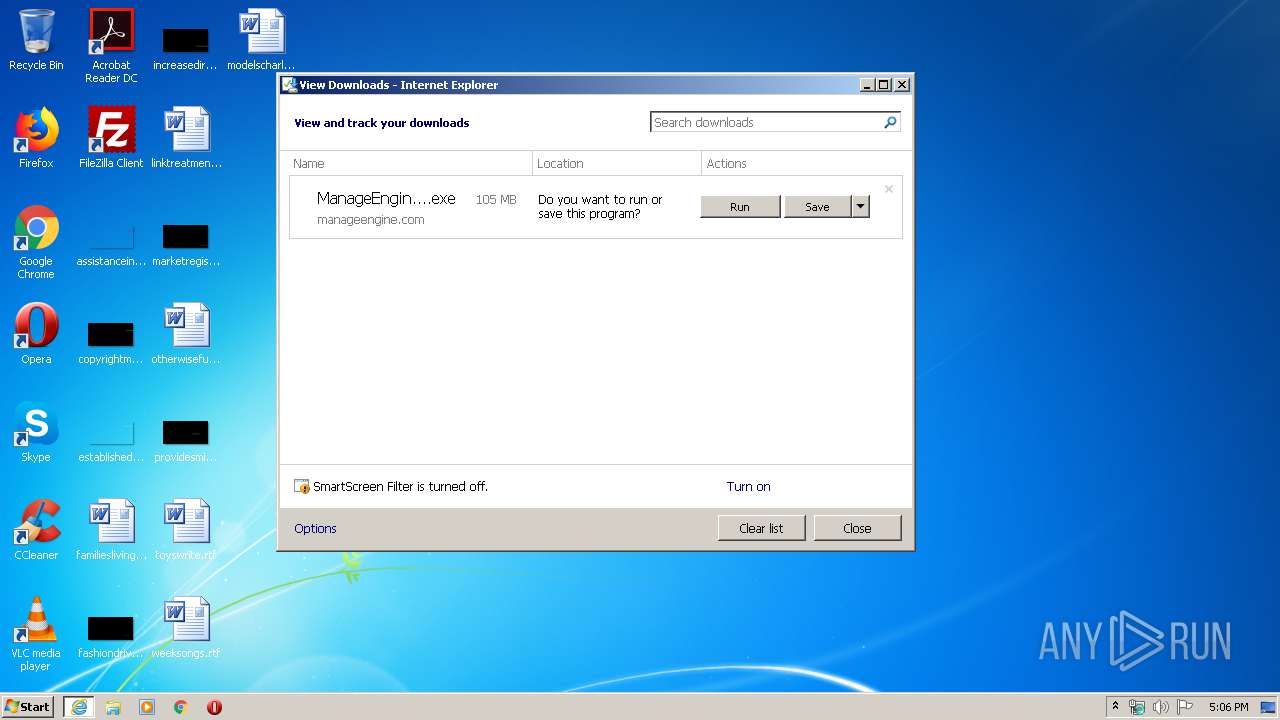
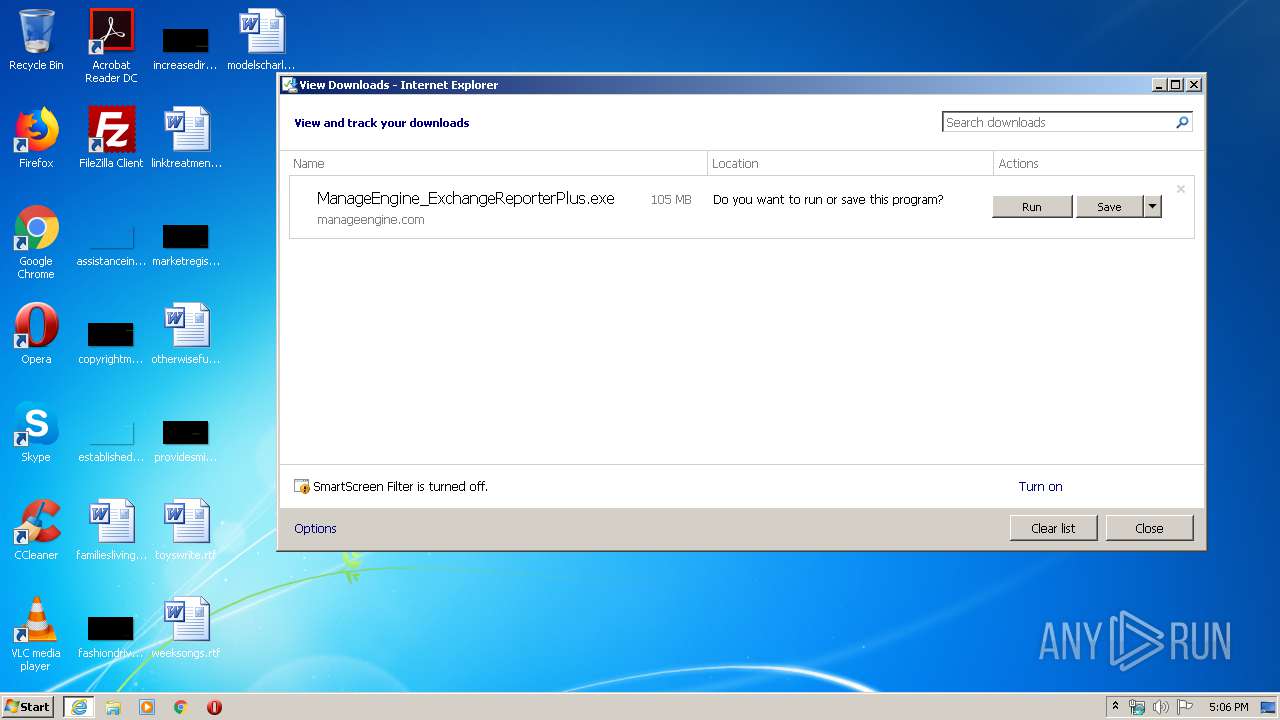
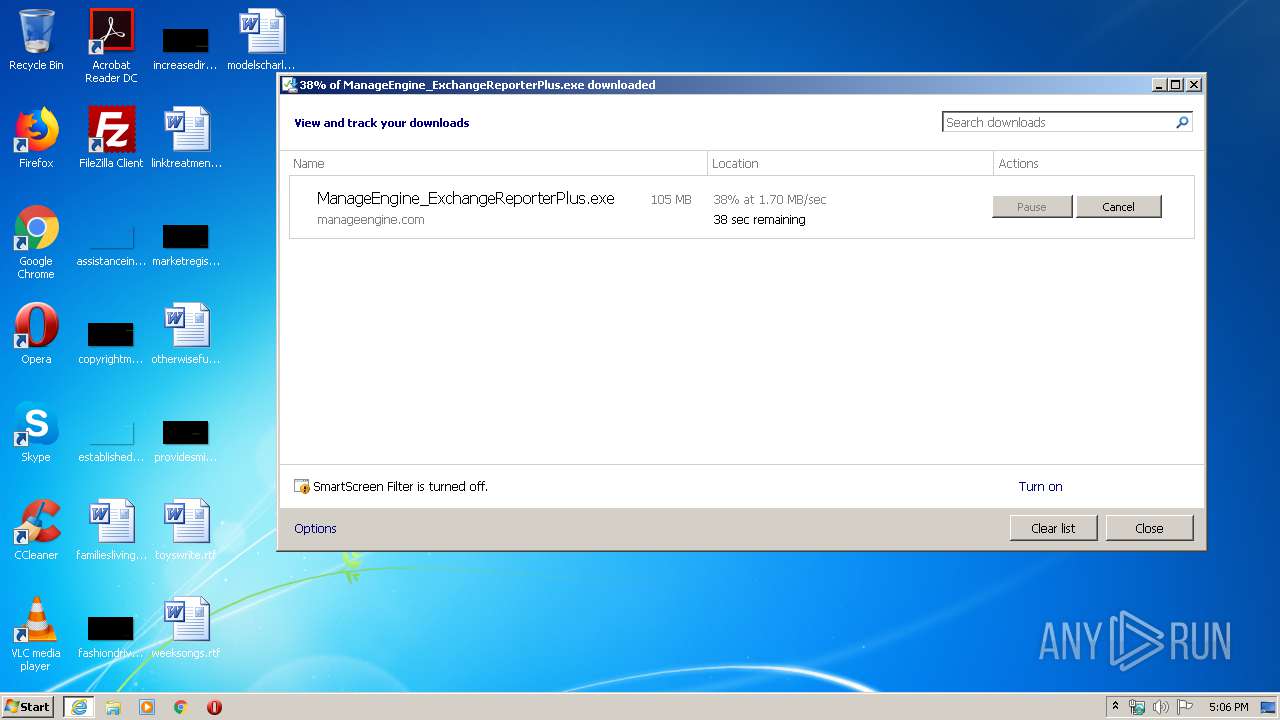
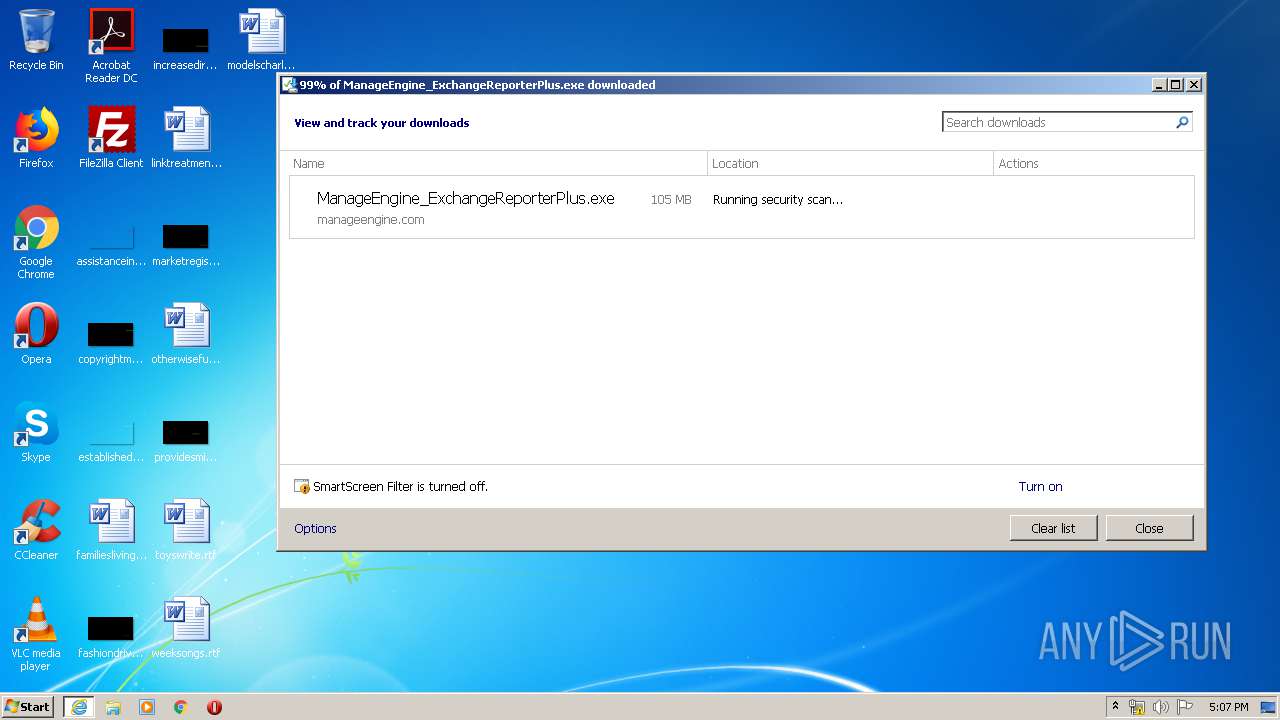
| URL: | http://www.manageengine.com/cgi-bin/download_exe?id=79-831-2020-02-06-15-29-04-57346 |
| Full analysis: | https://app.any.run/tasks/5d655302-a28c-4aba-90af-48e7d446f5c1 |
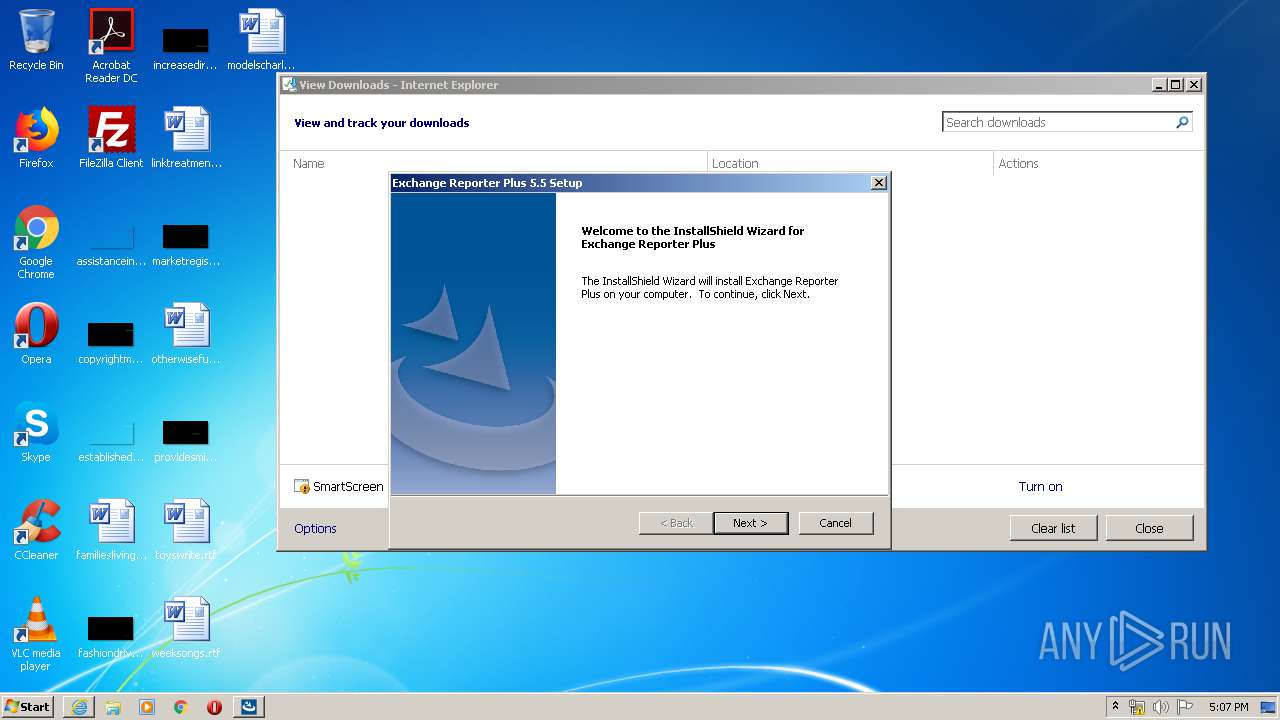
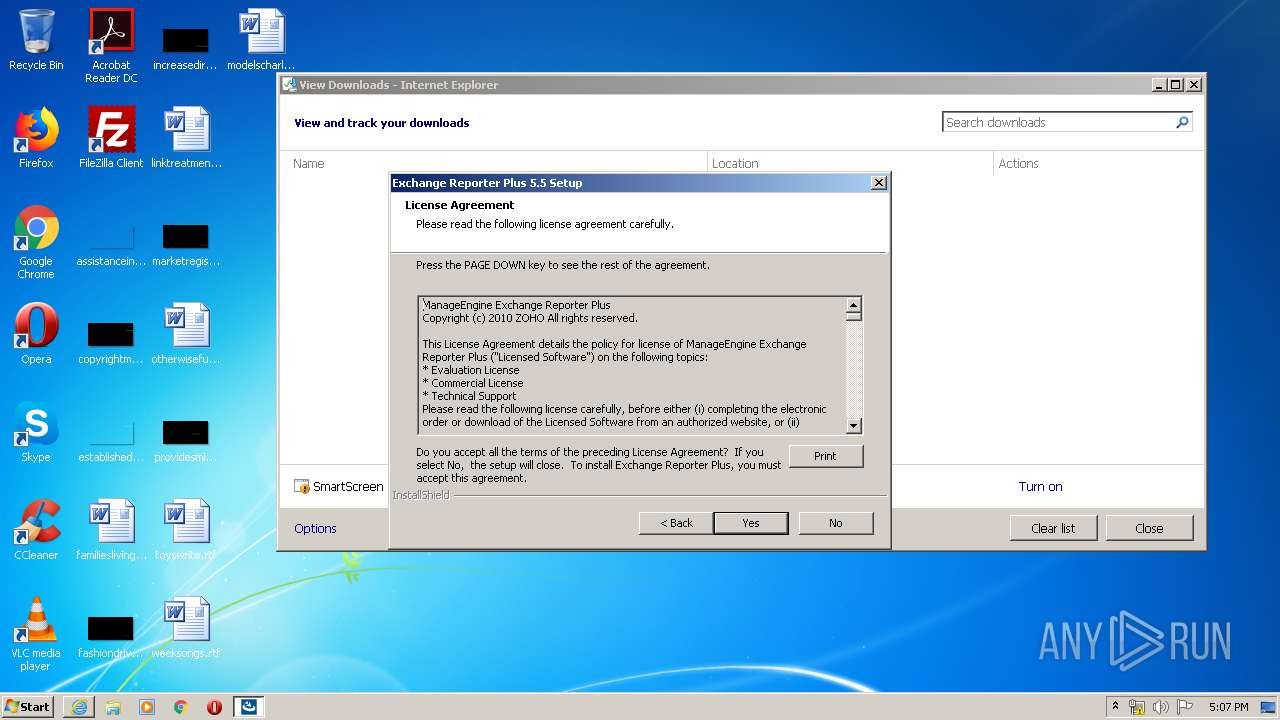
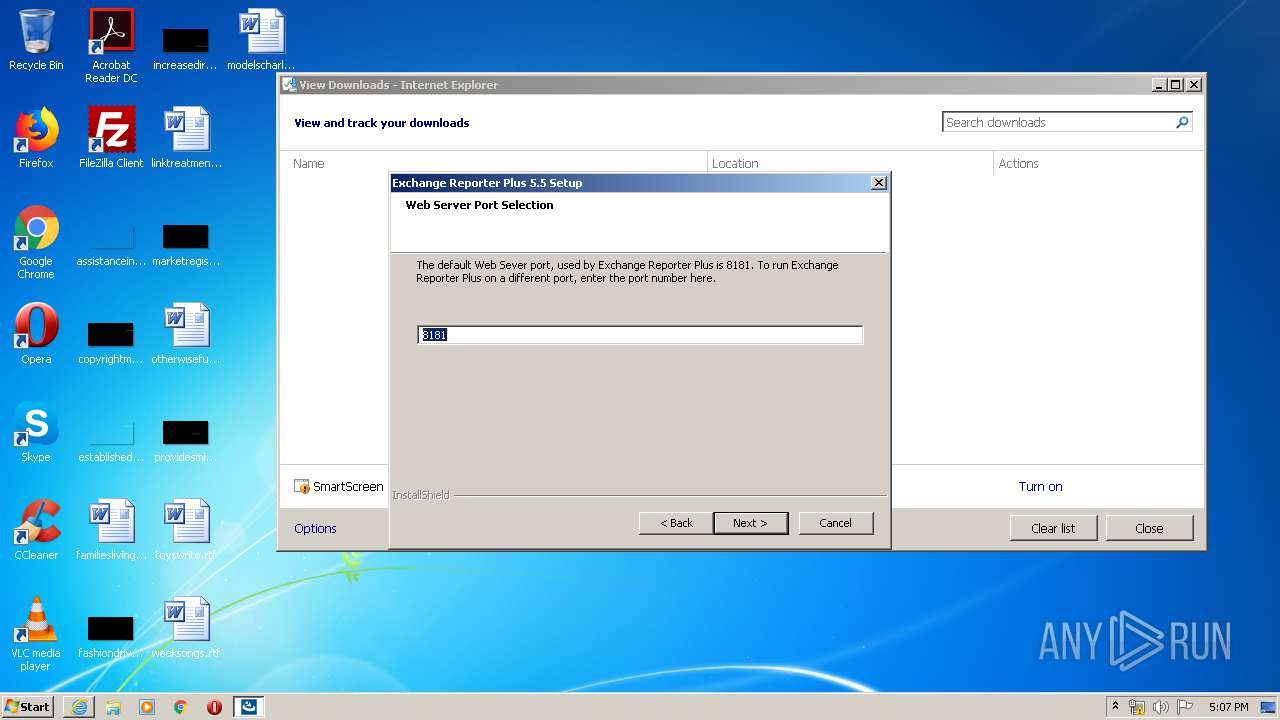
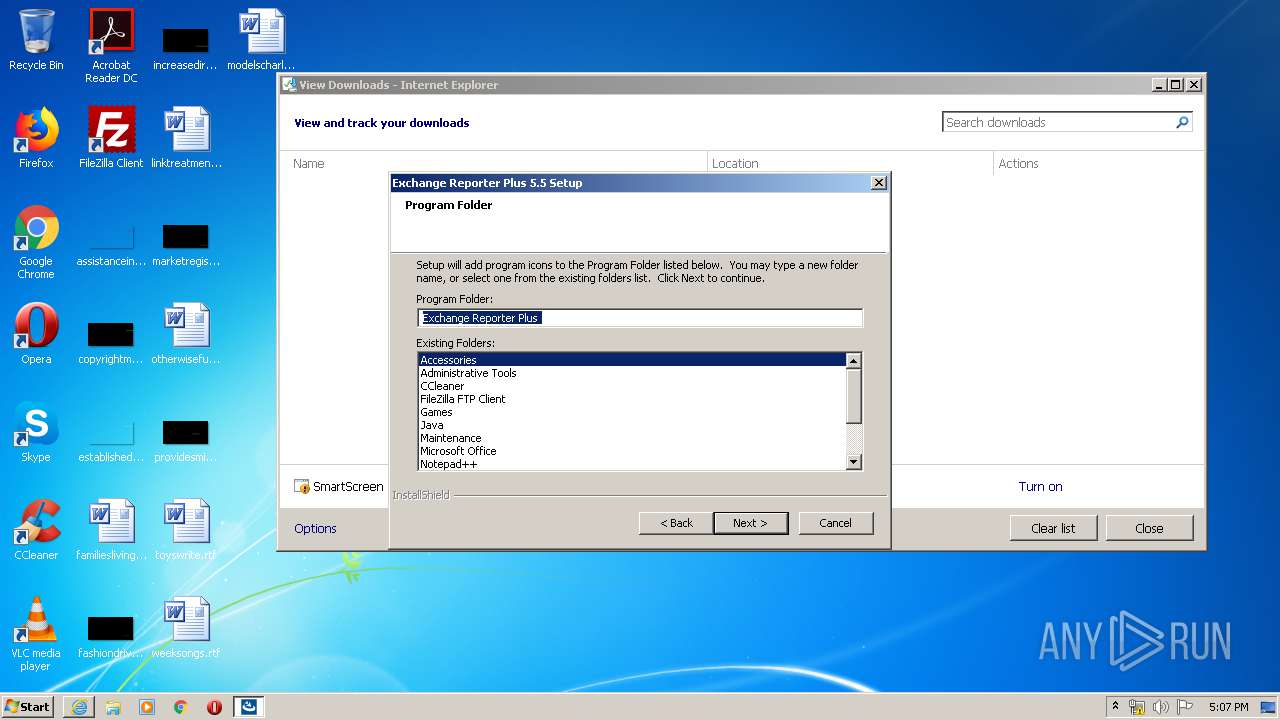
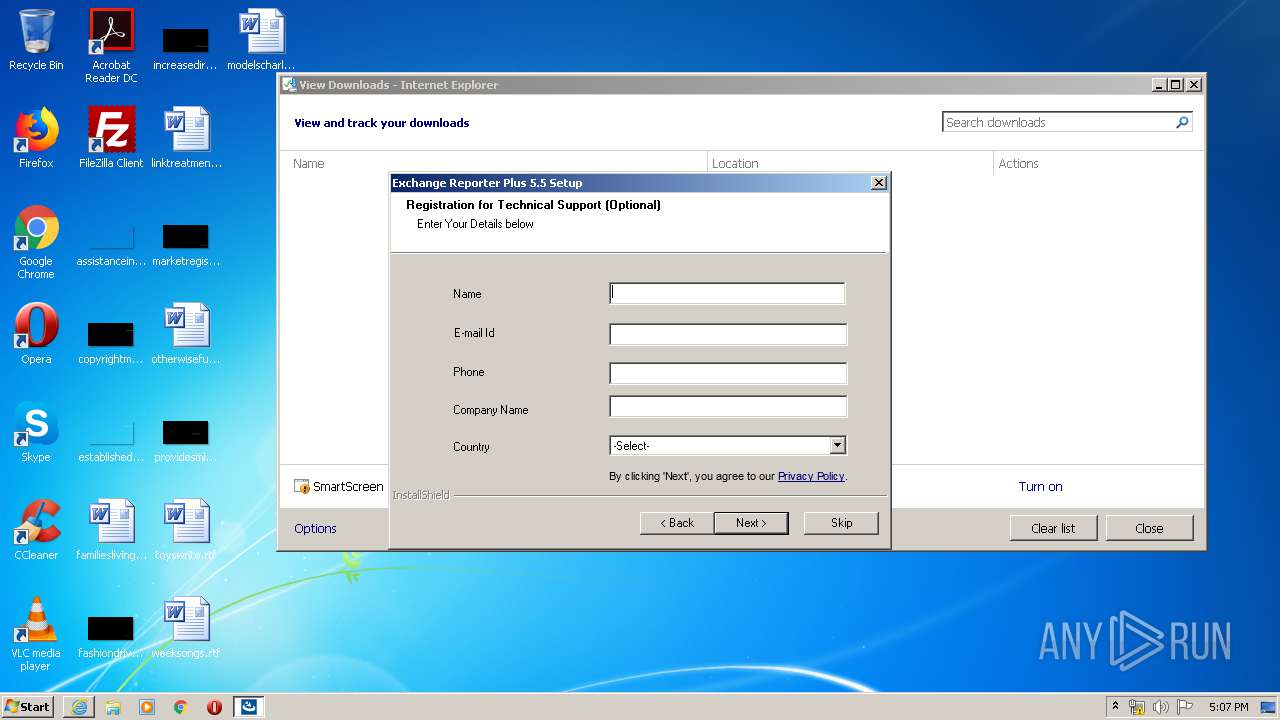
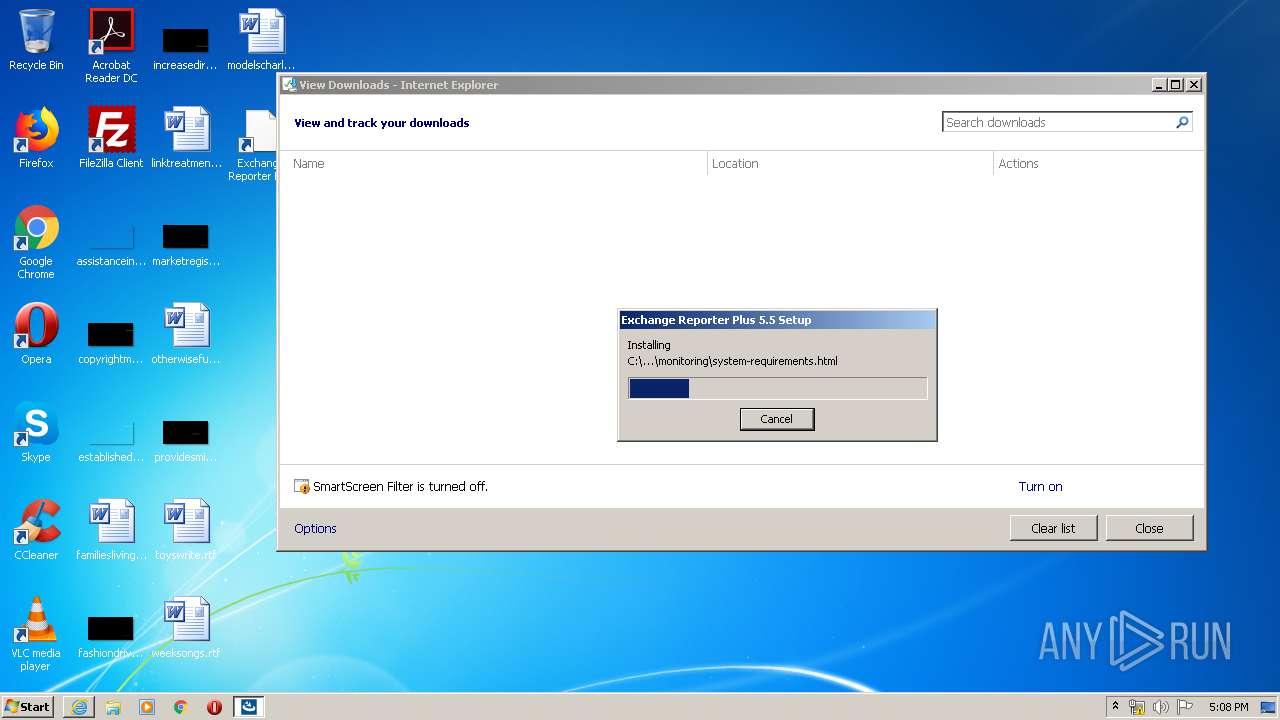
| Verdict: | Malicious activity |
| Analysis date: | February 06, 2020, 17:06:10 |
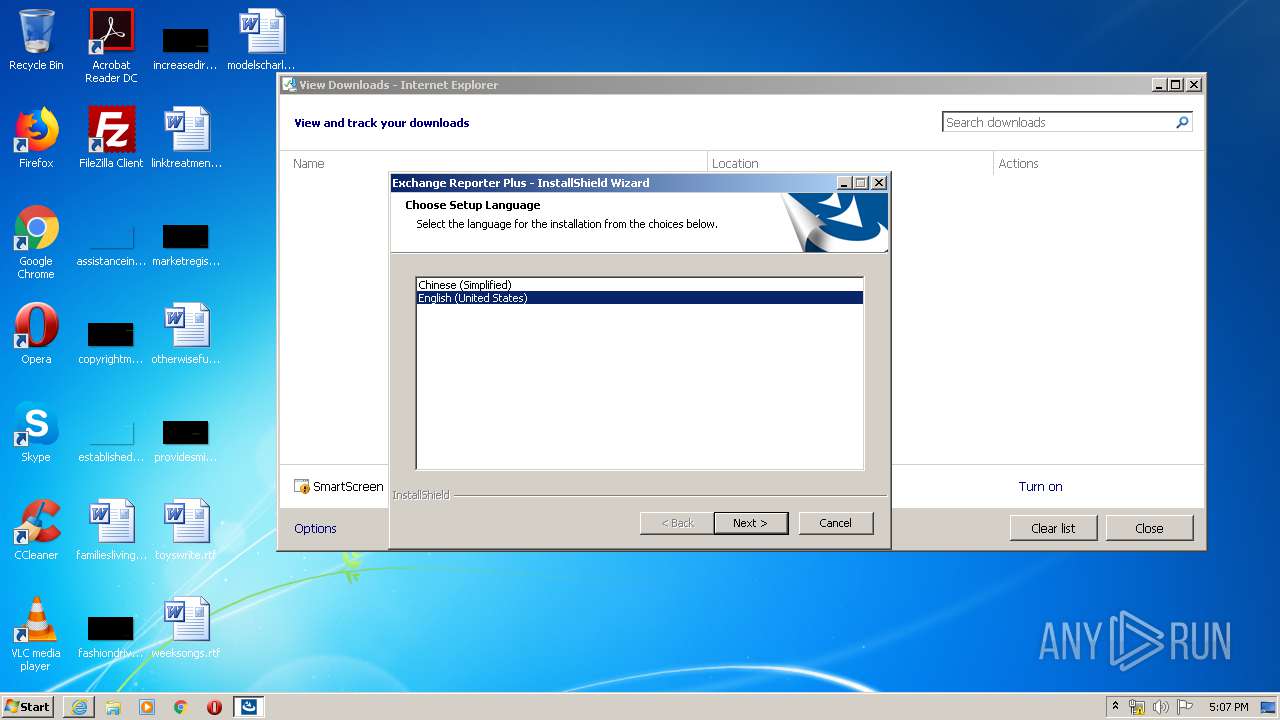
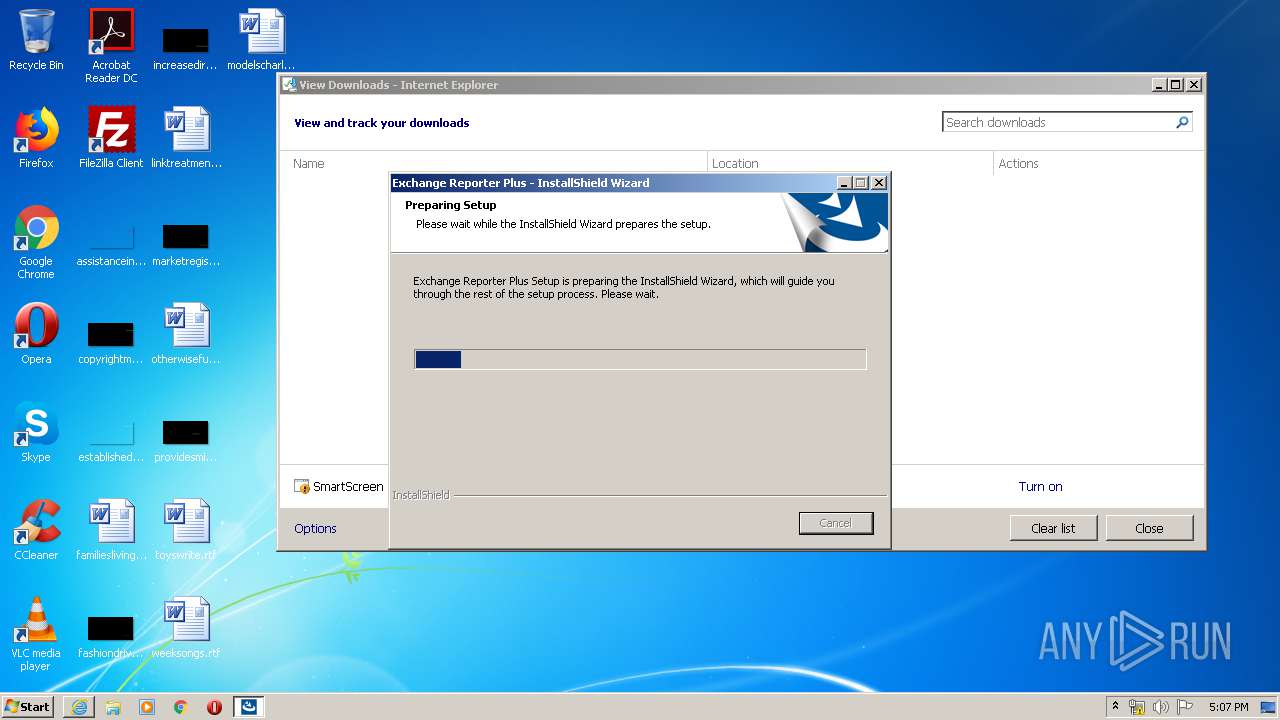
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 9D00FE86632F4825FD50128A023AEA11 |
| SHA1: | 1F4ED2F151ED94425E1FCBA2ECB1CD090499C327 |
| SHA256: | CD558838FC106C99FDAEAF19A97DA27B3115889D0082887E2CF398BCB8C5D001 |
| SSDEEP: | 3:N1KJS4uCl8IKGCMIqaJLW4AHd5aXVFKoTIJIJ0WRT:Cc4uChjaFiHqXVFZT+IeW1 |
MALICIOUS
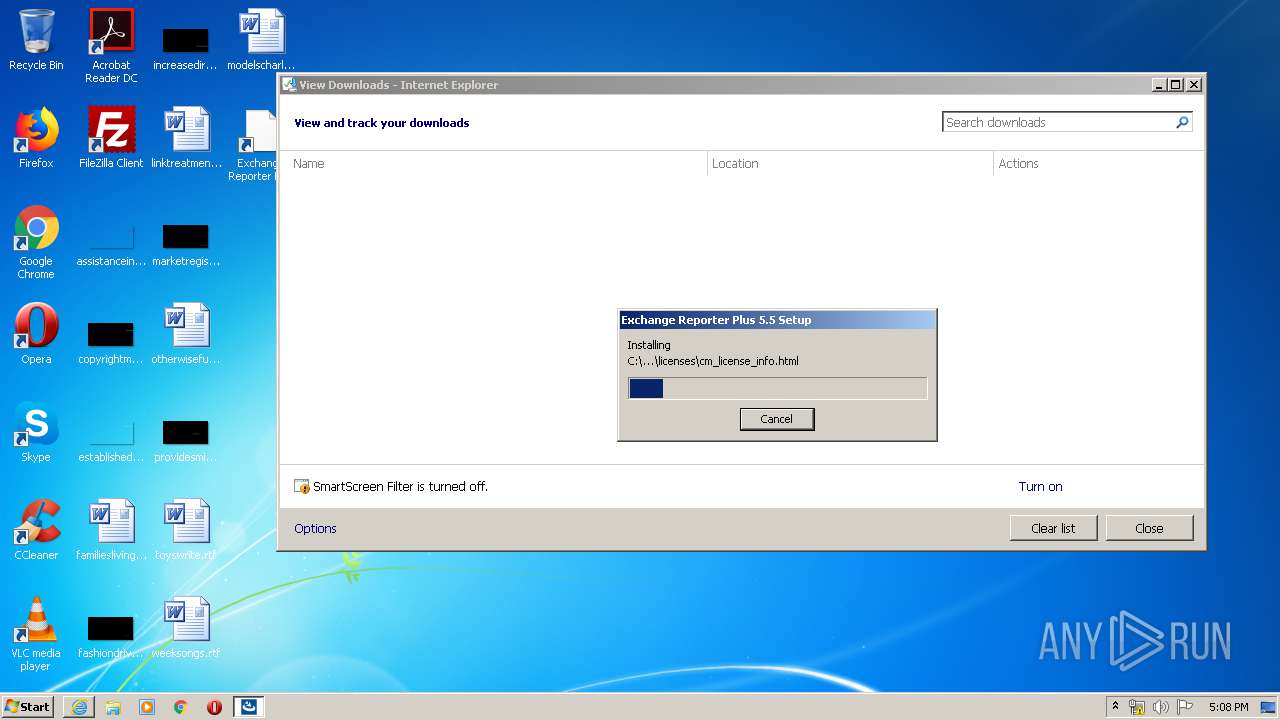
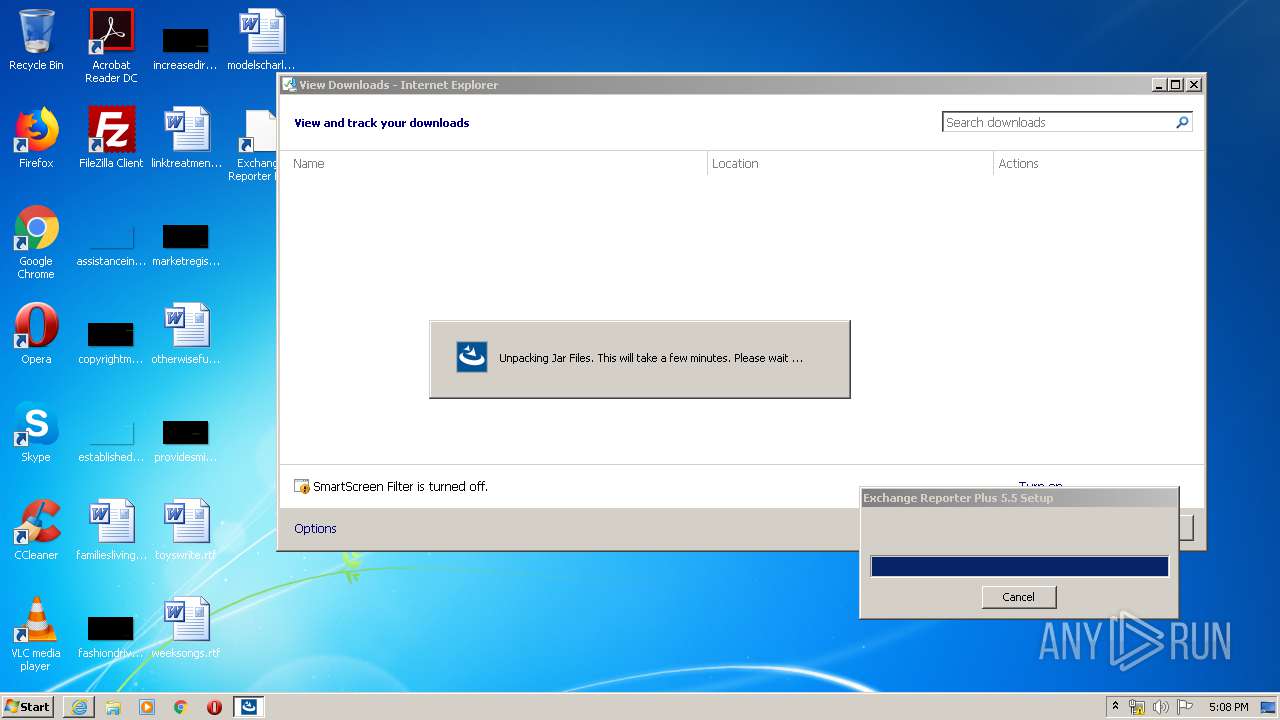
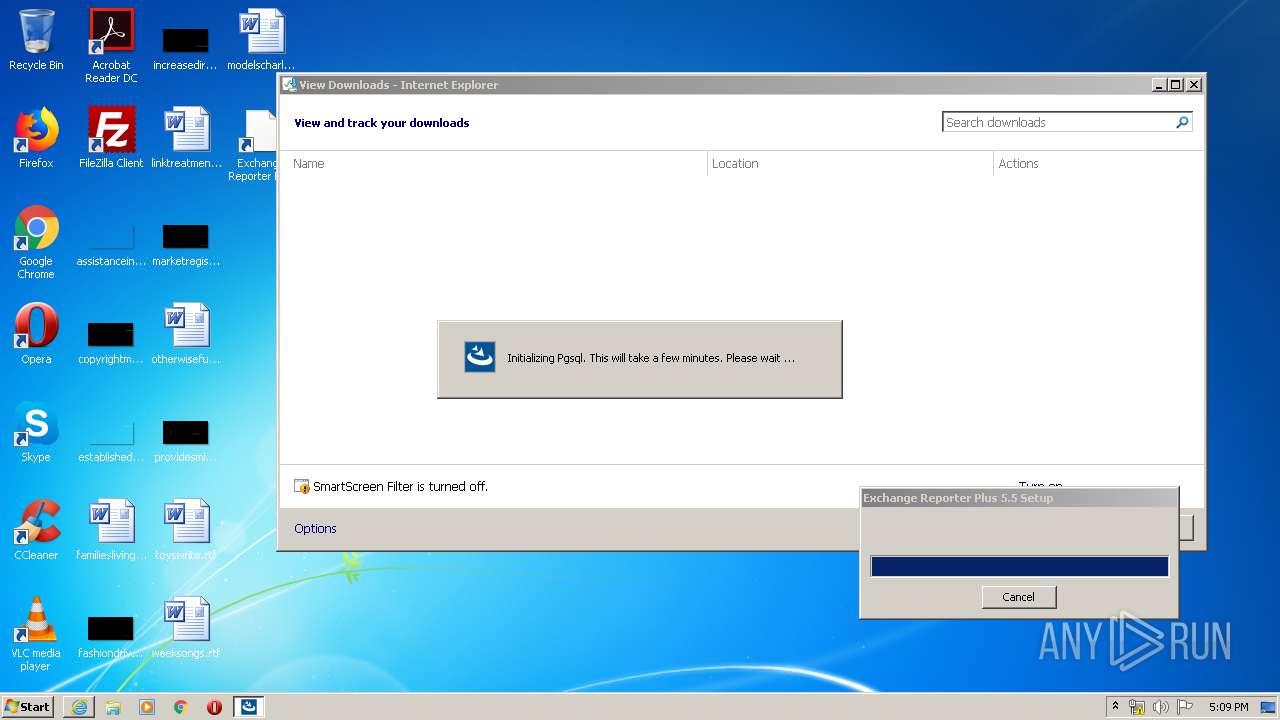
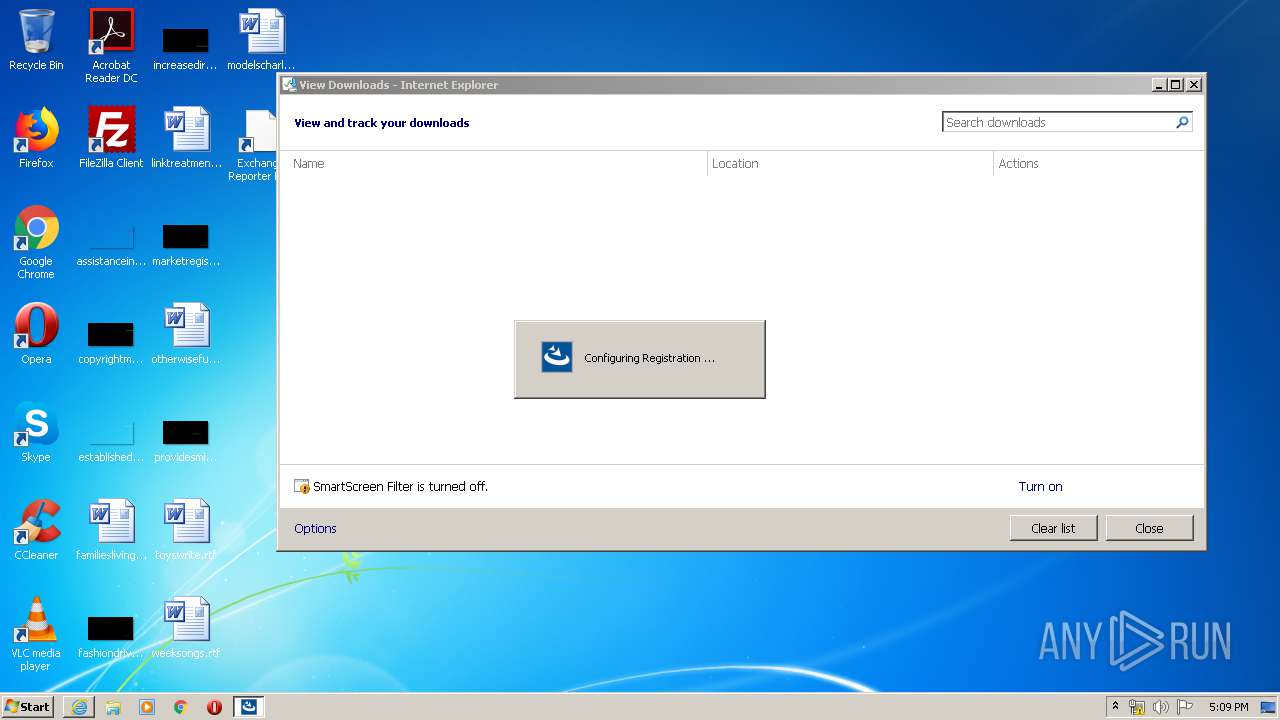
Loads dropped or rewritten executable
- ManageEngine_ExchangeReporterPlus.exe (PID: 1332)
- unpack200.exe (PID: 312)
- unpack200.exe (PID: 3536)
- unpack200.exe (PID: 984)
- unpack200.exe (PID: 3960)
- unpack200.exe (PID: 3380)
- unpack200.exe (PID: 3444)
- unpack200.exe (PID: 2420)
- unpack200.exe (PID: 3768)
- unpack200.exe (PID: 3992)
- unpack200.exe (PID: 2012)
- unpack200.exe (PID: 2692)
- unpack200.exe (PID: 940)
- unpack200.exe (PID: 2532)
- unpack200.exe (PID: 3228)
- unpack200.exe (PID: 3652)
- unpack200.exe (PID: 3232)
- unpack200.exe (PID: 3324)
- unpack200.exe (PID: 3248)
- unpack200.exe (PID: 880)
- unpack200.exe (PID: 1524)
- unpack200.exe (PID: 3832)
- unpack200.exe (PID: 3588)
- unpack200.exe (PID: 1948)
- unpack200.exe (PID: 3576)
- unpack200.exe (PID: 3632)
- unpack200.exe (PID: 1724)
- unpack200.exe (PID: 2080)
- unpack200.exe (PID: 1380)
- unpack200.exe (PID: 3172)
- unpack200.exe (PID: 304)
- unpack200.exe (PID: 2588)
- unpack200.exe (PID: 748)
- unpack200.exe (PID: 576)
- unpack200.exe (PID: 3652)
- unpack200.exe (PID: 3596)
- unpack200.exe (PID: 2080)
- unpack200.exe (PID: 3272)
- unpack200.exe (PID: 3848)
- unpack200.exe (PID: 3800)
- unpack200.exe (PID: 3704)
- unpack200.exe (PID: 1604)
- unpack200.exe (PID: 3452)
- unpack200.exe (PID: 1468)
- unpack200.exe (PID: 2192)
- unpack200.exe (PID: 1916)
- unpack200.exe (PID: 3736)
- unpack200.exe (PID: 2244)
- unpack200.exe (PID: 1828)
- unpack200.exe (PID: 528)
- unpack200.exe (PID: 2816)
- unpack200.exe (PID: 3288)
- unpack200.exe (PID: 2948)
- unpack200.exe (PID: 1380)
- unpack200.exe (PID: 1720)
- unpack200.exe (PID: 3640)
- unpack200.exe (PID: 1092)
- unpack200.exe (PID: 3152)
- unpack200.exe (PID: 3528)
- unpack200.exe (PID: 1844)
- unpack200.exe (PID: 3820)
- unpack200.exe (PID: 3024)
- unpack200.exe (PID: 1064)
- unpack200.exe (PID: 3544)
- unpack200.exe (PID: 1388)
- unpack200.exe (PID: 1912)
- unpack200.exe (PID: 1784)
- unpack200.exe (PID: 2764)
- unpack200.exe (PID: 3376)
- unpack200.exe (PID: 3224)
- unpack200.exe (PID: 3896)
- unpack200.exe (PID: 3648)
- unpack200.exe (PID: 1944)
- unpack200.exe (PID: 3504)
- unpack200.exe (PID: 3992)
- unpack200.exe (PID: 2012)
- unpack200.exe (PID: 2716)
- unpack200.exe (PID: 2212)
- unpack200.exe (PID: 576)
- unpack200.exe (PID: 1724)
- unpack200.exe (PID: 3640)
- unpack200.exe (PID: 3952)
- unpack200.exe (PID: 3832)
- unpack200.exe (PID: 3068)
- unpack200.exe (PID: 1140)
- unpack200.exe (PID: 3156)
- unpack200.exe (PID: 3588)
- unpack200.exe (PID: 2732)
- unpack200.exe (PID: 3584)
- unpack200.exe (PID: 2692)
- unpack200.exe (PID: 3452)
- unpack200.exe (PID: 2672)
- unpack200.exe (PID: 3380)
- unpack200.exe (PID: 3340)
- unpack200.exe (PID: 3776)
- unpack200.exe (PID: 4040)
- unpack200.exe (PID: 3168)
- unpack200.exe (PID: 1876)
- unpack200.exe (PID: 2500)
- unpack200.exe (PID: 3016)
- unpack200.exe (PID: 2616)
- unpack200.exe (PID: 2804)
- unpack200.exe (PID: 3468)
- unpack200.exe (PID: 3748)
- unpack200.exe (PID: 1092)
- unpack200.exe (PID: 2652)
- unpack200.exe (PID: 2508)
- unpack200.exe (PID: 2124)
- unpack200.exe (PID: 272)
- unpack200.exe (PID: 1836)
- unpack200.exe (PID: 3084)
- unpack200.exe (PID: 2760)
- unpack200.exe (PID: 2548)
- unpack200.exe (PID: 3384)
- unpack200.exe (PID: 1704)
- unpack200.exe (PID: 3316)
- unpack200.exe (PID: 3956)
- unpack200.exe (PID: 3968)
- unpack200.exe (PID: 3476)
- unpack200.exe (PID: 1352)
- unpack200.exe (PID: 816)
- unpack200.exe (PID: 2740)
- unpack200.exe (PID: 1468)
- unpack200.exe (PID: 780)
- unpack200.exe (PID: 2248)
- unpack200.exe (PID: 3096)
- unpack200.exe (PID: 2408)
- unpack200.exe (PID: 2004)
- unpack200.exe (PID: 3672)
- unpack200.exe (PID: 2772)
- unpack200.exe (PID: 1196)
- unpack200.exe (PID: 2460)
- unpack200.exe (PID: 572)
- unpack200.exe (PID: 1912)
- unpack200.exe (PID: 3724)
- unpack200.exe (PID: 2004)
- unpack200.exe (PID: 2948)
- unpack200.exe (PID: 2648)
- unpack200.exe (PID: 3148)
- unpack200.exe (PID: 1348)
- unpack200.exe (PID: 2808)
- unpack200.exe (PID: 1456)
- unpack200.exe (PID: 2724)
- unpack200.exe (PID: 3224)
- unpack200.exe (PID: 848)
- unpack200.exe (PID: 3572)
- unpack200.exe (PID: 3996)
- unpack200.exe (PID: 3204)
- unpack200.exe (PID: 280)
- unpack200.exe (PID: 3720)
- unpack200.exe (PID: 2140)
- unpack200.exe (PID: 3464)
- unpack200.exe (PID: 984)
- unpack200.exe (PID: 608)
- unpack200.exe (PID: 3436)
- unpack200.exe (PID: 3544)
- unpack200.exe (PID: 3320)
- unpack200.exe (PID: 3896)
- unpack200.exe (PID: 3932)
- unpack200.exe (PID: 2976)
- unpack200.exe (PID: 3708)
- unpack200.exe (PID: 3516)
- unpack200.exe (PID: 3220)
- unpack200.exe (PID: 3692)
- unpack200.exe (PID: 3348)
- unpack200.exe (PID: 3316)
- unpack200.exe (PID: 3152)
- unpack200.exe (PID: 3752)
- unpack200.exe (PID: 2248)
- unpack200.exe (PID: 2536)
- unpack200.exe (PID: 3260)
- unpack200.exe (PID: 664)
- unpack200.exe (PID: 1412)
- unpack200.exe (PID: 2460)
- unpack200.exe (PID: 2812)
- unpack200.exe (PID: 3680)
- unpack200.exe (PID: 2916)
- unpack200.exe (PID: 2752)
- unpack200.exe (PID: 2940)
- unpack200.exe (PID: 2892)
- unpack200.exe (PID: 3012)
- unpack200.exe (PID: 3504)
- unpack200.exe (PID: 3476)
- unpack200.exe (PID: 3796)
- unpack200.exe (PID: 2448)
- unpack200.exe (PID: 3912)
- unpack200.exe (PID: 820)
- unpack200.exe (PID: 2716)
- unpack200.exe (PID: 1852)
- unpack200.exe (PID: 3972)
- unpack200.exe (PID: 2748)
- unpack200.exe (PID: 272)
- unpack200.exe (PID: 1516)
- unpack200.exe (PID: 2820)
- unpack200.exe (PID: 3776)
- unpack200.exe (PID: 2856)
- unpack200.exe (PID: 3580)
- unpack200.exe (PID: 3168)
- unpack200.exe (PID: 1140)
- postgres.exe (PID: 2220)
- unpack200.exe (PID: 3336)
- unpack200.exe (PID: 1564)
- cmd.exe (PID: 3928)
- java.exe (PID: 3088)
- cmd.exe (PID: 2676)
- javaw.exe (PID: 3524)
- java.exe (PID: 1504)
- wrapper.exe (PID: 2084)
- pg_isready.exe (PID: 3548)
- pg_ctl.exe (PID: 2508)
- postgres.exe (PID: 2976)
- postgres.exe (PID: 3948)
- postgres.exe (PID: 2752)
- postgres.exe (PID: 2564)
- postgres.exe (PID: 2576)
- postgres.exe (PID: 2124)
- unpack200.exe (PID: 548)
- postgres.exe (PID: 3412)
- postgres.exe (PID: 3128)
- postgres.exe (PID: 3440)
- postgres.exe (PID: 2684)
- postgres.exe (PID: 2632)
- postgres.exe (PID: 3760)
- unpack200.exe (PID: 3616)
- postgres.exe (PID: 1352)
- psql.exe (PID: 3228)
- pg_isready.exe (PID: 4072)
- postgres.exe (PID: 1828)
- psql.exe (PID: 2524)
- unpack200.exe (PID: 3424)
- postgres.exe (PID: 2972)
- psql.exe (PID: 2900)
- postgres.exe (PID: 1832)
- postgres.exe (PID: 3312)
- postgres.exe (PID: 1440)
- psql.exe (PID: 3368)
- postgres.exe (PID: 1948)
- postgres.exe (PID: 2920)
- postgres.exe (PID: 3332)
- postgres.exe (PID: 3844)
Application was dropped or rewritten from another process
- ManageEngine_ExchangeReporterPlus.exe (PID: 1332)
- unpack200.exe (PID: 2532)
- unpack200.exe (PID: 312)
- unpack200.exe (PID: 3228)
- unpack200.exe (PID: 3536)
- unpack200.exe (PID: 3380)
- unpack200.exe (PID: 3960)
- unpack200.exe (PID: 2420)
- unpack200.exe (PID: 3444)
- unpack200.exe (PID: 3768)
- unpack200.exe (PID: 3992)
- unpack200.exe (PID: 2012)
- unpack200.exe (PID: 984)
- unpack200.exe (PID: 2692)
- unpack200.exe (PID: 940)
- unpack200.exe (PID: 3652)
- unpack200.exe (PID: 3232)
- unpack200.exe (PID: 1524)
- unpack200.exe (PID: 3632)
- unpack200.exe (PID: 3832)
- unpack200.exe (PID: 2080)
- unpack200.exe (PID: 3576)
- unpack200.exe (PID: 1724)
- unpack200.exe (PID: 880)
- unpack200.exe (PID: 3248)
- unpack200.exe (PID: 3324)
- unpack200.exe (PID: 1948)
- unpack200.exe (PID: 3588)
- unpack200.exe (PID: 3272)
- unpack200.exe (PID: 3848)
- unpack200.exe (PID: 3800)
- unpack200.exe (PID: 1380)
- unpack200.exe (PID: 3172)
- unpack200.exe (PID: 1604)
- unpack200.exe (PID: 3704)
- unpack200.exe (PID: 3596)
- unpack200.exe (PID: 3452)
- unpack200.exe (PID: 3652)
- unpack200.exe (PID: 2080)
- unpack200.exe (PID: 3640)
- unpack200.exe (PID: 1092)
- unpack200.exe (PID: 1916)
- unpack200.exe (PID: 304)
- unpack200.exe (PID: 2588)
- unpack200.exe (PID: 748)
- unpack200.exe (PID: 576)
- unpack200.exe (PID: 2192)
- unpack200.exe (PID: 2816)
- unpack200.exe (PID: 2948)
- unpack200.exe (PID: 1468)
- unpack200.exe (PID: 3528)
- unpack200.exe (PID: 3288)
- unpack200.exe (PID: 1380)
- unpack200.exe (PID: 1720)
- unpack200.exe (PID: 1912)
- unpack200.exe (PID: 1784)
- unpack200.exe (PID: 1844)
- unpack200.exe (PID: 3736)
- unpack200.exe (PID: 2244)
- unpack200.exe (PID: 1828)
- unpack200.exe (PID: 528)
- unpack200.exe (PID: 3152)
- unpack200.exe (PID: 3544)
- unpack200.exe (PID: 3024)
- unpack200.exe (PID: 2716)
- unpack200.exe (PID: 2012)
- unpack200.exe (PID: 3820)
- unpack200.exe (PID: 3992)
- unpack200.exe (PID: 2212)
- unpack200.exe (PID: 576)
- unpack200.exe (PID: 1724)
- unpack200.exe (PID: 2764)
- unpack200.exe (PID: 3224)
- unpack200.exe (PID: 3376)
- unpack200.exe (PID: 3896)
- unpack200.exe (PID: 1064)
- unpack200.exe (PID: 1388)
- unpack200.exe (PID: 3952)
- unpack200.exe (PID: 3832)
- unpack200.exe (PID: 3068)
- unpack200.exe (PID: 1140)
- unpack200.exe (PID: 3588)
- unpack200.exe (PID: 2732)
- unpack200.exe (PID: 3584)
- unpack200.exe (PID: 2672)
- unpack200.exe (PID: 3648)
- unpack200.exe (PID: 1944)
- unpack200.exe (PID: 3504)
- unpack200.exe (PID: 3640)
- unpack200.exe (PID: 3156)
- unpack200.exe (PID: 2500)
- unpack200.exe (PID: 3468)
- unpack200.exe (PID: 2616)
- unpack200.exe (PID: 2692)
- unpack200.exe (PID: 3452)
- unpack200.exe (PID: 3084)
- unpack200.exe (PID: 3748)
- unpack200.exe (PID: 1092)
- unpack200.exe (PID: 3340)
- unpack200.exe (PID: 3380)
- unpack200.exe (PID: 3776)
- unpack200.exe (PID: 4040)
- unpack200.exe (PID: 3168)
- unpack200.exe (PID: 1876)
- unpack200.exe (PID: 3016)
- unpack200.exe (PID: 2804)
- unpack200.exe (PID: 1836)
- unpack200.exe (PID: 2508)
- unpack200.exe (PID: 2124)
- unpack200.exe (PID: 2760)
- unpack200.exe (PID: 2548)
- unpack200.exe (PID: 272)
- unpack200.exe (PID: 2652)
- unpack200.exe (PID: 3476)
- unpack200.exe (PID: 3384)
- unpack200.exe (PID: 1704)
- unpack200.exe (PID: 3316)
- unpack200.exe (PID: 1352)
- unpack200.exe (PID: 780)
- unpack200.exe (PID: 3956)
- unpack200.exe (PID: 3968)
- unpack200.exe (PID: 816)
- unpack200.exe (PID: 3096)
- unpack200.exe (PID: 1468)
- unpack200.exe (PID: 2408)
- unpack200.exe (PID: 2740)
- unpack200.exe (PID: 2460)
- unpack200.exe (PID: 2248)
- unpack200.exe (PID: 1912)
- unpack200.exe (PID: 3672)
- unpack200.exe (PID: 1196)
- unpack200.exe (PID: 2772)
- unpack200.exe (PID: 3148)
- unpack200.exe (PID: 2648)
- unpack200.exe (PID: 572)
- unpack200.exe (PID: 2004)
- unpack200.exe (PID: 2808)
- unpack200.exe (PID: 3724)
- unpack200.exe (PID: 1456)
- unpack200.exe (PID: 2004)
- unpack200.exe (PID: 2948)
- unpack200.exe (PID: 280)
- unpack200.exe (PID: 1348)
- unpack200.exe (PID: 3224)
- unpack200.exe (PID: 848)
- unpack200.exe (PID: 3996)
- unpack200.exe (PID: 3572)
- unpack200.exe (PID: 3204)
- unpack200.exe (PID: 2724)
- unpack200.exe (PID: 3720)
- unpack200.exe (PID: 2140)
- unpack200.exe (PID: 608)
- unpack200.exe (PID: 3436)
- unpack200.exe (PID: 3464)
- unpack200.exe (PID: 3544)
- unpack200.exe (PID: 3320)
- unpack200.exe (PID: 984)
- unpack200.exe (PID: 3932)
- unpack200.exe (PID: 3708)
- unpack200.exe (PID: 3516)
- unpack200.exe (PID: 3220)
- unpack200.exe (PID: 3896)
- unpack200.exe (PID: 2976)
- unpack200.exe (PID: 3692)
- unpack200.exe (PID: 3348)
- unpack200.exe (PID: 3316)
- unpack200.exe (PID: 2536)
- unpack200.exe (PID: 3752)
- unpack200.exe (PID: 3260)
- unpack200.exe (PID: 3152)
- unpack200.exe (PID: 664)
- unpack200.exe (PID: 548)
- unpack200.exe (PID: 1412)
- unpack200.exe (PID: 3680)
- unpack200.exe (PID: 2916)
- unpack200.exe (PID: 2752)
- unpack200.exe (PID: 2812)
- unpack200.exe (PID: 2940)
- unpack200.exe (PID: 2892)
- unpack200.exe (PID: 3616)
- unpack200.exe (PID: 3012)
- unpack200.exe (PID: 3424)
- unpack200.exe (PID: 3504)
- unpack200.exe (PID: 3476)
- unpack200.exe (PID: 3796)
- unpack200.exe (PID: 2448)
- unpack200.exe (PID: 3912)
- unpack200.exe (PID: 820)
- unpack200.exe (PID: 2716)
- unpack200.exe (PID: 1852)
- unpack200.exe (PID: 3972)
- unpack200.exe (PID: 272)
- unpack200.exe (PID: 2748)
- unpack200.exe (PID: 1516)
- unpack200.exe (PID: 2820)
- unpack200.exe (PID: 3776)
- unpack200.exe (PID: 2856)
- unpack200.exe (PID: 3580)
- unpack200.exe (PID: 3168)
- unpack200.exe (PID: 1140)
- unpack200.exe (PID: 1564)
- java.exe (PID: 3088)
- postgres.exe (PID: 2220)
- gettimezone.exe (PID: 1256)
- ReadID.exe (PID: 2352)
- javaw.exe (PID: 3524)
- exchangereporter.exe (PID: 3692)
- wrapper.exe (PID: 2084)
- java.exe (PID: 1504)
- pg_isready.exe (PID: 3548)
- postgres.exe (PID: 2976)
- postgres.exe (PID: 3948)
- postgres.exe (PID: 2564)
- pg_ctl.exe (PID: 2508)
- postgres.exe (PID: 2752)
- postgres.exe (PID: 2576)
- unpack200.exe (PID: 2248)
- postgres.exe (PID: 2684)
- postgres.exe (PID: 3760)
- postgres.exe (PID: 2632)
- postgres.exe (PID: 3440)
- postgres.exe (PID: 2124)
- postgres.exe (PID: 3128)
- unpack200.exe (PID: 2460)
- pg_isready.exe (PID: 4072)
- postgres.exe (PID: 3412)
- psql.exe (PID: 3228)
- psql.exe (PID: 2524)
- postgres.exe (PID: 1828)
- postgres.exe (PID: 1352)
- psql.exe (PID: 2900)
- postgres.exe (PID: 1832)
- postgres.exe (PID: 3312)
- postgres.exe (PID: 2920)
- postgres.exe (PID: 1440)
- psql.exe (PID: 3368)
- postgres.exe (PID: 2972)
- unpack200.exe (PID: 3336)
- postgres.exe (PID: 1948)
- postgres.exe (PID: 3844)
- postgres.exe (PID: 2960)
- postgres.exe (PID: 3332)
Changes settings of System certificates
- wrapper.exe (PID: 2084)
- cscript.exe (PID: 2892)
SUSPICIOUS
Executes application which crashes
- cmd.exe (PID: 3400)
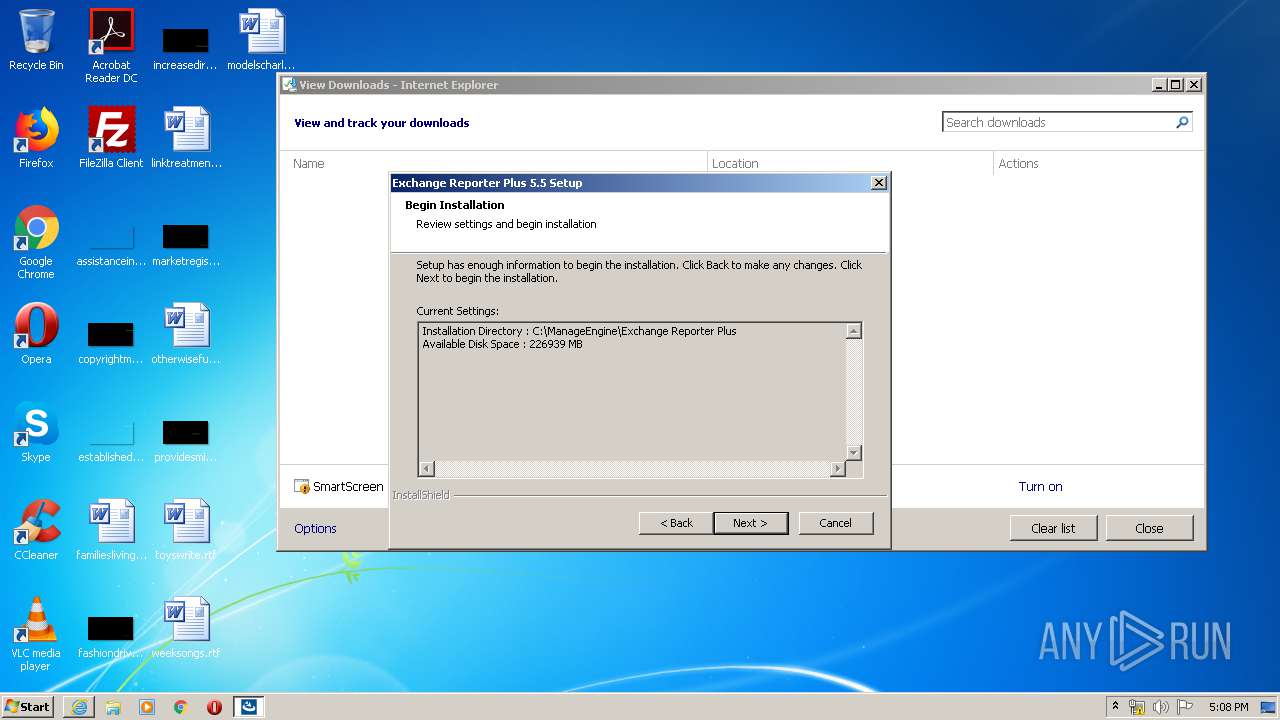
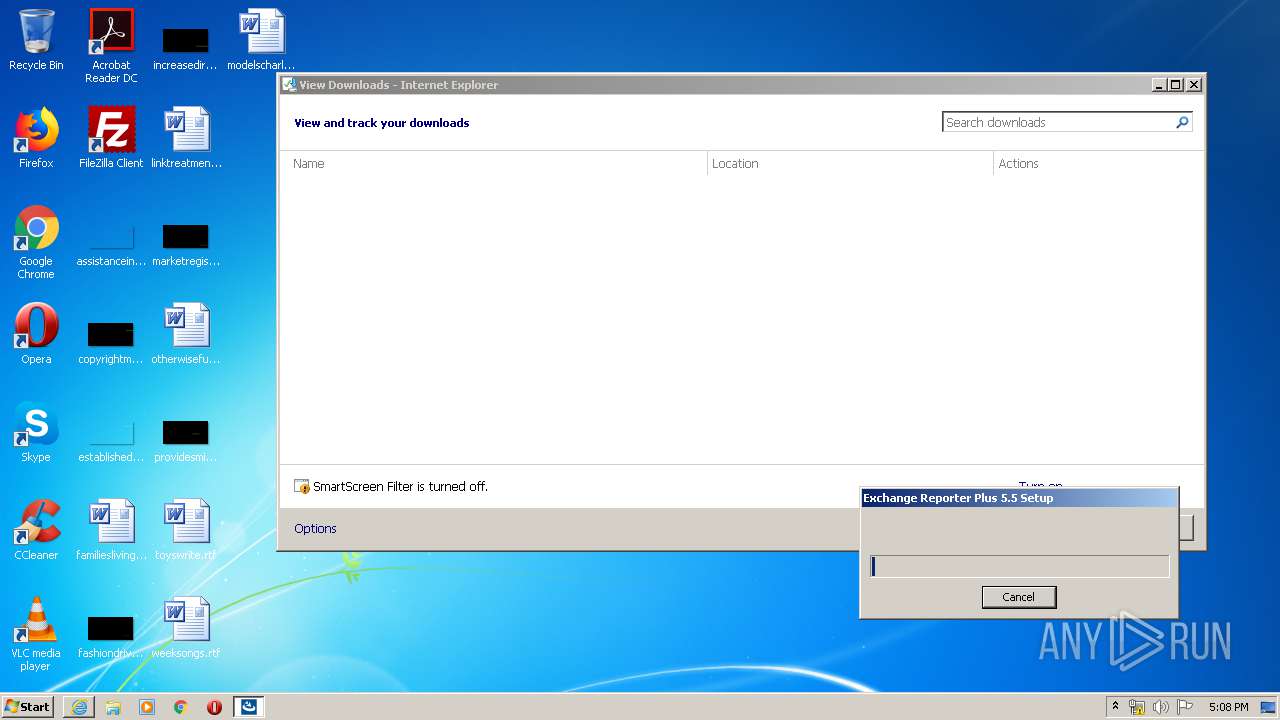
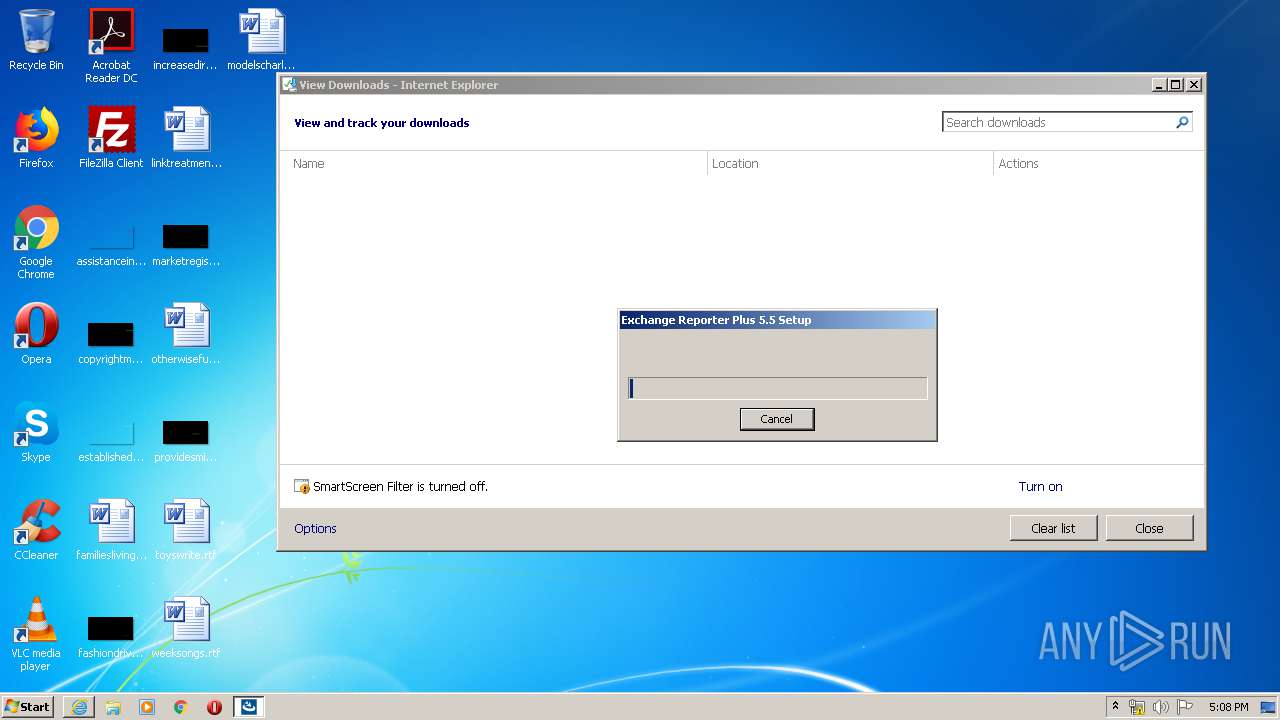
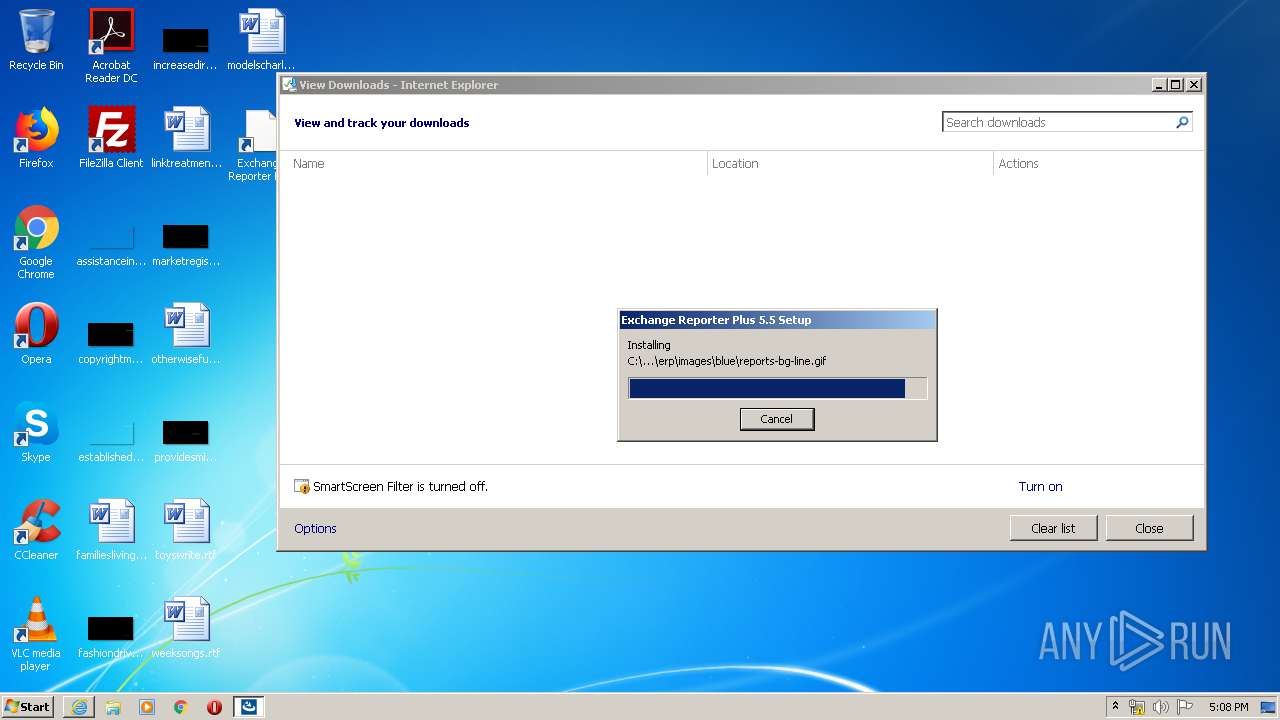
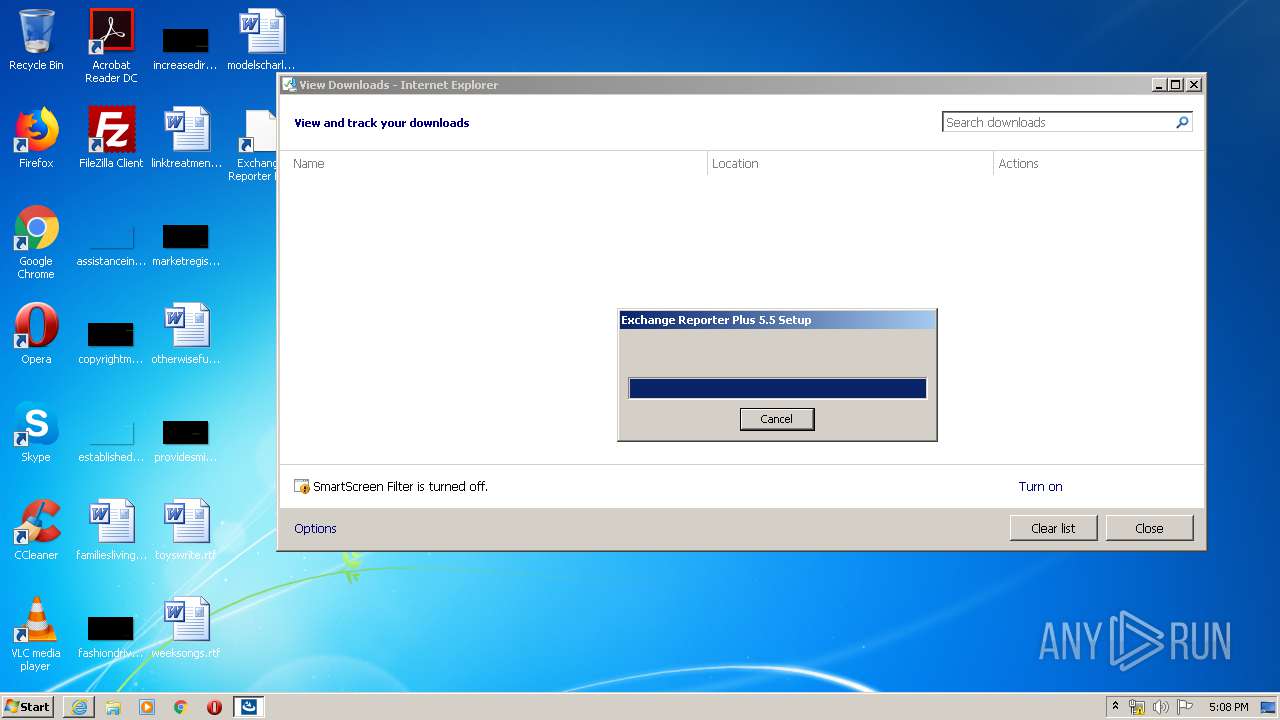
Creates files in the program directory
- ManageEngine_ExchangeReporterPlus.exe (PID: 1332)
- javaw.exe (PID: 3524)
Executable content was dropped or overwritten
- ManageEngine_ExchangeReporterPlus.exe (PID: 1632)
- ManageEngine_ExchangeReporterPlus.exe (PID: 1332)
Reads internet explorer settings
- ManageEngine_ExchangeReporterPlus.exe (PID: 1332)
Executed as Windows Service
- vssvc.exe (PID: 3180)
Searches for installed software
- ManageEngine_ExchangeReporterPlus.exe (PID: 1332)
Starts CMD.EXE for commands execution
- ManageEngine_ExchangeReporterPlus.exe (PID: 1332)
- cmd.exe (PID: 1232)
- exchangereporter.exe (PID: 3692)
- wrapper.exe (PID: 2084)
- pg_ctl.exe (PID: 2508)
- postgres.exe (PID: 3760)
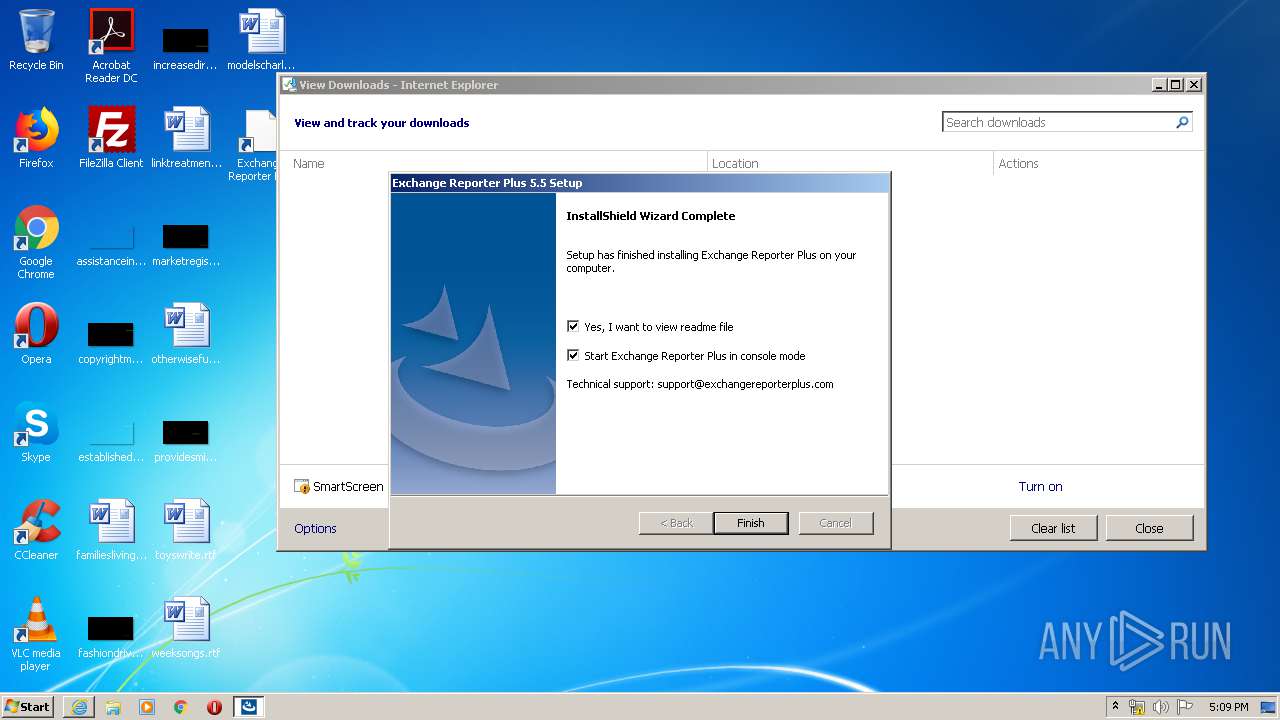
Creates a software uninstall entry
- ManageEngine_ExchangeReporterPlus.exe (PID: 1332)
Uses ICACLS.EXE to modify access control list
- cmd.exe (PID: 1232)
- cmd.exe (PID: 1516)
- javaw.exe (PID: 3524)
Executes scripts
- cmd.exe (PID: 608)
Reads Internet Cache Settings
- ManageEngine_ExchangeReporterPlus.exe (PID: 1332)
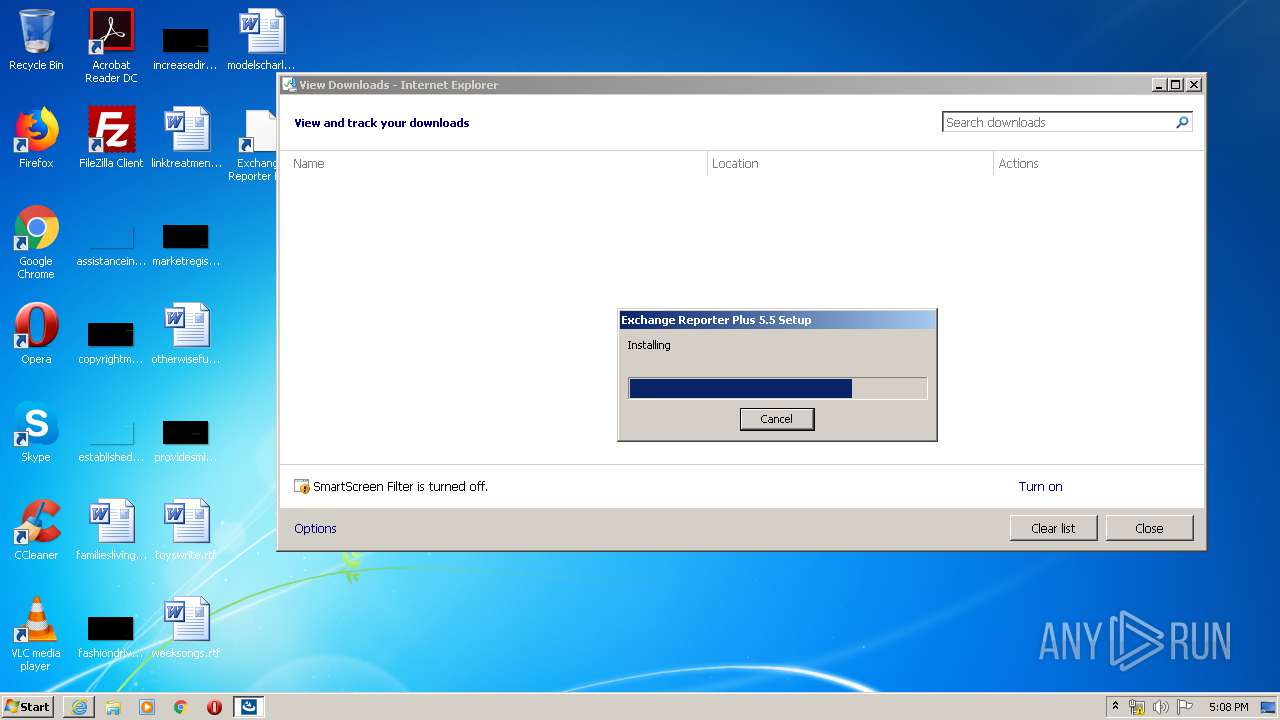
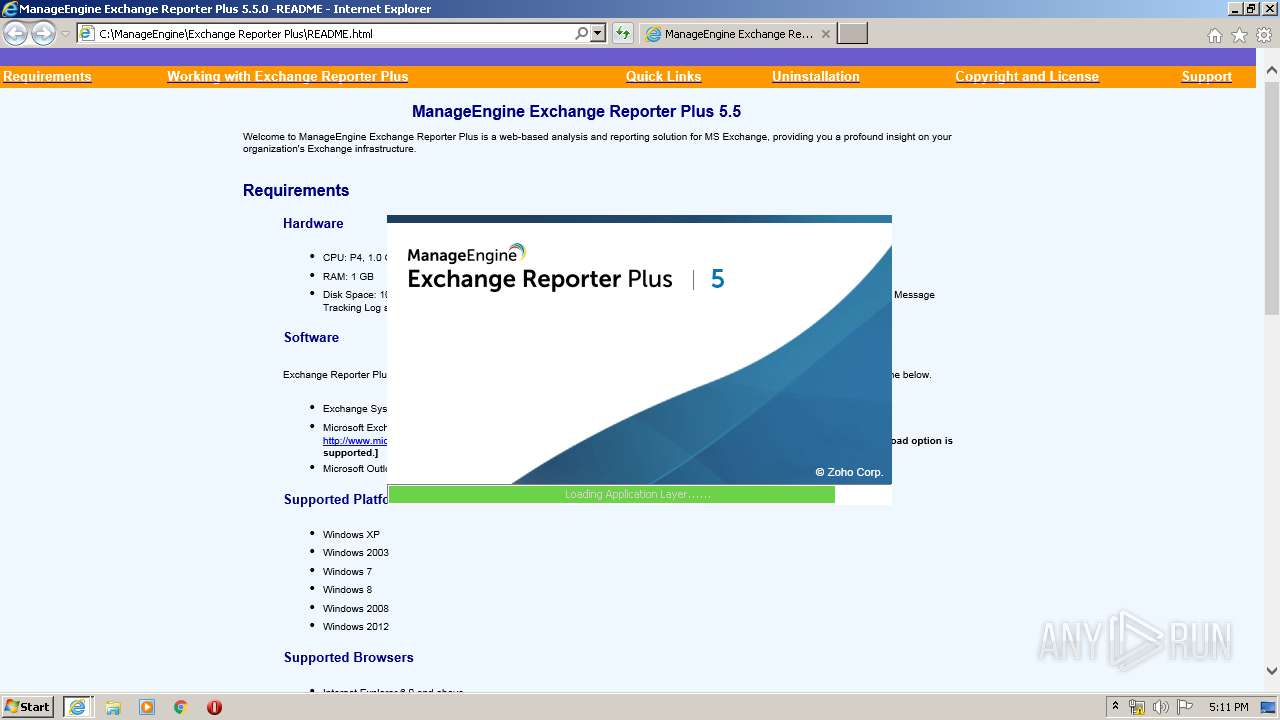
Starts Internet Explorer
- ManageEngine_ExchangeReporterPlus.exe (PID: 1332)
Adds / modifies Windows certificates
- wrapper.exe (PID: 2084)
- cscript.exe (PID: 2892)
Application launched itself
- postgres.exe (PID: 3948)
INFO
Reads Internet Cache Settings
- iexplore.exe (PID: 2880)
- iexplore.exe (PID: 4004)
- iexplore.exe (PID: 3400)
- iexplore.exe (PID: 2312)
Changes internet zones settings
- iexplore.exe (PID: 2880)
- iexplore.exe (PID: 3400)
Application launched itself
- iexplore.exe (PID: 2880)
- iexplore.exe (PID: 3400)
Low-level read access rights to disk partition
- vssvc.exe (PID: 3180)
Modifies the phishing filter of IE
- iexplore.exe (PID: 2880)
Creates files in the user directory
- iexplore.exe (PID: 2880)
Dropped object may contain Bitcoin addresses
- ManageEngine_ExchangeReporterPlus.exe (PID: 1332)
Reads settings of System Certificates
- iexplore.exe (PID: 2880)
- cscript.exe (PID: 2892)
Reads internet explorer settings
- iexplore.exe (PID: 2312)
Changes settings of System certificates
- iexplore.exe (PID: 2880)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2880)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
344
Monitored processes
281
Malicious processes
198
Suspicious processes
44
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 272 | .\jre\bin\unpack200 -J-mx200M -r "C:\ManageEngine\Exchange Reporter Plus\lib\struts-taglib-1.3.10.pack.gz" "lib\struts-taglib-1.3.10.jar" | C:\ManageEngine\Exchange Reporter Plus\jre\bin\unpack200.exe | — | cmd.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: HIGH Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.1310.11 Modules
| |||||||||||||||
| 272 | .\jre\bin\unpack200 -J-mx200M -r "C:\ManageEngine\Exchange Reporter Plus\lib\tomcat\tomcat-juli.pack.gz" "lib\tomcat\tomcat-juli.jar" | C:\ManageEngine\Exchange Reporter Plus\jre\bin\unpack200.exe | — | cmd.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: HIGH Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.1310.11 Modules
| |||||||||||||||
| 280 | .\jre\bin\unpack200 -J-mx200M -r "C:\ManageEngine\Exchange Reporter Plus\jre\lib\security\local_policy.pack.gz" "jre\lib\security\local_policy.jar" | C:\ManageEngine\Exchange Reporter Plus\jre\bin\unpack200.exe | — | cmd.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: HIGH Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.1310.11 Modules
| |||||||||||||||
| 304 | .\jre\bin\unpack200 -J-mx200M -r "C:\ManageEngine\Exchange Reporter Plus\lib\commons-csv-1.3.pack.gz" "lib\commons-csv-1.3.jar" | C:\ManageEngine\Exchange Reporter Plus\jre\bin\unpack200.exe | — | cmd.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: HIGH Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.1310.11 Modules
| |||||||||||||||
| 312 | .\jre\bin\unpack200 -J-mx200M -r "C:\ManageEngine\Exchange Reporter Plus\bin\wrapper.pack.gz" "bin\wrapper.jar" | C:\ManageEngine\Exchange Reporter Plus\jre\bin\unpack200.exe | — | cmd.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: HIGH Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.1310.11 Modules
| |||||||||||||||
| 376 | cmd /c ..\bin\jreCorrector.bat | C:\Windows\system32\cmd.exe | — | wrapper.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 528 | .\jre\bin\unpack200 -J-mx200M -r "C:\ManageEngine\Exchange Reporter Plus\lib\framework-tools.pack.gz" "lib\framework-tools.jar" | C:\ManageEngine\Exchange Reporter Plus\jre\bin\unpack200.exe | — | cmd.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: HIGH Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.1310.11 Modules
| |||||||||||||||
| 548 | .\jre\bin\unpack200 -J-mx200M -r "C:\ManageEngine\Exchange Reporter Plus\lib\tomcat\annotations-api.pack.gz" "lib\tomcat\annotations-api.jar" | C:\ManageEngine\Exchange Reporter Plus\jre\bin\unpack200.exe | — | cmd.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: HIGH Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.1310.11 Modules
| |||||||||||||||
| 548 | icacls.exe C:\ProgramData\Oracle\Java\.oracle_jre_usage\eb58023faf4258ed.timestamp /grant "everyone":(OI)(CI)M | C:\Windows\system32\icacls.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 572 | .\jre\bin\unpack200 -J-mx200M -r "C:\ManageEngine\Exchange Reporter Plus\jre\lib\jsse.pack.gz" "jre\lib\jsse.jar" | C:\ManageEngine\Exchange Reporter Plus\jre\bin\unpack200.exe | — | cmd.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: HIGH Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.1310.11 Modules
| |||||||||||||||
Total events
9 640
Read events
1 914
Write events
5 639
Delete events
2 087
Modification events
| (PID) Process: | (2880) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 3587414400 | |||
| (PID) Process: | (2880) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30792975 | |||
| (PID) Process: | (2880) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2880) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2880) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2880) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2880) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2880) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A1000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2880) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2880) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
515
Suspicious files
6 387
Text files
3 699
Unknown types
1 220
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4004 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\ManageEngine_ExchangeReporterPlus[1].exe | — | |
MD5:— | SHA256:— | |||
| 2880 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Cab3AF9.tmp | — | |
MD5:— | SHA256:— | |||
| 2880 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Tar3AFA.tmp | — | |
MD5:— | SHA256:— | |||
| 2880 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\VersionManager\ver46E2.tmp | — | |
MD5:— | SHA256:— | |||
| 2880 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\7A35XN3V.txt | — | |
MD5:— | SHA256:— | |||
| 2880 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\R5H90VP4.txt | — | |
MD5:— | SHA256:— | |||
| 4004 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\ManageEngine_ExchangeReporterPlus.exe.qcw5v5x.partial | — | |
MD5:— | SHA256:— | |||
| 2880 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFF77EC166ED738F72.TMP | — | |
MD5:— | SHA256:— | |||
| 2880 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\ManageEngine_ExchangeReporterPlus.exe.qcw5v5x.partial:Zone.Identifier | — | |
MD5:— | SHA256:— | |||
| 2880 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\ManageEngine_ExchangeReporterPlus.exe | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
15
DNS requests
13
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2880 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
1332 | ManageEngine_ExchangeReporterPlus.exe | POST | 200 | 117.20.43.131:80 | http://www.manageengine.com/cgi-bin/mail?manageengine-feedback | SG | text | 47 b | whitelisted |
2880 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
2892 | cscript.exe | GET | 301 | 8.39.54.155:80 | http://www.zoho.com/ | US | html | 134 b | suspicious |
3400 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2880 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2892 | cscript.exe | 8.39.54.155:443 | www.zoho.com | ZOHO | US | unknown |
1332 | ManageEngine_ExchangeReporterPlus.exe | 117.20.43.131:80 | www.manageengine.com | Internap Network Services | SG | suspicious |
3400 | iexplore.exe | 204.79.197.200:80 | ieonline.microsoft.com | Microsoft Corporation | US | whitelisted |
4004 | iexplore.exe | 117.20.43.131:80 | www.manageengine.com | Internap Network Services | SG | suspicious |
2892 | cscript.exe | 8.39.54.155:80 | www.zoho.com | ZOHO | US | unknown |
2880 | iexplore.exe | 204.79.197.200:443 | ieonline.microsoft.com | Microsoft Corporation | US | whitelisted |
2880 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.manageengine.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
ieonline.microsoft.com |
| whitelisted |
dns.msftncsi.com |
| shared |
www.zoho.com |
| suspicious |
www.bing.com |
| whitelisted |
api.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4004 | iexplore.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
4004 | iexplore.exe | Misc activity | ET INFO EXE - Served Attached HTTP |