| URL: | https://xll3525.z5.web.core.windows.net/?sv=2022-11-02&ss=b&srt=co&se=2024-11-10T12:04:57Z&sp=rwl&sig=oJnmp5lq9Kg+Ntl3naSeRszkWG1zipANSzh0A3020G4=/9HPBF9CT/XZEWYE3G/13KBX5KA/cGFydGhhc2FyYXRoeS5ibHNjbWNvbjE2QGJpb2Nvbi5jb20= |
| Full analysis: | https://app.any.run/tasks/814dd243-a6b6-43e5-931d-fa7ff89a6a81 |
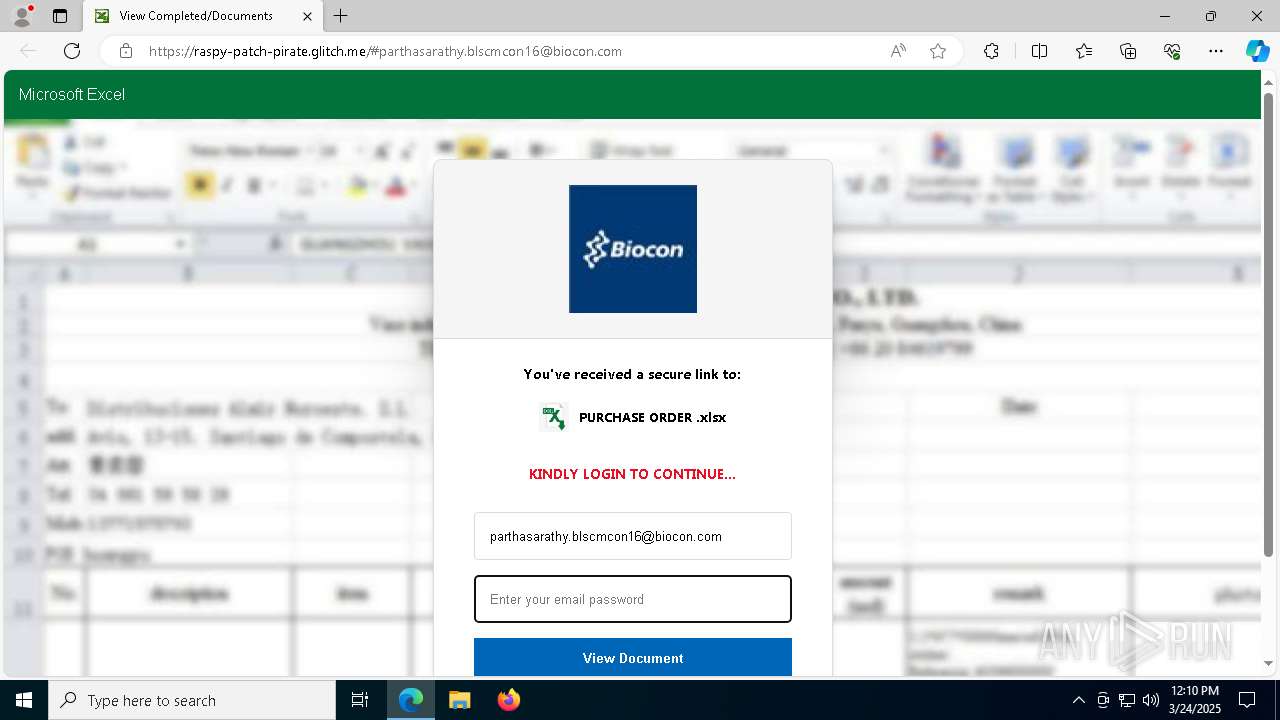
| Verdict: | Malicious activity |
| Analysis date: | March 24, 2025, 12:10:08 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | C626E678AB2D88B249D24FE4D55B2FB3 |
| SHA1: | 8C41D39A2441D7B6B4EBCF2E7093FC77888390F6 |
| SHA256: | CD4F974ED48435DD48876DE1581F9CC2C236F1C3AA9605E13BA48A7B91D79251 |
| SSDEEP: | 6:2bZ5UhhrXVP0MDmKDY0E19VLKc1NZLeGfRaf4Lfecr:2d5Wx0MDmKD0Oc1/aur |
MALICIOUS
PHISHING has been detected (SURICATA)
- msedge.exe (PID: 7440)
SUSPICIOUS
No suspicious indicators.INFO
Checks supported languages
- identity_helper.exe (PID: 8668)
Reads Environment values
- identity_helper.exe (PID: 8668)
Reads the computer name
- identity_helper.exe (PID: 8668)
Creates files or folders in the user directory
- BackgroundTransferHost.exe (PID: 4976)
Reads security settings of Internet Explorer
- BackgroundTransferHost.exe (PID: 6876)
- BackgroundTransferHost.exe (PID: 5260)
- BackgroundTransferHost.exe (PID: 7208)
- BackgroundTransferHost.exe (PID: 4976)
Checks proxy server information
- BackgroundTransferHost.exe (PID: 4976)
Reads the software policy settings
- BackgroundTransferHost.exe (PID: 4976)
- slui.exe (PID: 2516)
Application launched itself
- msedge.exe (PID: 5048)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
180
Monitored processes
45
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1328 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5448 --field-trial-handle=2240,i,13436869338017149074,11168090177426525132,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2516 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2692 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4364 --field-trial-handle=2240,i,13436869338017149074,11168090177426525132,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2904 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5448 --field-trial-handle=2240,i,13436869338017149074,11168090177426525132,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 4424 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=5368 --field-trial-handle=2240,i,13436869338017149074,11168090177426525132,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 4976 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5048 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" "https://xll3525.z5.web.core.windows.net/?sv=2022-11-02&ss=b&srt=co&se=2024-11-10T12:04:57Z&sp=rwl&sig=oJnmp5lq9Kg+Ntl3naSeRszkWG1zipANSzh0A3020G4=/9HPBF9CT/XZEWYE3G/13KBX5KA/cGFydGhhc2FyYXRoeS5ibHNjbWNvbjE2QGJpb2Nvbi5jb20=" | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 5260 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6876 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7208 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
6 365
Read events
6 335
Write events
30
Delete events
0
Modification events
| (PID) Process: | (5048) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (5048) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (5048) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (5048) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (5048) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 856E07C5AB8F2F00 | |||
| (PID) Process: | (5048) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 42E713C5AB8F2F00 | |||
| (PID) Process: | (5048) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328466 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {9E3E4830-9E96-4D9C-82BF-8F91DC1F71A7} | |||
| (PID) Process: | (5048) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328466 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {1C32960F-7183-400D-8042-BD9458B1A02A} | |||
| (PID) Process: | (5048) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 140576C5AB8F2F00 | |||
| (PID) Process: | (5048) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328466 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {674EBCCE-026D-4516-A518-0F990E9F187B} | |||
Executable files
6
Suspicious files
87
Text files
33
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5048 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10beed.TMP | — | |
MD5:— | SHA256:— | |||
| 5048 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10beed.TMP | — | |
MD5:— | SHA256:— | |||
| 5048 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5048 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5048 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10befc.TMP | — | |
MD5:— | SHA256:— | |||
| 5048 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10befc.TMP | — | |
MD5:— | SHA256:— | |||
| 5048 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5048 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5048 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10bf79.TMP | — | |
MD5:— | SHA256:— | |||
| 5048 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
16
TCP/UDP connections
58
DNS requests
71
Threats
22
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.48.23.137:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7964 | backgroundTaskHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
4976 | BackgroundTransferHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
8696 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
1452 | svchost.exe | HEAD | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/d0729495-2185-4a92-a46f-fde358fd775c?P1=1742957041&P2=404&P3=2&P4=FgCPVtPvQXlHyWAyzKXhF2%2f7QU82MEtIY0pUejyoObnPAv8tvp0iN2eWLMc1JRPYPi7nlt%2fe9Mxw%2fbXS6jVTPA%3d%3d | unknown | — | — | whitelisted |
8696 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
1452 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/d0729495-2185-4a92-a46f-fde358fd775c?P1=1742957041&P2=404&P3=2&P4=FgCPVtPvQXlHyWAyzKXhF2%2f7QU82MEtIY0pUejyoObnPAv8tvp0iN2eWLMc1JRPYPi7nlt%2fe9Mxw%2fbXS6jVTPA%3d%3d | unknown | — | — | whitelisted |
1452 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/d0729495-2185-4a92-a46f-fde358fd775c?P1=1742957041&P2=404&P3=2&P4=FgCPVtPvQXlHyWAyzKXhF2%2f7QU82MEtIY0pUejyoObnPAv8tvp0iN2eWLMc1JRPYPi7nlt%2fe9Mxw%2fbXS6jVTPA%3d%3d | unknown | — | — | whitelisted |
1452 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/d0729495-2185-4a92-a46f-fde358fd775c?P1=1742957041&P2=404&P3=2&P4=FgCPVtPvQXlHyWAyzKXhF2%2f7QU82MEtIY0pUejyoObnPAv8tvp0iN2eWLMc1JRPYPi7nlt%2fe9Mxw%2fbXS6jVTPA%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 23.48.23.137:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5048 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7440 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7440 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7440 | msedge.exe | 13.107.253.45:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7440 | msedge.exe | 20.209.187.233:443 | xll3525.z5.web.core.windows.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7440 | msedge.exe | 13.107.6.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
xll3525.z5.web.core.windows.net |
| whitelisted |
business.bing.com |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
www.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7440 | msedge.exe | Misc activity | ET INFO DNS Query to Online Application Hosting Domain (glitch .me) |
7440 | msedge.exe | Misc activity | ET INFO DNS Query to Online Application Hosting Domain (glitch .me) |
7440 | msedge.exe | Misc activity | ET INFO Observed Online Application Hosting Domain (glitch .me in TLS SNI) |
7440 | msedge.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Domain name pattern identified as Phishing (.glitch .me) |
7440 | msedge.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Domain name pattern identified as Phishing (.glitch .me) |
7440 | msedge.exe | Misc activity | ET INFO Observed Online Application Hosting Domain (glitch .me in TLS SNI) |
7440 | msedge.exe | Possible Social Engineering Attempted | ET HUNTING Suspicious Glitch Hosted TLS SNI Request - Possible Phishing Landing |
7440 | msedge.exe | Possible Social Engineering Attempted | ET HUNTING Suspicious Glitch Hosted TLS SNI Request - Possible Phishing Landing |
7440 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
7440 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |