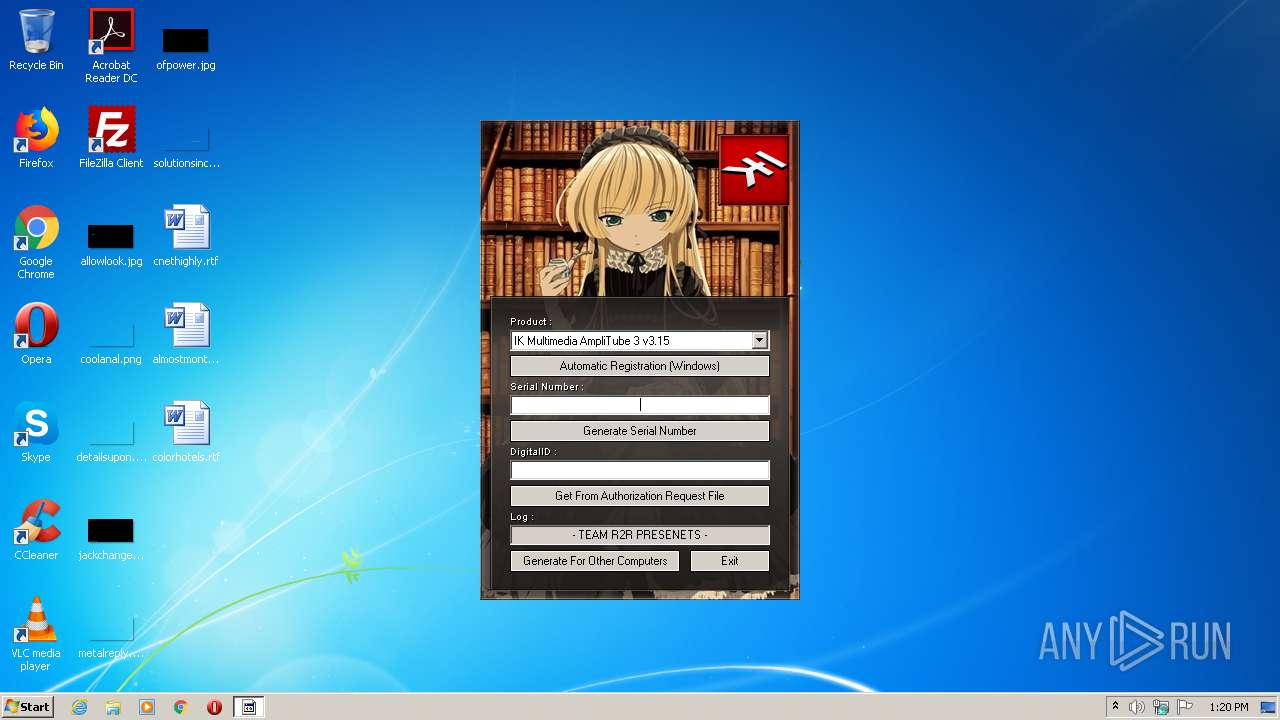
| File name: | IK_Multimedia_Keygen.exe |
| Full analysis: | https://app.any.run/tasks/c71cef29-a0cf-4f7f-9d3c-37c9559ce303 |
| Verdict: | No threats detected |
| Analysis date: | August 16, 2020, 12:20:10 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 5FD9156319FD088947431C680EEEE6BF |
| SHA1: | 0ADFB458B8B639C77770DA146CA2740E0CC153B2 |
| SHA256: | CD657F2DEA1CA9E13C815A8CFAF872C170BBA58E9C2A2BB5776175DA4BCA5B2B |
| SSDEEP: | 6144:iay2nA8P9tlASRzKW3kOG9gSfoQ3FH0YwQHSotzZ7A5olzKbvUjB7Y9ZIY6eKM7a:sc9t2SllU7qSf7h4EzLjSgiOX |
MALICIOUS
Loads dropped or rewritten executable
- keygen.exe (PID: 1296)
Application was dropped or rewritten from another process
- keygen.exe (PID: 1296)
SUSPICIOUS
Executable content was dropped or overwritten
- IK_Multimedia_Keygen.exe (PID: 3748)
INFO
Dropped object may contain Bitcoin addresses
- IK_Multimedia_Keygen.exe (PID: 3748)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:01:30 04:57:38+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 25088 |
| InitializedDataSize: | 118784 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x3328 |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 30-Jan-2018 03:57:38 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 30-Jan-2018 03:57:38 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00006077 | 0x00006200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.40397 |
