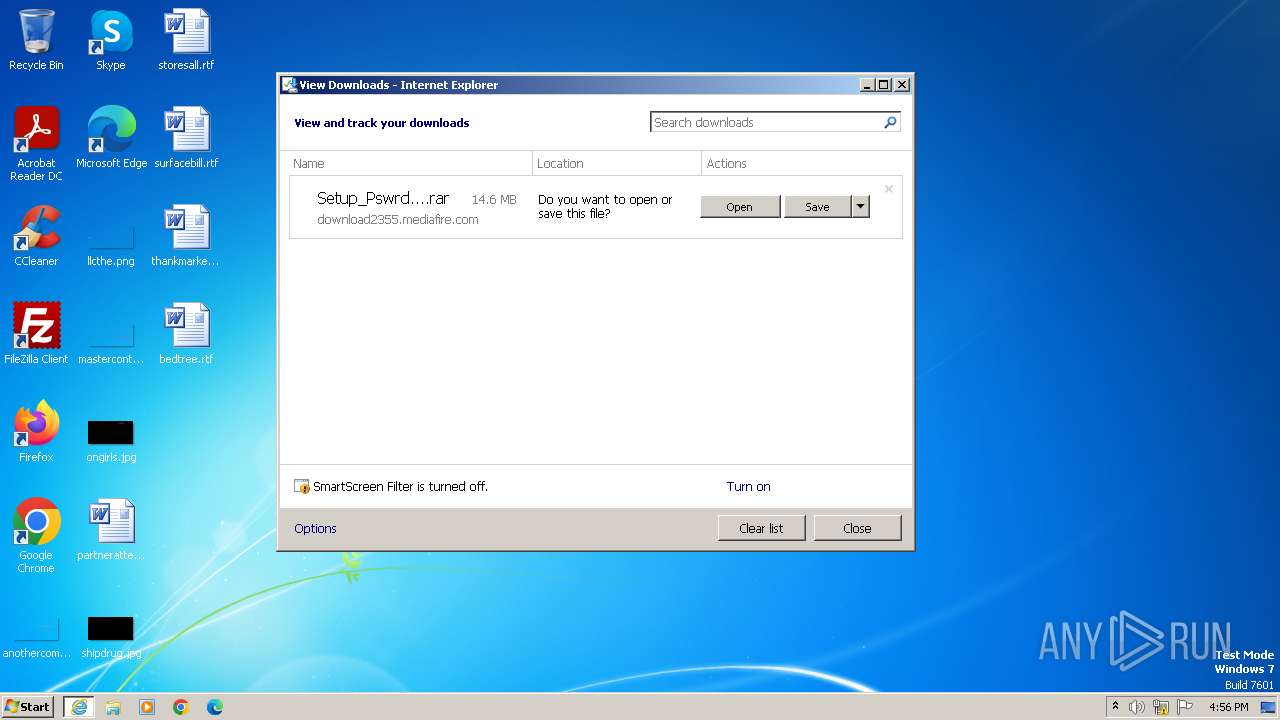
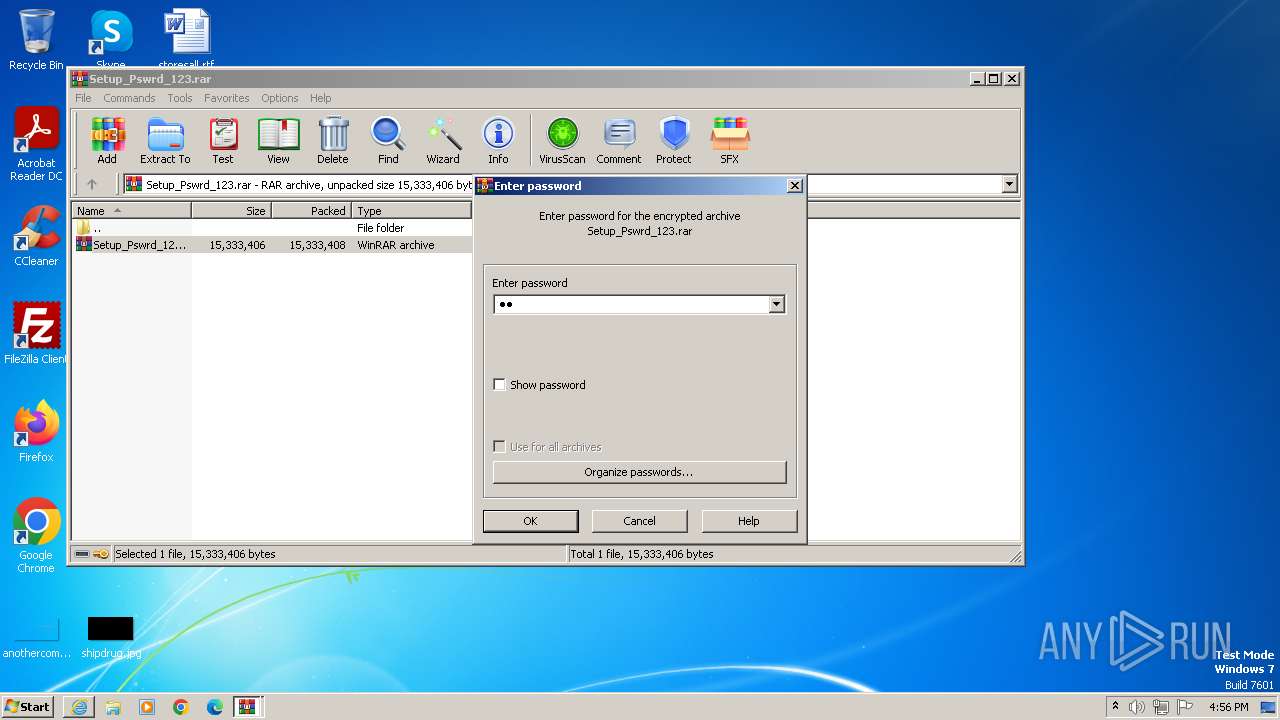
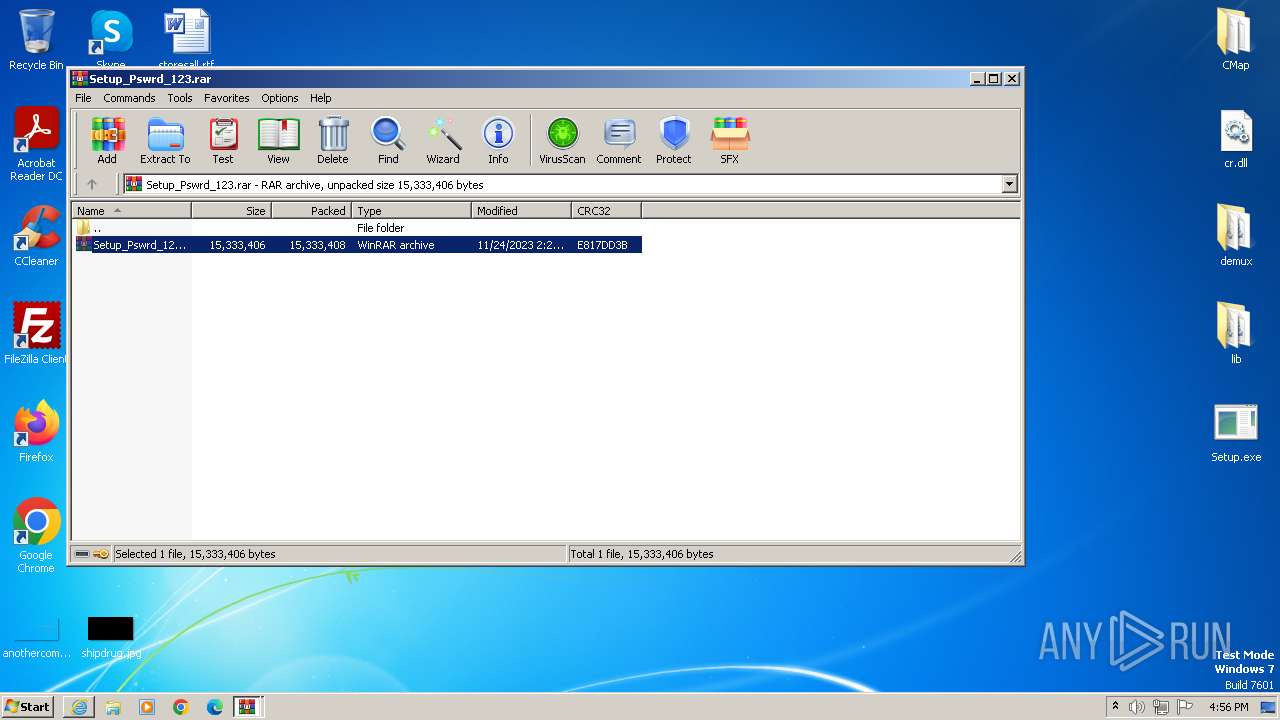
| URL: | https://download2355.mediafire.com/7qzv47ul3vzgvQfpHn6RFmgSvshyxuqIvrke1l6HHB9aIkfEr8B5e9ZZIjn1nomBTG7iInHiZFkDn5BgCf4z44rfcBtI7k2rfRtdCazRAsY7xPIlG6QYKV5R1sN5H9ZkiJTiCzr3qn9PTLMeLfj33i1ELwnsFhzuHMS6tiB9U5aQww/ou388wisa9rb0an/Setup_Pswrd_123.rar |
| Full analysis: | https://app.any.run/tasks/a142bbfc-f55b-405e-81d3-620d85df3d06 |
| Verdict: | Malicious activity |
| Analysis date: | November 25, 2023, 16:56:15 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| SHA1: | F01A0725BF5B95EE0CECA2072CFF0F8D8869C394 |
| SHA256: | CD33759826E3E8DF49F7385D4A78AAA1CC6AAEEAE66E165046CF0B3CAE6F1EAA |
| SSDEEP: | 6:2SWXQSeGyVTeETY+P5Bpp4wyHsALg7iTx9/T64aquo1Xq7W7:2tXNe/ep+MPSiTx1T/D1Xqa |
MALICIOUS
No malicious indicators.SUSPICIOUS
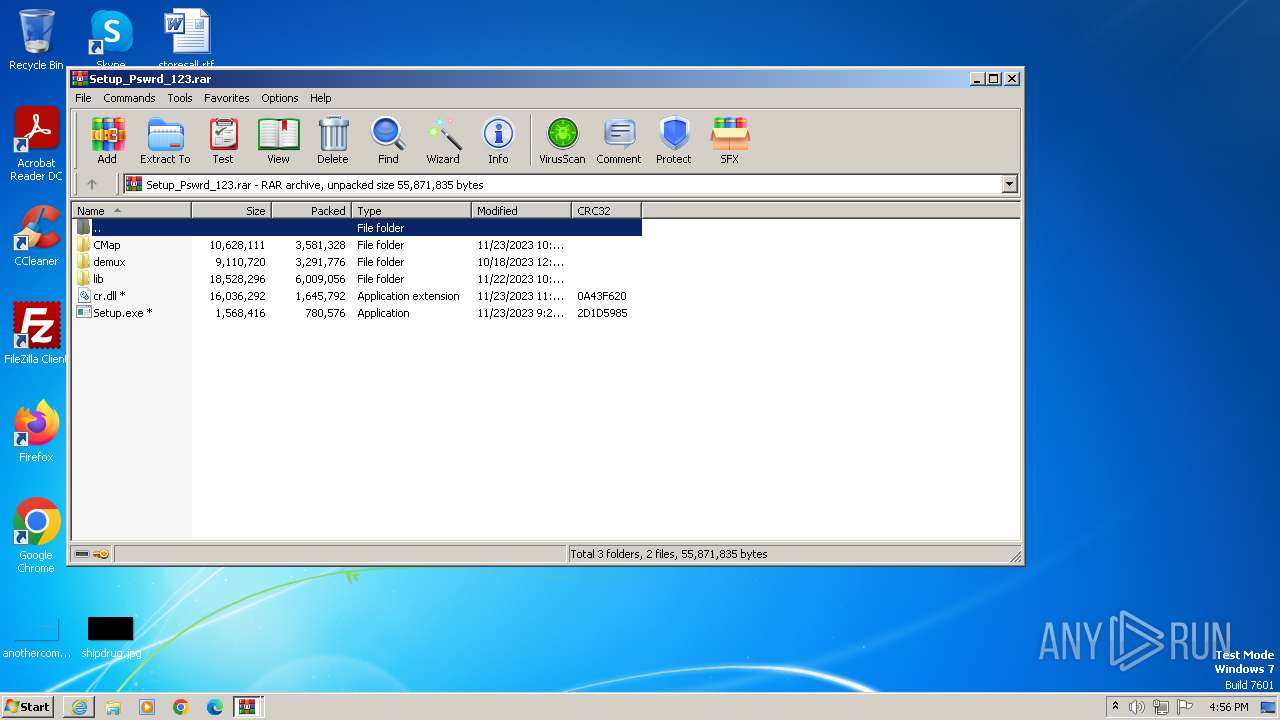
Application launched itself
- WinRAR.exe (PID: 1064)
Drops a system driver (possible attempt to evade defenses)
- WinRAR.exe (PID: 944)
Process uses IPCONFIG to discard the IP address configuration
- cmd.exe (PID: 3112)
Process uses IPCONFIG to renew DHCP configuration
- cmd.exe (PID: 3044)
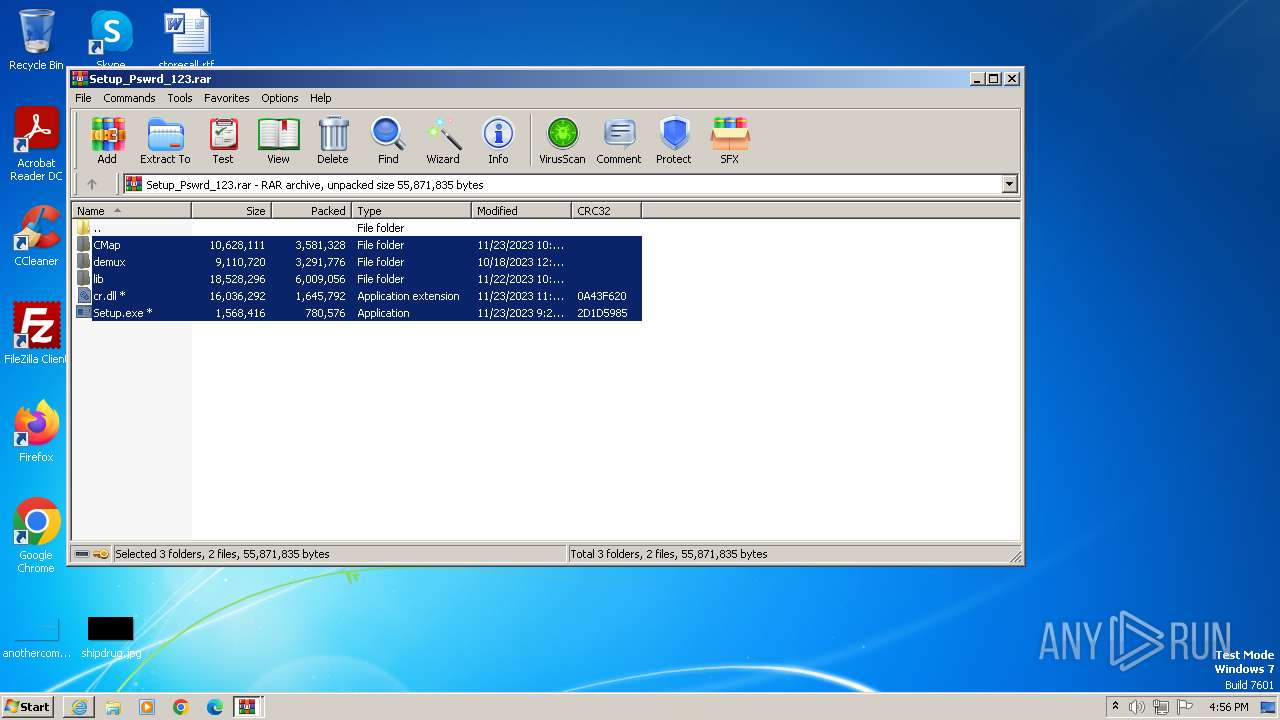
Reads the Internet Settings
- Setup.exe (PID: 2668)
Starts CMD.EXE for commands execution
- Setup.exe (PID: 2668)
INFO
Application launched itself
- iexplore.exe (PID: 888)
Reads the computer name
- wmpnscfg.exe (PID: 1128)
- Setup.exe (PID: 2668)
Checks supported languages
- wmpnscfg.exe (PID: 1128)
- Setup.exe (PID: 2668)
Manual execution by a user
- wmpnscfg.exe (PID: 1128)
- Setup.exe (PID: 2668)
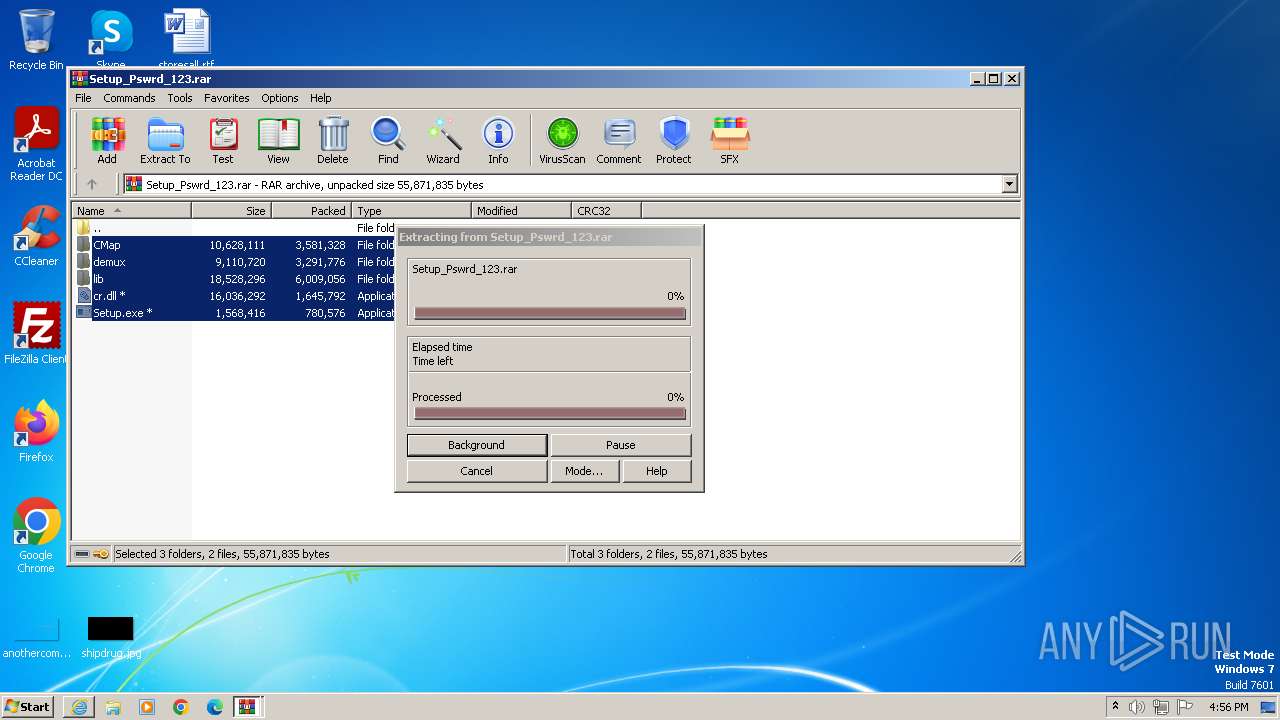
The process uses the downloaded file
- WinRAR.exe (PID: 1064)
- iexplore.exe (PID: 888)
Reads the machine GUID from the registry
- wmpnscfg.exe (PID: 1128)
- Setup.exe (PID: 2668)
Drops the executable file immediately after the start
- WinRAR.exe (PID: 944)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
49
Monitored processes
10
Malicious processes
0
Suspicious processes
2
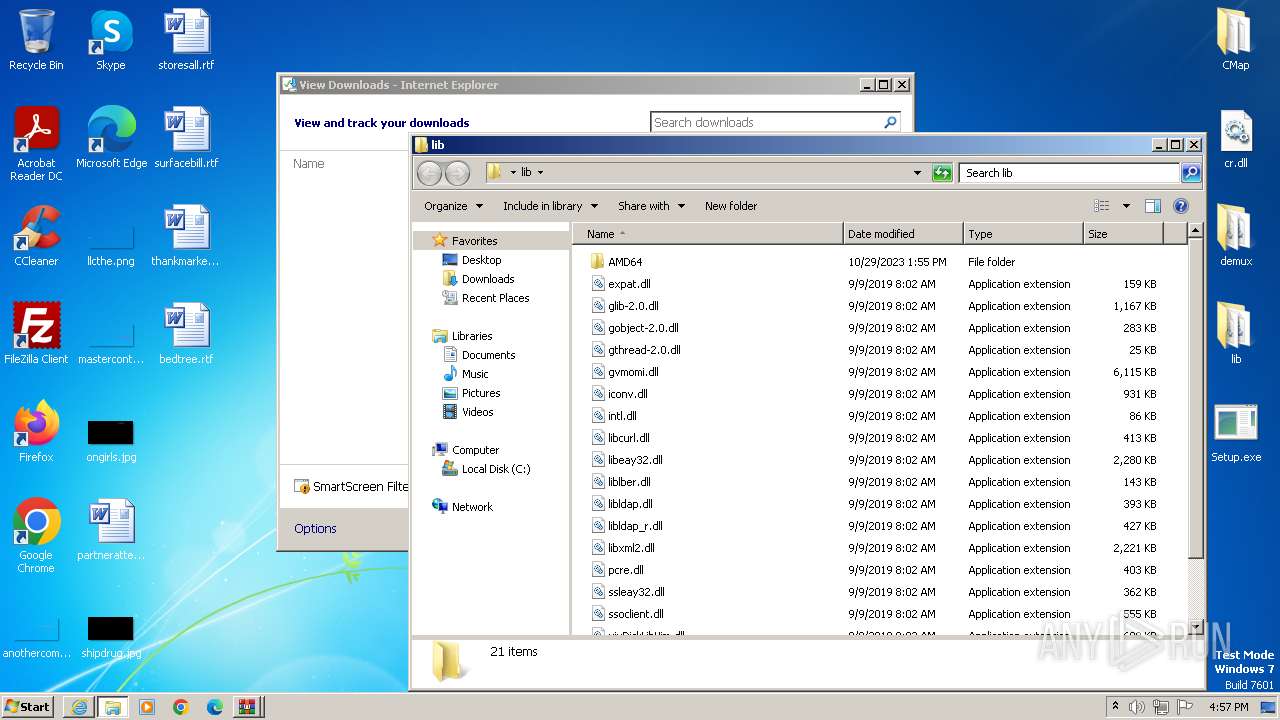
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 880 | ipconfig /renew | C:\Windows\System32\ipconfig.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: IP Configuration Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
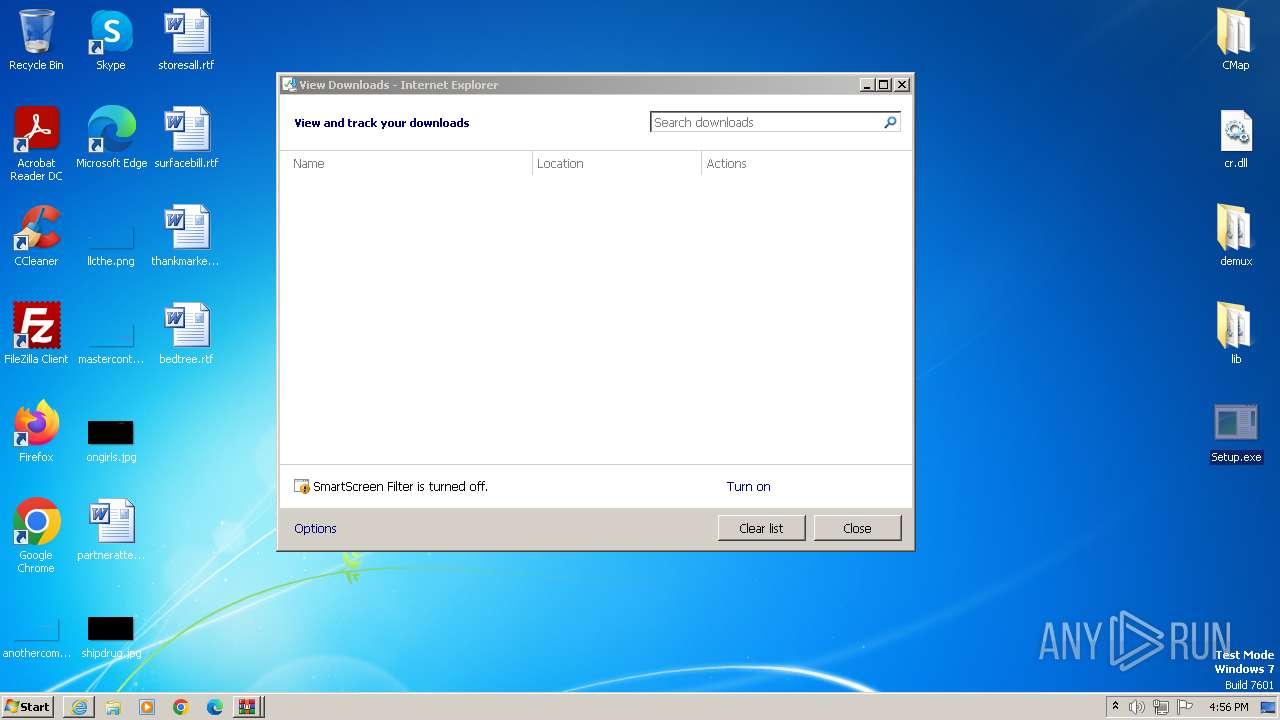
| 888 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://download2355.mediafire.com/7qzv47ul3vzgvQfpHn6RFmgSvshyxuqIvrke1l6HHB9aIkfEr8B5e9ZZIjn1nomBTG7iInHiZFkDn5BgCf4z44rfcBtI7k2rfRtdCazRAsY7xPIlG6QYKV5R1sN5H9ZkiJTiCzr3qn9PTLMeLfj33i1ELwnsFhzuHMS6tiB9U5aQww/ou388wisa9rb0an/Setup_Pswrd_123.rar" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
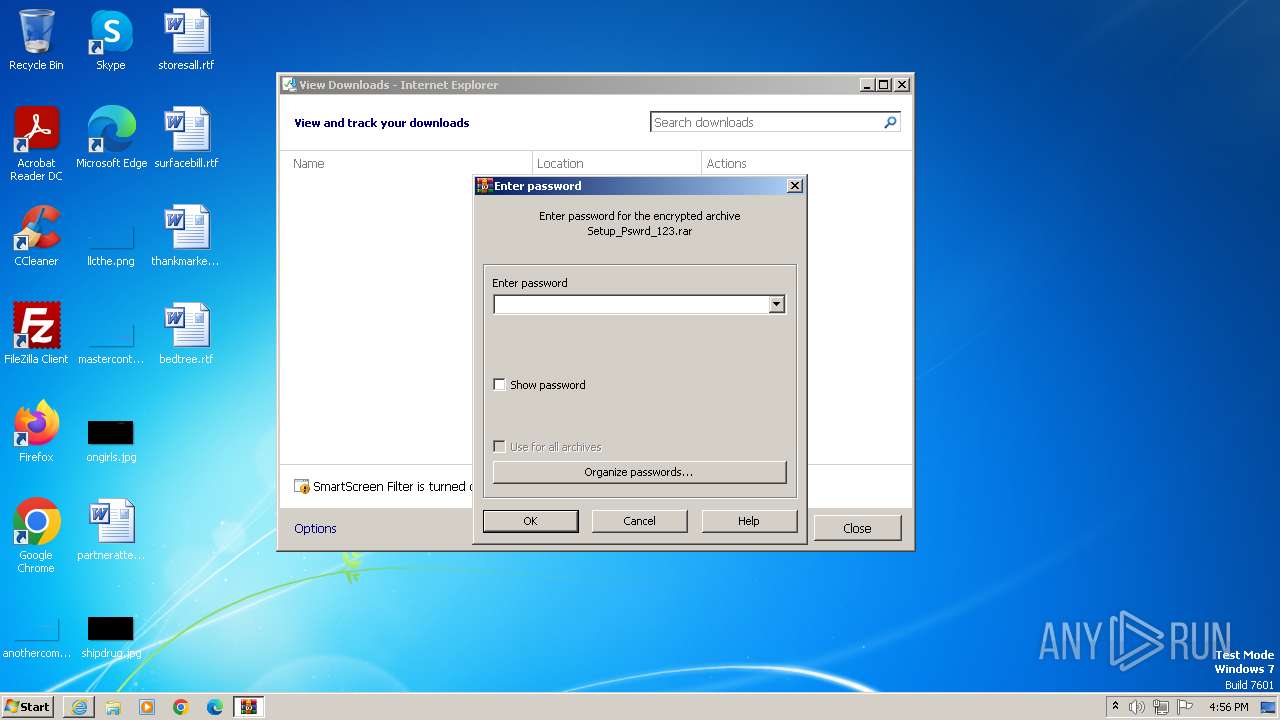
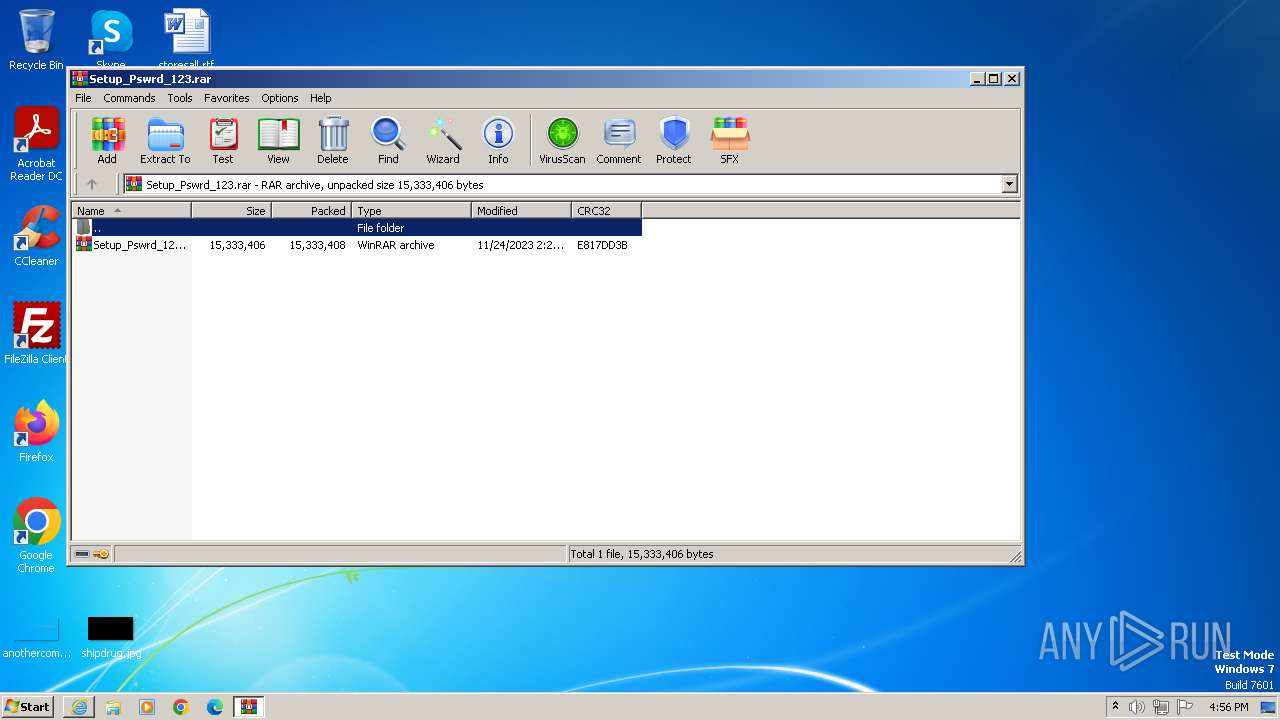
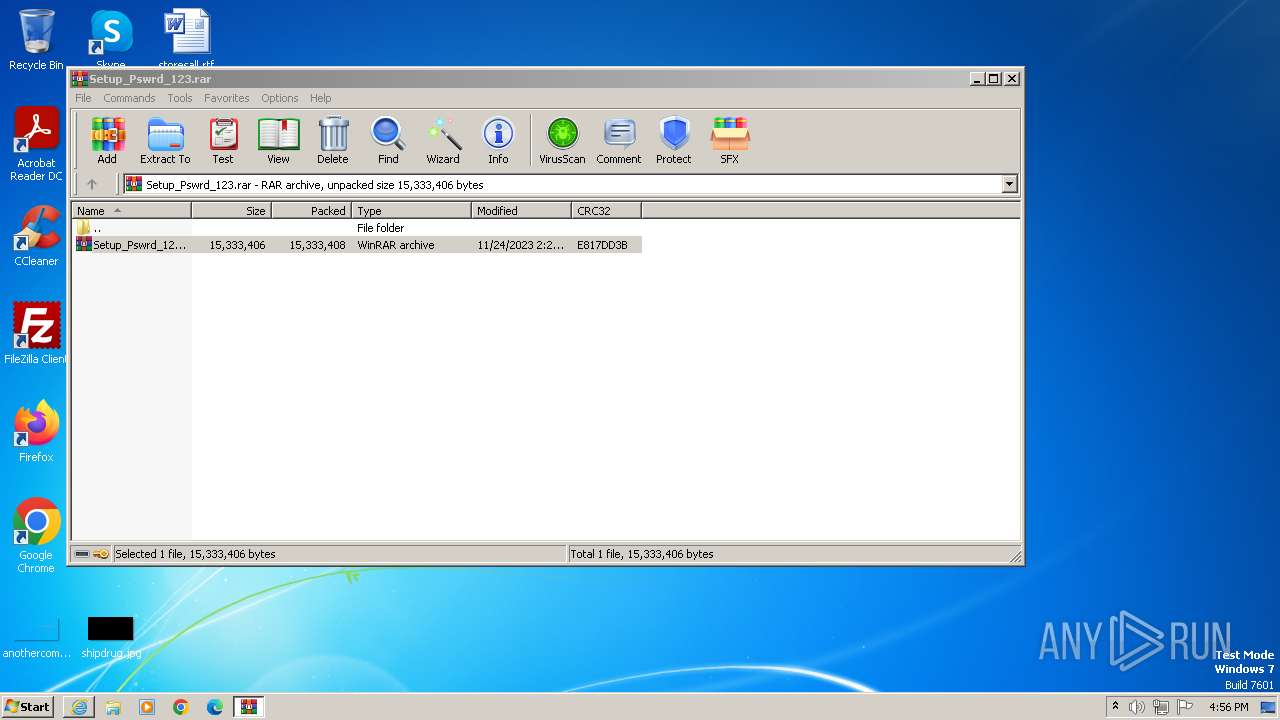
| 944 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\Rar$DIb1064.38294\Setup_Pswrd_123.rar | C:\Program Files\WinRAR\WinRAR.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 1064 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\Setup_Pswrd_123.rar" | C:\Program Files\WinRAR\WinRAR.exe | — | iexplore.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 1128 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2496 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:888 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2668 | "C:\Users\admin\Desktop\Setup.exe" | C:\Users\admin\Desktop\Setup.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3044 | "C:\Windows\System32\cmd.exe" /c ipconfig /renew | C:\Windows\System32\cmd.exe | — | Setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3112 | "C:\Windows\System32\cmd.exe" /c ipconfig /release | C:\Windows\System32\cmd.exe | — | Setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3208 | ipconfig /release | C:\Windows\System32\ipconfig.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: IP Configuration Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
19 644
Read events
19 553
Write events
88
Delete events
3
Modification events
| (PID) Process: | (888) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (888) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (888) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (888) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (888) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (888) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (888) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (888) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (888) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (888) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
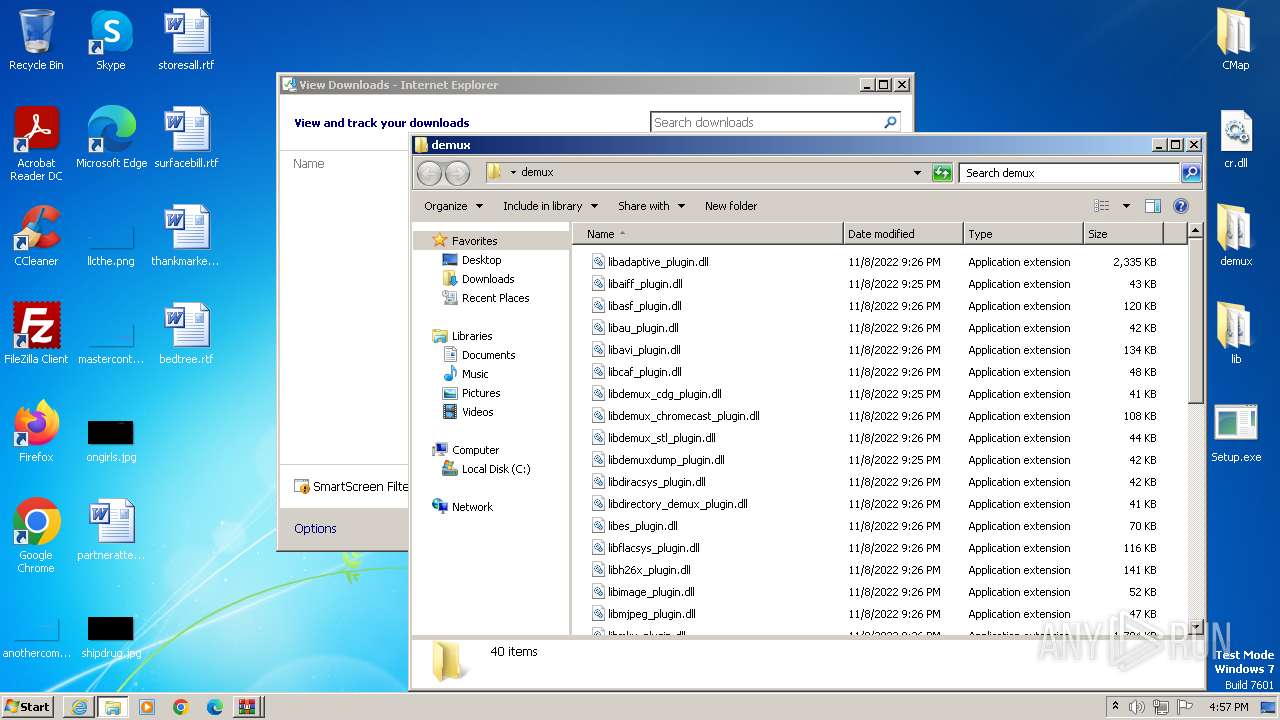
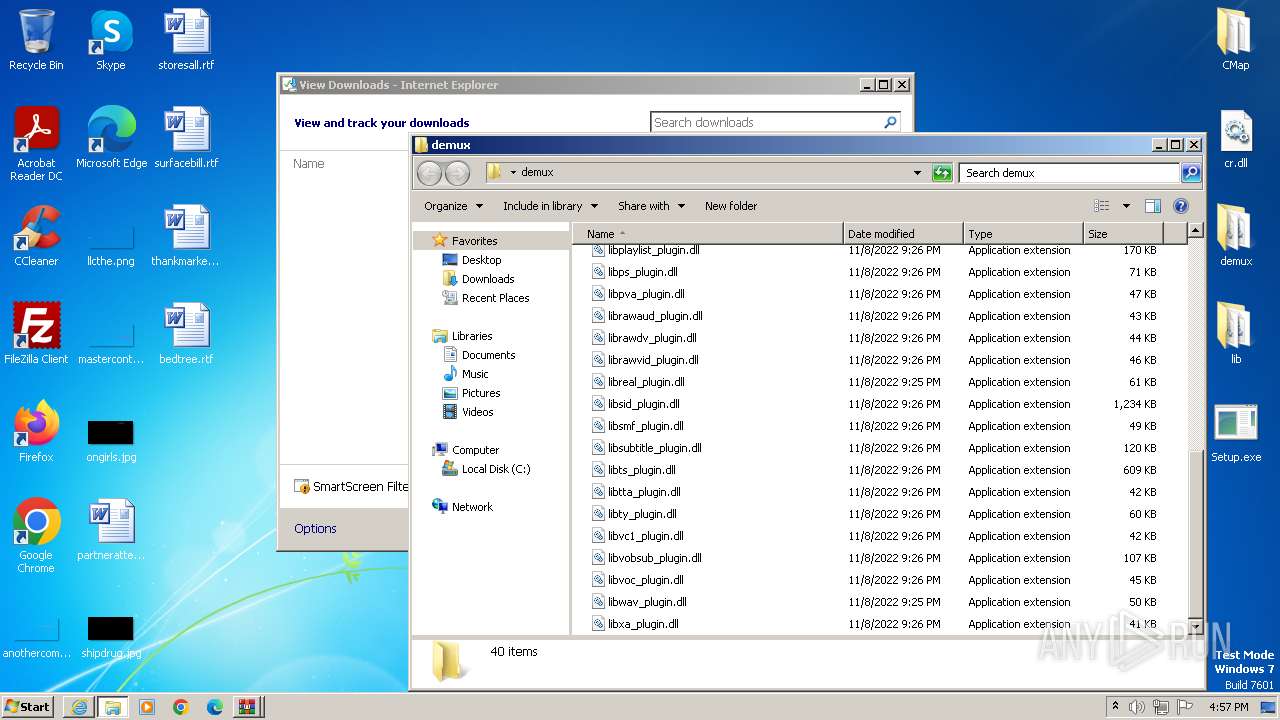
Executable files
68
Suspicious files
31
Text files
7
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2496 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\Setup_Pswrd_123.rar.r0b8hz3.partial | — | |
MD5:— | SHA256:— | |||
| 888 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\Setup_Pswrd_123.rar | — | |
MD5:— | SHA256:— | |||
| 1064 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIb1064.38294\Setup_Pswrd_123.rar | — | |
MD5:— | SHA256:— | |||
| 2496 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\Setup_Pswrd_123[1].rar | compressed | |
MD5:6A955E5114D7F97C30DFA828B62E0662 | SHA256:4F0FEFFAD18FAC1DBB6E1C6067491E0BDCCD74B759DBF499B0FE9C487CB9324C | |||
| 2496 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\07CEF2F654E3ED6050FFC9B6EB844250_BACC6CD2B29F18349081C9FD2343833B | binary | |
MD5:D4A0F7FF41E06E4B4BBBF7E6C79709B4 | SHA256:A7CC499F53C7CB985C05AC6F040DC63E0A3D67E91E08F21DB400DD5BA116EE30 | |||
