| File name: | PCPlayer.exe |
| Full analysis: | https://app.any.run/tasks/cbac6c73-12d5-4d9f-b4eb-da8620ee8254 |
| Verdict: | Malicious activity |
| Analysis date: | February 17, 2020, 22:08:41 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | FE6572BA7628C1B2E347BA02B782D0E4 |
| SHA1: | 3F995F914C5430119483C66DB8D74F4137F25DA5 |
| SHA256: | CD8964770837B0F2EB168B2DD2E326789238EA95C802B263407800C5B9AE7FA0 |
| SSDEEP: | 196608:AR9+UpjWFIw/G2MYoxWKzbV5M588Mi/sSqqQrDWnbRaTSJ/:YppqkWDqdTjFDWnbSSd |
MALICIOUS
Registers / Runs the DLL via REGSVR32.EXE
- PCPlayer.tmp (PID: 3852)
Loads dropped or rewritten executable
- regsvr32.exe (PID: 3836)
- regsvr32.exe (PID: 3756)
- regsvr32.exe (PID: 3472)
- explorer.exe (PID: 372)
- SPUpDateServer.exe (PID: 3592)
- iexplore.exe (PID: 2636)
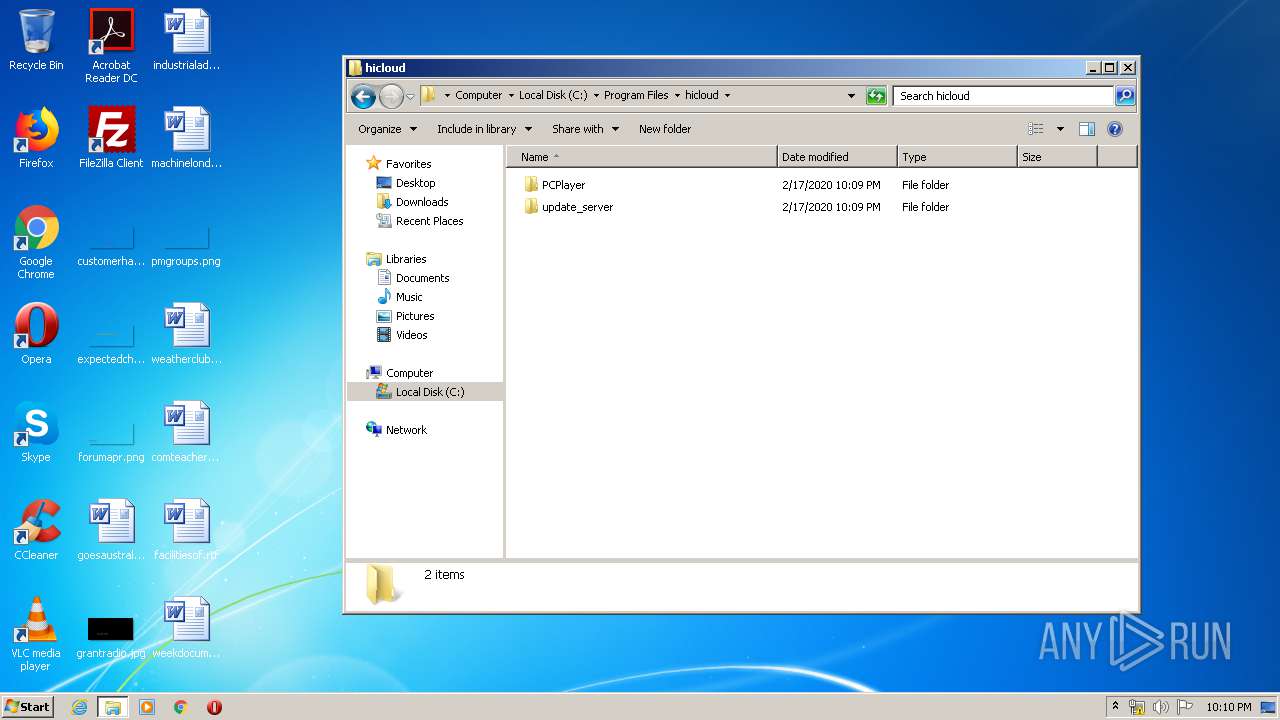
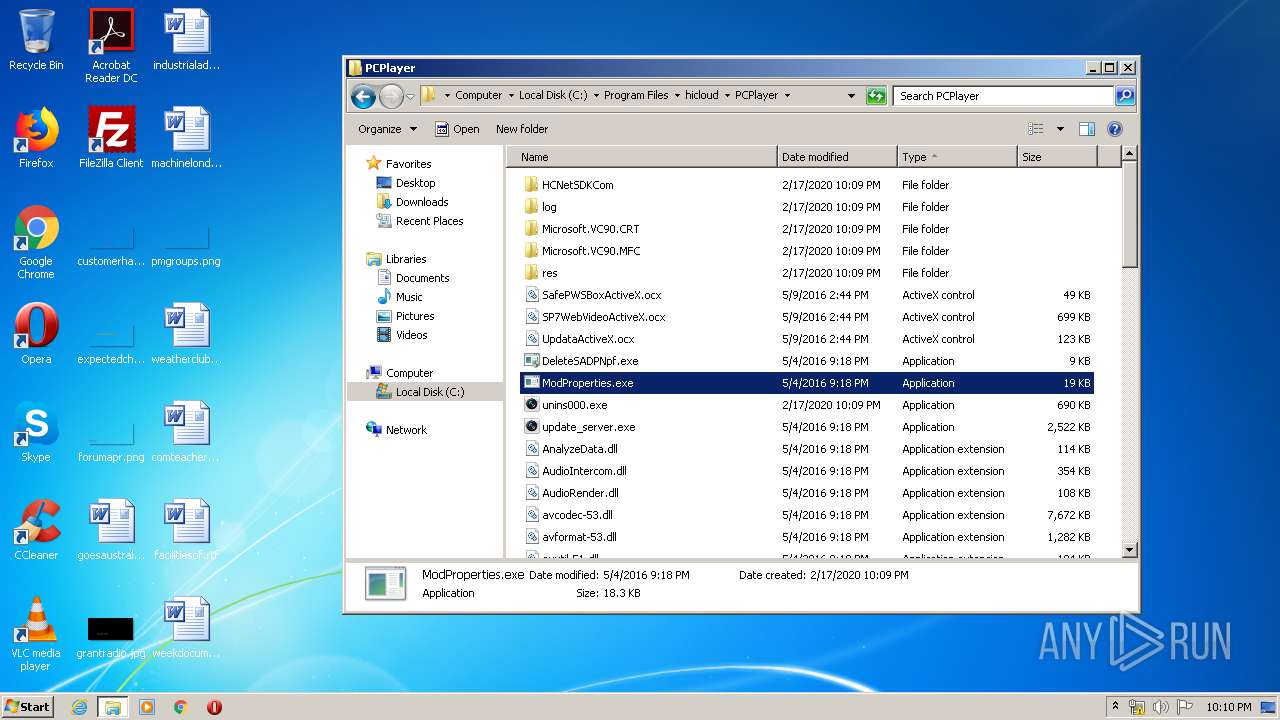
Application was dropped or rewritten from another process
- update_server.exe (PID: 2380)
- SPUpDateServer.exe (PID: 3592)
- startUp.exe (PID: 3020)
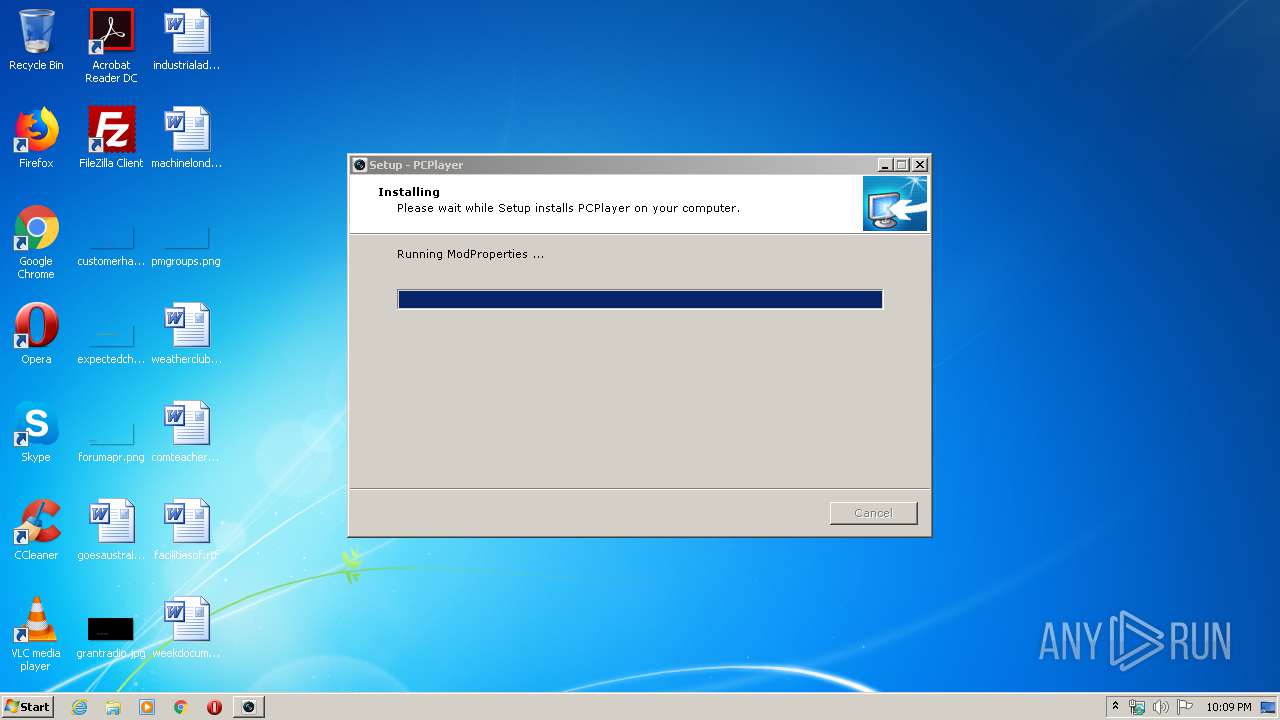
- ModProperties.exe (PID: 3000)
- ModProperties.exe (PID: 2876)
- DeleteSADPNpf.exe (PID: 3888)
- ModProperties.exe (PID: 1948)
Changes the autorun value in the registry
- update_server.tmp (PID: 2112)
SUSPICIOUS
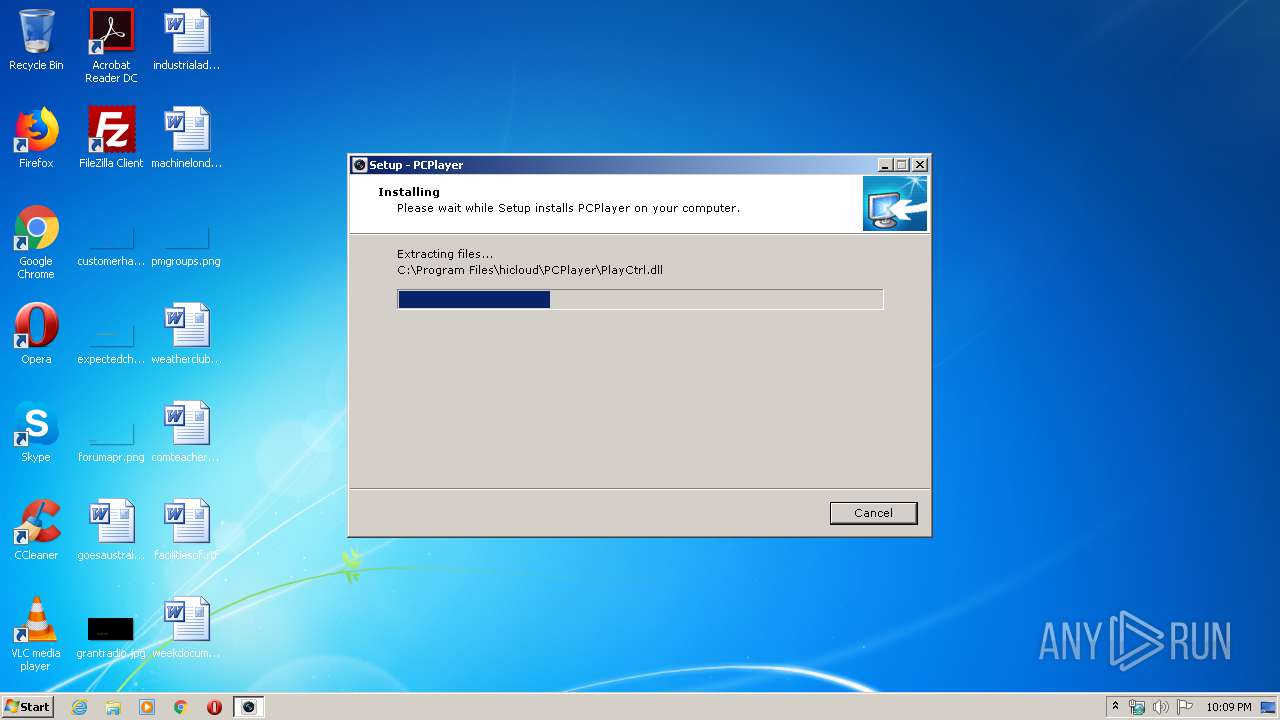
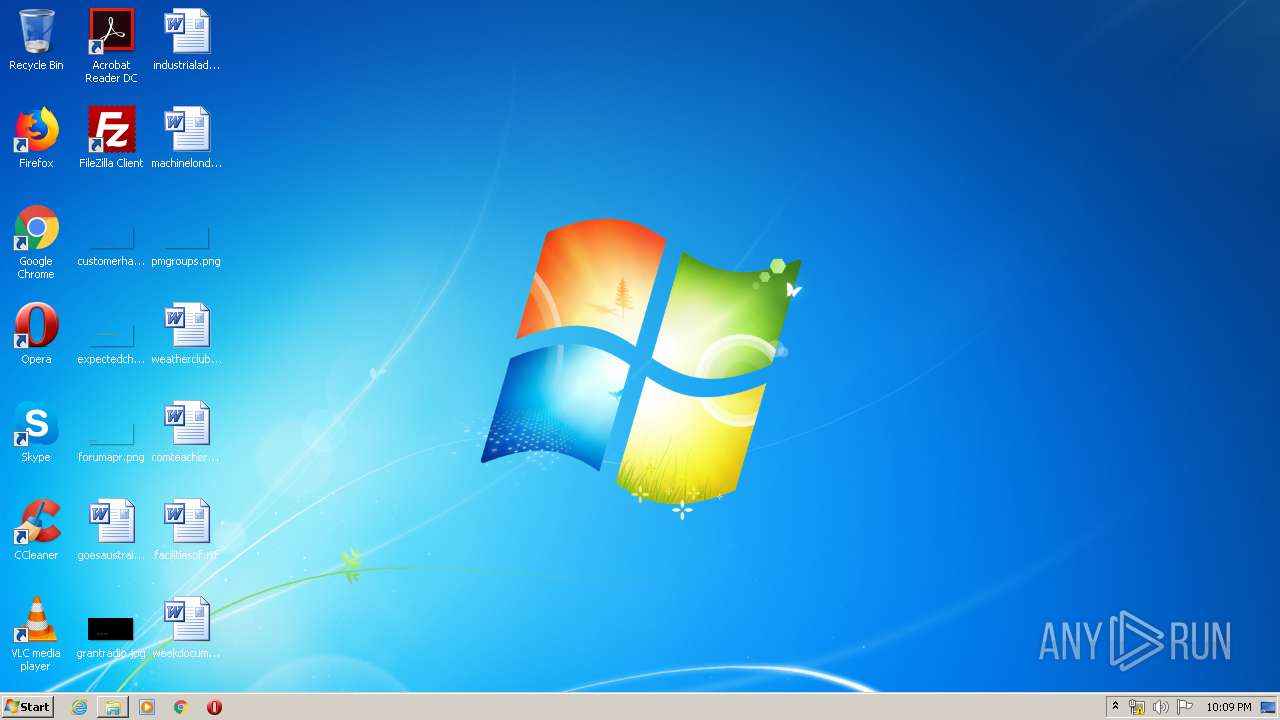
Executable content was dropped or overwritten
- PCPlayer.exe (PID: 2392)
- PCPlayer.exe (PID: 3804)
- PCPlayer.tmp (PID: 3852)
- update_server.tmp (PID: 2112)
- update_server.exe (PID: 2380)
Creates files in the Windows directory
- regsvr32.exe (PID: 3836)
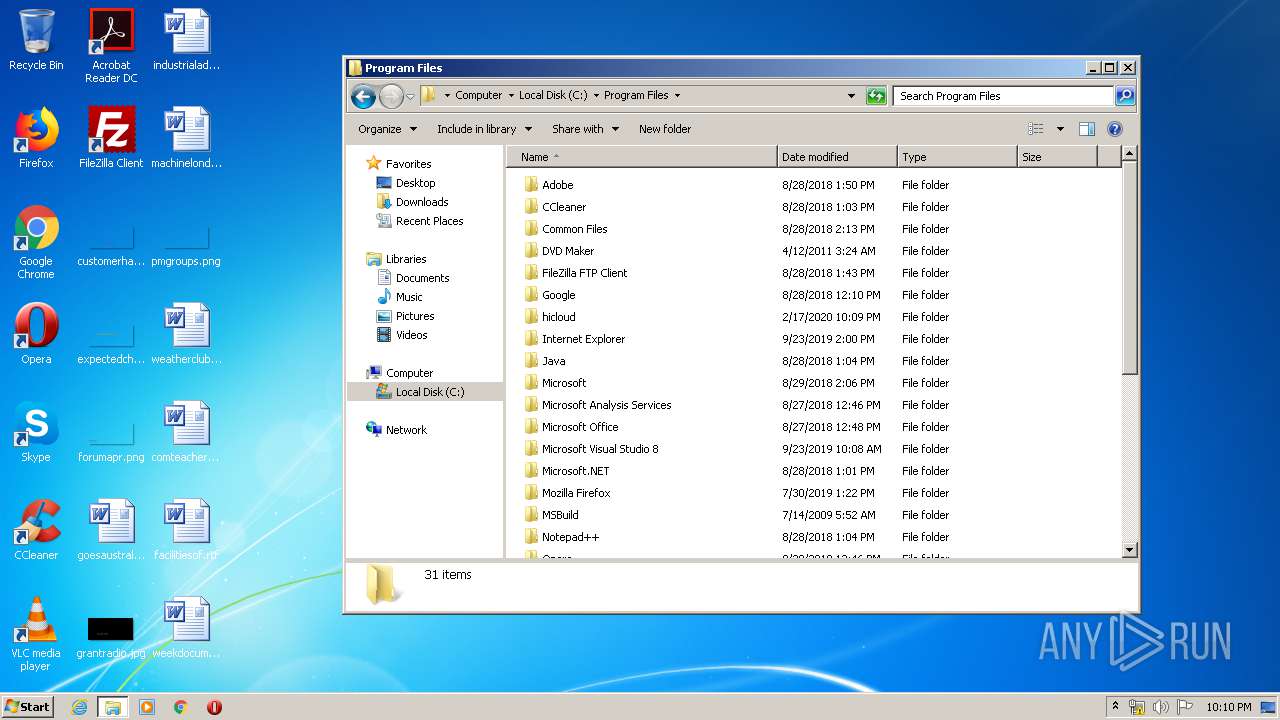
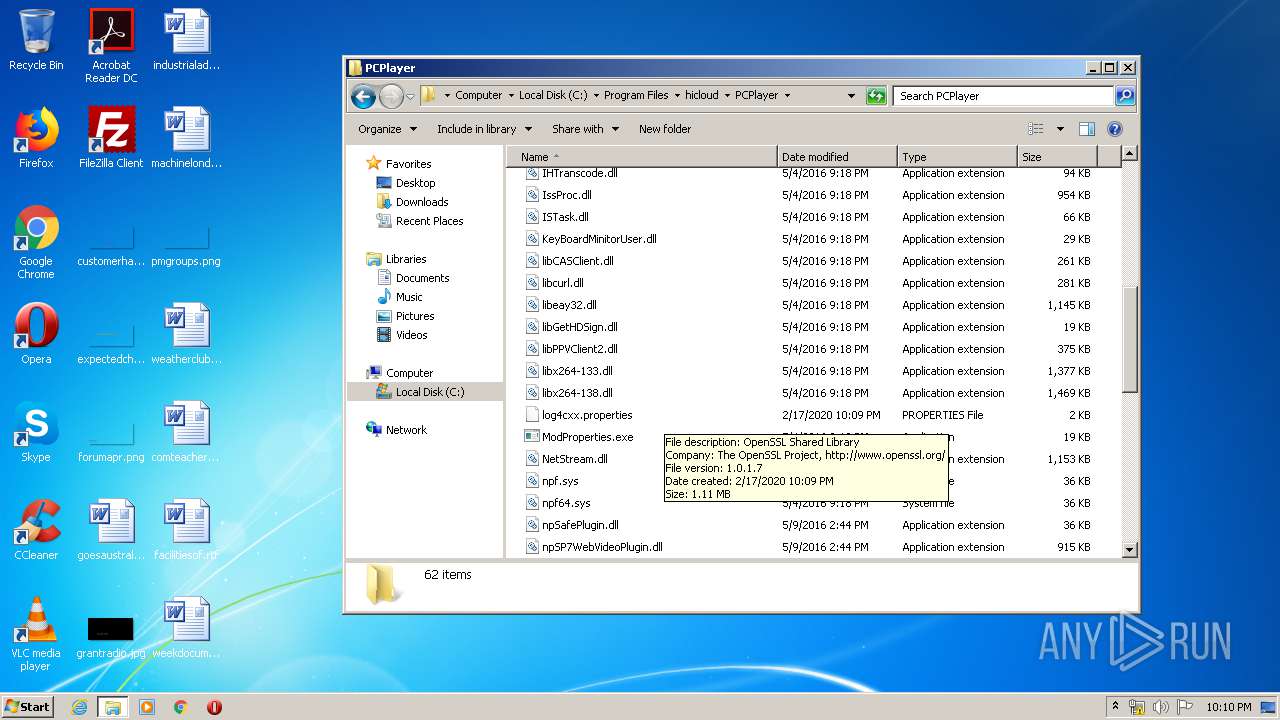
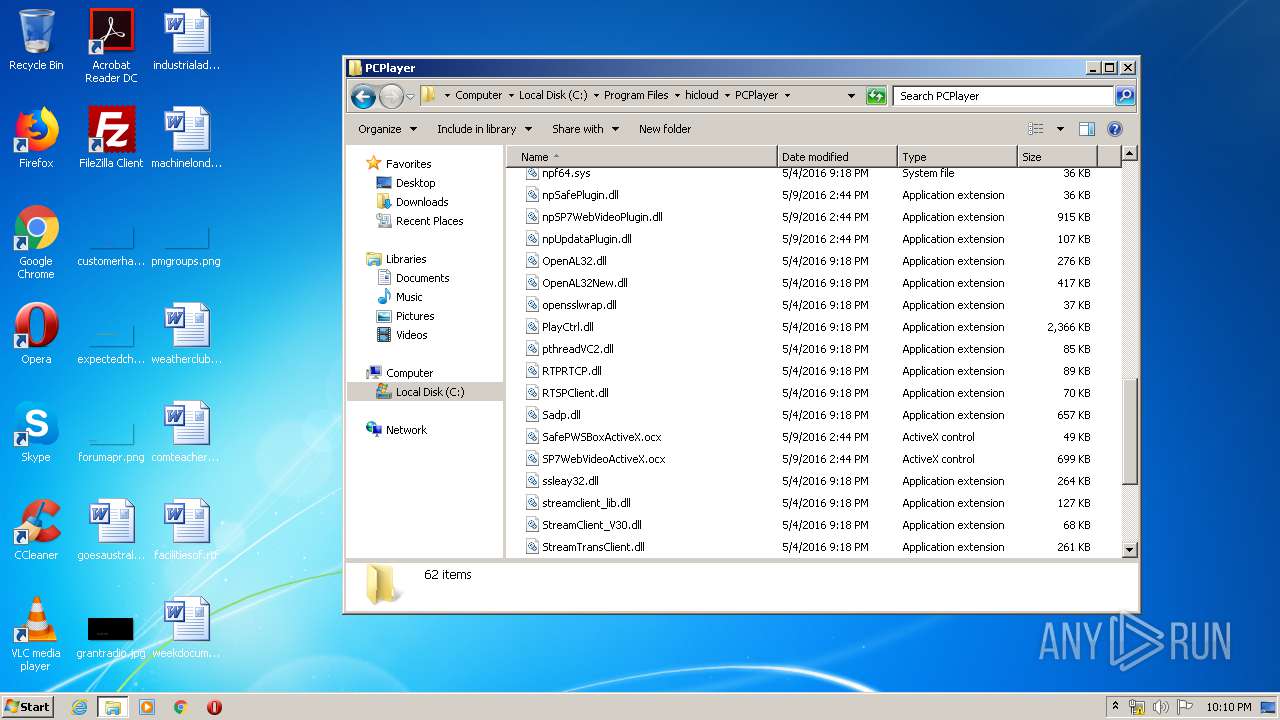
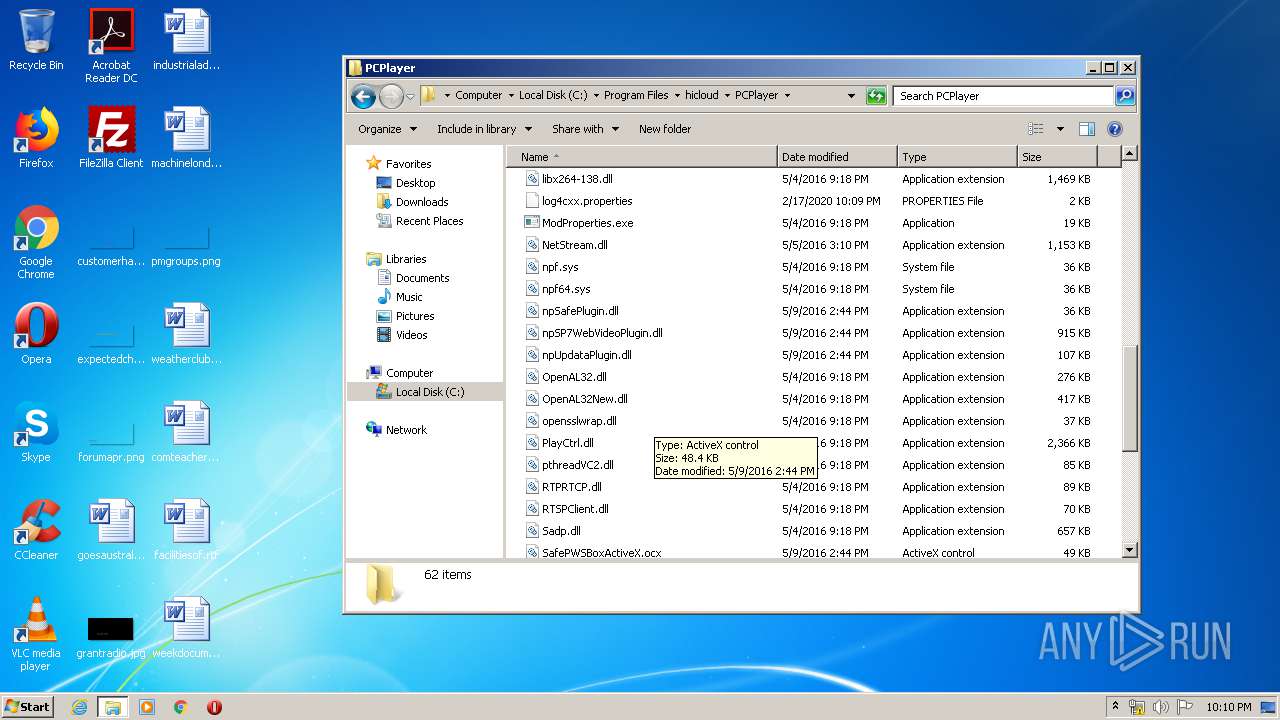
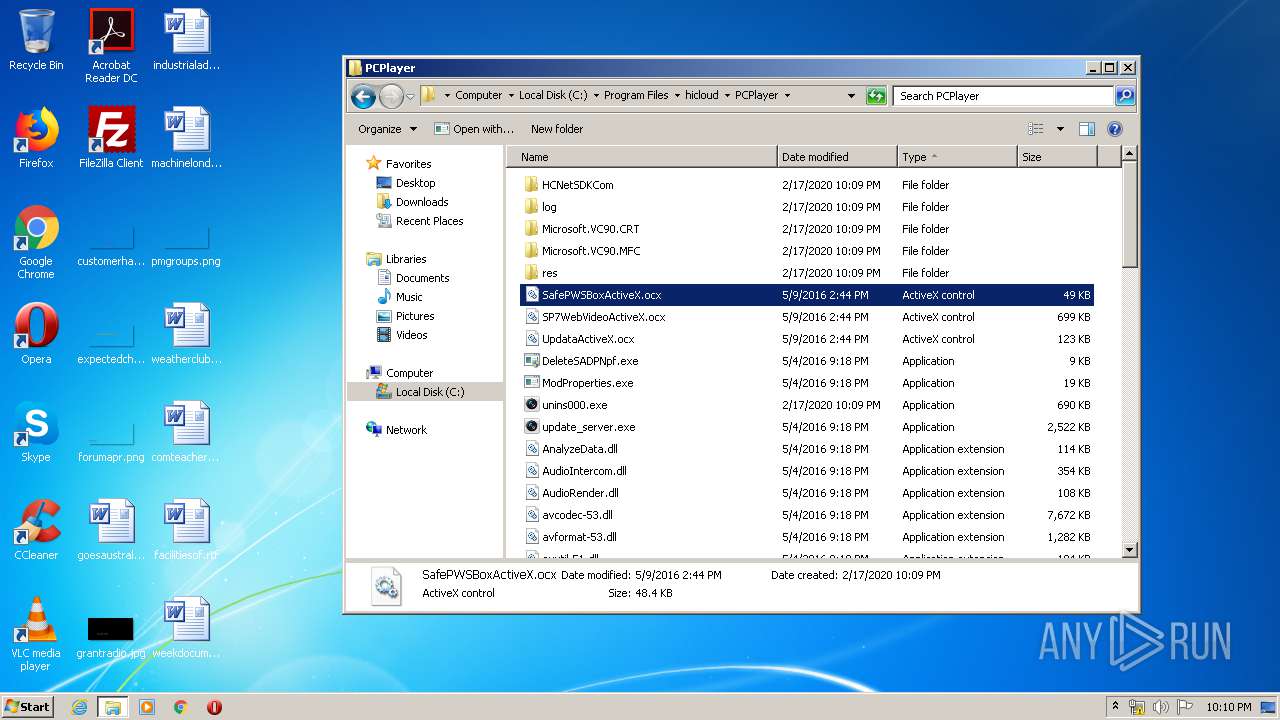
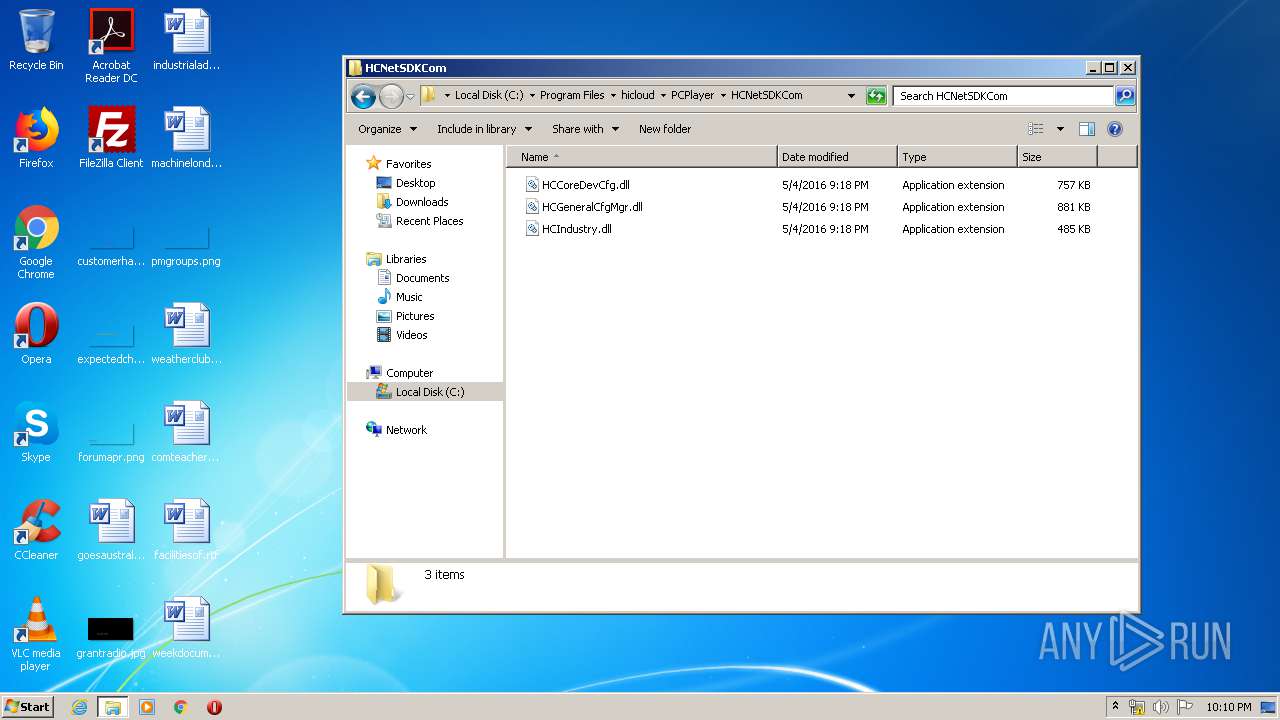
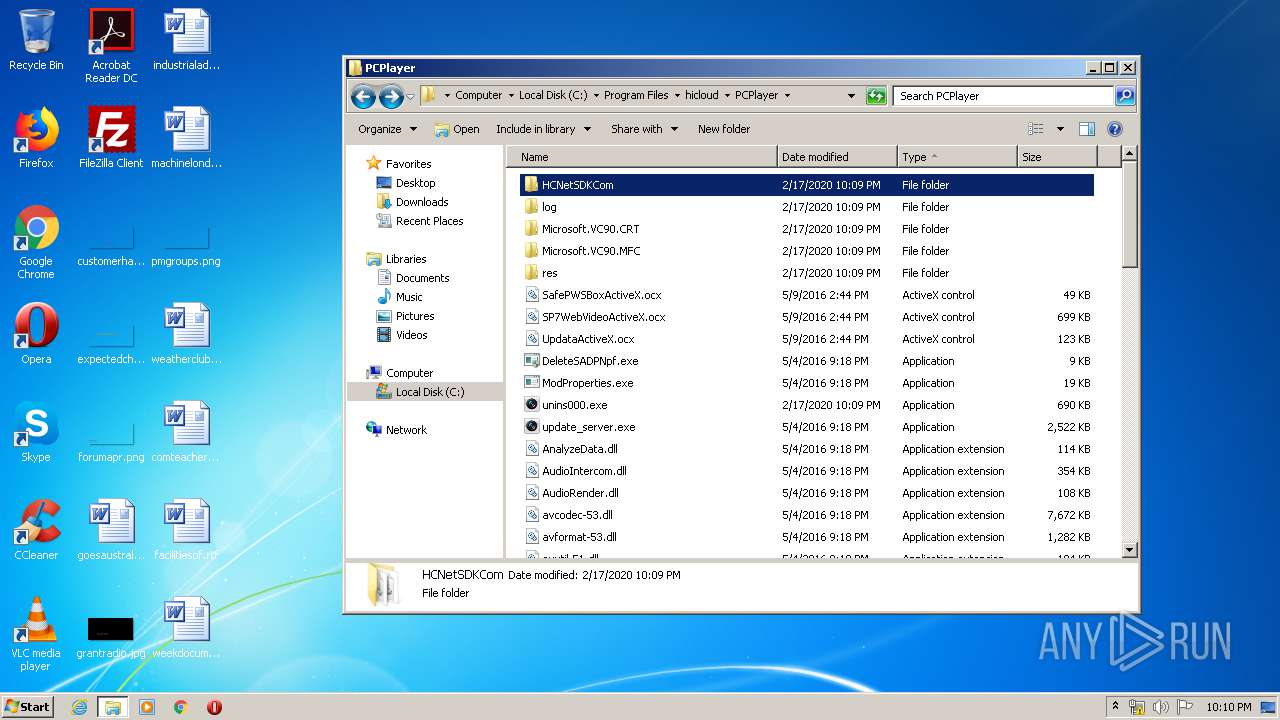
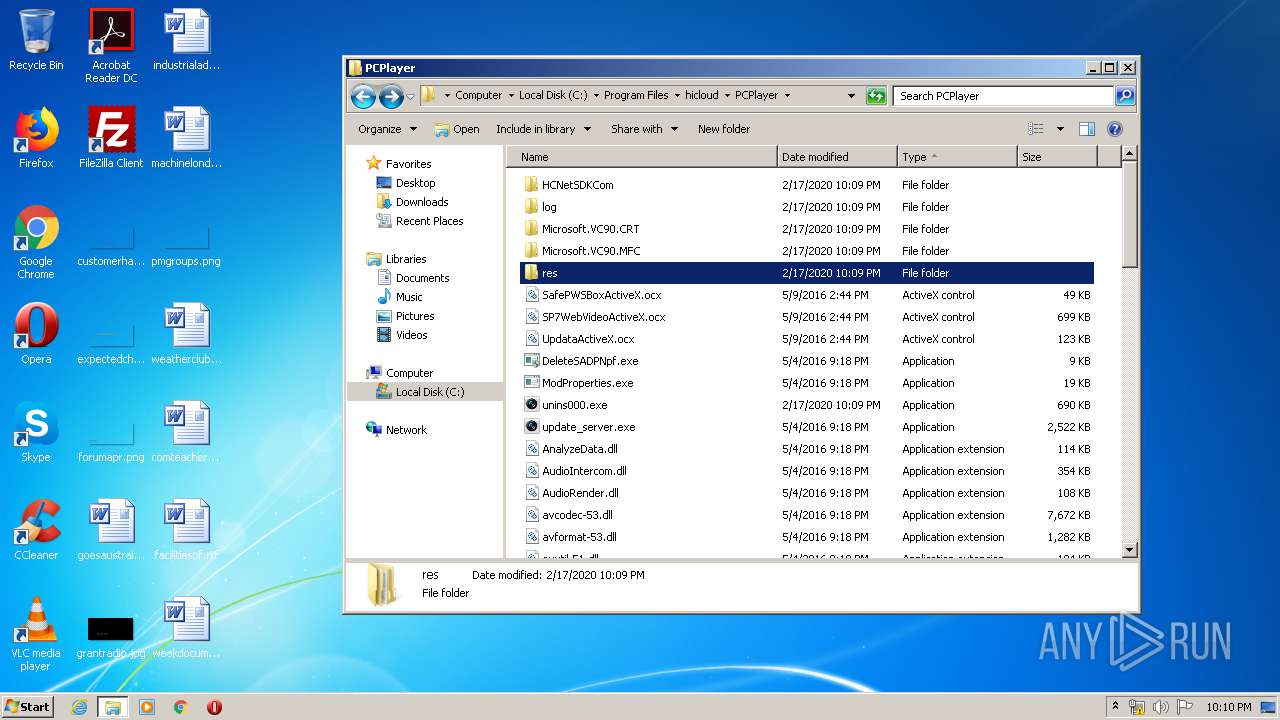
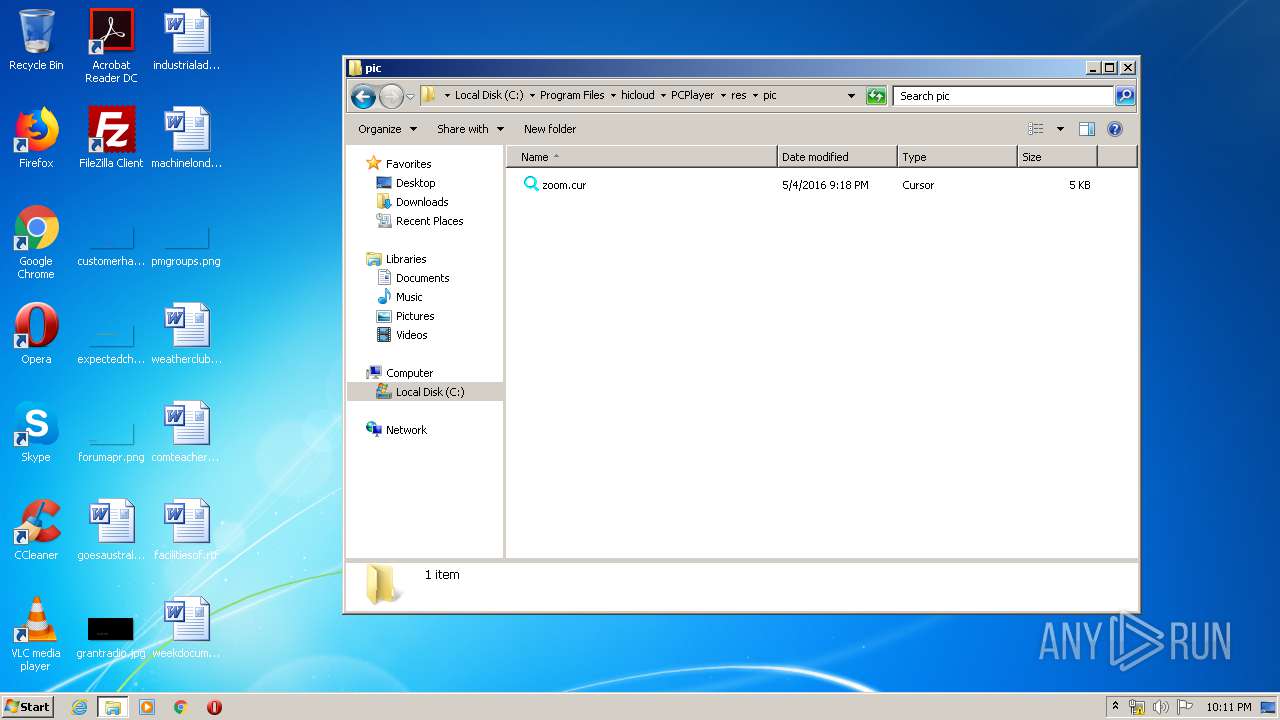
Creates files in the program directory
- regsvr32.exe (PID: 3836)
- ModProperties.exe (PID: 1948)
- SPUpDateServer.exe (PID: 3592)
- ModProperties.exe (PID: 2876)
- iexplore.exe (PID: 2636)
Uses RUNDLL32.EXE to load library
- explorer.exe (PID: 372)