.rdata | 0x00008000 | 0x00001248 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.04426 |
.data | 0x0000A000 | 0x0001A838 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.22445 |
.ndata | 0x00025000 | 0x00008000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x0002D000 | 0x00022910 | 0x00022A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.06462 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.28733 | 841 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 7.92764 | 54264 | UNKNOWN | English - United States | RT_ICON |
3 | 4.51849 | 9640 | UNKNOWN | English - United States | RT_ICON |
4 | 4.75617 | 4264 | UNKNOWN | English - United States | RT_ICON |
5 | 4.93004 | 2440 | UNKNOWN | English - United States | RT_ICON |
6 | 5.08765 | 1128 | UNKNOWN | English - United States | RT_ICON |
103 | 2.8213 | 90 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.66174 | 256 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.88094 | 284 | UNKNOWN | English - United States | RT_DIALOG |
111 | 2.48825 | 96 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
43
Monitored processes
3
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1296 | C:\Users\admin\AppData\Local\Temp\keygen.exe | C:\Users\admin\AppData\Local\Temp\keygen.exe | — | IK_Multimedia_Keygen.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2280 | "C:\Users\admin\AppData\Local\Temp\IK_Multimedia_Keygen.exe" | C:\Users\admin\AppData\Local\Temp\IK_Multimedia_Keygen.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 3748 | "C:\Users\admin\AppData\Local\Temp\IK_Multimedia_Keygen.exe" | C:\Users\admin\AppData\Local\Temp\IK_Multimedia_Keygen.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
623
Read events
351
Write events
272
Delete events
0
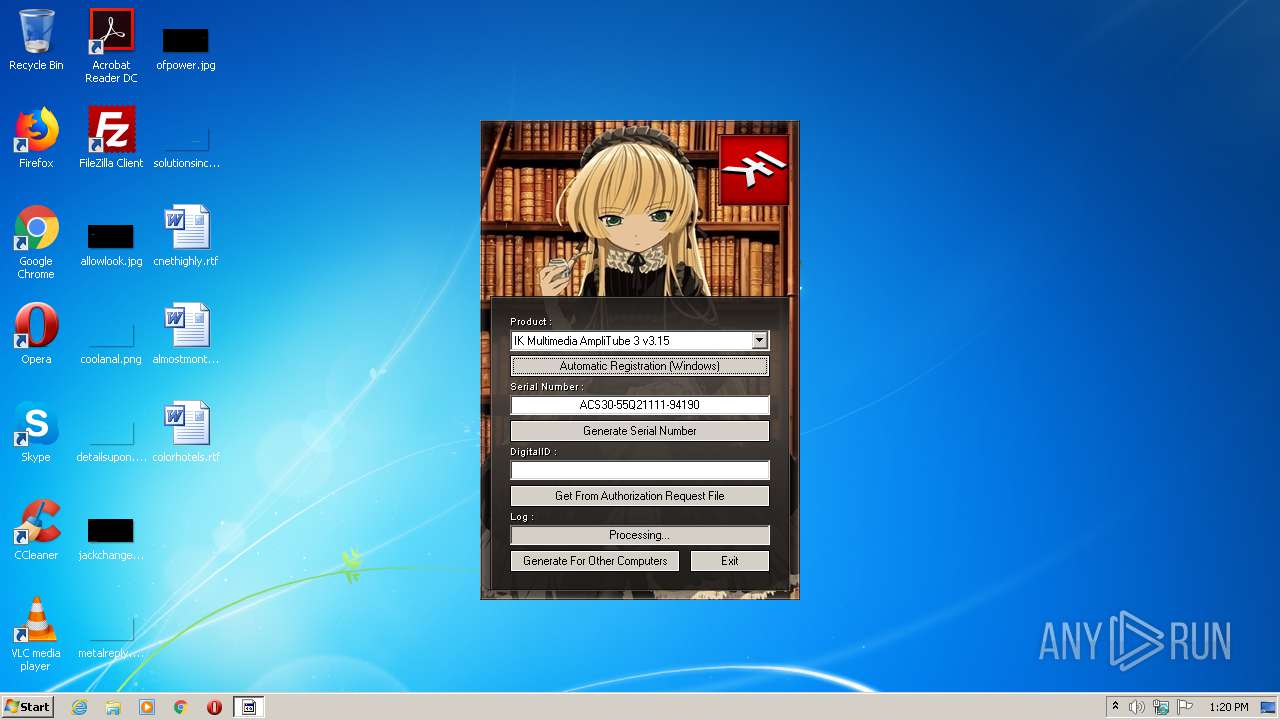
Modification events
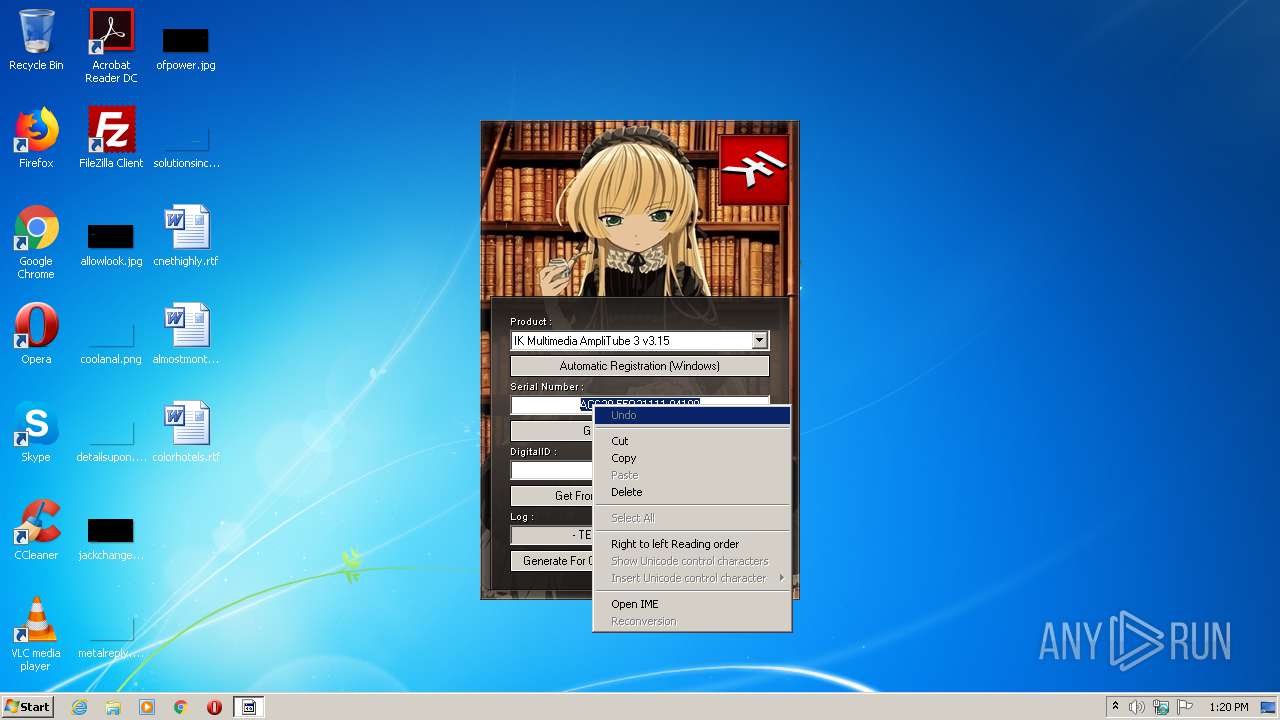
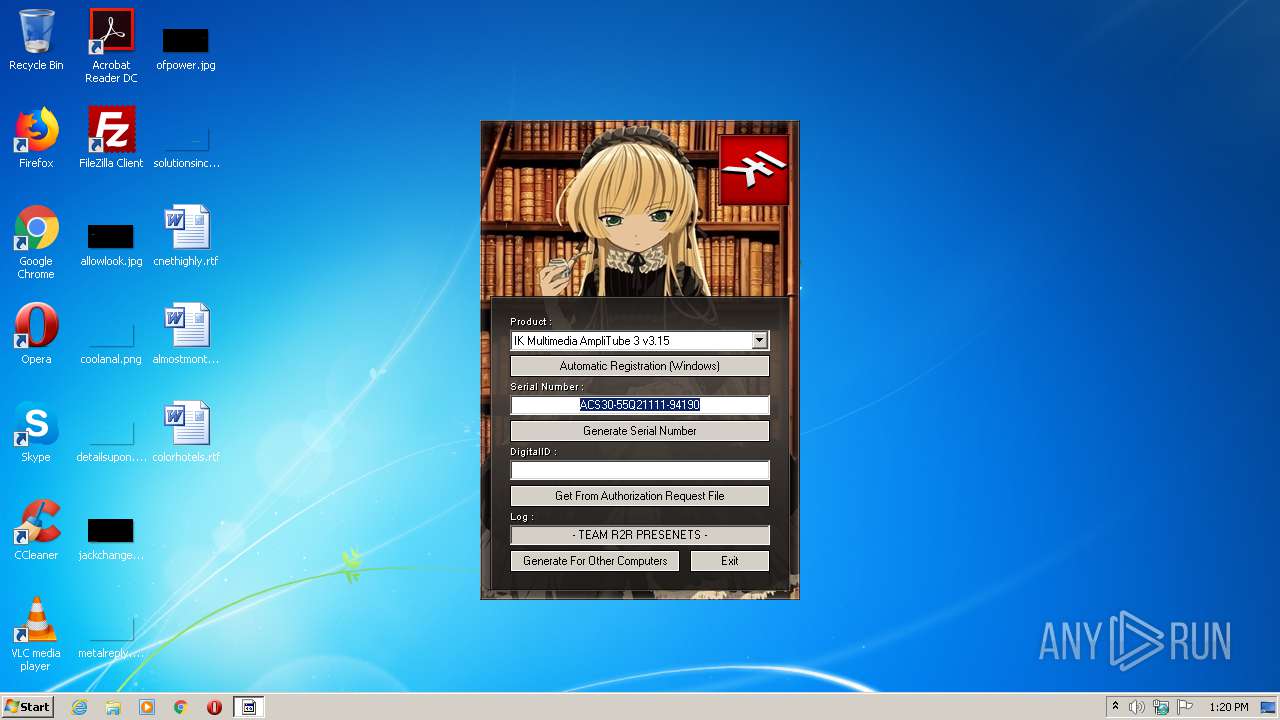
| (PID) Process: | (1296) keygen.exe | Key: | HKEY_CURRENT_USER\Software\IK Multimedia\AmpliTube 3 |
| Operation: | write | Name: | SerialNumber |
Value: ACS30-59A23013-87373 | |||
| (PID) Process: | (1296) keygen.exe | Key: | HKEY_CURRENT_USER\Software\IK Multimedia\AmpliTube 3 |
| Operation: | write | Name: | AuthCode |
Value: 84A7KTP5-XMSJ-CUW8-DHFF-FMXSMCME | |||
| (PID) Process: | (1296) keygen.exe | Key: | HKEY_CURRENT_USER\Software\IK Multimedia\AmpliTube 3 |
| Operation: | write | Name: | UserSerial |
Value: CLA10-53H23101-93757 | |||
| (PID) Process: | (1296) keygen.exe | Key: | HKEY_CURRENT_USER\Software\IK Multimedia\AmpliTube 3 |
| Operation: | write | Name: | 48e7b721-d57a-4c34-813b-95d8091d5eda |
Value: 2F85F344F1886152C38EA2E8B3AD4DF1 | |||
| (PID) Process: | (1296) keygen.exe | Key: | HKEY_CURRENT_USER\Software\IK Multimedia\AmpliTube 3 |
| Operation: | write | Name: | 907ecdf1-15be-4f41-b56d-2705e7bb89ae |
Value: E1E899AD600289B9B054B07B28C3854D | |||
| (PID) Process: | (1296) keygen.exe | Key: | HKEY_CURRENT_USER\Software\IK Multimedia\AmpliTube 3 |
| Operation: | write | Name: | 96b57f95-4380-444a-8c0a-fbcc9bef1dd9 |
Value: 73AAA863788C7A4B320C949C1B04DF7C | |||
| (PID) Process: | (1296) keygen.exe | Key: | HKEY_CURRENT_USER\Software\IK Multimedia\AmpliTube 3 |
| Operation: | write | Name: | 58dbec22-58e0-464c-8c04-91fb9d9973e2 |
Value: F285FA37EEECA0129392C1DBBD2BC413 | |||
| (PID) Process: | (1296) keygen.exe | Key: | HKEY_CURRENT_USER\Software\IK Multimedia\AmpliTube 3 |
| Operation: | write | Name: | 305c9b6b-04cf-4673-b58a-e62afb4fefcb |
Value: E32167B63C96C347C1AA9FA4CDE1732C | |||
| (PID) Process: | (1296) keygen.exe | Key: | HKEY_CURRENT_USER\Software\IK Multimedia\AmpliTube 3 |
| Operation: | write | Name: | 510f6d25-6ec4-417b-bf58-0f8028209cce |
Value: A4C247EA0346F06DAE08B9E34F6D9AA5 | |||
| (PID) Process: | (1296) keygen.exe | Key: | HKEY_CURRENT_USER\Software\IK Multimedia\AmpliTube 3 |
| Operation: | write | Name: | 395ed825-f3e8-40c1-8d69-34d8b23c9100 |
Value: AEA7E27D087700E05B69A00A228663F0 | |||
Executable files
3
Suspicious files
0
Text files
0
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3748 | IK_Multimedia_Keygen.exe | C:\Users\admin\AppData\Local\Temp\keygen.exe | executable | |
MD5:— | SHA256:— | |||
| 3748 | IK_Multimedia_Keygen.exe | C:\Users\admin\AppData\Local\Temp\R2RIKM2.dll | executable | |
MD5:511E942E713956682C1EA73F33A63542 | SHA256:7F8124C4B402BCDB0A0628447079CAFDA7755EC17397616B5CE510A98A4F3F07 | |||
| 3748 | IK_Multimedia_Keygen.exe | C:\Users\admin\AppData\Local\Temp\BASSMOD.dll | executable | |
MD5:E4EC57E8508C5C4040383EBE6D367928 | SHA256:8AD9E47693E292F381DA42DDC13724A3063040E51C26F4CA8E1F8E2F1DDD547F | |||
| 3748 | IK_Multimedia_Keygen.exe | C:\Users\admin\AppData\Local\Temp\bgm.xm | xm | |
MD5:A30878984AF33EE69ACE5CF8E330B974 | SHA256:498EADC5B3D65AAF34B8496954C3362F033297C489D7EF4559CBA8890C530171 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report