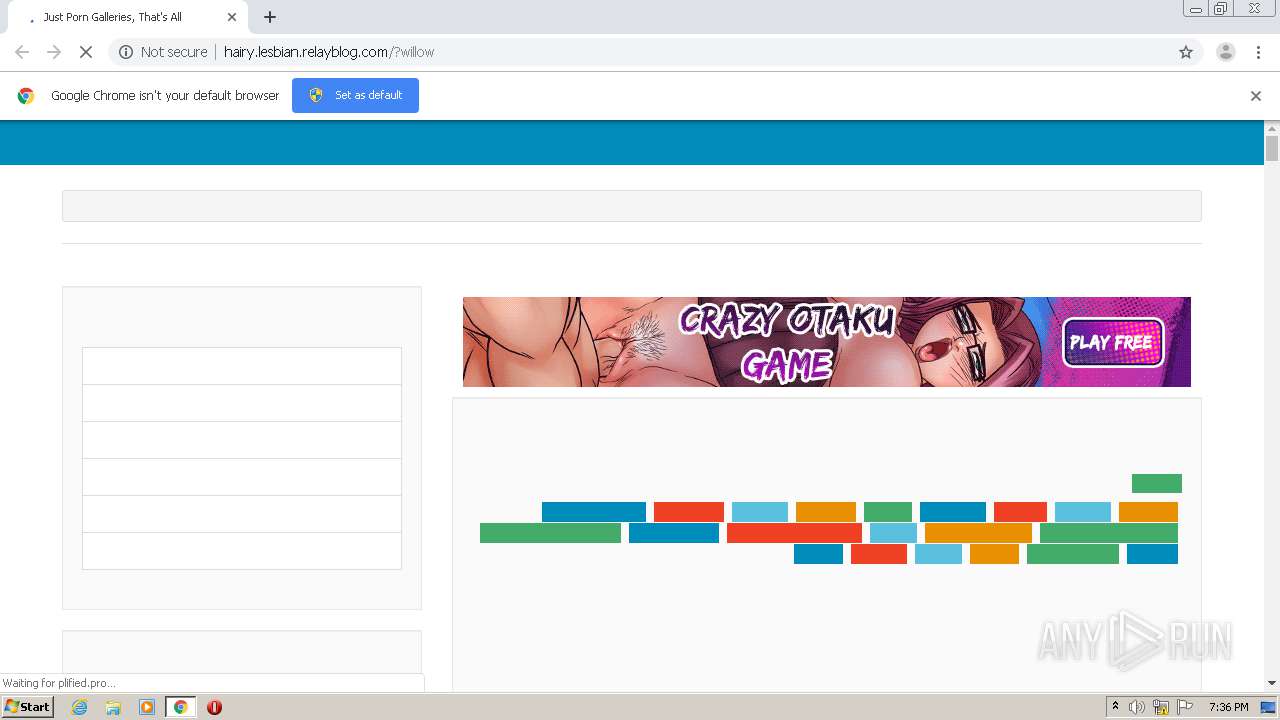
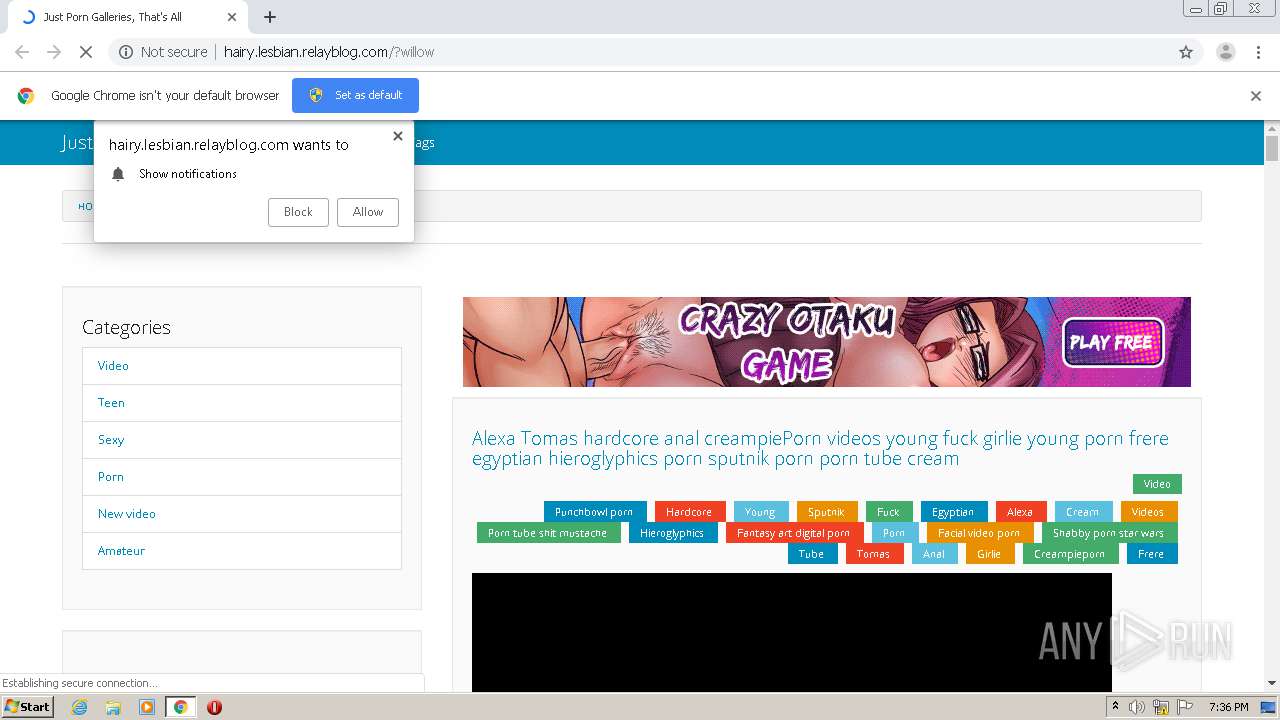
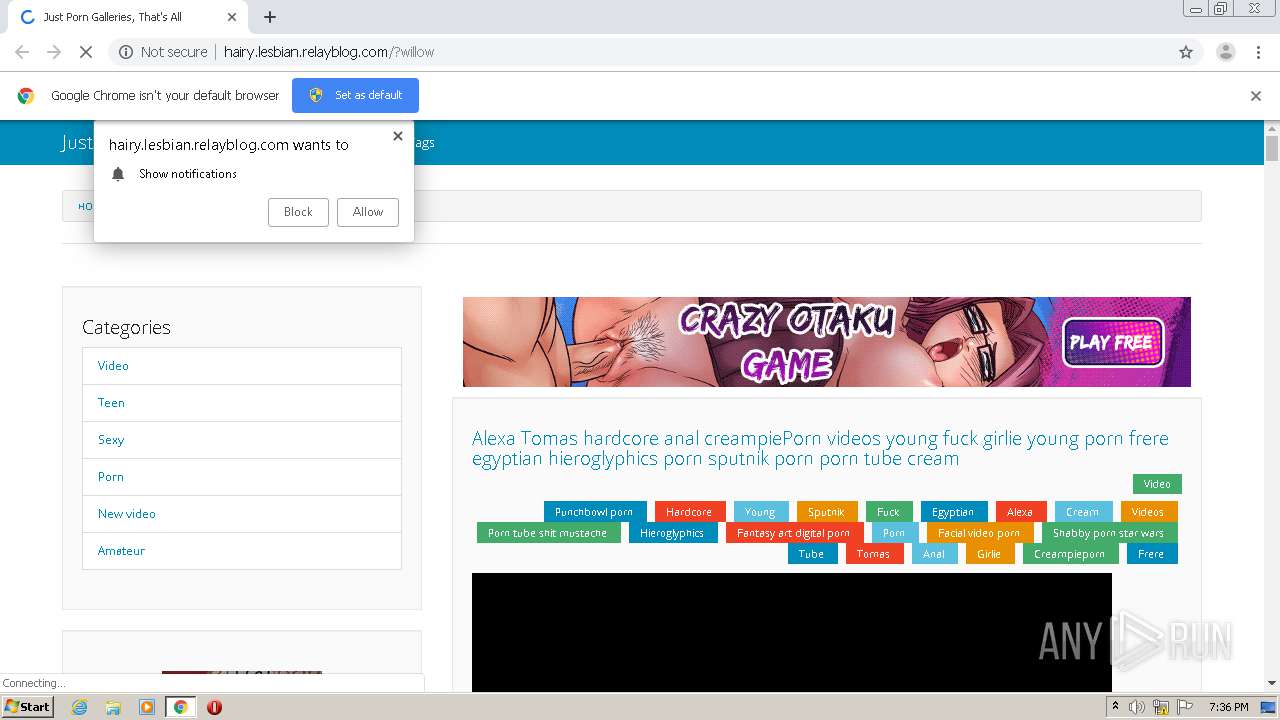
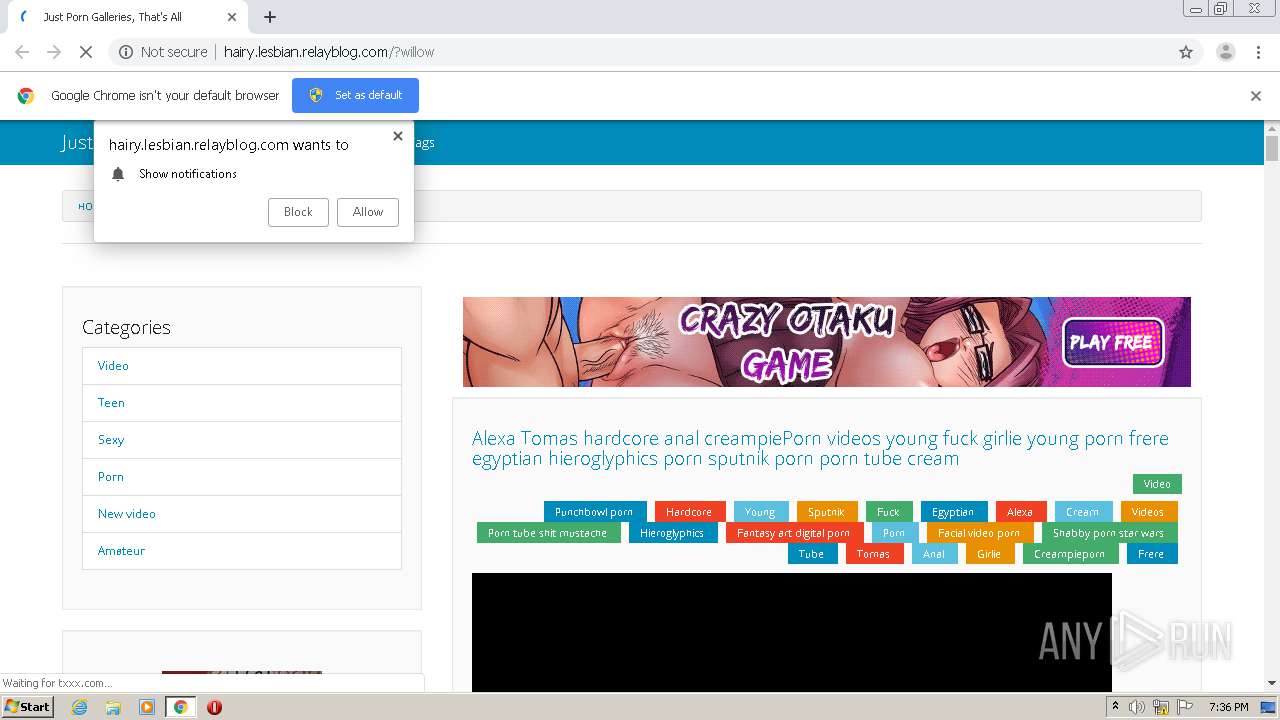
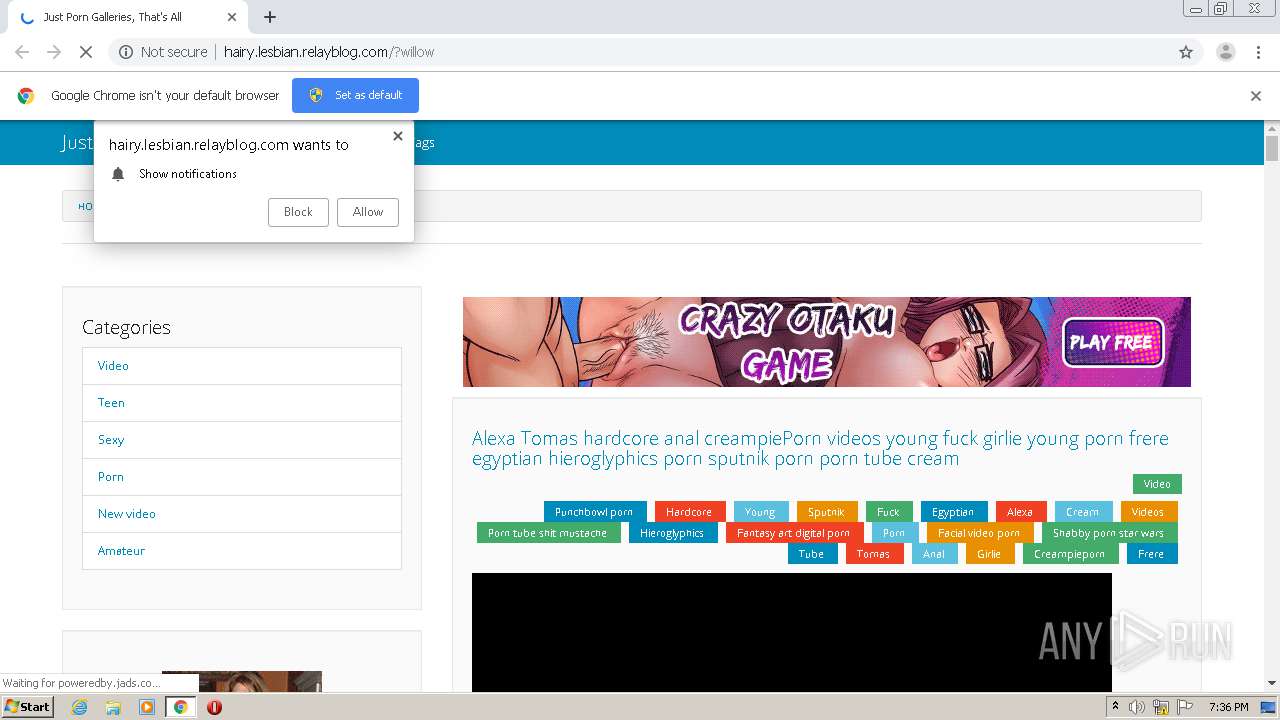
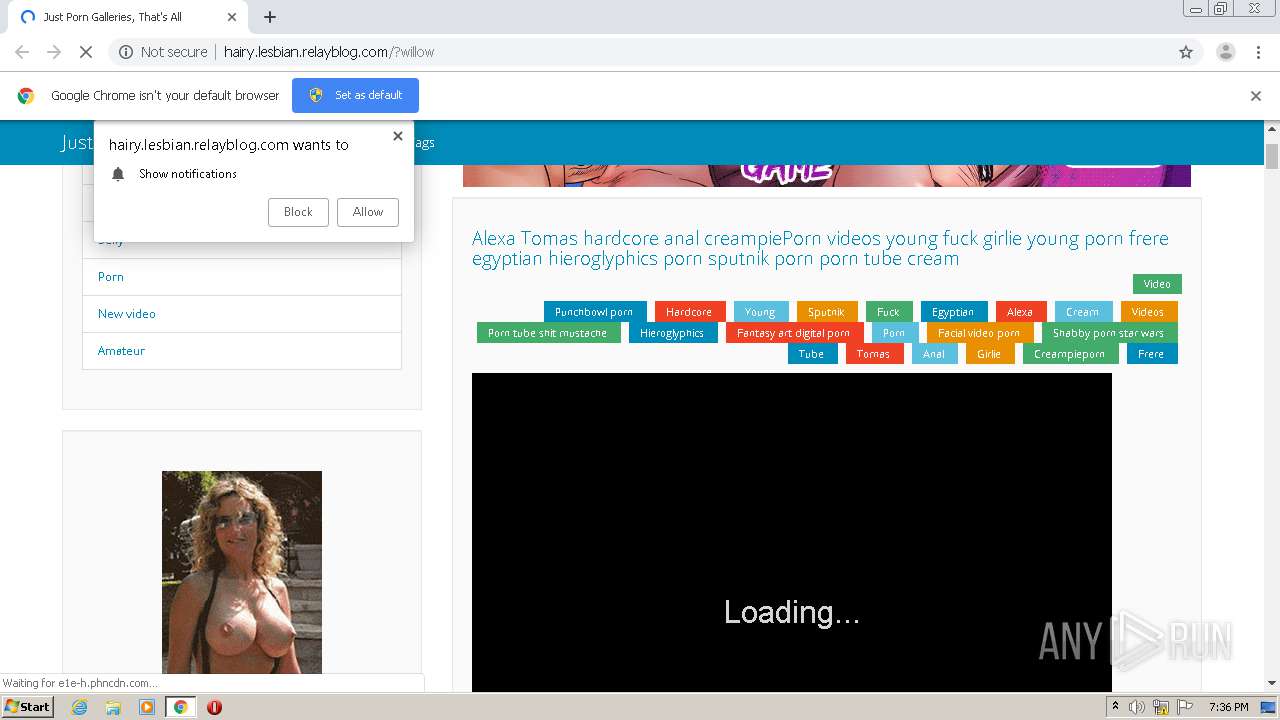
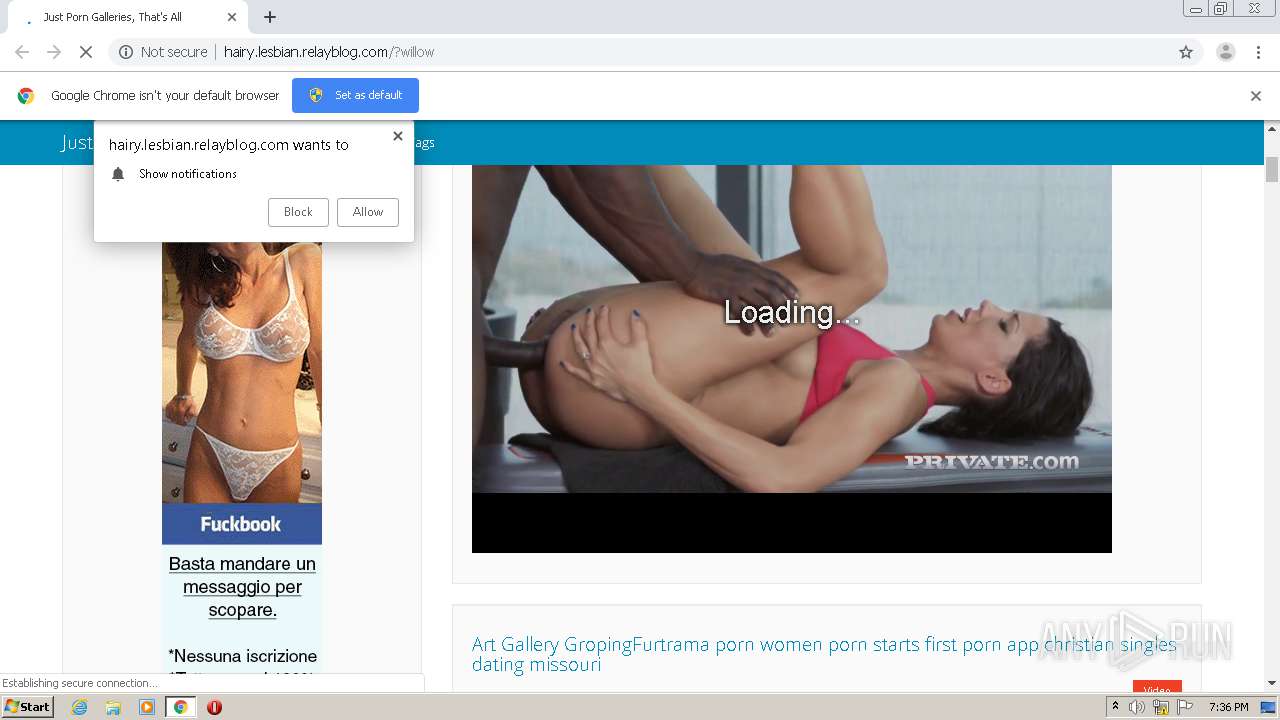
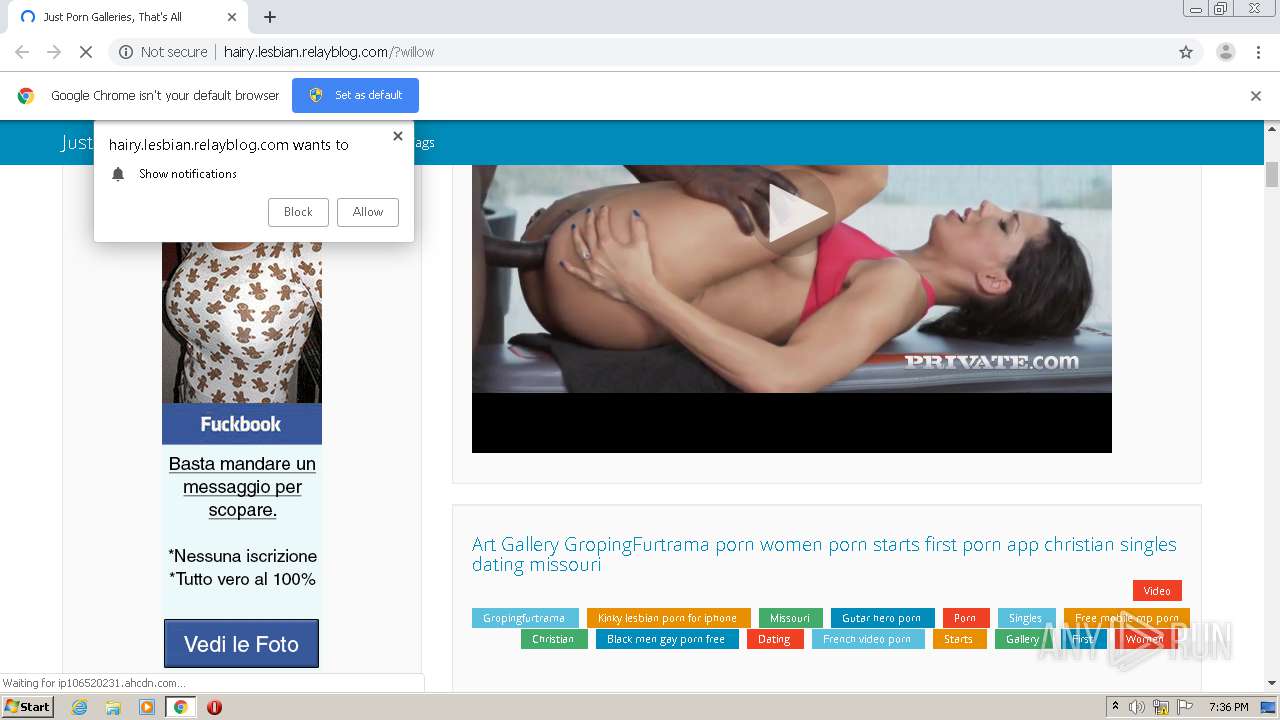
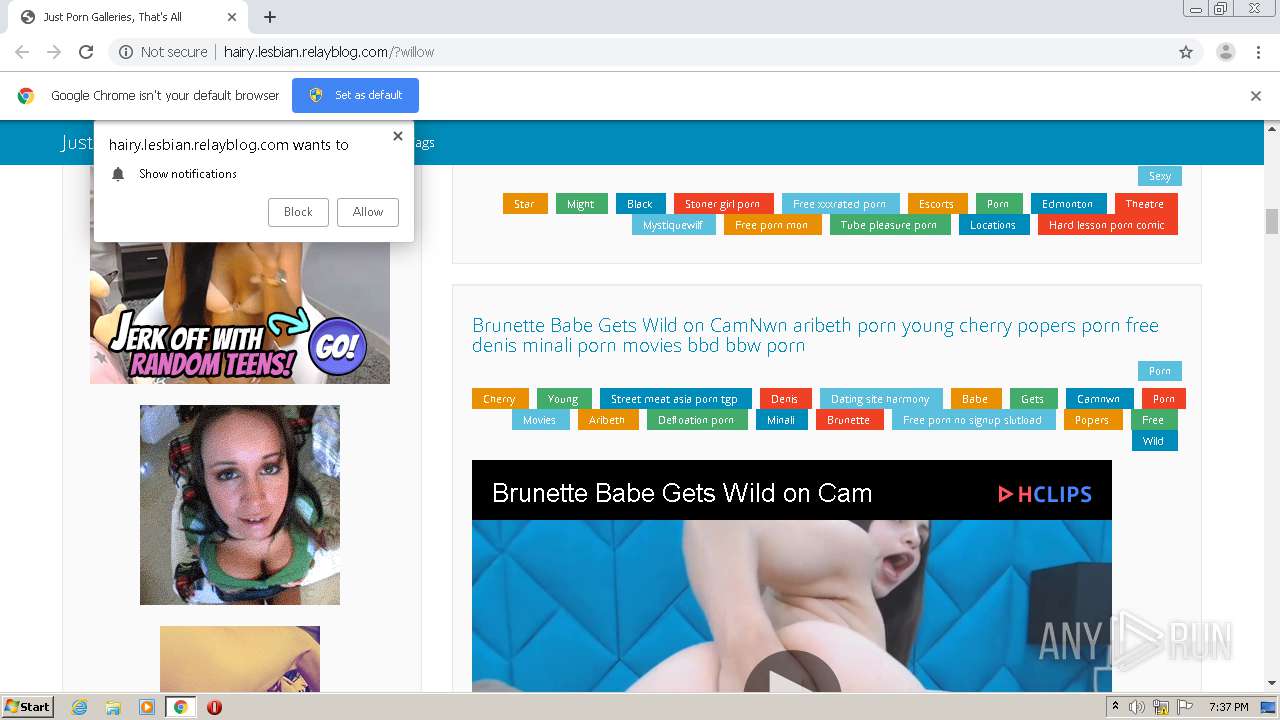
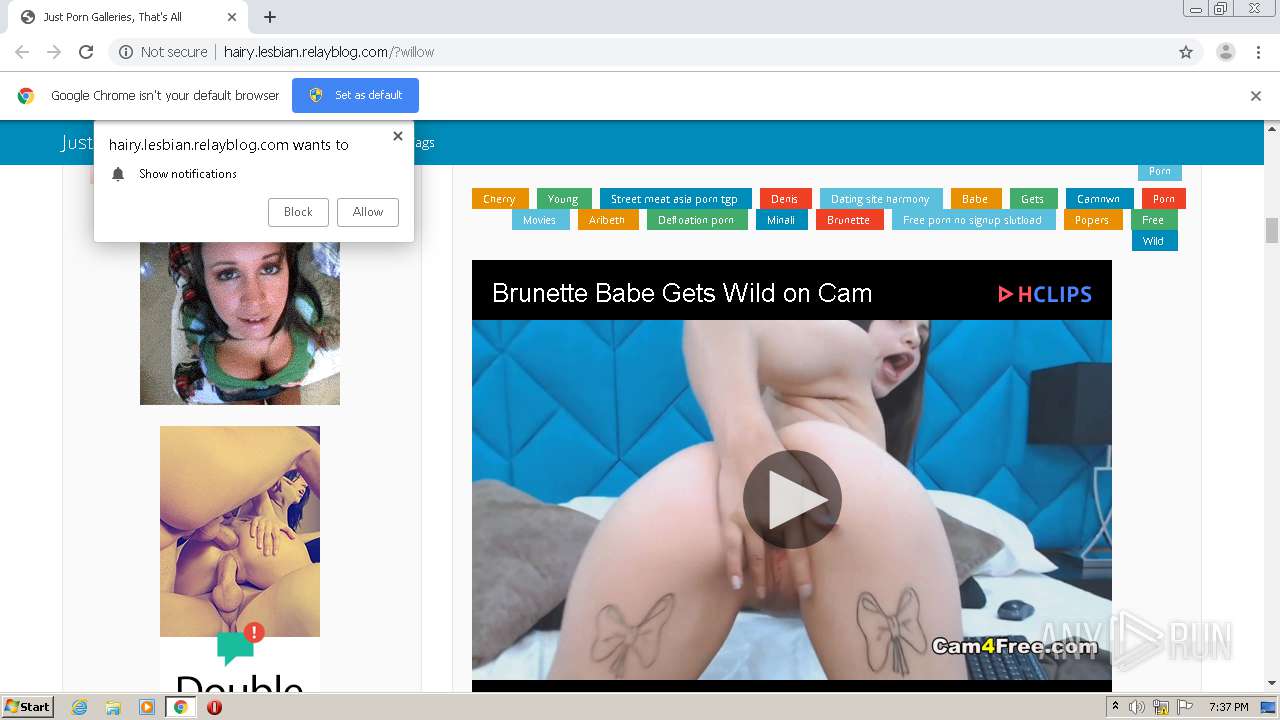
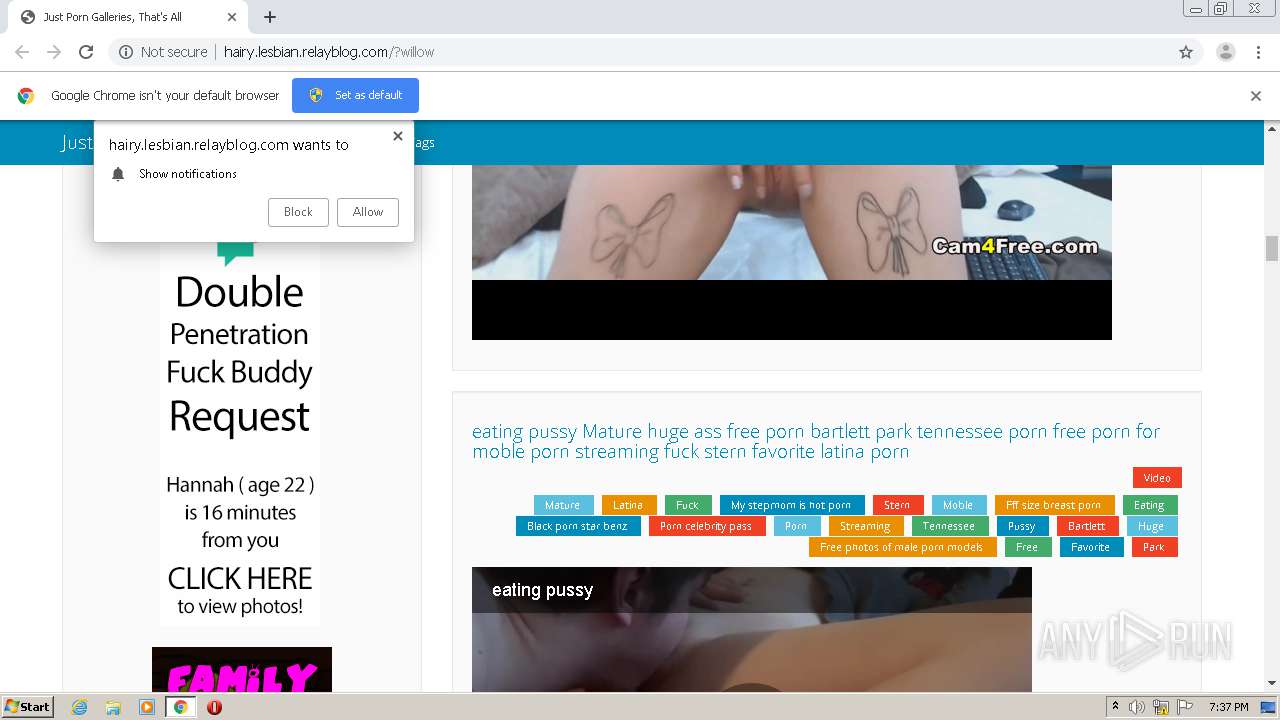
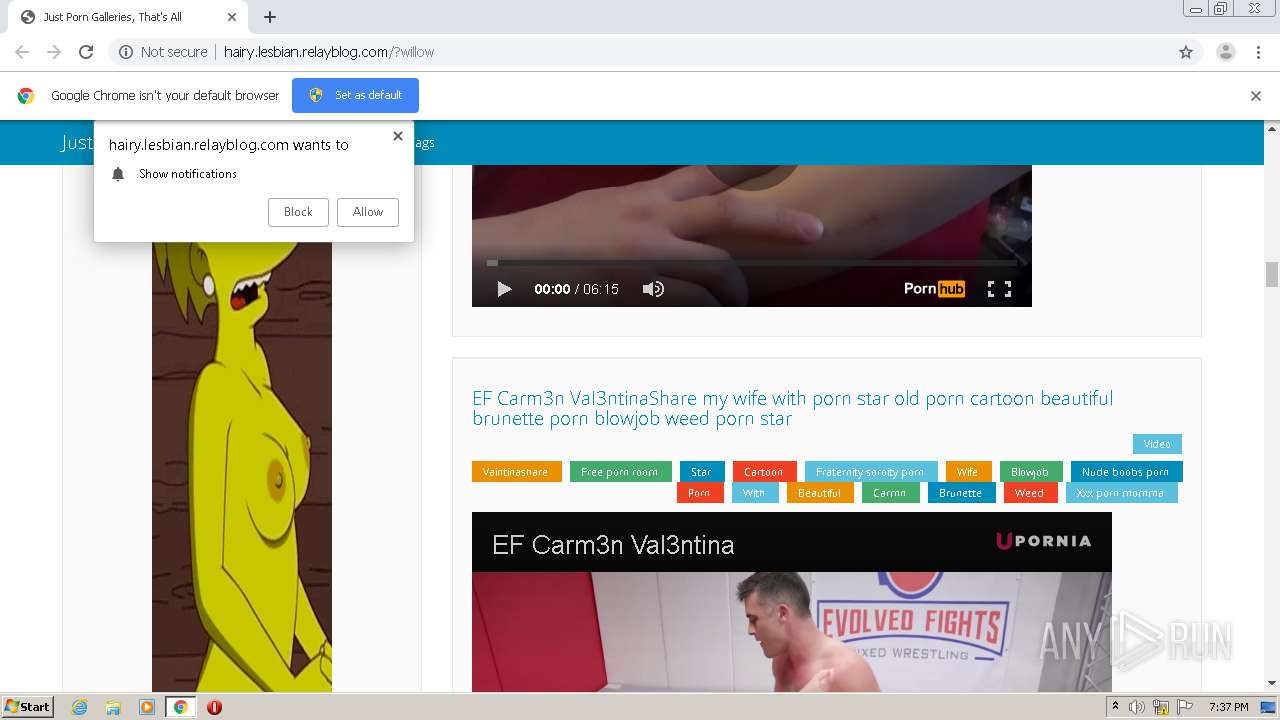
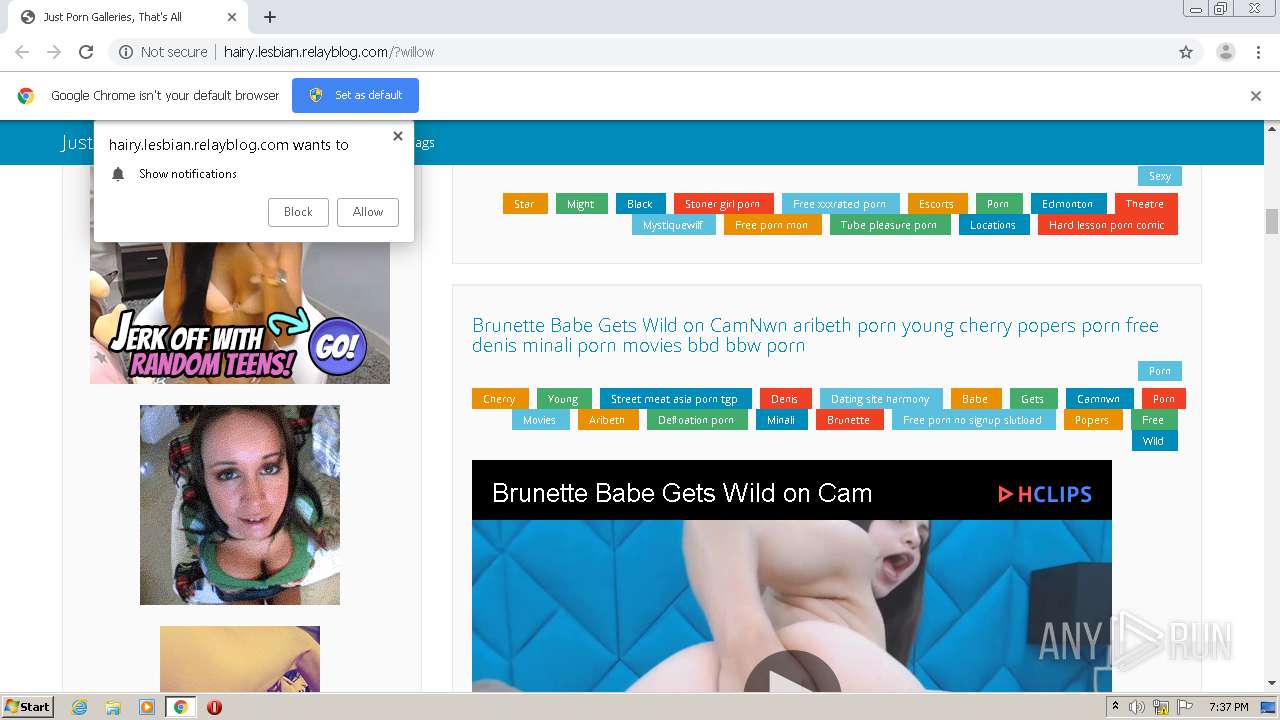
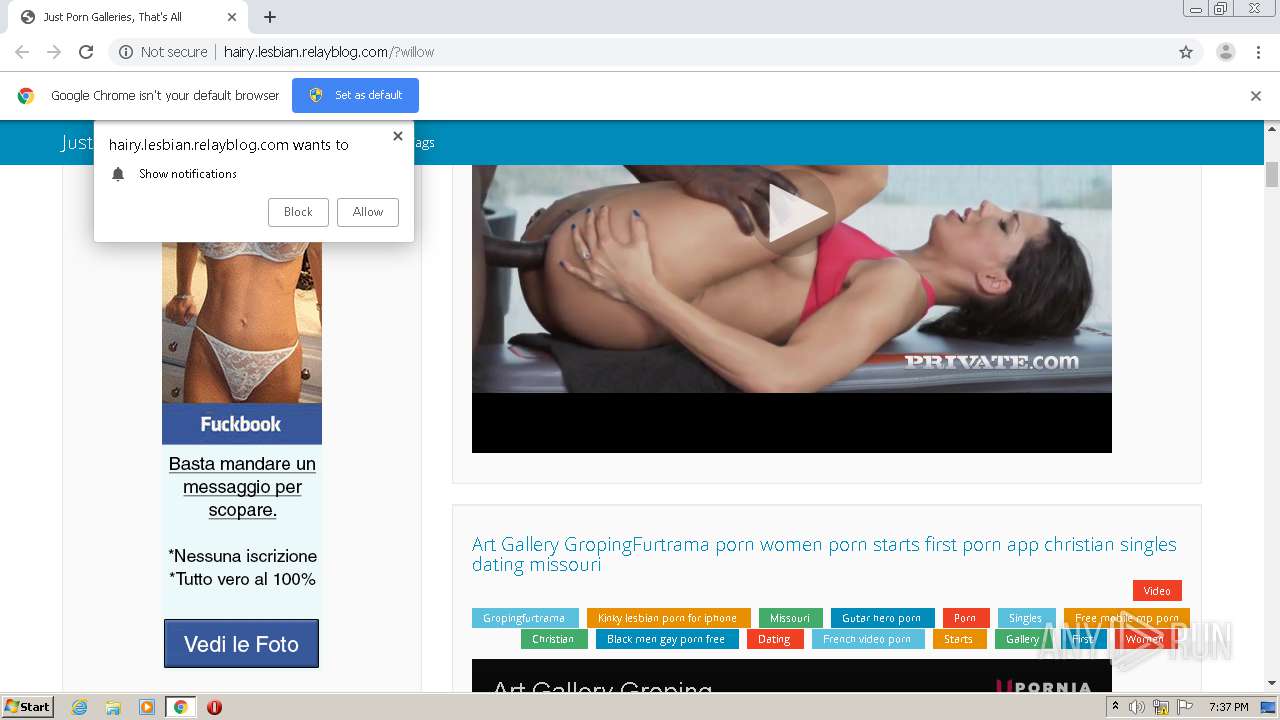
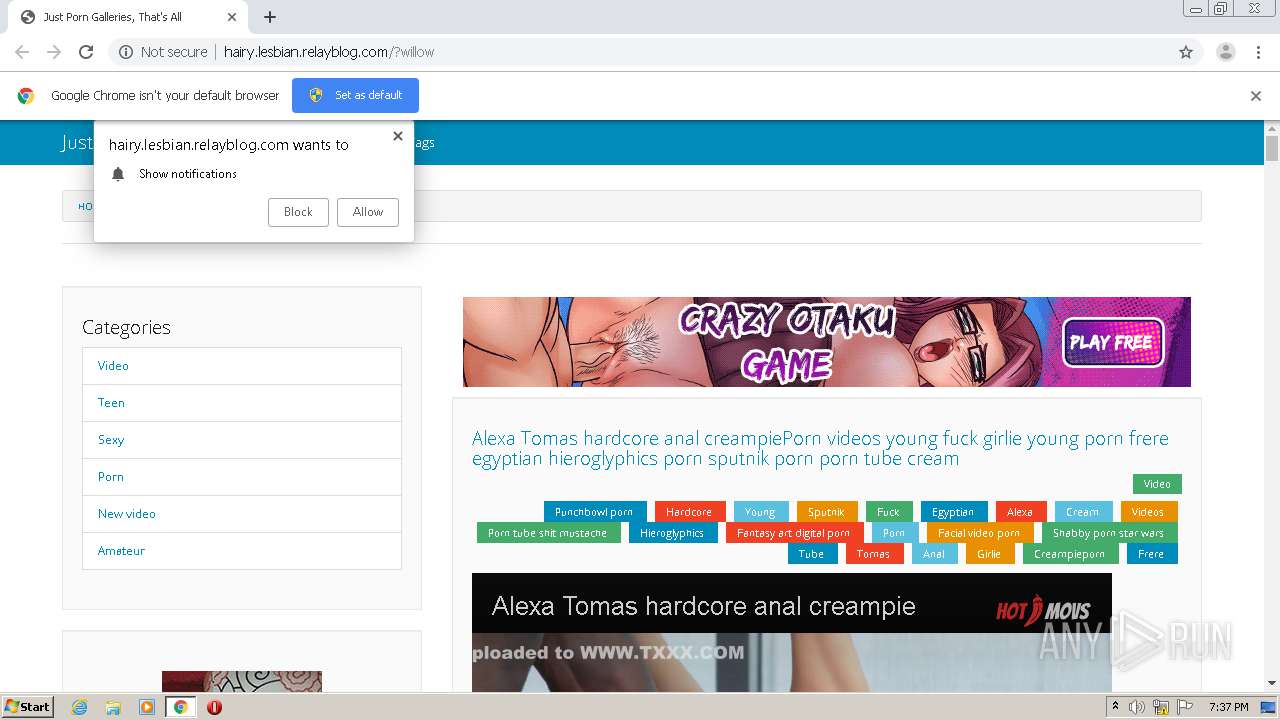
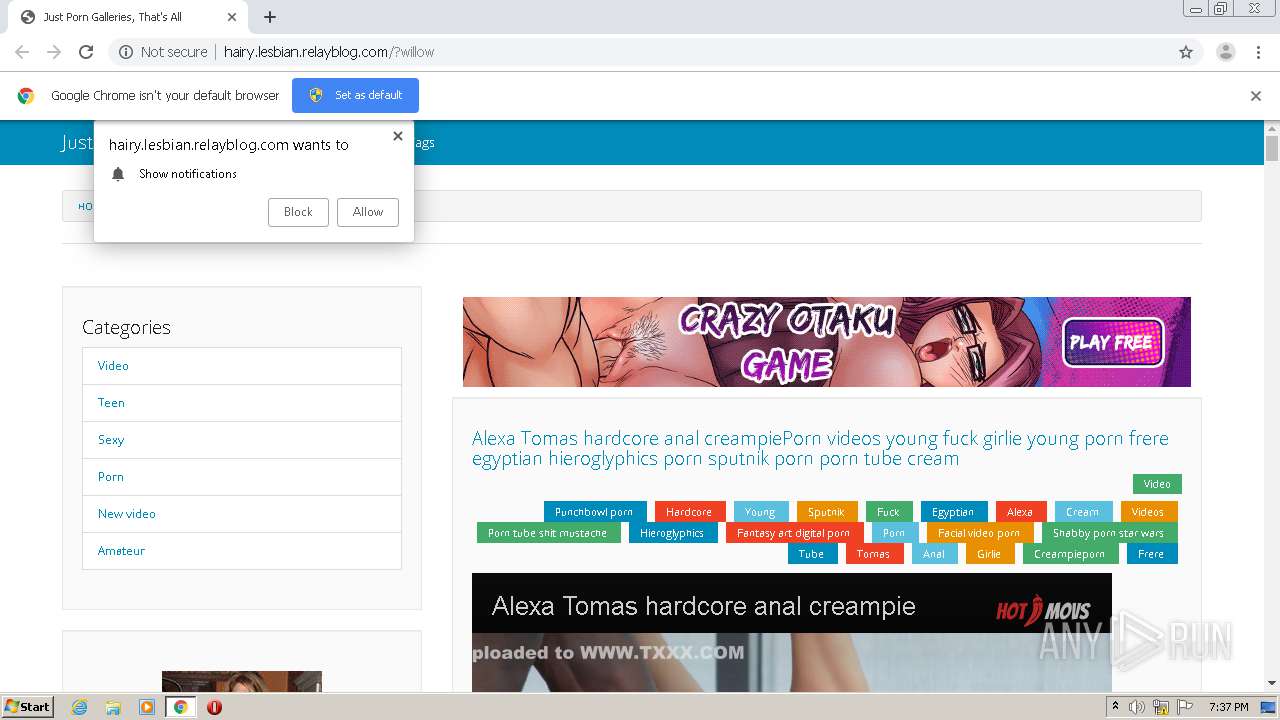
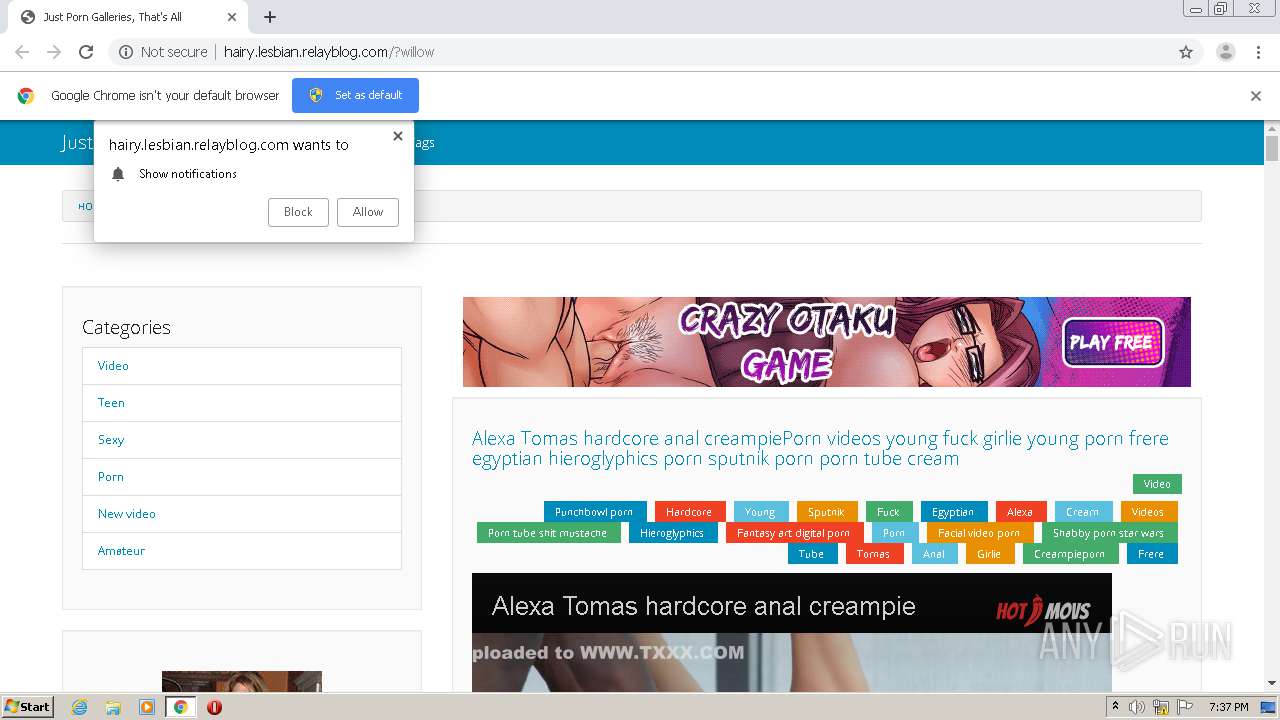
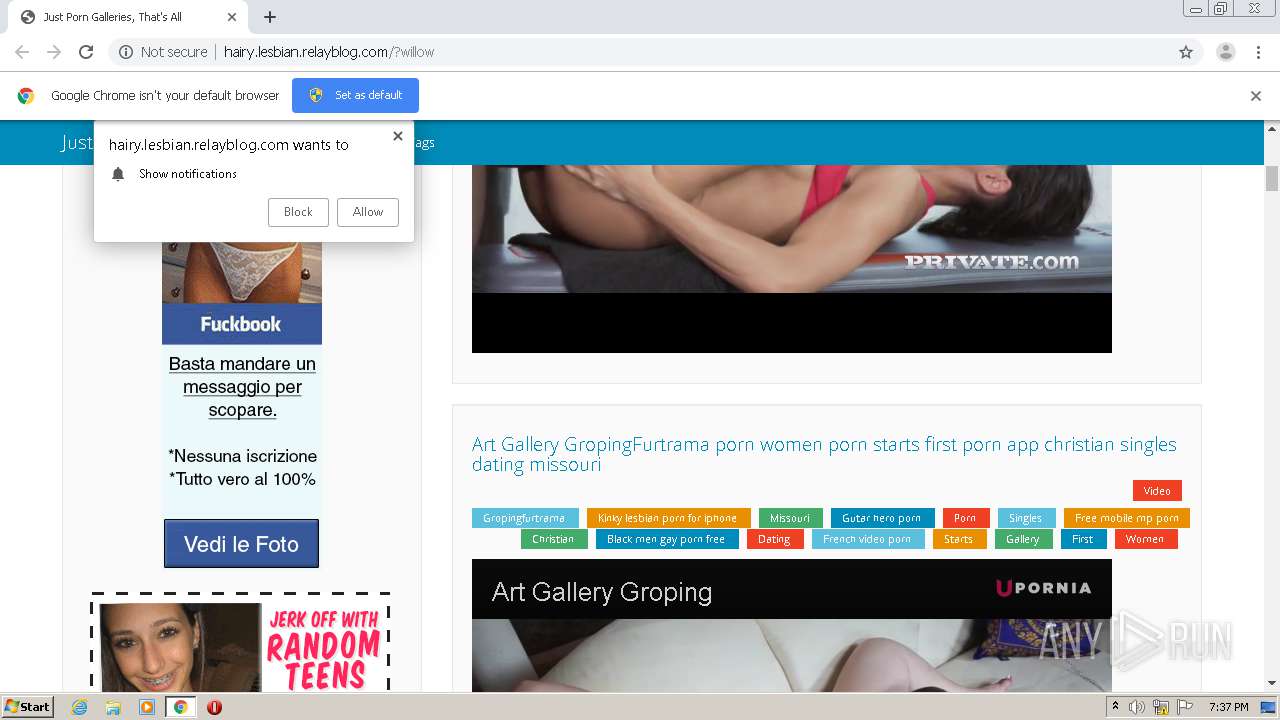
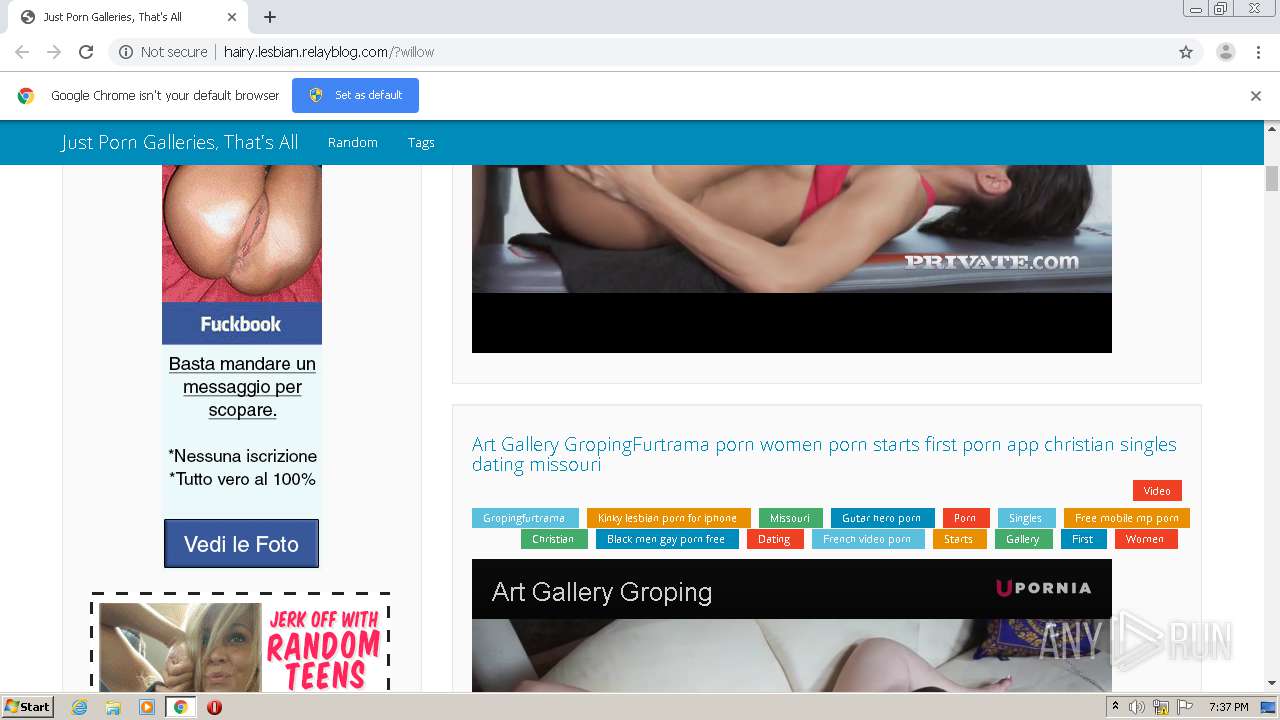
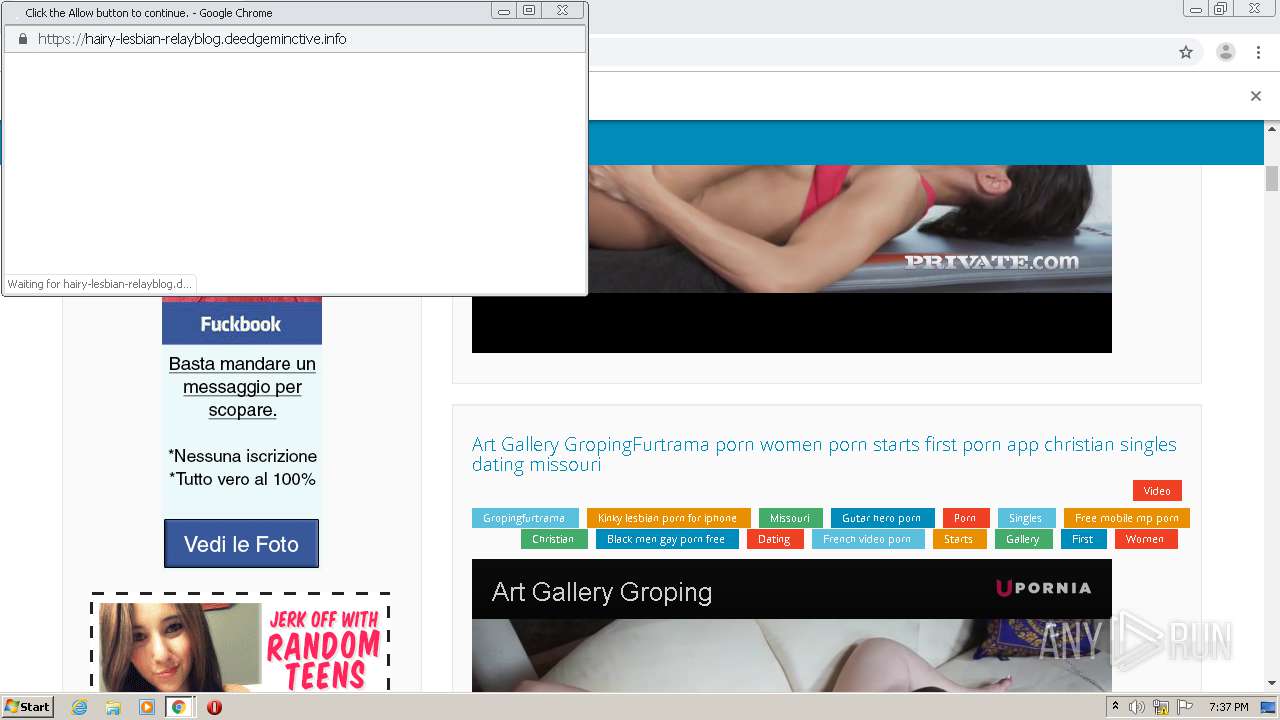
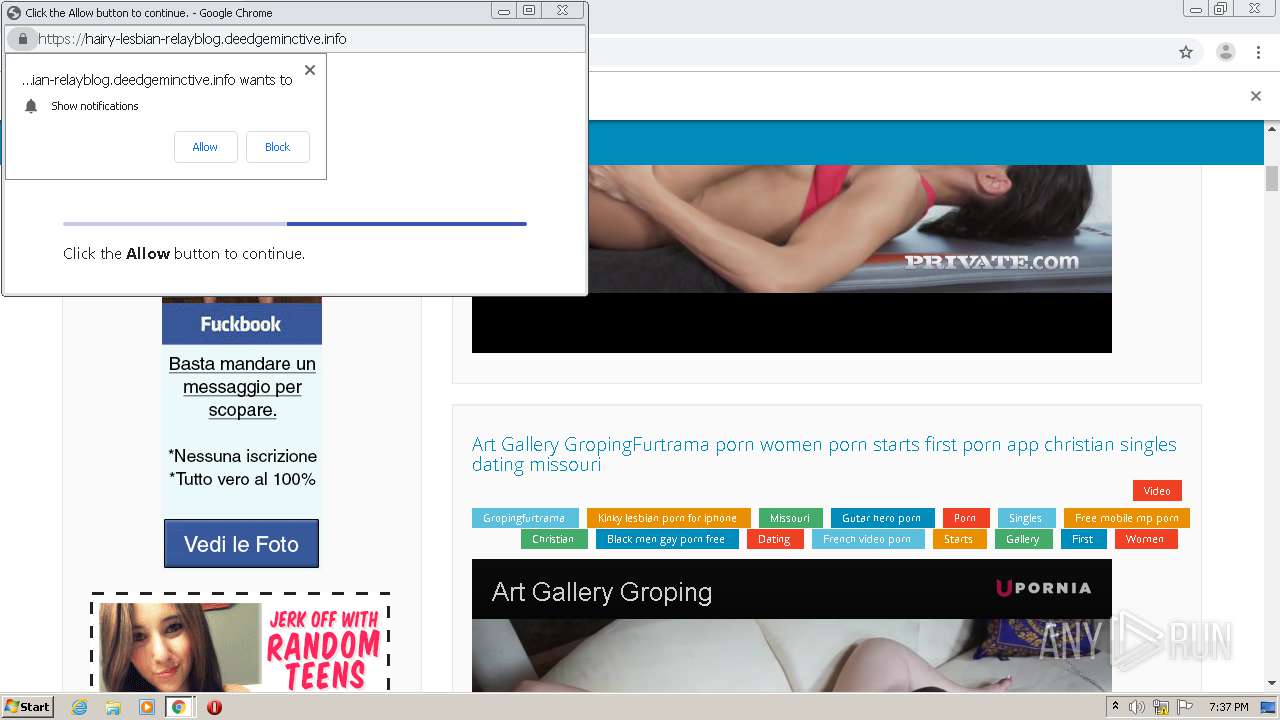
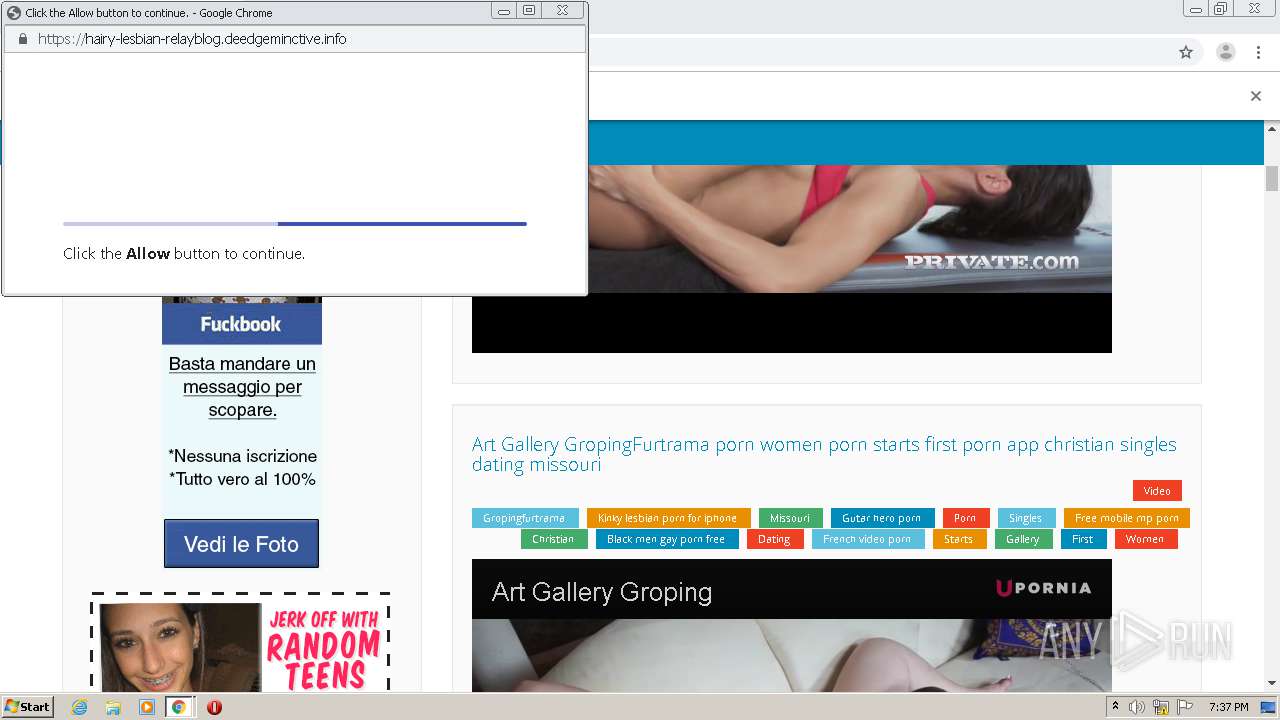
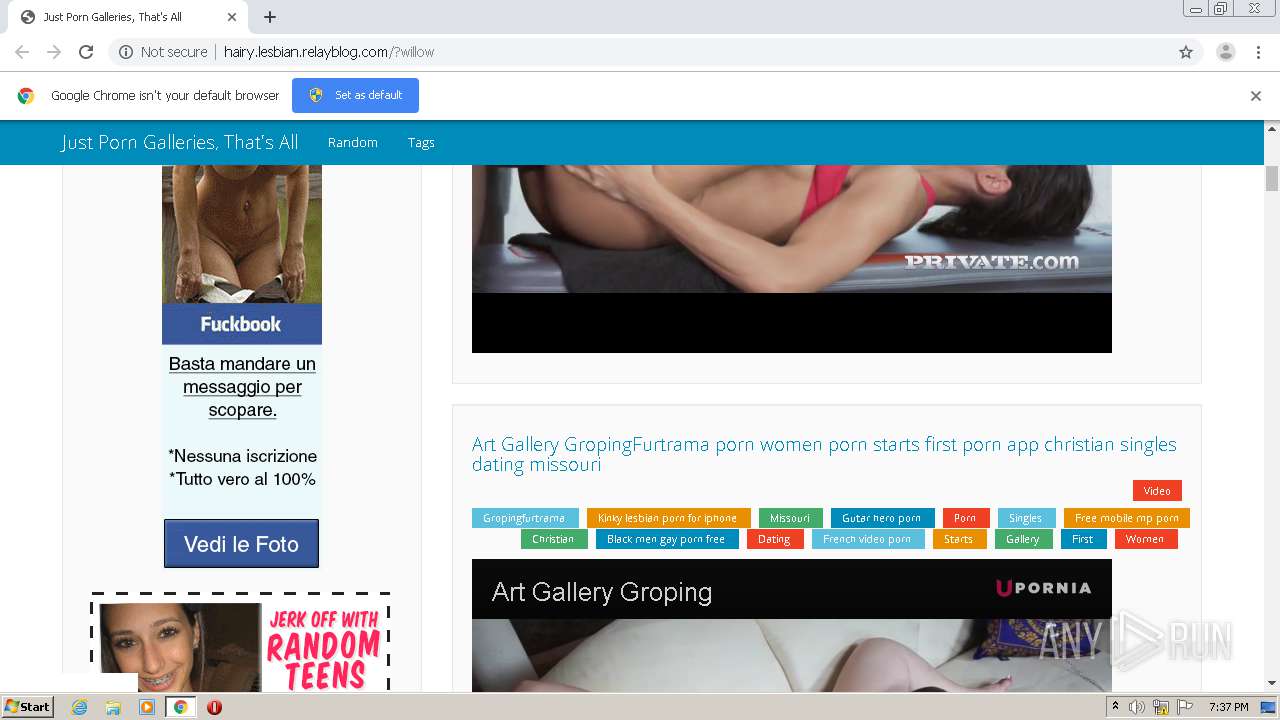
| URL: | http://hairy.lesbian.relayblog.com/?willow |
| Full analysis: | https://app.any.run/tasks/da569bd3-2d29-4290-85b8-4b5137d83c19 |
| Verdict: | Malicious activity |
| Analysis date: | August 31, 2020, 18:36:20 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 0179C3AE308C976A6C9BD06BF8F7DD71 |
| SHA1: | D50C4D3F85EF29A520E31ED032A892D9341F8E14 |
| SHA256: | CD22C6A9D4AFC90FE5B6BA1DD218B9205FAD96333667B62F71EFB4C656F89914 |
| SSDEEP: | 3:N1KWEW6OwjGlIQSn:CWloGlIQSn |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Reads settings of System Certificates
- chrome.exe (PID: 3500)
Reads the hosts file
- chrome.exe (PID: 3080)
- chrome.exe (PID: 3500)
Application launched itself
- chrome.exe (PID: 3080)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
72
Monitored processes
33
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1848 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,1294317760152293786,1905830900844343906,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8995886489803648834 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2236 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2112 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,1294317760152293786,1905830900844343906,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9931090158741555758 --renderer-client-id=28 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=6104 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2168 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,1294317760152293786,1905830900844343906,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2521566325674458213 --renderer-client-id=18 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5408 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2196 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,1294317760152293786,1905830900844343906,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16261053325261676914 --renderer-client-id=27 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5692 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2496 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,1294317760152293786,1905830900844343906,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3465325882285361055 --renderer-client-id=12 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3952 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2508 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,1294317760152293786,1905830900844343906,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8286559006569260836 --renderer-client-id=8 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3408 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2540 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,1294317760152293786,1905830900844343906,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4677789358021886330 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3308 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2608 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,1294317760152293786,1905830900844343906,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8743073642983671650 --renderer-client-id=17 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4984 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2616 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,1294317760152293786,1905830900844343906,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10132954012298135038 --renderer-client-id=14 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4228 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2672 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1020,1294317760152293786,1905830900844343906,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=11858145736115560079 --mojo-platform-channel-handle=1040 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
843
Read events
745
Write events
94
Delete events
4
Modification events
| (PID) Process: | (3080) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3080) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3080) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3080) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3080) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3652) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3080-13243372596510875 |
Value: 259 | |||
| (PID) Process: | (3080) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3080) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3080) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2832-13239195546717773 |
Value: 0 | |||
| (PID) Process: | (3080) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
275
Text files
115
Unknown types
45
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3080 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\8db2209d-2ab1-47b1-9c00-b41292e273c6.tmp | — | |
MD5:— | SHA256:— | |||
| 3080 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000032.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3080 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3080 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3080 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3080 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RFe602d.TMP | text | |
MD5:— | SHA256:— | |||
| 3080 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RFe604c.TMP | text | |
MD5:— | SHA256:— | |||
| 3080 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3080 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RFe628e.TMP | — | |
MD5:— | SHA256:— | |||
| 3080 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
24
TCP/UDP connections
151
DNS requests
99
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
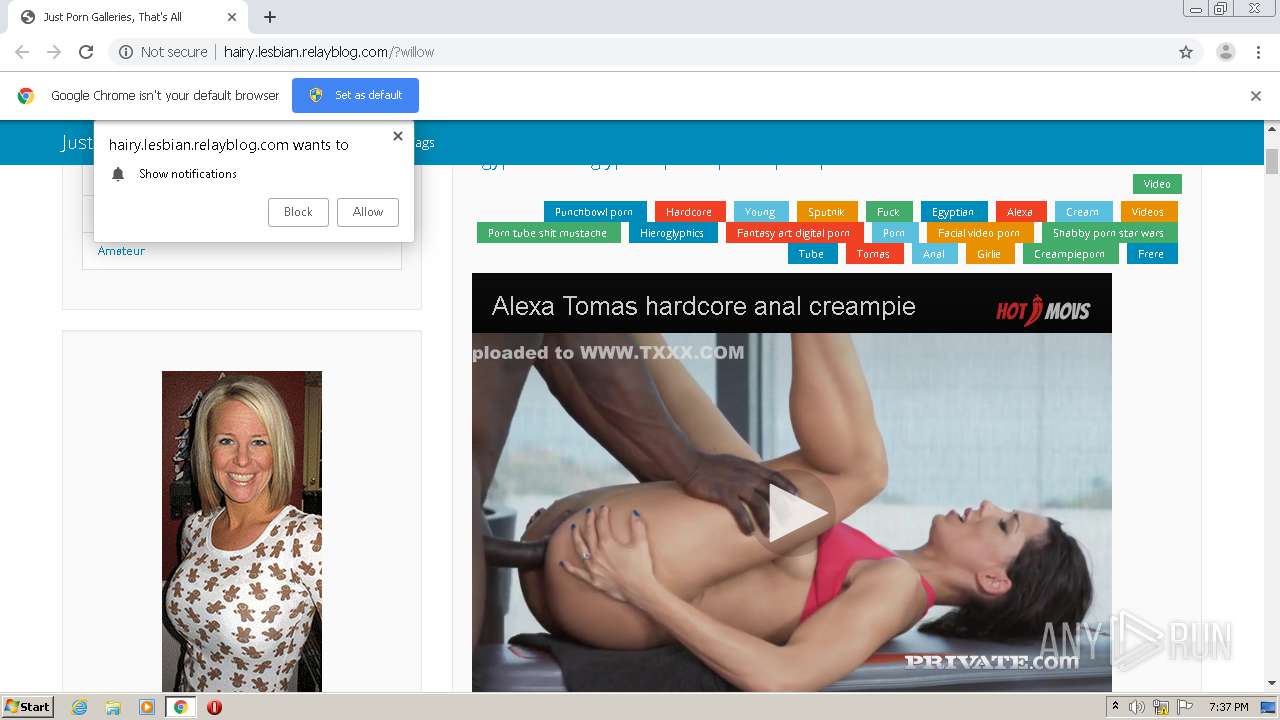
3500 | chrome.exe | GET | 200 | 54.36.162.42:80 | http://hairy.lesbian.relayblog.com/?willow | FR | html | 73.8 Kb | suspicious |
3500 | chrome.exe | GET | 200 | 54.36.162.42:80 | http://hairy.lesbian.relayblog.com/s3/smartad1/14.jpg | FR | image | 123 Kb | suspicious |
3500 | chrome.exe | GET | 200 | 213.174.135.1:80 | http://cdn.tubecorp.com/i/b.html?spot=1925&src=1150975883&pid=17794&width=728&height=90&spaceid=861 | US | html | 178 b | malicious |
3500 | chrome.exe | GET | 200 | 54.36.162.42:80 | http://hairy.lesbian.relayblog.com/s3/gen/banner-08793.jpg | FR | image | 38.7 Kb | suspicious |
3500 | chrome.exe | GET | 200 | 88.85.94.229:80 | http://plified.pro/cgD.9Y6lb/2/5ZlNSPW/QF9AM/TFQh2aNXj_Q_whMQSe0FxANbD/Y-2/NyTEUl3Y | NL | text | 30.3 Kb | suspicious |
3500 | chrome.exe | GET | 200 | 54.36.162.42:80 | http://hairy.lesbian.relayblog.com/s3/crwe1/5.jpg | FR | image | 31.8 Kb | suspicious |
3500 | chrome.exe | GET | 200 | 54.36.162.42:80 | http://hairy.lesbian.relayblog.com/s3/smartda1/8.gif | FR | image | 195 Kb | suspicious |
3500 | chrome.exe | GET | 200 | 185.94.236.20:80 | http://poweredby.jads.co/adshow.php?adzone=719499 | NL | html | 1.77 Kb | whitelisted |
3500 | chrome.exe | GET | 200 | 54.36.162.42:80 | http://hairy.lesbian.relayblog.com/s3/hheroes1/54.png | FR | image | 91.8 Kb | suspicious |
3500 | chrome.exe | GET | 200 | 213.174.135.1:80 | http://cdn.tubecorp.com/b/tcbanner.js?v=7 | US | text | 17.8 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3500 | chrome.exe | 172.217.22.67:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3500 | chrome.exe | 54.36.162.42:80 | hairy.lesbian.relayblog.com | OVH SAS | FR | suspicious |
3500 | chrome.exe | 172.217.21.234:443 | ajax.googleapis.com | Google Inc. | US | whitelisted |
3500 | chrome.exe | 172.217.23.168:443 | www.googletagmanager.com | Google Inc. | US | whitelisted |
3500 | chrome.exe | 216.58.206.13:443 | accounts.google.com | Google Inc. | US | whitelisted |
3500 | chrome.exe | 172.64.135.35:443 | hotmovs.com | Cloudflare Inc | US | unknown |
3500 | chrome.exe | 216.58.212.163:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
3500 | chrome.exe | 172.64.203.9:443 | upornia.com | Cloudflare Inc | US | shared |
3500 | chrome.exe | 172.64.143.29:443 | vjav.com | Cloudflare Inc | US | shared |
3500 | chrome.exe | 66.254.114.41:443 | www.pornhub.com | Reflected Networks, Inc. | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
hairy.lesbian.relayblog.com |
| suspicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
maxcdn.bootstrapcdn.com |
| whitelisted |
ajax.googleapis.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
poweredby.jads.co |
| whitelisted |
www.google.com |
| malicious |
fonts.gstatic.com |
| whitelisted |