| File name: | AutoClicker-3.1.1.exe |
| Full analysis: | https://app.any.run/tasks/0ee526b0-69d4-4c9c-8cd3-cbe3bd1b77e4 |
| Verdict: | Malicious activity |
| Analysis date: | August 16, 2025, 16:56:12 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 4 sections |
| MD5: | 9B2946BB3D8AE8D01F3D64FC6DEE2C9E |
| SHA1: | A62BE821AEB5667D445FC6710018B3CDCE66E417 |
| SHA256: | CD6BA78EA24A28B76160D343D46CFB16DF91B123AFD9BDE2AD234CCCD8D82083 |
| SSDEEP: | 24576:ngbEyQpu8U5uWicSSdhQ+prWbOT23S7JN+EKqvCr9xUQp4JghhGWBinSw+B++LC8:ngbEpu8U5uWicSSdhQ+prWbOT23S7JNk |
MALICIOUS
No malicious indicators.SUSPICIOUS
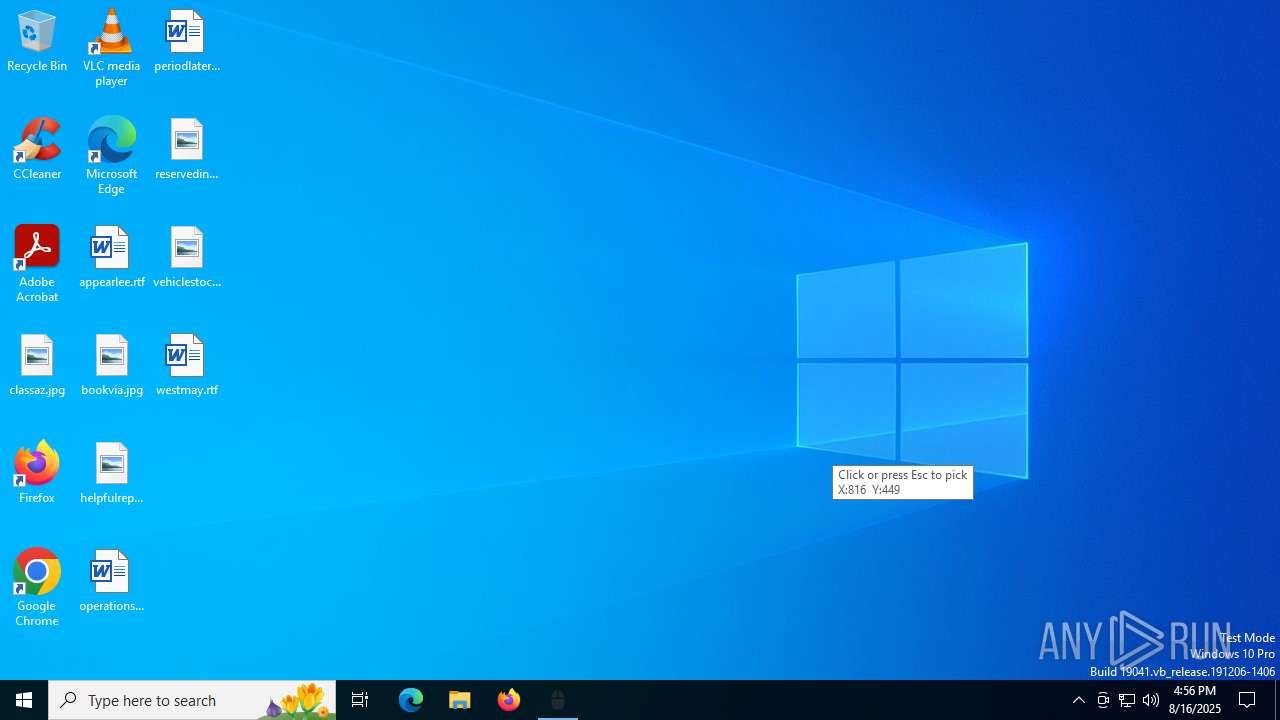
There is functionality for taking screenshot (YARA)
- AutoClicker-3.1.1.exe (PID: 5456)
INFO
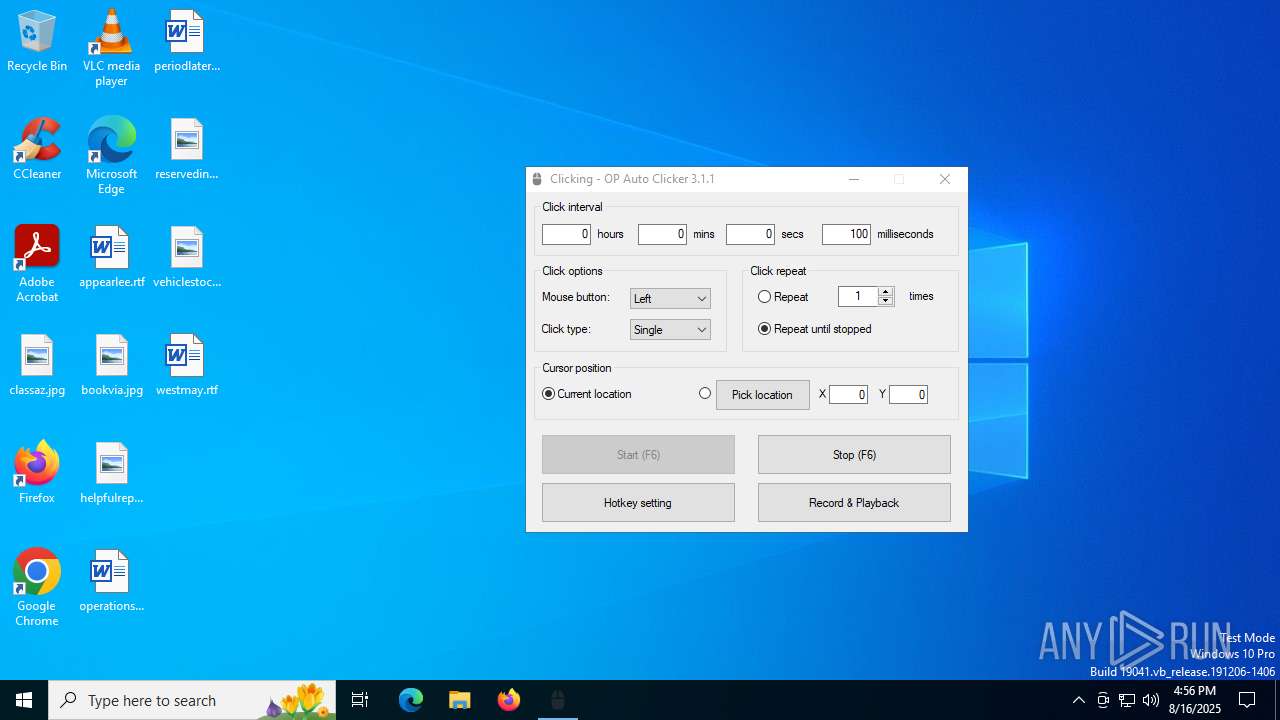
Reads mouse settings
- AutoClicker-3.1.1.exe (PID: 5456)
Reads the computer name
- AutoClicker-3.1.1.exe (PID: 5456)
Create files in a temporary directory
- AutoClicker-3.1.1.exe (PID: 5456)
Checks supported languages
- AutoClicker-3.1.1.exe (PID: 5456)
The process uses AutoIt
- AutoClicker-3.1.1.exe (PID: 5456)
The sample compiled with english language support
- AutoClicker-3.1.1.exe (PID: 5456)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2025:04:15 23:54:26+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, Large address aware, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 524800 |
| InitializedDataSize: | 126976 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x16310 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3.1.1.0 |
| ProductVersionNumber: | 3.1.1.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Unknown |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| Comments: | www.opautoclicker.com |
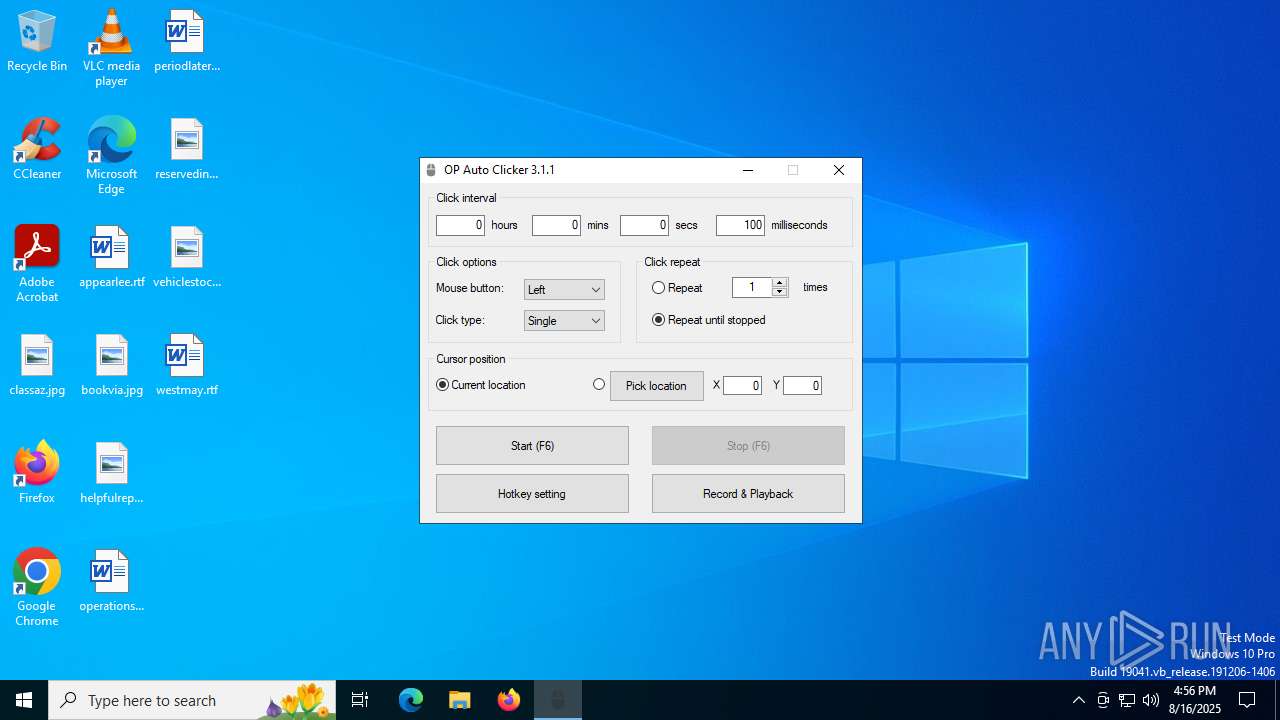
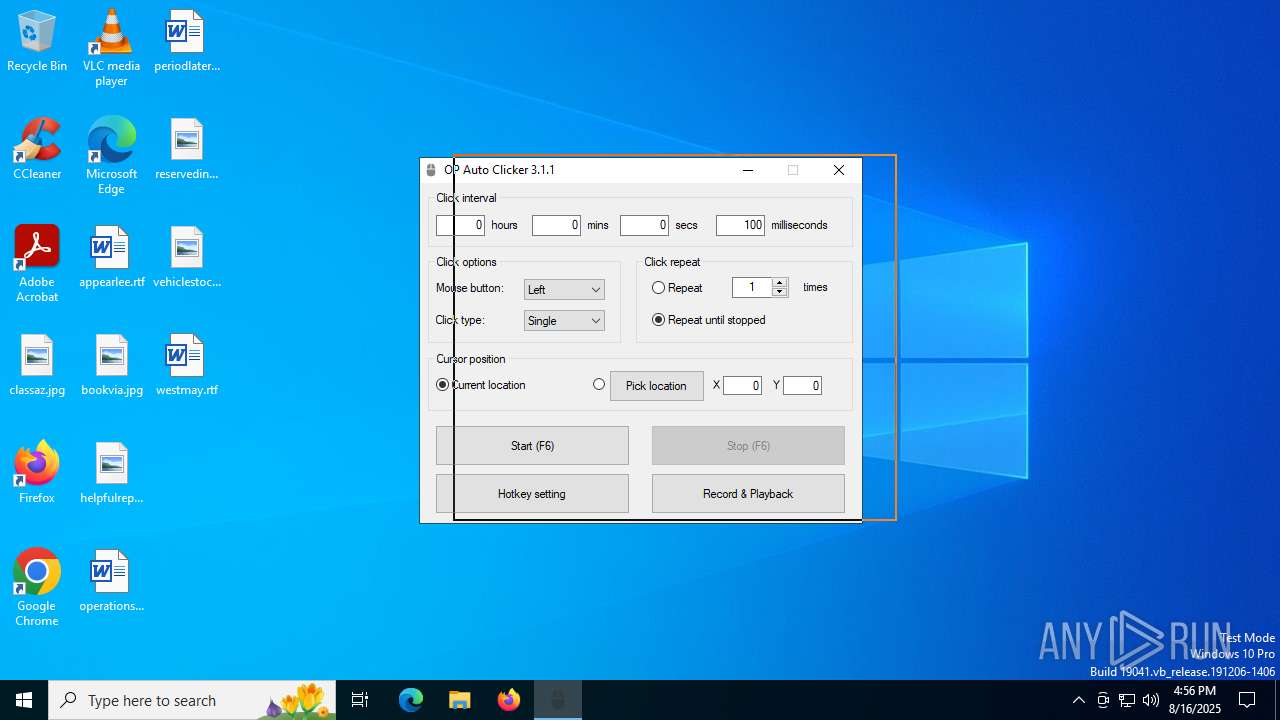
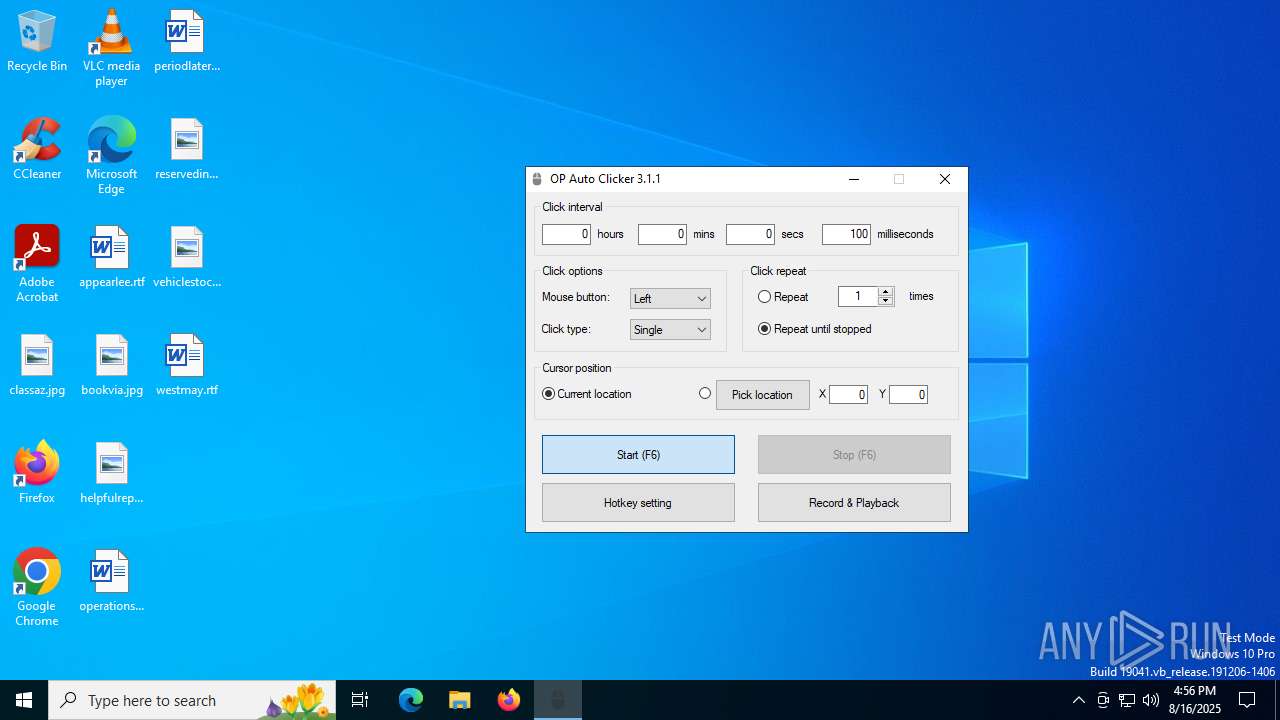
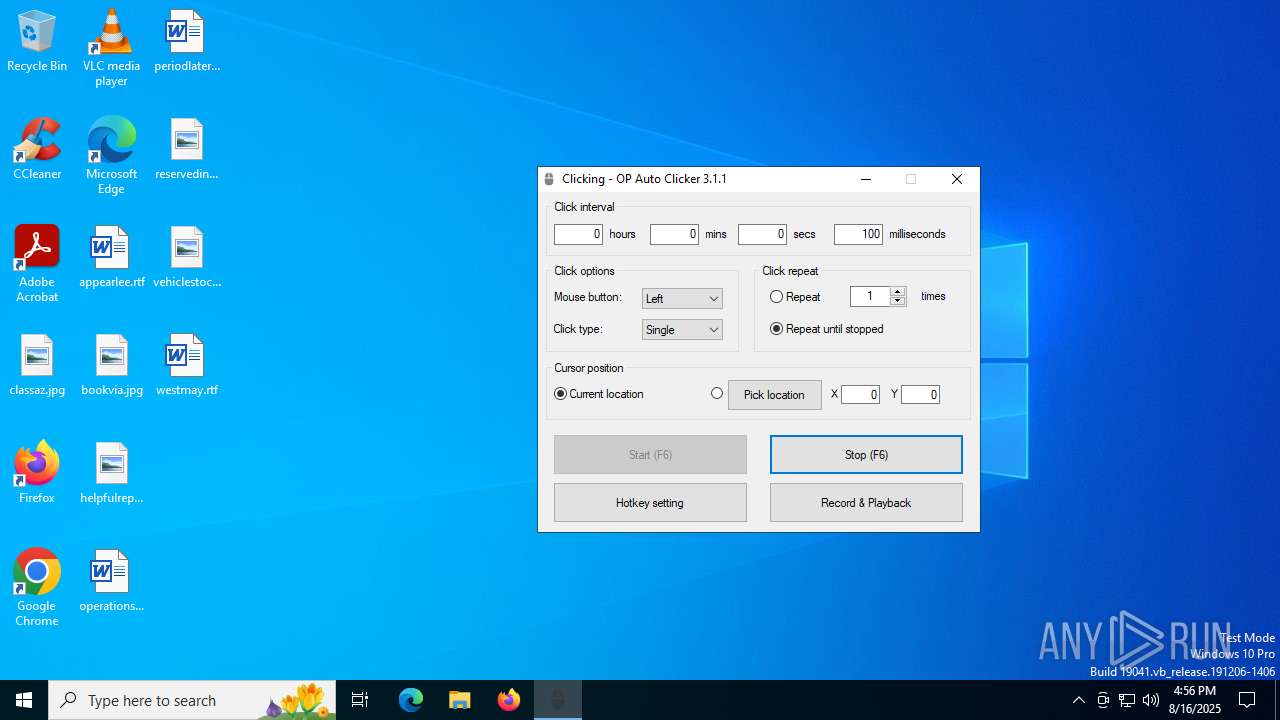
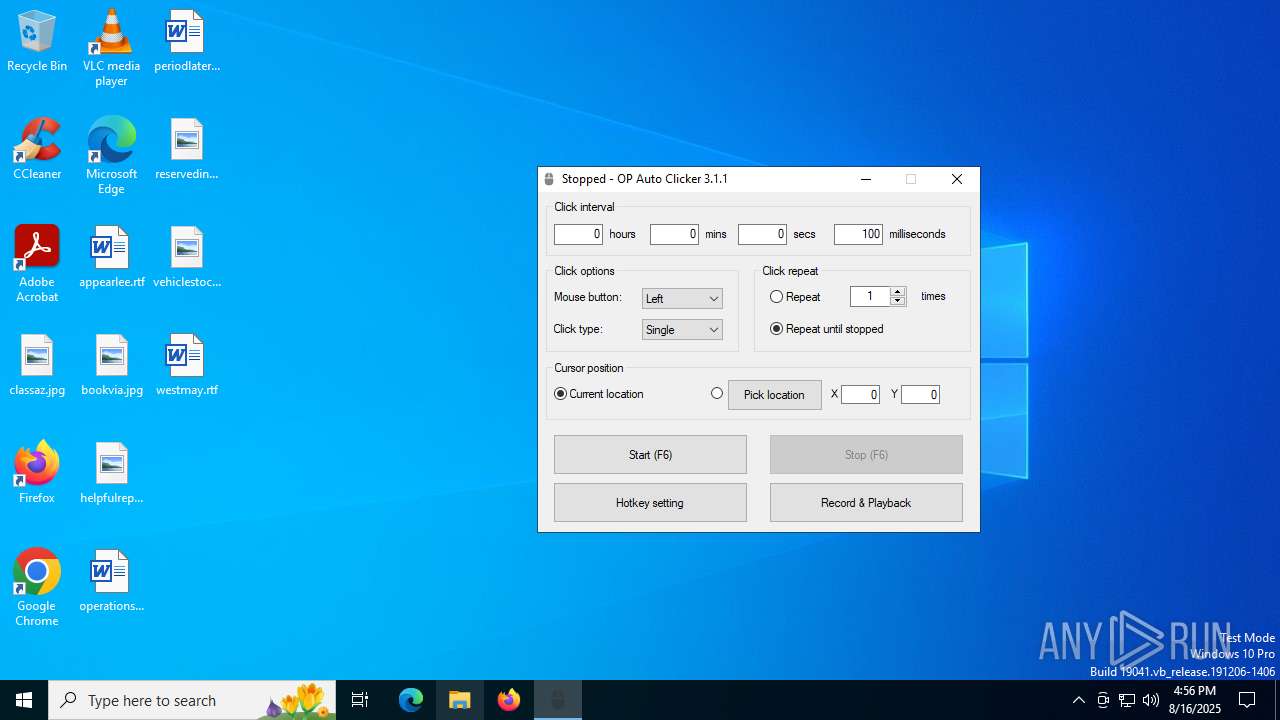
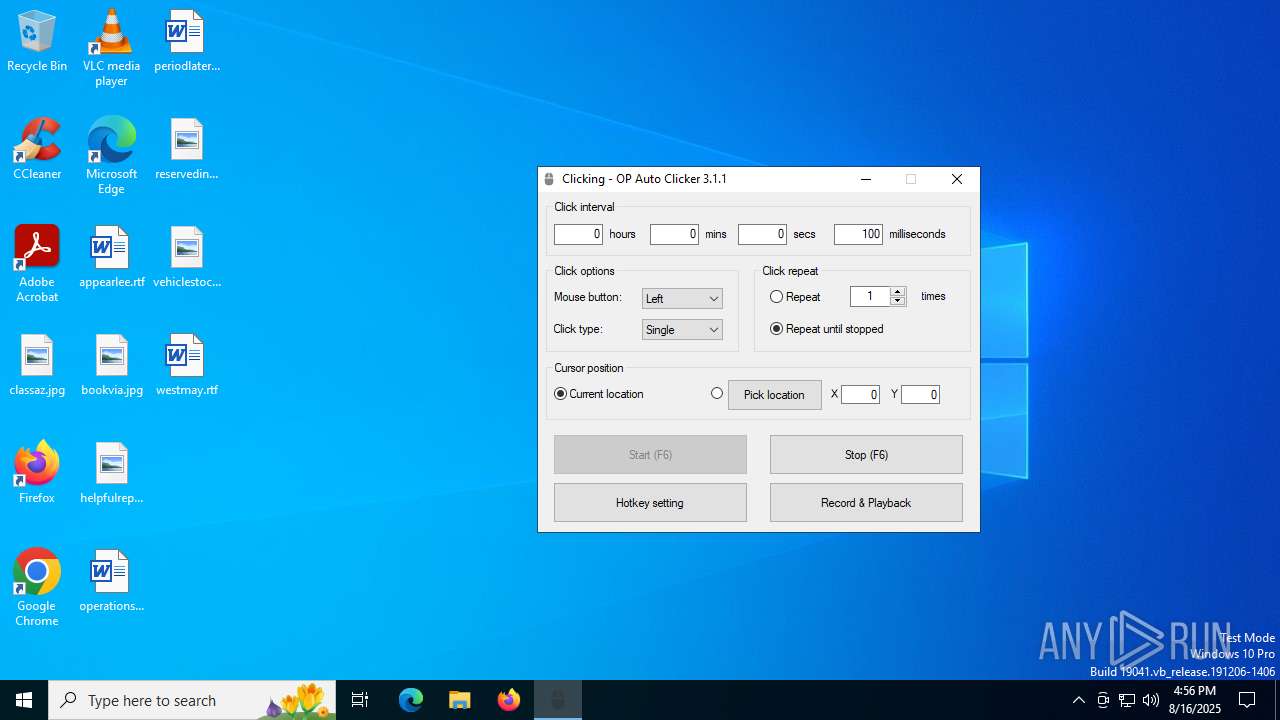
| FileDescription: | OP Auto Clicker |
| FileVersion: | 3.1.1 |
| LegalCopyright: | www.opautoclicker.com |
| ProductName: | OP Auto Clicker |
| ProductVersion: | 3.1.1 |
Total processes
133
Monitored processes
1
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 5456 | "C:\Users\admin\AppData\Local\Temp\AutoClicker-3.1.1.exe" | C:\Users\admin\AppData\Local\Temp\AutoClicker-3.1.1.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: OP Auto Clicker Version: 3.1.1 Modules
| |||||||||||||||
Total events
179
Read events
179
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
0
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5456 | AutoClicker-3.1.1.exe | C:\Users\admin\AppData\Local\Temp\ACLib\record.ico | image | |
MD5:1111E06679F96FF28C1E229B06CE7B41 | SHA256:59D5E9106E907FA61A560294A51C14ABCDE024FDD690E41A7F4D6C88DB7287A6 | |||
| 5456 | AutoClicker-3.1.1.exe | C:\Users\admin\AppData\Local\Temp\ACLib\playback.ico | image | |
MD5:A20254EA7F9EF810C1681FA314EDAA28 | SHA256:5375290E66A20BFF81FB4D80346756F2D442184789681297CD1B84446A3FE80D | |||
| 5456 | AutoClicker-3.1.1.exe | C:\Users\admin\AppData\Local\Temp\zxjjtwt | text | |
MD5:A85463F373A5F684958FBBBA9F1EC4D8 | SHA256:3DF534D4D1AD20A6176846F0C36DC0D4C09E102D56A9691A1E06B2106354FD28 | |||
| 5456 | AutoClicker-3.1.1.exe | C:\Users\admin\AppData\Local\Temp\ACLib\stop.ico | image | |
MD5:7824CEFAD2522BE614AE5B7BDBF88339 | SHA256:9E869F60EA0A0DE06C7D562FF56D1AC53C534849C919E4B12344E73513649483 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
12
DNS requests
8
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1268 | svchost.exe | GET | 200 | 23.32.238.107:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
3092 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5476 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1268 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 23.32.238.107:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1268 | svchost.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
3092 | svchost.exe | 20.190.159.71:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3092 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |