| File name: | cd103fd7e6bd4213e3bf138a3b40d77aa2980161bdddd88d0f4b227224d4bcd2.exe |
| Full analysis: | https://app.any.run/tasks/8f844011-a443-4f77-8021-05b02a11eda7 |
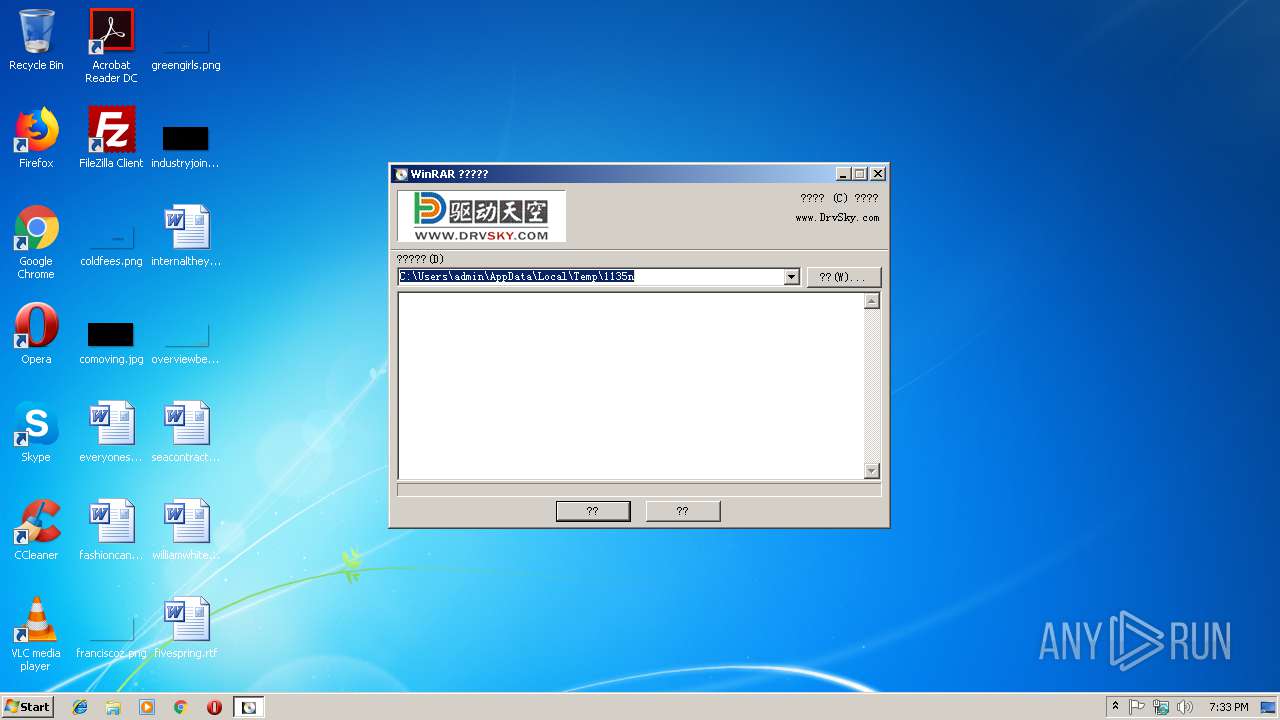
| Verdict: | Malicious activity |
| Analysis date: | February 18, 2019, 19:33:26 |
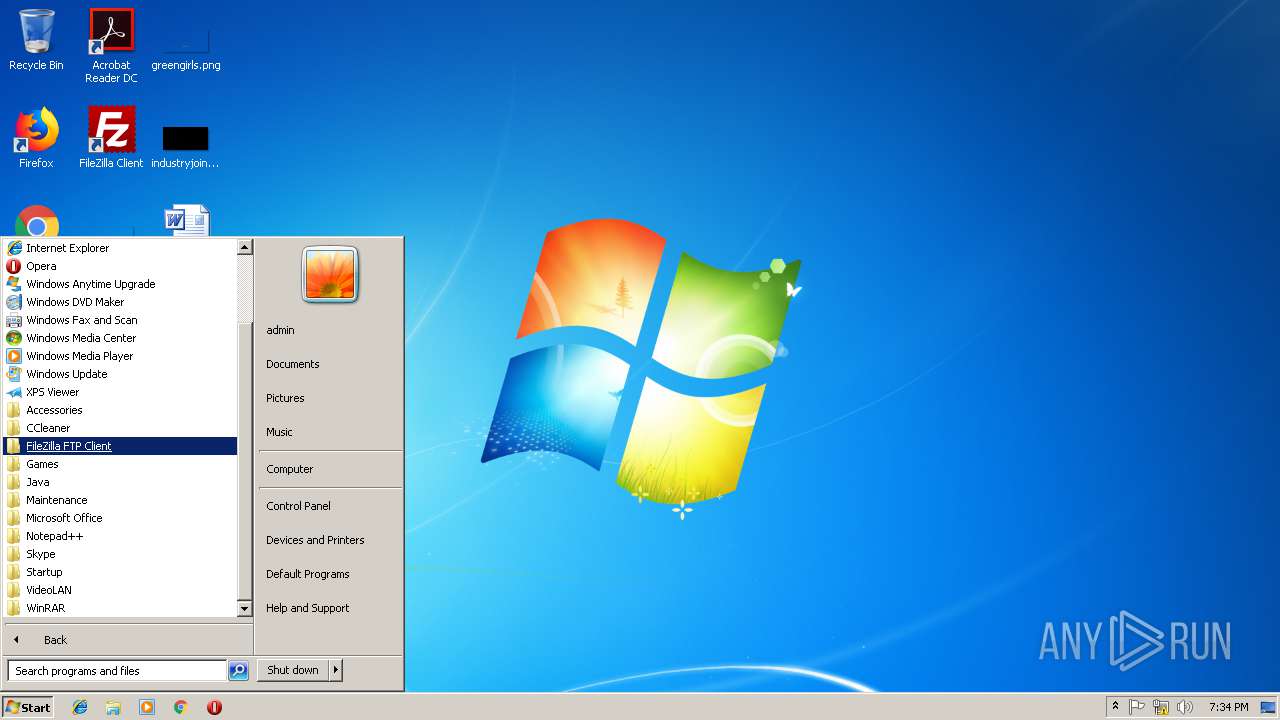
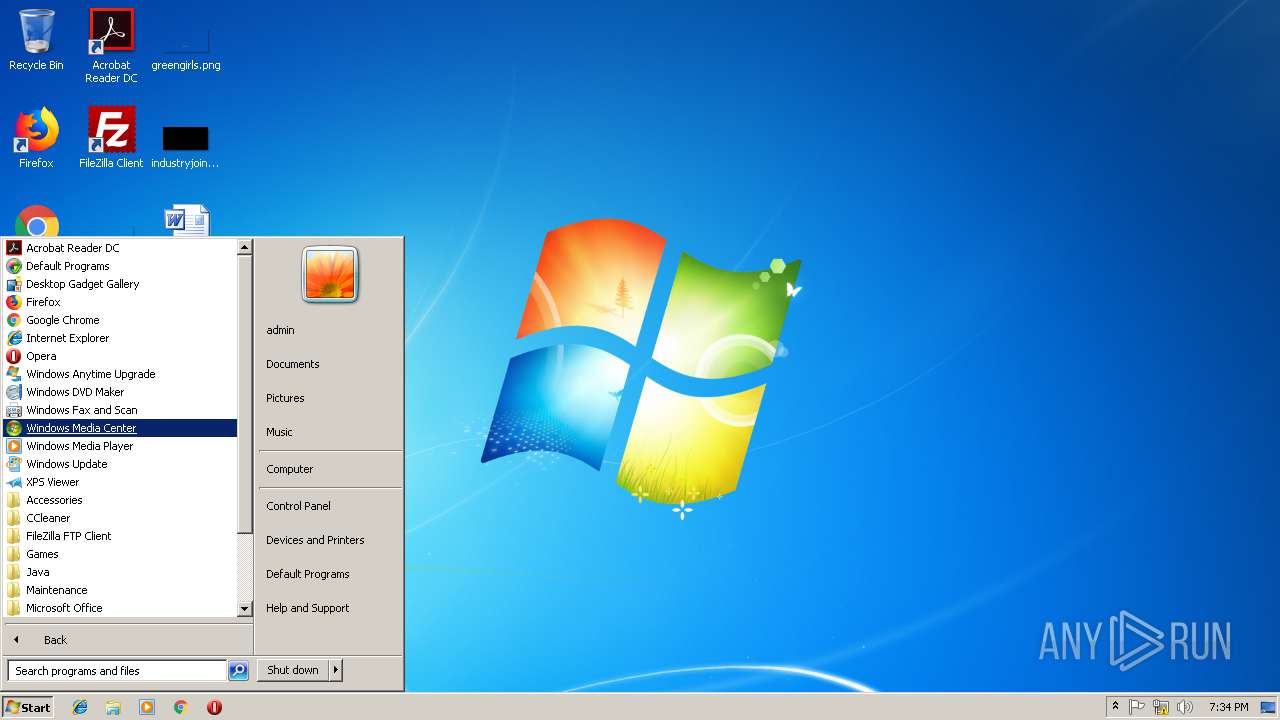
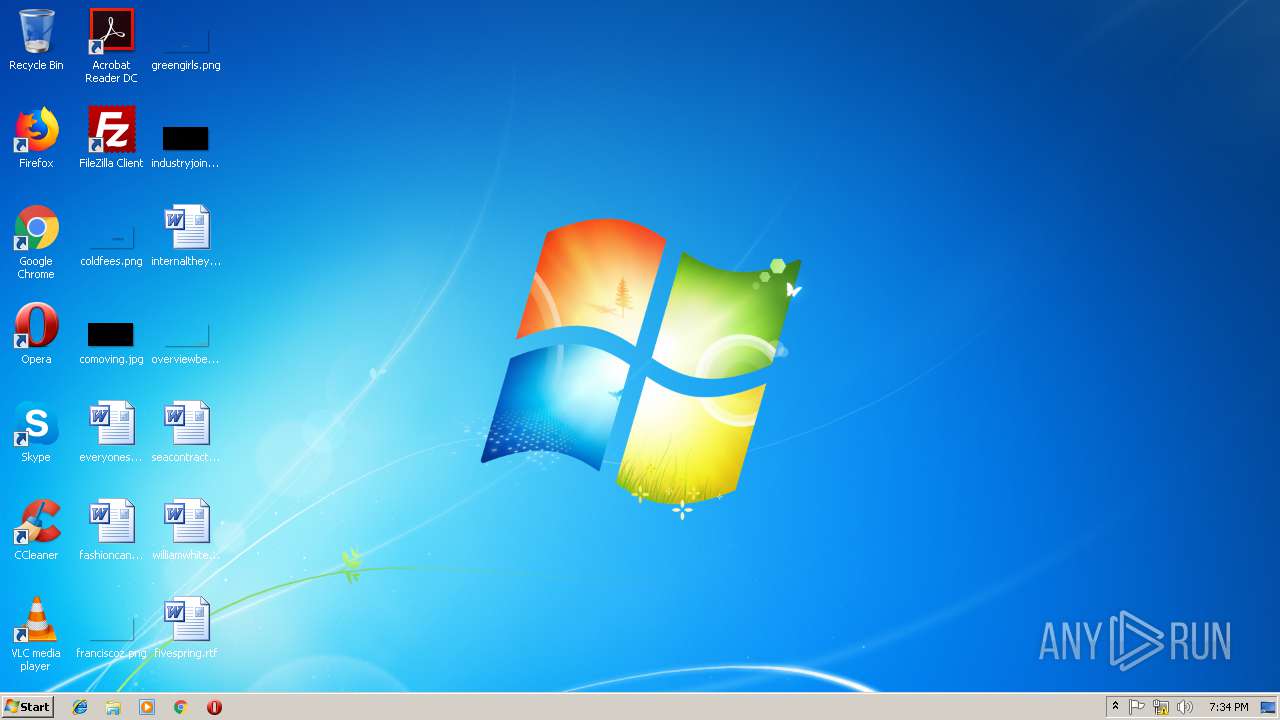
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, RAR self-extracting archive |
| MD5: | 87E160812F2A47DF1B56A0975A566704 |
| SHA1: | 4F27D9371A55894F28DEDF3F6C51CE30C6CB7393 |
| SHA256: | CD103FD7E6BD4213E3BF138A3B40D77AA2980161BDDDD88D0F4B227224D4BCD2 |
| SSDEEP: | 196608:5tei7+jn2LyLawh8h2Tfedww+FchdE6Bnl+cM5NMOq0nLw:6Lj2dga2Tf1b6O6BnxM5KDX |
MALICIOUS
Changes settings of System certificates
- cd103fd7e6bd4213e3bf138a3b40d77aa2980161bdddd88d0f4b227224d4bcd2.exe (PID: 2780)
Starts NET.EXE for service management
- cmd.exe (PID: 3088)
Application was dropped or rewritten from another process
- dpinst32.exe (PID: 3508)
- Setup.exe (PID: 2480)
SUSPICIOUS
Starts CMD.EXE for commands execution
- cmd.exe (PID: 3088)
- Setup.exe (PID: 2480)
Changes tracing settings of the file or console
- cd103fd7e6bd4213e3bf138a3b40d77aa2980161bdddd88d0f4b227224d4bcd2.exe (PID: 2780)
Adds / modifies Windows certificates
- cd103fd7e6bd4213e3bf138a3b40d77aa2980161bdddd88d0f4b227224d4bcd2.exe (PID: 2780)
Reads internet explorer settings
- cd103fd7e6bd4213e3bf138a3b40d77aa2980161bdddd88d0f4b227224d4bcd2.exe (PID: 2780)
Starts SC.EXE for service management
- cmd.exe (PID: 3088)
- cmd.exe (PID: 3664)
Creates files in the Windows directory
- dpinst32.exe (PID: 3508)
- DrvInst.exe (PID: 2552)
- DrvInst.exe (PID: 3288)
Creates files in the driver directory
- DrvInst.exe (PID: 2552)
- DrvInst.exe (PID: 3288)
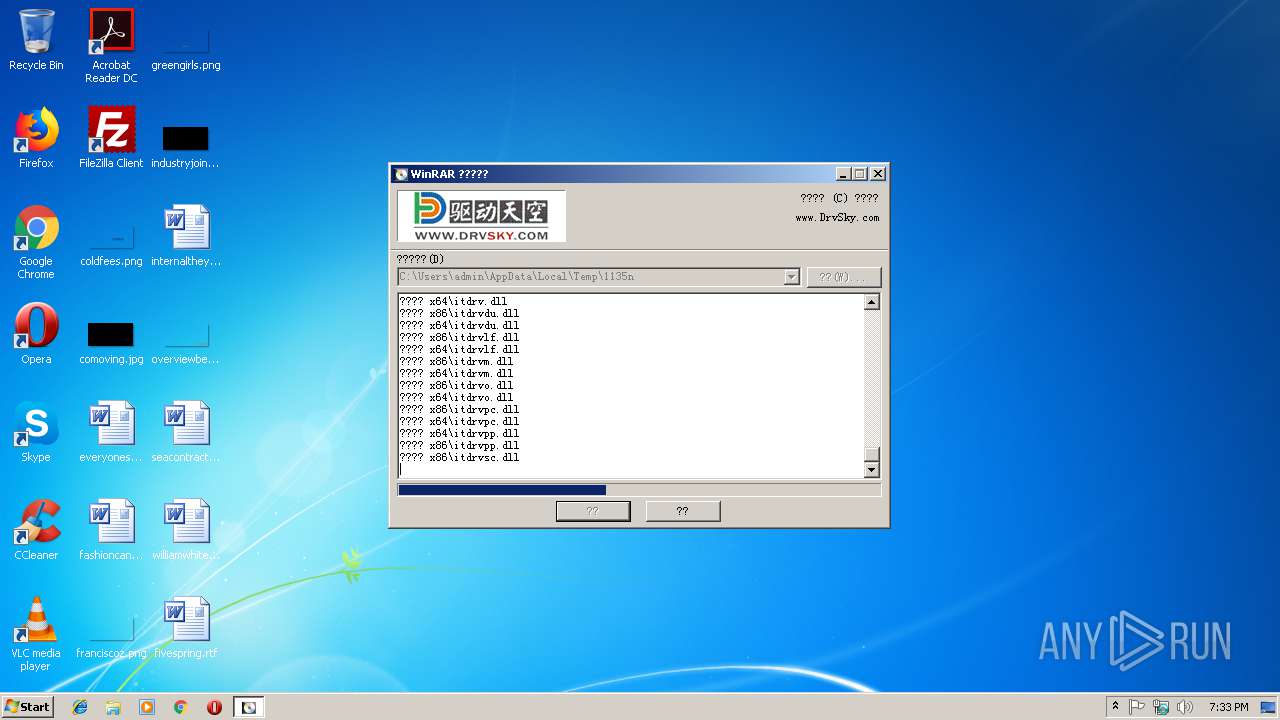
Executable content was dropped or overwritten
- dpinst32.exe (PID: 3508)
- DrvInst.exe (PID: 3288)
- DrvInst.exe (PID: 2552)
- cd103fd7e6bd4213e3bf138a3b40d77aa2980161bdddd88d0f4b227224d4bcd2.exe (PID: 2780)
Removes files from Windows directory
- DrvInst.exe (PID: 2552)
- DrvInst.exe (PID: 3288)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2010:03:15 07:28:07+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 58368 |
| InitializedDataSize: | 38400 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x8c84 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 15-Mar-2010 06:28:07 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 15-Mar-2010 06:28:07 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000E299 | 0x0000E400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.51153 |
.rdata | 0x00010000 | 0x000016FB | 0x00001800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.62548 |
.data | 0x00012000 | 0x0000B96C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.47787 |
.CRT | 0x0001E000 | 0x00000010 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.213101 |
.rsrc | 0x0001F000 | 0x00007939 | 0x00007A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.12378 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.21862 | 1461 | Latin 1 / Western European | Chinese - PRC | RT_MANIFEST |
7 | 5.31352 | 226 | Latin 1 / Western European | Chinese - PRC | RT_STRING |
8 | 5.80297 | 336 | Latin 1 / Western European | Chinese - PRC | RT_STRING |
9 | 5.46722 | 208 | Latin 1 / Western European | Chinese - PRC | RT_STRING |
100 | 1.91924 | 20 | Latin 1 / Western European | Chinese - PRC | RT_GROUP_ICON |
TITLE_BMP | 3.64328 | 9466 | Latin 1 / Western European | Chinese - PRC | RT_BITMAP |
LICENSEDLG | 3.42766 | 166 | Latin 1 / Western European | Chinese - PRC | RT_DIALOG |
RENAMEDLG | 3.3152 | 258 | Latin 1 / Western European | Chinese - PRC | RT_DIALOG |
REPLACEFILEDLG | 3.73596 | 642 | Latin 1 / Western European | Chinese - PRC | RT_DIALOG |
STARTDLG | 3.97255 | 504 | Latin 1 / Western European | Chinese - PRC | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.DLL |
OLEAUT32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
45
Monitored processes
12
Malicious processes
5
Suspicious processes
0
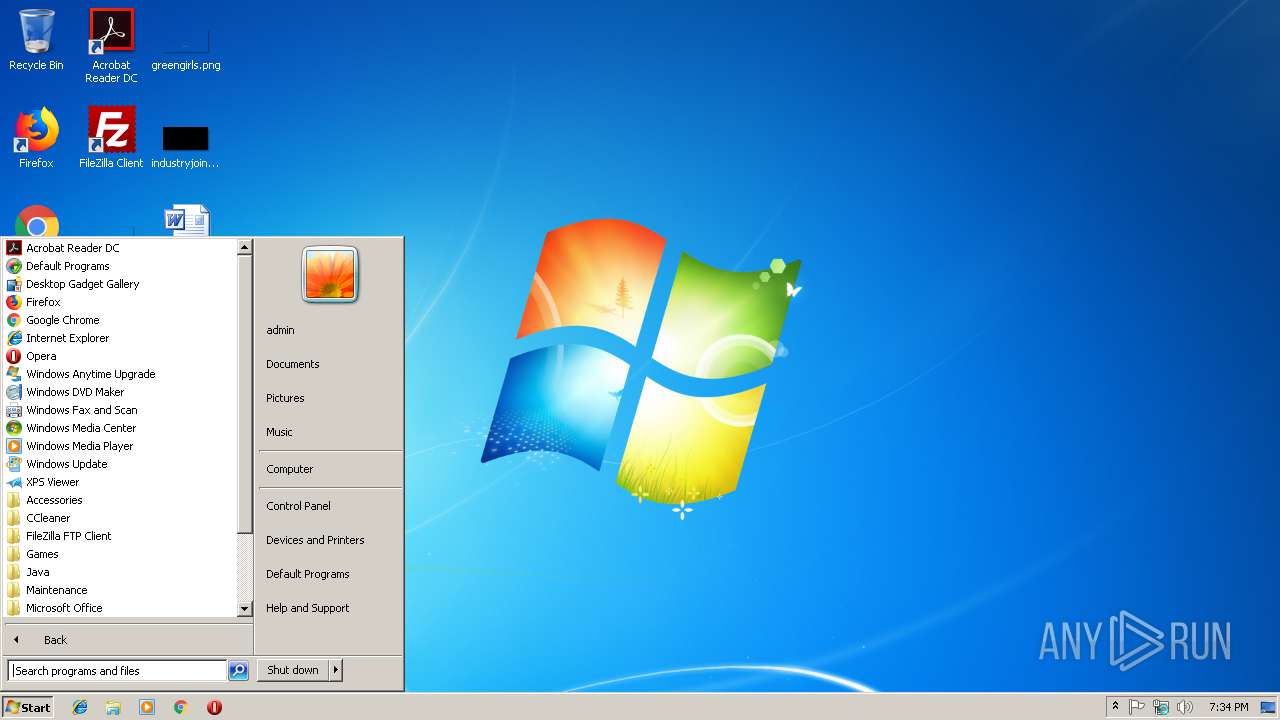
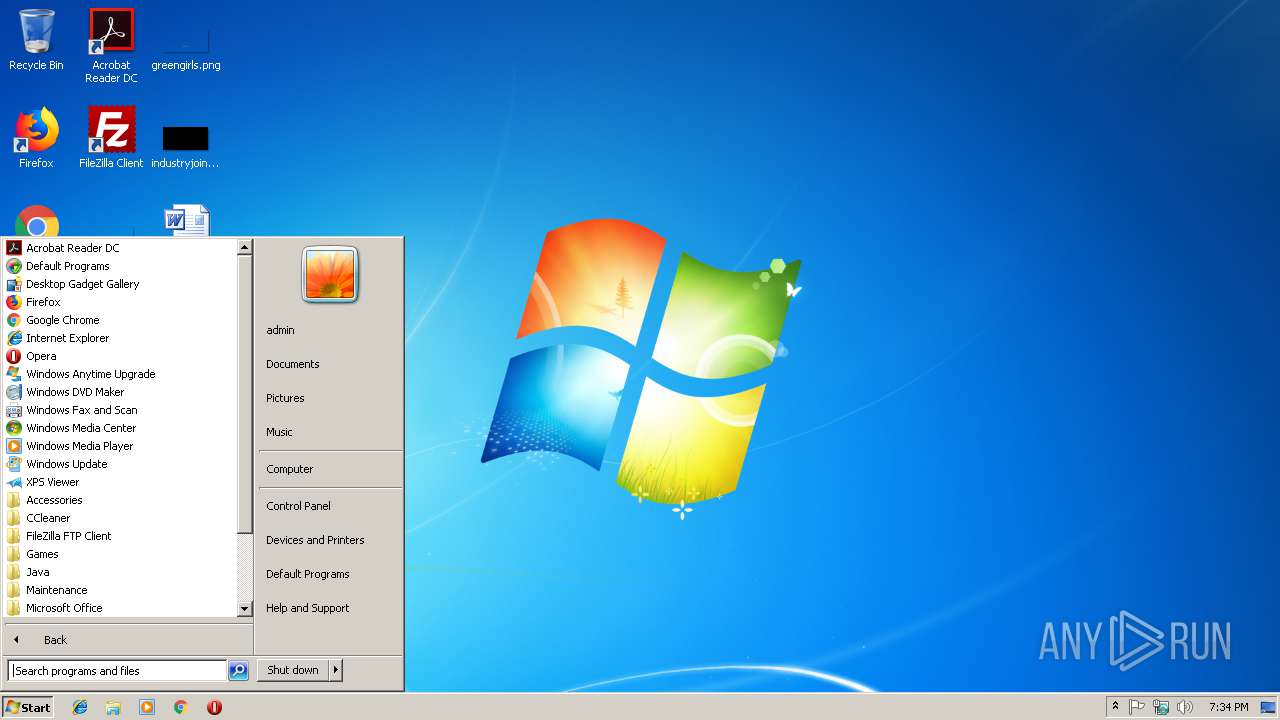
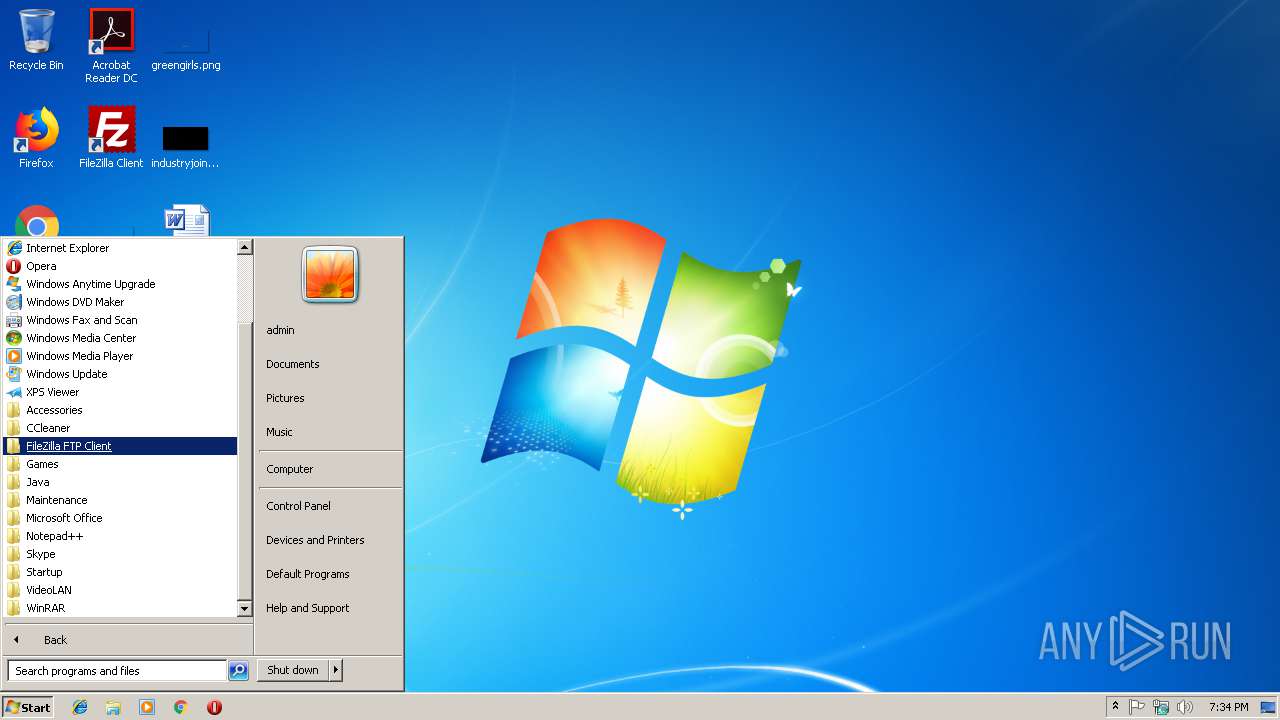
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1868 | C:\Windows\system32\net1 start Spooler | C:\Windows\system32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2200 | sc config Spooler start= auto | C:\Windows\system32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2464 | net start Spooler | C:\Windows\system32\net.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
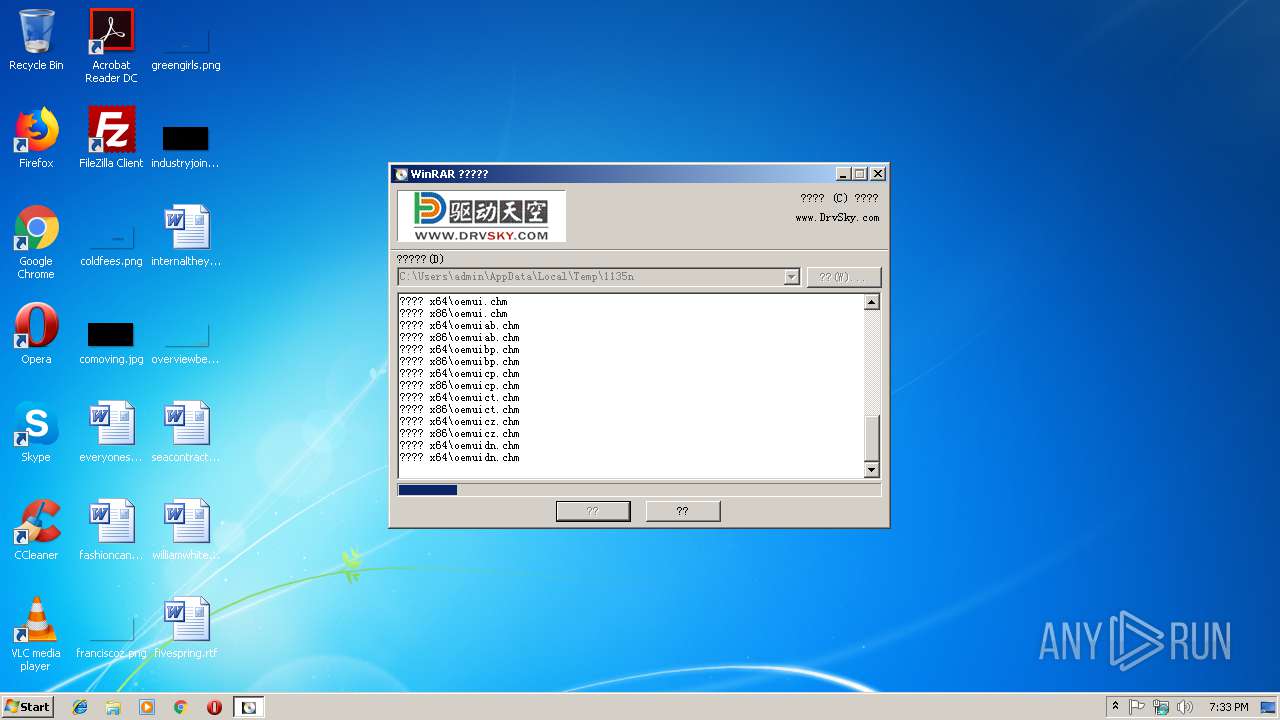
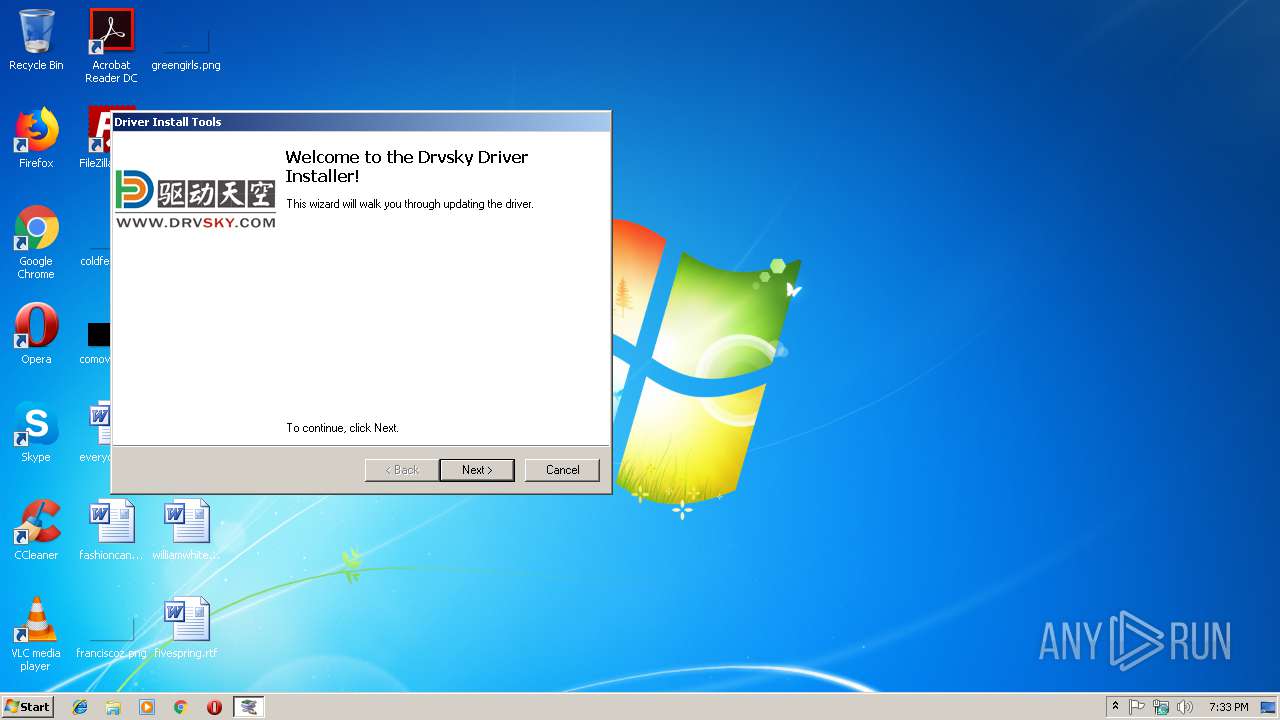
| 2480 | "C:\Users\admin\AppData\Local\Temp\1135n\Setup.exe" | C:\Users\admin\AppData\Local\Temp\1135n\Setup.exe | — | cd103fd7e6bd4213e3bf138a3b40d77aa2980161bdddd88d0f4b227224d4bcd2.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 512 Modules
| |||||||||||||||
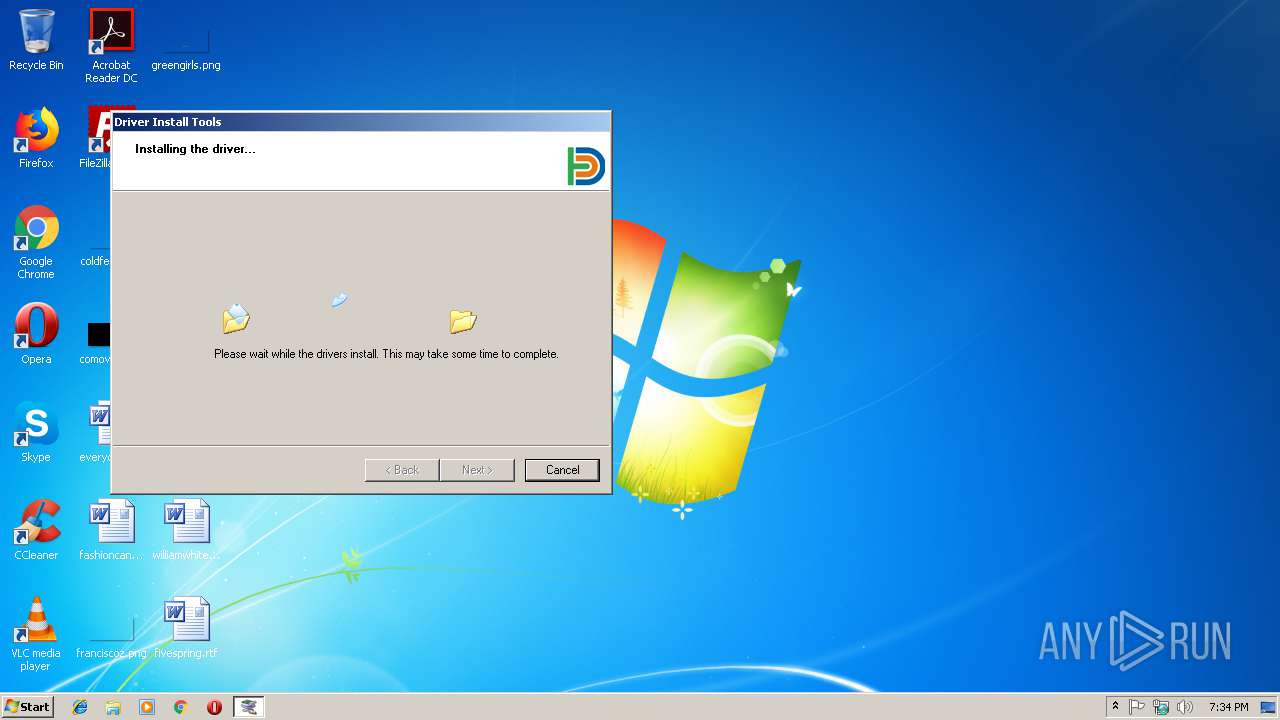
| 2552 | DrvInst.exe "4" "0" "C:\Users\admin\AppData\Local\Temp\{2a325f4f-9546-104d-2914-a276a8337556}\dell1135.inf" "0" "6555ac9f7" "0000055C" "WinSta0\Default" "00000394" "208" "c:\users\admin\appdata\local\temp\1135n\x86" | C:\Windows\system32\DrvInst.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2780 | "C:\Users\admin\AppData\Local\Temp\cd103fd7e6bd4213e3bf138a3b40d77aa2980161bdddd88d0f4b227224d4bcd2.exe" | C:\Users\admin\AppData\Local\Temp\cd103fd7e6bd4213e3bf138a3b40d77aa2980161bdddd88d0f4b227224d4bcd2.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3088 | cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\2480QMIB.bat" "C:\Users\admin\AppData\Local\Temp\1135n\Setup.exe" " | C:\Windows\system32\cmd.exe | — | Setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 512 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3288 | DrvInst.exe "4" "0" "C:\Users\admin\AppData\Local\Temp\{6bc25de7-95c8-10a4-bead-4e0c86b3f045}\sdo2m.inf" "0" "6ac1febfb" "00000394" "WinSta0\Default" "00000298" "208" "c:\users\admin\appdata\local\temp\1135n\x86" | C:\Windows\system32\DrvInst.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3404 | "C:\Users\admin\AppData\Local\Temp\cd103fd7e6bd4213e3bf138a3b40d77aa2980161bdddd88d0f4b227224d4bcd2.exe" | C:\Users\admin\AppData\Local\Temp\cd103fd7e6bd4213e3bf138a3b40d77aa2980161bdddd88d0f4b227224d4bcd2.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 3508 | dpinst32.exe /SA /F /LM /PATH "x86" | C:\Users\admin\AppData\Local\Temp\1135n\dpinst32.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Driver Package Installer Exit code: 512 Version: 2.1 Modules
| |||||||||||||||
Total events
529
Read events
466
Write events
63
Delete events
0
Modification events
| (PID) Process: | (2780) cd103fd7e6bd4213e3bf138a3b40d77aa2980161bdddd88d0f4b227224d4bcd2.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2780) cd103fd7e6bd4213e3bf138a3b40d77aa2980161bdddd88d0f4b227224d4bcd2.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2780) cd103fd7e6bd4213e3bf138a3b40d77aa2980161bdddd88d0f4b227224d4bcd2.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2780) cd103fd7e6bd4213e3bf138a3b40d77aa2980161bdddd88d0f4b227224d4bcd2.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2780) cd103fd7e6bd4213e3bf138a3b40d77aa2980161bdddd88d0f4b227224d4bcd2.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (2780) cd103fd7e6bd4213e3bf138a3b40d77aa2980161bdddd88d0f4b227224d4bcd2.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (2780) cd103fd7e6bd4213e3bf138a3b40d77aa2980161bdddd88d0f4b227224d4bcd2.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2780) cd103fd7e6bd4213e3bf138a3b40d77aa2980161bdddd88d0f4b227224d4bcd2.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2780) cd103fd7e6bd4213e3bf138a3b40d77aa2980161bdddd88d0f4b227224d4bcd2.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2780) cd103fd7e6bd4213e3bf138a3b40d77aa2980161bdddd88d0f4b227224d4bcd2.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RASMANCS |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
Executable files
143
Suspicious files
22
Text files
218
Unknown types
150
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2780 | cd103fd7e6bd4213e3bf138a3b40d77aa2980161bdddd88d0f4b227224d4bcd2.exe | C:\Users\admin\AppData\Local\Temp\1135n\x64\itdrvLC.bmp | image | |
MD5:— | SHA256:— | |||
| 2780 | cd103fd7e6bd4213e3bf138a3b40d77aa2980161bdddd88d0f4b227224d4bcd2.exe | C:\Users\admin\AppData\Local\Temp\1135n\x86\itdrvM3.bmp | image | |
MD5:— | SHA256:— | |||
| 2780 | cd103fd7e6bd4213e3bf138a3b40d77aa2980161bdddd88d0f4b227224d4bcd2.exe | C:\Users\admin\AppData\Local\Temp\1135n\x86\itdrvLC.bmp | image | |
MD5:— | SHA256:— | |||
