| URL: | https://1drv.ms/w/s!BNuWSPxeV1Jsg02hd_zxyBAfMmkH |
| Full analysis: | https://app.any.run/tasks/0fc43aaa-fa99-4325-a970-311740fb7d4f |
| Verdict: | Malicious activity |
| Analysis date: | December 18, 2018, 14:10:59 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 4EDE88D98DCAB4D10DF7771DB16AE2F7 |
| SHA1: | C4154CE38731B368A90F8C139EA84FAE72059378 |
| SHA256: | CD50A0D929383CF898896B6EF9966D272B3398BCDEF88C990C917D1DE1D0CC4D |
| SSDEEP: | 3:N8qDLIWK5DbPivXNB6WkDk:2qXYPPodBL |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Reads settings of System Certificates
- chrome.exe (PID: 2844)
Application launched itself
- chrome.exe (PID: 2844)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
40
Monitored processes
12
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2260 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=884,9649827737269624848,17959204316204225719,131072 --enable-features=PasswordImport --service-pipe-token=C7E7CECACA2241A5A05BD0661CAD52E9 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=C7E7CECACA2241A5A05BD0661CAD52E9 --renderer-client-id=4 --mojo-platform-channel-handle=1904 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2424 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=884,9649827737269624848,17959204316204225719,131072 --enable-features=PasswordImport --disable-gpu-sandbox --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=2849381AEE9DDE39B7F7A6ED12895314 --mojo-platform-channel-handle=3204 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2468 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=884,9649827737269624848,17959204316204225719,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=E8FA8BA63C363B99253457780B436EEC --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=E8FA8BA63C363B99253457780B436EEC --renderer-client-id=5 --mojo-platform-channel-handle=2756 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2592 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=884,9649827737269624848,17959204316204225719,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=2C557FA825441A09DB5D5A9F4DCC2668 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2C557FA825441A09DB5D5A9F4DCC2668 --renderer-client-id=8 --mojo-platform-channel-handle=2212 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2780 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2848 --on-initialized-event-handle=304 --parent-handle=308 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2844 | "C:\Program Files\Google\Chrome\Application\chrome.exe" https://1drv.ms/w/s!BNuWSPxeV1Jsg02hd_zxyBAfMmkH | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3084 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=884,9649827737269624848,17959204316204225719,131072 --enable-features=PasswordImport --service-pipe-token=1C349B87DBD137BD147BBA25B2FF3549 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1C349B87DBD137BD147BBA25B2FF3549 --renderer-client-id=3 --mojo-platform-channel-handle=2104 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3320 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=884,9649827737269624848,17959204316204225719,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=B5C2DF00D17703BAF5655F75B3049B16 --mojo-platform-channel-handle=608 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3568 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=68.0.3440.106 --initial-client-data=0x78,0x7c,0x80,0x74,0x84,0x6faf00b0,0x6faf00c0,0x6faf00cc | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3816 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=884,9649827737269624848,17959204316204225719,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=664AB509766A9BE9FE2F04A0935B7C73 --mojo-platform-channel-handle=2976 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
Total events
523
Read events
472
Write events
48
Delete events
3
Modification events
| (PID) Process: | (2780) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2844-13189615875543125 |
Value: 259 | |||
| (PID) Process: | (2844) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2844) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2844) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2844) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2844) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2844) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3516-13180984670829101 |
Value: 0 | |||
| (PID) Process: | (2844) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2844) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
| (PID) Process: | (2844) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2844-13189615875543125 |
Value: 259 | |||
Executable files
0
Suspicious files
13
Text files
78
Unknown types
17
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2844 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\e4bb69d8-3b9d-4e36-907b-3f2298914f4d.tmp | — | |
MD5:— | SHA256:— | |||
| 2844 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2844 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2844 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\6264eaff-860a-45f9-a72f-27a8d4a0ac28.tmp | — | |
MD5:— | SHA256:— | |||
| 2844 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:— | SHA256:— | |||
| 2844 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2844 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2844 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF13a972.TMP | text | |
MD5:— | SHA256:— | |||
| 2844 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF13a953.TMP | text | |
MD5:— | SHA256:— | |||
| 2844 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
46
TCP/UDP connections
59
DNS requests
30
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
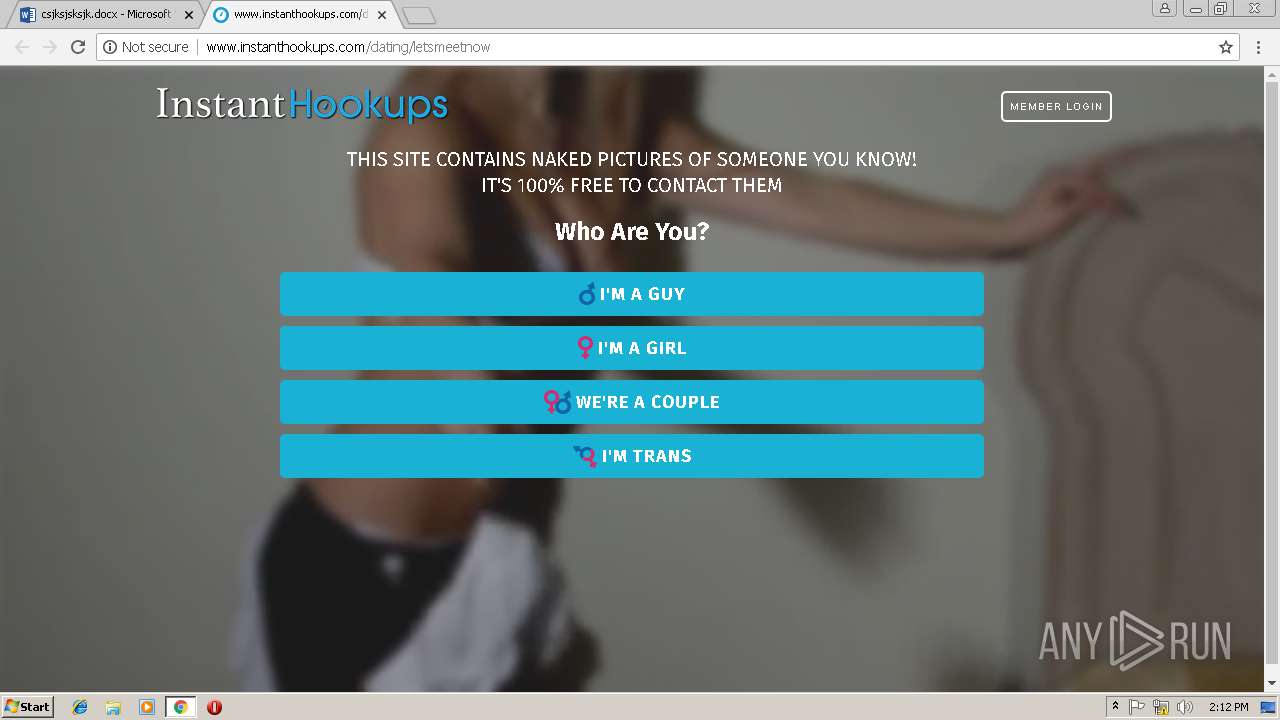
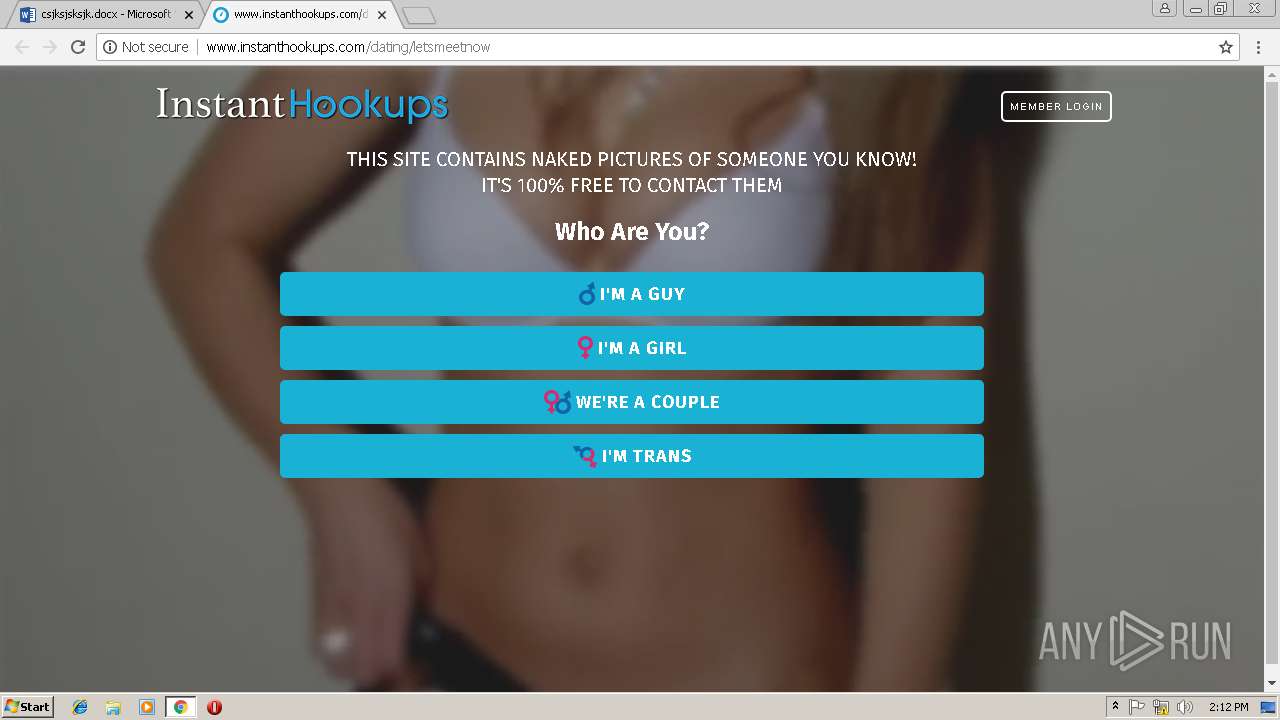
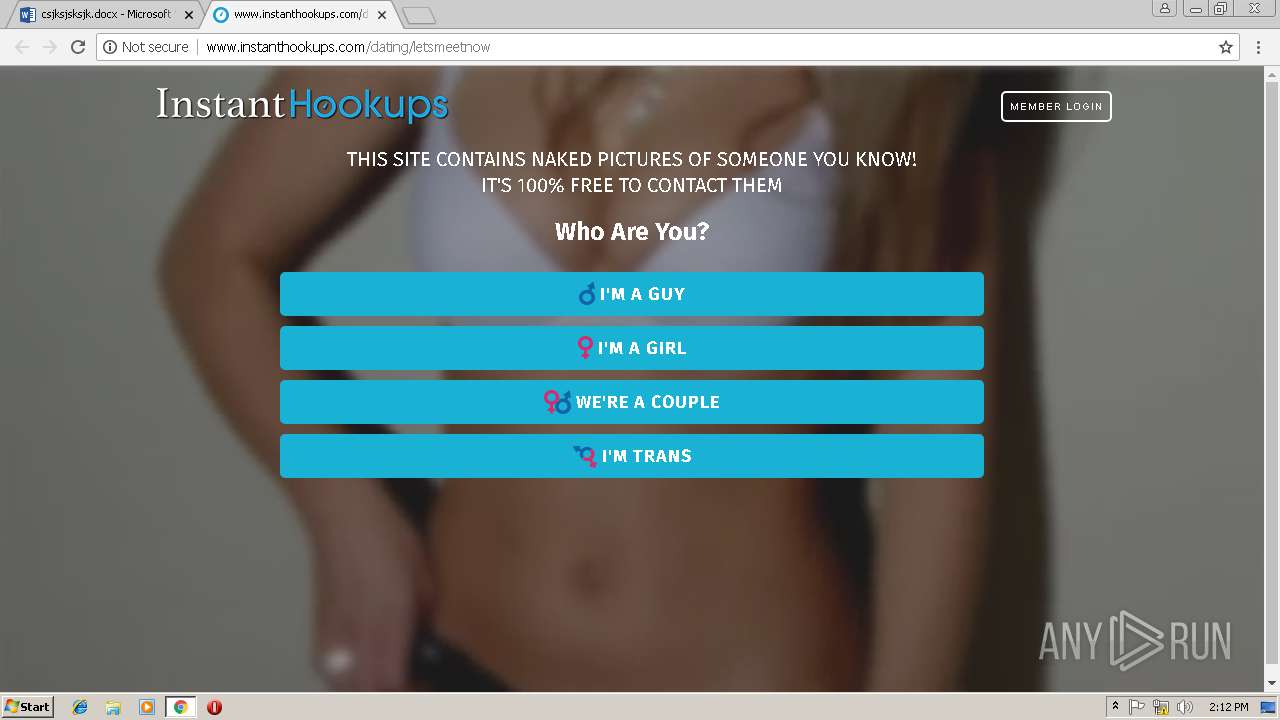
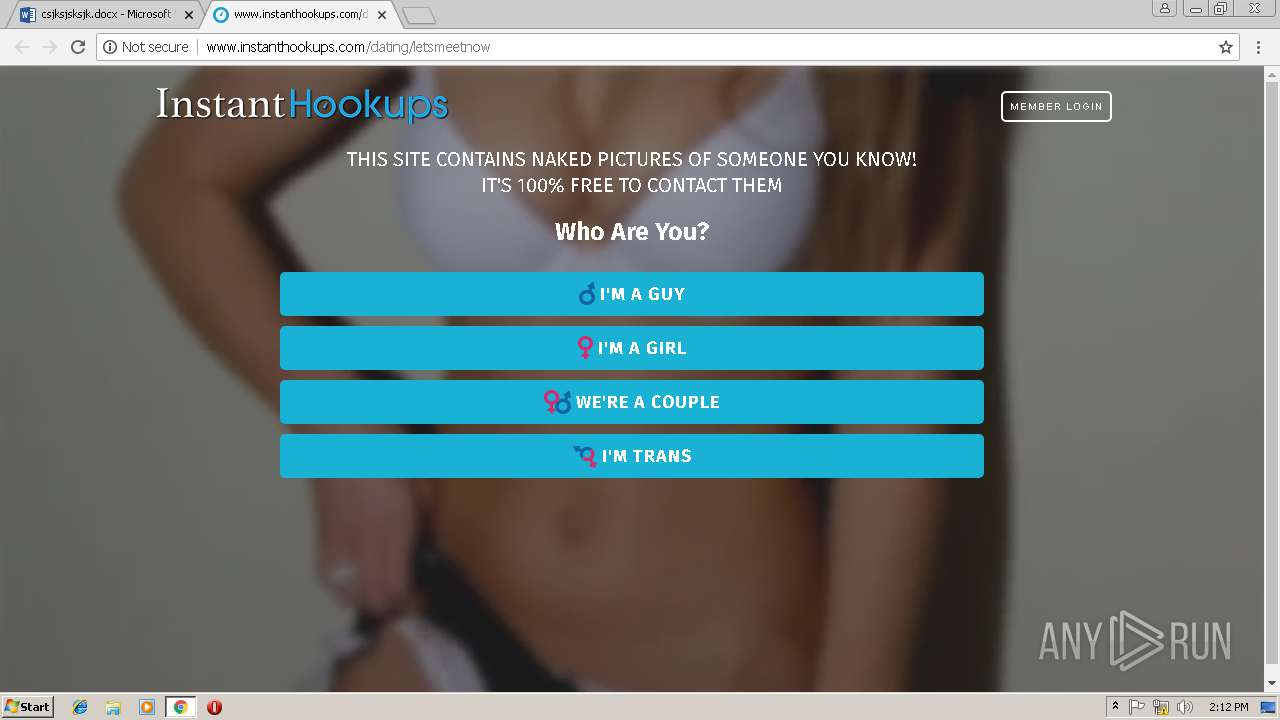
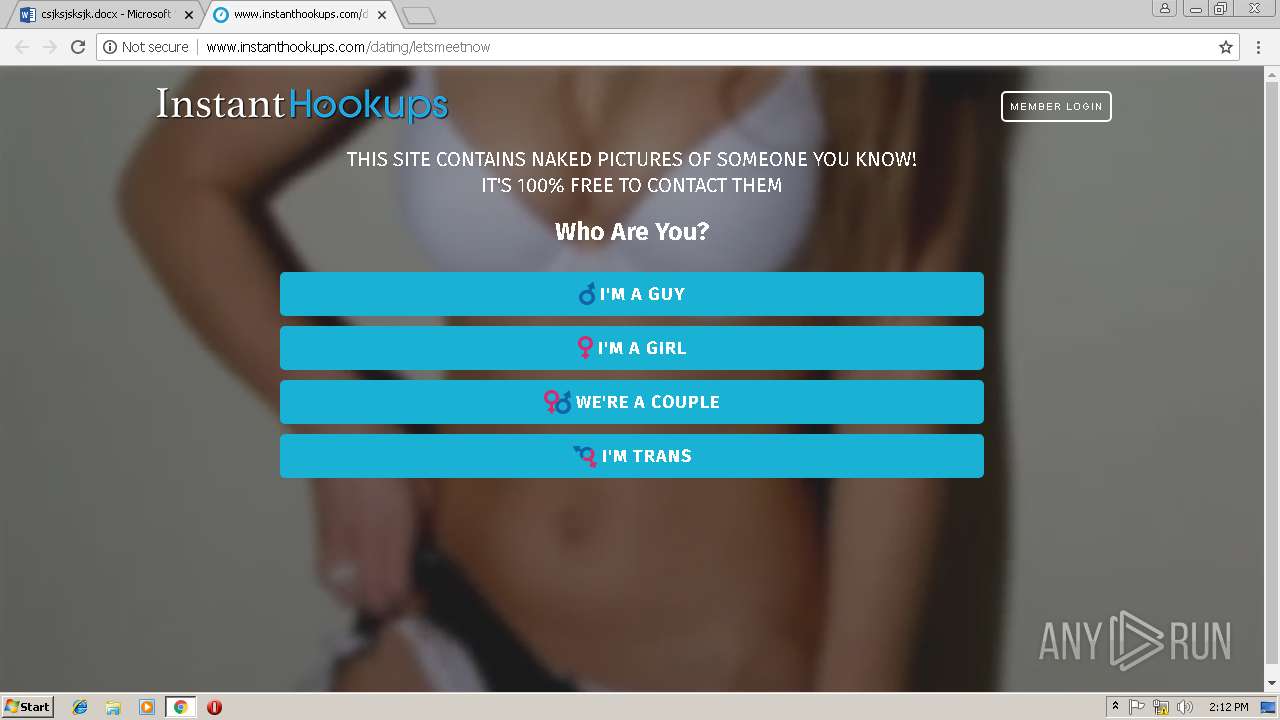
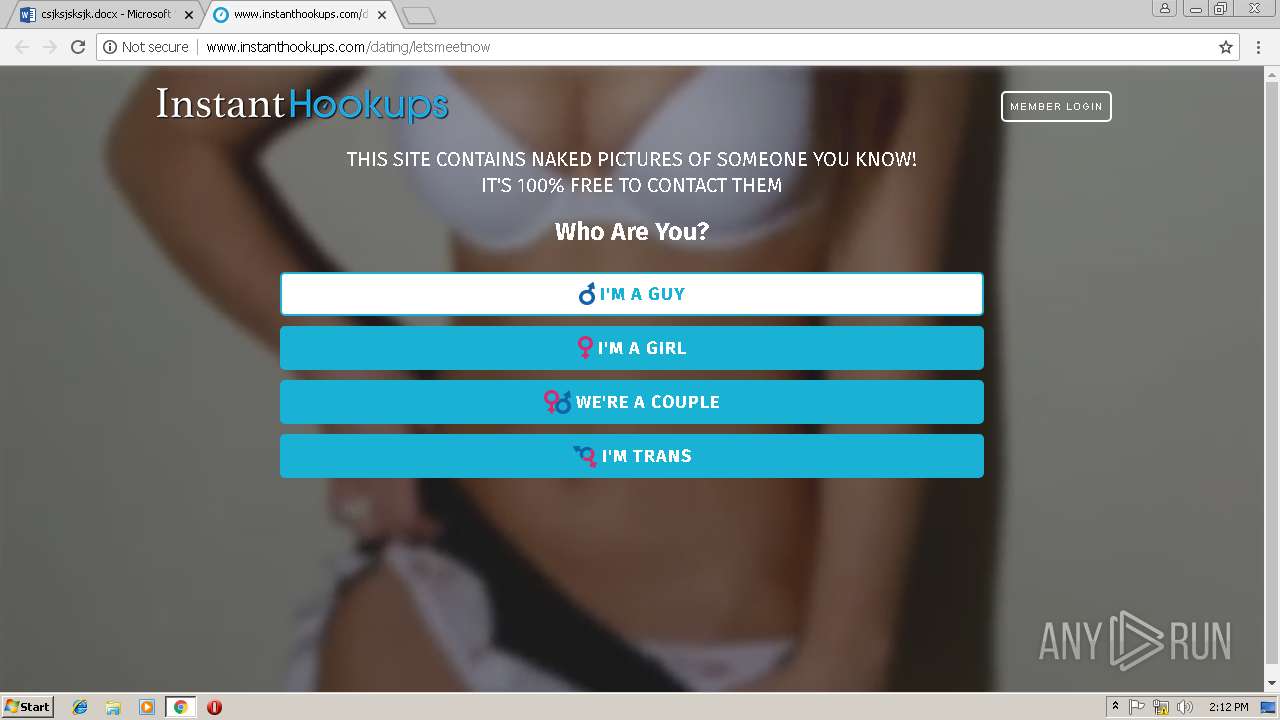
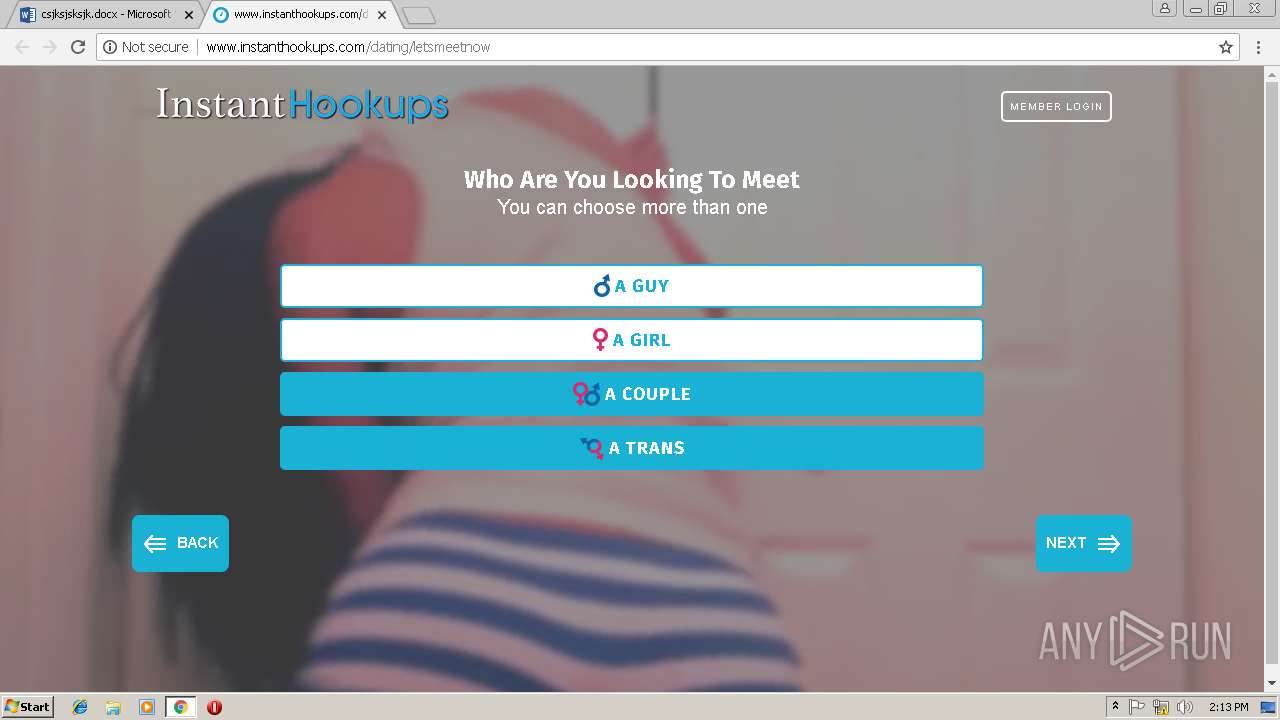
2844 | chrome.exe | GET | 302 | 198.54.126.78:80 | http://cpawide.com/click.php?camp=131&pubid=31&sid2= | US | — | — | suspicious |
2844 | chrome.exe | GET | 301 | 104.17.27.11:80 | http://www.instanthookups.com/dating/letsmeetnow/102262/8972/102beacc5b60d84fbf5ebd7e1e0b85 | US | — | — | shared |
2844 | chrome.exe | GET | 302 | 52.30.52.254:80 | http://www.laxob.com/aff_c?offer_id=11571&aff_id=8972&aff_sub={aff_sub}&aff_sub=31-8734ec9c8dc6e1fc1161c449a | IE | html | 305 b | shared |
