053828CBF53F3DB014C05000034090000D50700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1356) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 480000000000000053828CBF53F3DB014C05000034090000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1356) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Leave) |
Value: 48000000000000005A00B5BF53F3DB014C05000034090000D20700000100000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1356) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Enter) |
Value: 48000000000000005A00B5BF53F3DB014C05000034090000D10700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1356) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Leave) |
Value: 48000000000000005A00B5BF53F3DB014C05000034090000D10700000100000000000000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1356) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 480000000000000057C7B9BF53F3DB014C05000034090000D00700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1356) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 11 | |||
| (PID) Process: | (1356) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 48000000000000006A5401C053F3DB014C05000034090000D30700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1356) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4800000000000000F51B06C053F3DB014C0500009C120000E8030000010000000000000000000000EE1BBD0470C16E488492F474E02FCBAE00000000000000000000000000000000 | |||
| (PID) Process: | (6720) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4800000000000000160212C053F3DB01401A0000001A0000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
27
Suspicious files
91
Text files
12
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1356 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 536 | msiexec.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\RR3E01RZ\malucobeleza[1].wav | — | |
MD5:— | SHA256:— | |||
| 536 | msiexec.exe | C:\Users\Public\f4ZoAgmlYd7V_f4ZoAgmlYd7V_f4ZoAgmlYd7V.zip | — | |
MD5:— | SHA256:— | |||
| 1356 | msiexec.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{04bd1bee-c170-486e-8492-f474e02fcbae}_OnDiskSnapshotProp | binary | |
MD5:726F0E1508F55A54C90247BD481142DA | SHA256:E9447704A495B290CAA7AFF4B4944C72EEF05EDF79345A24AC5815B28E01986F | |||
| 1356 | msiexec.exe | C:\System Volume Information\SPP\snapshot-2 | binary | |
MD5:726F0E1508F55A54C90247BD481142DA | SHA256:E9447704A495B290CAA7AFF4B4944C72EEF05EDF79345A24AC5815B28E01986F | |||
| 1356 | msiexec.exe | C:\Windows\Installer\MSI7EB7.tmp | executable | |
MD5:421643EE7BB89E6DF092BC4B18A40FF8 | SHA256:D6B89FD5A95071E7B144D8BEDCB09B694E9CD14BFBFAFB782B17CF8413EAC6DA | |||
| 1356 | msiexec.exe | C:\Windows\Installer\MSI7E68.tmp | executable | |
MD5:421643EE7BB89E6DF092BC4B18A40FF8 | SHA256:D6B89FD5A95071E7B144D8BEDCB09B694E9CD14BFBFAFB782B17CF8413EAC6DA | |||
| 1356 | msiexec.exe | C:\Windows\Installer\MSI7EE7.tmp | executable | |
MD5:421643EE7BB89E6DF092BC4B18A40FF8 | SHA256:D6B89FD5A95071E7B144D8BEDCB09B694E9CD14BFBFAFB782B17CF8413EAC6DA | |||
| 1356 | msiexec.exe | C:\Windows\Installer\MSI7DAC.tmp | executable | |
MD5:421643EE7BB89E6DF092BC4B18A40FF8 | SHA256:D6B89FD5A95071E7B144D8BEDCB09B694E9CD14BFBFAFB782B17CF8413EAC6DA | |||
| 536 | msiexec.exe | C:\Users\Public\f4ZoAgmlYd7V\138.0.7204.97\icudtl.dat | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
31
DNS requests
17
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1268 | svchost.exe | GET | 200 | 2.16.241.12:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2520 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
536 | msiexec.exe | GET | 200 | 185.247.117.128:80 | http://185.247.117.128/14840646743032/malucobeleza.wav | unknown | — | — | unknown |
6388 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
4880 | f4ZoAgmlYd7Vº.exe | POST | 200 | 181.224.24.202:80 | http://181.224.24.202/14840646743032MM/14840646743032.php | unknown | — | — | unknown |
2940 | svchost.exe | GET | 200 | 72.246.169.163:80 | http://x1.c.lencr.org/ | unknown | — | — | whitelisted |
6388 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5944 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6376 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1268 | svchost.exe | 20.44.239.154:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | SG | whitelisted |
1268 | svchost.exe | 2.16.241.12:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1268 | svchost.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
1984 | svchost.exe | 184.28.89.167:443 | go.microsoft.com | AKAMAI-AS | US | whitelisted |
2520 | svchost.exe | 20.190.159.73:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
536 | msiexec.exe | Misc activity | ET INFO Observed UA-CPU Header |