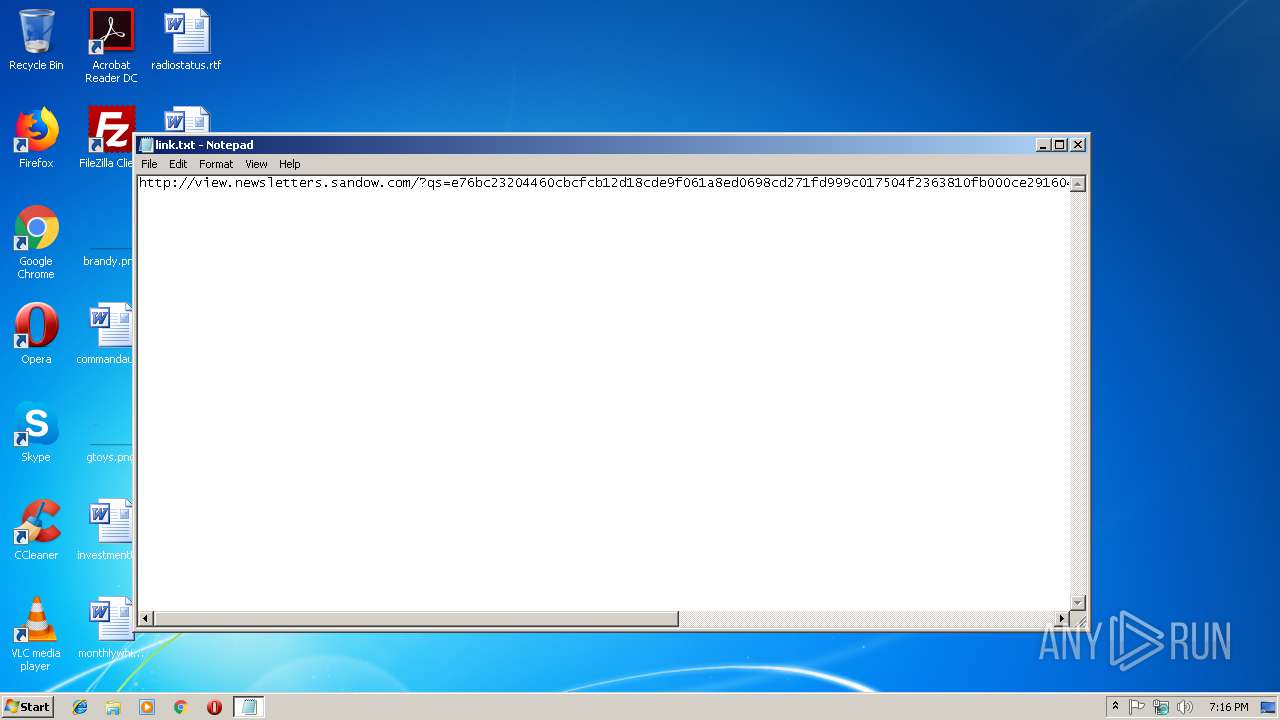
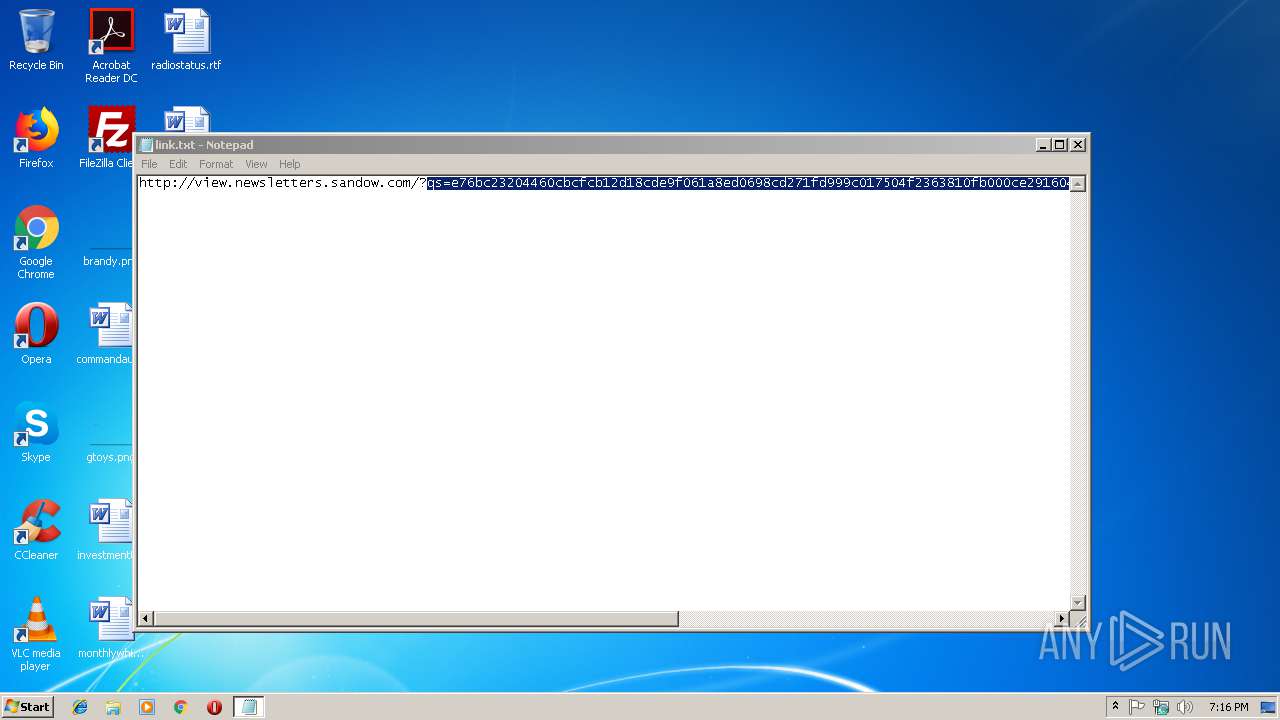
| File name: | link.txt |
| Full analysis: | https://app.any.run/tasks/25a147d6-3ad5-4463-83f6-0d1c3f9a2e47 |
| Verdict: | Malicious activity |
| Analysis date: | February 18, 2019, 19:15:59 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text |
| MD5: | D283AF5D7BEBDB0C529696D2587BE5C9 |
| SHA1: | 09BB5B9163F37434E0E385DAE61CCF24CBFF7DD9 |
| SHA256: | CD82866604A5D647B1287446D467A7315EEBF70A030DE49A2B9A3BBF7097B196 |
| SSDEEP: | 6:CICsYTLMO1eQOOpNPWVTsylvnRQs4piopFWAa6Z:dUTLMXOjOVFxh4piO1t |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Reads settings of System Certificates
- chrome.exe (PID: 2272)
Application launched itself
- chrome.exe (PID: 2272)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
41
Monitored processes
12
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1488 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1012,12277141311165040025,4549092249178412732,131072 --enable-features=PasswordImport --disable-gpu-sandbox --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=ADD55347E4C540CC155B2F3AAE711926 --mojo-platform-channel-handle=3860 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2192 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,12277141311165040025,4549092249178412732,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=B250E93BD2743EAC6506161783373AD3 --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=B250E93BD2743EAC6506161783373AD3 --renderer-client-id=6 --mojo-platform-channel-handle=3524 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2272 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2288 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,12277141311165040025,4549092249178412732,131072 --enable-features=PasswordImport --service-pipe-token=BD4228273279D117DEC392AB7F7D6E3B --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=BD4228273279D117DEC392AB7F7D6E3B --renderer-client-id=5 --mojo-platform-channel-handle=1900 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2300 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2280 --on-initialized-event-handle=304 --parent-handle=308 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2576 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,12277141311165040025,4549092249178412732,131072 --enable-features=PasswordImport --service-pipe-token=3103128A9145D3E137824612F24312FB --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3103128A9145D3E137824612F24312FB --renderer-client-id=3 --mojo-platform-channel-handle=2016 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2960 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\AppData\Local\Temp\link.txt | C:\Windows\system32\NOTEPAD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3048 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=68.0.3440.106 --initial-client-data=0x78,0x7c,0x80,0x74,0x84,0x6f4300b0,0x6f4300c0,0x6f4300cc | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3236 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,12277141311165040025,4549092249178412732,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=86CC0B9465A50DB22900C6F0F0604867 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=86CC0B9465A50DB22900C6F0F0604867 --renderer-client-id=9 --mojo-platform-channel-handle=3840 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3444 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1012,12277141311165040025,4549092249178412732,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=3D7CEA94AD4043EF58B5F278882999DE --mojo-platform-channel-handle=952 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
Total events
529
Read events
483
Write events
43
Delete events
3
Modification events
| (PID) Process: | (2272) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2272) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2272) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2300) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2272-13194990985053250 |
Value: 259 | |||
| (PID) Process: | (2272) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2272) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2272) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3516-13180984670829101 |
Value: 0 | |||
| (PID) Process: | (2272) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2272) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2272-13194990985053250 |
Value: 259 | |||
| (PID) Process: | (2272) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
0
Suspicious files
59
Text files
88
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2272 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\b17b3723-2d5a-49ba-bc99-0e77af1cae12.tmp | — | |
MD5:— | SHA256:— | |||
| 2272 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2272 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2272 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\3b3f5763-dde9-4384-b313-ebd9d3b1692e.tmp | — | |
MD5:— | SHA256:— | |||
| 2272 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2272 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\CacheStorage\e6622492fa163609ddd4212f54512baa07929ed3\caecb3bd-7969-4305-84d6-3a376453ec73\index-dir\temp-index | — | |
MD5:— | SHA256:— | |||
| 2272 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF249154.TMP | text | |
MD5:— | SHA256:— | |||
| 2272 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2272 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF249125.TMP | text | |
MD5:— | SHA256:— | |||
| 2272 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old~RF249154.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
16
TCP/UDP connections
109
DNS requests
74
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
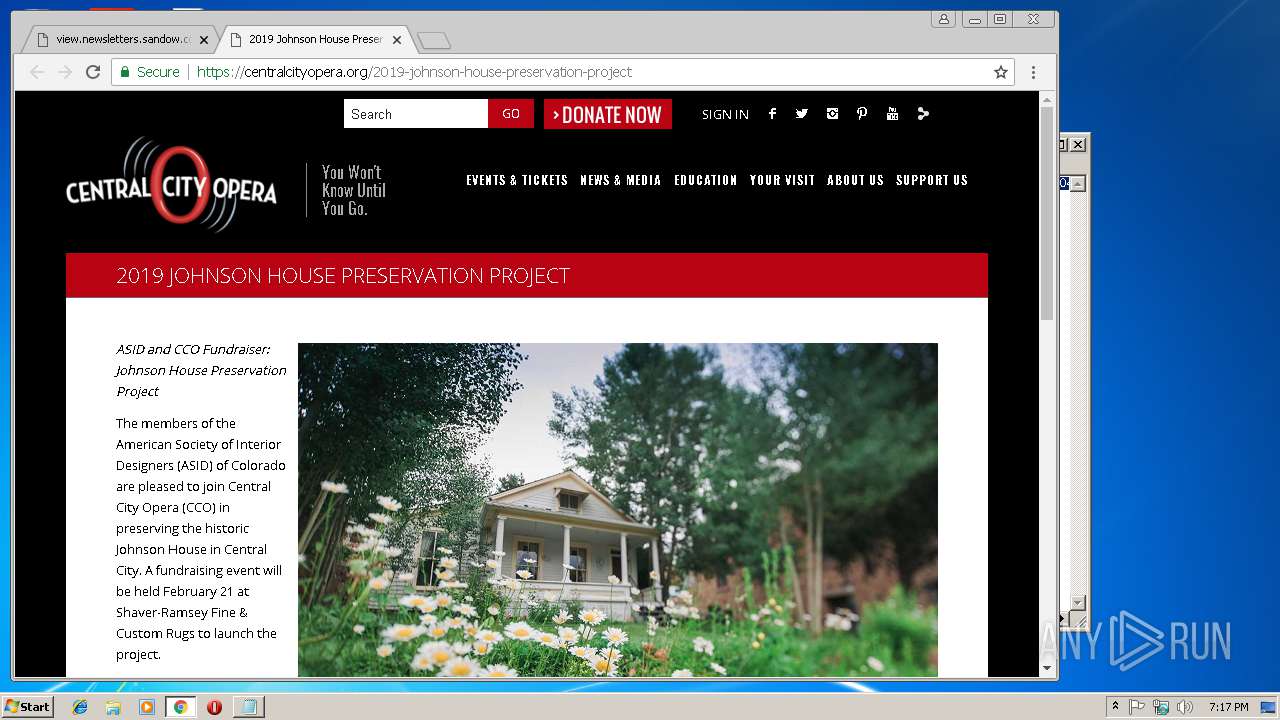
2272 | chrome.exe | GET | 200 | 136.147.129.32:80 | http://view.newsletters.sandow.com/?qs=e76bc23204460cbcfcb12d18cde9f061a8ed0698cd271fd999c017504f2363810fb000ce291604ad050452e29b86eeee5700c6c3d5a706f349c72eb20bd088f766ae661c04b434e2248c4e3a69231f27 | US | html | 31.1 Kb | unknown |
2272 | chrome.exe | GET | 200 | 2.16.186.120:80 | http://image.newsletters.sandow.com/lib/fe9d13727464017d76/m/17/97ca7365-cf6b-4636-bdb5-033963653edc.jpg | unknown | image | 11.8 Kb | whitelisted |
2272 | chrome.exe | GET | 200 | 2.16.186.120:80 | http://image.newsletters.sandow.com/lib/fe9d13727464017d76/m/17/6a21127c-e1f0-4786-8ea1-969199aec65d.jpg | unknown | image | 10.1 Kb | whitelisted |
2272 | chrome.exe | GET | 200 | 2.16.186.120:80 | http://image.newsletters.sandow.com/lib/fe9d13727464017d76/m/17/7e2c6ac2-fdd7-4be2-97f1-a1d093d06a71.jpg | unknown | image | 14.3 Kb | whitelisted |
2272 | chrome.exe | GET | 200 | 2.16.186.120:80 | http://image.newsletters.sandow.com/lib/fe9d13727464017d76/m/17/3753fbde-3aaf-468f-a623-5bb8db59e1e0.jpg | unknown | image | 11.9 Kb | whitelisted |
2272 | chrome.exe | GET | 200 | 2.16.186.120:80 | http://image.newsletters.sandow.com/lib/fe9d13727464017d76/m/17/37fde2b4-1b3d-4fdf-a450-acc2c0c49aa6.jpg | unknown | image | 8.84 Kb | whitelisted |
2272 | chrome.exe | GET | 302 | 2.16.106.112:80 | http://click.newsletters.sandow.com/?qs=d276e98123b7726a5a875018281773aa73c97a1b09d0940df0b571d1d583705c5b335a3240e074546488f730e7067dbb7f056df4c523dd74 | unknown | html | 185 b | whitelisted |
2272 | chrome.exe | GET | 200 | 2.16.186.120:80 | http://image.newsletters.sandow.com/lib/fe9d13727464017d76/m/17/2e1b51ab-bb55-42a2-85de-03fac1642b09.jpg | unknown | image | 67.1 Kb | whitelisted |
2272 | chrome.exe | GET | 200 | 93.184.221.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 55.2 Kb | whitelisted |
2272 | chrome.exe | GET | 200 | 2.16.106.112:80 | http://click.newsletters.sandow.com/open.aspx?ffcb10-fe8d15727d600d7474-fe5f157776640c7a7710-fe9d13727464017d76-ff5d15787c-fe5f15707c60027a7014-ffce15 | unknown | image | 43 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2272 | chrome.exe | 172.217.16.131:443 | www.google.de | Google Inc. | US | whitelisted |
2272 | chrome.exe | 172.217.22.10:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
2272 | chrome.exe | 216.58.207.45:443 | accounts.google.com | Google Inc. | US | whitelisted |
2272 | chrome.exe | 172.217.22.3:443 | www.google.fr | Google Inc. | US | whitelisted |
2272 | chrome.exe | 172.217.16.142:443 | apis.google.com | Google Inc. | US | whitelisted |
2272 | chrome.exe | 136.147.129.32:80 | view.newsletters.sandow.com | ExactTarget, Inc. | US | unknown |
2272 | chrome.exe | 172.217.18.10:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2272 | chrome.exe | 172.217.18.3:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2272 | chrome.exe | 2.16.186.120:80 | image.newsletters.sandow.com | Akamai International B.V. | — | whitelisted |
2272 | chrome.exe | 54.192.95.100:443 | cdn2.webdamdb.com | Amazon.com, Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
www.google.de |
| whitelisted |
www.gstatic.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
ssl.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
www.google.com |
| malicious |
www.google.fr |
| whitelisted |
fonts.googleapis.com |
| whitelisted |