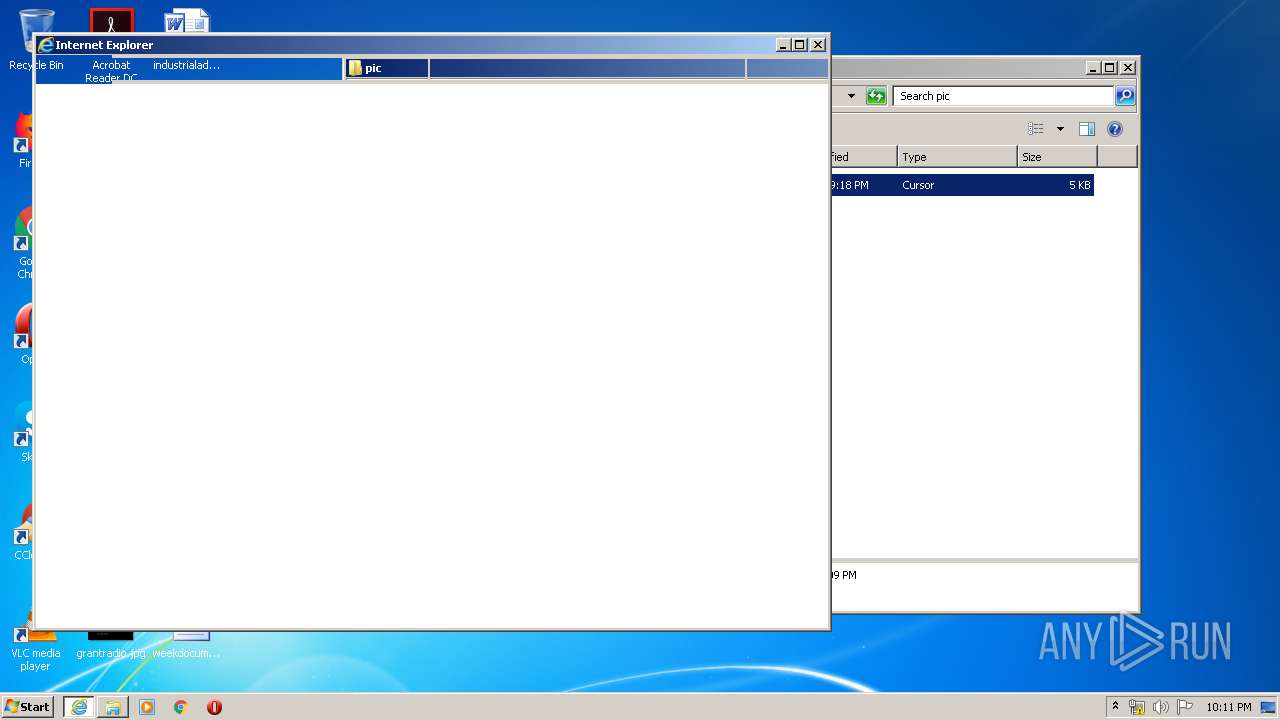
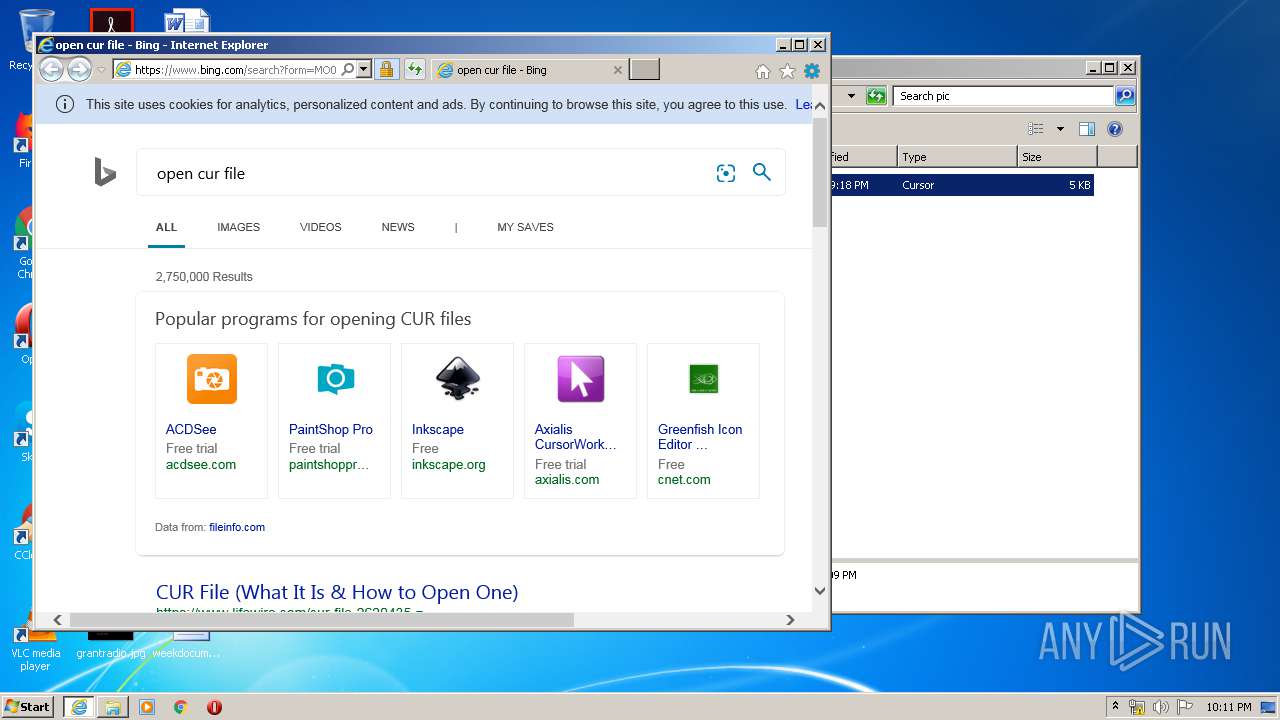
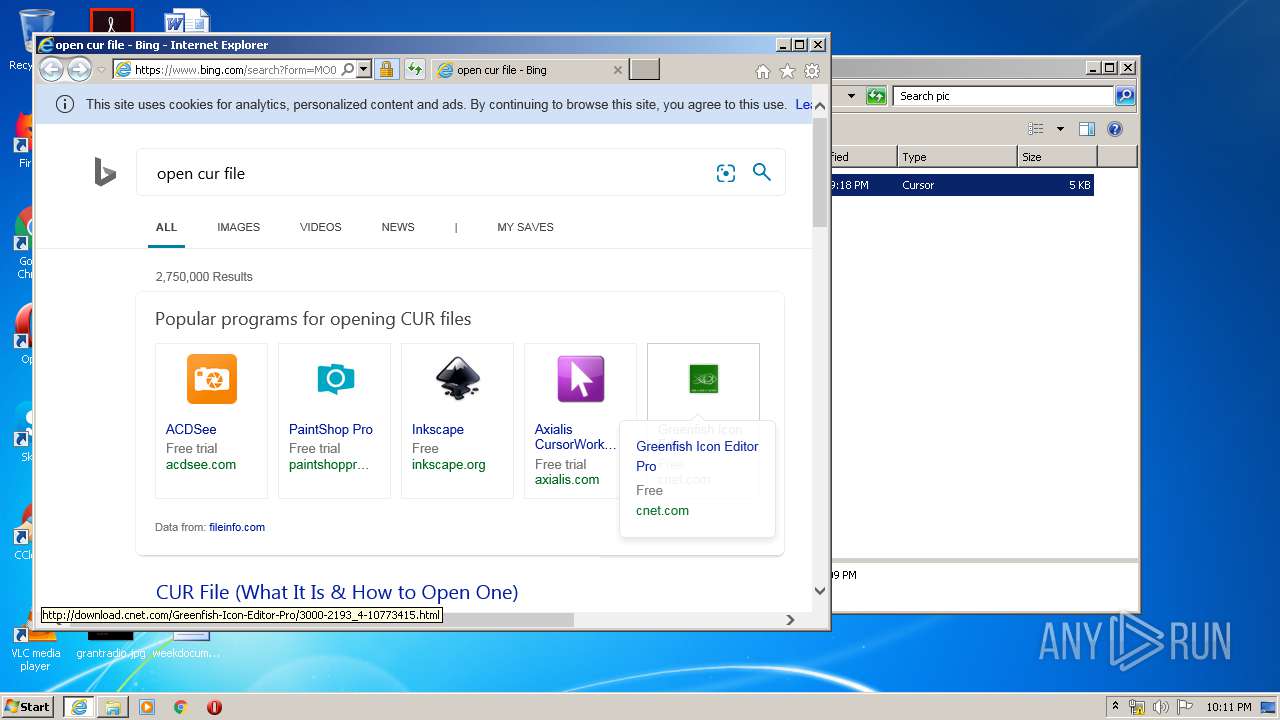
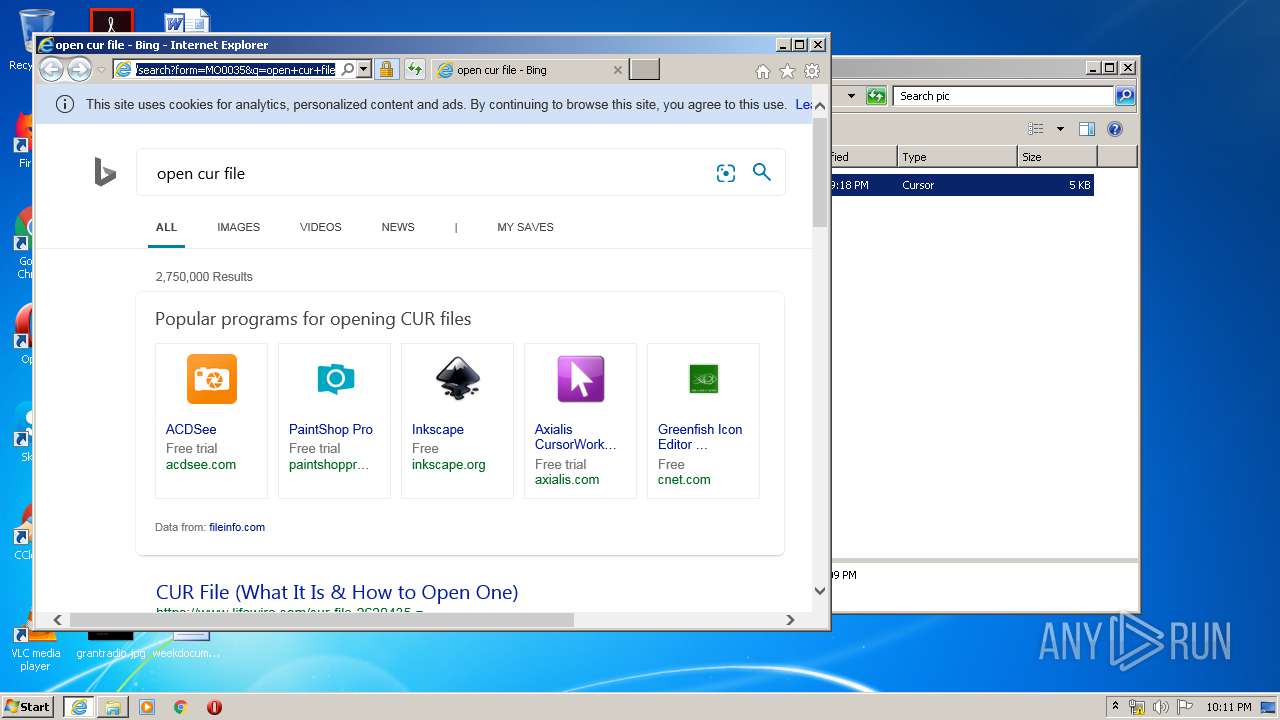
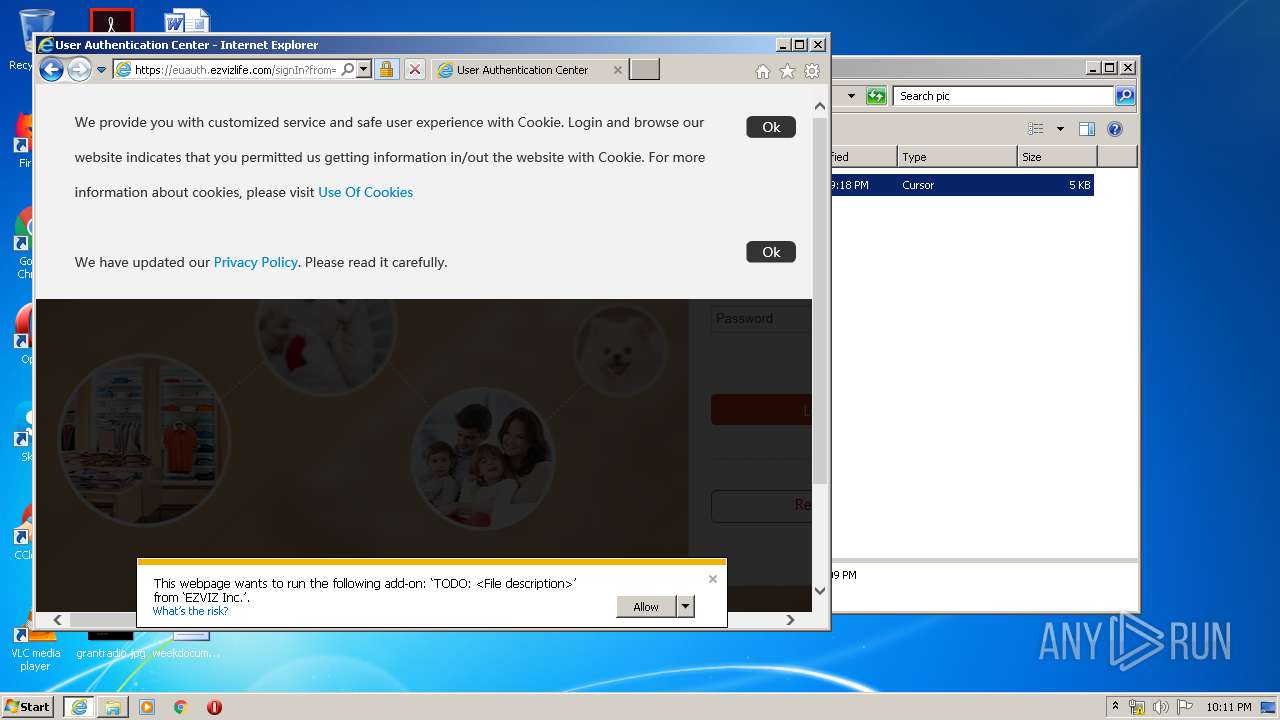
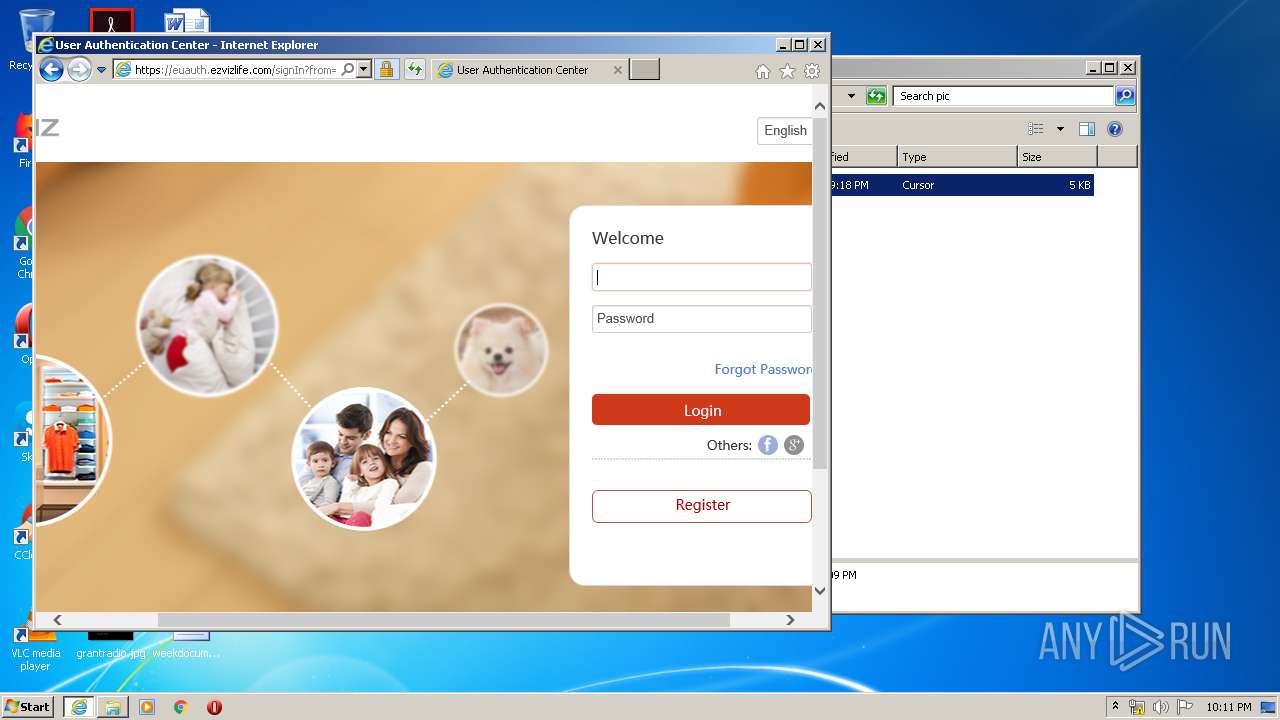
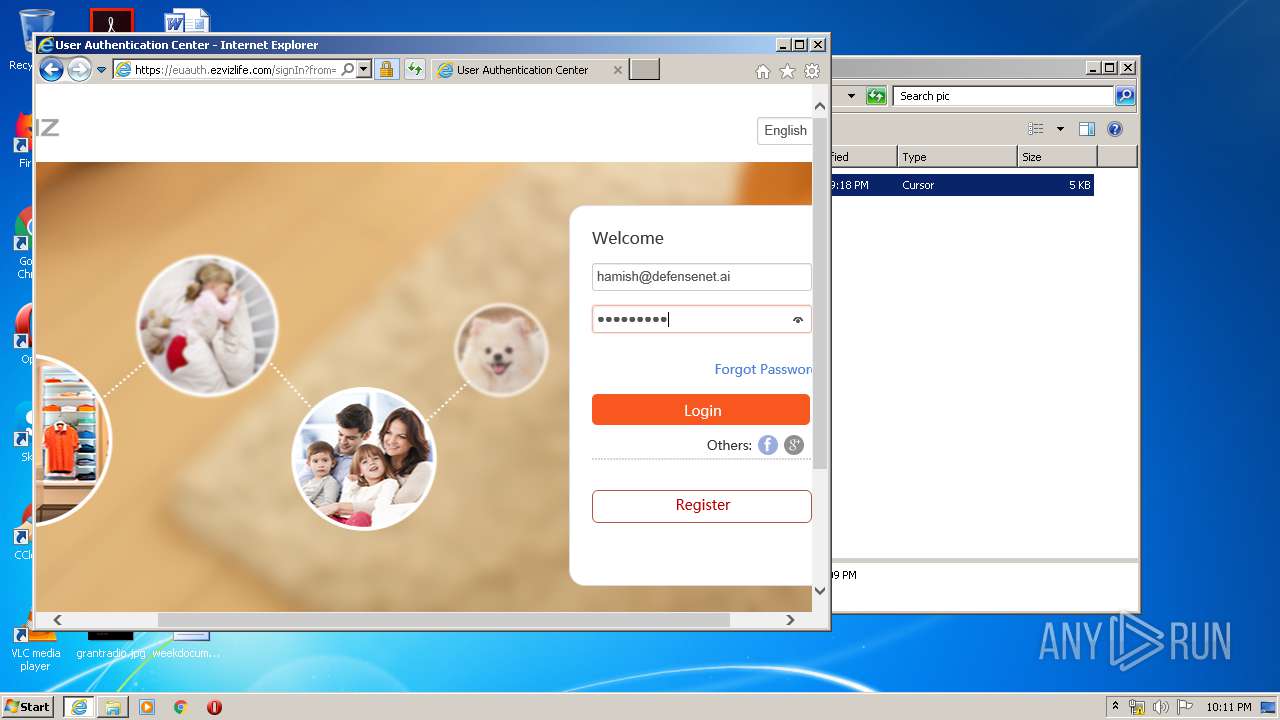
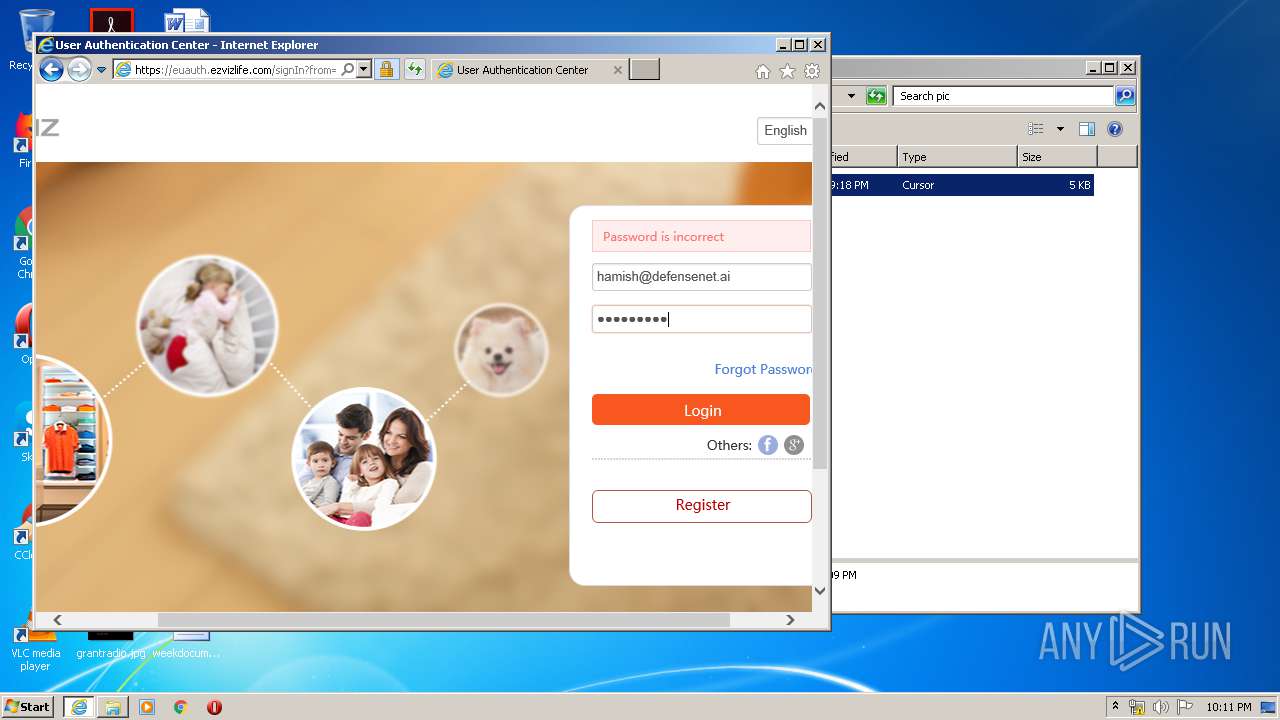
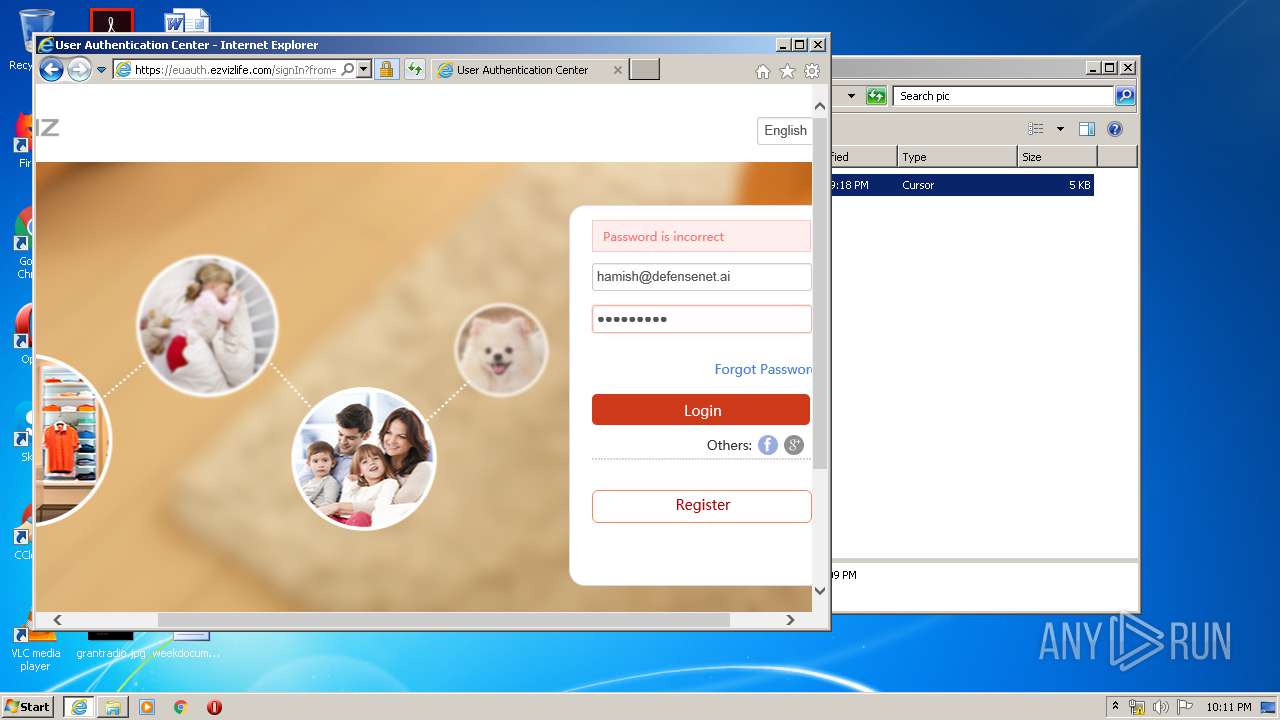
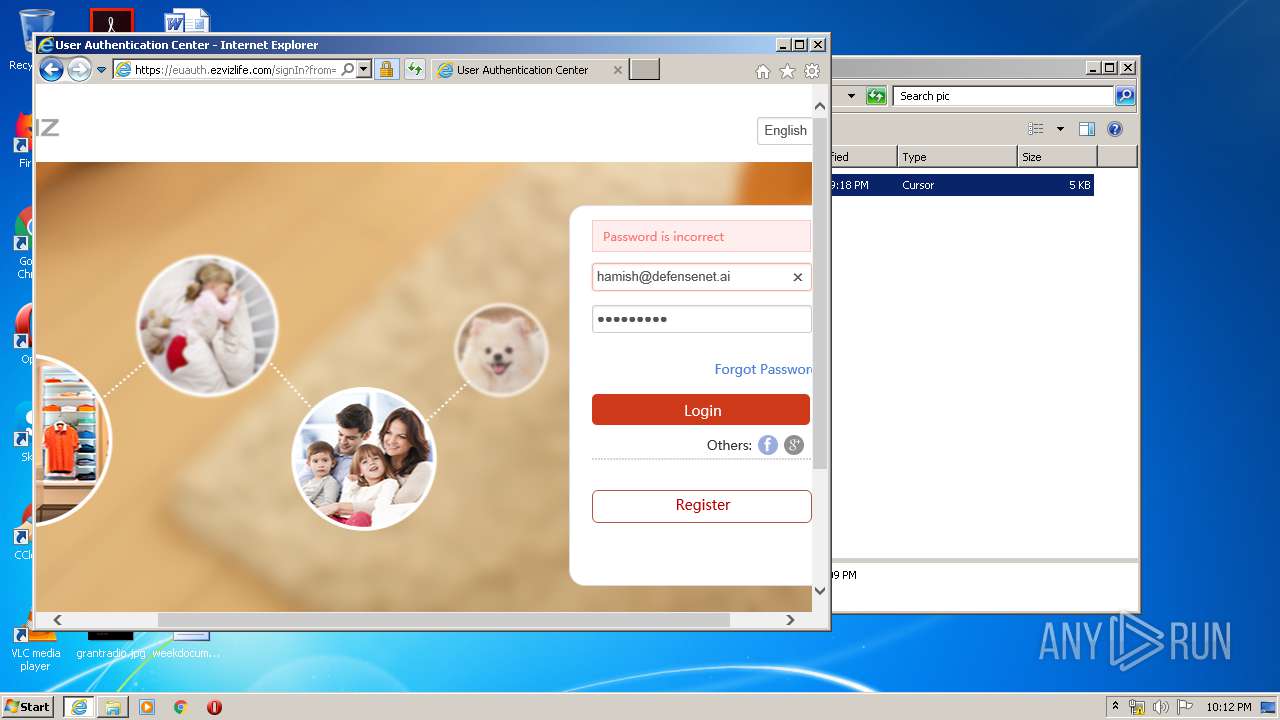
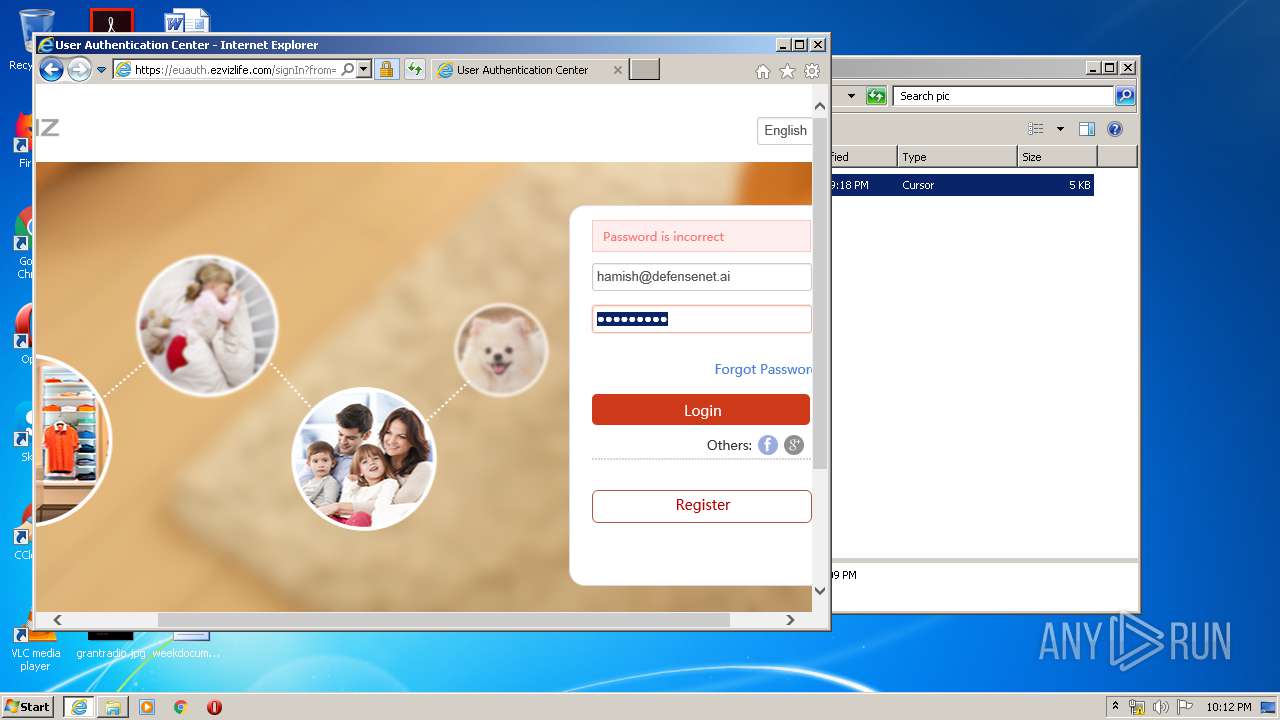
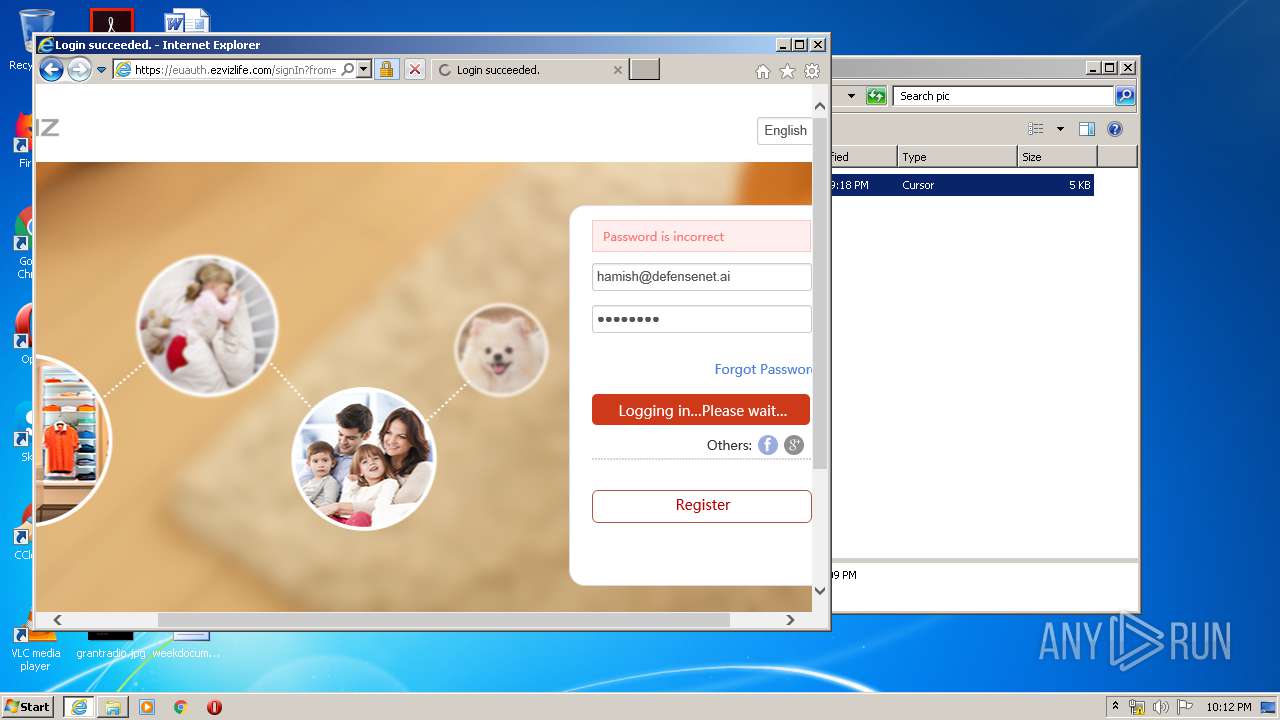
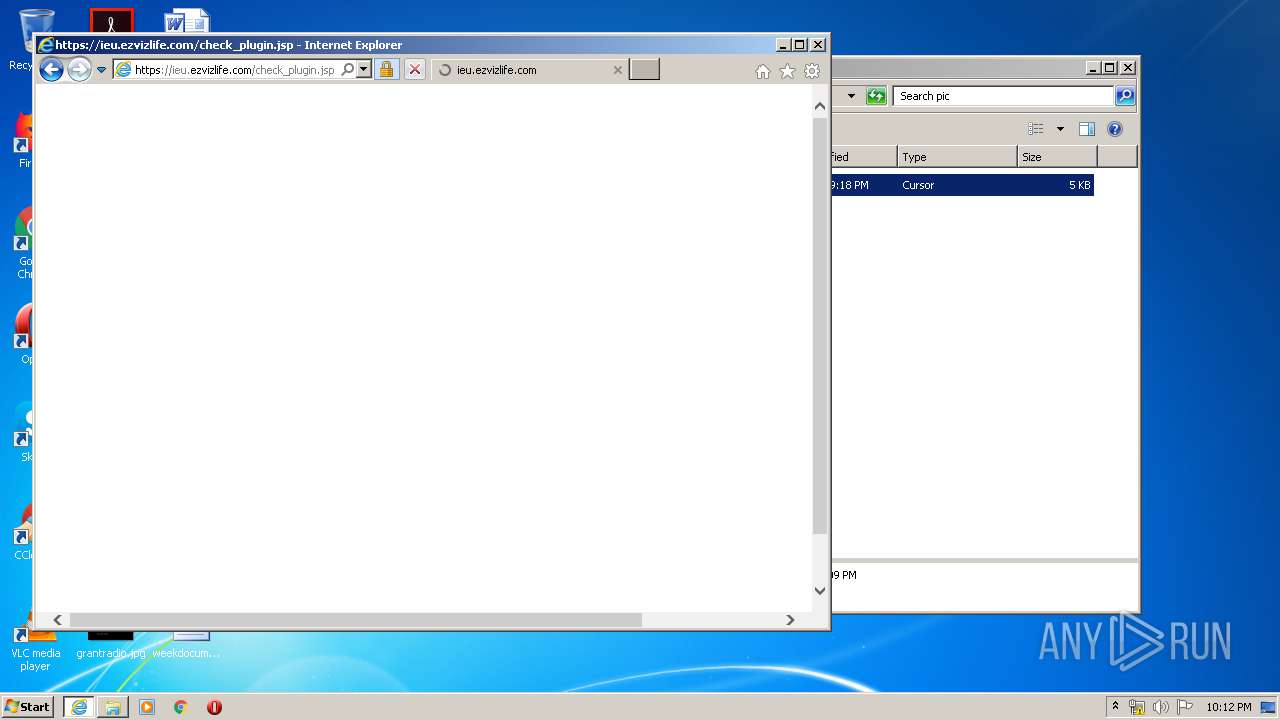
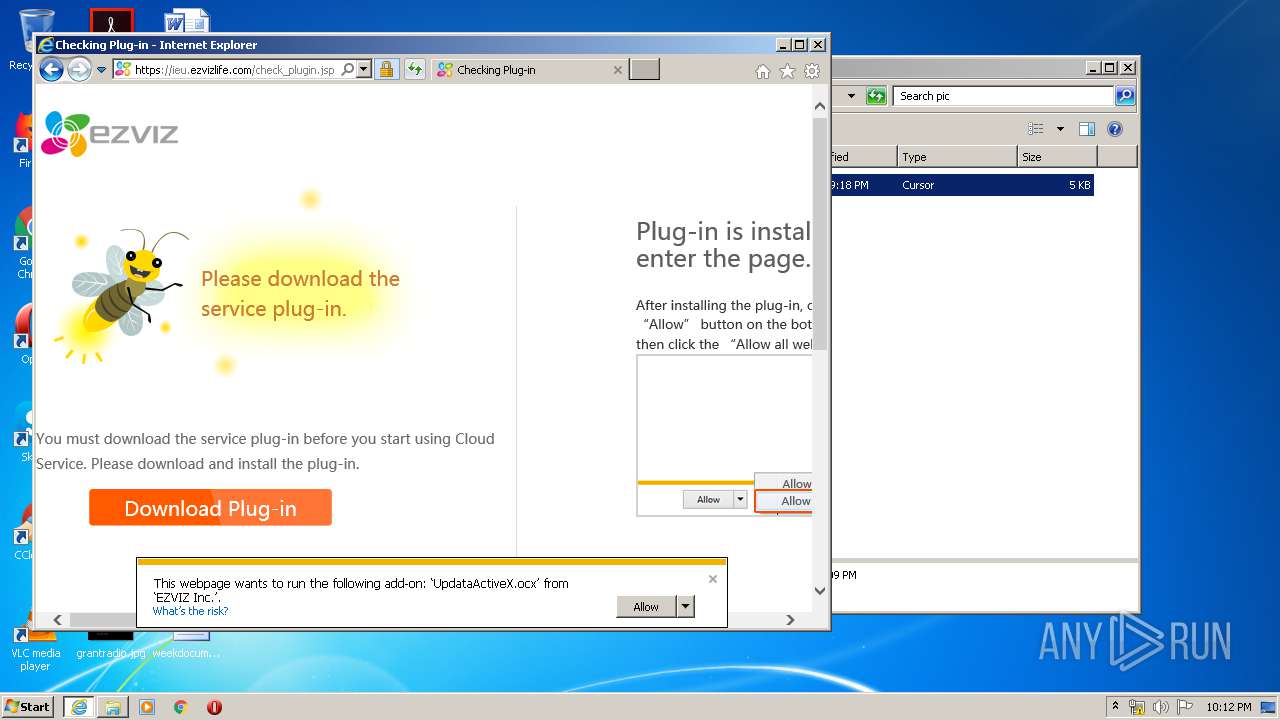
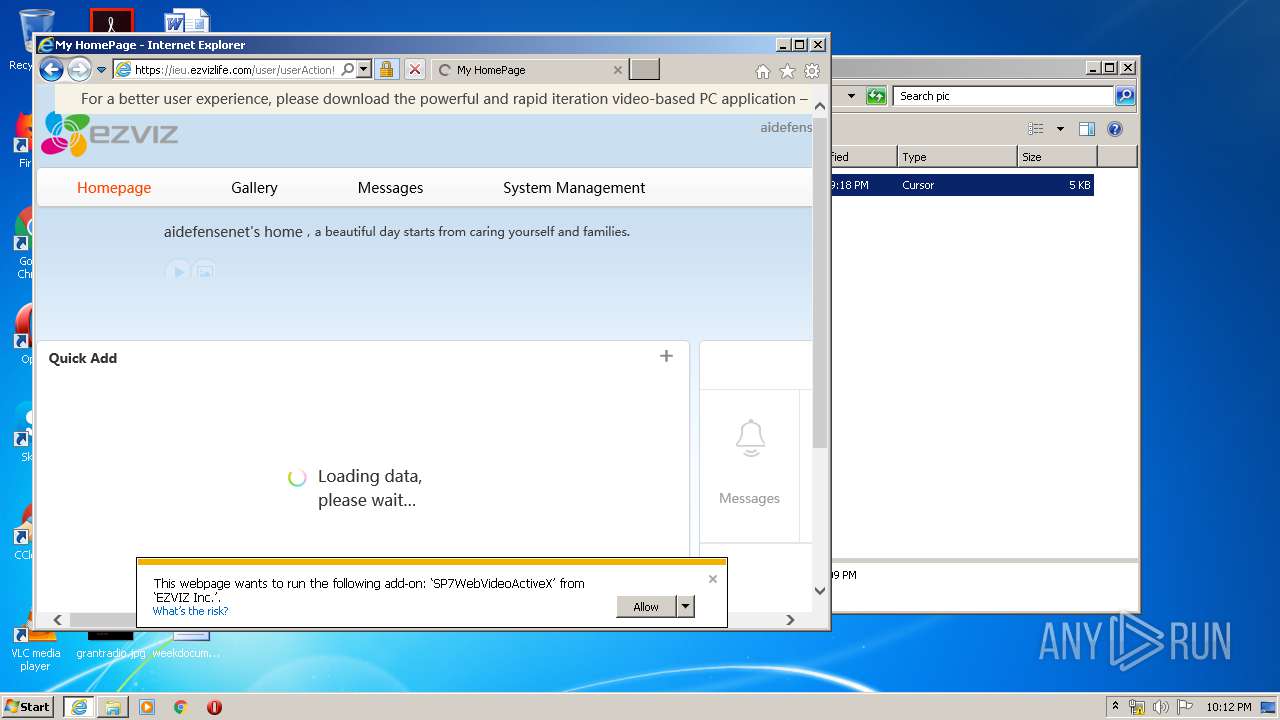
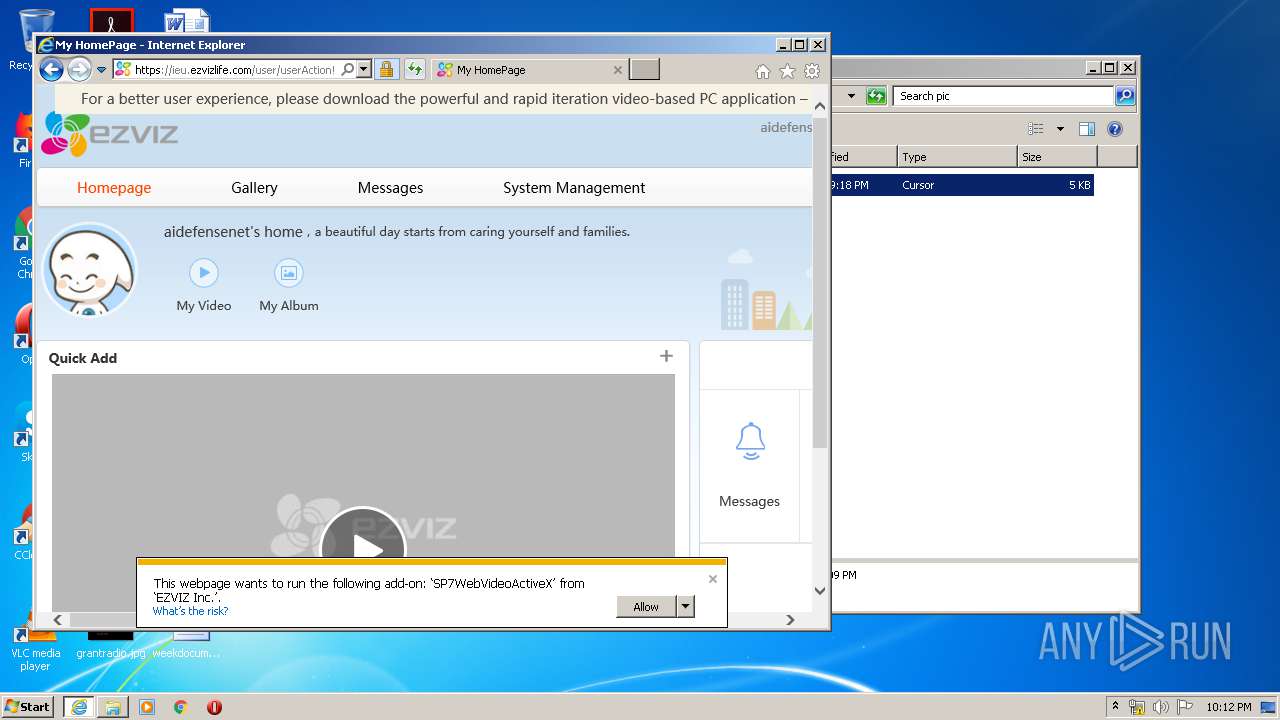
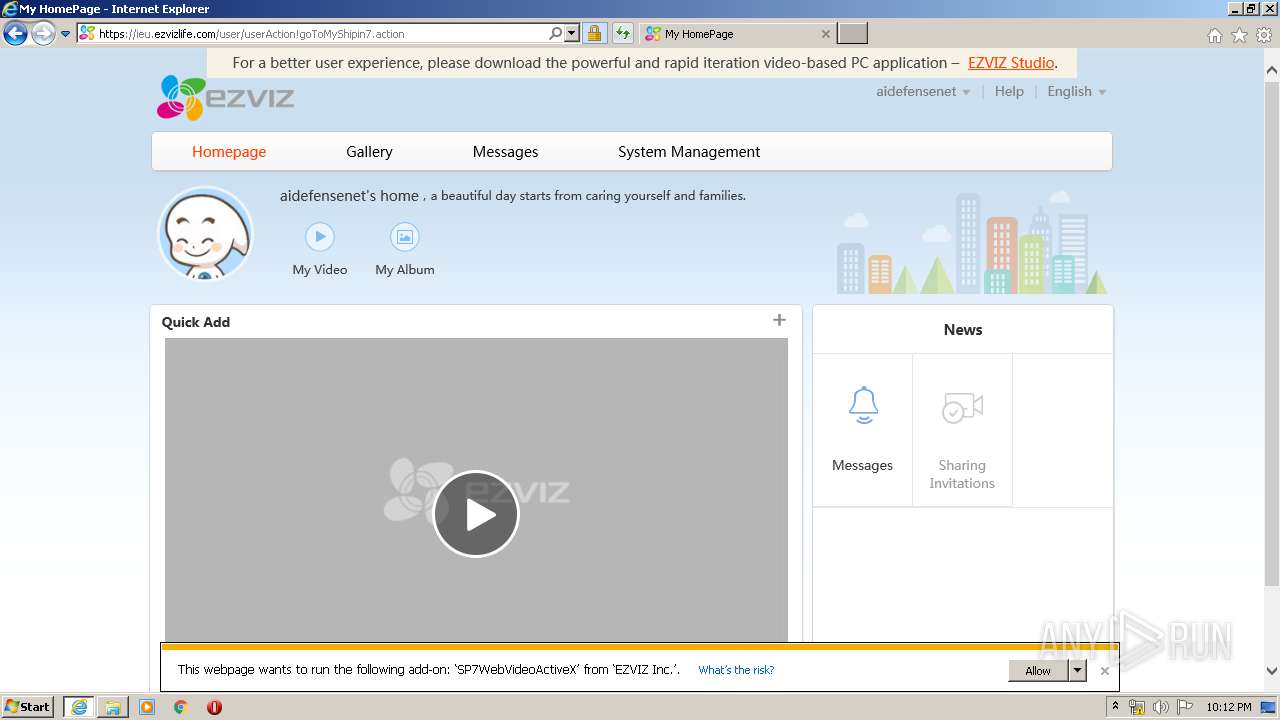
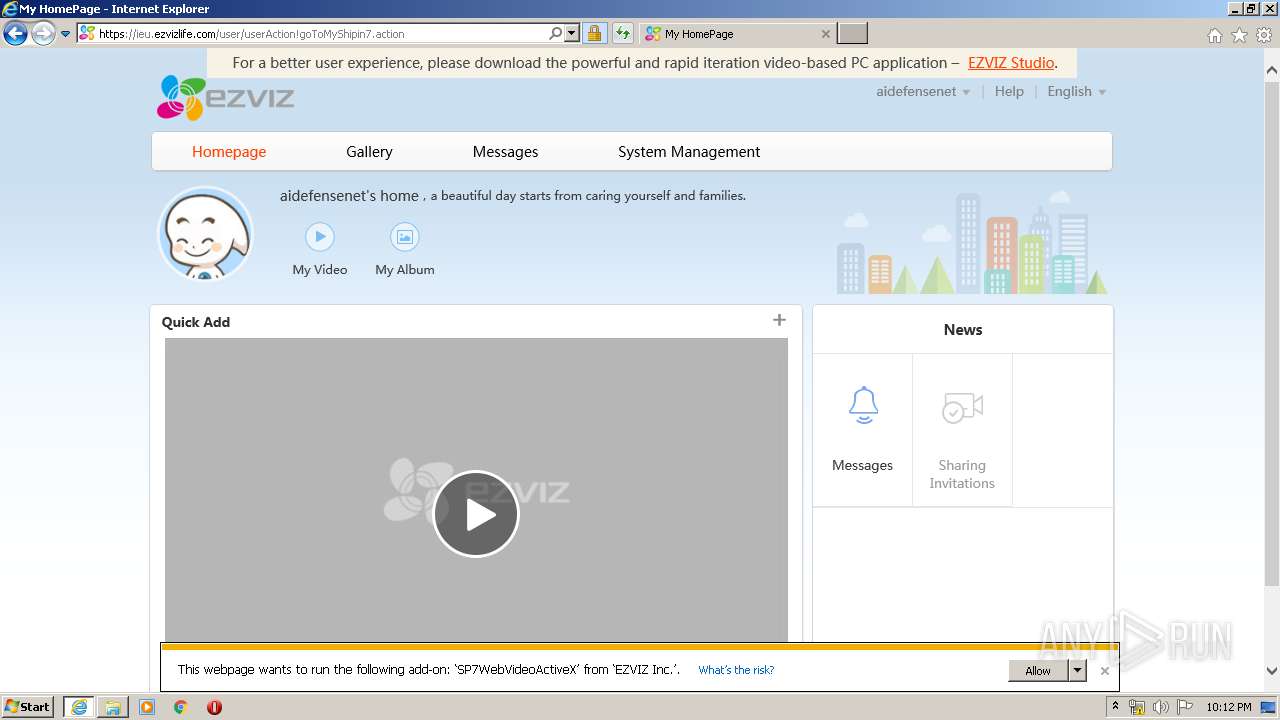
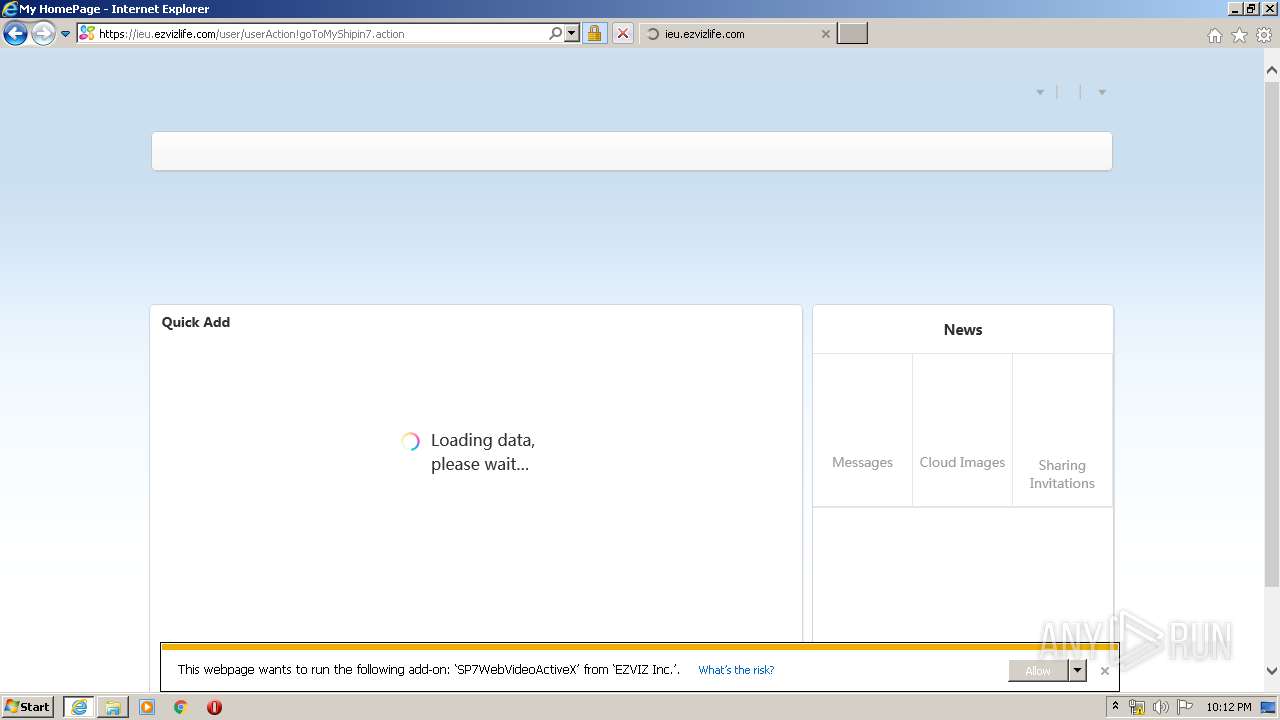
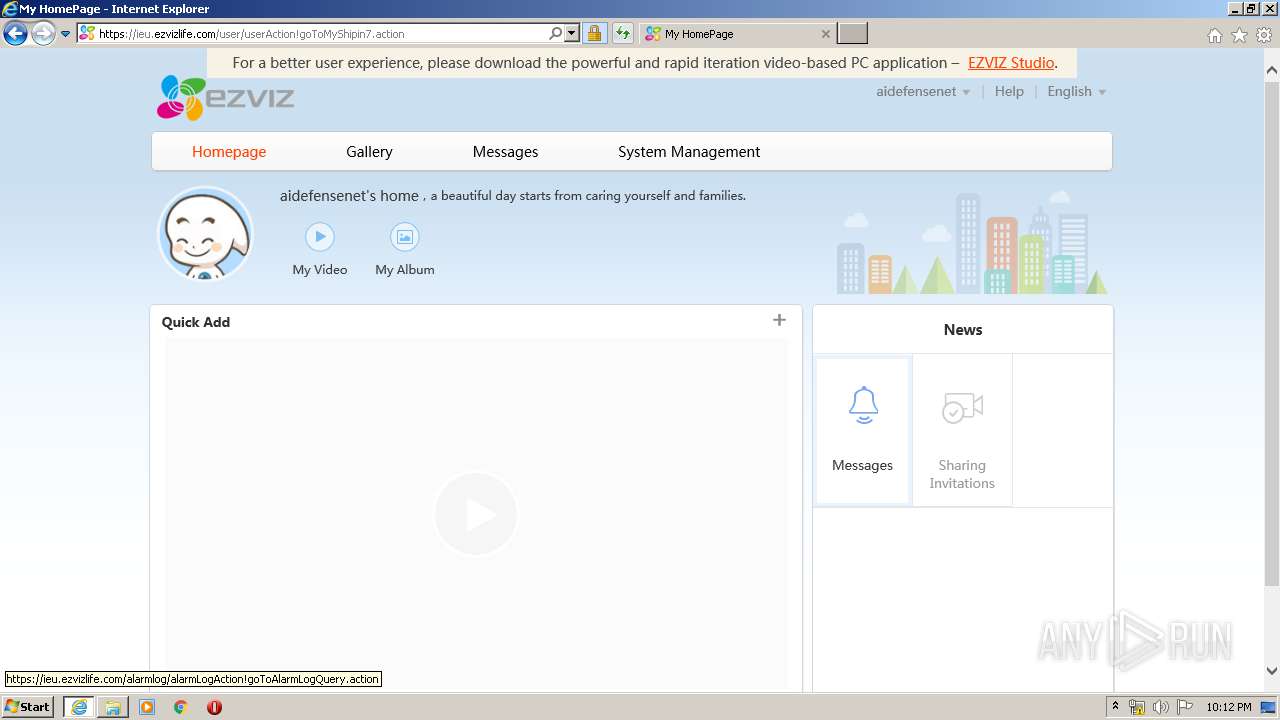
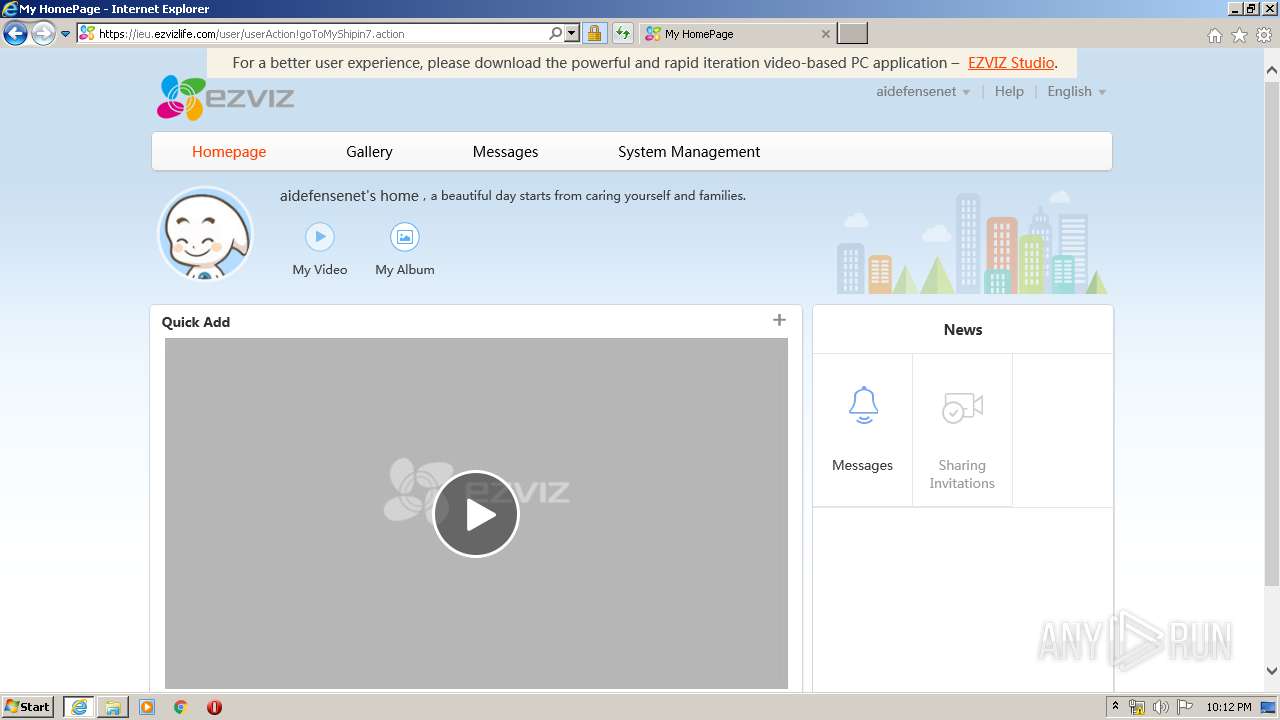
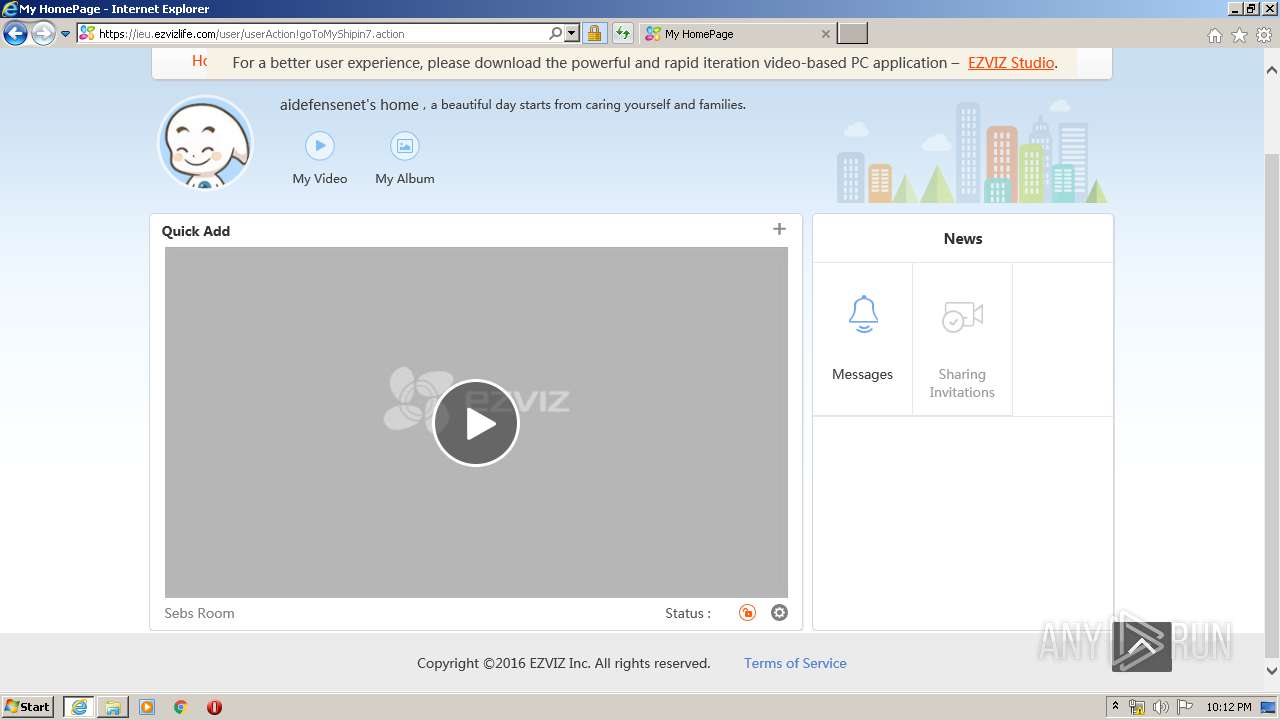
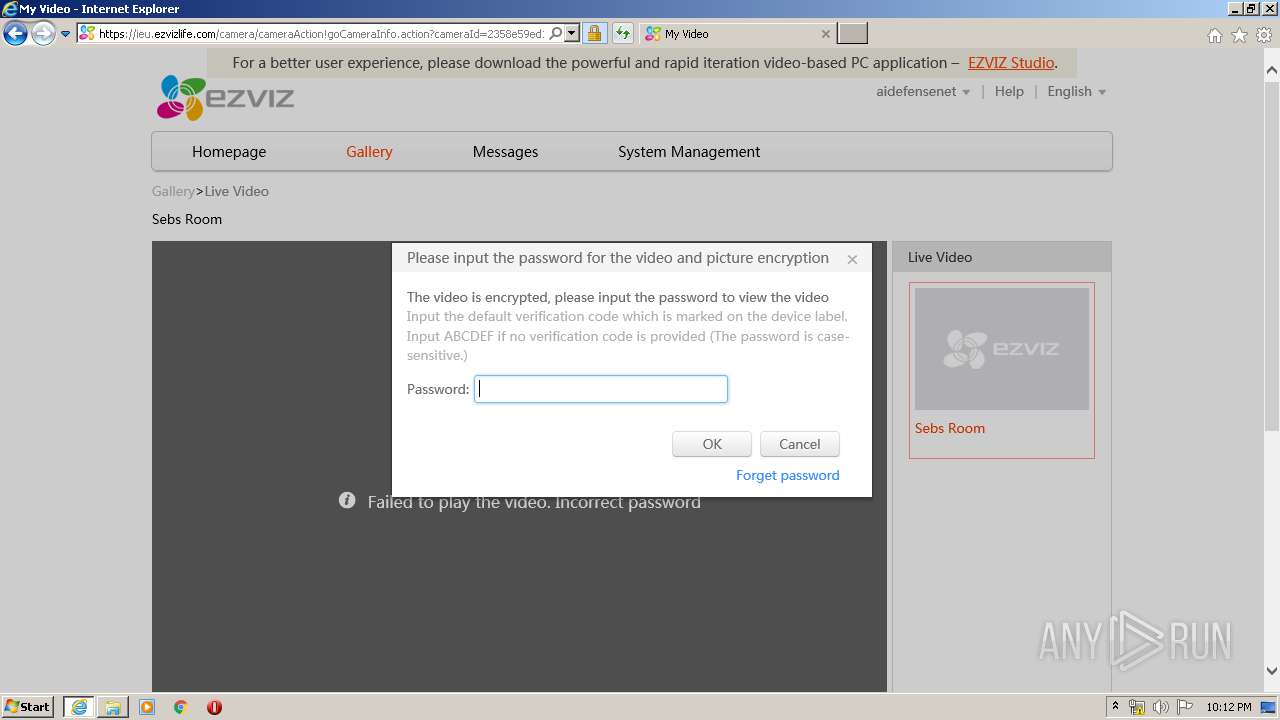
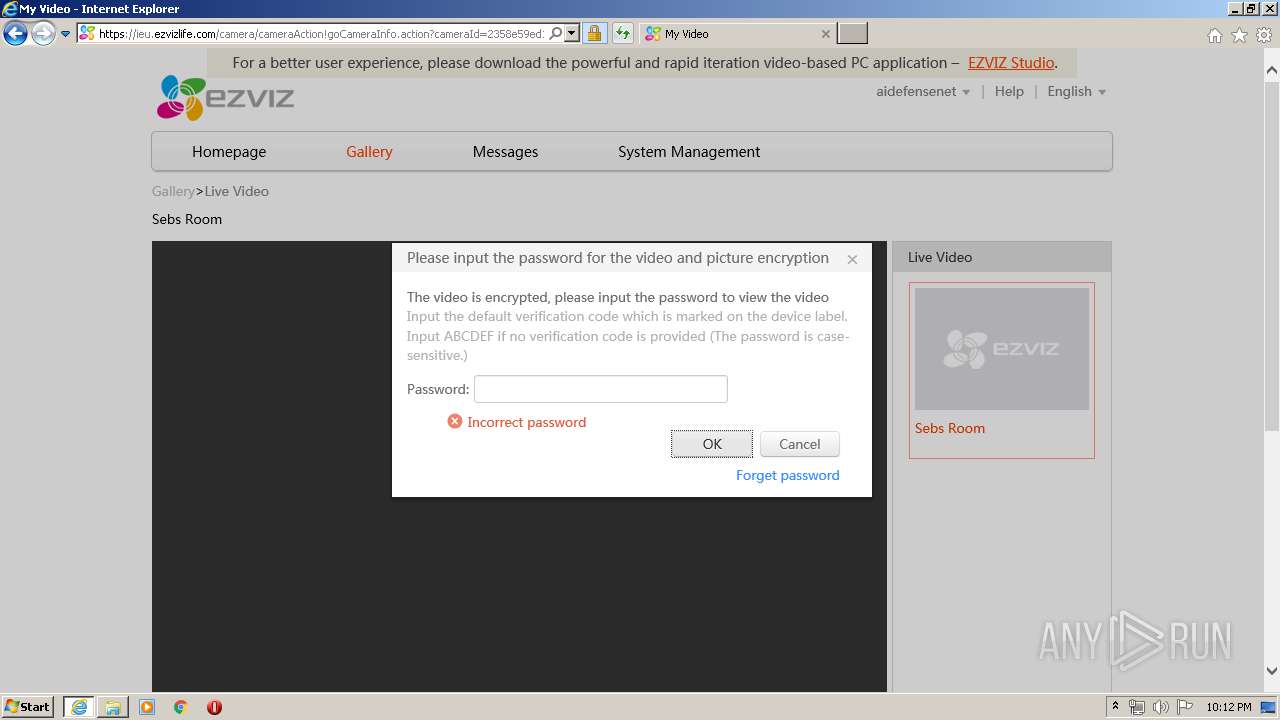
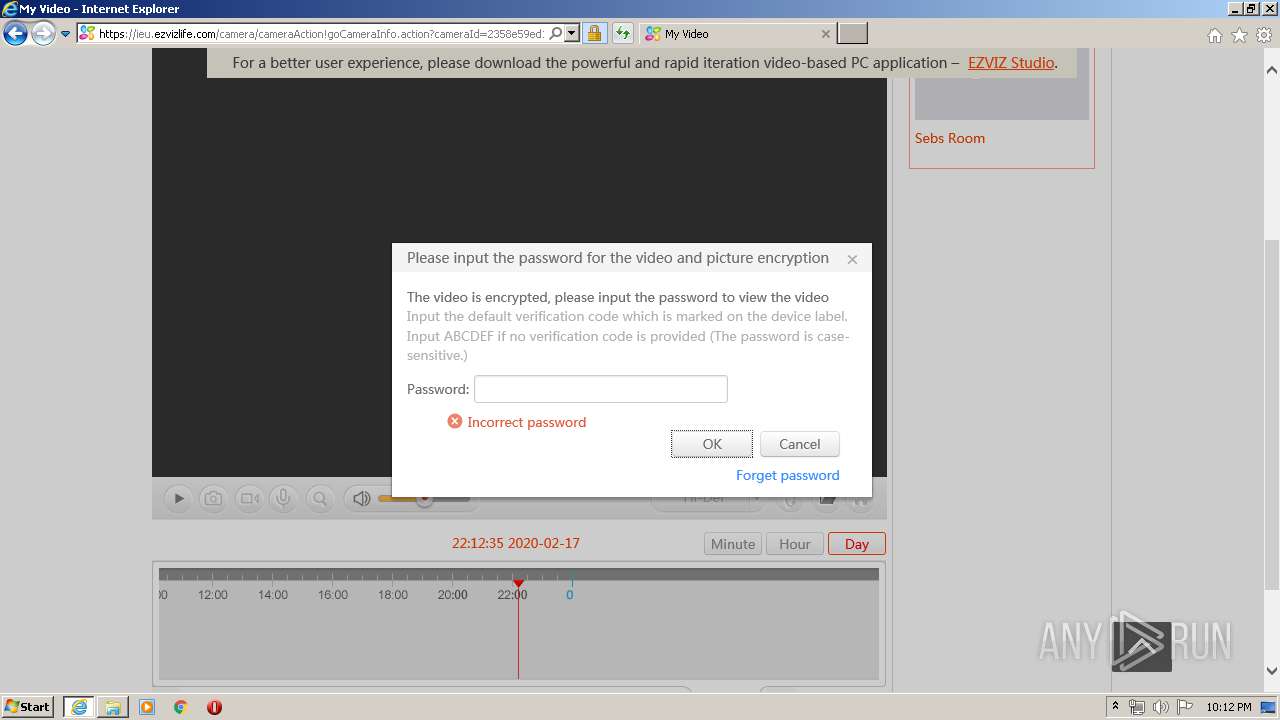
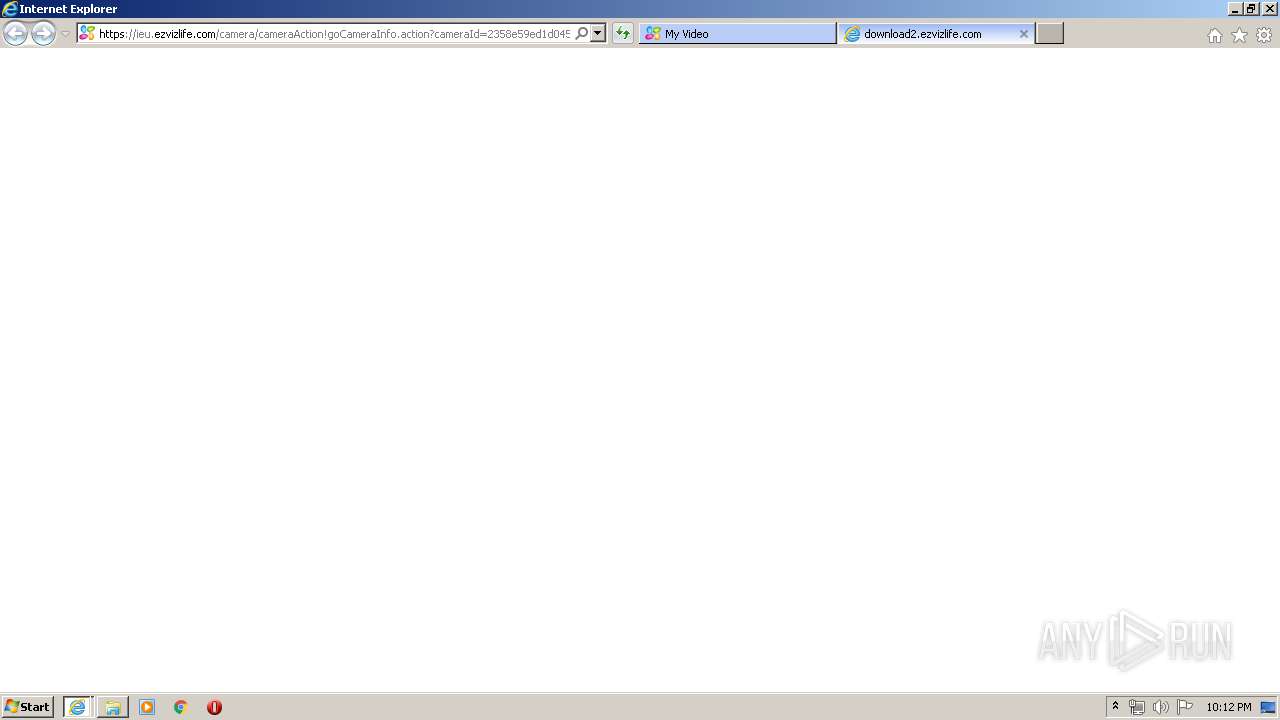
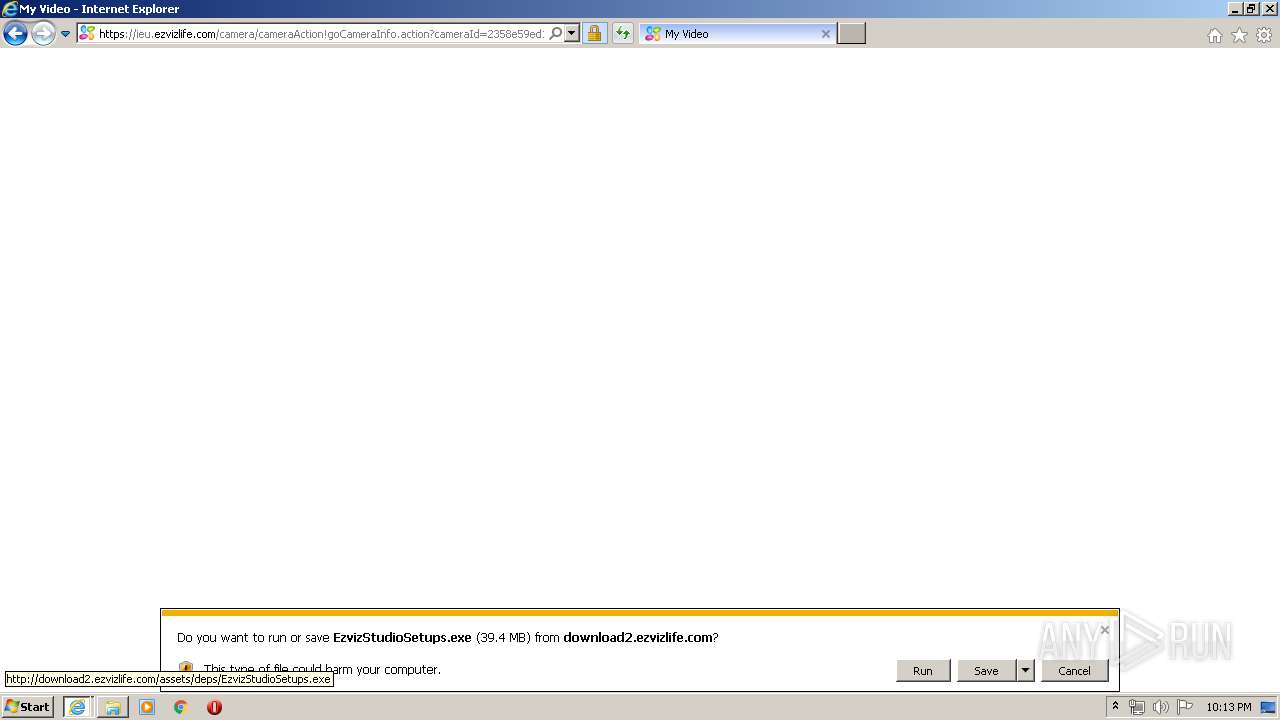
Starts Internet Explorer
- rundll32.exe (PID: 3032)
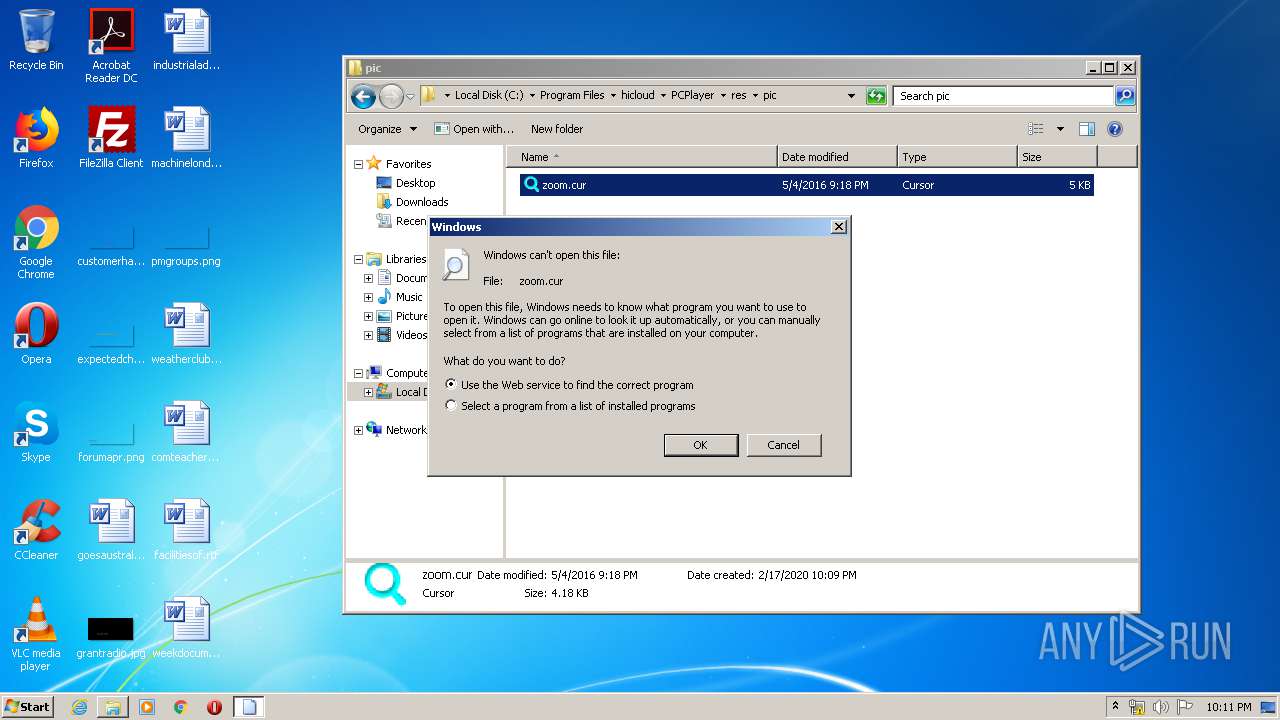
Reads default file associations for system extensions
- explorer.exe (PID: 372)
INFO
Application was dropped or rewritten from another process
- PCPlayer.tmp (PID: 2600)
- PCPlayer.tmp (PID: 3852)
- update_server.tmp (PID: 2112)
Loads dropped or rewritten executable
- PCPlayer.tmp (PID: 3852)
- update_server.tmp (PID: 2112)
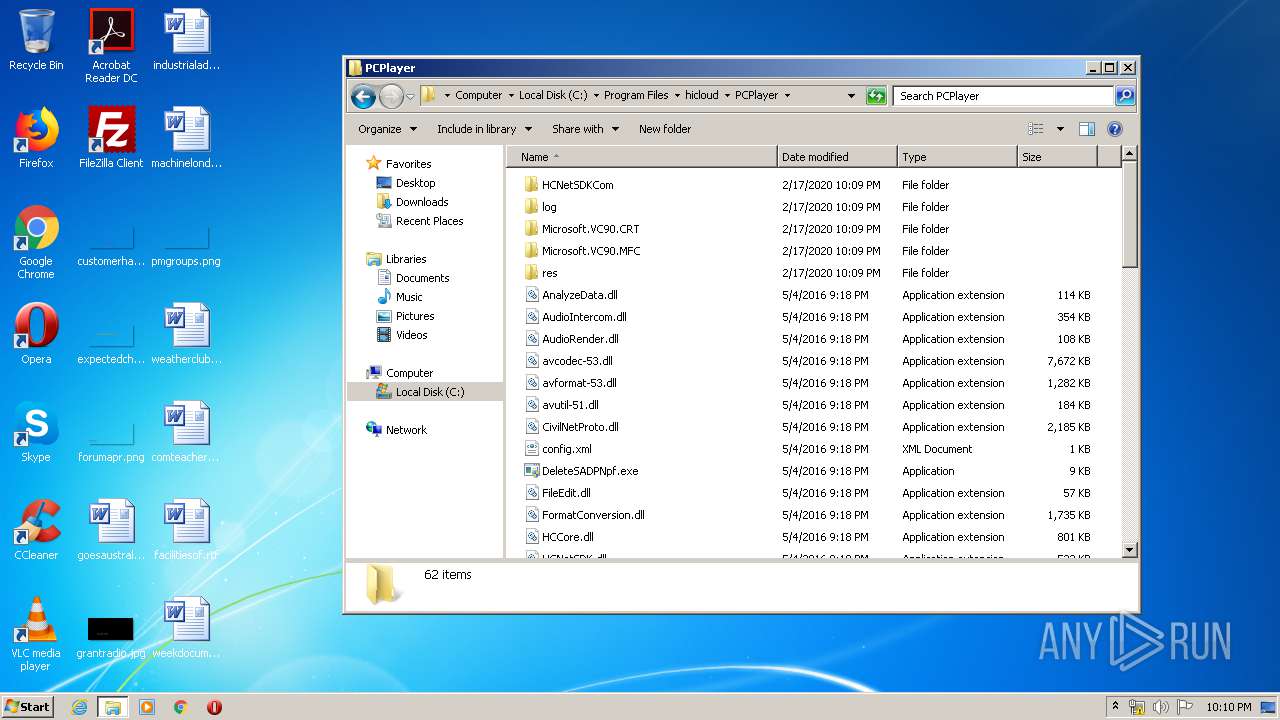
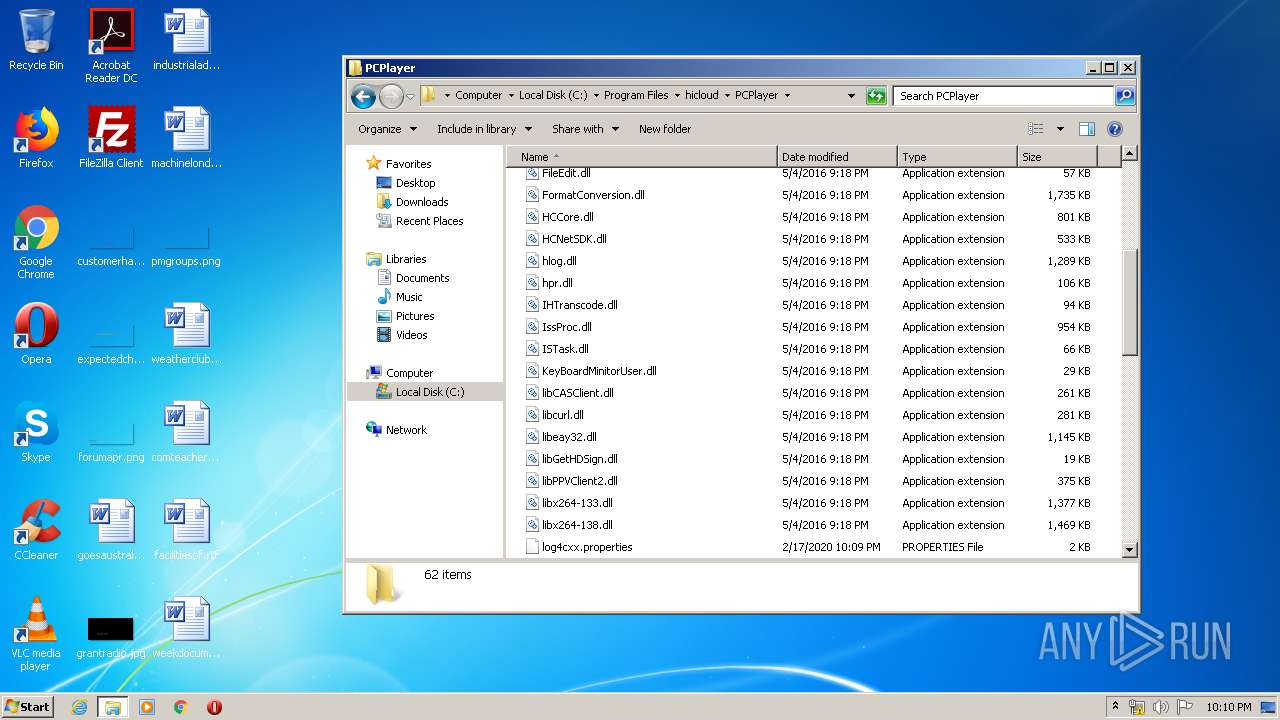
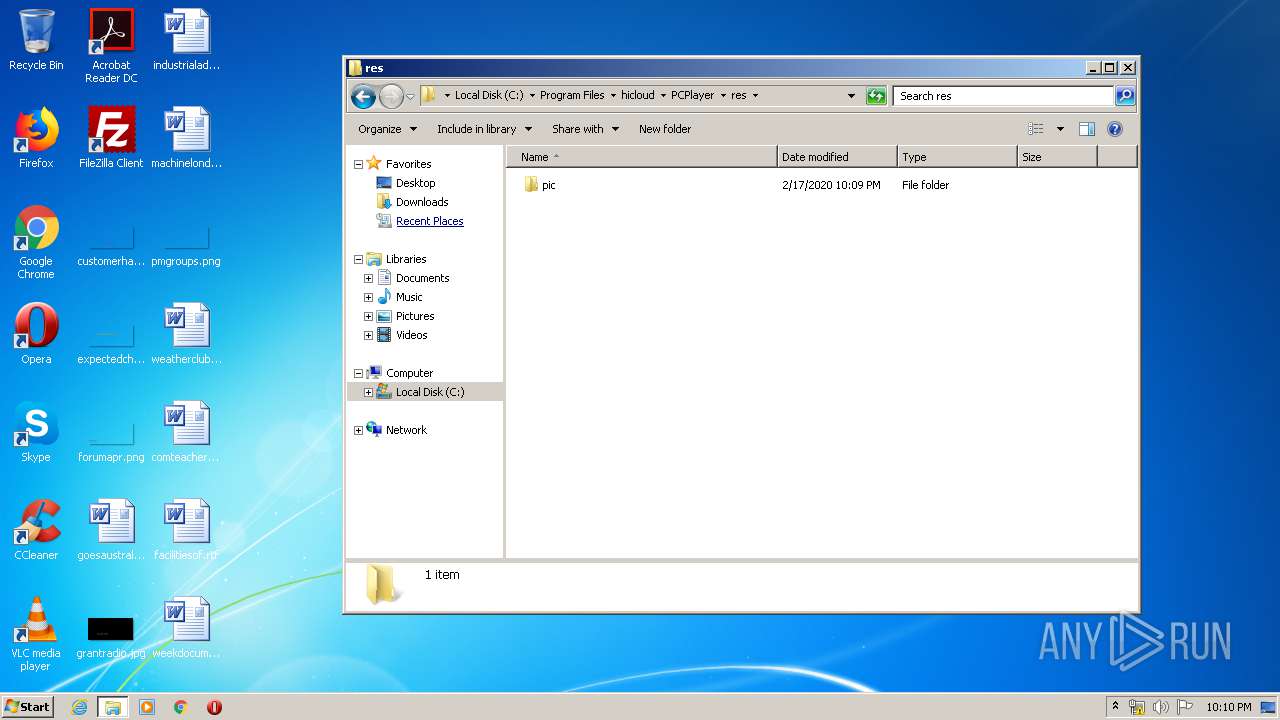
Creates files in the program directory
- PCPlayer.tmp (PID: 3852)
- update_server.tmp (PID: 2112)
Dropped object may contain Bitcoin addresses
- PCPlayer.tmp (PID: 3852)
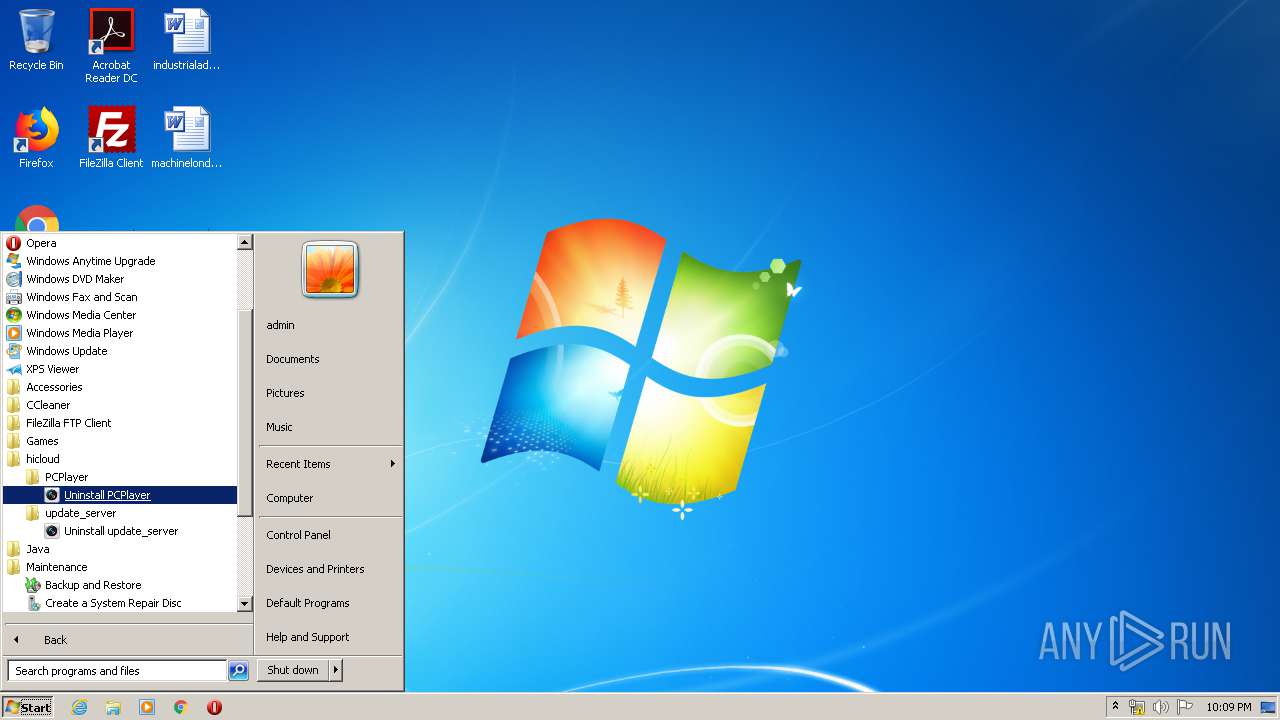
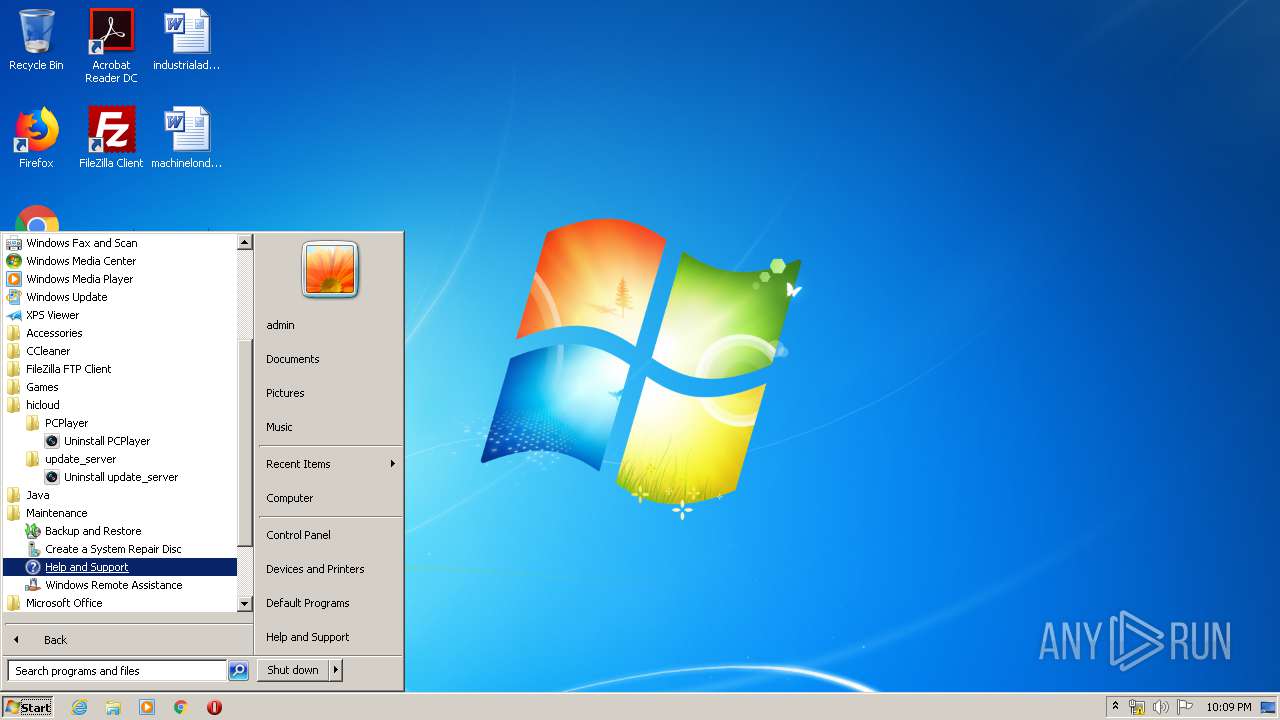
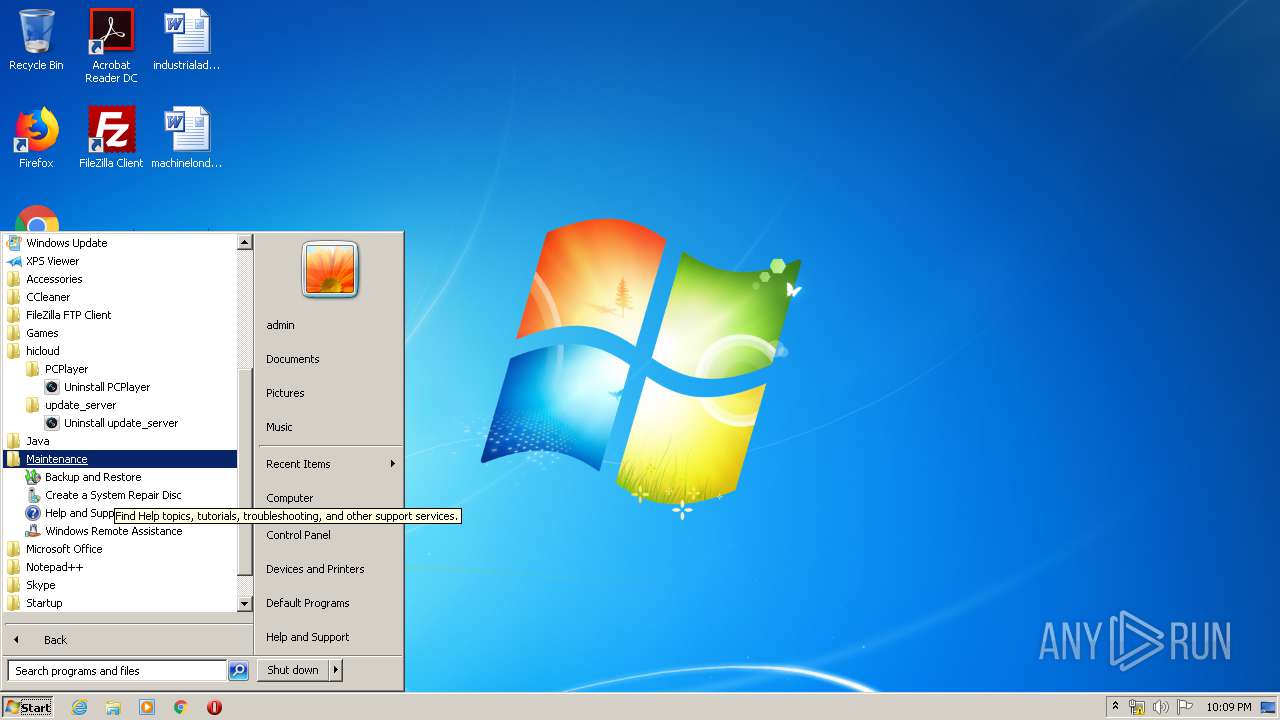
Creates a software uninstall entry
- PCPlayer.tmp (PID: 3852)
- update_server.tmp (PID: 2112)
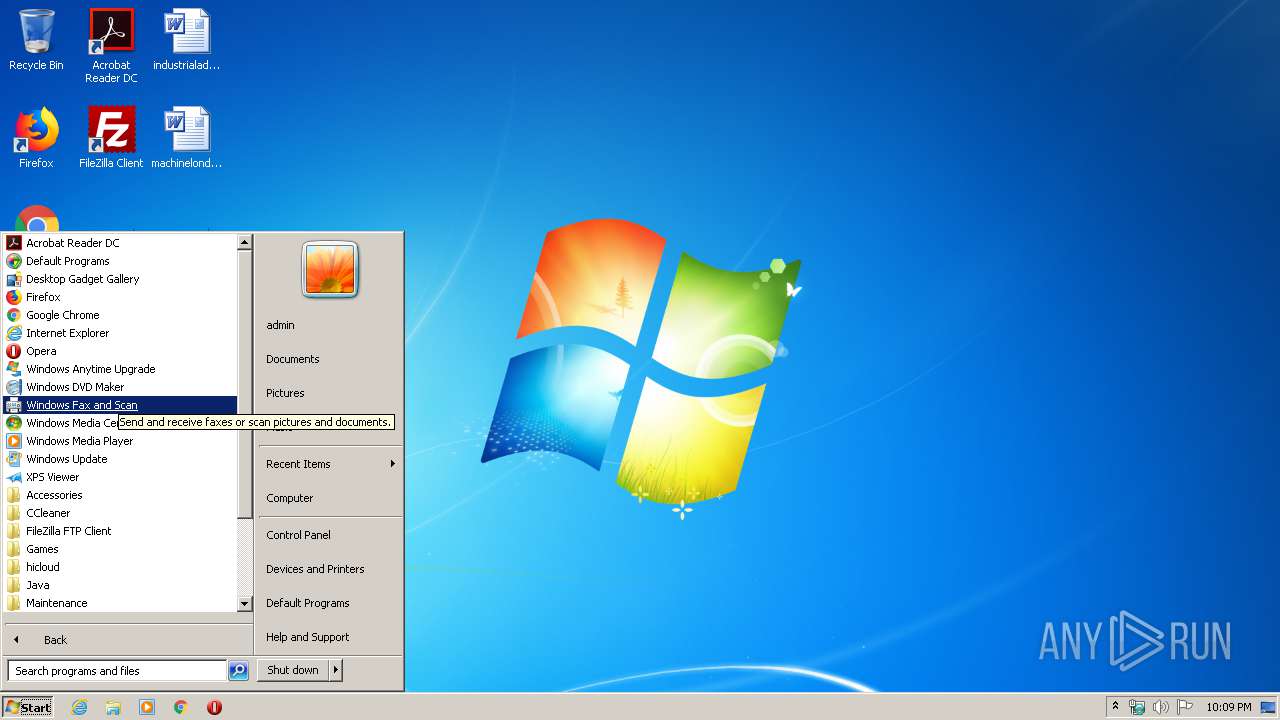
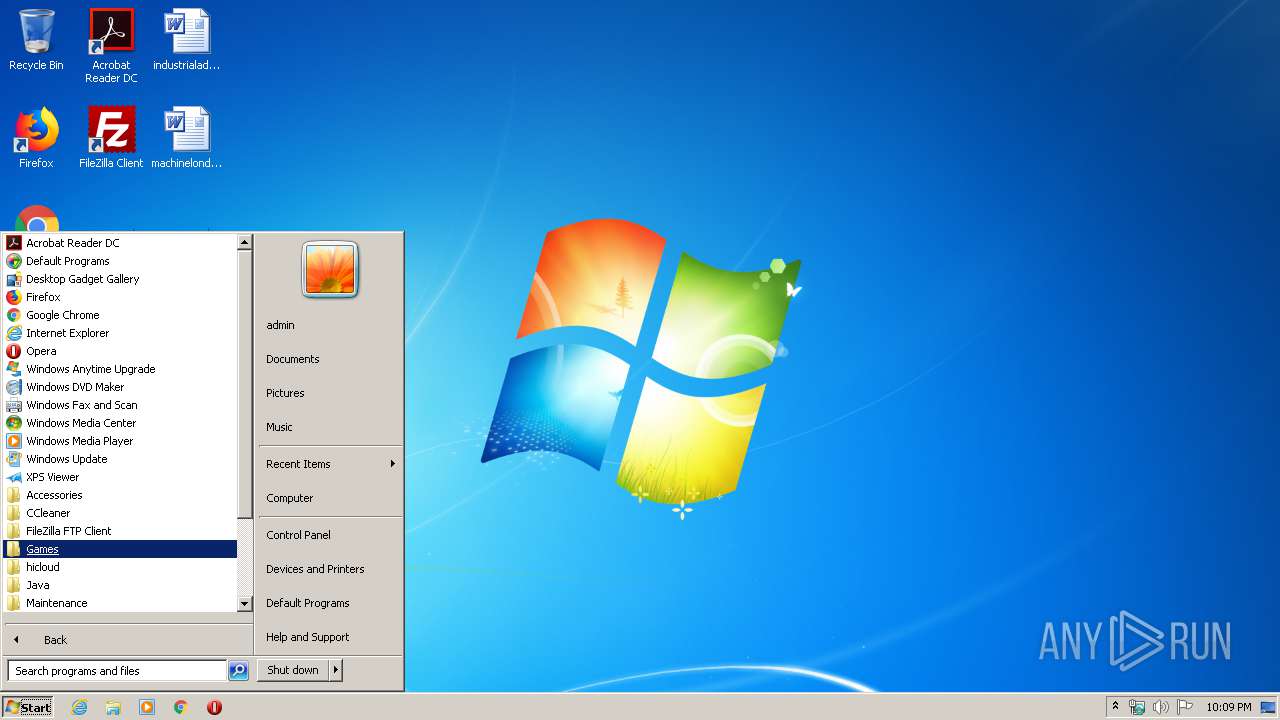
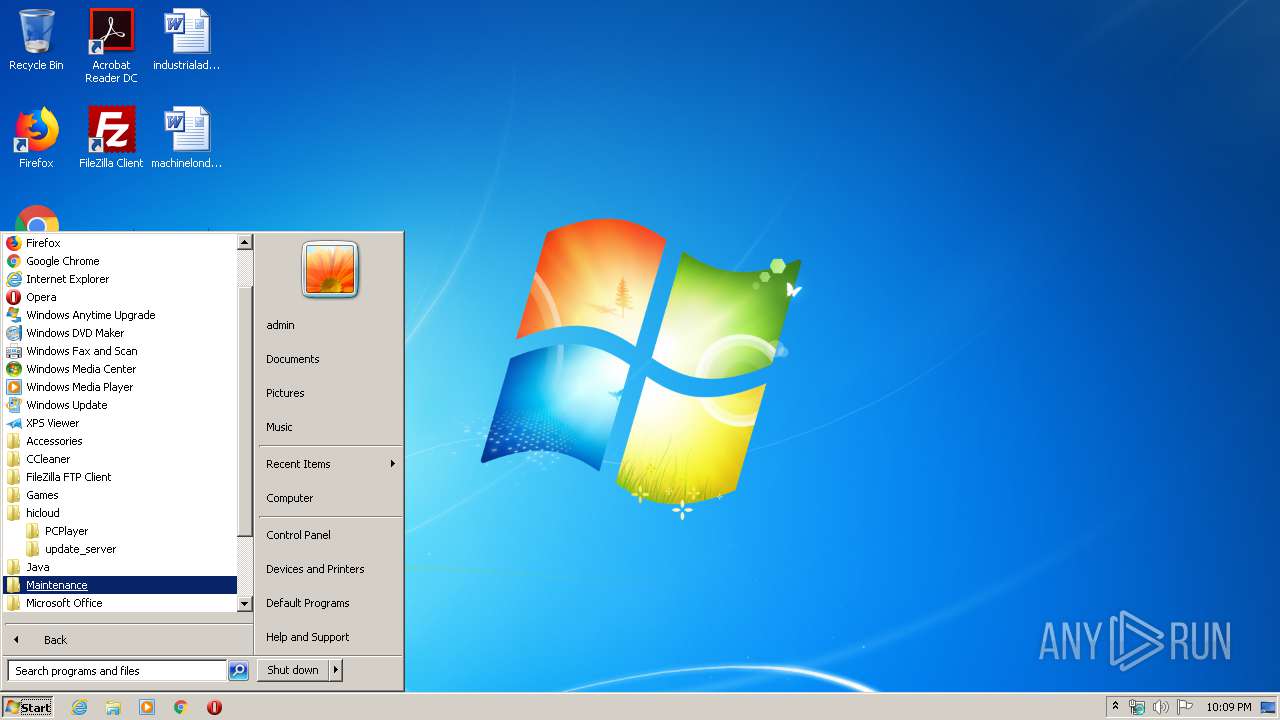
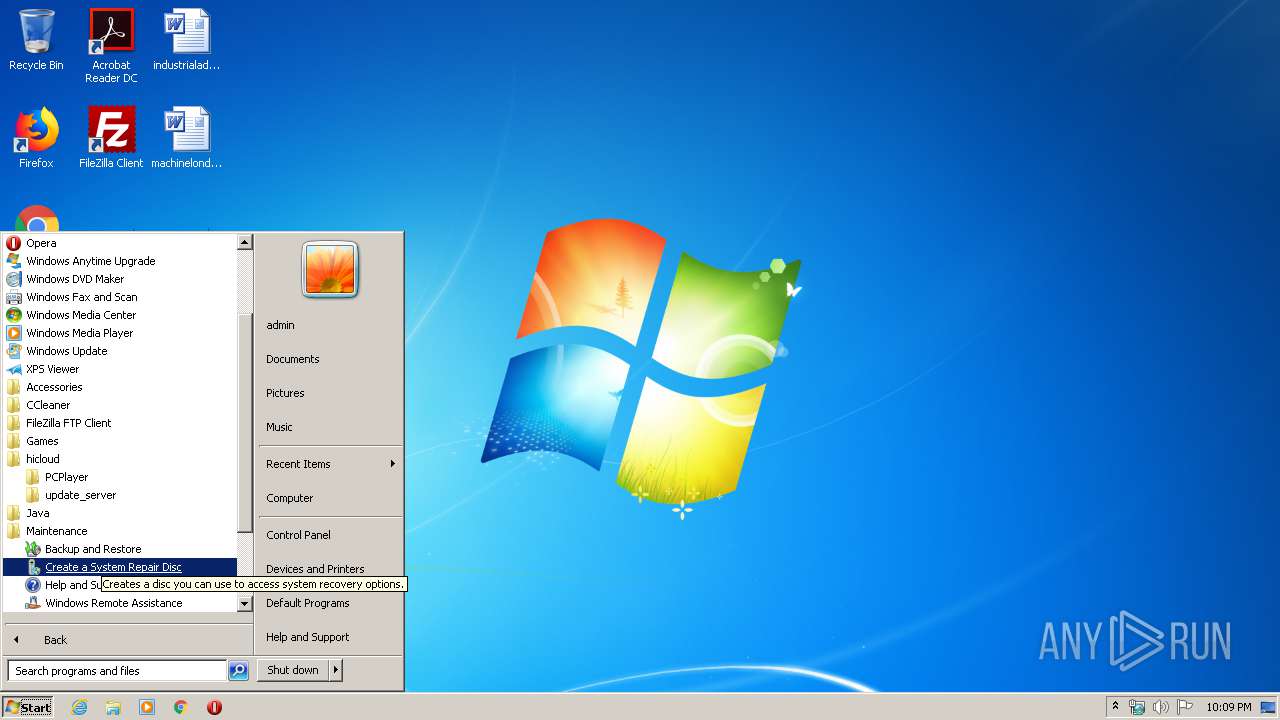
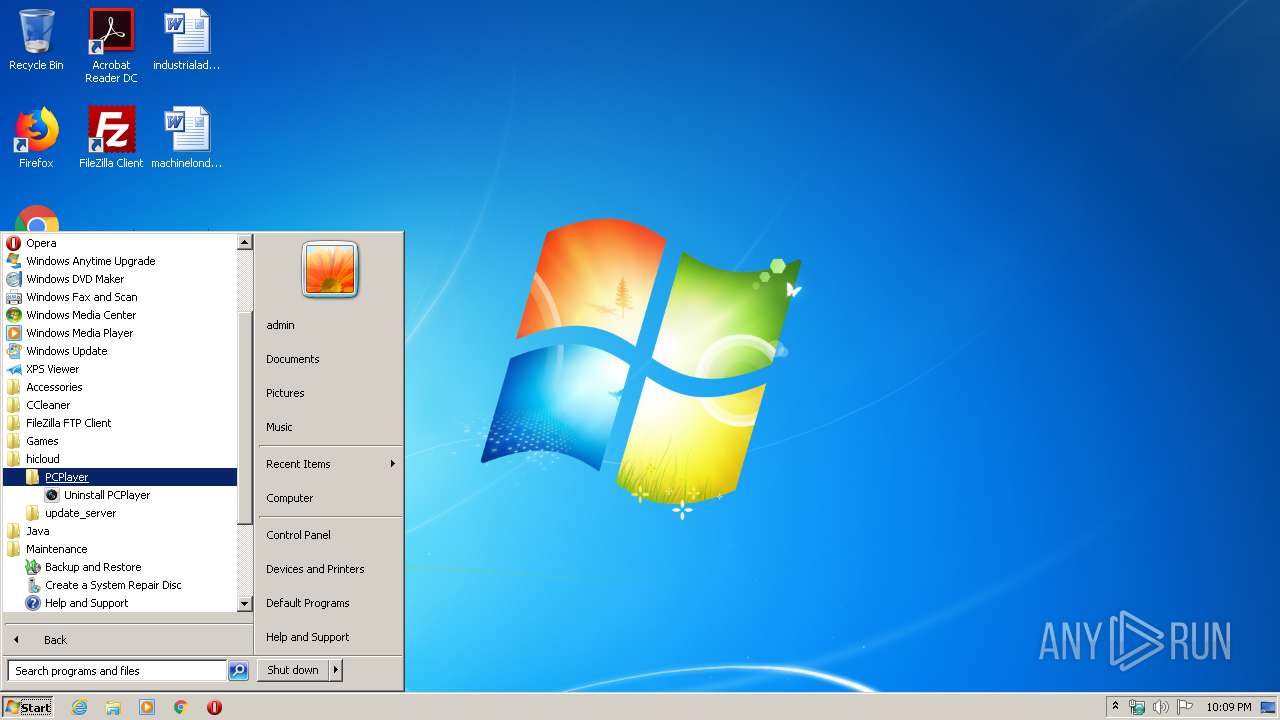
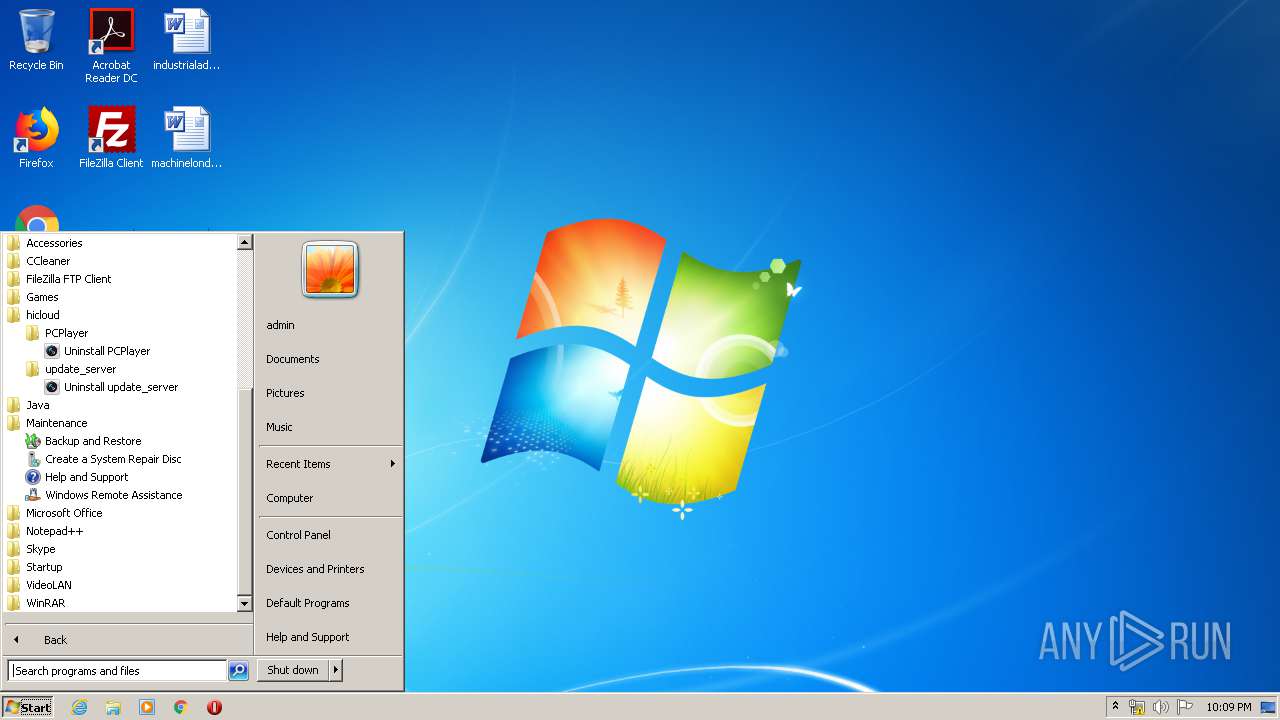
Manual execution by user
- explorer.exe (PID: 1268)
Reads Internet Cache Settings
- iexplore.exe (PID: 3680)
- iexplore.exe (PID: 3184)
- iexplore.exe (PID: 2636)
Creates files in the user directory
- iexplore.exe (PID: 2636)
- iexplore.exe (PID: 3680)
Reads internet explorer settings
- iexplore.exe (PID: 2636)
- iexplore.exe (PID: 3184)
Dropped object may contain TOR URL's
- iexplore.exe (PID: 2636)
Application launched itself
- iexplore.exe (PID: 3680)
Modifies the phishing filter of IE
- iexplore.exe (PID: 3680)
Changes internet zones settings
- iexplore.exe (PID: 3680)
Reads settings of System Certificates
- iexplore.exe (PID: 2636)
- iexplore.exe (PID: 3680)
Changes settings of System certificates
- iexplore.exe (PID: 3680)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3680)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (77.7) |
|---|---|---|
| .exe | | | Win32 Executable Delphi generic (10) |
| .dll | | | Win32 Dynamic Link Library (generic) (4.6) |
| .exe | | | Win32 Executable (generic) (3.1) |
| .exe | | | Win16/32 Executable Delphi generic (1.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 37888 |
| InitializedDataSize: | 14848 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x9b24 |
| OSVersion: | 1 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3.18.11.0 |
| ProductVersionNumber: | 3.18.11.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | EZVIZ Inc. |
| FileDescription: | PCPlayer Setup |
| FileVersion: | 3.18.11.0 |
| LegalCopyright: | |
| ProductName: | PCPlayer |
| ProductVersion: | 3.18.11.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-1992 22:22:17 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | EZVIZ Inc. |
| FileDescription: | PCPlayer Setup |
| FileVersion: | 3.18.11.0 |
| LegalCopyright: | - |
| ProductName: | PCPlayer |
| ProductVersion: | 3.18.11.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 19-Jun-1992 22:22:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 0x00001000 | 0x00009244 | 0x00009400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.52973 |
DATA | 0x0000B000 | 0x0000024C | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.73422 |
BSS | 0x0000C000 | 0x00000E48 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x0000D000 | 0x00000950 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.43073 |
.tls | 0x0000E000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x0000F000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.204488 |
.reloc | 0x00010000 | 0x000008B4 | 0x00000000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0 |
.rsrc | 0x00011000 | 0x00002860 | 0x00002A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 5.78059 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.05007 | 1376 | Latin 1 / Western European | English - United States | RT_MANIFEST |
4089 | 3.21823 | 754 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4090 | 3.31515 | 780 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4091 | 3.25024 | 718 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4093 | 2.86149 | 104 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4094 | 3.20731 | 180 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4095 | 3.04592 | 174 | Latin 1 / Western European | UNKNOWN | RT_STRING |
11111 | 4.59457 | 44 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
MAINICON | 1.7815 | 20 | Latin 1 / Western European | English - United States | RT_GROUP_ICON |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
oleaut32.dll |
user32.dll |
Total processes
63
Monitored processes
21
Malicious processes
9
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 372 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | — | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1268 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1948 | "C:\Program Files\hicloud\PCPlayer\ModProperties.exe" shipin7 | C:\Program Files\hicloud\PCPlayer\ModProperties.exe | PCPlayer.tmp | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2112 | "C:\Users\admin\AppData\Local\Temp\is-M2MGL.tmp\update_server.tmp" /SL5="$70228,2317461,53760,C:\Program Files\hicloud\PCPlayer\update_server.exe" /VERYSILENT | C:\Users\admin\AppData\Local\Temp\is-M2MGL.tmp\update_server.tmp | update_server.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.50.0.0 Modules
| |||||||||||||||
| 2380 | "C:\Program Files\hicloud\PCPlayer\update_server.exe" /VERYSILENT | C:\Program Files\hicloud\PCPlayer\update_server.exe | PCPlayer.tmp | ||||||||||||
User: admin Company: Integrity Level: HIGH Description: update_server Setup Exit code: 0 Version: 1.0.1.17 Modules
| |||||||||||||||
| 2392 | "C:\Users\admin\AppData\Local\Temp\PCPlayer.exe" | C:\Users\admin\AppData\Local\Temp\PCPlayer.exe | explorer.exe | ||||||||||||
User: admin Company: EZVIZ Inc. Integrity Level: MEDIUM Description: PCPlayer Setup Exit code: 0 Version: 3.18.11.0 Modules
| |||||||||||||||
| 2600 | "C:\Users\admin\AppData\Local\Temp\is-B00JB.tmp\PCPlayer.tmp" /SL5="$90140,12816275,53760,C:\Users\admin\AppData\Local\Temp\PCPlayer.exe" | C:\Users\admin\AppData\Local\Temp\is-B00JB.tmp\PCPlayer.tmp | — | PCPlayer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.50.0.0 Modules
| |||||||||||||||
| 2636 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3680 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2876 | "C:\Program Files\hicloud\update_server\ModProperties.exe" update_server | C:\Program Files\hicloud\update_server\ModProperties.exe | update_server.tmp | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3000 | "C:\Program Files\hicloud\PCPlayer\ModProperties.exe" | C:\Program Files\hicloud\PCPlayer\ModProperties.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
11 438
Read events
5 447
Write events
4 278
Delete events
1 713
Modification events
| (PID) Process: | (372) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3852) PCPlayer.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\MozillaPlugins\shipin7 |
| Operation: | write | Name: | Path |
Value: C:\Program Files\hicloud\PCPlayer\npSP7WebVideoPlugin.dll | |||
| (PID) Process: | (3852) PCPlayer.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\MozillaPlugins\shipin7update |
| Operation: | write | Name: | Path |
Value: C:\Program Files\hicloud\PCPlayer\npUpdataPlugin.dll | |||
| (PID) Process: | (3852) PCPlayer.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\MozillaPlugins\shipin7safebox |
| Operation: | write | Name: | Path |
Value: C:\Program Files\hicloud\PCPlayer\npSafePlugin.dll | |||
| (PID) Process: | (3852) PCPlayer.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\shipin7\shipin7_player |
| Operation: | write | Name: | InstallPath |
