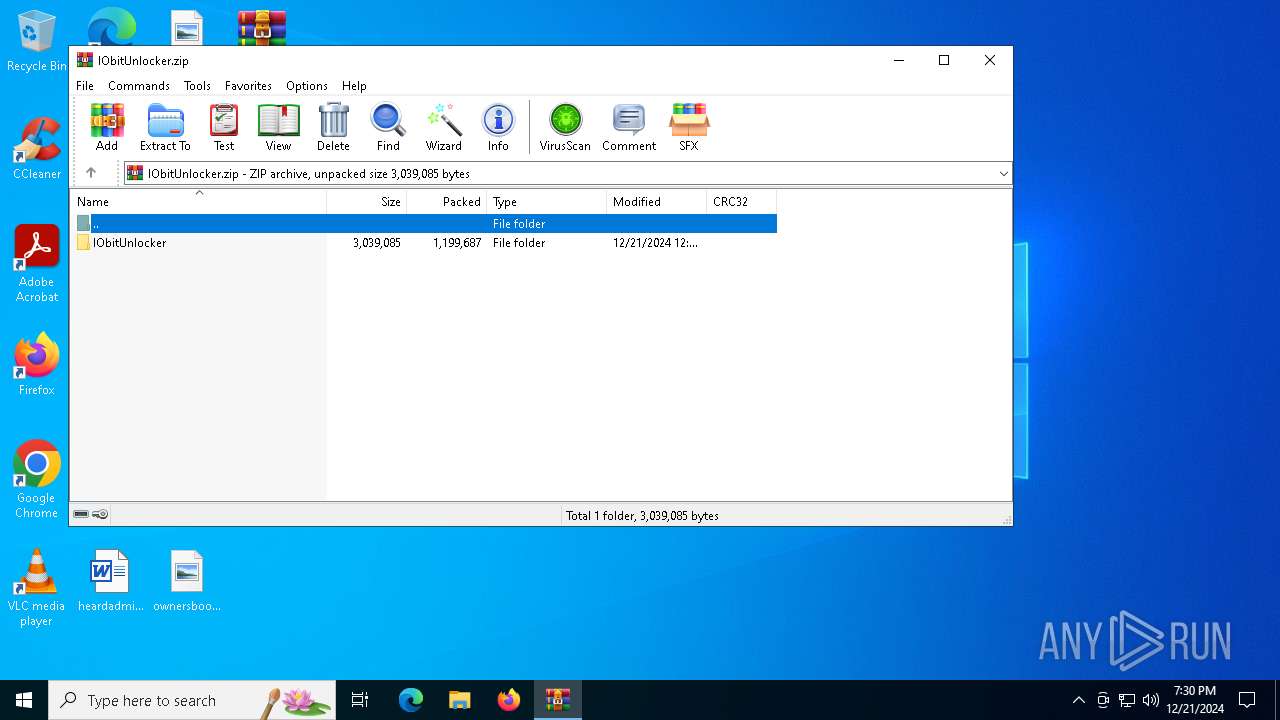
| File name: | IObitUnlocker.zip |
| Full analysis: | https://app.any.run/tasks/2fb9904f-83e1-4162-b81f-2eac2f40edf6 |
| Verdict: | Malicious activity |
| Analysis date: | December 21, 2024, 19:29:58 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=store |
| MD5: | 2A12DE940BE492FA9F65B77903C455A2 |
| SHA1: | F790289DE300CC53DBE9A8DA247C907137E5B005 |
| SHA256: | CD17FD2149133C39E5BF2F32F4526C2C06A8B556F4B10CBB03B799F52DFE4CDE |
| SSDEEP: | 49152:L3SlI6dXxHBG4vO4GTt8pWWOMGX4gQbZVtu9Jpn4IS4mTW3I1WwOULip/hnhDrG0:ShJvO4IuGogQI9Jpn4RoOyUep/1hDreY |
MALICIOUS
Bypass execution policy to execute commands
- powershell.exe (PID: 6744)
- powershell.exe (PID: 6980)
Generic archive extractor
- WinRAR.exe (PID: 6548)
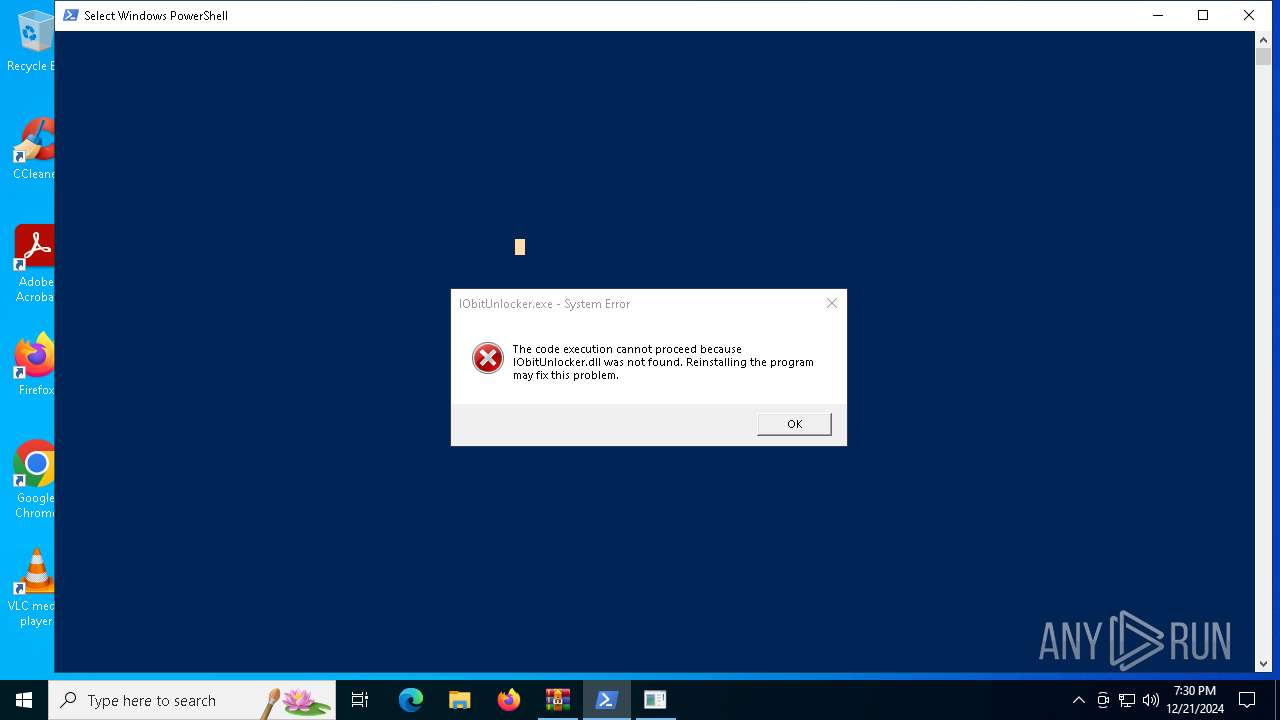
Executing a file with an untrusted certificate
- IObitUnlocker.exe (PID: 6968)
Changes powershell execution policy (Bypass)
- wscript.exe (PID: 6812)
SUSPICIOUS
The process executes Powershell scripts
- wscript.exe (PID: 6812)
Possibly malicious use of IEX has been detected
- wscript.exe (PID: 6812)
Likely accesses (executes) a file from the Public directory
- powershell.exe (PID: 6980)
Runs shell command (SCRIPT)
- wscript.exe (PID: 6812)
Starts POWERSHELL.EXE for commands execution
- wscript.exe (PID: 6812)
INFO
Manual execution by a user
- IObitUnlocker.exe (PID: 6752)
- powershell.exe (PID: 6744)
- wscript.exe (PID: 6812)
- IObitUnlocker.exe (PID: 6968)
The process uses the downloaded file
- wscript.exe (PID: 6812)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 6980)
- powershell.exe (PID: 6744)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 6744)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2024:12:21 12:13:14 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | IObitUnlocker/ |
Total processes
127
Monitored processes
8
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 6548 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\IObitUnlocker.zip | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 6744 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -ep bypass C:\Users\admin\Desktop\Report.ps1 | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6752 | "C:\Users\admin\Desktop\IObitUnlocker.exe" | C:\Users\admin\Desktop\IObitUnlocker.exe | — | explorer.exe | |||||||||||
User: admin Company: IObit Integrity Level: MEDIUM Description: IObitUnlocker Exit code: 3221226540 Version: 1.3.1.26 Modules
| |||||||||||||||
| 6764 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6812 | "C:\WINDOWS\System32\WScript.exe" C:\Users\admin\Desktop\Loader.vbs | C:\Windows\System32\wscript.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 6968 | "C:\Users\admin\Desktop\IObitUnlocker.exe" | C:\Users\admin\Desktop\IObitUnlocker.exe | explorer.exe | ||||||||||||
User: admin Company: IObit Integrity Level: HIGH Description: IObitUnlocker Exit code: 3221225781 Version: 1.3.1.26 Modules
| |||||||||||||||
| 6980 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -ExecutionPolicy Bypass iex([IO.File]::ReadAllText('C:\Users\Public\IObitUnlocker\Report.ps1')) | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6988 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
11 568
Read events
11 560
Write events
8
Delete events
0
Modification events
| (PID) Process: | (6548) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (6548) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (6548) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (6548) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\IObitUnlocker.zip | |||
| (PID) Process: | (6548) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6548) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6548) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6548) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
0
Suspicious files
4
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6744 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms | binary | |
MD5:625647785FEF9DE434AB02C476CD7B39 | SHA256:D90A2E504E71BD84051DB072266AB55B91D54ADD25EBB9B2CB06804317217685 | |||
| 6744 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_4roh44n3.q5f.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6744 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms~RF13734f.TMP | binary | |
MD5:D040F64E9E7A2BB91ABCA5613424598E | SHA256:D04E0A6940609BD6F3B561B0F6027F5CA4E8C5CF0FB0D0874B380A0374A8D670 | |||
| 6744 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_k4uqcqhn.dup.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6980 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:8A2769FD9B45ACC222FD843CFFA1EB51 | SHA256:C5D947C3C518C5FB76A14E06AAA4EC952A715B7407482AB772F1AB2C6B37B862 | |||
| 6980 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_nuxwe4jb.1z1.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6980 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_a43jardc.oyn.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6744 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\JPCJXTYZZSABH0QLDR8Z.temp | binary | |
MD5:625647785FEF9DE434AB02C476CD7B39 | SHA256:D90A2E504E71BD84051DB072266AB55B91D54ADD25EBB9B2CB06804317217685 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
23
DNS requests
8
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2624 | svchost.exe | GET | 304 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2624 | svchost.exe | GET | 304 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2624 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4712 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 104.126.37.130:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
2624 | svchost.exe | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
2624 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |