| download: | DatairPDF5019.exe |
| Full analysis: | https://app.any.run/tasks/f5367428-dd08-4b6e-b6e7-05a0127dd918 |
| Verdict: | Malicious activity |
| Analysis date: | October 14, 2019, 19:53:44 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 97283EB481B0757C193A140D089B9A80 |
| SHA1: | FF2427C01E6E582A11436869ECA379DD2445D1E2 |
| SHA256: | CDA7A7F6CDE61F1B019DF39DA89FA0E39B230F6C1172858B689EECA2428F5CBD |
| SSDEEP: | 196608:8RgZcdq+DY6uLV5gTr+5XD2zXSvB+ZQc2sGTFxr97+O7ToQmBTzBVcTfEAVo9ExN:8hq+DYDXire/sGz57UQuzBVr9E9l |
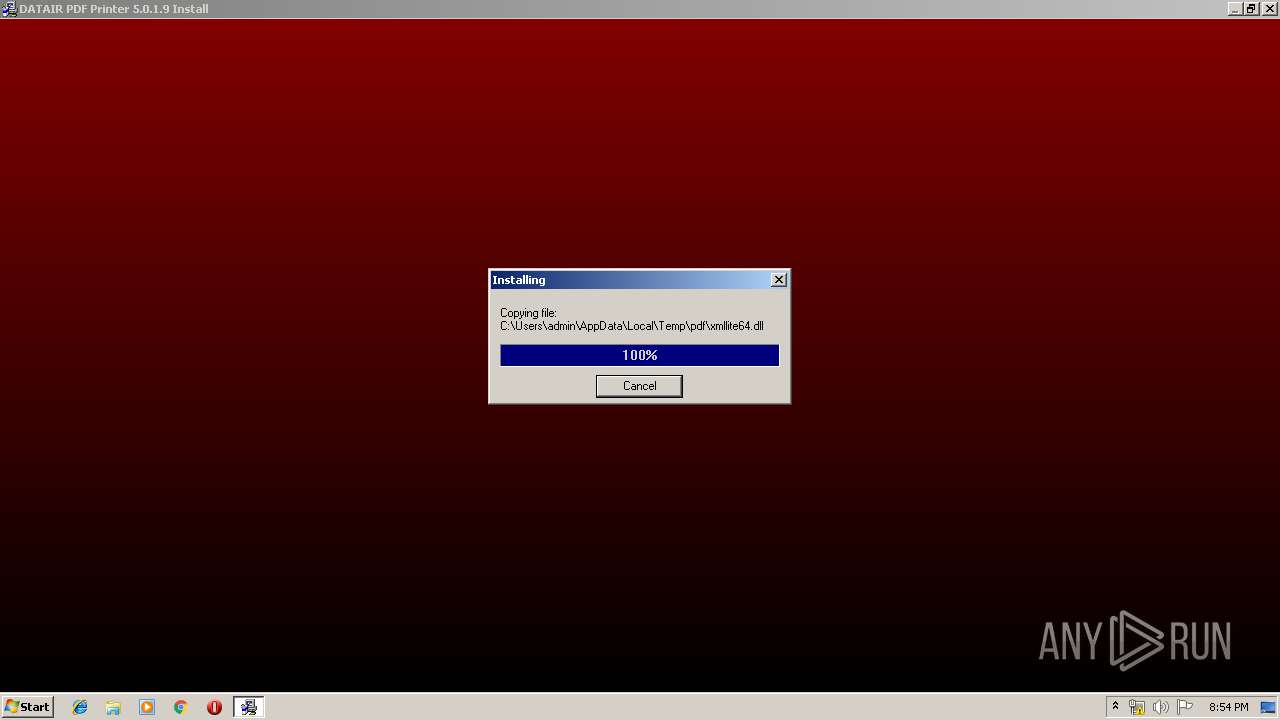
MALICIOUS
Loads dropped or rewritten executable
- DatairPDF5019.exe (PID: 3036)
- svchost.exe (PID: 840)
- Install.exe (PID: 2260)
- spoolsv.exe (PID: 1204)
Application was dropped or rewritten from another process
- Install.exe (PID: 2260)
SUSPICIOUS
Executable content was dropped or overwritten
- DatairPDF5019.exe (PID: 3036)
- Install.exe (PID: 2260)
- spoolsv.exe (PID: 1204)
Creates files in the Windows directory
- DatairPDF5019.exe (PID: 3036)
- Install.exe (PID: 2260)
- DrvInst.exe (PID: 2432)
- spoolsv.exe (PID: 1204)
Executed via COM
- DrvInst.exe (PID: 2432)
Removes files from Windows directory
- spoolsv.exe (PID: 1204)
- DrvInst.exe (PID: 2432)
- Install.exe (PID: 2260)
Creates COM task schedule object
- Install.exe (PID: 2260)
- spoolsv.exe (PID: 1204)
Creates files in the program directory
- Install.exe (PID: 2260)
Creates files in the driver directory
- DrvInst.exe (PID: 2432)
Executes scripts
- spoolsv.exe (PID: 1204)
Searches for installed software
- svchost.exe (PID: 840)
INFO
Dropped object may contain Bitcoin addresses
- DatairPDF5019.exe (PID: 3036)
- Install.exe (PID: 2260)
- spoolsv.exe (PID: 1204)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Wise Installer executable (91.7) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (5.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (1.2) |
| .exe | | | Win32 Executable (generic) (0.8) |
| .exe | | | Generic Win/DOS Executable (0.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2001:08:13 19:13:38+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 8704 |
| InitializedDataSize: | 5632 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x21af |
| OSVersion: | 4 |
| ImageVersion: | 4 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.20.0.0 |
| ProductVersionNumber: | 1.20.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows 16-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | DATAIR Employee Benefit Systems, Inc. |
| FileDescription: | DATAIR Pension Reporter |
| FileVersion: | 1.2 |
| LegalCopyright: | (c) 1995-2006 DATAIR |
Total processes
40
Monitored processes
6
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 776 | "C:\Users\admin\AppData\Local\Temp\DatairPDF5019.exe" | C:\Users\admin\AppData\Local\Temp\DatairPDF5019.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 840 | C:\Windows\System32\svchost.exe -k LocalSystemNetworkRestricted | C:\Windows\System32\svchost.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1204 | C:\Windows\System32\spoolsv.exe | C:\Windows\System32\spoolsv.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Spooler SubSystem App Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2260 | "C:\Users\admin\AppData\Local\Temp\pdf\Install.exe" /S | C:\Users\admin\AppData\Local\Temp\pdf\Install.exe | DatairPDF5019.exe | ||||||||||||
User: admin Company: Amyuni Technologies Integrity Level: HIGH Description: Amyuni PDF Converter Installer Exit code: 0 Version: 1.0.0.1 Modules
| |||||||||||||||
| 2432 | DrvInst.exe "4" "8" "C:\Users\admin\AppData\Local\Temp\{729b2705-18c8-5023-cbc4-5202cc45a34c}\amyuni.inf" "0" "6a49fb0a3" "000003E4" "WinSta0\Default" "000005A4" "208" "c:\users\admin\appdata\local\temp\pdf" | C:\Windows\system32\DrvInst.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3036 | "C:\Users\admin\AppData\Local\Temp\DatairPDF5019.exe" | C:\Users\admin\AppData\Local\Temp\DatairPDF5019.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
1 167
Read events
846
Write events
321
Delete events
0
Modification events
| (PID) Process: | (3036) DatairPDF5019.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3036) DatairPDF5019.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2260) Install.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\TypeLib\{4856F14A-7516-11D3-BBE5-D53DCBD65107}\5.0 |
| Operation: | write | Name: | |
Value: Amyuni Document Converter ActiveX | |||
| (PID) Process: | (2260) Install.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\TypeLib\{4856F14A-7516-11D3-BBE5-D53DCBD65107}\5.0\FLAGS |
| Operation: | write | Name: | |
Value: 2 | |||
| (PID) Process: | (2260) Install.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\TypeLib\{4856F14A-7516-11D3-BBE5-D53DCBD65107}\5.0\0\win32 |
| Operation: | write | Name: | |
Value: C:\Windows\system32\cdintf500.dll | |||
| (PID) Process: | (2260) Install.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\TypeLib\{4856F14A-7516-11D3-BBE5-D53DCBD65107}\5.0\HELPDIR |
| Operation: | write | Name: | |
Value: | |||
| (PID) Process: | (2260) Install.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Interface\{68B3426D-7559-11D3-BBE5-D53DCBD65107} |
| Operation: | write | Name: | |
Value: ICDIntfEx | |||
| (PID) Process: | (2260) Install.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Interface\{68B3426D-7559-11D3-BBE5-D53DCBD65107}\ProxyStubClsid |
| Operation: | write | Name: | |
Value: {00020420-0000-0000-C000-000000000046} | |||
| (PID) Process: | (2260) Install.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Interface\{68B3426D-7559-11D3-BBE5-D53DCBD65107}\ProxyStubClsid32 |
| Operation: | write | Name: | |
Value: {00020420-0000-0000-C000-000000000046} | |||
| (PID) Process: | (2260) Install.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Interface\{68B3426D-7559-11D3-BBE5-D53DCBD65107}\TypeLib |
| Operation: | write | Name: | |
Value: {4856F14A-7516-11D3-BBE5-D53DCBD65107} | |||
Executable files
17
Suspicious files
7
Text files
20
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3036 | DatairPDF5019.exe | C:\Users\admin\AppData\Local\Temp\pdf\~GLH0000.TMP | — | |
MD5:— | SHA256:— | |||
| 3036 | DatairPDF5019.exe | C:\Users\admin\AppData\Local\Temp\pdf\~GLH0001.TMP | — | |
MD5:— | SHA256:— | |||
| 3036 | DatairPDF5019.exe | C:\Users\admin\AppData\Local\Temp\pdf\~GLH0002.TMP | — | |
MD5:— | SHA256:— | |||
| 3036 | DatairPDF5019.exe | C:\Users\admin\AppData\Local\Temp\pdf\~GLH0003.TMP | — | |
MD5:— | SHA256:— | |||
| 3036 | DatairPDF5019.exe | C:\Users\admin\AppData\Local\Temp\pdf\~GLH0004.TMP | — | |
MD5:— | SHA256:— | |||
| 3036 | DatairPDF5019.exe | C:\Users\admin\AppData\Local\Temp\pdf\~GLH0005.TMP | — | |
MD5:— | SHA256:— | |||
| 3036 | DatairPDF5019.exe | C:\Users\admin\AppData\Local\Temp\pdf\~GLH0006.TMP | — | |
MD5:— | SHA256:— | |||
| 3036 | DatairPDF5019.exe | C:\Users\admin\AppData\Local\Temp\pdf\~GLH0007.TMP | — | |
MD5:— | SHA256:— | |||
| 3036 | DatairPDF5019.exe | C:\Users\admin\AppData\Local\Temp\pdf\~GLH0008.TMP | — | |
MD5:— | SHA256:— | |||
| 3036 | DatairPDF5019.exe | C:\Users\admin\AppData\Local\Temp\pdf\~GLH0009.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report