Value: C:\Program Files\hicloud\PCPlayer | |||
| (PID) Process: | (3852) PCPlayer.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\shipin7\shipin7_player |
| Operation: | write | Name: | ClientType |
Value: PCPlayer | |||
| (PID) Process: | (3852) PCPlayer.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\shipin7\shipin7_player |
| Operation: | write | Name: | ClientVision |
Value: 3.18.11.0 | |||
| (PID) Process: | (3852) PCPlayer.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\shipin7\shipin7_player |
| Operation: | write | Name: | ClientKey |
Value: 0 | |||
| (PID) Process: | (3756) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\TypeLib\{63CEA1AF-4FF9-428E-985A-14F86BF99716}\1.0 |
| Operation: | write | Name: | |
Value: SafePWSBox ActiveX Control module | |||
| (PID) Process: | (3756) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\TypeLib\{63CEA1AF-4FF9-428E-985A-14F86BF99716}\1.0\FLAGS |
| Operation: | write | Name: | |
Value: 2 | |||
Executable files
94
Suspicious files
53
Text files
339
Unknown types
26
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3852 | PCPlayer.tmp | C:\Program Files\hicloud\PCPlayer\is-U6U69.tmp | — | |
MD5:— | SHA256:— | |||
| 3852 | PCPlayer.tmp | C:\Program Files\hicloud\PCPlayer\is-2PS83.tmp | — | |
MD5:— | SHA256:— | |||
| 3852 | PCPlayer.tmp | C:\Program Files\hicloud\PCPlayer\is-3M3SE.tmp | — | |
MD5:— | SHA256:— | |||
| 3852 | PCPlayer.tmp | C:\Program Files\hicloud\PCPlayer\is-AA8QA.tmp | — | |
MD5:— | SHA256:— | |||
| 3852 | PCPlayer.tmp | C:\Program Files\hicloud\PCPlayer\HCNetSDKCom\is-HI391.tmp | — | |
MD5:— | SHA256:— | |||
| 3852 | PCPlayer.tmp | C:\Program Files\hicloud\PCPlayer\HCNetSDKCom\is-39OGQ.tmp | — | |
MD5:— | SHA256:— | |||
| 3852 | PCPlayer.tmp | C:\Program Files\hicloud\PCPlayer\HCNetSDKCom\is-IOVF2.tmp | — | |
MD5:— | SHA256:— | |||
| 3852 | PCPlayer.tmp | C:\Program Files\hicloud\PCPlayer\is-Q0PQF.tmp | — | |
MD5:— | SHA256:— | |||
| 3852 | PCPlayer.tmp | C:\Program Files\hicloud\PCPlayer\is-FERON.tmp | — | |
MD5:— | SHA256:— | |||
| 3852 | PCPlayer.tmp | C:\Program Files\hicloud\PCPlayer\is-854AA.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
66
TCP/UDP connections
109
DNS requests
33
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2636 | iexplore.exe | GET | 302 | 2.19.38.59:80 | http://go.microsoft.com/fwlink/?LinkId=57426&Ext=cur | unknown | — | — | whitelisted |
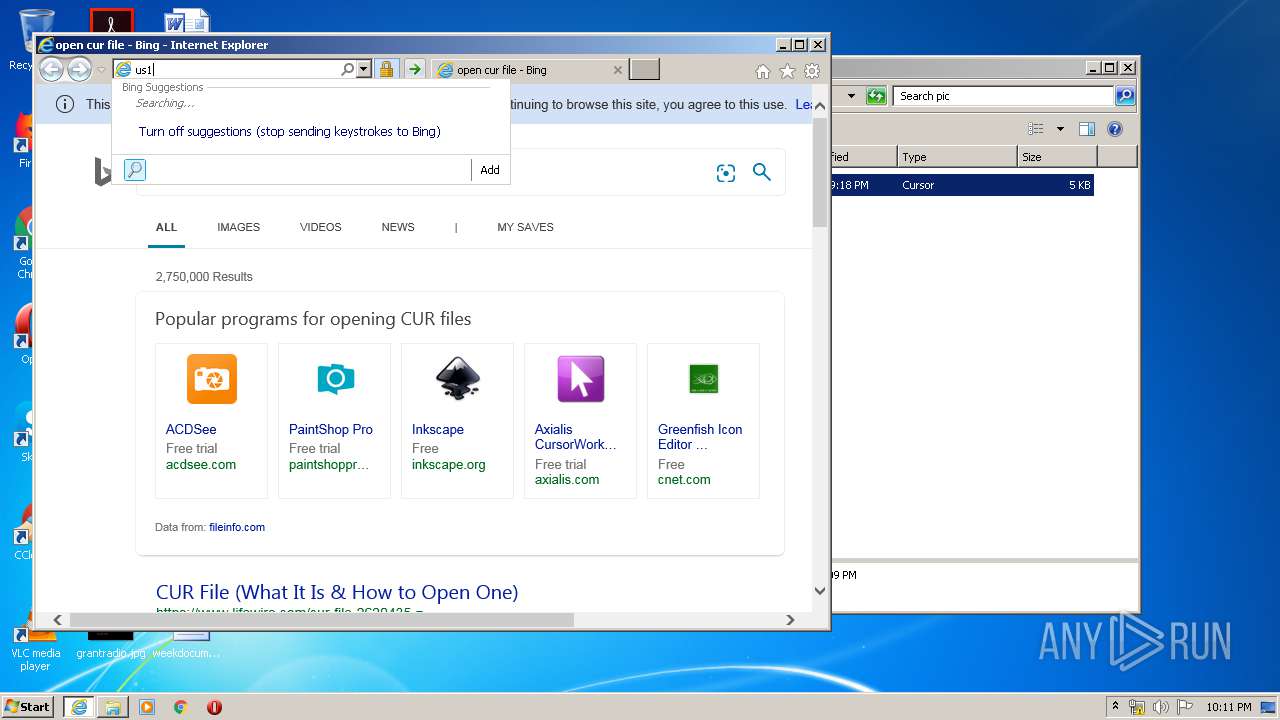
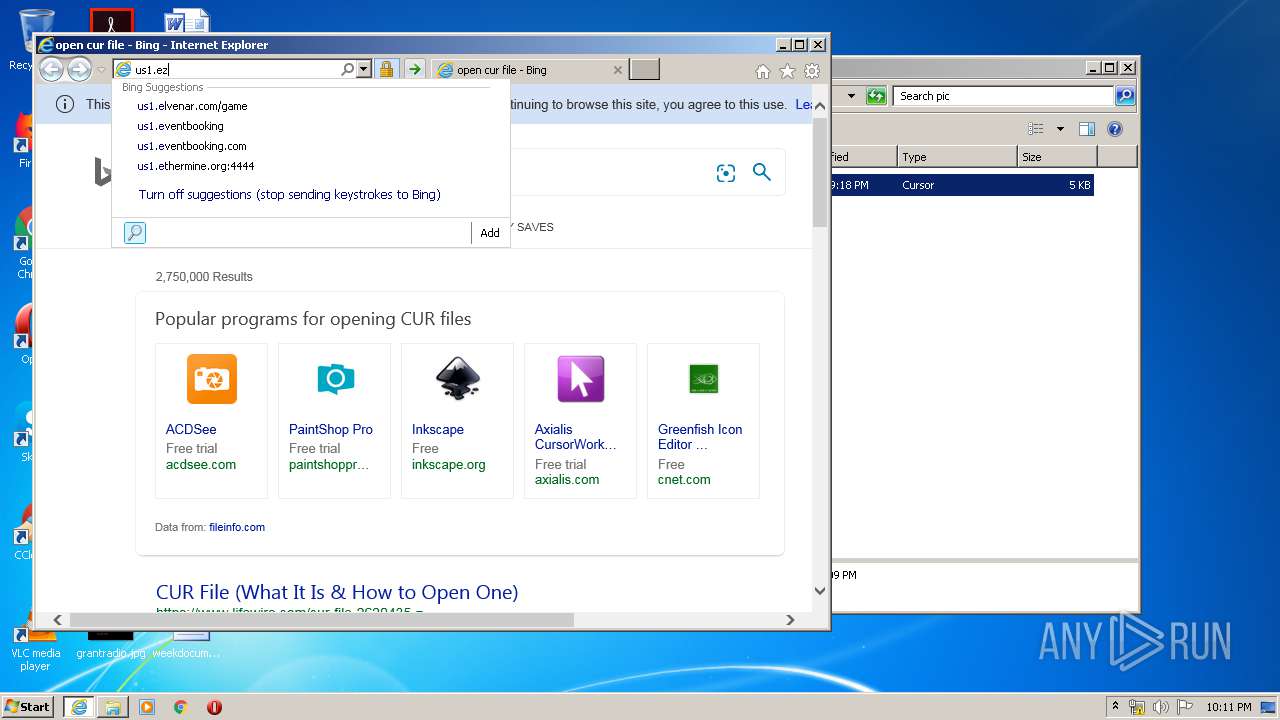
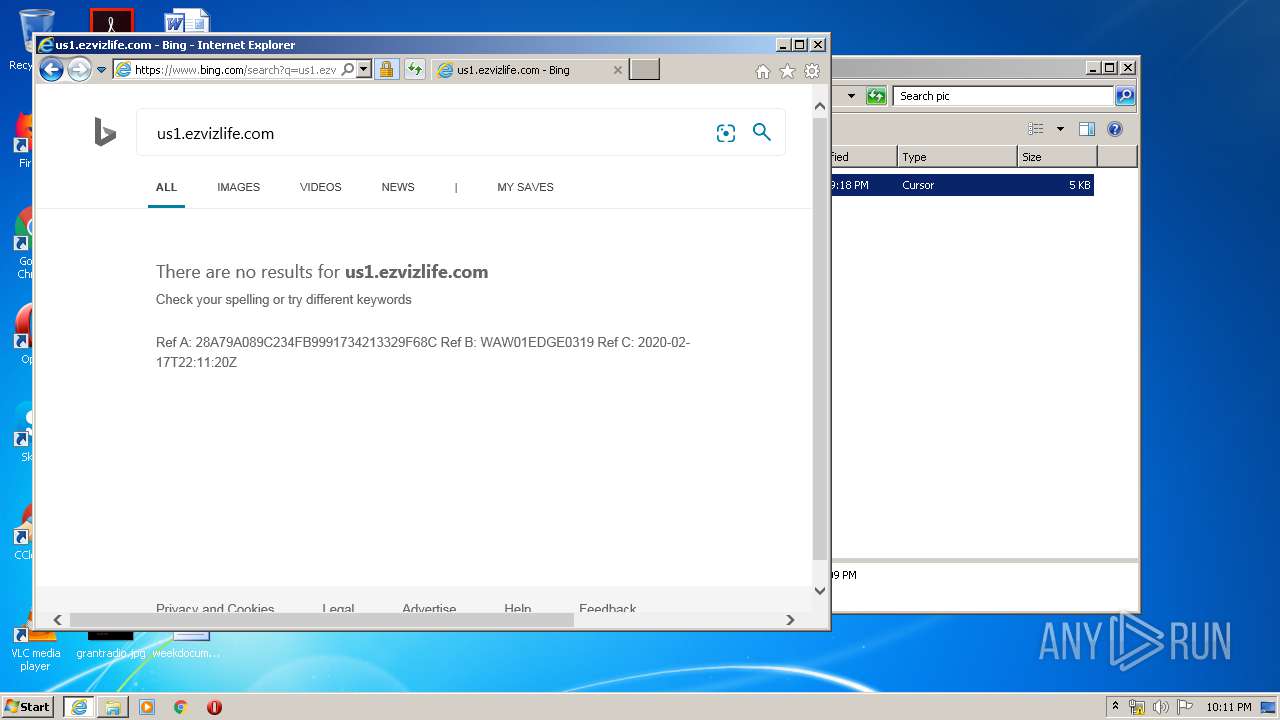
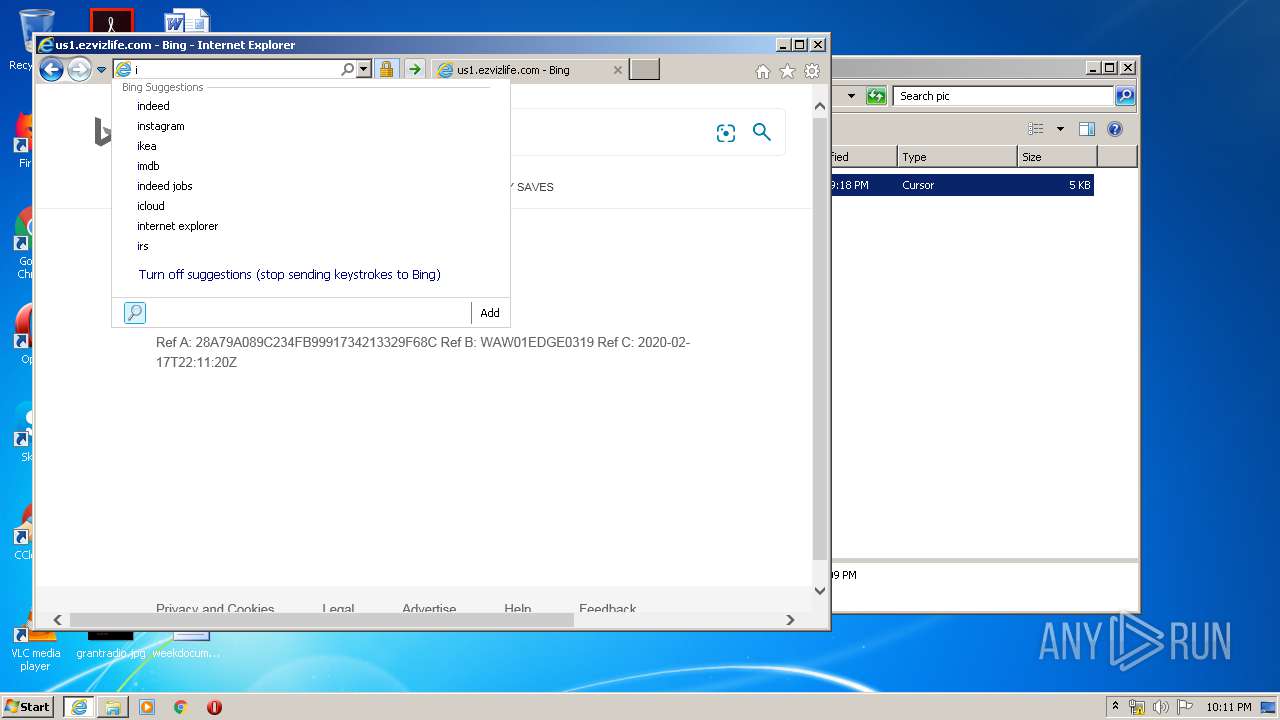
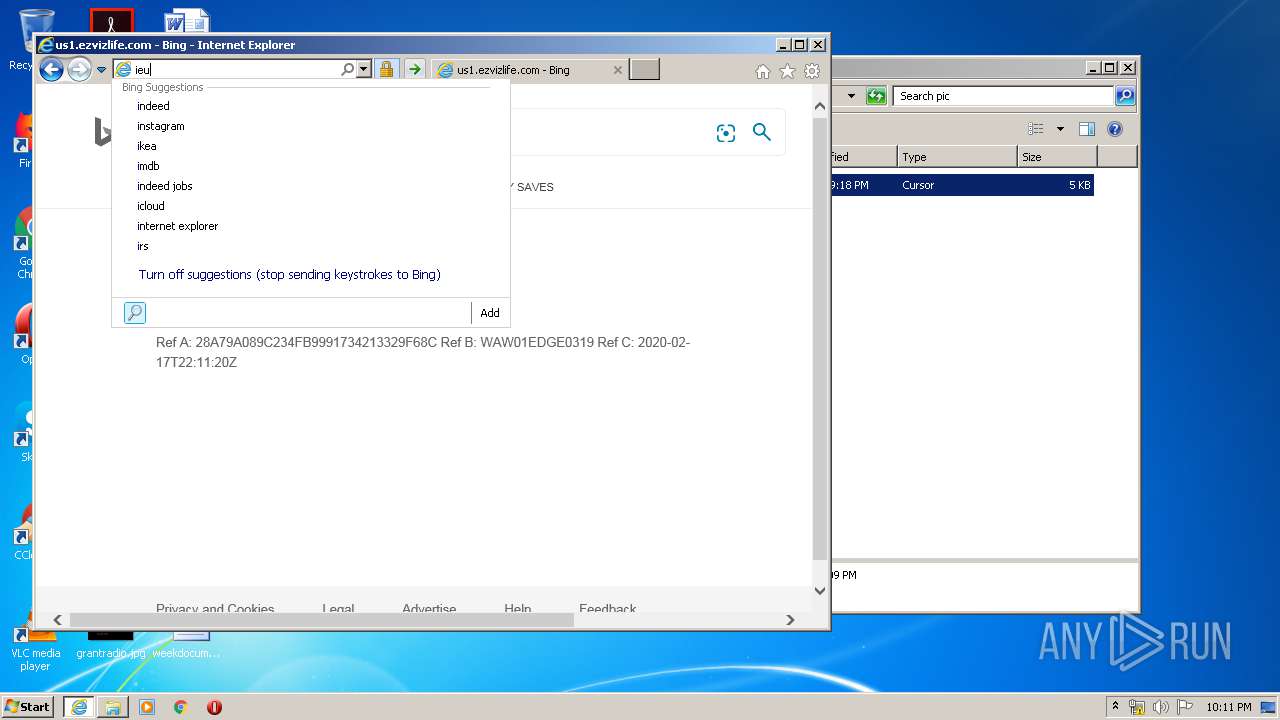
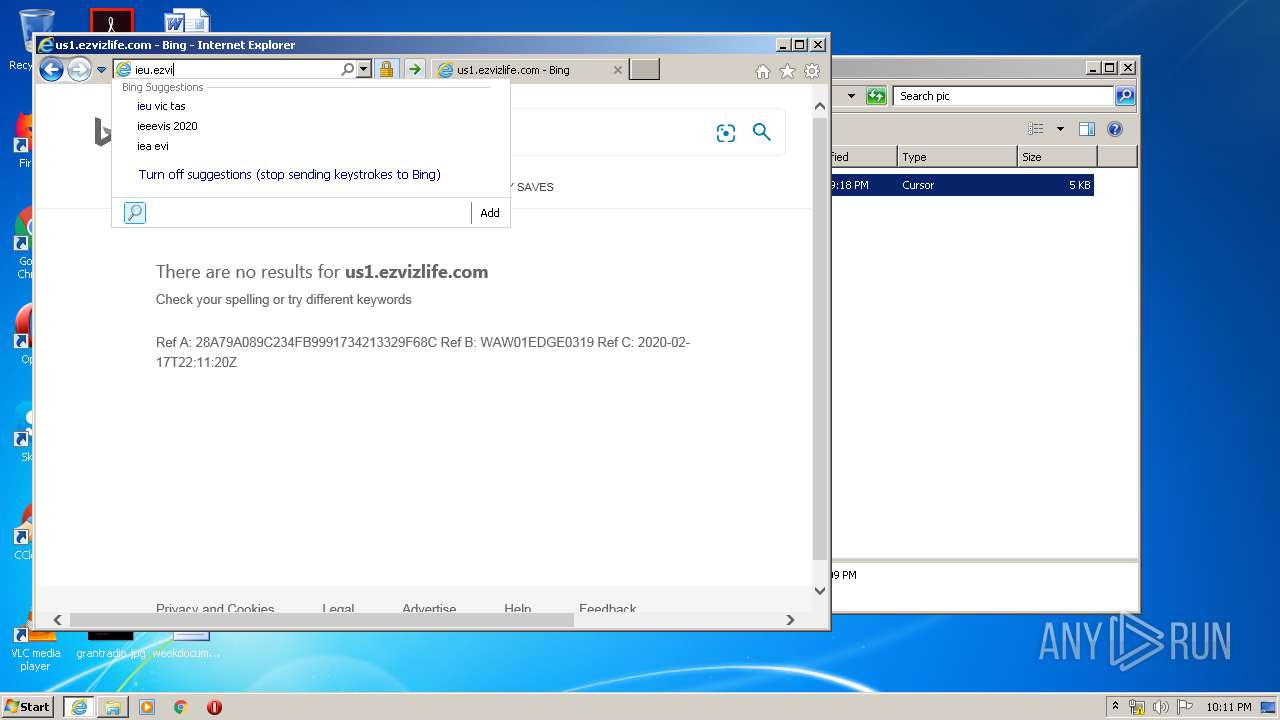
2636 | iexplore.exe | GET | — | 13.107.5.80:80 | http://api.bing.com/qsml.aspx?query=us1.ezvi&maxwidth=32765&rowheight=20§ionHeight=160&FORM=IE11SS&market=en-US | US | — | — | whitelisted |
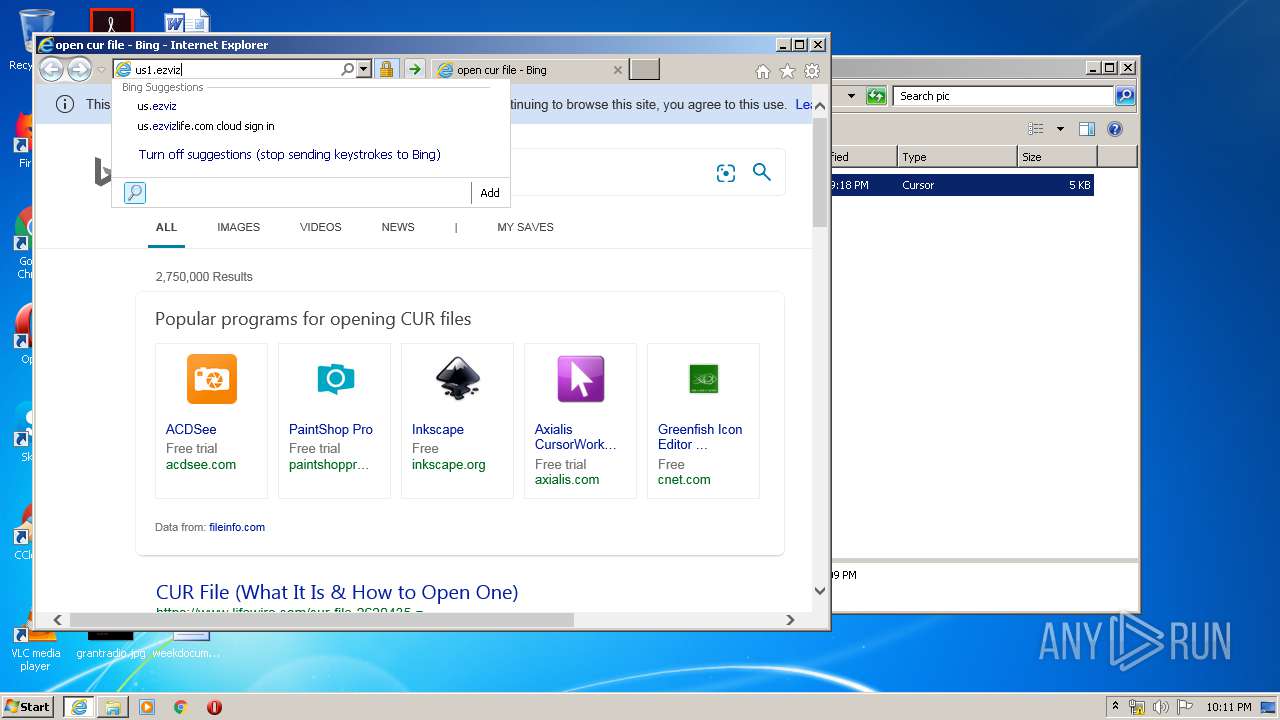
2636 | iexplore.exe | GET | — | 13.107.5.80:80 | http://api.bing.com/qsml.aspx?query=us1.ezvizl&maxwidth=32765&rowheight=20§ionHeight=160&FORM=IE11SS&market=en-US | US | — | — | whitelisted |
2636 | iexplore.exe | GET | — | 13.107.5.80:80 | http://api.bing.com/qsml.aspx?query=us1.ezvizlif&maxwidth=32765&rowheight=20§ionHeight=160&FORM=IE11SS&market=en-US | US | — | — | whitelisted |
2636 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAi4elAbvpzaLRZNPjlRv1U%3D | US | der | 1.47 Kb | whitelisted |
2636 | iexplore.exe | GET | 200 | 104.18.25.243:80 | http://ocsp.msocsp.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBRPC1vZt9qvn7bzY3Iidtbhla4mKQQUWIif1tycSCK3FD7%2FhIjo5oX%2F%2Bn0CE3sAAvTsRon4%2BRVzrdwAAAAC9Ow%3D | US | der | 1.79 Kb | whitelisted |
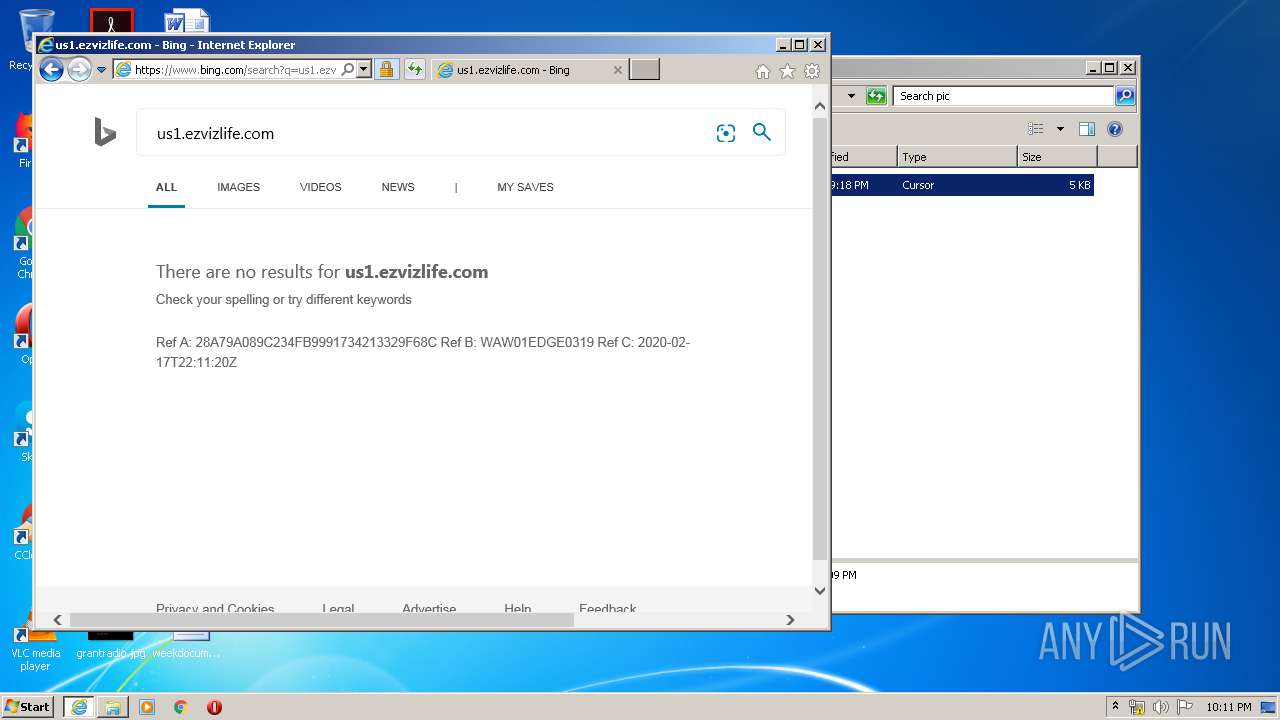
2636 | iexplore.exe | GET | 200 | 13.107.5.80:80 | http://api.bing.com/qsml.aspx?query=us1.&maxwidth=32765&rowheight=20§ionHeight=160&FORM=IE11SS&market=en-US | US | xml | 229 b | whitelisted |
2636 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
2636 | iexplore.exe | GET | 304 | 104.18.25.243:80 | http://ocsp.msocsp.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBRPC1vZt9qvn7bzY3Iidtbhla4mKQQUWIif1tycSCK3FD7%2FhIjo5oX%2F%2Bn0CE3sAAvTsRon4%2BRVzrdwAAAAC9Ow%3D | US | der | 1.79 Kb | whitelisted |
2636 | iexplore.exe | GET | 200 | 13.107.5.80:80 | http://api.bing.com/qsml.aspx?query=us1&maxwidth=32765&rowheight=20§ionHeight=160&FORM=IE11SS&market=en-US | US | xml | 228 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 2.16.186.27:80 | shell.windows.com | Akamai International B.V. | — | whitelisted |
