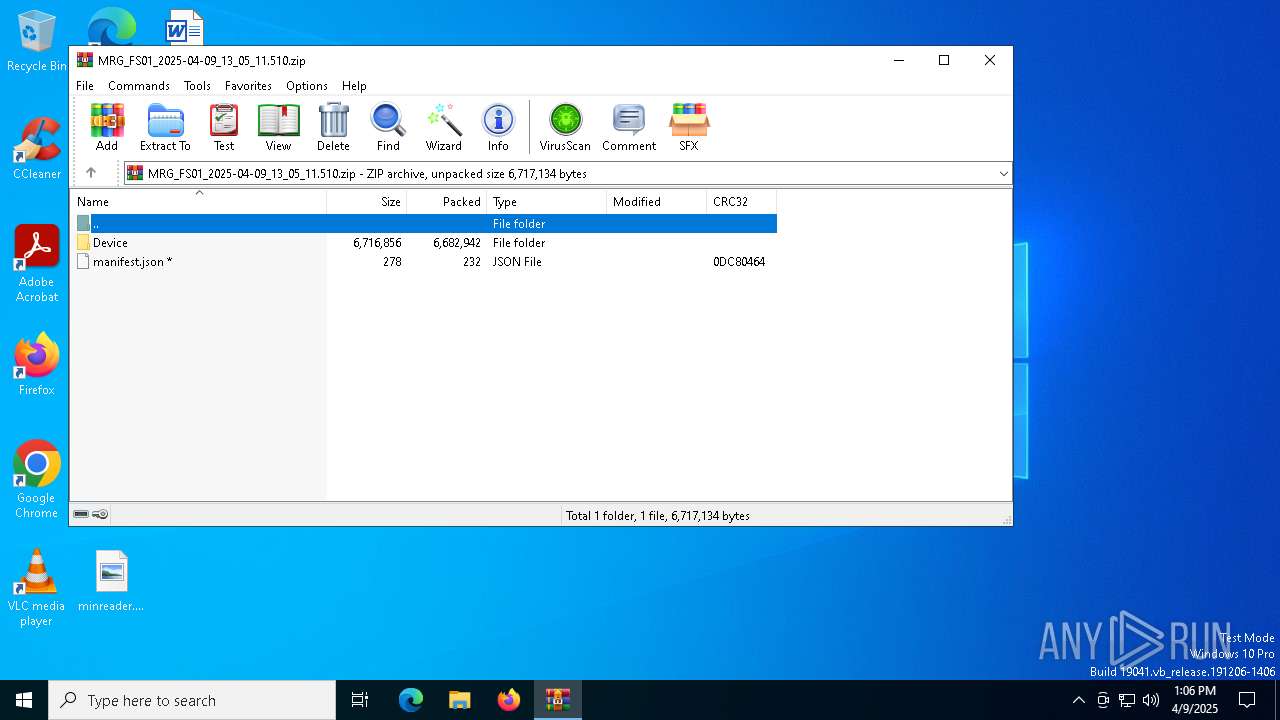
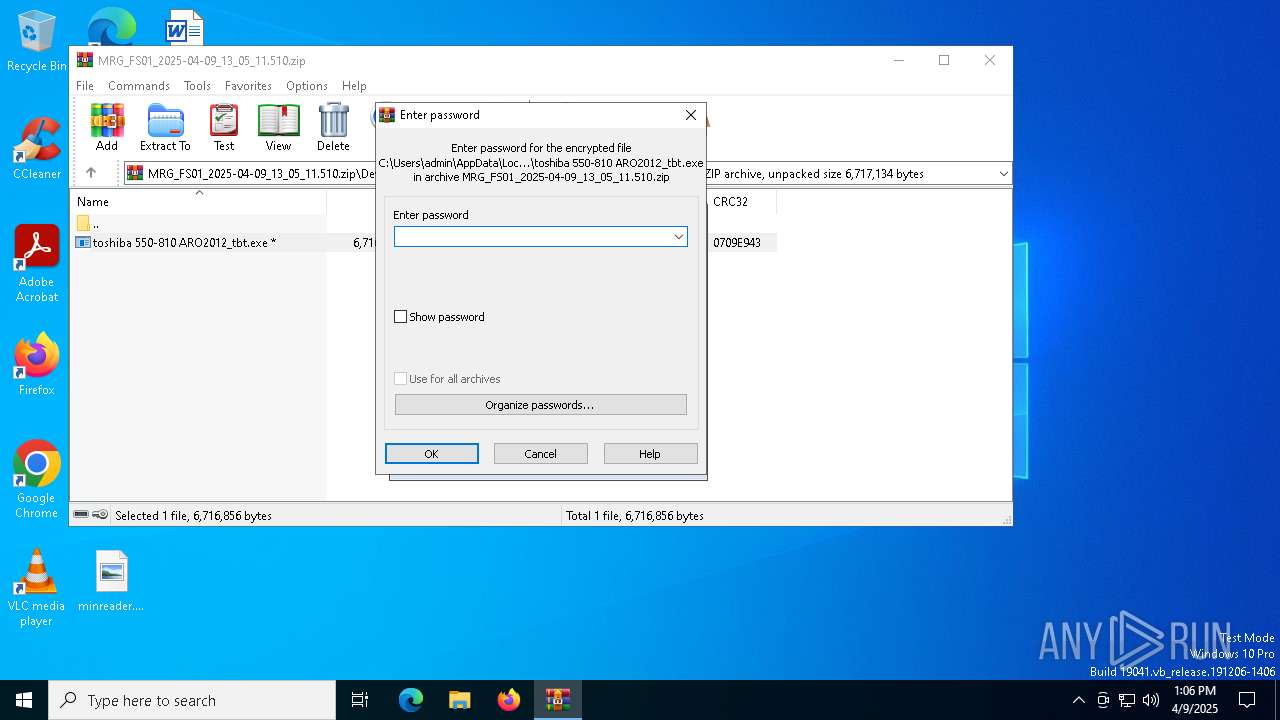
| File name: | MRG_FS01_2025-04-09_13_05_11.510.zip |
| Full analysis: | https://app.any.run/tasks/15a98f7d-2878-4212-824d-31dc876cf689 |
| Verdict: | Malicious activity |
| Threats: | Stealers are a group of malicious software that are intended for gaining unauthorized access to users’ information and transferring it to the attacker. The stealer malware category includes various types of programs that focus on their particular kind of data, including files, passwords, and cryptocurrency. Stealers are capable of spying on their targets by recording their keystrokes and taking screenshots. This type of malware is primarily distributed as part of phishing campaigns. |
| Analysis date: | April 09, 2025, 13:05:51 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
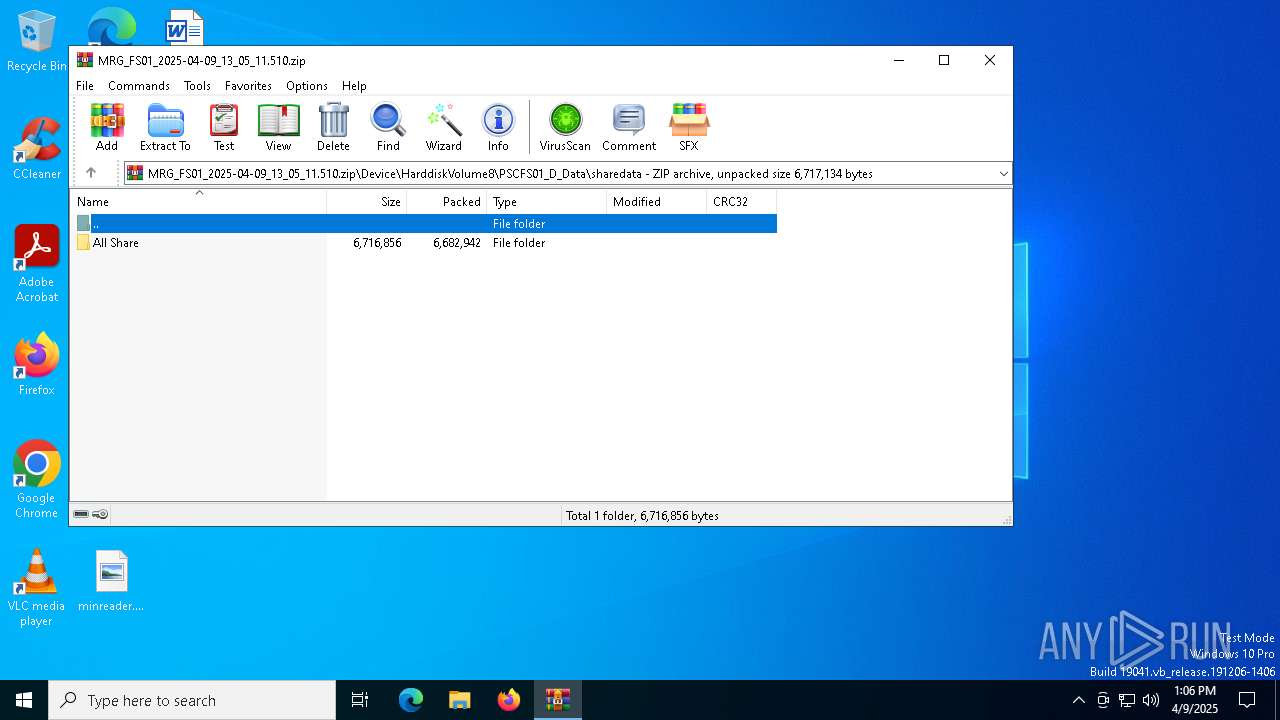
| MIME: | application/zip |
| File info: | Zip archive data, at least v4.5 to extract, compression method=deflate |
| MD5: | 7F5EC584CBA5968043407D52E1BC9048 |
| SHA1: | 7C2191F2CD25DE47D542C611BF9012DDBA236B70 |
| SHA256: | CD48082AA0578FFBF9EE147C632FD04D1A283C6E98162F427E15F14F3B76E784 |
| SSDEEP: | 98304:khdZDP/idzHMVNjRrX9pR8yA91zyymIVK5CchQLIQxP3hwgHeAFV40tlE47Netgh:4PL0Y+7MfBLPU |
MALICIOUS
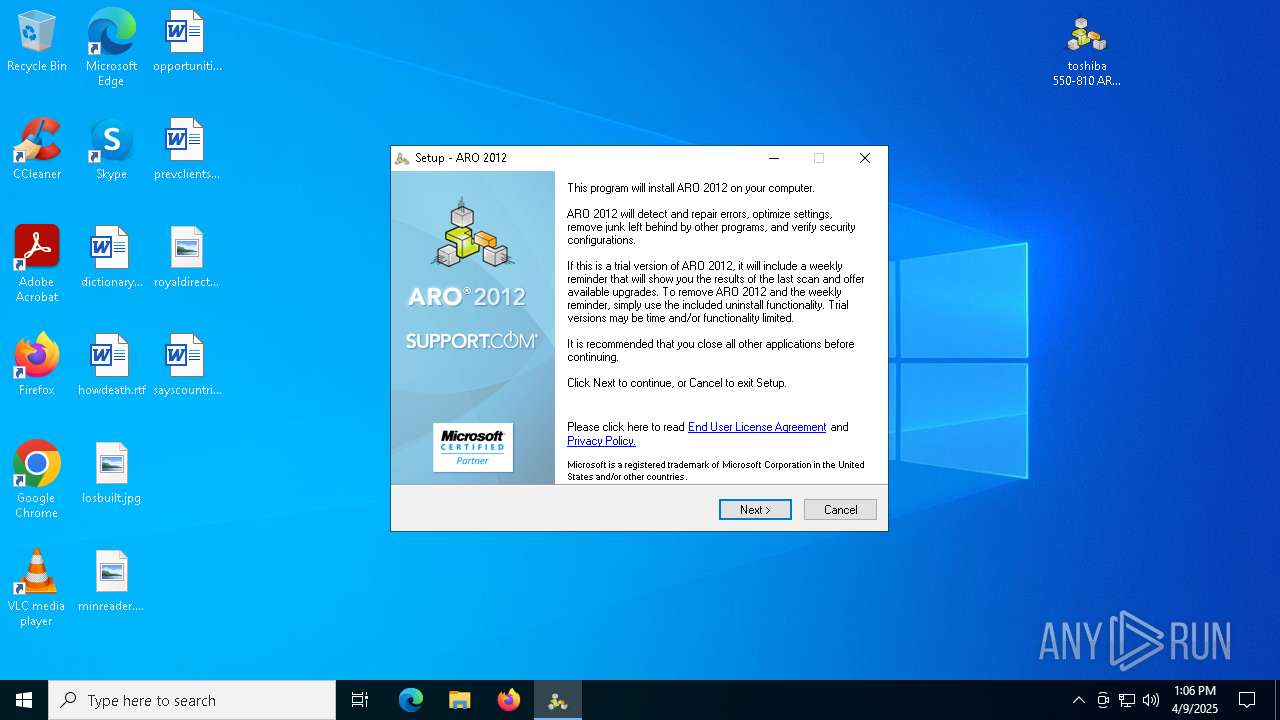
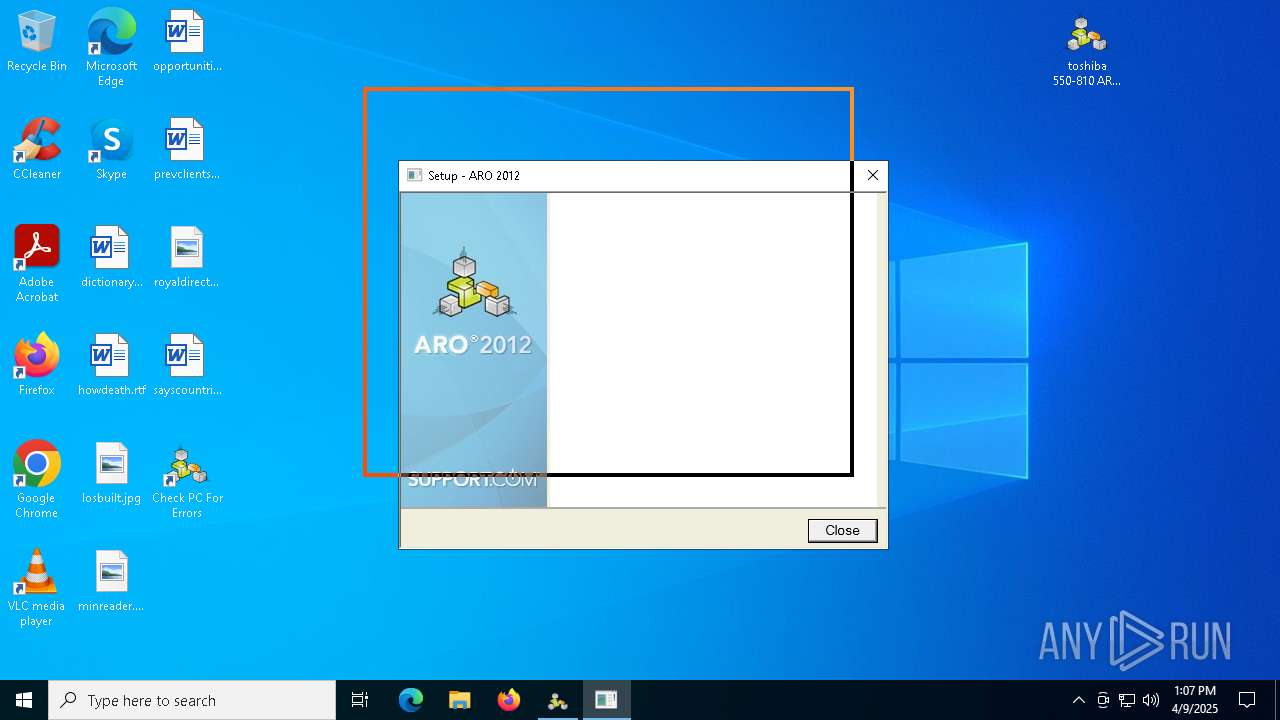
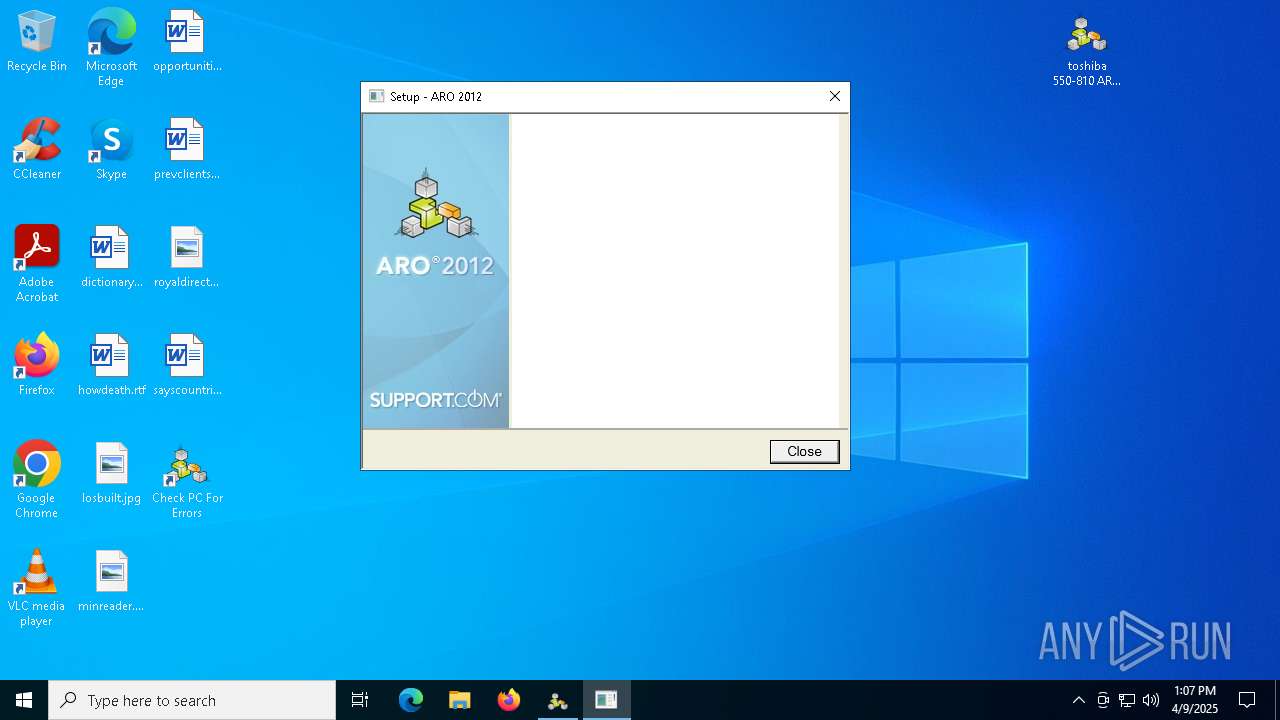
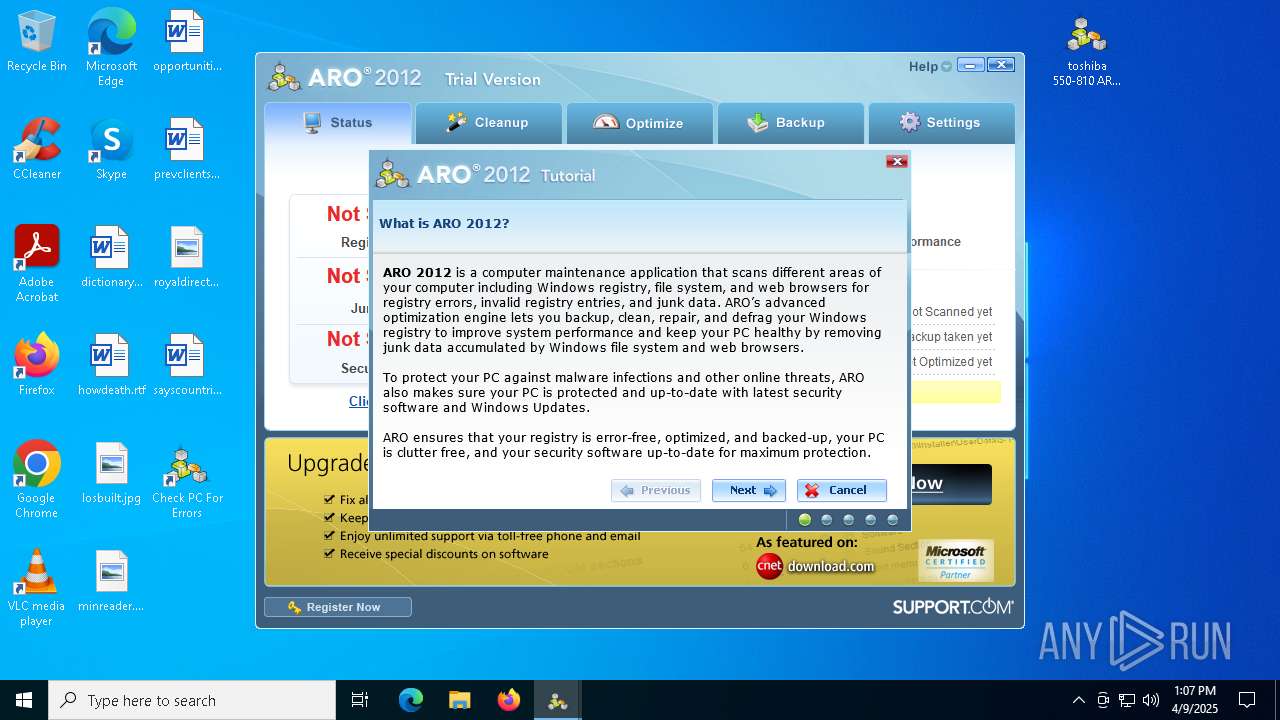
Executing a file with an untrusted certificate
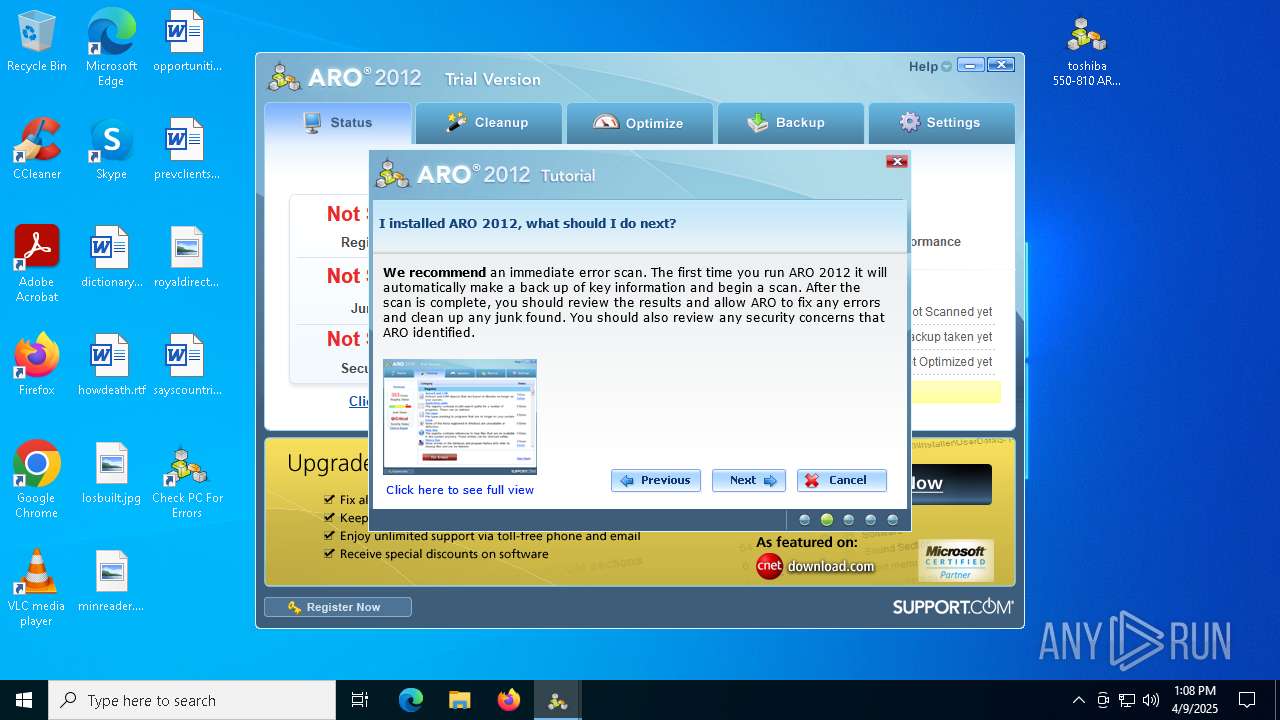
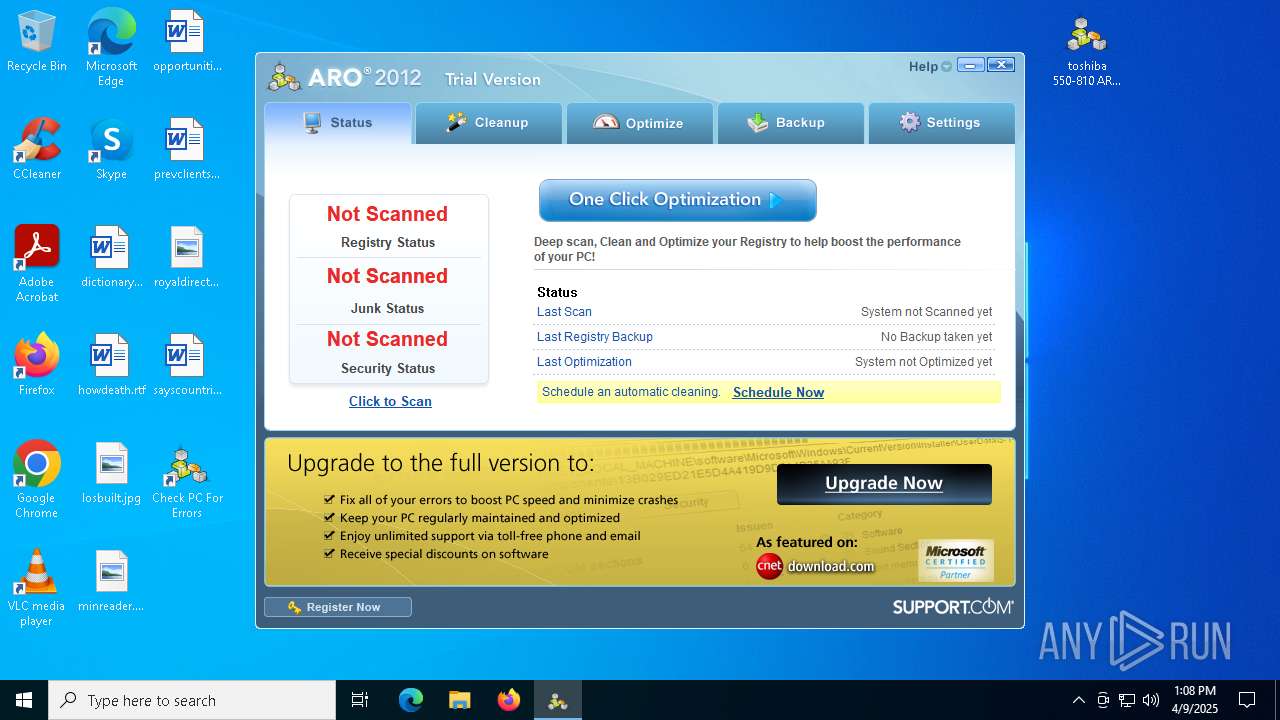
- toshiba 550-810 ARO2012_tbt.exe (PID: 864)
- toshiba 550-810 ARO2012_tbt.exe (PID: 1228)
- ApnStub.exe (PID: 3180)
- ApnStub.exe (PID: 7660)
- ApnToolbarInstaller.exe (PID: 7864)
- NEWF7AB.tmp.exe (PID: 7820)
- AskPartnerCobrandingTool.exe (PID: 736)
- TaskScheduler.exe (PID: 8080)
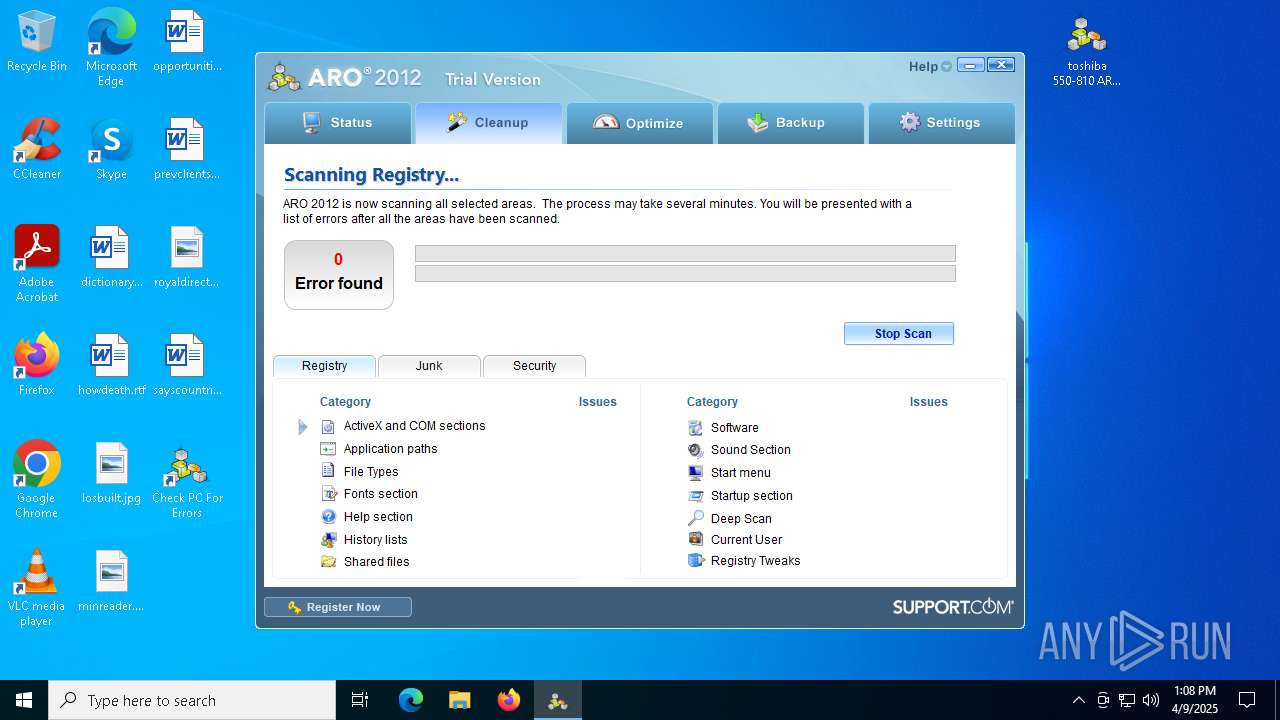
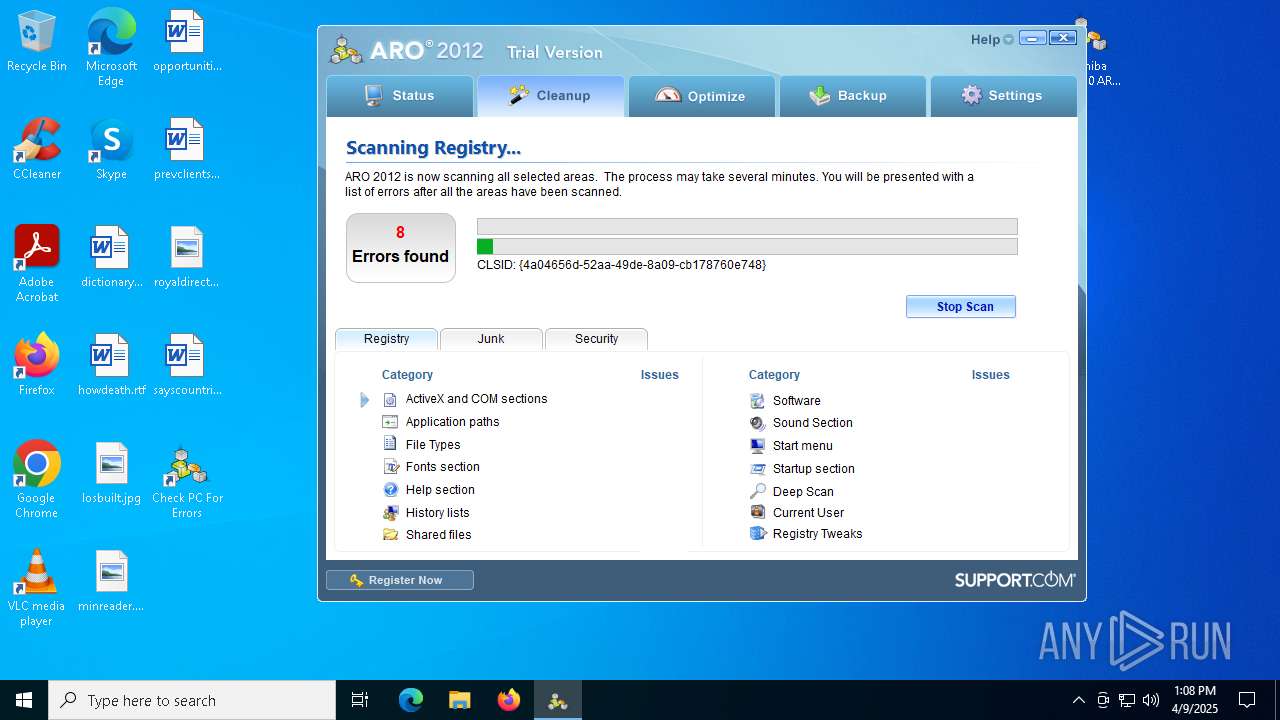
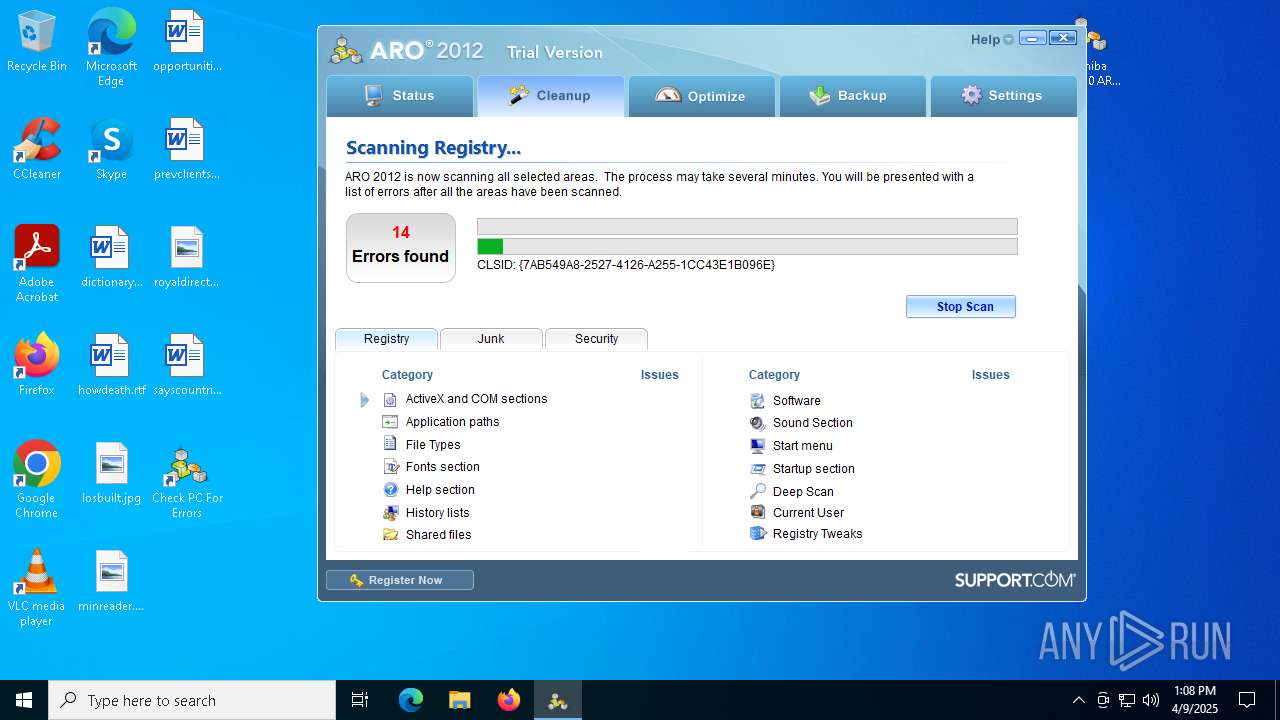
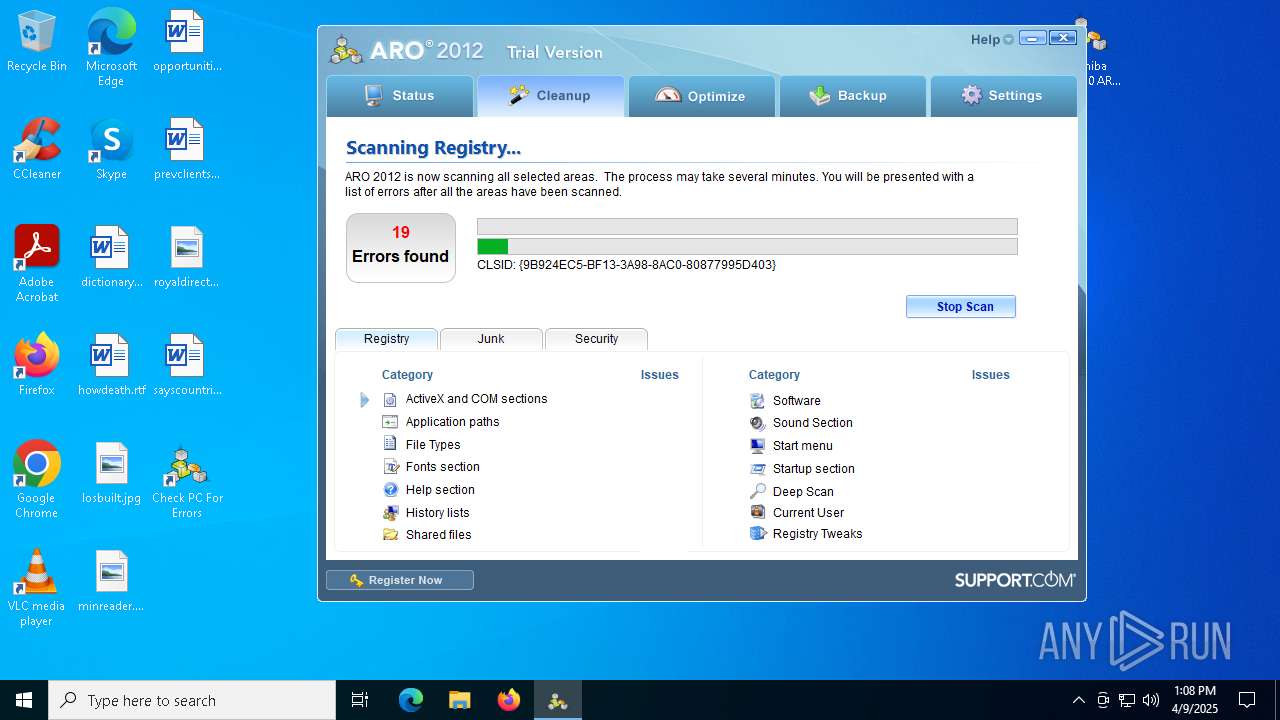
- ARO.exe (PID: 6264)
- ARO.exe (PID: 7352)
Actions looks like stealing of personal data
- ApnStub.exe (PID: 3180)
- ApnToolbarInstaller.exe (PID: 7864)
- msiexec.exe (PID: 6972)
- msiexec.exe (PID: 2656)
- CompatTelRunner.exe (PID: 2772)
Gets path to any of the special folders (SCRIPT)
- msiexec.exe (PID: 2656)
Creates a new folder (SCRIPT)
- msiexec.exe (PID: 2656)
Creates a new registry key or changes the value of an existing one (SCRIPT)
- msiexec.exe (PID: 2656)
Opens a text file (SCRIPT)
- msiexec.exe (PID: 2656)
Reads the value of a key from the registry (SCRIPT)
- msiexec.exe (PID: 2656)
Deletes a file (SCRIPT)
- msiexec.exe (PID: 2656)
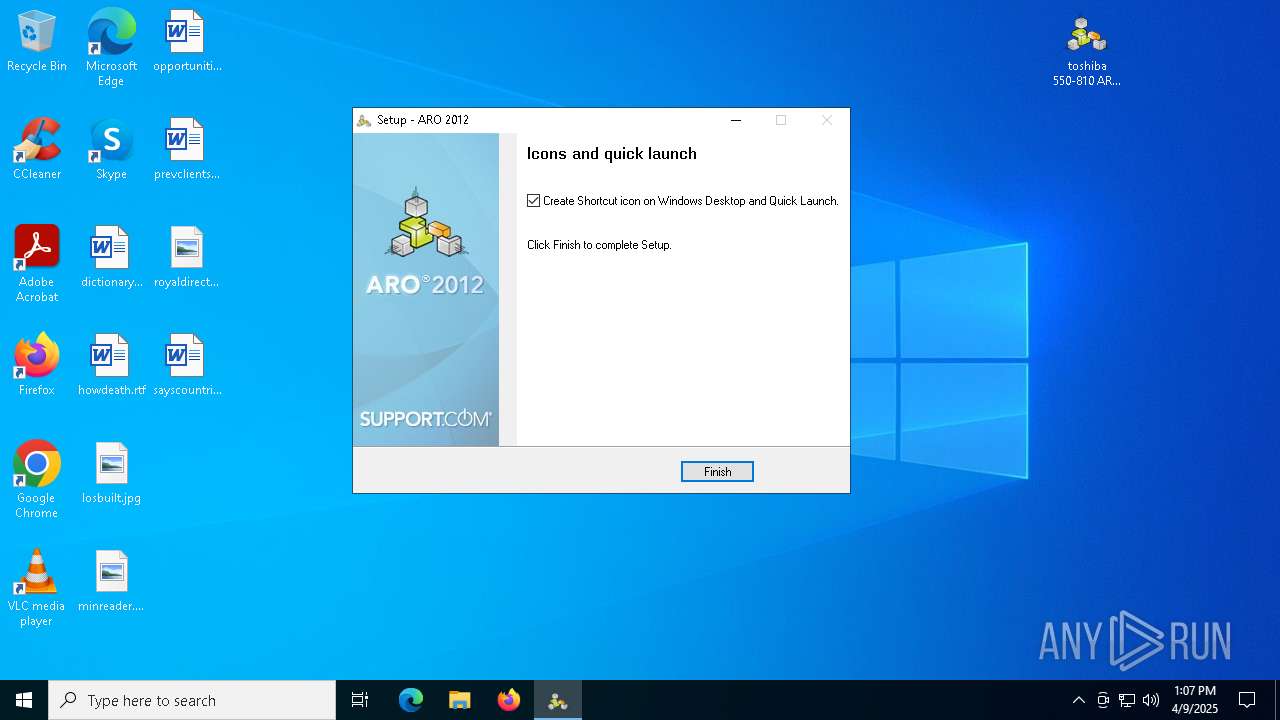
Changes the autorun value in the registry
- toshiba 550-810 ARO2012_tbt.tmp (PID: 6272)
SUSPICIOUS
Executable content was dropped or overwritten
- toshiba 550-810 ARO2012_tbt.exe (PID: 864)
- toshiba 550-810 ARO2012_tbt.exe (PID: 1228)
- toshiba 550-810 ARO2012_tbt.tmp (PID: 6272)
- ApnToolbarInstaller.exe (PID: 7864)
- NEWF7AB.tmp.exe (PID: 7820)
Reads security settings of Internet Explorer
- toshiba 550-810 ARO2012_tbt.tmp (PID: 6456)
- toshiba 550-810 ARO2012_tbt.tmp (PID: 6272)
- ApnStub.exe (PID: 3180)
- ApnStub.exe (PID: 7660)
- ApnToolbarInstaller.exe (PID: 7864)
- NEWF7AB.tmp.exe (PID: 7820)
- msiexec.exe (PID: 2656)
- msiexec.exe (PID: 5756)
- AskPartnerCobrandingTool.exe (PID: 736)
- TaskScheduler.exe (PID: 8080)
- ARO.exe (PID: 6264)
- ARO.exe (PID: 7352)
Reads the BIOS version
- toshiba 550-810 ARO2012_tbt.tmp (PID: 6272)
- ARO.exe (PID: 7352)
- ARO.exe (PID: 6264)
Reads Microsoft Outlook installation path
- toshiba 550-810 ARO2012_tbt.tmp (PID: 6272)
- ARO.exe (PID: 7352)
- ARO.exe (PID: 6264)
Creates/Modifies COM task schedule object
- toshiba 550-810 ARO2012_tbt.tmp (PID: 6272)
- msiexec.exe (PID: 5756)
Reads the Windows owner or organization settings
- toshiba 550-810 ARO2012_tbt.tmp (PID: 6272)
- msiexec.exe (PID: 6972)
Process drops legitimate windows executable
- toshiba 550-810 ARO2012_tbt.tmp (PID: 6272)
- NEWF7AB.tmp.exe (PID: 7820)
There is functionality for taking screenshot (YARA)
- toshiba 550-810 ARO2012_tbt.tmp (PID: 6272)
Executes as Windows Service
- VSSVC.exe (PID: 7900)
Adds/modifies Windows certificates
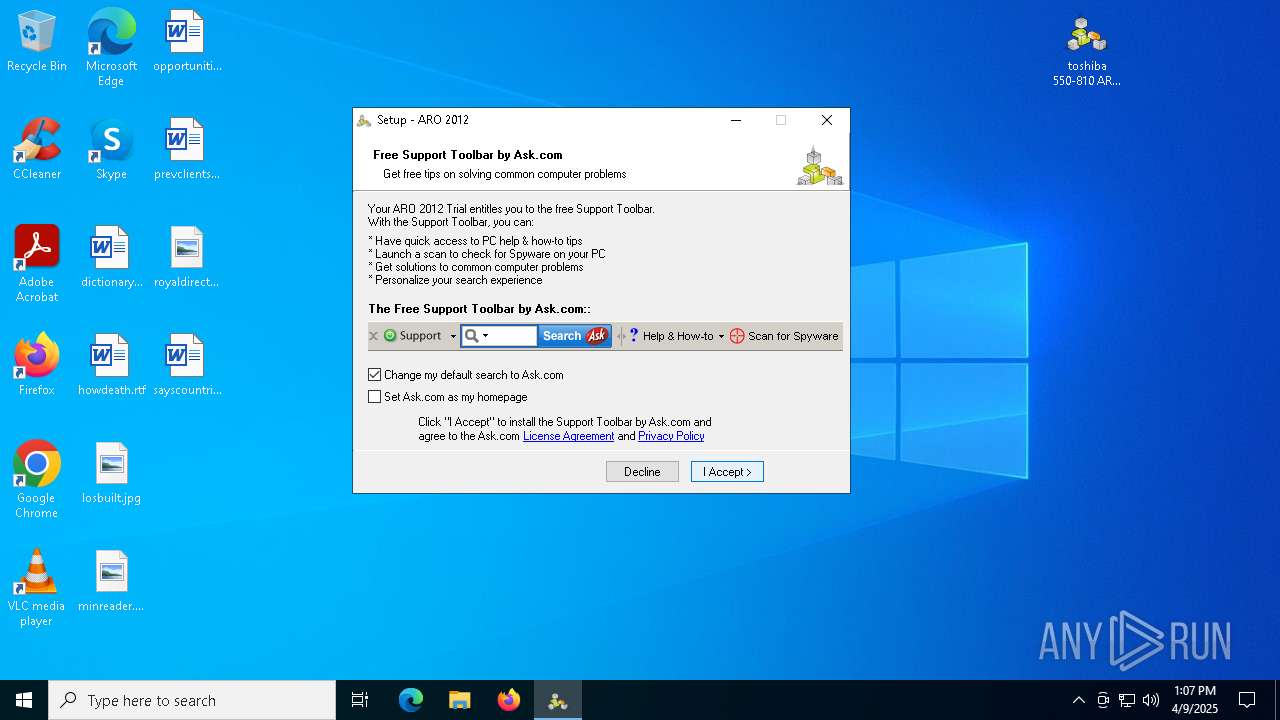
- ApnStub.exe (PID: 3180)
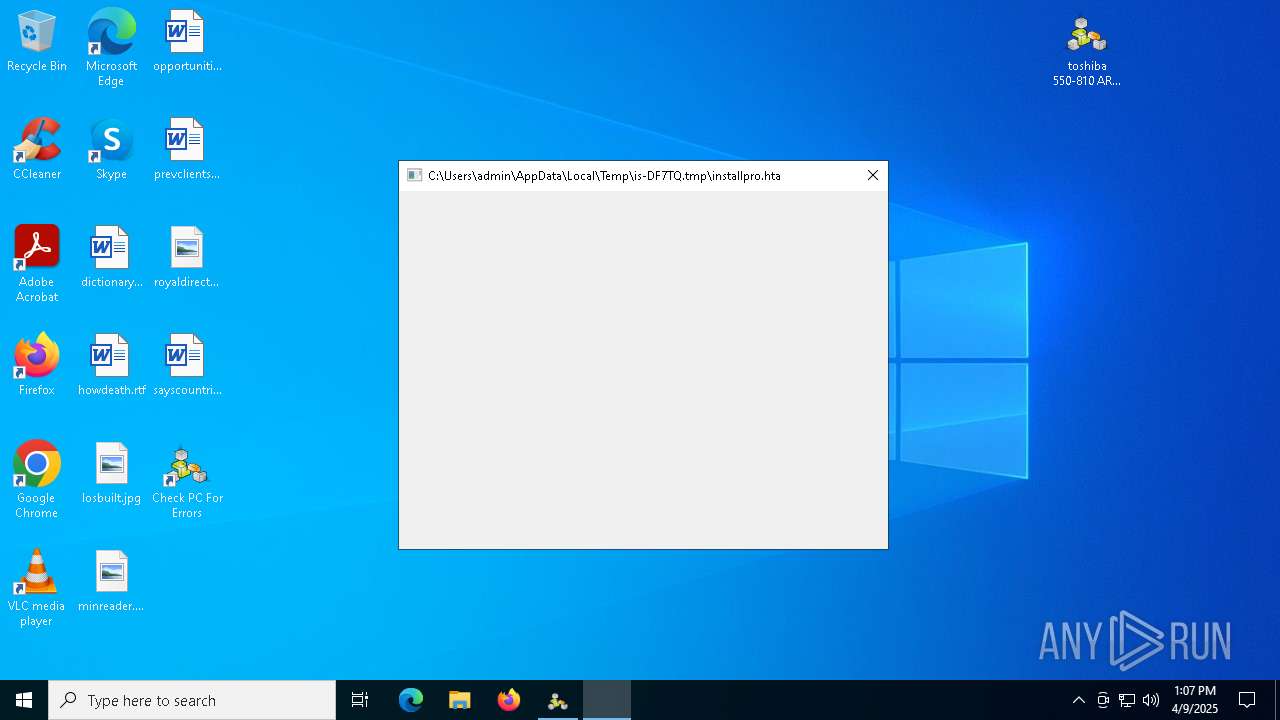
Creates FileSystem object to access computer's file system (SCRIPT)
- msiexec.exe (PID: 2656)
Writes binary data to a Stream object (SCRIPT)
- msiexec.exe (PID: 2656)
Searches for installed software
- dllhost.exe (PID: 7740)
- toshiba 550-810 ARO2012_tbt.tmp (PID: 6272)
- CompatTelRunner.exe (PID: 2772)
Reads data from a binary Stream object (SCRIPT)
- msiexec.exe (PID: 2656)
Runs shell command (SCRIPT)
- msiexec.exe (PID: 2656)
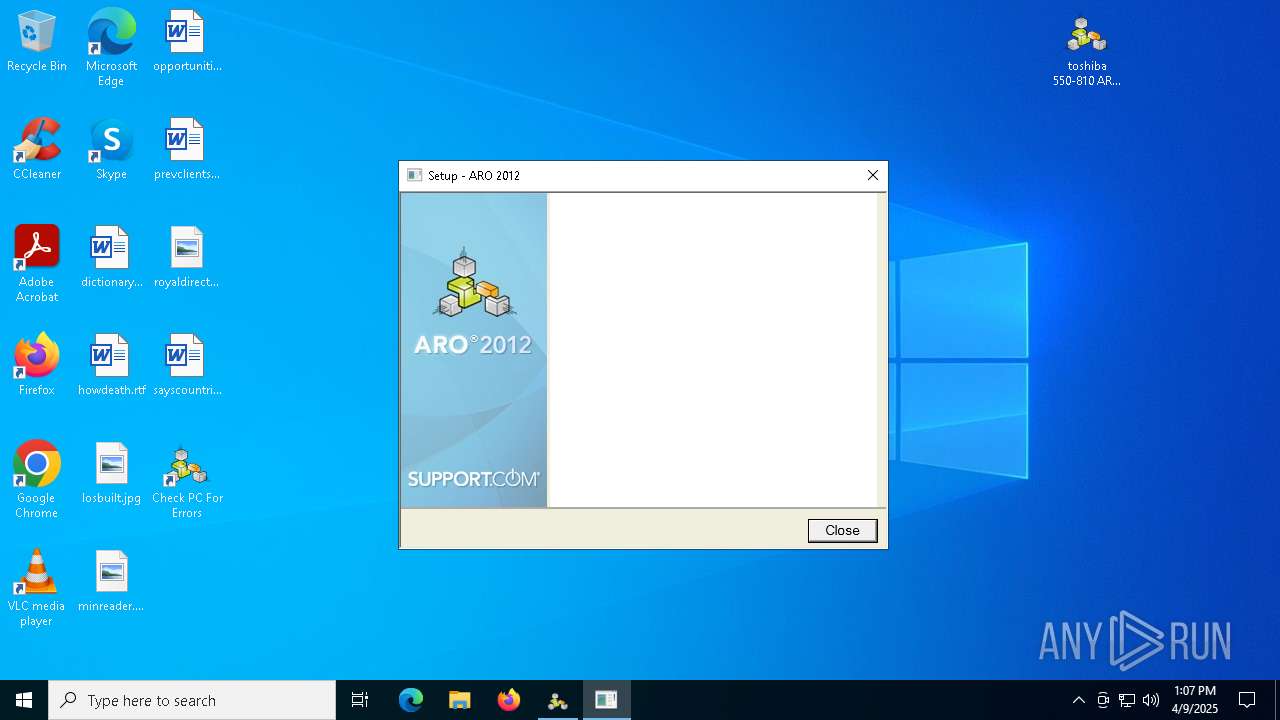
Reads Internet Explorer settings
- ARO.exe (PID: 7352)
INFO
Checks supported languages
- toshiba 550-810 ARO2012_tbt.exe (PID: 864)
- toshiba 550-810 ARO2012_tbt.tmp (PID: 6456)
- toshiba 550-810 ARO2012_tbt.exe (PID: 1228)
- ApnStub.exe (PID: 3180)
- toshiba 550-810 ARO2012_tbt.tmp (PID: 6272)
- ApnStub.exe (PID: 7660)
- ApnToolbarInstaller.exe (PID: 7864)
- NEWF7AB.tmp.exe (PID: 7820)
- msiexec.exe (PID: 6972)
- msiexec.exe (PID: 5756)
- msiexec.exe (PID: 2656)
- AskPartnerCobrandingTool.exe (PID: 736)
- TaskScheduler.exe (PID: 8080)
- ARO.exe (PID: 7352)
- ARO.exe (PID: 6264)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7504)
- msiexec.exe (PID: 6972)
- msiexec.exe (PID: 2656)
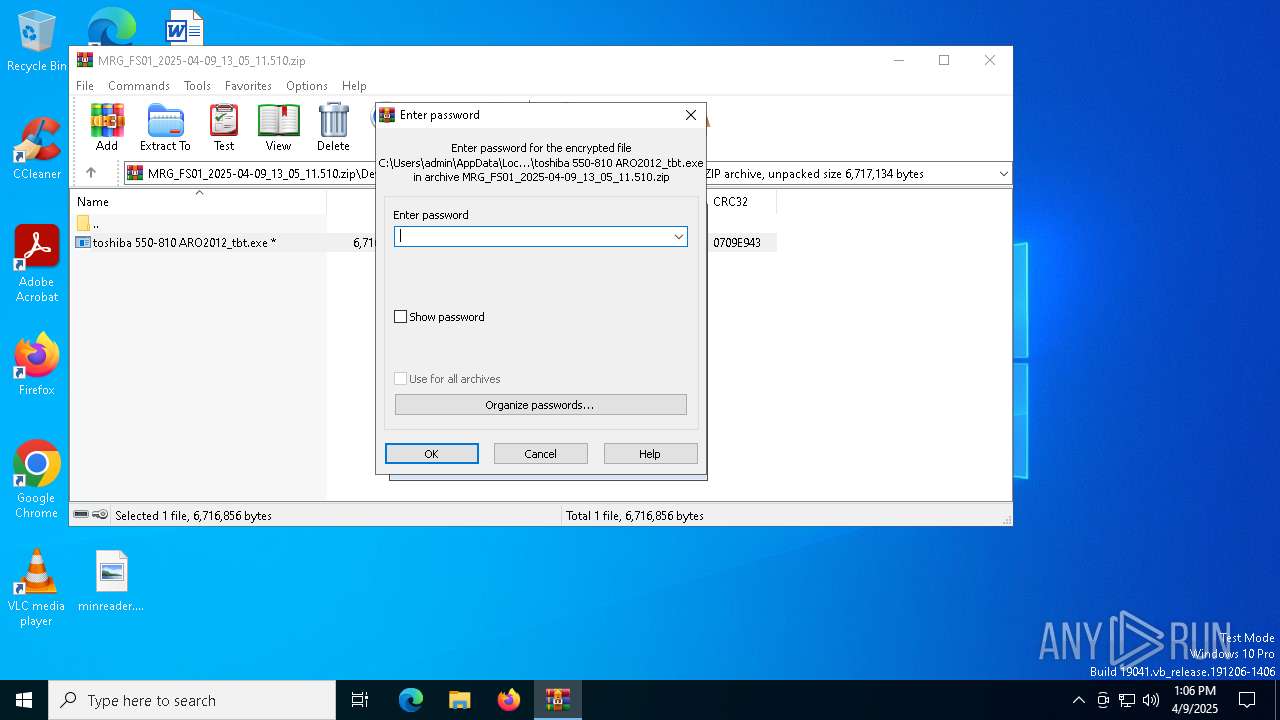
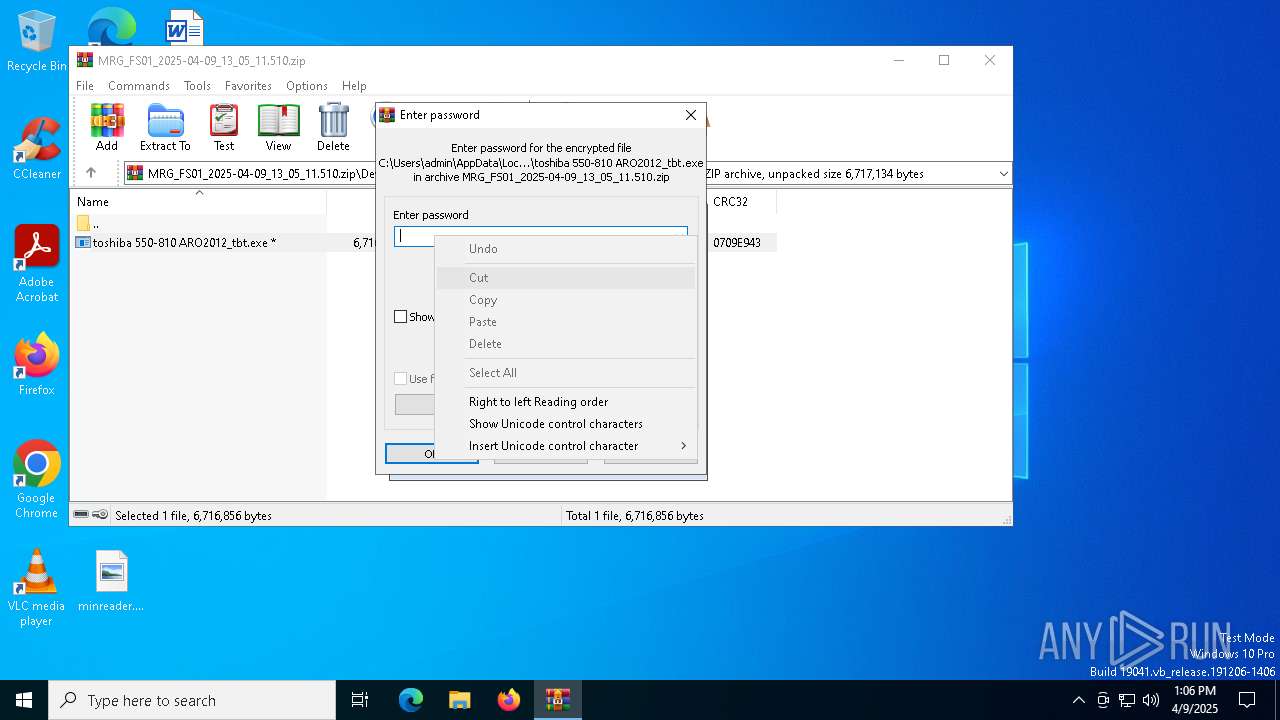
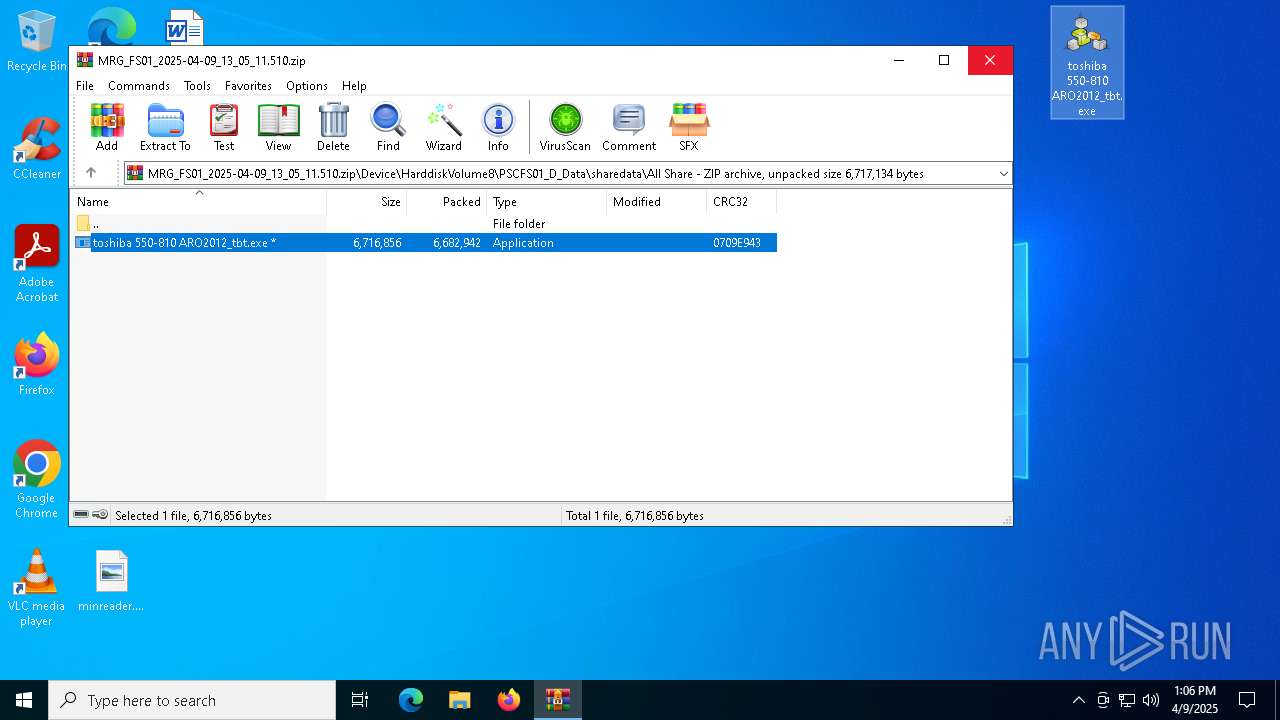
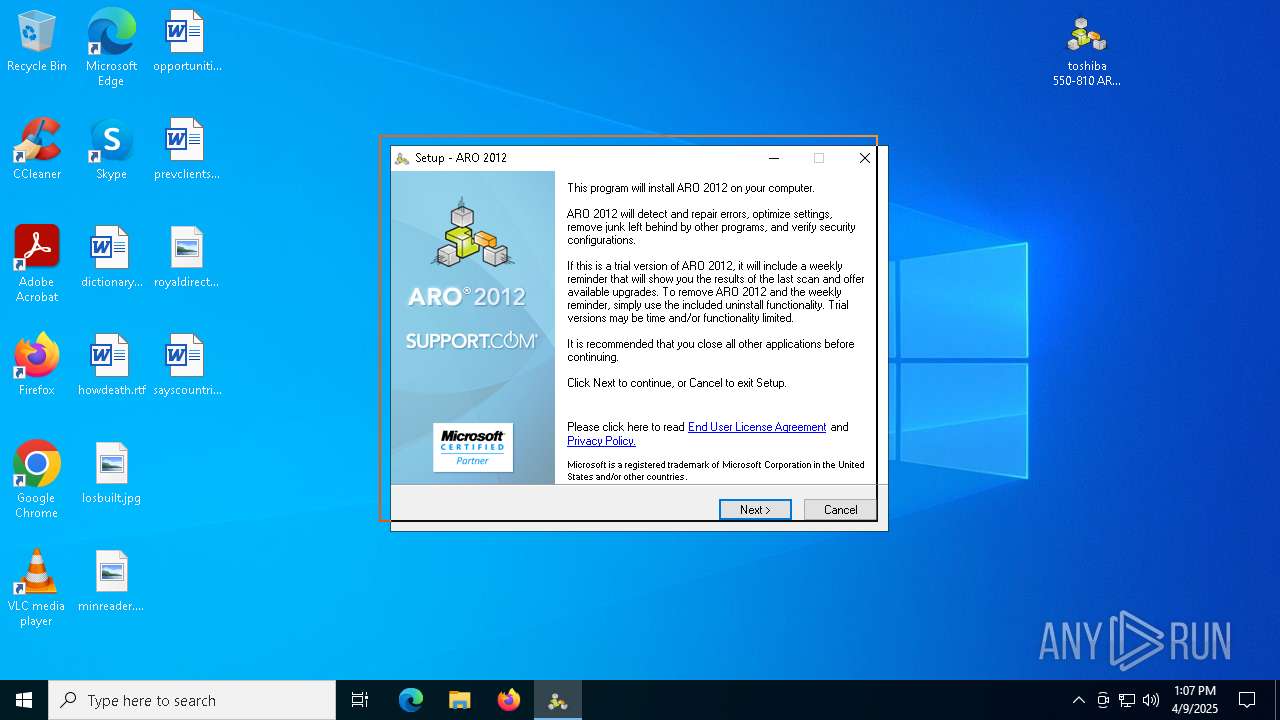
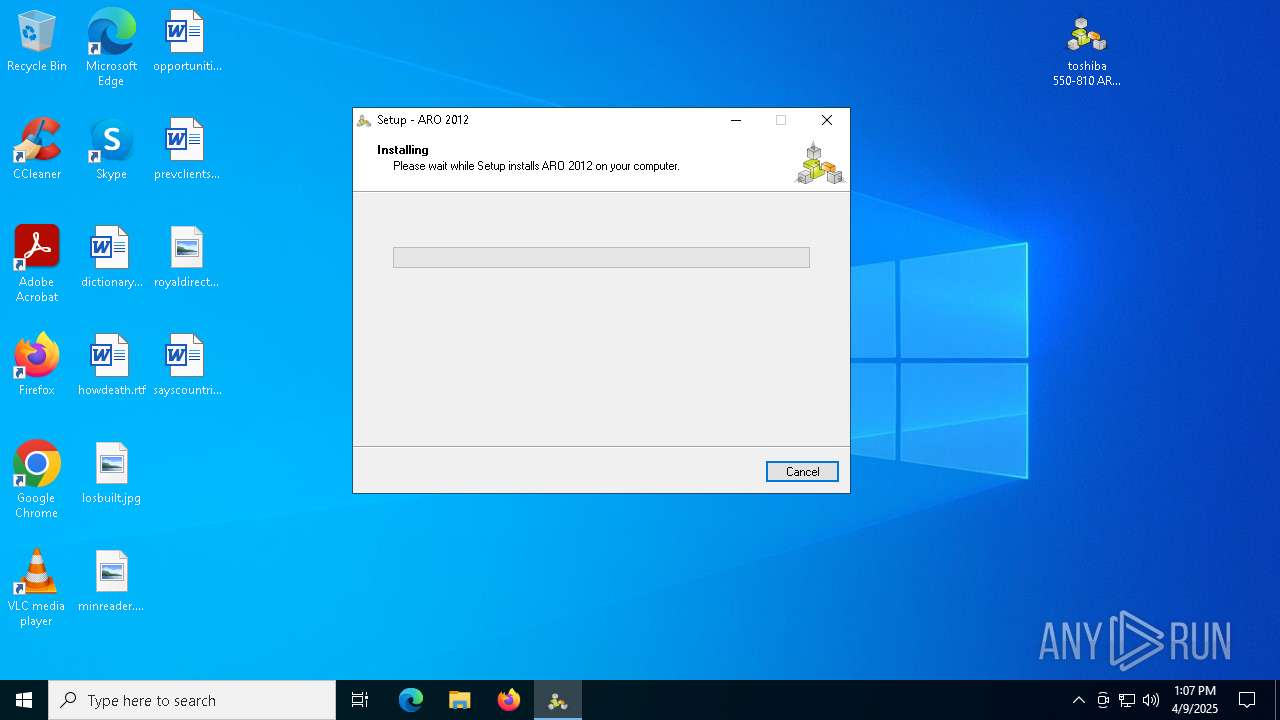
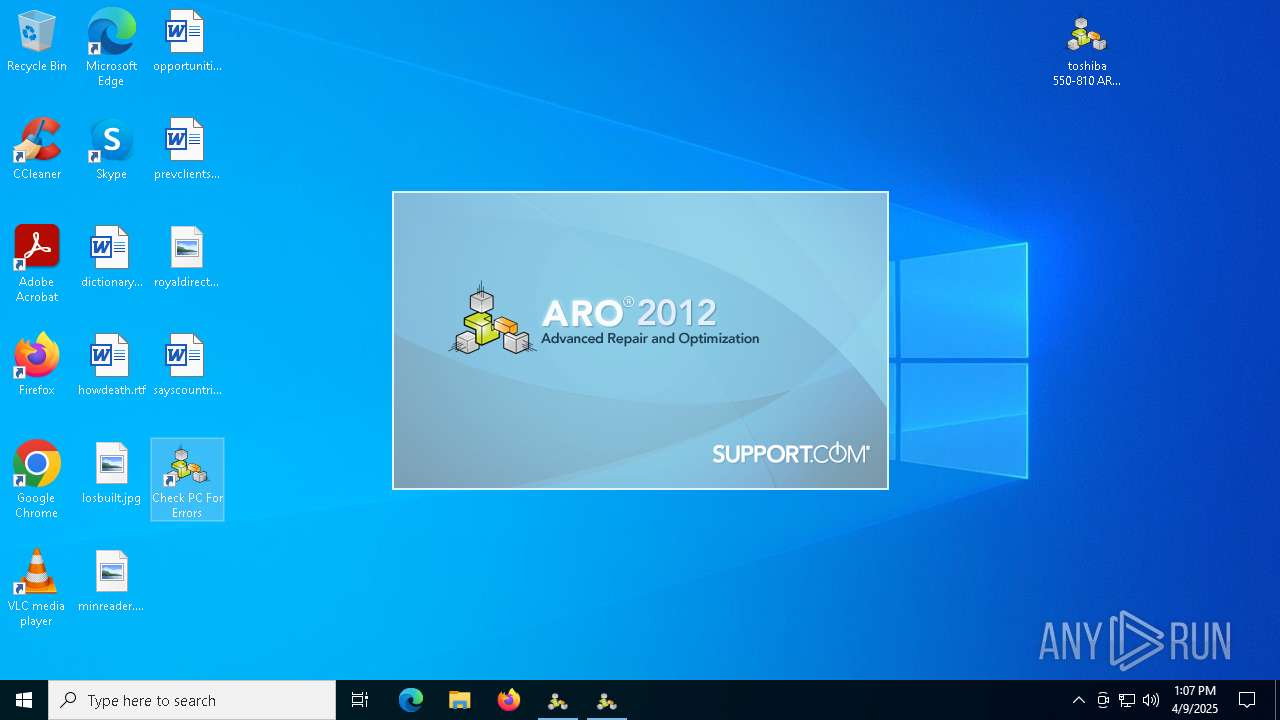
Manual execution by a user
- toshiba 550-810 ARO2012_tbt.exe (PID: 864)
- ARO.exe (PID: 6264)
Create files in a temporary directory
- toshiba 550-810 ARO2012_tbt.exe (PID: 864)
- toshiba 550-810 ARO2012_tbt.exe (PID: 1228)
- toshiba 550-810 ARO2012_tbt.tmp (PID: 6272)
- ApnToolbarInstaller.exe (PID: 7864)
- NEWF7AB.tmp.exe (PID: 7820)
- msiexec.exe (PID: 2656)
- msiexec.exe (PID: 7836)
- ARO.exe (PID: 7352)
Reads the computer name
- toshiba 550-810 ARO2012_tbt.tmp (PID: 6456)
- ApnStub.exe (PID: 3180)
- toshiba 550-810 ARO2012_tbt.tmp (PID: 6272)
- ApnStub.exe (PID: 7660)
- ApnToolbarInstaller.exe (PID: 7864)
- NEWF7AB.tmp.exe (PID: 7820)
- msiexec.exe (PID: 6972)
- msiexec.exe (PID: 2656)
- msiexec.exe (PID: 5756)
- AskPartnerCobrandingTool.exe (PID: 736)
- TaskScheduler.exe (PID: 8080)
- ARO.exe (PID: 7352)
- ARO.exe (PID: 6264)
Process checks computer location settings
- toshiba 550-810 ARO2012_tbt.tmp (PID: 6456)
- ApnStub.exe (PID: 7660)
- ApnToolbarInstaller.exe (PID: 7864)
- msiexec.exe (PID: 2656)
- toshiba 550-810 ARO2012_tbt.tmp (PID: 6272)
The sample compiled with english language support
- toshiba 550-810 ARO2012_tbt.tmp (PID: 6272)
- ApnToolbarInstaller.exe (PID: 7864)
- msiexec.exe (PID: 6972)
- msiexec.exe (PID: 2656)
- NEWF7AB.tmp.exe (PID: 7820)
Detects InnoSetup installer (YARA)
- toshiba 550-810 ARO2012_tbt.exe (PID: 864)
- toshiba 550-810 ARO2012_tbt.tmp (PID: 6456)
- toshiba 550-810 ARO2012_tbt.exe (PID: 1228)
- toshiba 550-810 ARO2012_tbt.tmp (PID: 6272)
Compiled with Borland Delphi (YARA)
- toshiba 550-810 ARO2012_tbt.tmp (PID: 6456)
- toshiba 550-810 ARO2012_tbt.tmp (PID: 6272)
Reads the machine GUID from the registry
- ApnStub.exe (PID: 7660)
- ApnStub.exe (PID: 3180)
- ARO.exe (PID: 7352)
Reads the software policy settings
- ApnStub.exe (PID: 7660)
- ApnStub.exe (PID: 3180)
- slui.exe (PID: 7244)
- CompatTelRunner.exe (PID: 2772)
Checks proxy server information
- ApnStub.exe (PID: 3180)
- ApnToolbarInstaller.exe (PID: 7864)
- ApnStub.exe (PID: 7660)
- AskPartnerCobrandingTool.exe (PID: 736)
- ARO.exe (PID: 7352)
- mshta.exe (PID: 7476)
- slui.exe (PID: 7244)
Creates files or folders in the user directory
- ApnStub.exe (PID: 3180)
- msiexec.exe (PID: 6972)
- ARO.exe (PID: 6264)
- ARO.exe (PID: 7352)
Creates a software uninstall entry
- msiexec.exe (PID: 6972)
- toshiba 550-810 ARO2012_tbt.tmp (PID: 6272)
Creates files in the program directory
- AskPartnerCobrandingTool.exe (PID: 736)
- toshiba 550-810 ARO2012_tbt.tmp (PID: 6272)
Manages system restore points
- SrTasks.exe (PID: 6660)
Reads Internet Explorer settings
- mshta.exe (PID: 7476)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0801 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 1980:00:00 00:00:00 |
| ZipCRC: | 0x0709e943 |
| ZipCompressedSize: | 6682942 |
| ZipUncompressedSize: | 6716856 |
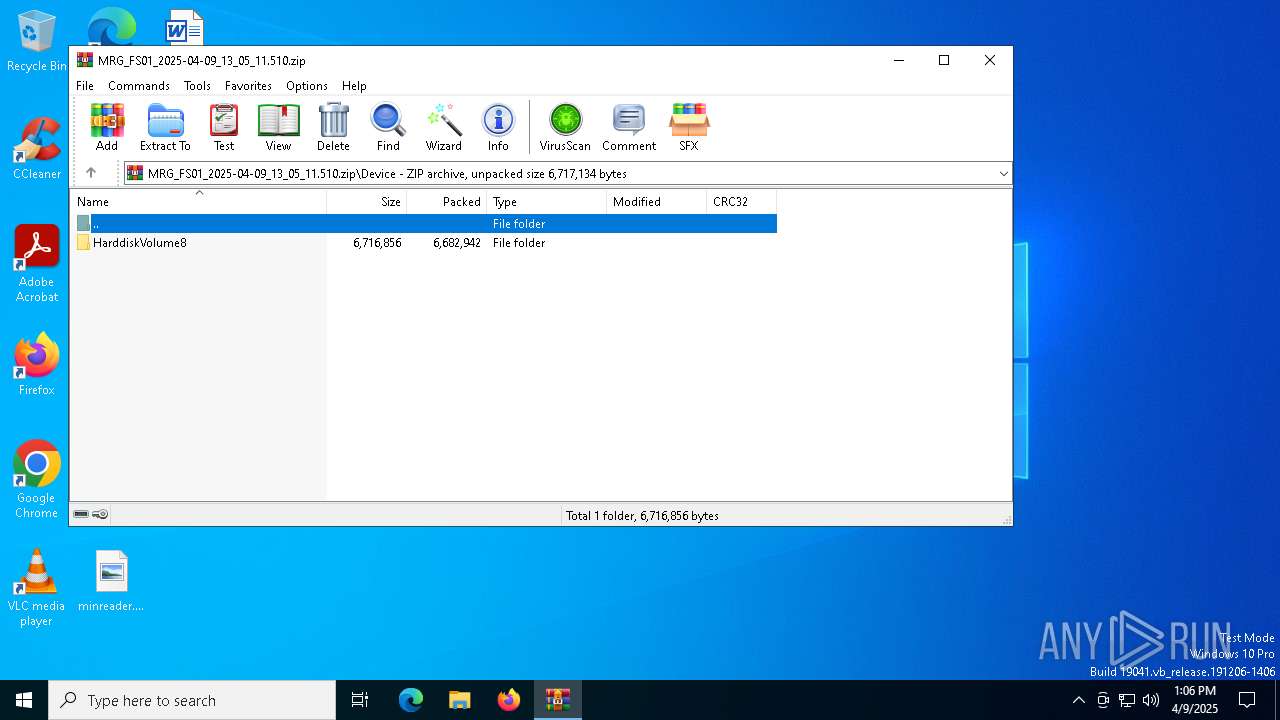
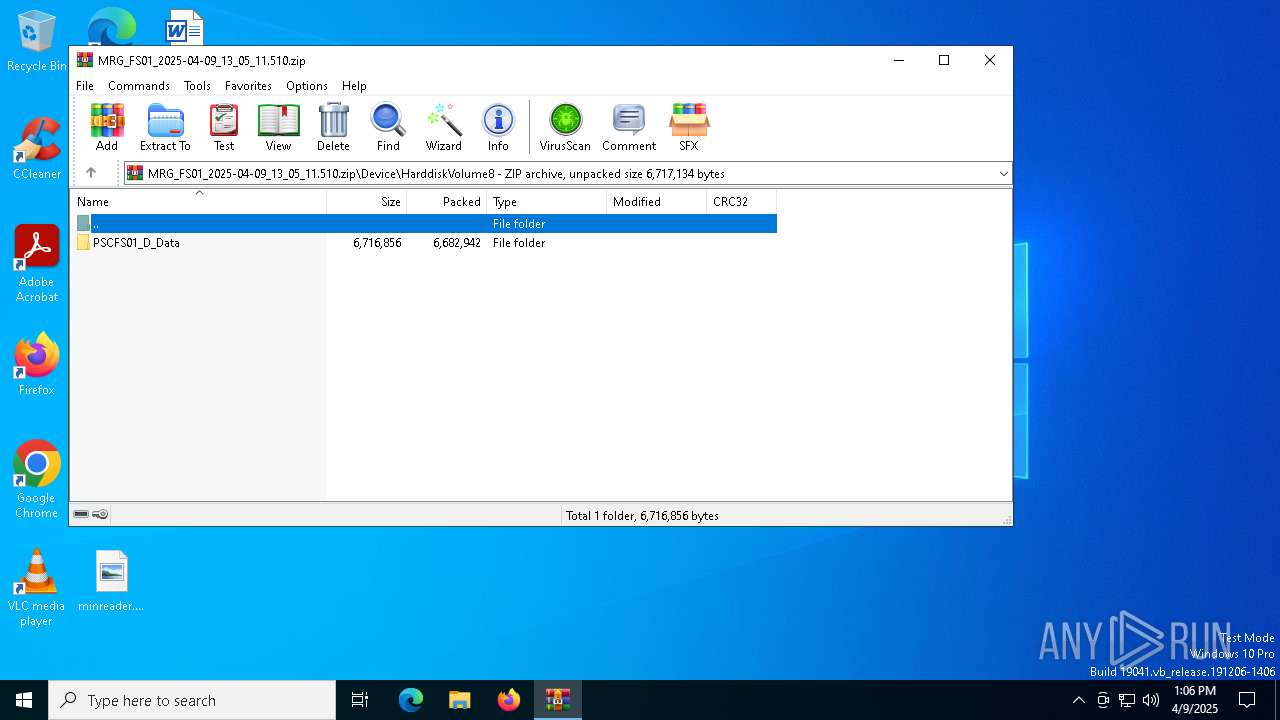
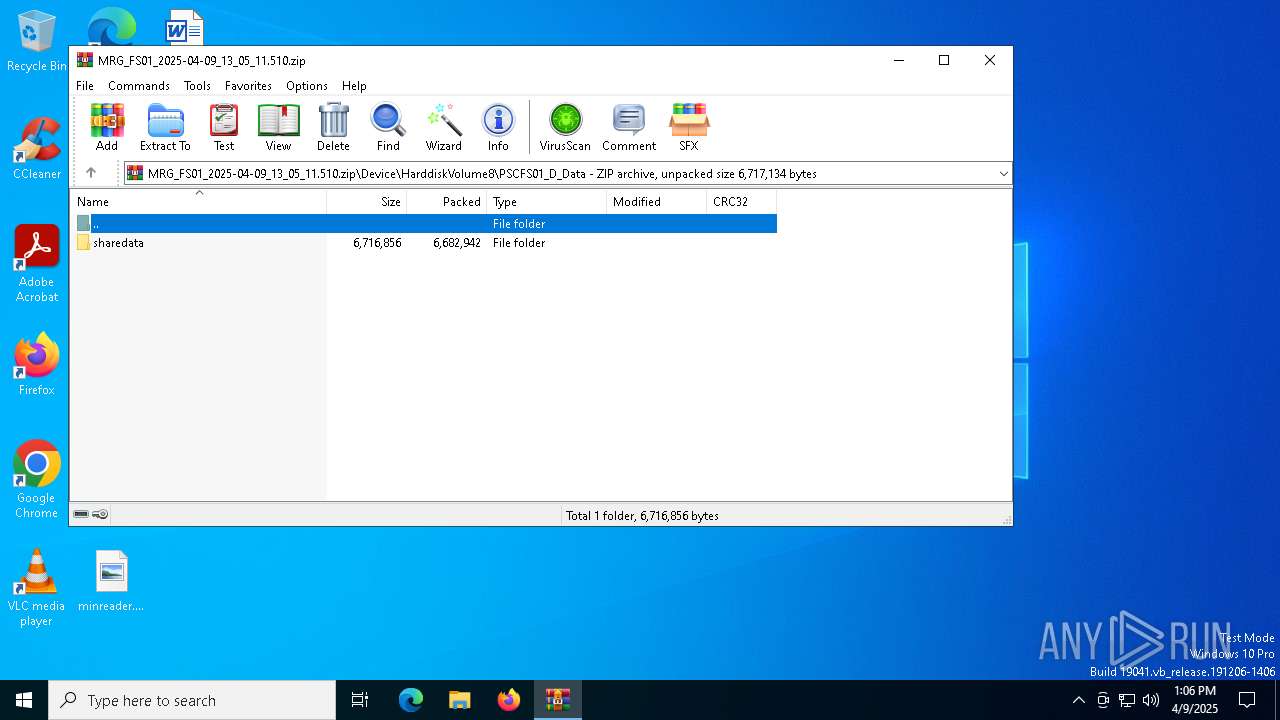
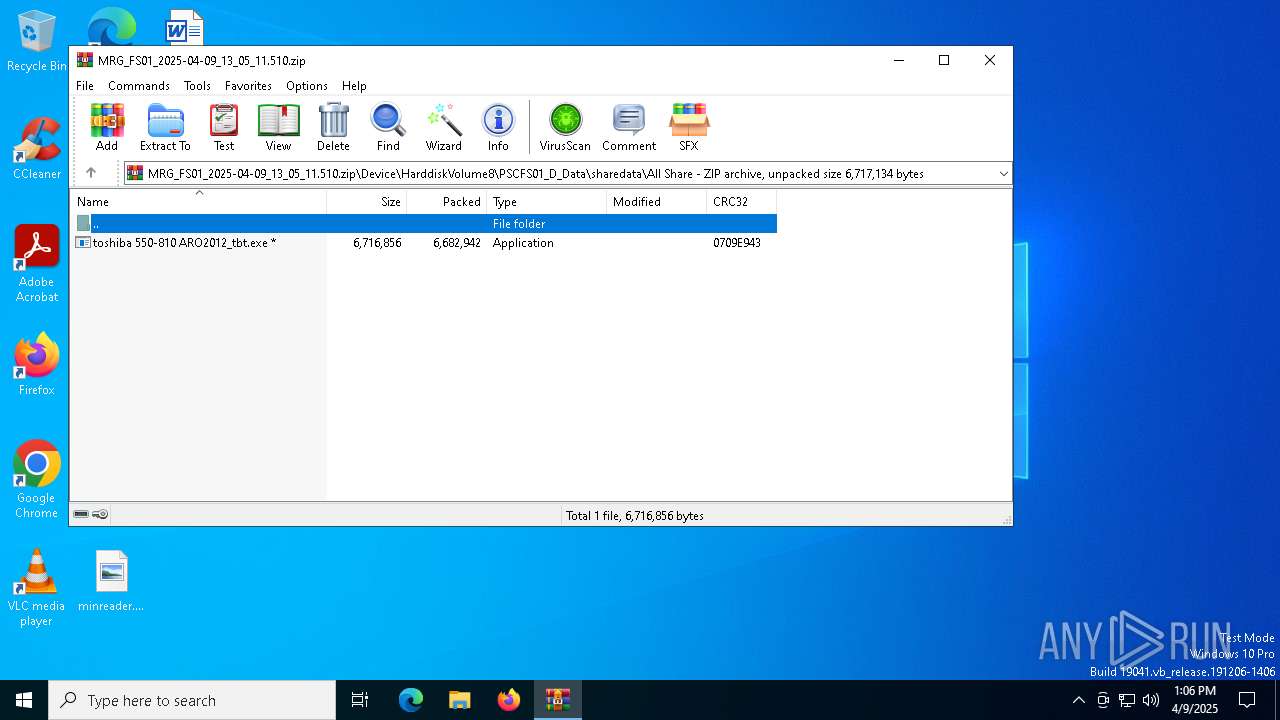
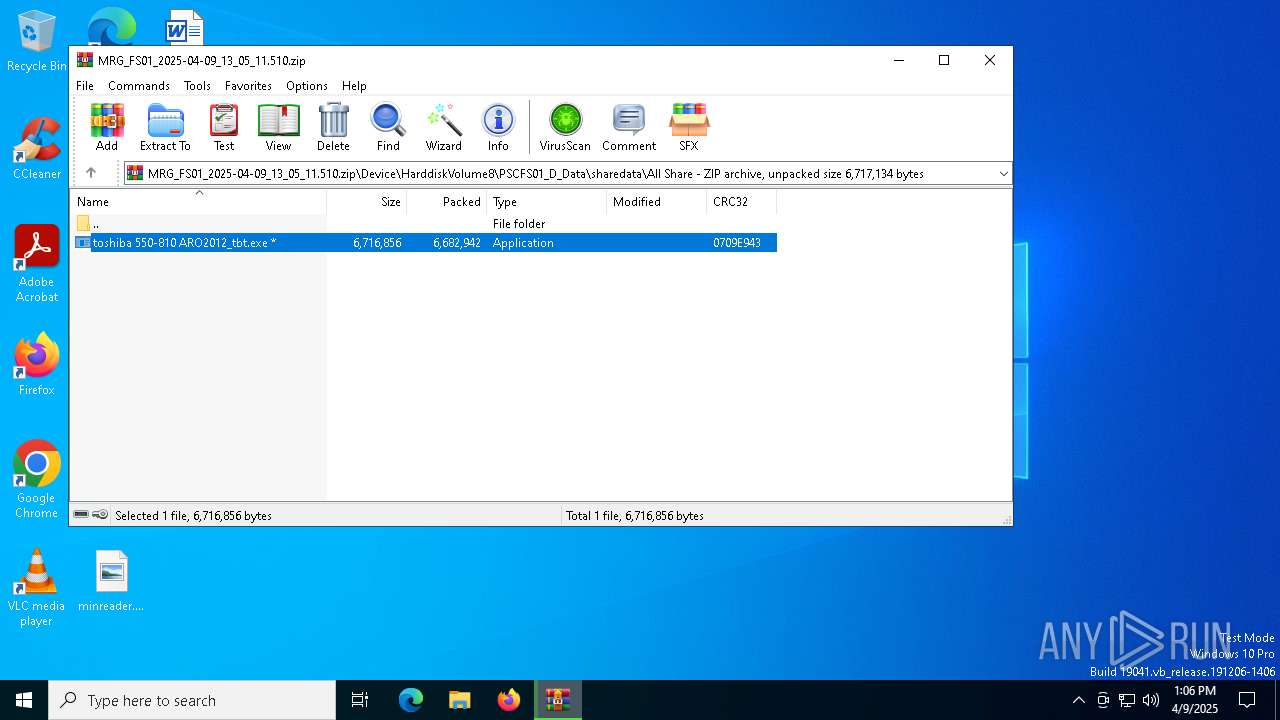
| ZipFileName: | Device/HarddiskVolume8/PSCFS01_D_Data/sharedata/All Share/toshiba 550-810 ARO2012_tbt.exe |
Total processes
166
Monitored processes
27
Malicious processes
14
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 736 | "C:\Users\admin\AppData\Local\Temp\{86D4B82A-ABED-442A-BE86-96357B70F4FE}\AskPartnerCobrandingTool.exe" X-SD | C:\Users\admin\AppData\Local\Temp\{86D4B82A-ABED-442A-BE86-96357B70F4FE}\AskPartnerCobrandingTool.exe | — | msiexec.exe | |||||||||||
User: admin Company: Ask Integrity Level: HIGH Description: Ask Toolbar Partner Cobranding Exit code: 4294967295 Version: 5.11.3.15590 Modules
| |||||||||||||||
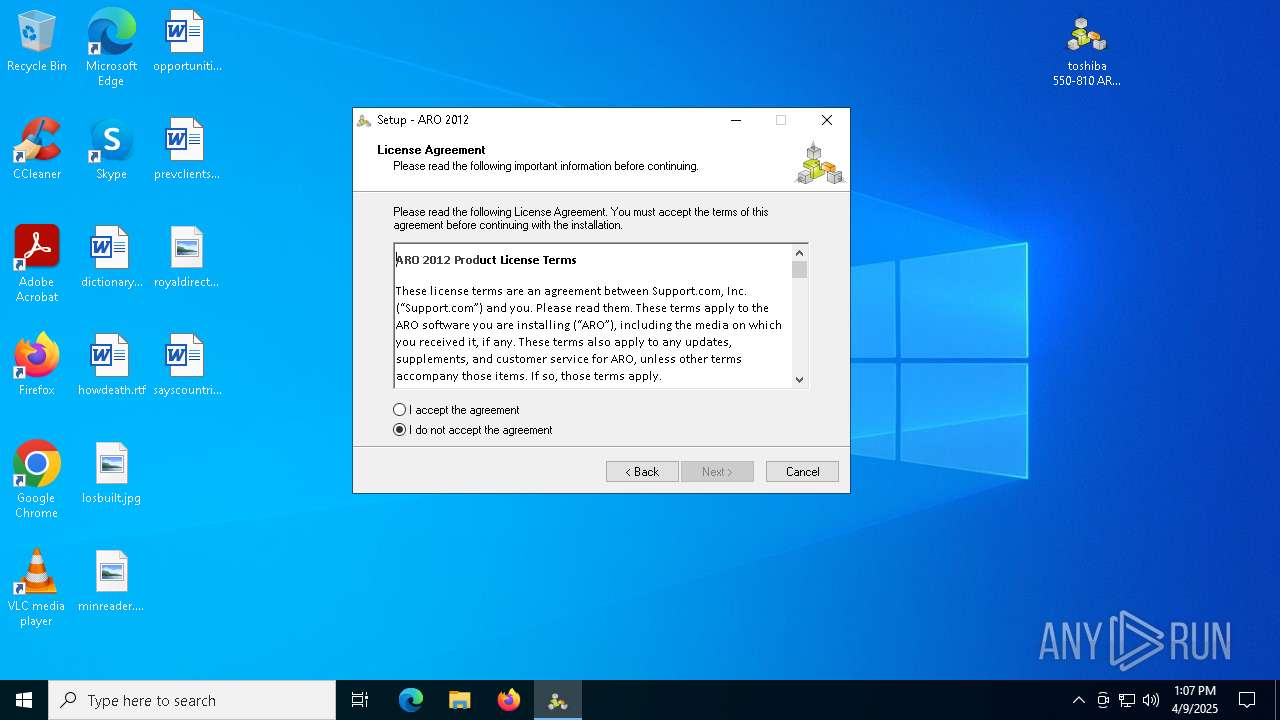
| 864 | "C:\Users\admin\Desktop\toshiba 550-810 ARO2012_tbt.exe" | C:\Users\admin\Desktop\toshiba 550-810 ARO2012_tbt.exe | explorer.exe | ||||||||||||
User: admin Company: Support.com Integrity Level: MEDIUM Description: ARO 2012 Exit code: 0 Version: ARO 2012 Modules
| |||||||||||||||
| 1228 | "C:\Users\admin\Desktop\toshiba 550-810 ARO2012_tbt.exe" /SPAWNWND=$1802DC /NOTIFYWND=$A02A2 | C:\Users\admin\Desktop\toshiba 550-810 ARO2012_tbt.exe | toshiba 550-810 ARO2012_tbt.tmp | ||||||||||||
User: admin Company: Support.com Integrity Level: HIGH Description: ARO 2012 Exit code: 0 Version: ARO 2012 Modules
| |||||||||||||||
| 2656 | C:\Windows\syswow64\MsiExec.exe -Embedding 1DC91FE5984998A894D5A8460DD7F391 | C:\Windows\SysWOW64\msiexec.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2772 | C:\WINDOWS\system32\compattelrunner.exe -m:aeinv.dll -f:UpdateSoftwareInventoryW | C:\Windows\System32\CompatTelRunner.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Compatibility Telemetry Exit code: 0 Version: 10.0.19645.1102 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3180 | "C:\Users\admin\AppData\Local\Temp\is-DF7TQ.tmp\ApnStub.exe" /tb=X-SD | C:\Users\admin\AppData\Local\Temp\is-DF7TQ.tmp\ApnStub.exe | toshiba 550-810 ARO2012_tbt.tmp | ||||||||||||
User: admin Company: Ask.com Integrity Level: HIGH Description: AskStub Application Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 5728 | C:\WINDOWS\system32\DllHost.exe /Processid:{F32D97DF-E3E5-4CB9-9E3E-0EB5B4E49801} | C:\Windows\System32\dllhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5756 | C:\Windows\syswow64\MsiExec.exe -Embedding 3FE5A344C86FB75228B7F20B50EE7E90 E Global\MSI0000 | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6264 | "C:\Program Files (x86)\ARO 2012\ARO.exe" | C:\Program Files (x86)\ARO 2012\ARO.exe | — | explorer.exe | |||||||||||
User: admin Company: Support.com, Inc. Integrity Level: MEDIUM Exit code: 0 Version: 8.0.7.0 Modules
| |||||||||||||||
| 6272 | "C:\Users\admin\AppData\Local\Temp\is-VSFID.tmp\toshiba 550-810 ARO2012_tbt.tmp" /SL5="$5030E,6405596,67072,C:\Users\admin\Desktop\toshiba 550-810 ARO2012_tbt.exe" /SPAWNWND=$1802DC /NOTIFYWND=$A02A2 | C:\Users\admin\AppData\Local\Temp\is-VSFID.tmp\toshiba 550-810 ARO2012_tbt.tmp | toshiba 550-810 ARO2012_tbt.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.50.0.0 Modules
| |||||||||||||||
Total events
82 005
Read events
81 390
Write events
566
Delete events
49
Modification events
| (PID) Process: | (7504) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (7504) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (7504) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (7504) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\MRG_FS01_2025-04-09_13_05_11.510.zip | |||
| (PID) Process: | (7504) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (7504) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (7504) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (7504) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (7504) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (7504) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | name |
Value: 256 | |||
Executable files
61
Suspicious files
58
Text files
165
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1228 | toshiba 550-810 ARO2012_tbt.exe | C:\Users\admin\AppData\Local\Temp\is-VSFID.tmp\toshiba 550-810 ARO2012_tbt.tmp | executable | |
MD5:CC957EB4298890C015A9FEDDE8BA6F32 | SHA256:91AD6AFE4870D909D8EFE16AE1272D92693C8C539486DD17767E199721EABBA5 | |||
| 7504 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb7504.28142\Device\HarddiskVolume8\PSCFS01_D_Data\sharedata\All Share\toshiba 550-810 ARO2012_tbt.exe | executable | |
MD5:1985CAF6CF1C560425B7D453C85A7812 | SHA256:35908ED6F8B5E9D2DCB5D80035F930167765F7F702765D8F385A59CD98E8A582 | |||
| 6272 | toshiba 550-810 ARO2012_tbt.tmp | C:\Users\admin\AppData\Local\Temp\is-DF7TQ.tmp\_isetup\_setup64.tmp | executable | |
MD5:4FF75F505FDDCC6A9AE62216446205D9 | SHA256:A4C86FC4836AC728D7BD96E7915090FD59521A9E74F1D06EF8E5A47C8695FD81 | |||
| 6272 | toshiba 550-810 ARO2012_tbt.tmp | C:\Users\admin\AppData\Local\Temp\is-DF7TQ.tmp\ApnIC.dll | executable | |
MD5:0994A240F1A80D332C24930A1B713633 | SHA256:85AF9002C0513EE7EC5A6751AED976A2A6213E13A0BD3CF9DBE7C4CD143BB561 | |||
| 6272 | toshiba 550-810 ARO2012_tbt.tmp | C:\Users\admin\AppData\Local\Temp\is-DF7TQ.tmp\AskToolbarMockup.bmp | image | |
MD5:D4A574D90C480B4232A742E66F61BCFC | SHA256:23955C739097A61ADF9BFFDAE636EFE0D131B9DFCD2FBFA7238FDE48B03F85A3 | |||
| 6272 | toshiba 550-810 ARO2012_tbt.tmp | C:\Users\admin\AppData\Local\Temp\is-DF7TQ.tmp\setup_icon.bmp | image | |
MD5:DF3A9A444B27BC4E5718AA8DA3105A90 | SHA256:BC89E6C757AF80612E54BEE67CEF556176F2A0F6C46DEACC6BA67874F54F2E18 | |||
| 3180 | ApnStub.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\3C3948BE6E525B8A8CEE9FAC91C9E392_1053BC6C384022F220EA45C1780667AC | binary | |
MD5:5BFA51F3A417B98E7443ECA90FC94703 | SHA256:BEBE2853A3485D1C2E5C5BE4249183E0DDAFF9F87DE71652371700A89D937128 | |||
| 3180 | ApnStub.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\3C3948BE6E525B8A8CEE9FAC91C9E392_1053BC6C384022F220EA45C1780667AC | binary | |
MD5:CFEC84CE906610B4102B4ED77937B645 | SHA256:962BC8A2EFB7D720C49CA4C3E0BB17DA7D0C7A607E01E576949F30D42C199282 | |||
| 6272 | toshiba 550-810 ARO2012_tbt.tmp | C:\Users\admin\AppData\Local\Temp\is-DF7TQ.tmp\installer_mspartner.bmp | image | |
MD5:EF40CEAB47696EB4BCE5FE2E70EC6D7C | SHA256:ECED8A2096F1EB1420943DBED1913202F23B14B06BC8B83D3D836AB7E2770FB9 | |||
| 6272 | toshiba 550-810 ARO2012_tbt.tmp | C:\Users\admin\AppData\Local\Temp\is-DF7TQ.tmp\install_left_image.bmp | image | |
MD5:8B732474F04E6EB8A04530B0701E49E7 | SHA256:C4625870FE298DF5B8C969C3F3259E6651C25E7C0BA22FAD7552EA2051D74C96 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
18
TCP/UDP connections
43
DNS requests
34
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7320 | SIHClient.exe | GET | 200 | 104.119.109.218:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7320 | SIHClient.exe | GET | 200 | 104.119.109.218:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
3180 | ApnStub.exe | GET | 200 | 2.17.189.192:80 | http://crl.verisign.com/pca3.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
3180 | ApnStub.exe | GET | 200 | 2.17.189.192:80 | http://ocsp.verisign.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ%2FxkCfyHfJr7GQ6M658NRZ4SHo%2FAQUCPVR6Pv%2BPT1kNnxoz1t4qN%2B5xTcCEChvijDi6saWW5NvgmoFMF0%3D | unknown | — | — | whitelisted |
3180 | ApnStub.exe | GET | 200 | 34.117.224.112:80 | http://img.apnanalytics.com/images/nocache/apn/tr.gif?ev=eichk&cb=&encb=&chk=sucof&ts=WvpZf&guid=93d867da-31f6-44fb-a059-20f9df2e3f3d&dt=0&wft=local&harch=64&hloc=en-US&iev=9.11.19041.0&dbr=&vb=&msi=&inst=&tb=X-SD&hos=6.2.1.sp0.x64&dot=6 | unknown | — | — | unknown |
3180 | ApnStub.exe | GET | 200 | 2.17.189.192:80 | http://ocsp.verisign.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ%2FxkCfyHfJr7GQ6M658NRZ4SHo%2FAQUCPVR6Pv%2BPT1kNnxoz1t4qN%2B5xTcCEChvijDi6saWW5NvgmoFMF0%3D | unknown | — | — | whitelisted |
7660 | ApnStub.exe | GET | 200 | 2.17.189.192:80 | http://ocsp.verisign.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ%2FxkCfyHfJr7GQ6M658NRZ4SHo%2FAQUCPVR6Pv%2BPT1kNnxoz1t4qN%2B5xTcCEChvijDi6saWW5NvgmoFMF0%3D | unknown | — | — | whitelisted |
7864 | ApnToolbarInstaller.exe | GET | 200 | 34.117.224.112:80 | http://img.apnanalytics.com/images/nocache/apn/tr.gif?ev=ewrap&cb=&stb=acct&ssa=decl&shpr=decl¶m=succ&ts=kZtId&guid=59166152-3D27-4ADE-AD88-1CA4D76FA327&dt=&wft=&harch=&hloc=&iev=9.11.19041.0&dbr=&vb=&msi=&inst=&tb=X-SD | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.216.77.28:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4208 | RUXIMICS.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 40.126.32.68:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
2104 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
7320 | SIHClient.exe | 20.12.23.50:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
apnmedia.ask.com |
| whitelisted |