2844 | chrome.exe | GET | 302 | 52.50.109.222:80 | http://www.edftrk.com/aff_c?offer_id=10567&aff_id=8972&aff_sub={aff_sub}&aff_sub=31-8734ec9c8dc6e1fc1161c449a | IE | html | 275 b | malicious |
2844 | chrome.exe | GET | 200 | 104.17.27.11:80 | http://www.instanthookups.com/dating/letsmeetnow | US | html | 2.70 Kb | shared |
2844 | chrome.exe | GET | 200 | 69.16.175.10:80 | http://static.instanthookups.com/tour/instanthookups.com/letsmeetnow/style.min.css | US | text | 28.9 Kb | malicious |
2844 | chrome.exe | GET | 200 | 104.17.28.11:80 | http://wt.instanthookups.com/asdfasdf/wtid.js | US | text | 84 b | shared |
2844 | chrome.exe | GET | 200 | 69.16.175.10:80 | http://static.instanthookups.com/de/res/site/default/js/tour_utils.js | US | text | 6.25 Kb | malicious |
2844 | chrome.exe | GET | 200 | 69.16.175.10:80 | http://static.instanthookups.com/tour/instanthookups.com/letsmeetnow/script.min.js | US | text | 89.8 Kb | malicious |
2844 | chrome.exe | GET | 200 | 69.16.175.10:80 | http://static.instanthookups.com/tour/instanthookups.com/letsmeetnow/couple_symbol.png | US | image | 15.3 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2844 | chrome.exe | 13.107.42.12:443 | 1drv.ms | Microsoft Corporation | US | suspicious |
2844 | chrome.exe | 52.108.24.1:443 | word-view.officeapps.live.com | Microsoft Corporation | US | unknown |
2844 | chrome.exe | 2.18.233.62:443 | c.s-microsoft.com | Akamai International B.V. | — | whitelisted |
2844 | chrome.exe | 40.90.142.226:443 | skyapi.onedrive.live.com | Microsoft Corporation | US | whitelisted |
2844 | chrome.exe | 172.217.168.13:443 | accounts.google.com | Google Inc. | US | whitelisted |
2844 | chrome.exe | 172.217.168.35:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2844 | chrome.exe | 13.107.42.13:443 | onedrive.live.com | Microsoft Corporation | US | malicious |
2844 | chrome.exe | 2.16.186.40:443 | spoprod-a.akamaihd.net | Akamai International B.V. | — | whitelisted |
2844 | chrome.exe | 216.58.215.234:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
2844 | chrome.exe | 198.54.126.78:80 | cpawide.com | Namecheap, Inc. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
1drv.ms |
| shared |
www.gstatic.com |
| whitelisted |
accounts.google.com |
| shared |
onedrive.live.com |
| shared |
safebrowsing.googleapis.com |
| whitelisted |
spoprod-a.akamaihd.net |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
p.sfx.ms |
| whitelisted |
word-view.officeapps.live.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2844 | chrome.exe | Generic Protocol Command Decode | SURICATA Applayer Wrong direction first Data |