| File name: | osc.exe.bin |
| Full analysis: | https://app.any.run/tasks/3b4b9130-052d-47b5-82b2-ff4eed04ac25 |
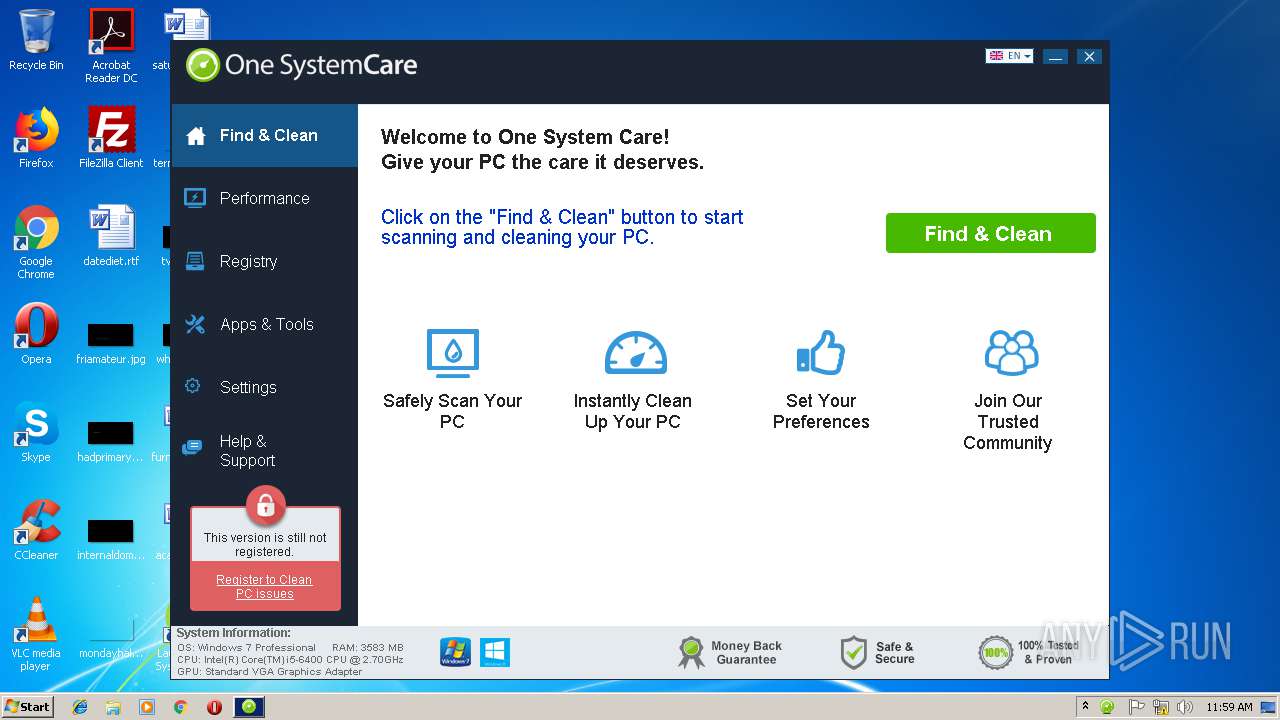
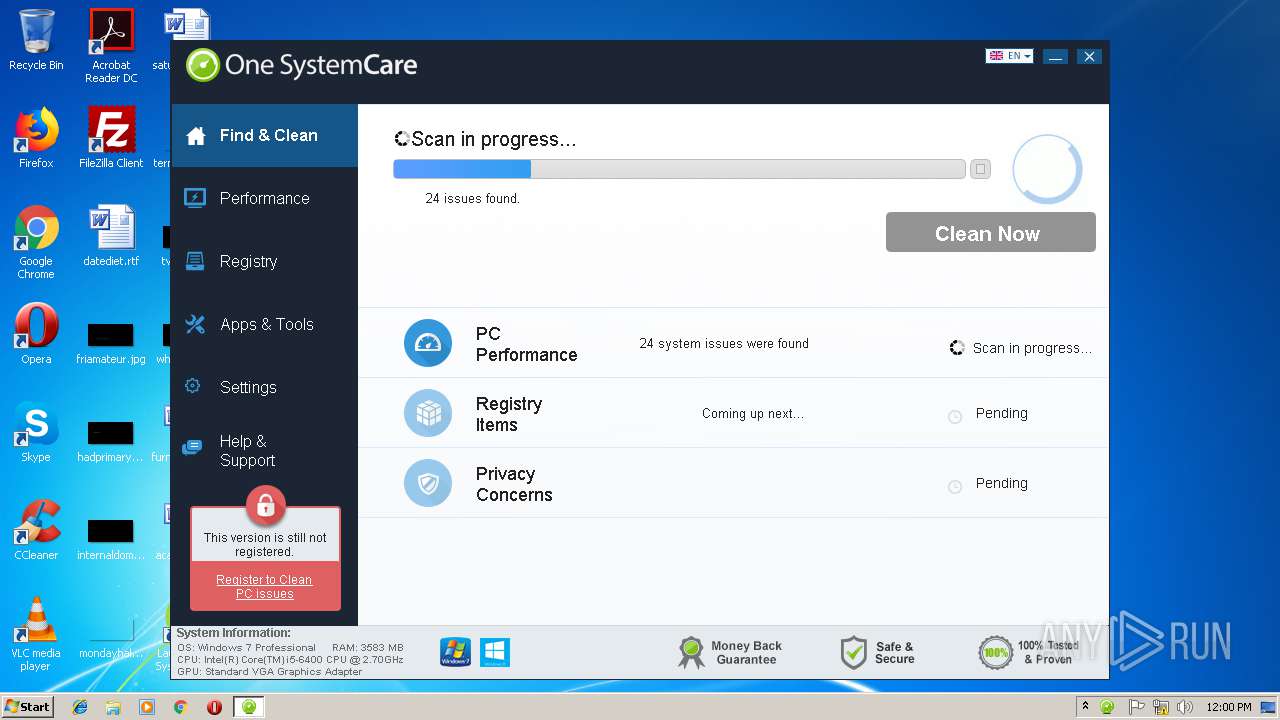
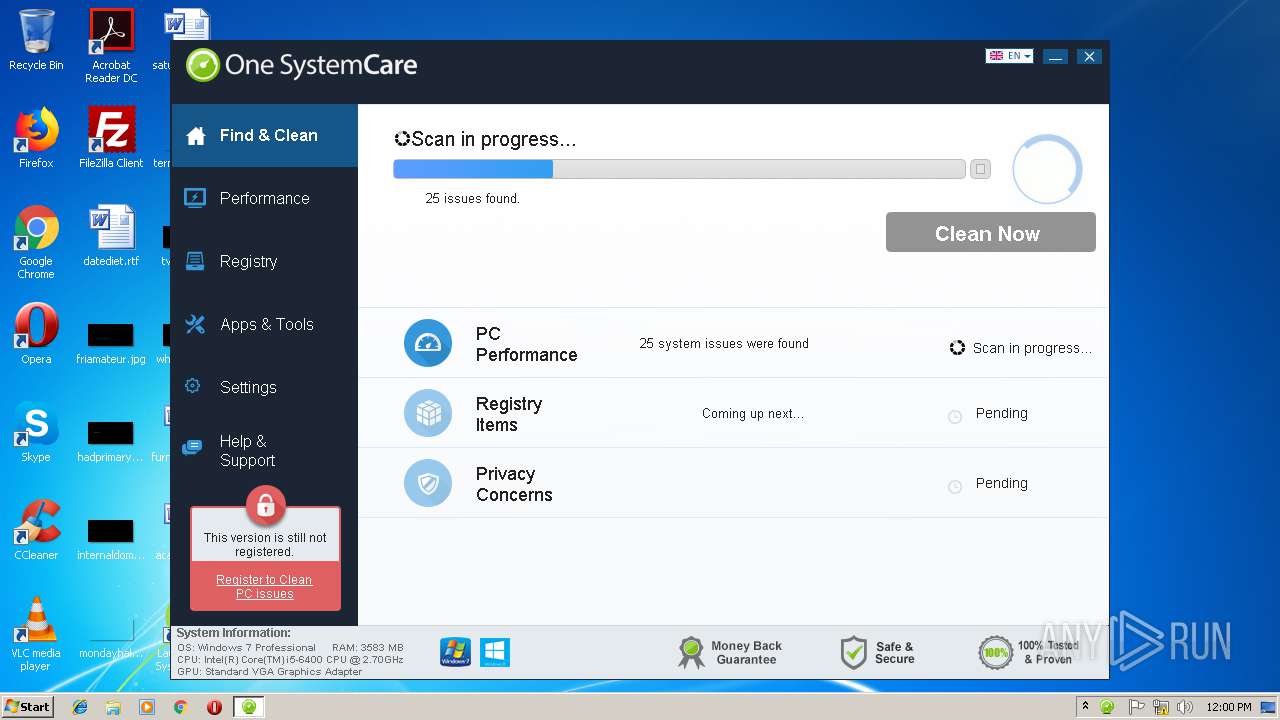
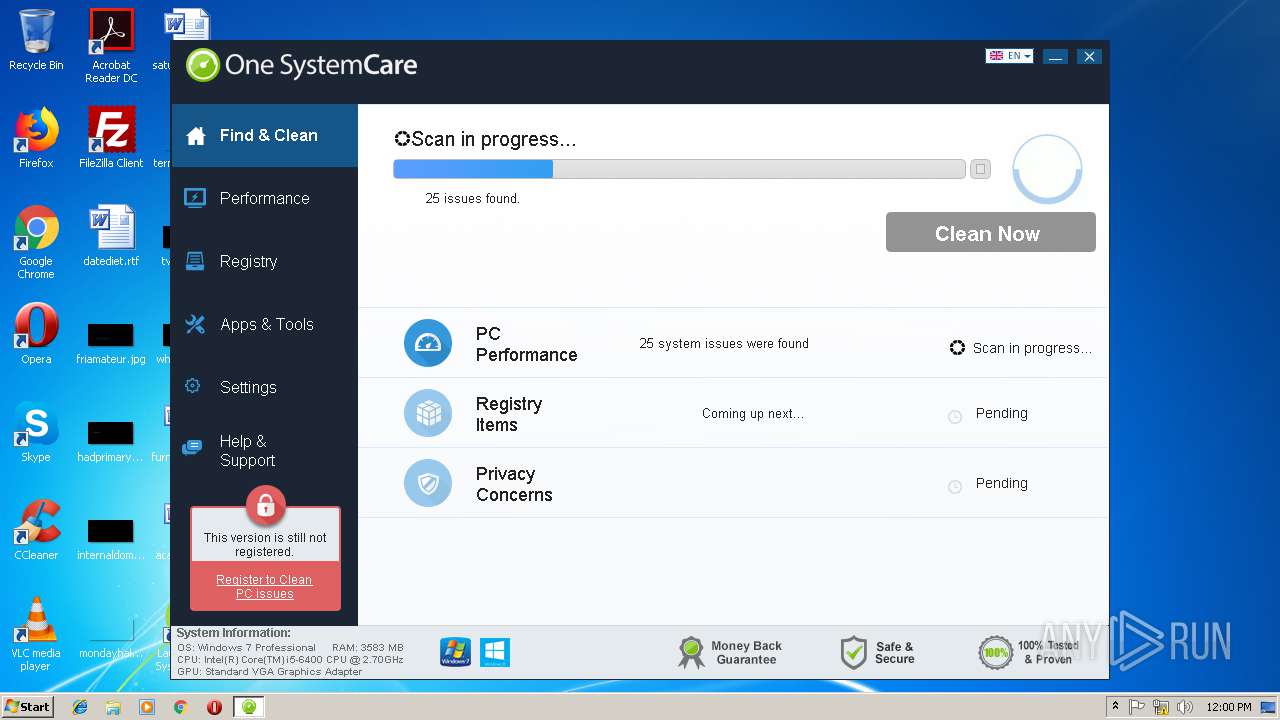
| Verdict: | Malicious activity |
| Analysis date: | March 14, 2019, 11:57:21 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | D14D9FA1DE10211E5A7CB8A32B2FC960 |
| SHA1: | 8489B5E26B42930A27579C7A4E29FCFB560ECCBA |
| SHA256: | CD4AA43403E69D55B34AE91B8847C7404C9738836D73DC4E0D27C8A9EC6F29B5 |
| SSDEEP: | 98304:uKL+1tLnQIzgnhdDM5Z/9CPLhbizxhe4ezJdf5L8lwfIgopkC5JHo4saIDB:7GLnQFnhFM5Z1CKxh1uJdh8qfIgopkOM |
MALICIOUS
Connects to CnC server
- osc.exe.bin.tmp (PID: 3084)
- osc.exe.bin.tmp (PID: 3588)
- OneSystemCare.exe (PID: 1148)
Application was dropped or rewritten from another process
- unins000.exe (PID: 4020)
- _iu14D2N.tmp (PID: 2892)
- OneSystemCare.exe (PID: 2312)
- OneSystemCare.exe (PID: 2336)
- OneSystemCare.exe (PID: 1148)
Loads dropped or rewritten executable
- _iu14D2N.tmp (PID: 2892)
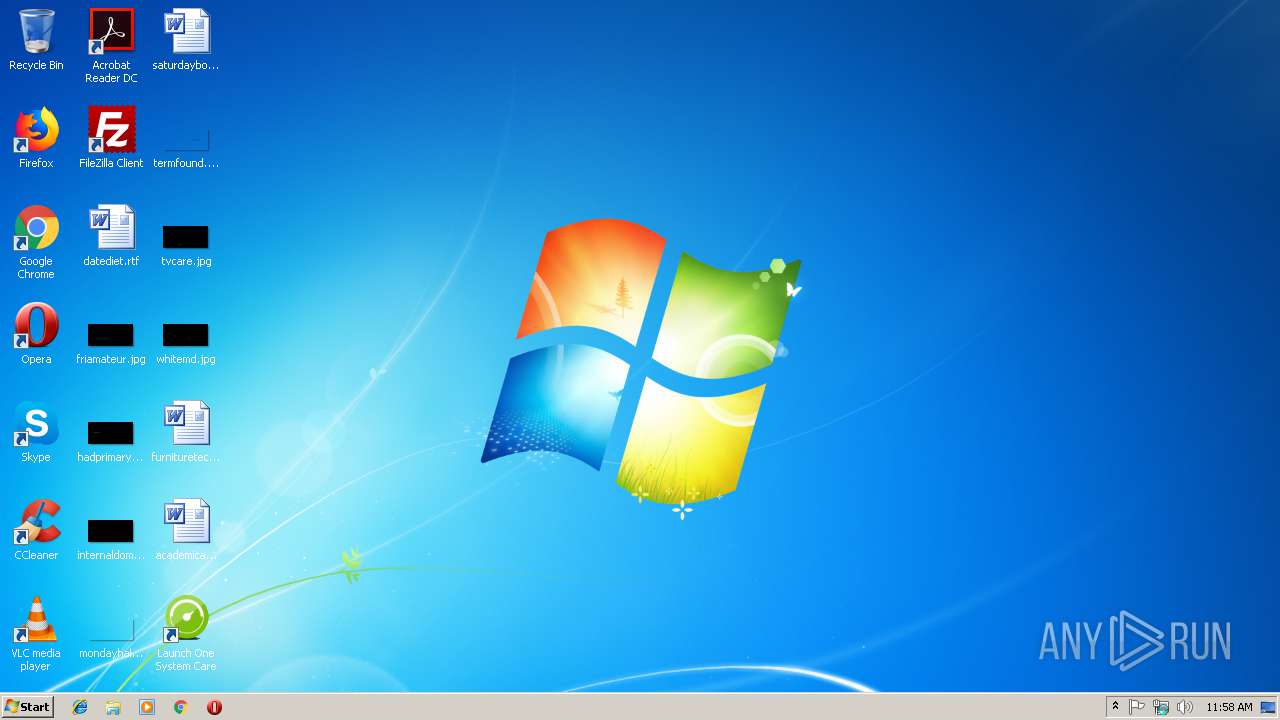
Uses Task Scheduler to run other applications
- osc.exe.bin.tmp (PID: 3588)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 2676)
- schtasks.exe (PID: 2836)
Loads the Task Scheduler DLL interface
- OneSystemCare.exe (PID: 1148)
SUSPICIOUS
Reads the Windows organization settings
- osc.exe.bin.tmp (PID: 3084)
- osc.exe.bin.tmp (PID: 3588)
- _iu14D2N.tmp (PID: 2892)
Executable content was dropped or overwritten
- osc.exe.bin.exe (PID: 3916)
- osc.exe.bin.tmp (PID: 3588)
- osc.exe.bin.exe (PID: 2412)
- osc.exe.bin.tmp (PID: 3084)
- osc.exe.bin.exe (PID: 2988)
- unins000.exe (PID: 4020)
- _iu14D2N.tmp (PID: 2892)
Reads Windows owner or organization settings
- osc.exe.bin.tmp (PID: 3084)
- osc.exe.bin.tmp (PID: 3588)
- _iu14D2N.tmp (PID: 2892)
Creates files in the user directory
- osc.exe.bin.tmp (PID: 3588)
- OneSystemCare.exe (PID: 1148)
Starts application with an unusual extension
- unins000.exe (PID: 4020)
Starts itself from another location
- unins000.exe (PID: 4020)
Creates a software uninstall entry
- _iu14D2N.tmp (PID: 2892)
- OneSystemCare.exe (PID: 2312)
- OneSystemCare.exe (PID: 1148)
Starts CMD.EXE for commands execution
- osc.exe.bin.tmp (PID: 3084)
- osc.exe.bin.tmp (PID: 3588)
Application launched itself
- OneSystemCare.exe (PID: 2336)
Creates files in the Windows directory
- OneSystemCare.exe (PID: 1148)
INFO
Application was dropped or rewritten from another process
- osc.exe.bin.tmp (PID: 3084)
- osc.exe.bin.tmp (PID: 3588)
- osc.exe.bin.tmp (PID: 2784)
Loads dropped or rewritten executable
- osc.exe.bin.tmp (PID: 3084)
- osc.exe.bin.tmp (PID: 3588)
Creates files in the program directory
- osc.exe.bin.tmp (PID: 3588)
Dropped object may contain Bitcoin addresses
- osc.exe.bin.tmp (PID: 3588)
Creates a software uninstall entry
- osc.exe.bin.tmp (PID: 3588)
- osc.exe.bin.tmp (PID: 3084)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Delphi generic (57.2) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (18.2) |
| .exe | | | Win16/32 Executable Delphi generic (8.3) |
| .exe | | | Generic Win/DOS Executable (8) |
| .exe | | | DOS Executable Generic (8) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:04:06 16:39:04+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 66560 |
| InitializedDataSize: | 83456 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x117dc |
| OSVersion: | 5 |
| ImageVersion: | 6 |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | |
| FileDescription: | |
| FileVersion: | |
| LegalCopyright: | |
| ProductName: | |
| ProductVersion: |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 06-Apr-2016 14:39:04 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | - |
| FileDescription: | - |
| FileVersion: | - |
| LegalCopyright: | - |
| ProductName: | - |
| ProductVersion: | - |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 06-Apr-2016 14:39:04 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000F244 | 0x0000F400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.37521 |
.itext | 0x00011000 | 0x00000F64 | 0x00001000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.7322 |
.data | 0x00012000 | 0x00000C88 | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.29672 |
.bss | 0x00013000 | 0x000056BC | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00019000 | 0x00000E04 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.59781 |
.tls | 0x0001A000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x0001B000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.204488 |
.rsrc | 0x0001C000 | 0x00012500 | 0x00012600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.02502 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.13965 | 1580 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 5.40403 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 5.43363 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 5.18684 | 16936 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 5.83518 | 2440 | Latin 1 / Western European | English - United States | RT_ICON |
4091 | 2.56031 | 104 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4092 | 3.25287 | 212 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4093 | 3.26919 | 164 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4094 | 3.33268 | 684 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4095 | 3.34579 | 844 | Latin 1 / Western European | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
oleaut32.dll |
user32.dll |
Total processes
67
Monitored processes
25
Malicious processes
8
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1148 | "C:\Program Files\OneSystemCare\OneSystemCare.exe" | C:\Program Files\OneSystemCare\OneSystemCare.exe | OneSystemCare.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2120 | cmd /c for /l %x in (1, 1, 2) do del /Q "C:\Users\admin\AppData\Local\Temp\osc.exe.bin.exe" & timeout /t 5 | C:\Windows\system32\cmd.exe | — | osc.exe.bin.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2312 | "C:\Program Files\OneSystemCare\OneSystemCare.exe" /sn=bG6DK1vhwsW5eknSD8w7TUZVIYmnDzDhmqpAQu1vCQer8q_IqqNzACytZCaNyZDR1tAiM496z7eGT__zZiLcXh5rNHg-qE-JeWjGCA3z2xHP21k7pGBPE60hOOKVp9iBvDNzSHnzmbLRlpo_HJ4KYwMrjQlAa409WcIxRcJAGF_V5Kfo4G3A3Fiyj1YwGZpRn82MhcurZeIiEeT1Jscs2JZYQO1sv_afykfY62BxrsXVQ2VKDVv4jDrTnJvZb1ppnBeN079dvruoSDFl6oMEhwFr4AfjI_qBPmO0CexYUA8qTNN4J-5LF_zaxl-JJU9mEWPOEThgRShf25lhGHY8YFe7KzfMGxw5LysxzIeNFC6fOfSENUuuB8C1COvNEbLrQit5sh1W2YFpZdgGIcupDoqU24GGwMRoMJ-qUR0H0dfXn66k4EuFmO0iVakqBL21J18Xl-rRghzipzAgJJsxhCHvx1bi4q923eNtx3fD8ppB-qSPtMm2H4Bdo5TP0wjDDU1uXhsUu53jETiiShnn1tyvael7j5PQhBUex1wV73EtHKxZIE0E5pJZ3D2amQfxIwzQ6Kiy3JJAHQCNHOzyaXtwv5JmUurTWS0q9H_luGonEmqy | C:\Program Files\OneSystemCare\OneSystemCare.exe | — | osc.exe.bin.tmp | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2336 | "C:\Program Files\OneSystemCare\OneSystemCare.exe" | C:\Program Files\OneSystemCare\OneSystemCare.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
| 2412 | "C:\Users\admin\AppData\Local\Temp\osc.exe.bin.exe" /SPAWNWND=$20118 /NOTIFYWND=$2011C | C:\Users\admin\AppData\Local\Temp\osc.exe.bin.exe | osc.exe.bin.tmp | ||||||||||||
User: admin Company: Integrity Level: HIGH Description: Exit code: 1000 Version: Modules
| |||||||||||||||
| 2512 | timeout /t 5 | C:\Windows\system32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: timeout - pauses command processing Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2636 | cmd /c for /l %x in (1, 1, 2) do del /Q "C:\Users\admin\AppData\Local\Temp\osc.exe.bin.exe" & timeout /t 5 | C:\Windows\system32\cmd.exe | — | osc.exe.bin.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2676 | "C:\Windows\System32\schtasks.exe" /Create /TR "'C:\Program Files\OneSystemCare\OneSystemCare.exe' --scan" /sc ONCE /st 12:03 /sd 03/14/2019 /TN "One System Care Delayed" /F /RL HIGHEST | C:\Windows\System32\schtasks.exe | — | osc.exe.bin.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2684 | timeout /t 5 | C:\Windows\system32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: timeout - pauses command processing Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2708 | cmd /c for /l %x in (1, 1, 2) do rmdir /S /Q "C:\Users\admin\AppData\Local\Temp\is-MUCC4.tmp" & timeout /t 5 | C:\Windows\system32\cmd.exe | — | osc.exe.bin.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
1 562
Read events
1 446
Write events
104
Delete events
12
Modification events
| (PID) Process: | (3084) osc.exe.bin.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: 0C0C0000C00B42205DDAD401 | |||
| (PID) Process: | (3084) osc.exe.bin.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: EF78FBF029C6ABECFCC2F3EFD96EF7D3F1C9AD89C520E8FF0563C21D730ADF7D | |||
| (PID) Process: | (3084) osc.exe.bin.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (3084) osc.exe.bin.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{764DADE4-0F9B-A755-FFFD-7B71A9FBF8E8} |
| Operation: | write | Name: | cd77f991 |
Value: 019FF8E97F05000100000040000000400000004111438D19C203FD61238EB58C1C52DDF5486AE09484AF01F049EC75558E6447E9DF8FD2703A900413487225CB3ACF599E0E0E2442071A5ED079975AD37864609D913436BB40A3D28C5128A07E0C02F7 | |||
| (PID) Process: | (3588) osc.exe.bin.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0001 |
| Operation: | write | Name: | Owner |
Value: 040E0000502D6B225DDAD401 | |||
| (PID) Process: | (3588) osc.exe.bin.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0001 |
| Operation: | write | Name: | SessionHash |
Value: 2025FC4BB897032082C80D4EAD8F01A8782BF68227A047117755986FC58F28A4 | |||
| (PID) Process: | (3588) osc.exe.bin.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0001 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (3084) osc.exe.bin.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{764DADE4-0F9B-A755-FFFD-7B71A9FBF8E8} |
| Operation: | write | Name: | cd77f991 |
Value: 018B500BA60500010000004000000040000000DEA99E53EB3611C57B707011EECEA397E47E21FFA568DB47161545D2E90E7AA691879A4D653537DC02AFE7FECC4D03EB18D611EFF5950E27F33EF429151193503D93A17F7E1ACC714AF2E2140FA83A62 | |||
| (PID) Process: | (3084) osc.exe.bin.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{764DADE4-0F9B-A755-FFFD-7B71A9FBF8E8} |
| Operation: | write | Name: | 7e34172e |
Value: 01A745CE4D0500010000001C0000001C00000037585A12A259AC69D3A4AC7089D796343E2821C035FF52D3149B3B9709C3FACB2291A684970FFEF0964C3164 | |||
| (PID) Process: | (3084) osc.exe.bin.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{2C332E1D-92EE-193A-D785-47D53FBD1B51} |
| Operation: | write | Name: | cd77f991 |
Value: 019BC20A5A050001000000400000004000000083724CBE96CCEC17A8E62272DA5A1A21344263158F7F04261474B4351BE010B97044AAD1300034EA001B9E343F4CA67964E3E4F0D8BC9FC1DF679C181CE0AA48244A42CA277D61BEADA08BBA08651CD6 | |||
Executable files
13
Suspicious files
1
Text files
16
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3588 | osc.exe.bin.tmp | C:\Program Files\OneSystemCare\is-MSJN1.tmp | — | |
MD5:— | SHA256:— | |||
| 3588 | osc.exe.bin.tmp | C:\Program Files\OneSystemCare\is-0H3VS.tmp | — | |
MD5:— | SHA256:— | |||
| 3588 | osc.exe.bin.tmp | C:\Program Files\OneSystemCare\is-44N79.tmp | — | |
MD5:— | SHA256:— | |||
| 3588 | osc.exe.bin.tmp | C:\Program Files\OneSystemCare\is-8B8KI.tmp | — | |
MD5:— | SHA256:— | |||
| 3588 | osc.exe.bin.tmp | C:\Users\admin\AppData\Roaming\One System Care\Languages\is-LIU07.tmp | — | |
MD5:— | SHA256:— | |||
| 3588 | osc.exe.bin.tmp | C:\Users\admin\AppData\Roaming\One System Care\Languages\is-CD88P.tmp | — | |
MD5:— | SHA256:— | |||
| 3588 | osc.exe.bin.tmp | C:\Users\admin\AppData\Roaming\One System Care\Languages\is-NB0QR.tmp | — | |
MD5:— | SHA256:— | |||
| 3588 | osc.exe.bin.tmp | C:\Users\admin\AppData\Roaming\One System Care\Languages\is-AHTPC.tmp | — | |
MD5:— | SHA256:— | |||
| 3588 | osc.exe.bin.tmp | C:\Users\admin\AppData\Roaming\One System Care\Languages\is-3R17B.tmp | — | |
MD5:— | SHA256:— | |||
| 3588 | osc.exe.bin.tmp | C:\Users\admin\AppData\Roaming\One System Care\Languages\is-S6NNF.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
9
DNS requests
8
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | HEAD | 503 | 81.171.17.144:80 | http://areasons.info/?ch=sQQV5K9n9lFkcA0Q-KWdDB5B6W9YUXwWhQbUIB7nN3vHV_dnZsAn_PaLu7KnzJRobu7uFxr-H4FKJ0Wcf-LeBf95XixQ_nTkh7mimKqi5KV6B7A-lb8M3NJZu7Kn7CIqKOn3goXsmZ_L&ac=StPAahsWcy4XtV7vHHcfPfyYgiohk6o1yeJbh6qCU-3NZJtCEWcRqHWX_GnhFybmeTA-RlvOrYRddK4obV2E71DtkiaXOQzE6aseh6Cb47xObU3FFLHmtH1auEghT9iu1c09U9_H4Lnk0uBrshLc8nCz37wxBexx6KRCXtnV46Fw8YUPZ3LjaqIglTHPpFgx_n5hdCc1rIfHAJ5pI0W8lVt4o4gRPo-z0pcIVjcqmo5ZxhZH6G8chci4SJjcI7NYwaefZxRxK3oSu04LNI17sPnL_DvBsp9MC-ZQENQEGo_7gmZdEoV_zjeebNCKVlGGYe1kFqcbr6SAOpDF6HPAJO83oL4zUaK5cNIUgJ17IcQRpEoO3qBSdoHKa4zmaVDKa7u778olu2hMeyx-bgJYVuh2E4Xv-MfHdHph7vojVKwRp3U6nXen_MDWQ172SAOiPOeIGKel2GyvjMUmYx5TKomoCwW8ylkvxSczgbaXKsingP3TEzZNOHb5KEAHuNXH467tMMSW-jT6amMRjno8XuBN69eiX7grSl8Wcy35eYk9mwgCdX5FXRqv4uxKpA5ryrvajSvV77miHf0GQGH9Y0ZTSIwyxJwtpMR4_02g5_dxvipyu9cBwoEQInpMKmj3DCF1_jY3_E2o1zz6qR9xL1BLFxbiTTo9WVlxdGkHoVKEPPnX3We5CLl2izPIi7t1brnvThXdf26zHExWfYiZPMtF812cJGMblvA0O5M4LS4Nwn5441HIhBjuA1SUkFimJSyV0hn7RNS1QQuLImD2P9g4lqFpo8UVvhdH9Ia1DbK4Leod7QbS9r7AYzVA92nhWBM2GHr_E3mhjOsUgiDNdPVVkG-BTTn4_GgEU6rZBvILBMqVleTSaYWOM2YRuRkun3qc-JPQePg9RPxdmDWLtaaKwN5kBlhEP5CURfsGgJIkcDPMGRnVDaDrSQzlqt6l_j310JnpO56GafvHdhU4vKTz3KMyzB5GW2yOQEpVqb7OfW063qVD7ui5uwXLEz5UpgaDwtDPpcfdHZhoteH1QFq7iJcHKR9n3q0Cpm1SSYgCQngRUCixf-IvFajl622GCdSGqb-AJO2hoPjTtXtnE2uA9ttzfBeR57WcYCLcm5fr&tr=sDOBxOtnnRlkffje4QomsRfNBFzKrzlObZrrNn5t3Gg-DL09Lq5l977_S313t7F-wN3ZL3YOBzm4CEQFrfXlFPPrrKnoPRldD9oKGkBXrO4ewSlJ47SYwIu_2k0DHNiOOqD4CNuKBx68FoamJz66htYw-IVXf14ZTohPkFgHLiwzkBsymtCTPmZkT151SfOOe-Cmy-RKrhI010SGervJudih-cyvx6D5j50wGW746kQcMmjtZRbsAlYpnytNL1OjpW3qt6S7XjWY_xO_yQlgddkxPBtvZVN8aFDG9JUKmC17YmpBE8EiQZ9D6iQ5-j0vlvcBLSiTPG18XnKTmZ_L | NL | — | — | malicious |
1148 | OneSystemCare.exe | GET | 200 | 104.31.4.172:80 | http://callbanner.onesystemcare.com/?type=43 | US | — | — | shared |
1148 | OneSystemCare.exe | GET | 200 | 104.31.4.172:80 | http://callbanner.onesystemcare.com/?type=44 | US | — | — | shared |
3588 | osc.exe.bin.tmp | POST | 200 | 104.31.92.189:80 | http://inf1.onesystemhost.info/ | US | text | 20 b | malicious |
1148 | OneSystemCare.exe | POST | 200 | 104.31.93.189:80 | http://act1.onesystemhost.info/ | US | text | 84 b | malicious |
3588 | osc.exe.bin.tmp | POST | 200 | 104.31.92.189:80 | http://ins1.onesystemhost.info/ | US | text | 84 b | malicious |
3084 | osc.exe.bin.tmp | POST | 200 | 104.31.92.189:80 | http://tm1.onesystemhost.info/ | US | text | 148 b | malicious |
3588 | osc.exe.bin.tmp | POST | 200 | 104.31.92.189:80 | http://tm1.onesystemhost.info/ | US | text | 152 b | malicious |
— | — | HEAD | 503 | 81.171.17.144:80 | http://credicalls.info/?ch=oyBXnDLFm1pI_L0YIJ_5mC65YsU5rnCQh8nJ535cAqLm1i_lNtUn2FzMXnRtS3kRx7pG7tAP5D07bSob4I1xN36KNBRWdQvraDYMEyfdSsoBeZgqBEuzPLVIK9JOB9Gsdx5HKhAxeNrn&ac=E96YRresO_rWfbA_hjHKDLFQ6veEZK1_Q3Sa9Tn_e0hXL12ouGkiTO0FYvI6HeSqOF2ux066ATOm2Oj355mhvQWZkpjQcQYJN4Xp9NCGM1ecr6ct8G8RJJZ9LB64zbcJ-R_R-rfoh2XWyByrJfZpbQcTQJBKW3NG8AfzR4MIqk8llr8Sc0wGJIwDQKSgZPSN_0Dp_vbWkaL-53isUGJQii-7nCEgUZEnv4j3EDbFWmReElSkUz1FYUD-pfSOow-EJys_fWQ3uHsEv7c80x3MllHSUxq6pJe6aVdgkQpgzP9DEzvjOM8-L0EXJewtnvvR41_CZz8UiXJrIoJUp80g6gXvDfEyzXD3AV3byJPe2s6yNLGJ8-EcwhL7Gb1fnvHBT3QXSSPNP-DlnDGoO_gj9b5nup9hTvXLuzWUEHLmQUq54fEJkzWm5AgnNwCGxeLItXjE2BpRKHUcfZlGyOKOiaizBgKGLmBR0Ic1KCx2ncXEZOiFu13AF8uXZhC1mnoLHHgzE0eEQYgD_mGry1ogW1w-yU9_jZKe44diKRbvHfd_MgdVAXser3M4mAXxC0pavPrdEkxsgz8IpQWET-4Q508Vsfz6cSwwFuC18CI3HsNyk_KnV8YzBl-RgmhegsCB_Pwe-jwThQvhNHyYjLBeevcJn7x_1GvR-Bv1PZZ40fdSiej145YMcrQeHrzrr7WOnKrOc0itiG-KDlorLPQvjD5ydnQRG0k17Wv1acxK2u0unWFOpPlMp8iPdcNqe4gTMUQ-D0loXR_eyay6pzSu1ogkzk3dwruTMxtuLp1jM6HSYK7_nP7xox6ByMzlv7Z-hP9pLrCcmH0FEwDukmg4nLUqnwWhCARM6Vau7etM1RDLSEhwpZ9h0aRUVq7WVoUsbhtIc-KTJhVo53LJ7H7wEUMXOfVCMfrHG6GbEemDVVvNlU2_NqDCFuXl3ACNSRGQuL-bAjK58l7PhHfCuXh7JoUEqF_EE0D2j0wcfFQZpd93rIhI2K8v3LWrCEq7o-508AIvTG1oAmj31OMEghYLe0CgU96GwNJZgMkFCZ-raCREdKJqDpwv32HyUEKinMsuUrYTlGFfx7x87gu7x1Hai2cJ0RoCNs2XFZJQddgPKPZt&tr=HNR2CKIdImTecJ6ppLue47tZW_5loY4Ykn1okMIFthgdHTZvypq6zhvVwdkbd5b9W0gESrP4e91dch1RXCr6qz_FnMFf684-0J54It3dYM2rrO0oL-9xDC1pC2Y0yYNyocPE2S0vyoV2ckyKrGA7iW-jixwApsuIldSZoAUWGv5UJVLjQR-7Y6QpmNzMbKjGo4Hw_8tKvZ9G94WlNJ7iw-jnt7RaQu1YoJOESH3M5siyDAaiHIvJvWHeZR5eg1wVRc0y62aPbEDsnbNwsxytbyUw_hMTHw8Ygot_6fN_rmX3u-b3Ka031RLtXD0xGpR0G7MX8Vh595M37gFrQYoI | NL | — | — | malicious |
3588 | osc.exe.bin.tmp | POST | 200 | 104.31.93.189:80 | http://ins2.onesystemhost.info/ | US | text | 84 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3084 | osc.exe.bin.tmp | 104.31.92.189:80 | tm1.onesystemhost.info | Cloudflare Inc | US | shared |
3588 | osc.exe.bin.tmp | 104.31.93.189:80 | tm1.onesystemhost.info | Cloudflare Inc | US | shared |
3588 | osc.exe.bin.tmp | 104.31.92.189:80 | tm1.onesystemhost.info | Cloudflare Inc | US | shared |
— | — | 81.171.17.144:80 | credicalls.info | LeaseWeb Netherlands B.V. | NL | malicious |
1148 | OneSystemCare.exe | 104.31.4.172:80 | callbanner.onesystemcare.com | Cloudflare Inc | US | shared |
1148 | OneSystemCare.exe | 104.31.93.189:80 | tm1.onesystemhost.info | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
tm1.onesystemhost.info |
| malicious |
ins1.onesystemhost.info |
| malicious |
ins2.onesystemhost.info |
| malicious |
credicalls.info |
| unknown |
areasons.info |
| unknown |
inf1.onesystemhost.info |
| malicious |
act1.onesystemhost.info |
| malicious |
callbanner.onesystemcare.com |
| unknown |
Threats
6 ETPRO signatures available at the full report