| 2496 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\07CEF2F654E3ED6050FFC9B6EB844250_BACC6CD2B29F18349081C9FD2343833B | binary | |
MD5:5DFA098E5A43E7F6D53A37A7A56F4A72 | SHA256:7AEBB2948E43040E99ED008DB318C24B35F2BF218FED46D632843EECF3792E07 | |||
| 888 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF5FB676BA5D09F4AD.TMP | binary | |
MD5:CDAD7B09B54CEF9B53DD4894AE518D75 | SHA256:13471558FC23C90BB16F3C17C2136744DA832653ABFEE9F7177C7F2C2599E894 | |||
| 2496 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\72BA427A91F50409B9EAC87F2B59B951_8FD6BB79A5EEF06F3F8595CB48A9AB04 | binary | |
MD5:2EB7C99210C23D343133FE1436D3FFD2 | SHA256:D6656E0696AAB30920A1DA0675223B6A85574E5A9039C836B4A4F575512097AC | |||
| 2496 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\72BA427A91F50409B9EAC87F2B59B951_8FD6BB79A5EEF06F3F8595CB48A9AB04 | binary | |
MD5:A7B815E7B8B30A3F76DBE86F506D7D2D | SHA256:DB3307A332A1A974FBEFEBD7C7751673B70E56883E13A64305F9ABA7ECCBE719 | |||
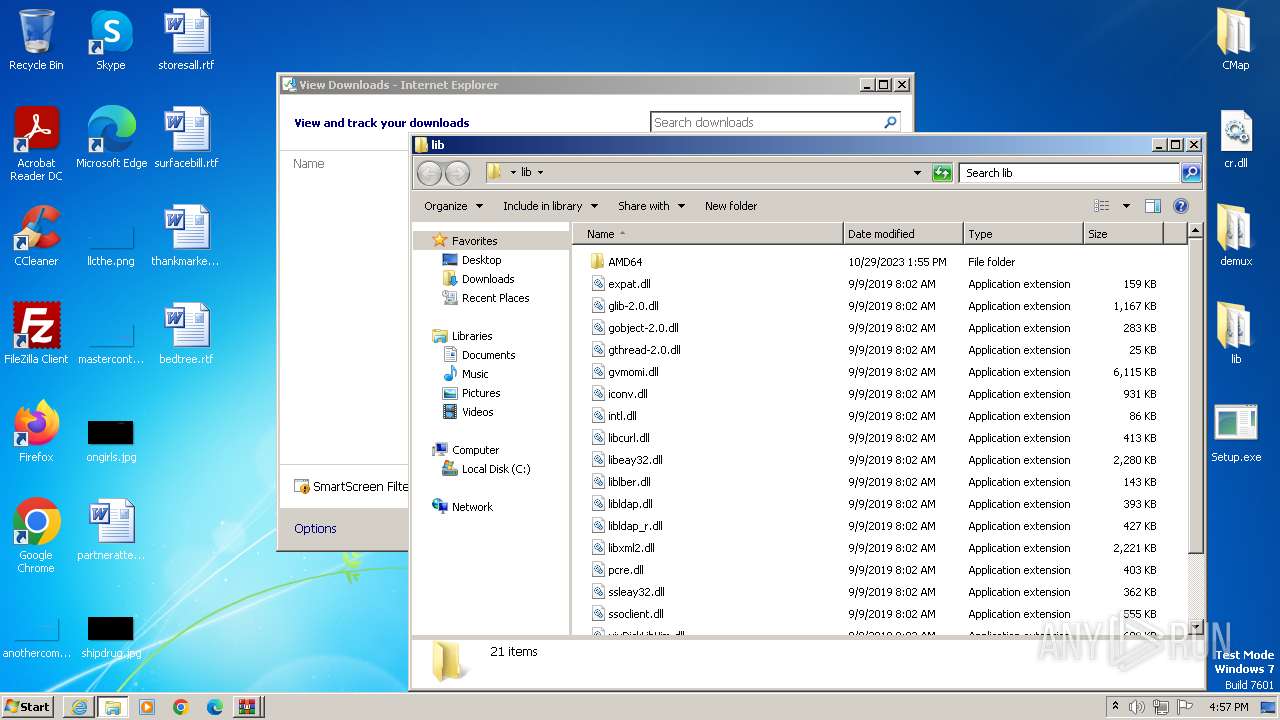
| 944 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb944.38823\demux\libasf_plugin.dll | executable | |
MD5:ADB40CE292245AC624CDB1ABEC8E253B | SHA256:882C9DEA7C3E1EF25848814FEE8E9AA591F9AFDC1A46270E0D5F702B0EBCAD7D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
15
DNS requests
8
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2496 | iexplore.exe | GET | 200 | 184.24.77.203:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?f0029c2e649eb62c | unknown | compressed | 4.66 Kb | unknown |
2496 | iexplore.exe | GET | 200 | 184.24.77.203:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?e569524345d4d114 | unknown | compressed | 4.66 Kb | unknown |
1080 | svchost.exe | GET | 304 | 184.24.77.203:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?5312bc669adcb130 | unknown | — | — | unknown |
888 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | binary | 471 b | unknown |
1080 | svchost.exe | GET | 200 | 184.24.77.203:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?68f52e492152febd | unknown | compressed | 61.6 Kb | unknown |
2496 | iexplore.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEBN9U5yqfDGppDNwGWiEeo0%3D | unknown | binary | 2.18 Kb | unknown |
2496 | iexplore.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.sectigo.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQh80WaEMqmyEvaHjlisSfVM4p8SAQUF9nWJSdn%2BTHCSUPZMDZEjGypT%2BsCED%2B0KeRQ8NP60VP53TIby3A%3D | unknown | binary | 471 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2496 | iexplore.exe | 199.91.155.96:443 | download2355.mediafire.com | MEDIAFIRE | US | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2496 | iexplore.exe | 184.24.77.203:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
2588 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
2496 | iexplore.exe | 104.18.38.233:80 | ocsp.usertrust.com | CLOUDFLARENET | — | shared |
1080 | svchost.exe | 184.24.77.203:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
888 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | EDGECAST | US | whitelisted |
888 | iexplore.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
download2355.mediafire.com |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.usertrust.com |
| whitelisted |
ocsp.sectigo.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1080 | svchost.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain in DNS Lookup (download .mediafire .com) |