2636 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2636 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
2636 | iexplore.exe | 20.190.129.162:443 | login.microsoftonline.com | Microsoft Corporation | US | unknown |
3680 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
2636 | iexplore.exe | 40.90.23.154:443 | login.live.com | Microsoft Corporation | US | unknown |
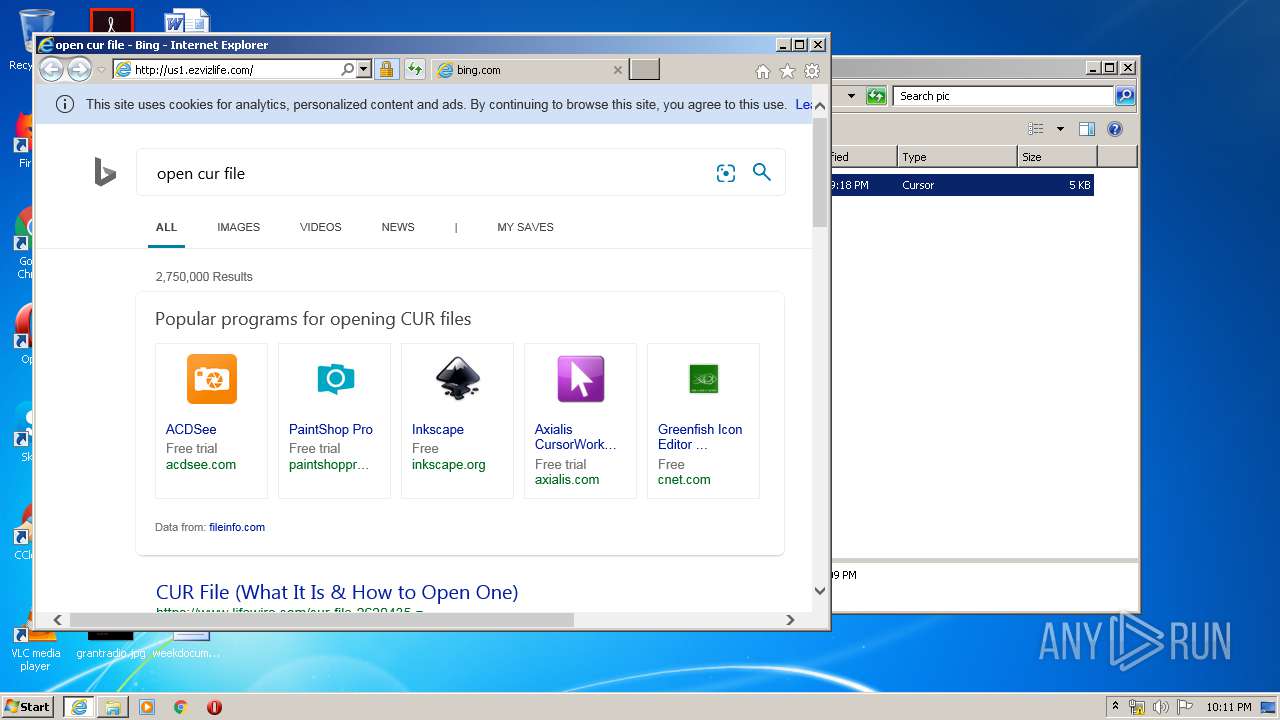
2636 | iexplore.exe | 52.209.20.225:80 | ieu.ezvizlife.com | Amazon.com, Inc. | IE | unknown |
2636 | iexplore.exe | 23.45.103.47:80 | ocsp.entrust.net | Akamai International B.V. | NL | unknown |
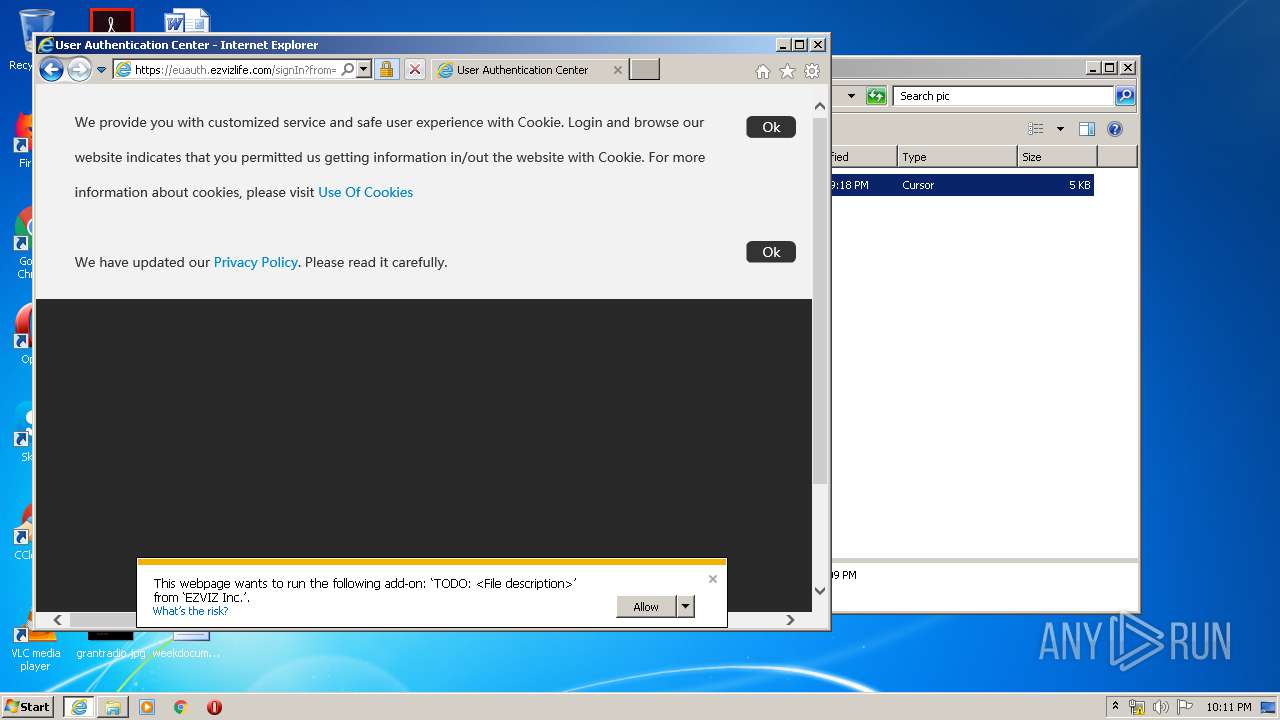
2636 | iexplore.exe | 52.209.218.248:443 | euauth.ezvizlife.com | Amazon.com, Inc. | IE | unknown |
2636 | iexplore.exe | 52.209.20.225:443 | ieu.ezvizlife.com | Amazon.com, Inc. | IE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
api.ezviz7.com |
| unknown |
go.microsoft.com |
| whitelisted |
shell.windows.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.microsoftonline.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.msocsp.com |
| whitelisted |
api.bing.com |
| whitelisted |
www2.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3184 | iexplore.exe | Potentially Bad Traffic | ET POLICY Executable served from Amazon S3 |
3184 | iexplore.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
Process | Message |
|---|---|
regsvr32.exe | CWebVideoActiveXApp::InitInstance 1
|
regsvr32.exe | enter config parse: |
regsvr32.exe | enter CLocalConfig constructor |
regsvr32.exe | [3836] NS ERROR <GetMemoryIncrease> <943>,GetMomoryIncrease Failed
|
regsvr32.exe | [3836] NS ERROR <GetMemoryIncrease> <943>,GetMomoryIncrease Failed
|
regsvr32.exe | [3836] NS ERROR <GetMemoryIncrease> <943>,GetMomoryIncrease Failed
|
regsvr32.exe | [3836] NS ERROR <GetMemoryIncrease> <943>,GetMomoryIncrease Failed
|
regsvr32.exe | [3836] NS ERROR <GetMemoryIncrease> <943>,GetMomoryIncrease Failed
|
regsvr32.exe | [3836] NS INFO <SoundConfig::SoundConfig> <88>,sound config file path:C:\Users\admin\HicloudConfig\soundconfig.xml
|
regsvr32.exe | [3836] NS ERROR <GetMemoryIncrease> <943>,GetMomoryIncrease Failed
|