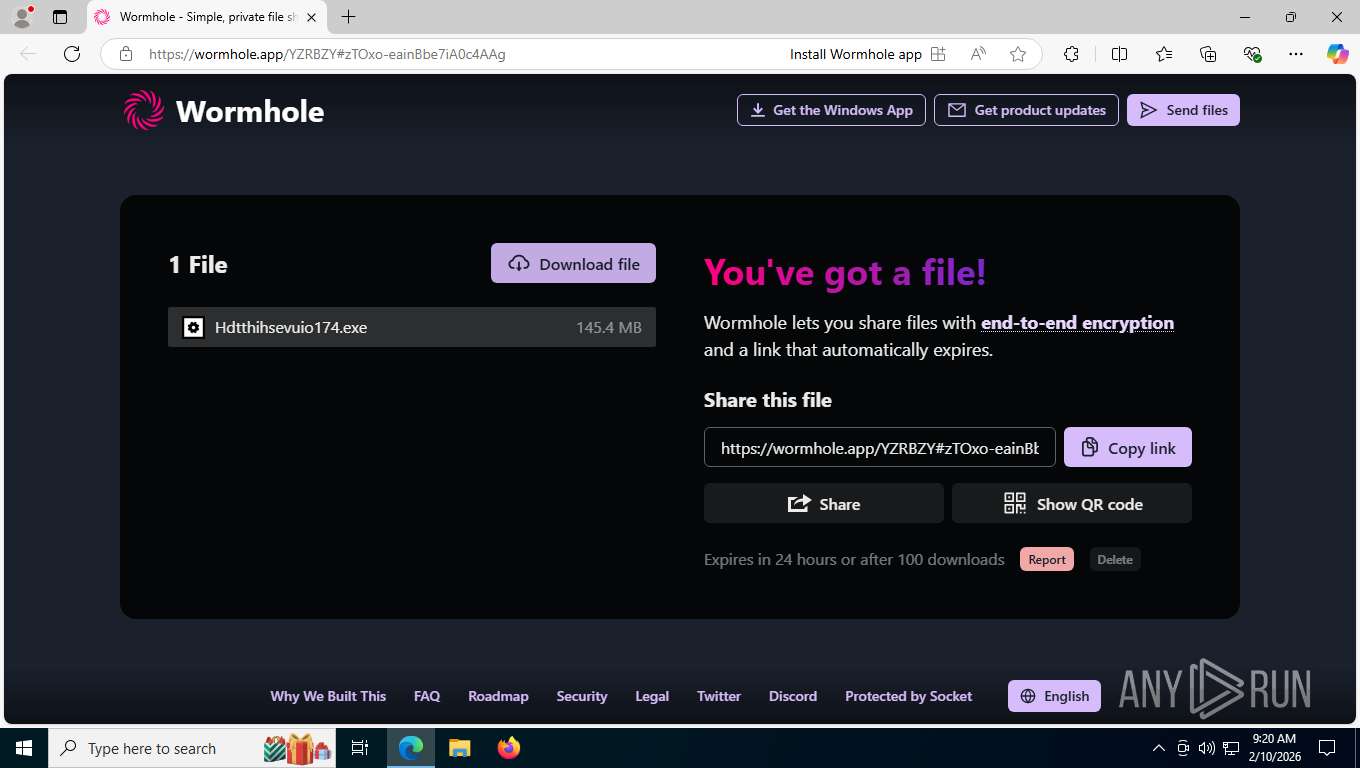
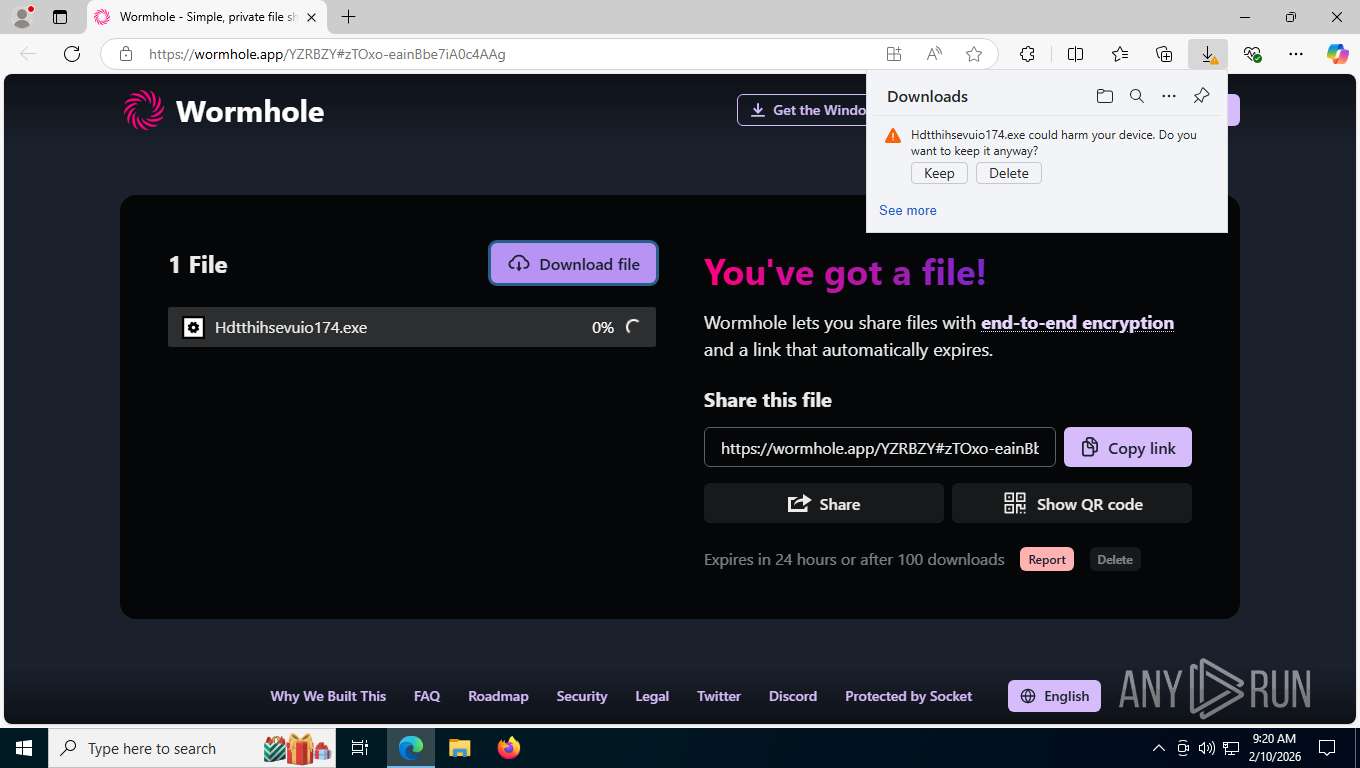
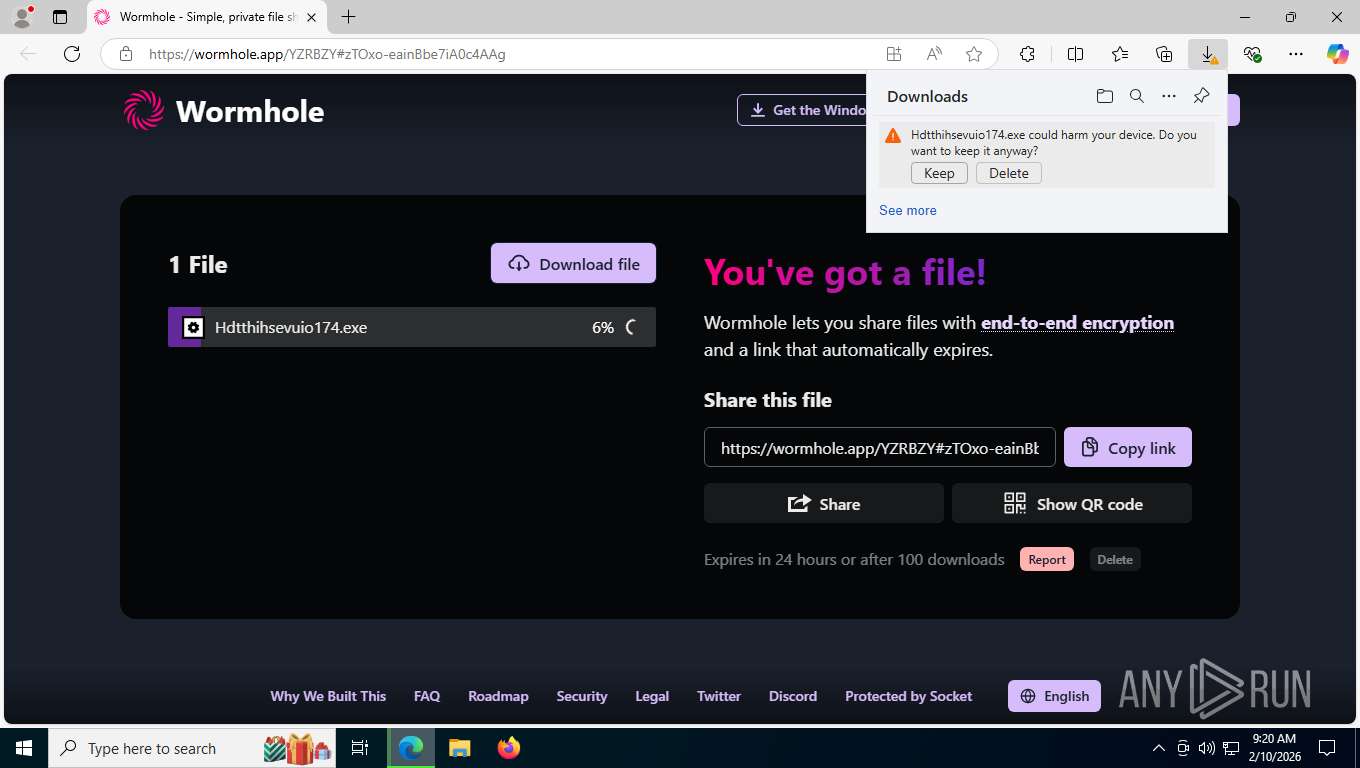
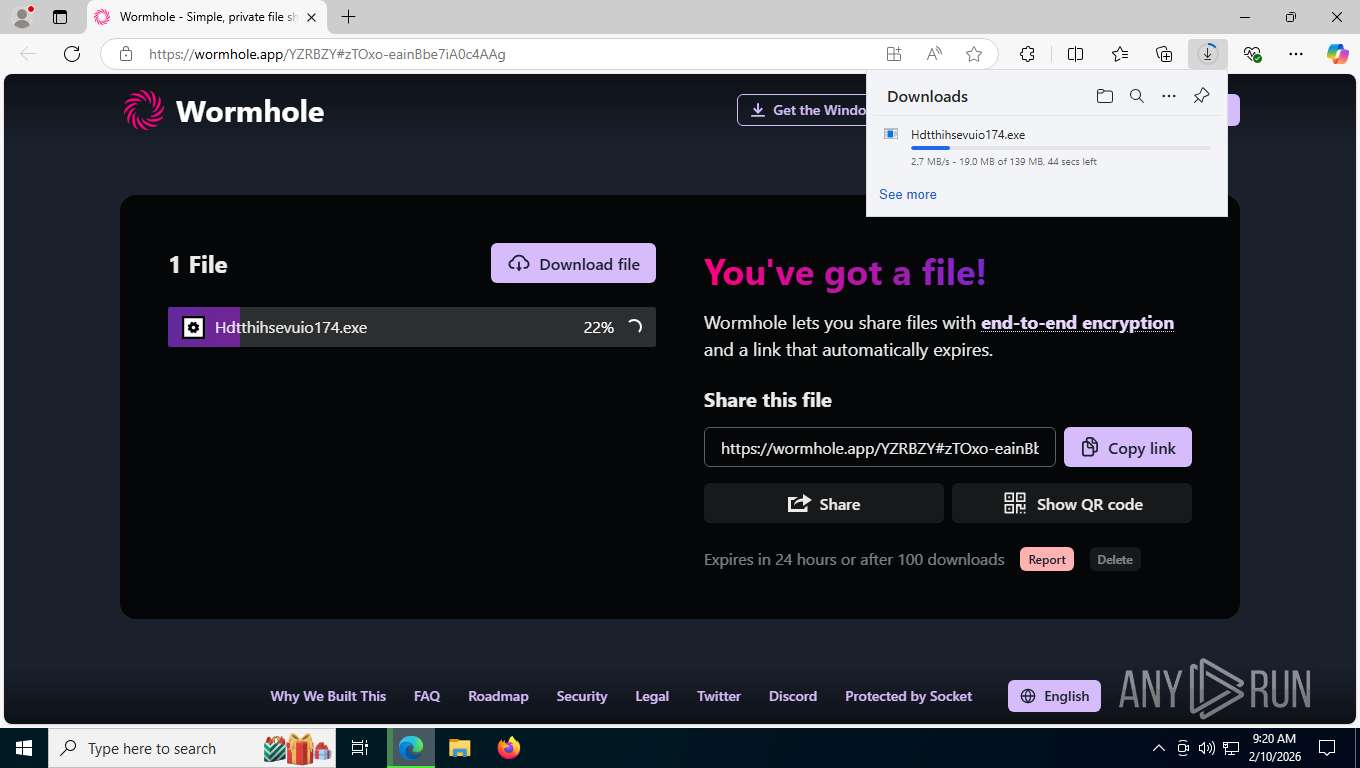
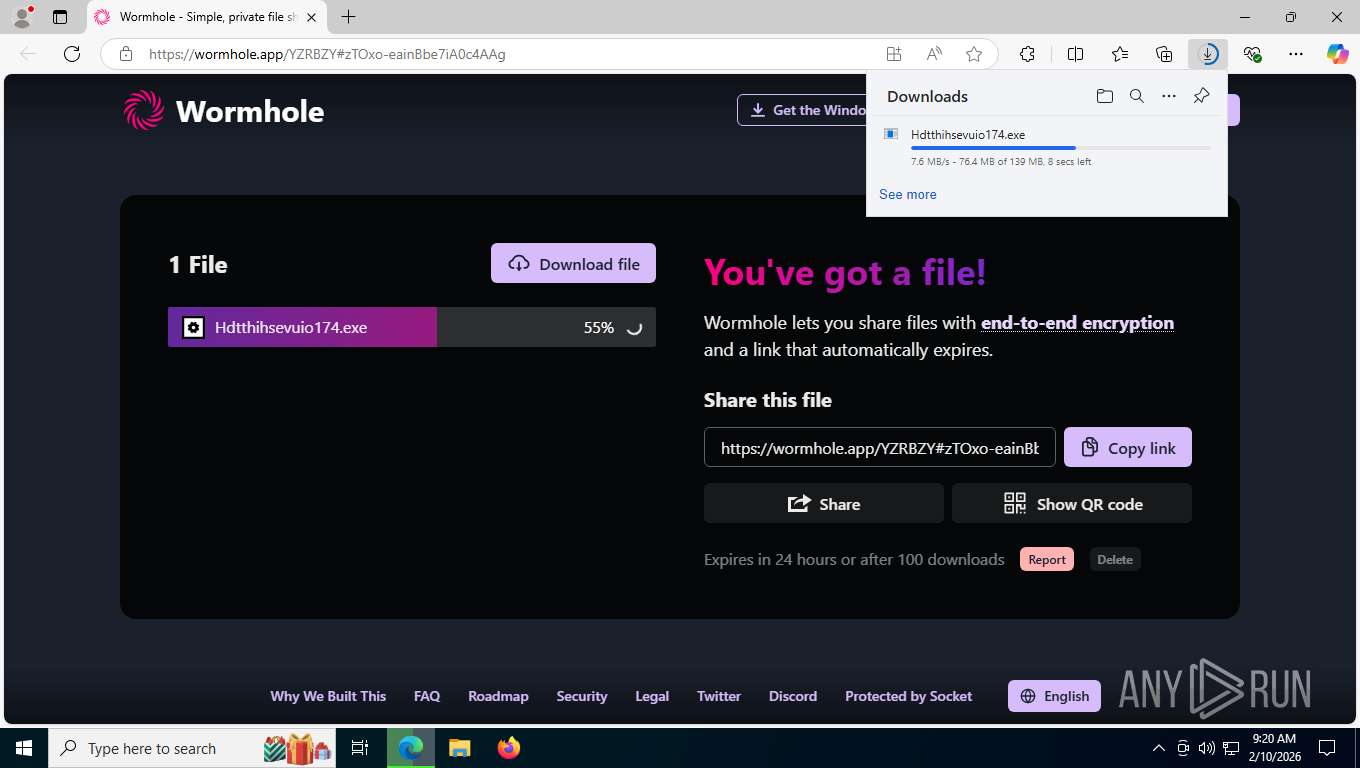
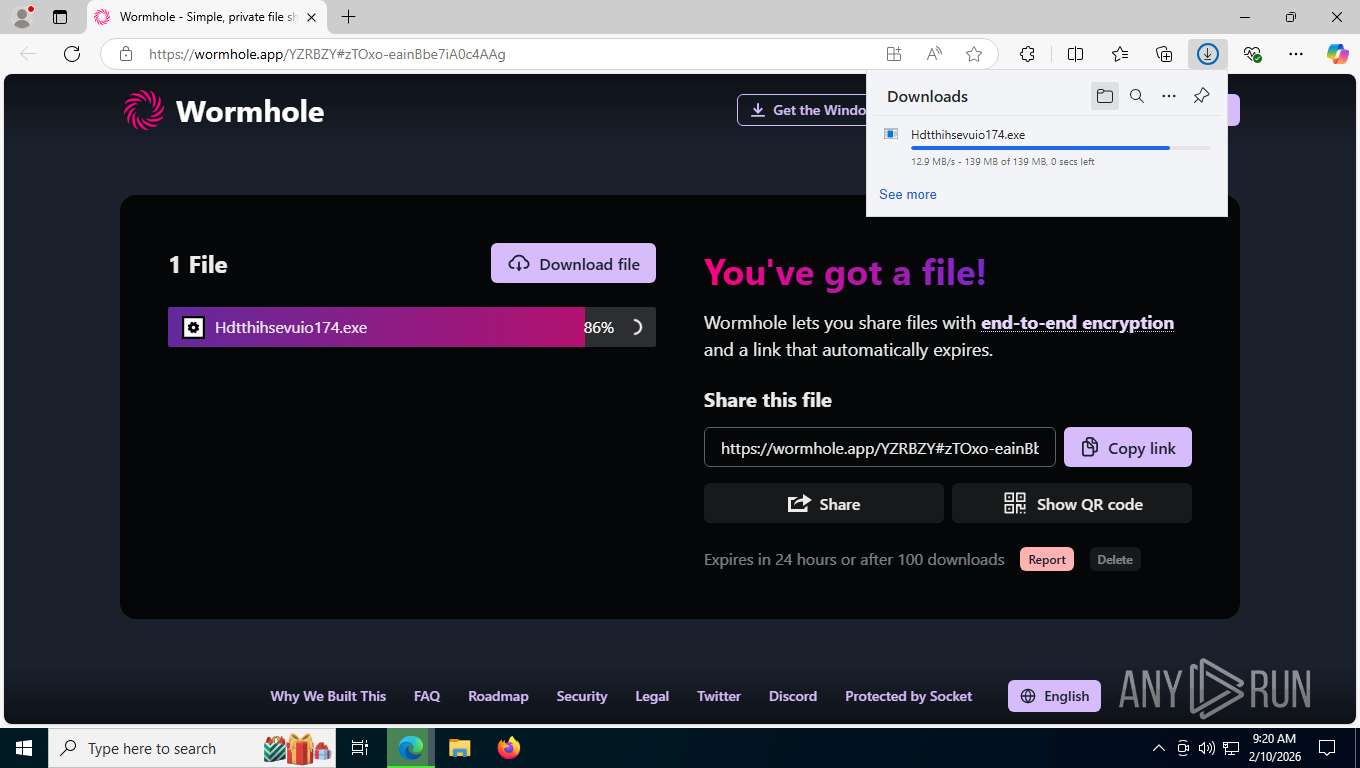
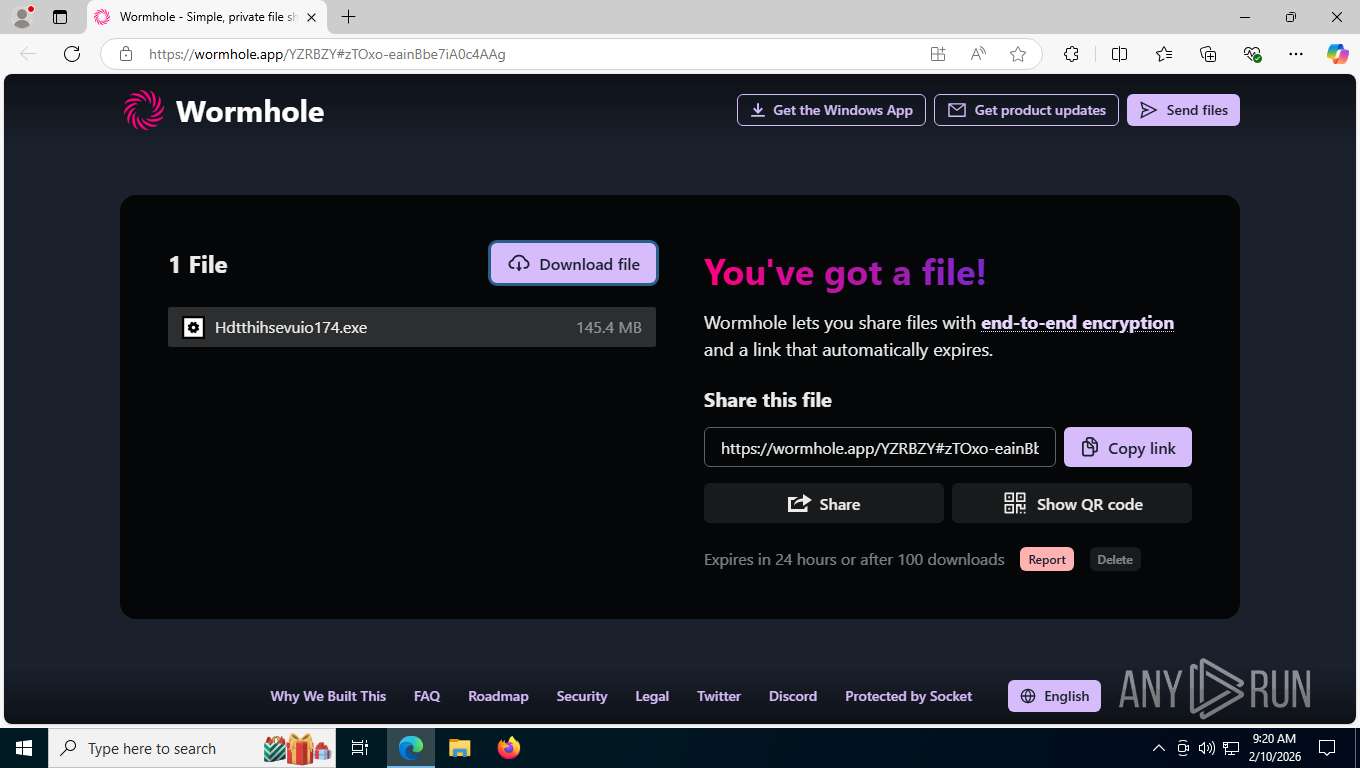
| URL: | https://wormhole.app/YZRBZY#zTOxo-eainBbe7iA0c4AAg |
| Full analysis: | https://app.any.run/tasks/d3e4997d-fdc0-470c-8397-5dc9ff7ec3f1 |
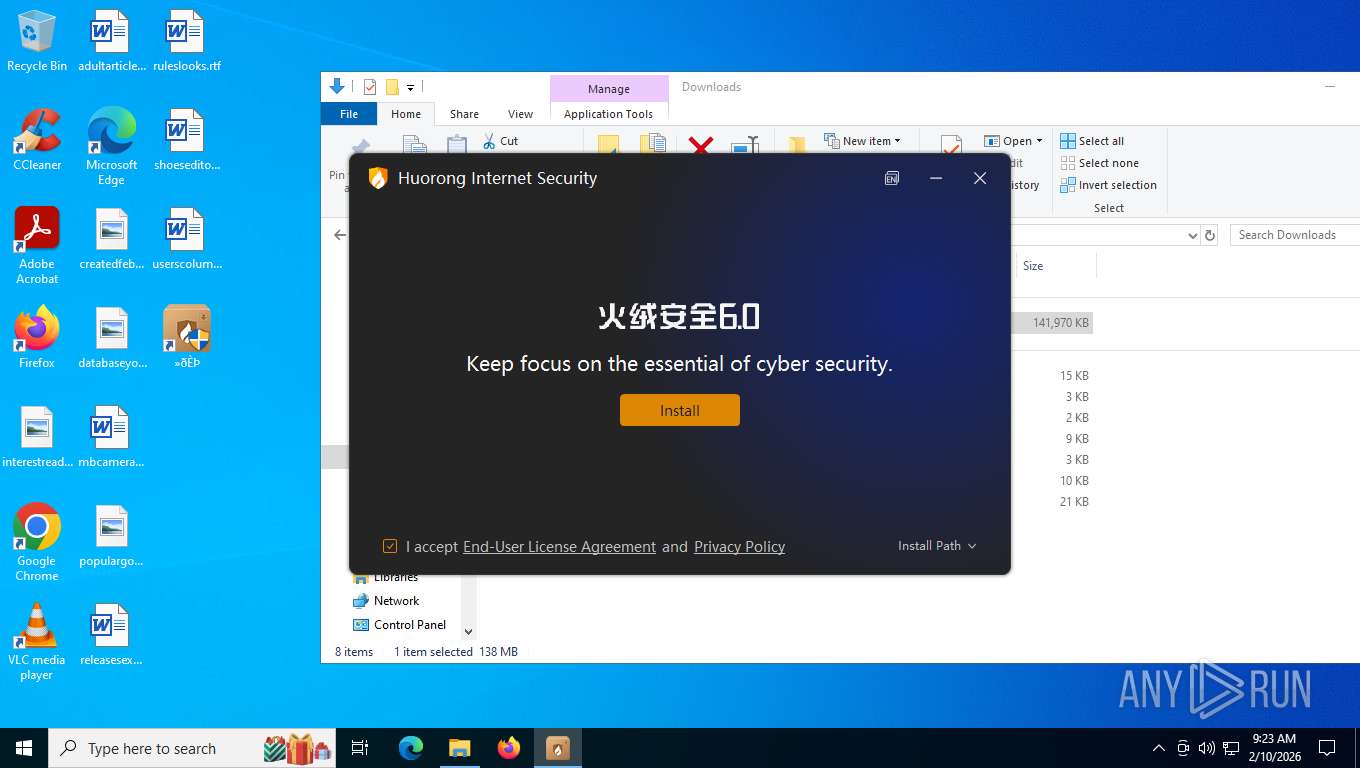
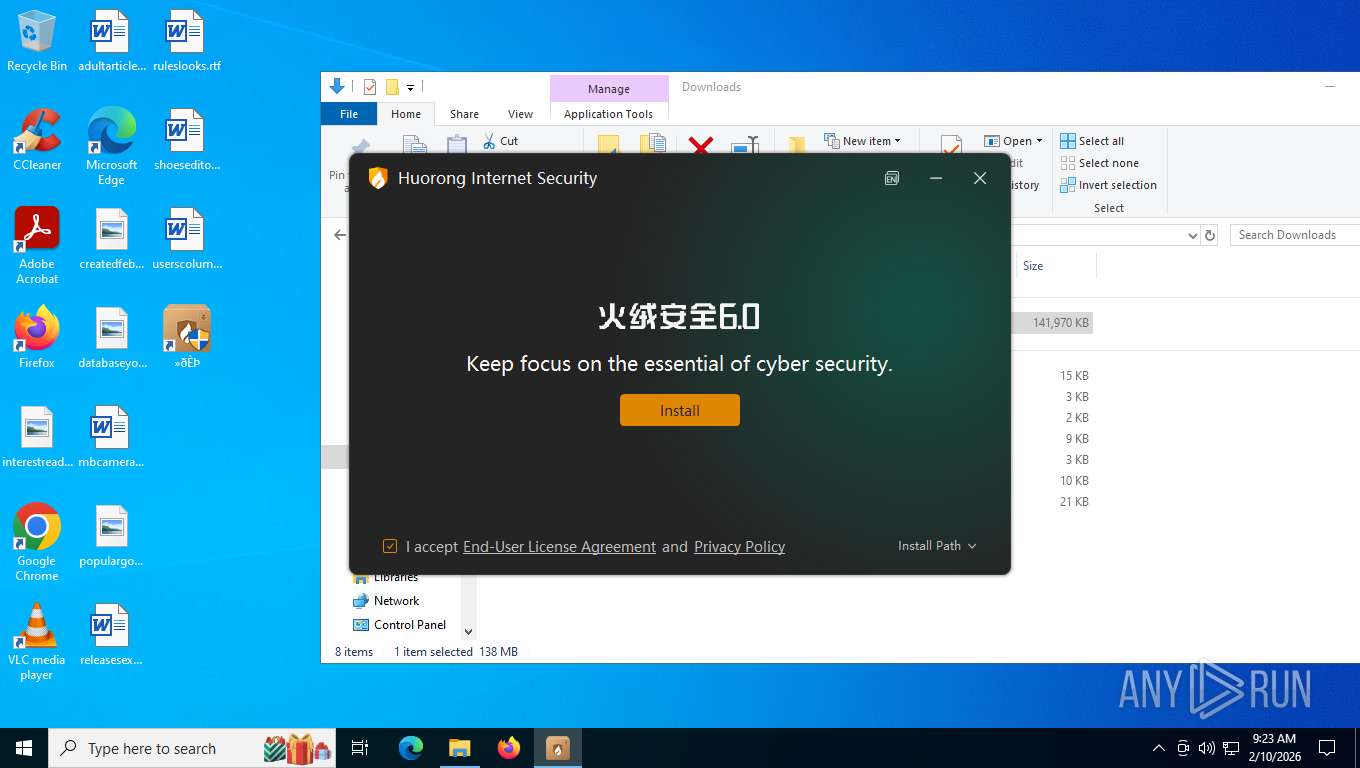
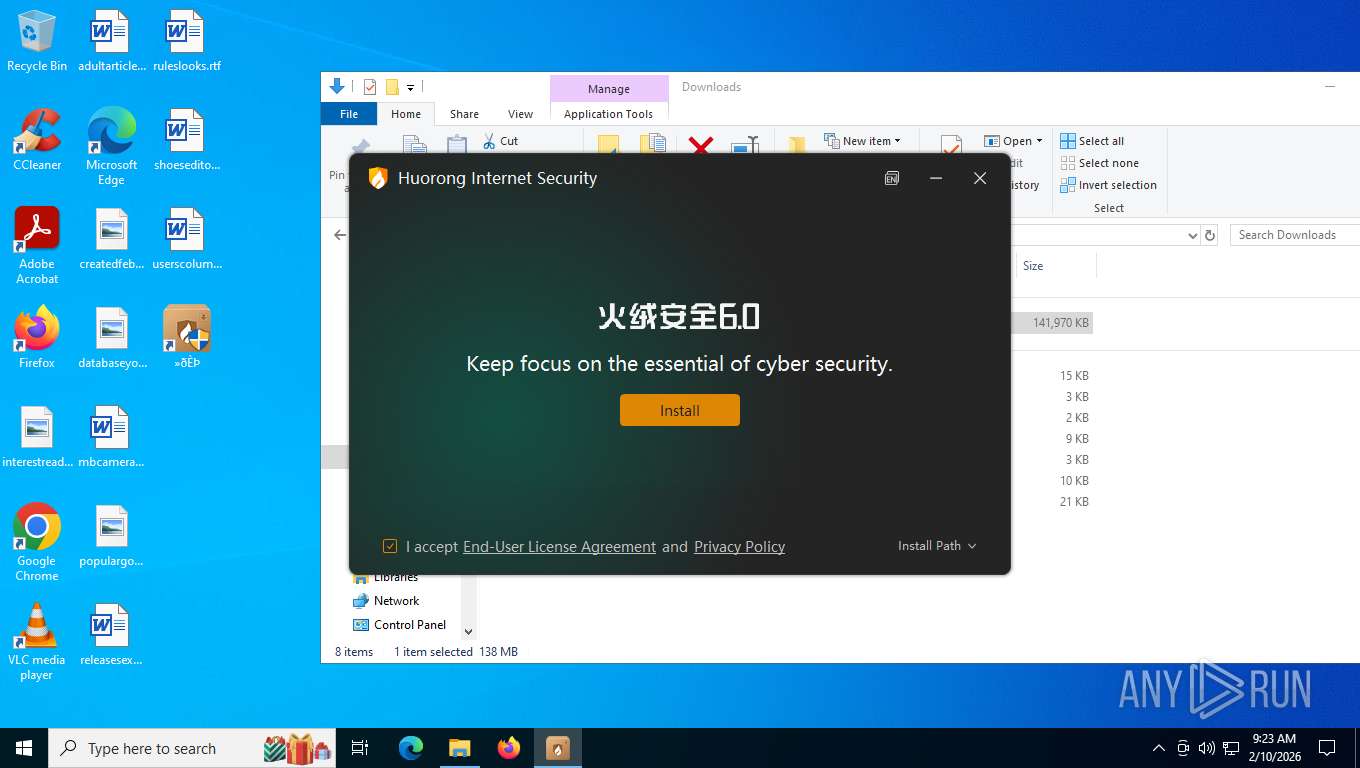
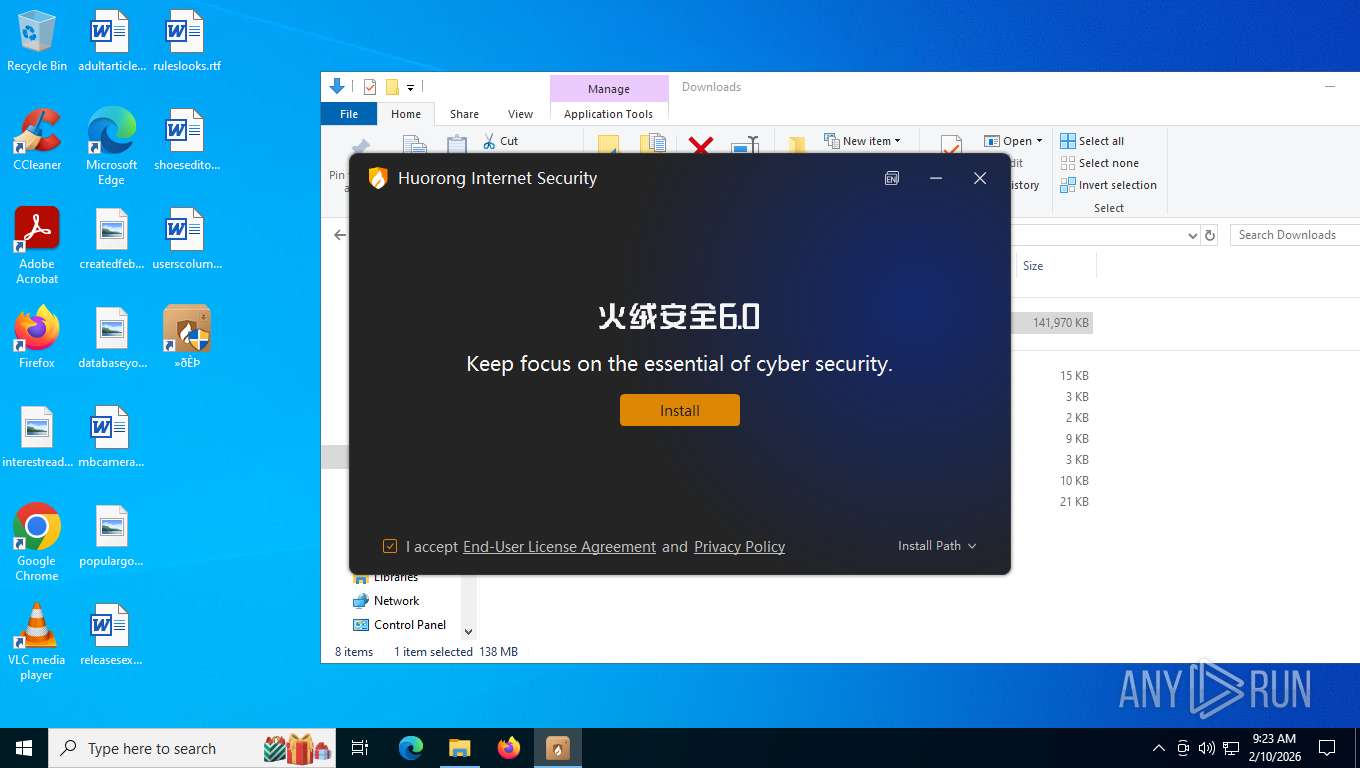
| Verdict: | Malicious activity |
| Analysis date: | February 10, 2026, 14:20:01 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 85FF31AF6EFFAF0214E47CFA84A946C3 |
| SHA1: | B1AC8E38E36F9DD2115B65A272AB3B1309DB7B16 |
| SHA256: | CD1FF53007D9DFE848909A249D2344147BACE185427A0997E0E8404017F13F80 |
| SSDEEP: | 3:N8bXINKJuju30JKPgsVGkL:2kNSuj4TVww |
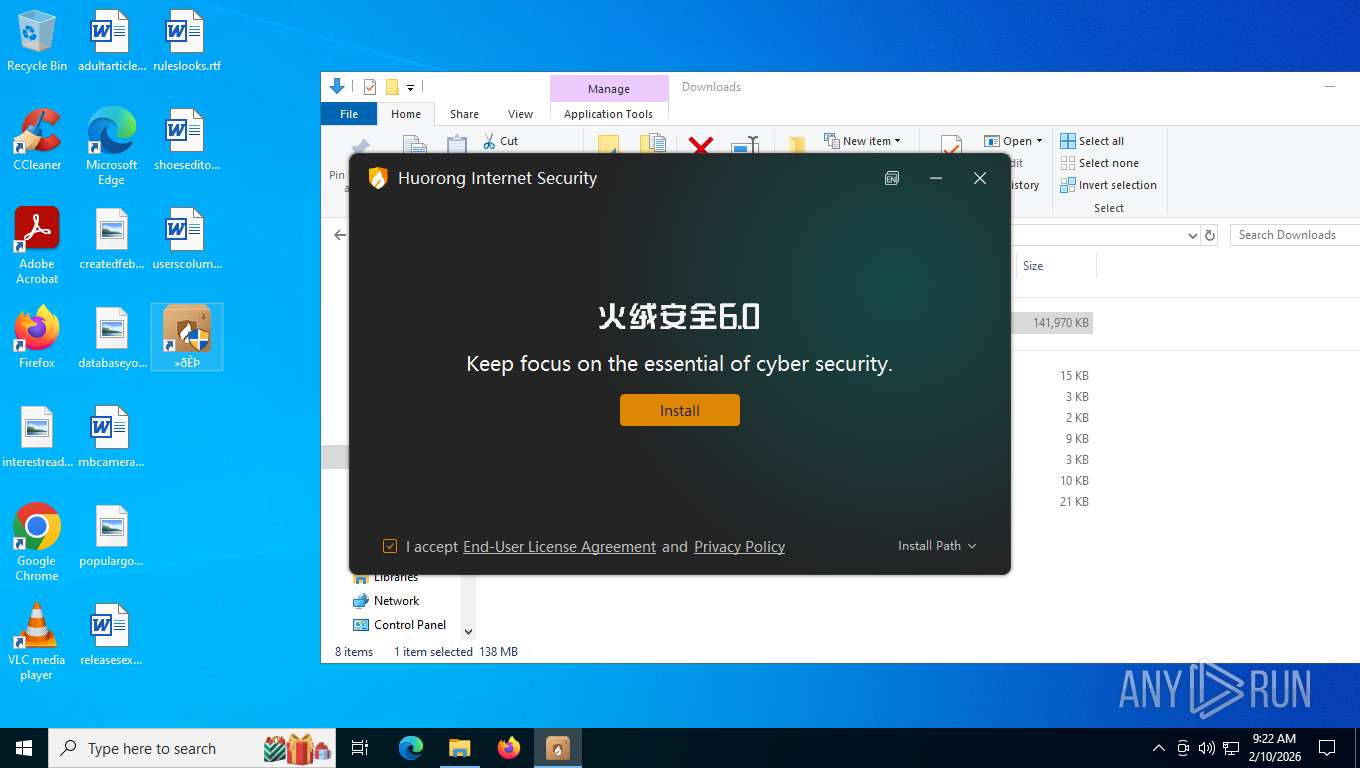
MALICIOUS
No malicious indicators.SUSPICIOUS
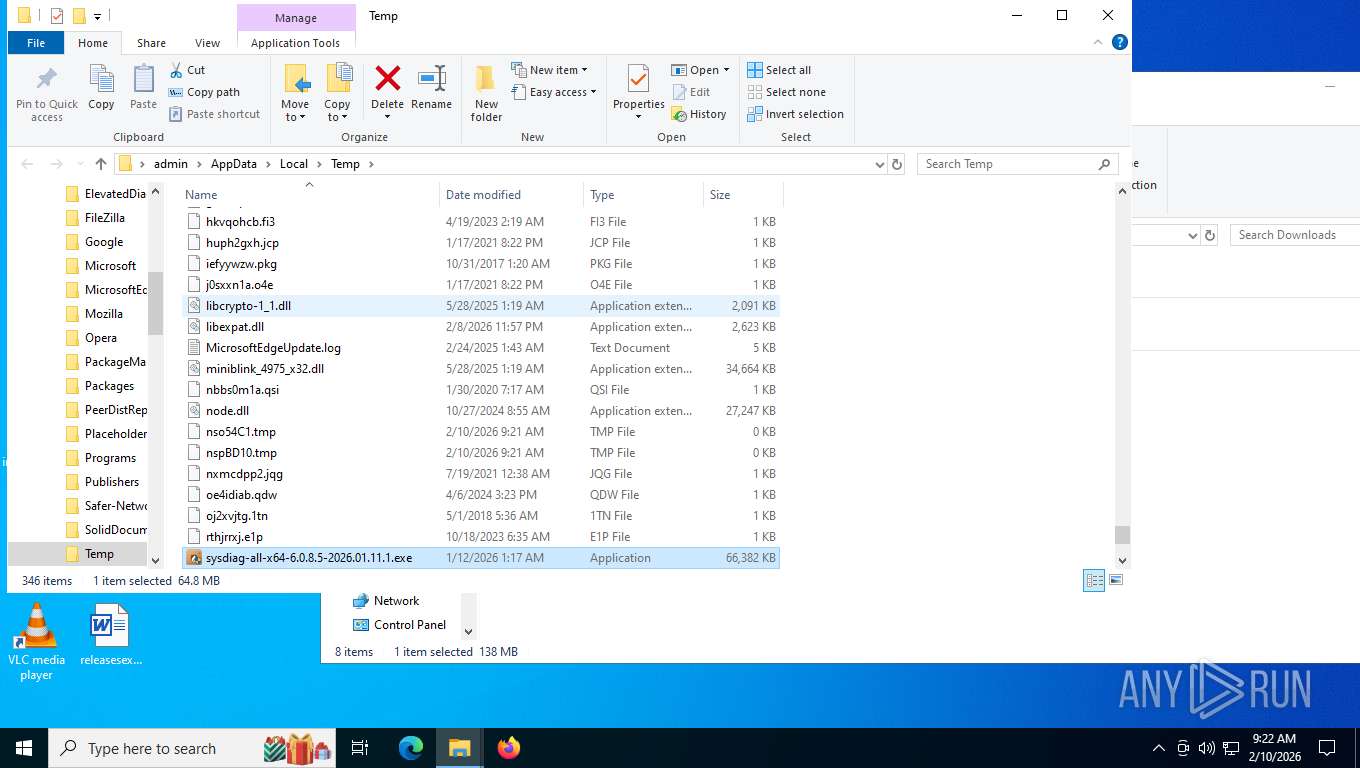
Process drops legitimate windows executable
- Hdtthihsevuio174.exe (PID: 6360)
- WavesSvc64.exe (PID: 4680)
- Hdtthihsevuio174.exe (PID: 4796)
The process creates files with name similar to system file names
- Hdtthihsevuio174.exe (PID: 6360)
- Hdtthihsevuio174.exe (PID: 4796)
- sysdiag-all-x64-6.0.8.5-2026.01.11.1.exe (PID: 2284)
Malware-specific behavior (creating "System.dll" in Temp)
- Hdtthihsevuio174.exe (PID: 6360)
- Hdtthihsevuio174.exe (PID: 4796)
- sysdiag-all-x64-6.0.8.5-2026.01.11.1.exe (PID: 2284)
The process drops C-runtime libraries
- Hdtthihsevuio174.exe (PID: 6360)
- WavesSvc64.exe (PID: 4680)
- Hdtthihsevuio174.exe (PID: 4796)
Executable content was dropped or overwritten
- Hdtthihsevuio174.exe (PID: 6360)
- WavesSvc64.exe (PID: 4680)
- Hdtthihsevuio174.exe (PID: 4796)
- sysdiag-all-x64-6.0.8.5-2026.01.11.1.exe (PID: 2284)
Reads the BIOS version
- WavesSvc64.exe (PID: 4680)
- WavesSvc64.exe (PID: 6808)
- WavesSvc64.exe (PID: 7036)
- WavesSvc64.exe (PID: 2872)
The process executes via Task Scheduler
- WavesSvc64.exe (PID: 6808)
- WavesSvc64.exe (PID: 2872)
Searches for installed software
- sysdiag-all-x64-6.0.8.5-2026.01.11.1.exe (PID: 2284)
INFO
Reads the computer name
- identity_helper.exe (PID: 5896)
- Hdtthihsevuio174.exe (PID: 6360)
- WavesSvc64.exe (PID: 4680)
- Hdtthihsevuio174.exe (PID: 4796)
- WavesSvc64.exe (PID: 7036)
- sysdiag-all-x64-6.0.8.5-2026.01.11.1.exe (PID: 2284)
The sample compiled with english language support
- Hdtthihsevuio174.exe (PID: 6360)
- WavesSvc64.exe (PID: 4680)
- Hdtthihsevuio174.exe (PID: 4796)
- sysdiag-all-x64-6.0.8.5-2026.01.11.1.exe (PID: 2284)
Checks supported languages
- identity_helper.exe (PID: 5896)
- Hdtthihsevuio174.exe (PID: 6360)
- WavesSvc64.exe (PID: 4680)
- WavesSvc64.exe (PID: 6808)
- Hdtthihsevuio174.exe (PID: 4796)
- WavesSvc64.exe (PID: 7036)
- WavesSvc64.exe (PID: 2872)
- sysdiag-all-x64-6.0.8.5-2026.01.11.1.exe (PID: 2284)
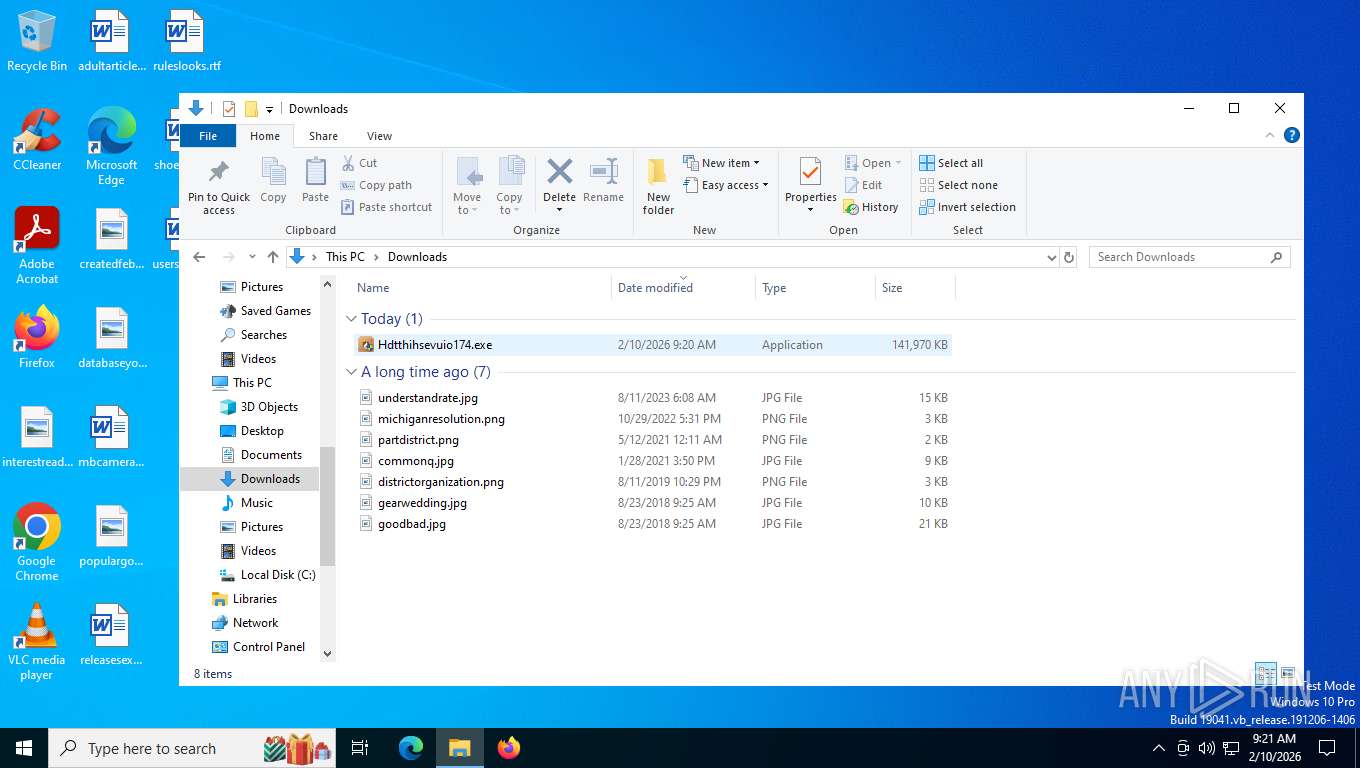
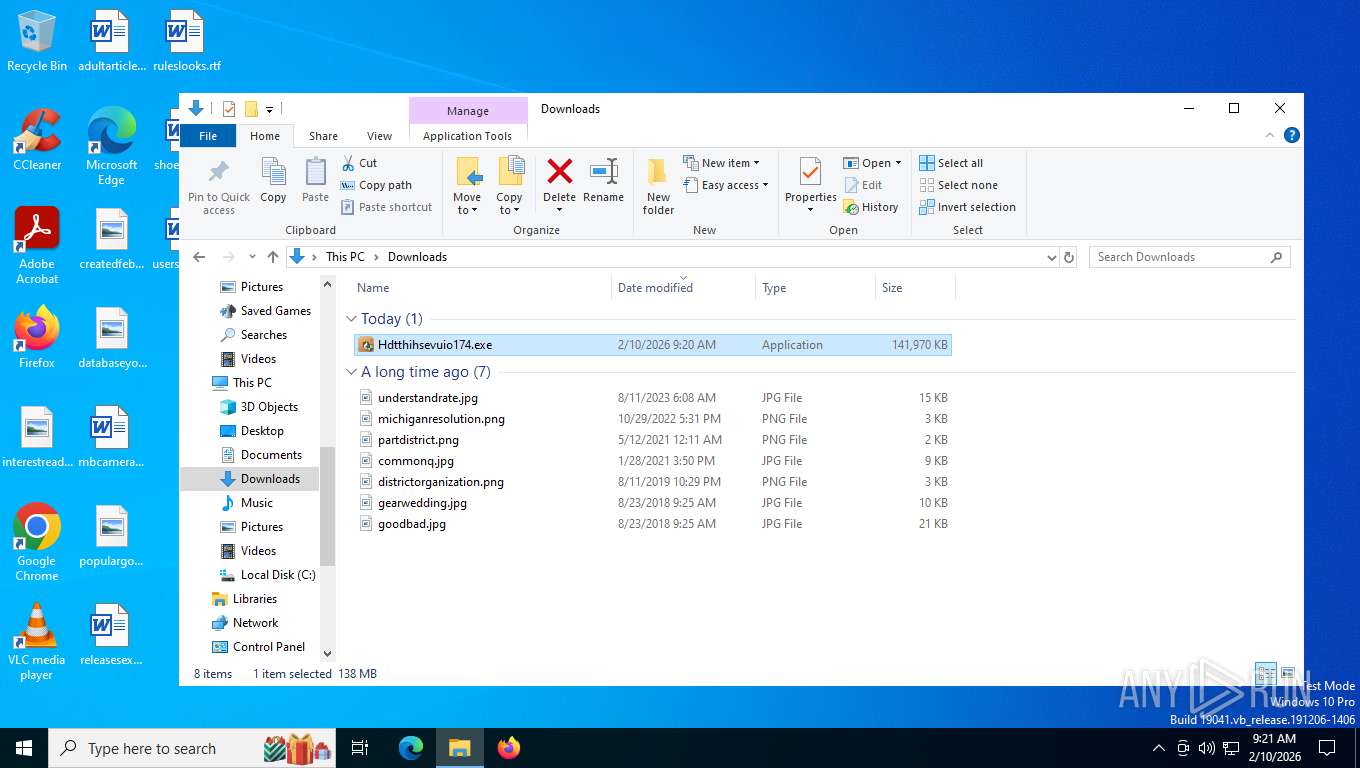
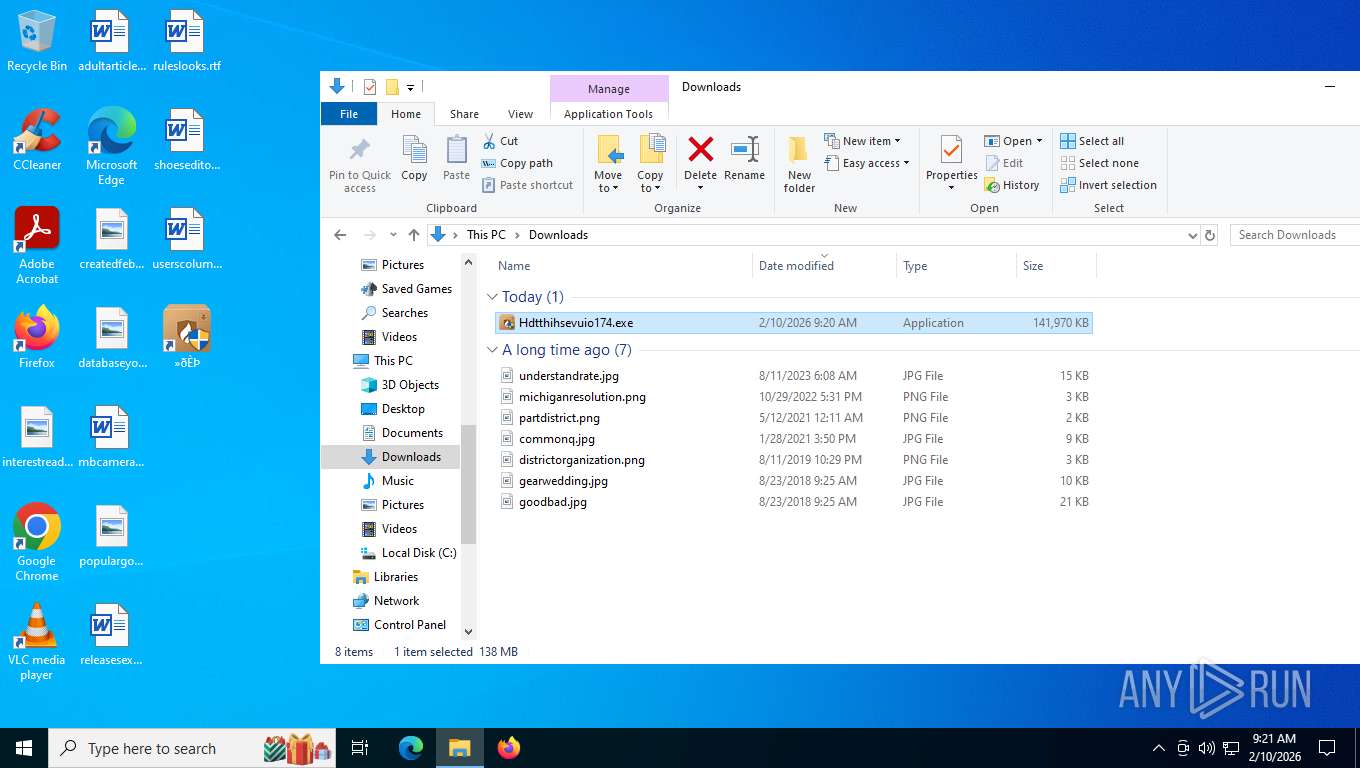
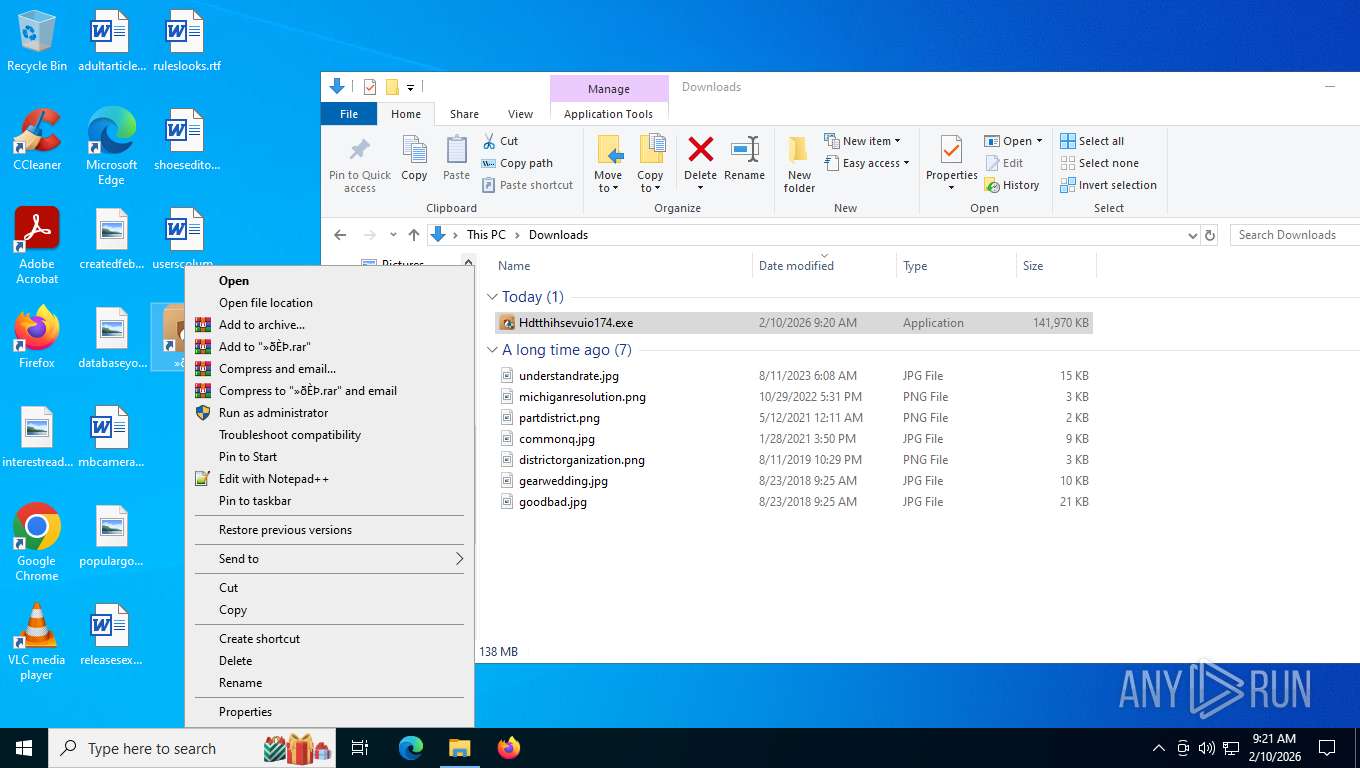
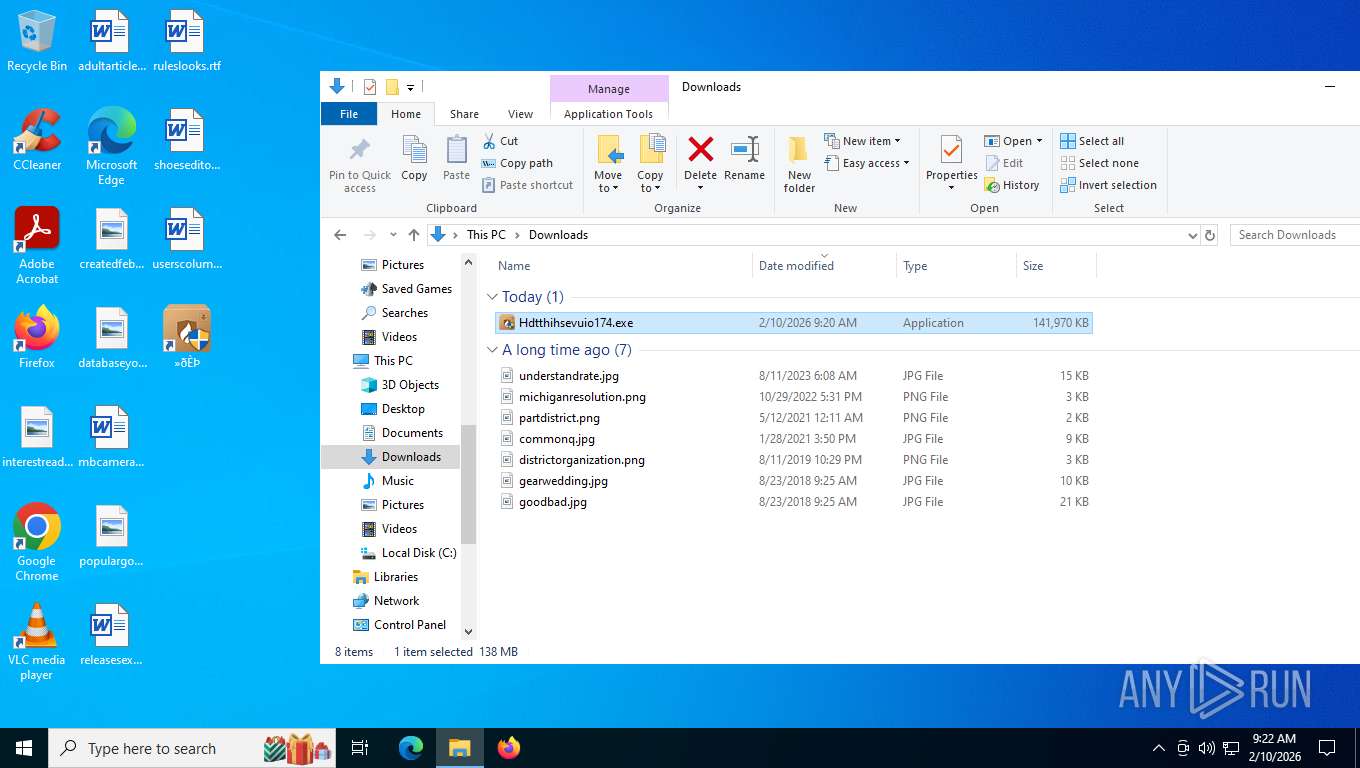
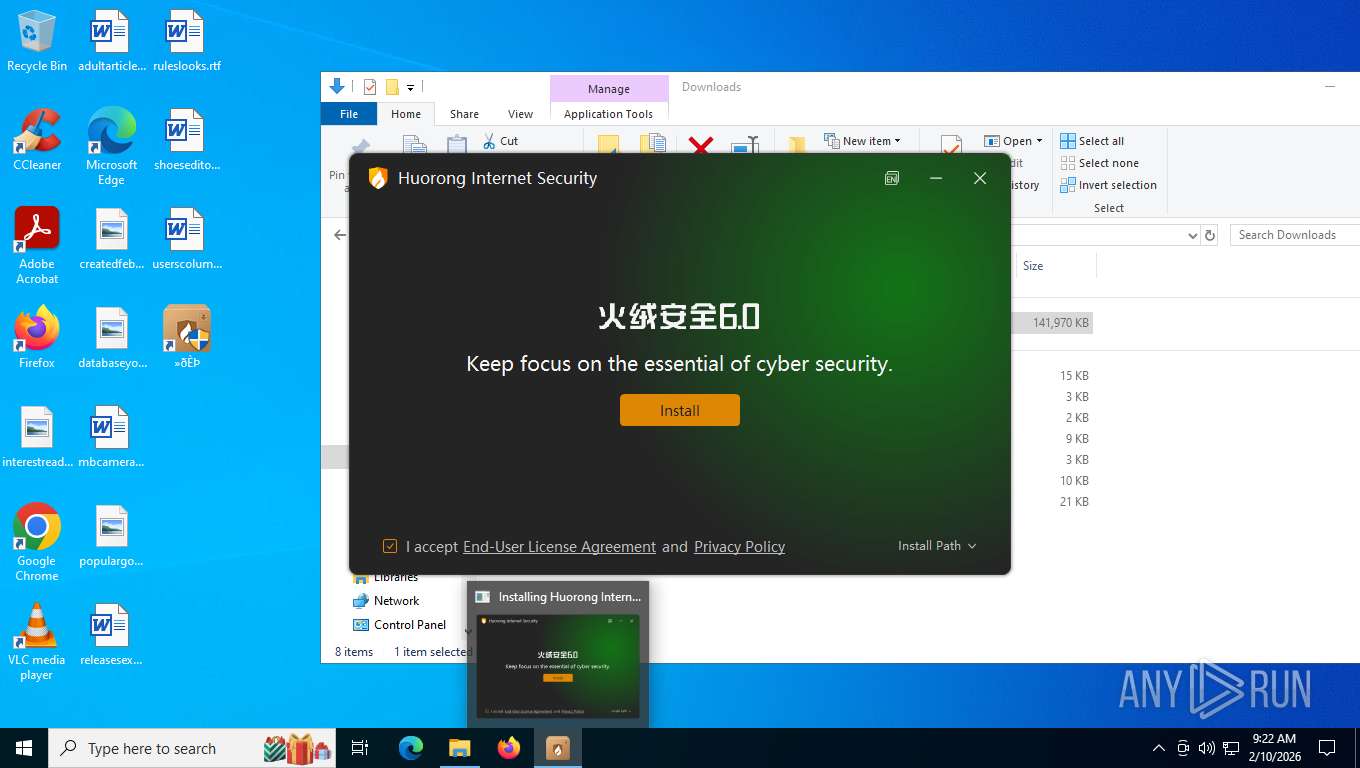
Manual execution by a user
- Hdtthihsevuio174.exe (PID: 6172)
- Hdtthihsevuio174.exe (PID: 6360)
- Hdtthihsevuio174.exe (PID: 2052)
- Hdtthihsevuio174.exe (PID: 4796)
- sysdiag-all-x64-6.0.8.5-2026.01.11.1.exe (PID: 4856)
- sysdiag-all-x64-6.0.8.5-2026.01.11.1.exe (PID: 2284)
Drops script file
- msedge.exe (PID: 2372)
- msedge.exe (PID: 4128)
Create files in a temporary directory
- Hdtthihsevuio174.exe (PID: 6360)
- Hdtthihsevuio174.exe (PID: 4796)
- sysdiag-all-x64-6.0.8.5-2026.01.11.1.exe (PID: 2284)
There is functionality for taking screenshot (YARA)
- Hdtthihsevuio174.exe (PID: 6360)
- Hdtthihsevuio174.exe (PID: 4796)
- sysdiag-all-x64-6.0.8.5-2026.01.11.1.exe (PID: 2284)
The sample compiled with chinese language support
- Hdtthihsevuio174.exe (PID: 6360)
- WavesSvc64.exe (PID: 4680)
- Hdtthihsevuio174.exe (PID: 4796)
Reads Environment values
- identity_helper.exe (PID: 5896)
Application launched itself
- msedge.exe (PID: 4128)
Process checks whether UAC notifications are on
- WavesSvc64.exe (PID: 4680)
- WavesSvc64.exe (PID: 6808)
- WavesSvc64.exe (PID: 7036)
- WavesSvc64.exe (PID: 2872)
Creates files in the program directory
- WavesSvc64.exe (PID: 4680)
Reads the machine GUID from the registry
- WavesSvc64.exe (PID: 4680)
- WavesSvc64.exe (PID: 6808)
- WavesSvc64.exe (PID: 7036)
- WavesSvc64.exe (PID: 2872)
Themida protector has been detected
- WavesSvc64.exe (PID: 6808)
- WavesSvc64.exe (PID: 4680)
- WavesSvc64.exe (PID: 7036)
- WavesSvc64.exe (PID: 2872)
Checks proxy server information
- slui.exe (PID: 148)
UPX packer has been detected
- sysdiag-all-x64-6.0.8.5-2026.01.11.1.exe (PID: 2284)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
190
Monitored processes
38
Malicious processes
0
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 148 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1080 | "rundll32.exe" | C:\Windows\SysWOW64\rundll32.exe | WavesSvc64.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1632 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --pdf-upsell-enabled --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=18 --always-read-main-dll --field-trial-handle=7024,i,10788441984877532616,2257086624424998160,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=6760 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
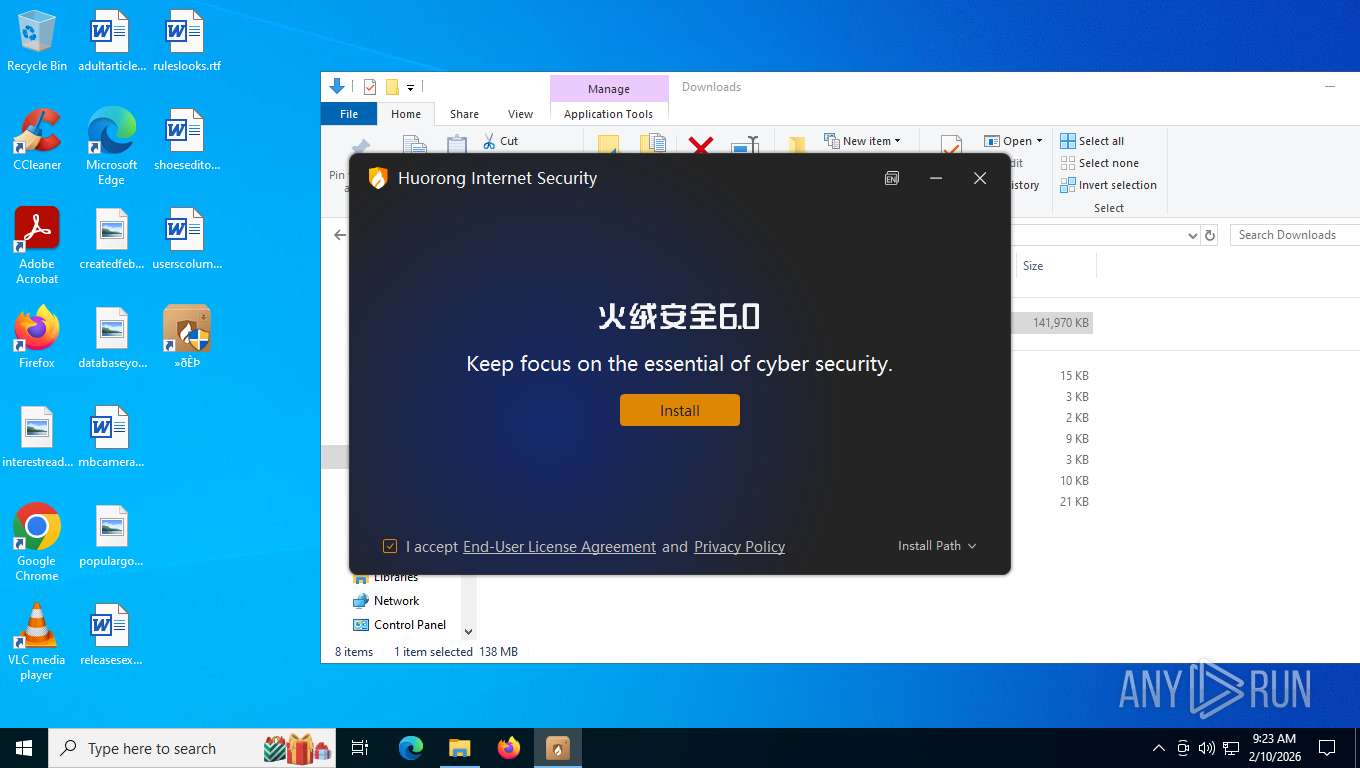
| 2052 | "C:\Users\admin\Downloads\Hdtthihsevuio174.exe" | C:\Users\admin\Downloads\Hdtthihsevuio174.exe | — | explorer.exe | |||||||||||
User: admin Company: HUOPRONG Integrity Level: MEDIUM Description: Fhuorong Exit code: 3221226540 Version: 6.0.1.11 Modules
| |||||||||||||||
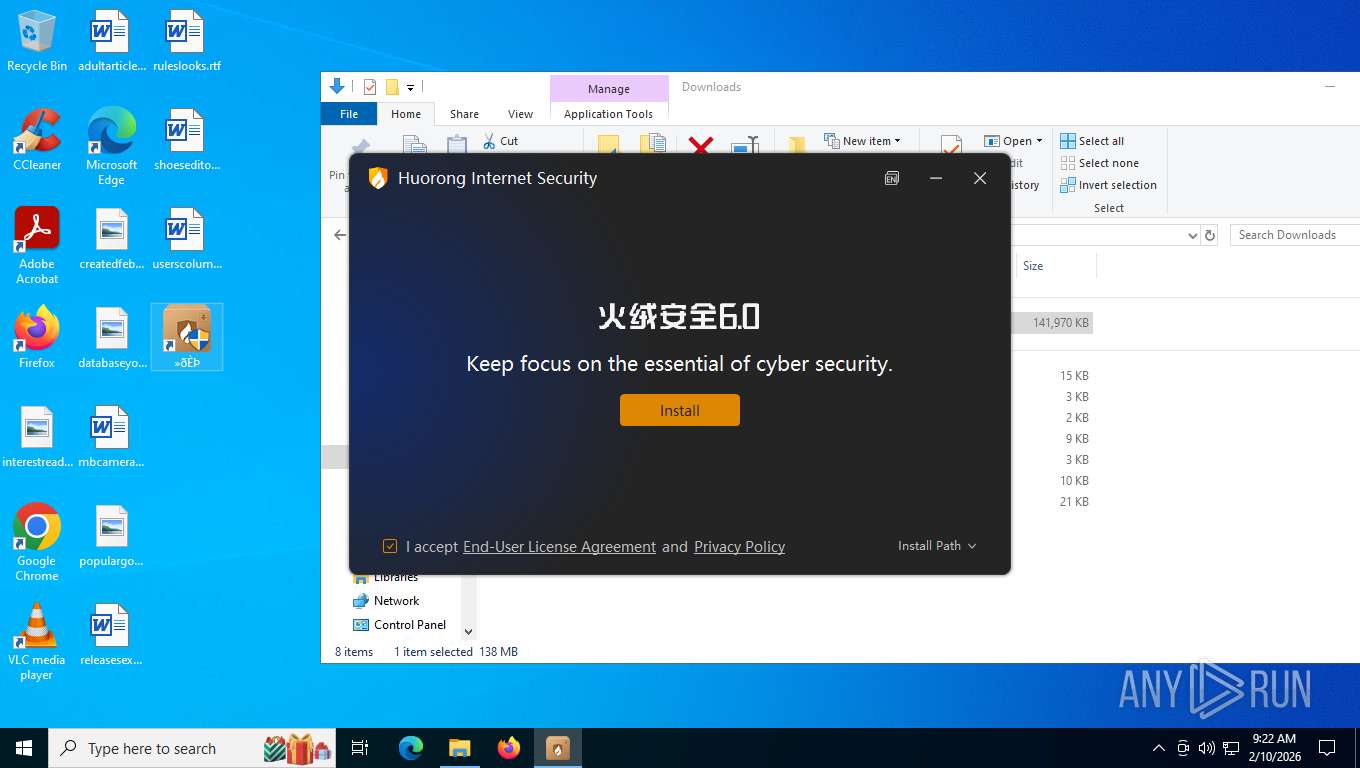
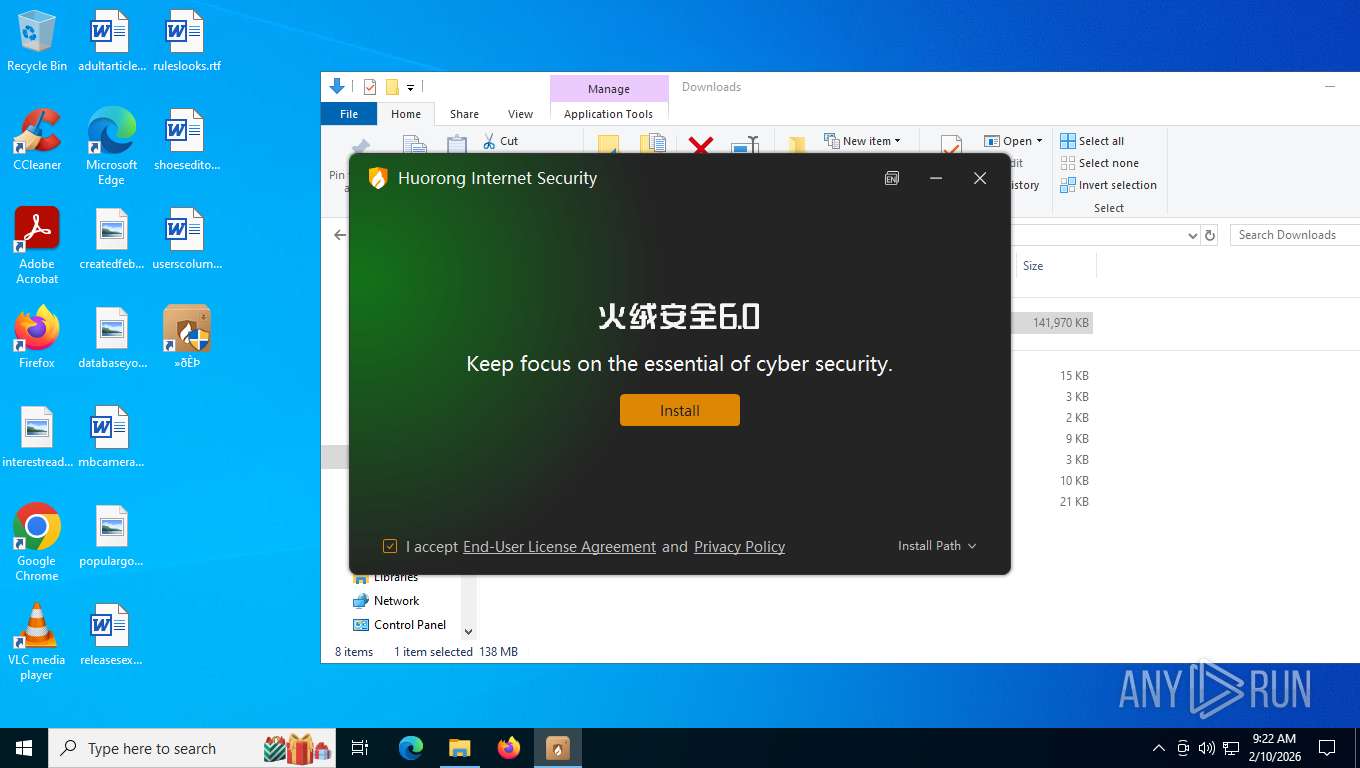
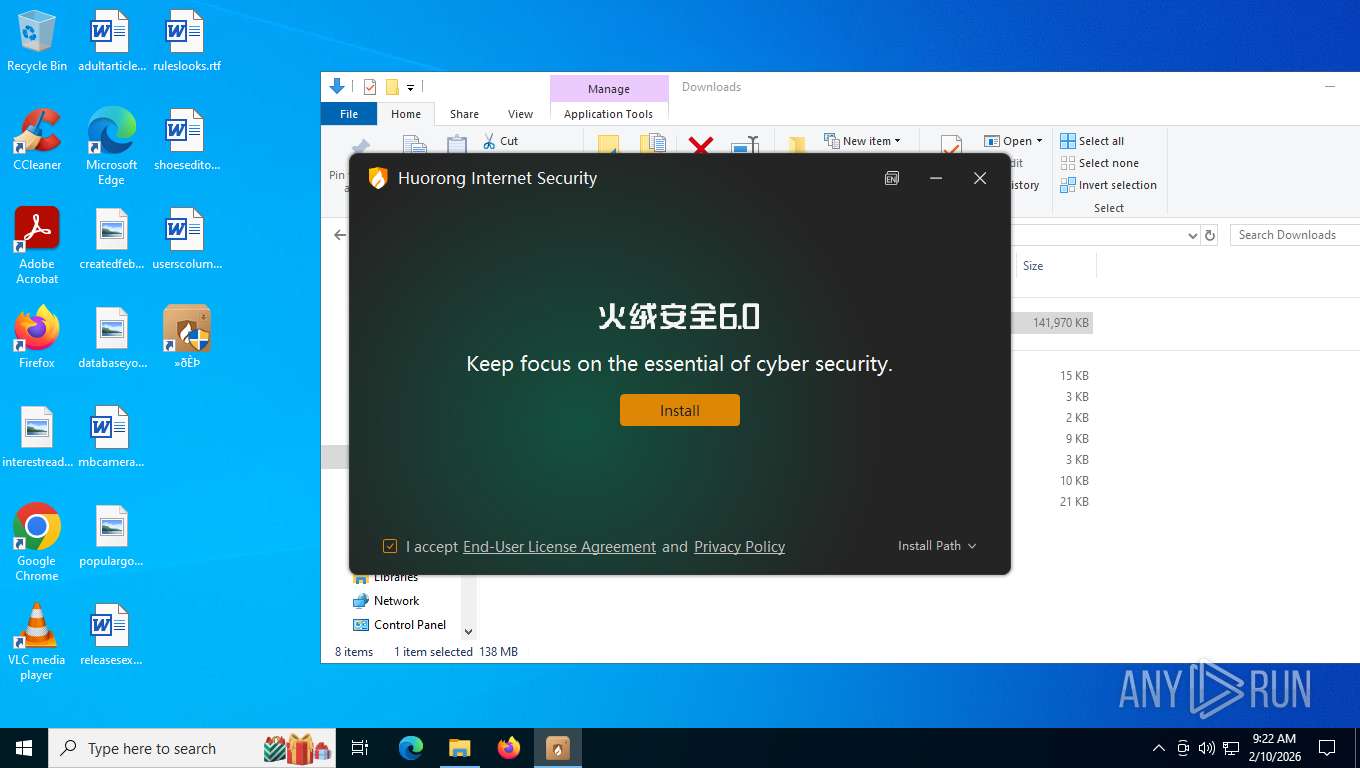
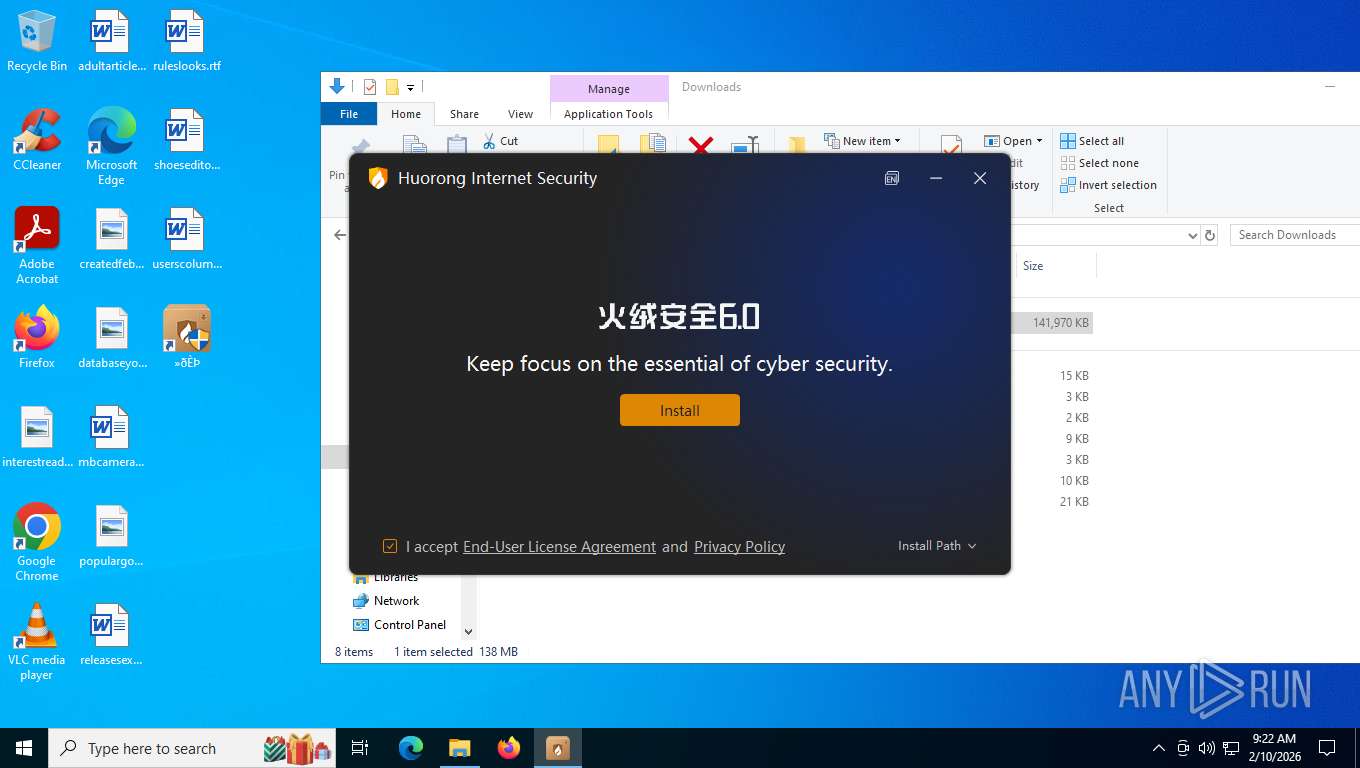
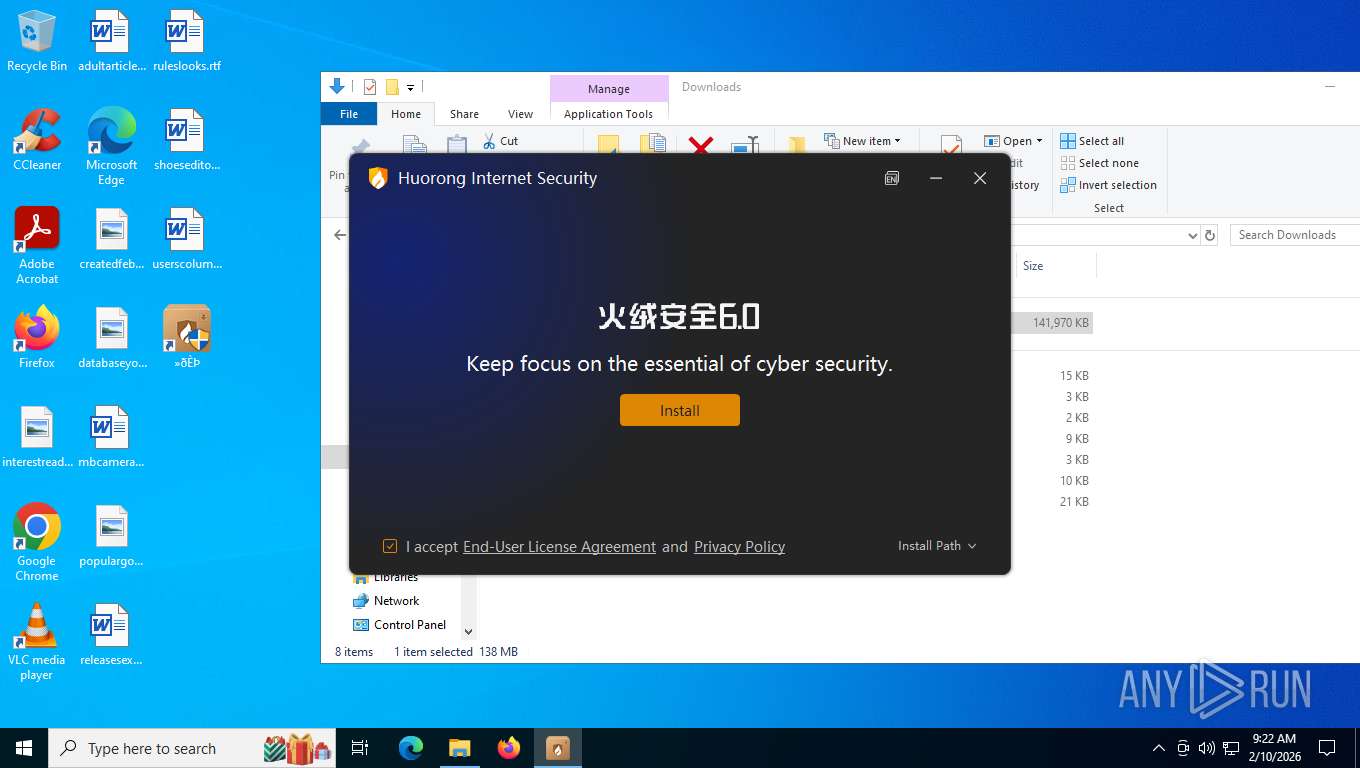
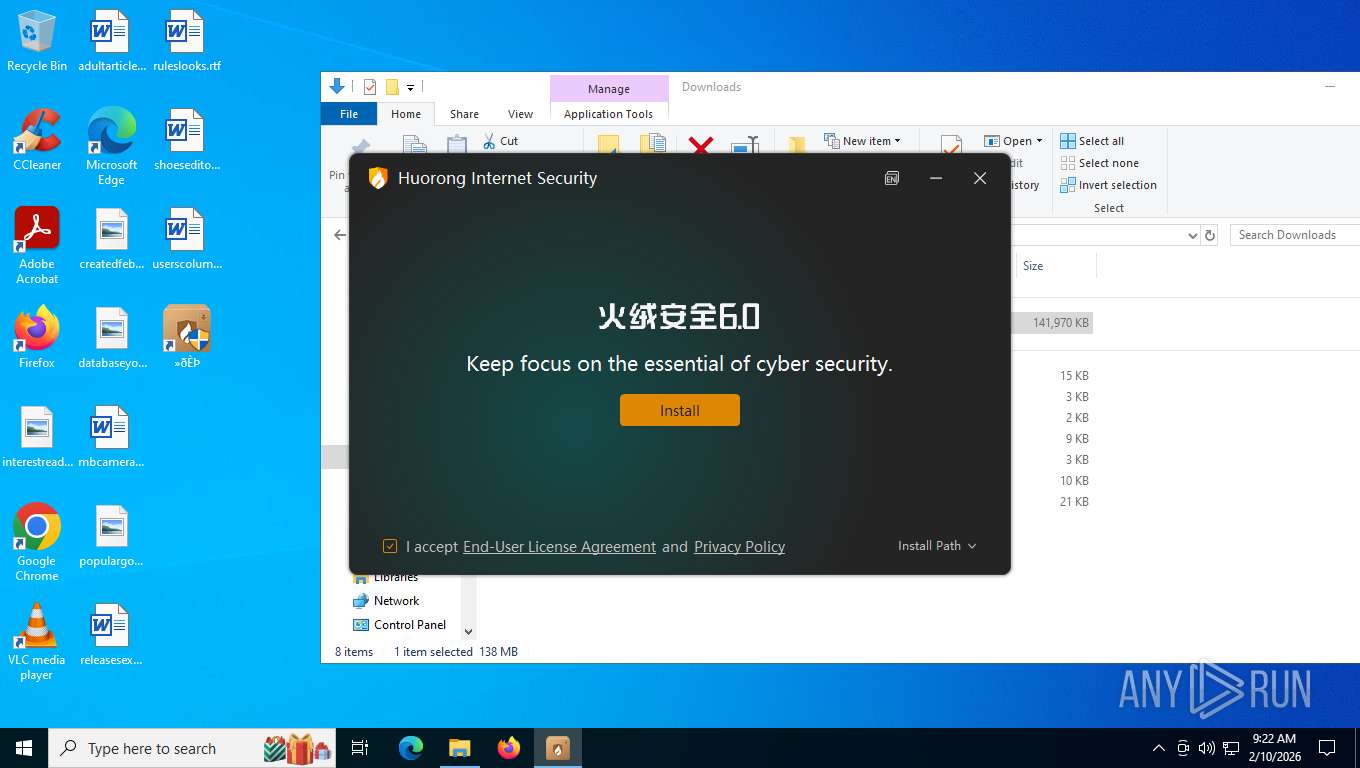
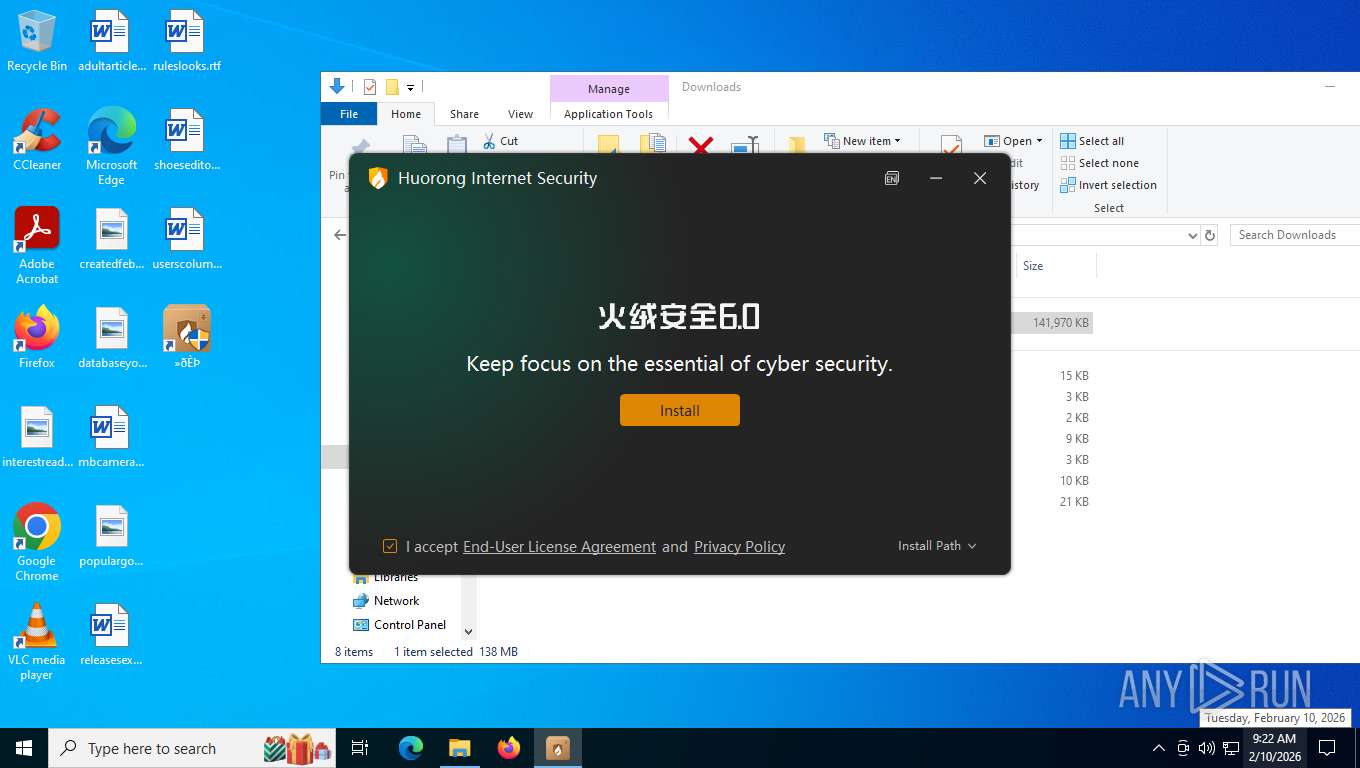
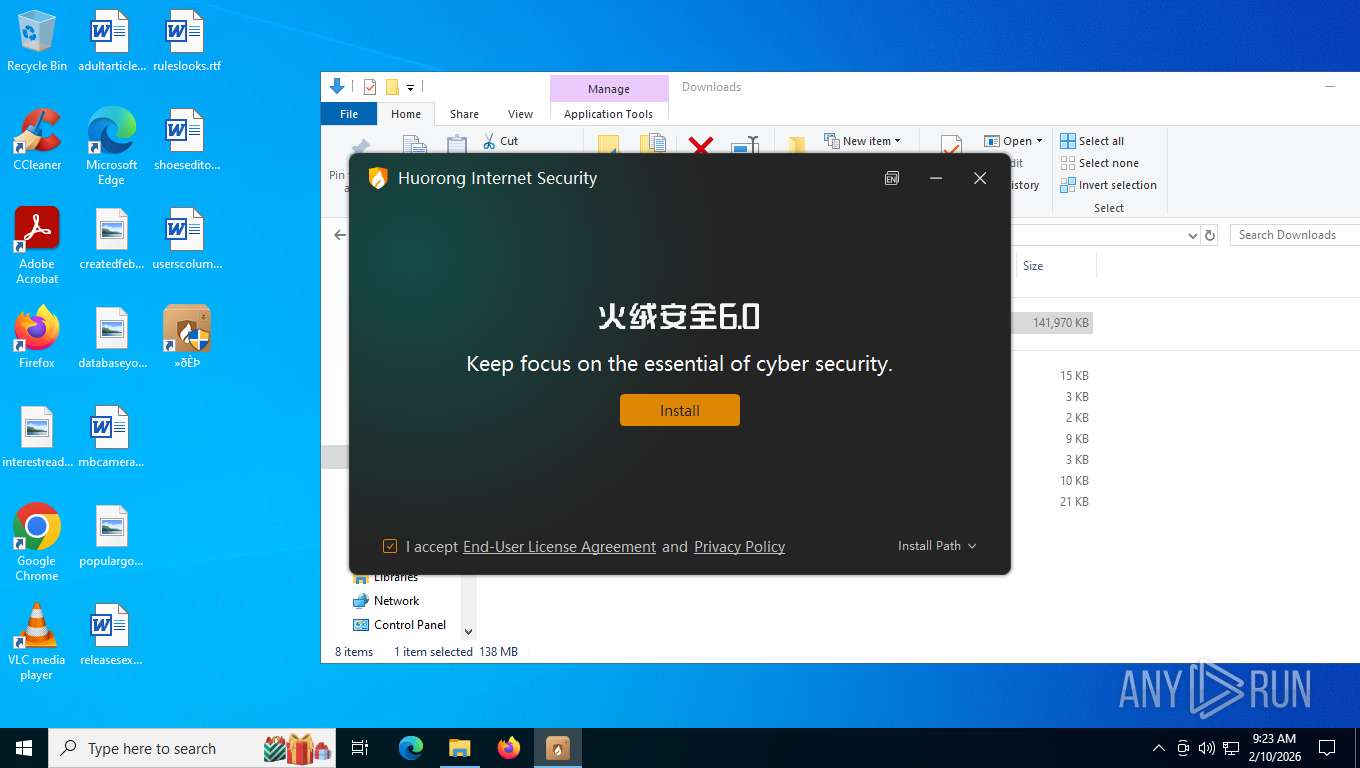
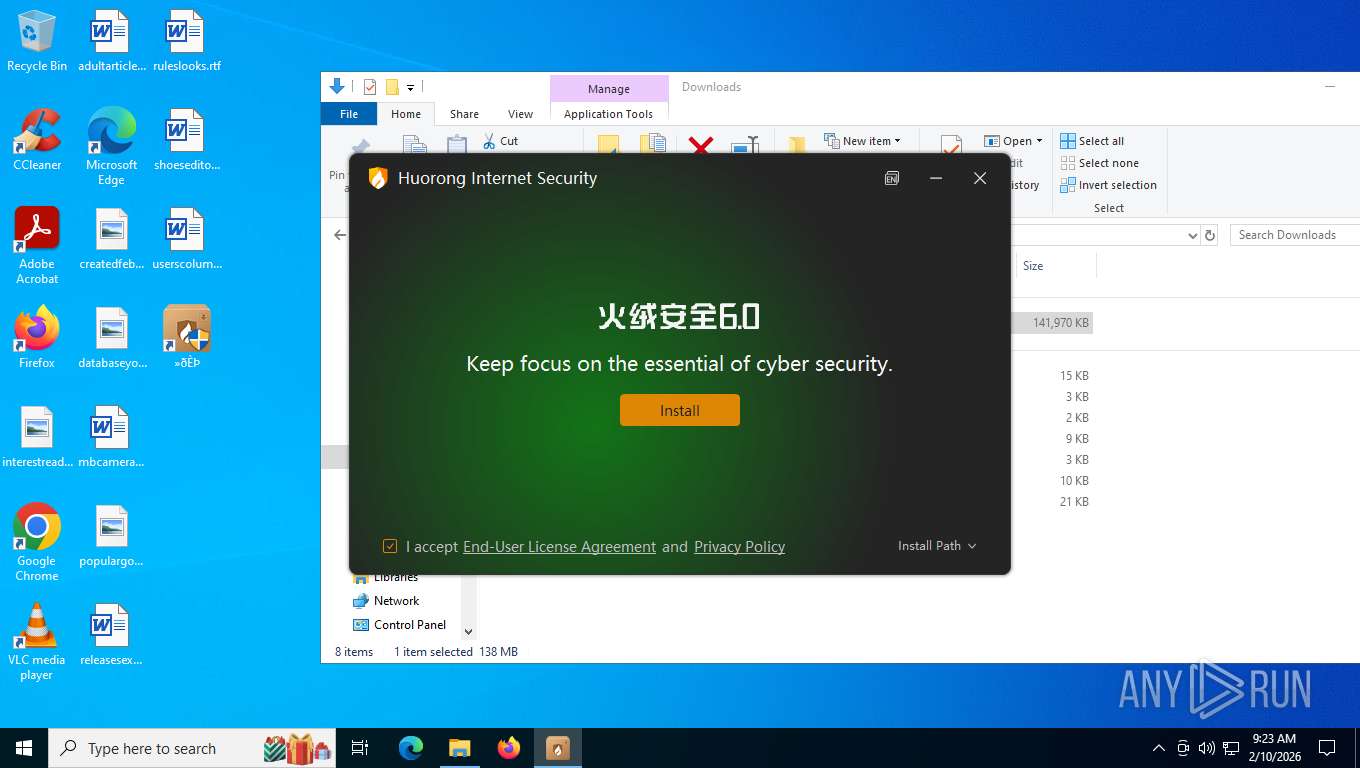
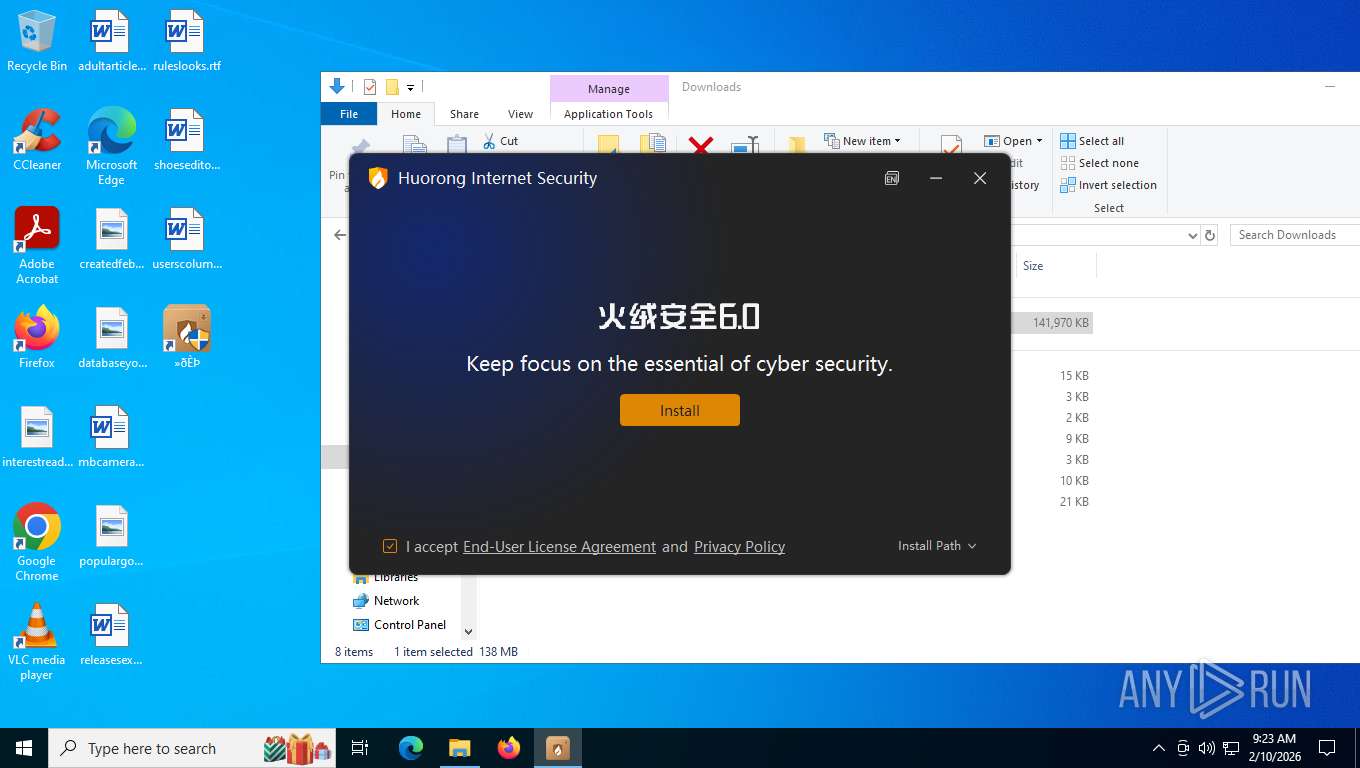
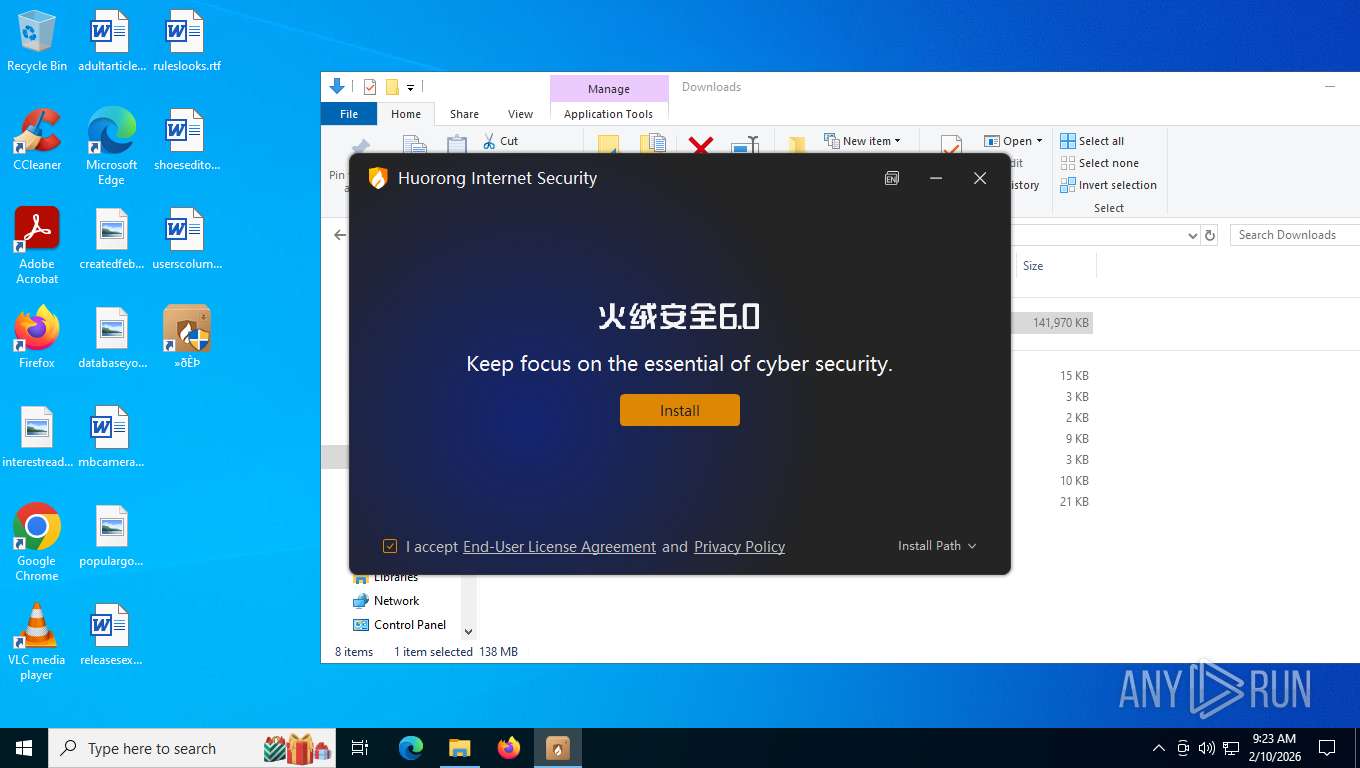
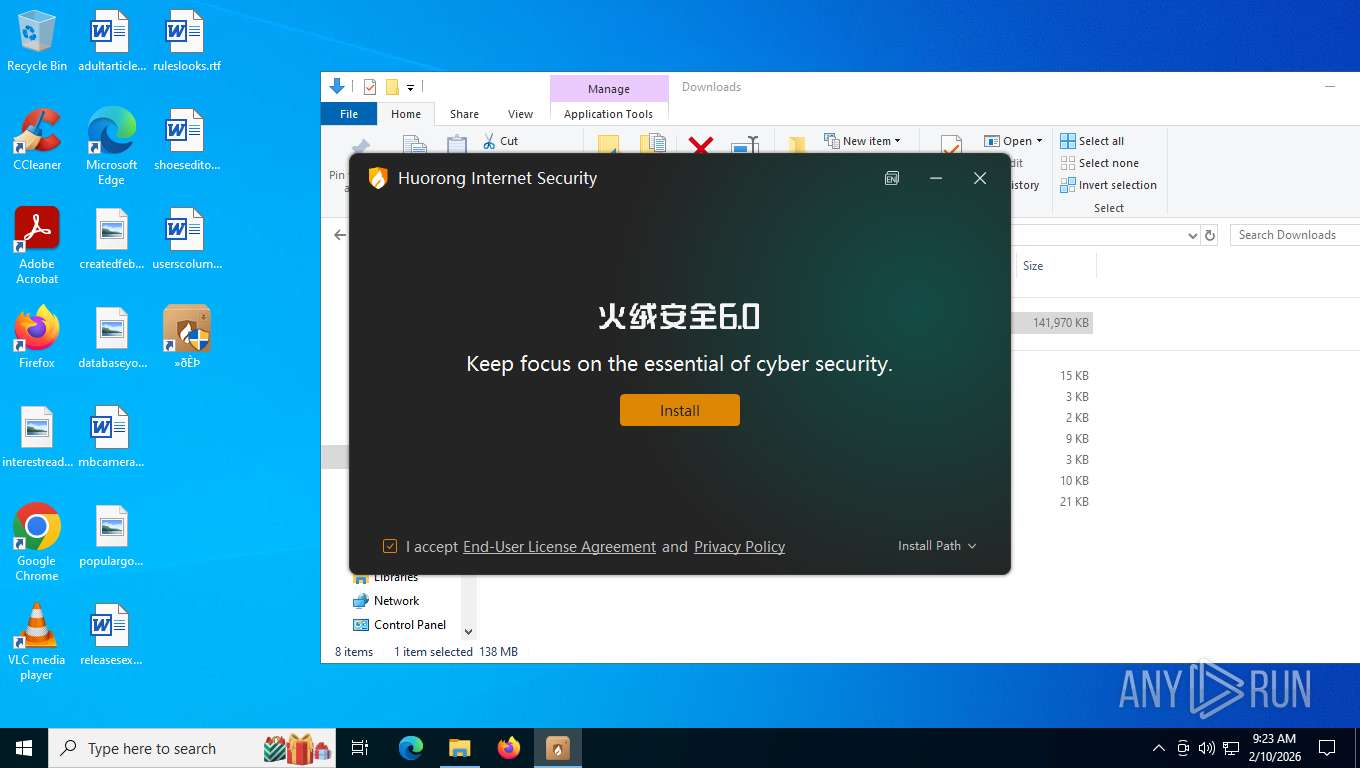
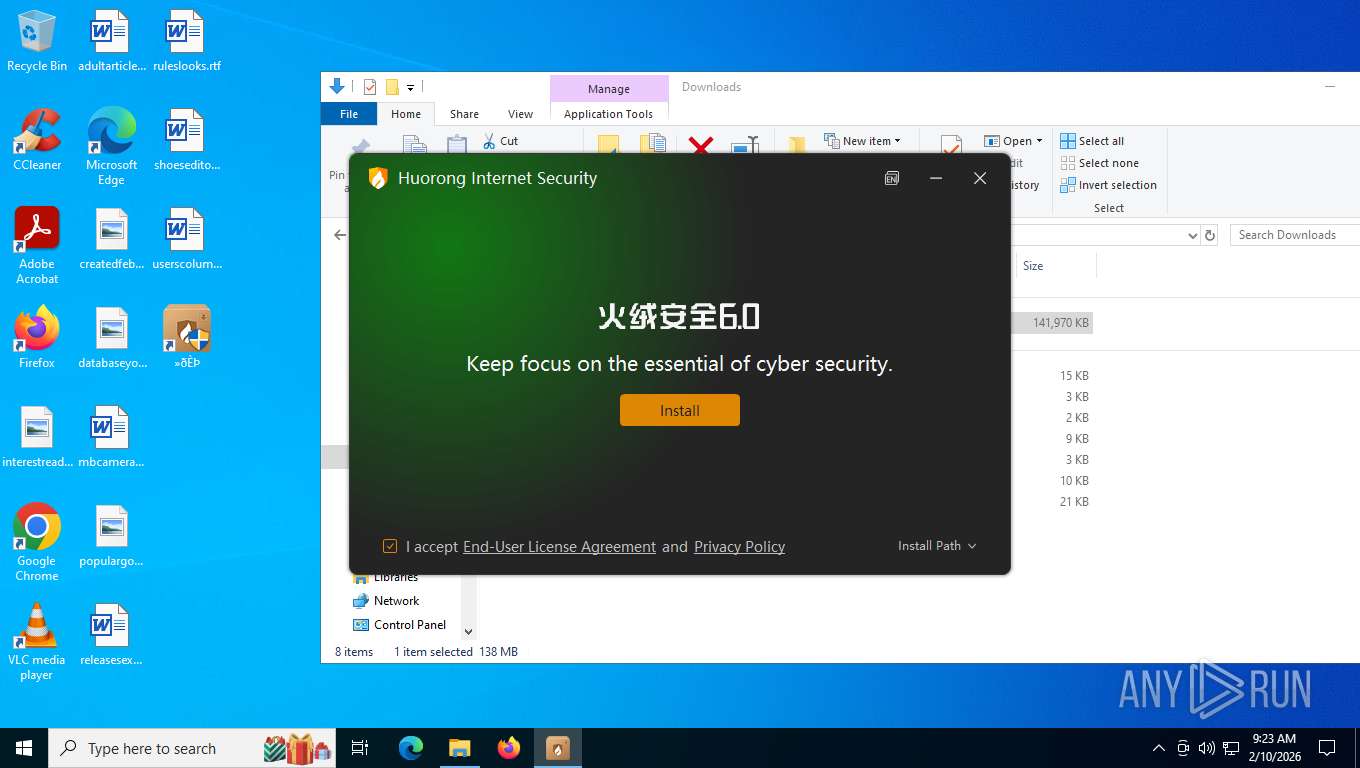
| 2284 | "C:\Users\admin\AppData\Local\Temp\sysdiag-all-x64-6.0.8.5-2026.01.11.1.exe" | C:\Users\admin\AppData\Local\Temp\sysdiag-all-x64-6.0.8.5-2026.01.11.1.exe | explorer.exe | ||||||||||||
User: admin Company: Beijing Huorong Network Technology Co., Ltd. Integrity Level: HIGH Description: Huorong Internet Security Version: 6.0.8.5 Modules
| |||||||||||||||
| 2372 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=6428,i,10788441984877532616,2257086624424998160,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=6636 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2872 | "C:\Users\admin\AppData\Roaming\trvePath\WavesSvc64.exe" /run | C:\Users\admin\AppData\Roaming\trvePath\WavesSvc64.exe | — | svchost.exe | |||||||||||
User: admin Company: 深圳市迅雷网络技术有限公司 Integrity Level: HIGH Description: 迅雷游戏 Version: 1.0.0.38 Modules
| |||||||||||||||
| 3644 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=asset_store.mojom.AssetStoreService --lang=en-US --service-sandbox-type=asset_store_service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=5720,i,10788441984877532616,2257086624424998160,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=5648 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 4128 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --disable-features=HttpsUpgrades,HttpsFirstModeV2,HttpsOnlyMode,HttpsFirstBalancedMode --no-first-run --no-default-browser-check https://wormhole.app/YZRBZY#zTOxo-eainBbe7iA0c4AAg | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 4368 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --pdf-upsell-enabled --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=5 --always-read-main-dll --field-trial-handle=3636,i,10788441984877532616,2257086624424998160,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=3744 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
5 831
Read events
5 831
Write events
0
Delete events
0
Modification events
Executable files
27
Suspicious files
127
Text files
274
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4128 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF1e4f75.TMP | — | |
MD5:— | SHA256:— | |||
| 4128 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4128 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF1e4f75.TMP | — | |
MD5:— | SHA256:— | |||
| 4128 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF1e4f75.TMP | — | |
MD5:— | SHA256:— | |||
| 4128 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4128 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF1e4f75.TMP | — | |
MD5:— | SHA256:— | |||
| 4128 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF1e4f75.TMP | — | |
MD5:— | SHA256:— | |||
| 4128 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4128 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4128 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
133
TCP/UDP connections
523
DNS requests
65
Threats
95
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 104.82.114.5:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAjTxtAB8my1oj8MfWpz%2F7Y%3D | US | binary | 313 b | whitelisted |
— | — | GET | 200 | 204.79.197.203:80 | http://oneocsp.microsoft.com/ocsp/MFQwUjBQME4wTDAJBgUrDgMCGgUABBQ3L3%2F%2Fa6ADK8NraY2GXzVaYrHG4AQUb6t%2B2v%2BXQ3LsO2d33oJhNYhHQoUCEzMAAAAGb6JMMcOVb6sAAAAAAAY%3D | US | binary | 959 b | whitelisted |
7772 | msedge.exe | GET | 200 | 150.171.27.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:VznTPB_un0ACK6oQRYi-a6RHhcRG7VG14BSoLcEjYx8&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | US | text | 99 b | whitelisted |
7772 | msedge.exe | GET | 200 | 150.171.22.17:443 | https://config.edge.skype.com/config/v1/Edge/133.0.3065.92?clientId=4489578223053569932&agents=Edge%2CEdgeConfig%2CEdgeServices%2CEdgeFirstRun%2CEdgeFirstRunConfig&osname=win&client=edge&channel=stable&scpfre=0&osarch=x86_64&osver=10.0.19045&wu=1&devicefamily=desktop&uma=0&sessionid=66&mngd=0&installdate=1661339457&edu=0&soobedate=1504771245&bphint=2&fg=1&lbfgdate=1766135237&lafgdate=0 | US | text | 4.30 Kb | whitelisted |
7772 | msedge.exe | GET | 200 | 150.171.28.11:443 | https://edge.microsoft.com/serviceexperimentation/v3/?osname=win&channel=stable&osver=10.0.19045&devicefamily=desktop&installdate=1661339457&clientversion=133.0.3065.92&experimentationmode=2&scpguard=0&scpfull=0&scpver=0 | US | text | 446 b | whitelisted |
7772 | msedge.exe | GET | 200 | 104.18.23.222:443 | https://copilot.microsoft.com/c/api/user/eligibility | US | text | 25 b | whitelisted |
7772 | msedge.exe | GET | 200 | 172.67.70.141:443 | https://wormhole.app/images/galaxy.jpg | US | image | 188 Kb | unknown |
7772 | msedge.exe | GET | 200 | 172.67.70.141:443 | https://wormhole.app/YZRBZY | US | html | 87.6 Kb | unknown |
7772 | msedge.exe | GET | 200 | 172.67.70.141:443 | https://wormhole.app/_next/static/chunks/webpack-023767403b8f230c.js | US | text | 4.60 Kb | unknown |
7772 | msedge.exe | GET | 200 | 172.67.70.141:443 | https://wormhole.app/_next/static/chunks/framework-834e107486a0d020.js | US | text | 126 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
1324 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7212 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5568 | SearchApp.exe | 2.16.204.148:443 | www.bing.com | AKAMAI-ASN1 | NL | whitelisted |
— | — | 104.82.114.5:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
— | — | 204.79.197.203:80 | oneocsp.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7772 | msedge.exe | 150.171.22.17:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7772 | msedge.exe | 150.171.27.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7772 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
oneocsp.microsoft.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
wormhole.app |
| unknown |
api.edgeoffer.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7772 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (wormhole .app) |
7772 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (wormhole .app) |
7772 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Domain Observed in TLS SNI (wormhole .app) |
7772 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Domain Observed in TLS SNI (wormhole .app) |
7772 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Domain Observed in TLS SNI (wormhole .app) |
7772 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Domain Observed in TLS SNI (wormhole .app) |
7772 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (wormhole .app) |
7772 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (wormhole .app) |
7772 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Domain Observed in TLS SNI (wormhole .app) |
7772 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Domain Observed in TLS SNI (wormhole .app) |