| 2780 | cd103fd7e6bd4213e3bf138a3b40d77aa2980161bdddd88d0f4b227224d4bcd2.exe | C:\Users\admin\AppData\Local\Temp\1135n\x64\itdrvM3.bmp | image | |
MD5:— | SHA256:— | |||
| 2780 | cd103fd7e6bd4213e3bf138a3b40d77aa2980161bdddd88d0f4b227224d4bcd2.exe | C:\Users\admin\AppData\Local\Temp\1135n\x64\itdrvyc.BMP | image | |
MD5:— | SHA256:— | |||
| 2780 | cd103fd7e6bd4213e3bf138a3b40d77aa2980161bdddd88d0f4b227224d4bcd2.exe | C:\Users\admin\AppData\Local\Temp\1135n\x64\DELL1135.cat | cat | |
MD5:— | SHA256:— | |||
| 2780 | cd103fd7e6bd4213e3bf138a3b40d77aa2980161bdddd88d0f4b227224d4bcd2.exe | C:\Users\admin\AppData\Local\Temp\1135n\x86\itdrvyc.BMP | image | |
MD5:— | SHA256:— | |||
| 2780 | cd103fd7e6bd4213e3bf138a3b40d77aa2980161bdddd88d0f4b227224d4bcd2.exe | C:\Users\admin\AppData\Local\Temp\1135n\x86\sdo2m.cat | cat | |
MD5:— | SHA256:— | |||
| 2780 | cd103fd7e6bd4213e3bf138a3b40d77aa2980161bdddd88d0f4b227224d4bcd2.exe | C:\Users\admin\AppData\Local\Temp\1135n\x86\DELL1135.cat | cat | |
MD5:— | SHA256:— | |||
| 2780 | cd103fd7e6bd4213e3bf138a3b40d77aa2980161bdddd88d0f4b227224d4bcd2.exe | C:\Users\admin\AppData\Local\Temp\1135n\x64\itdrvcp.chm | chm | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
2
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
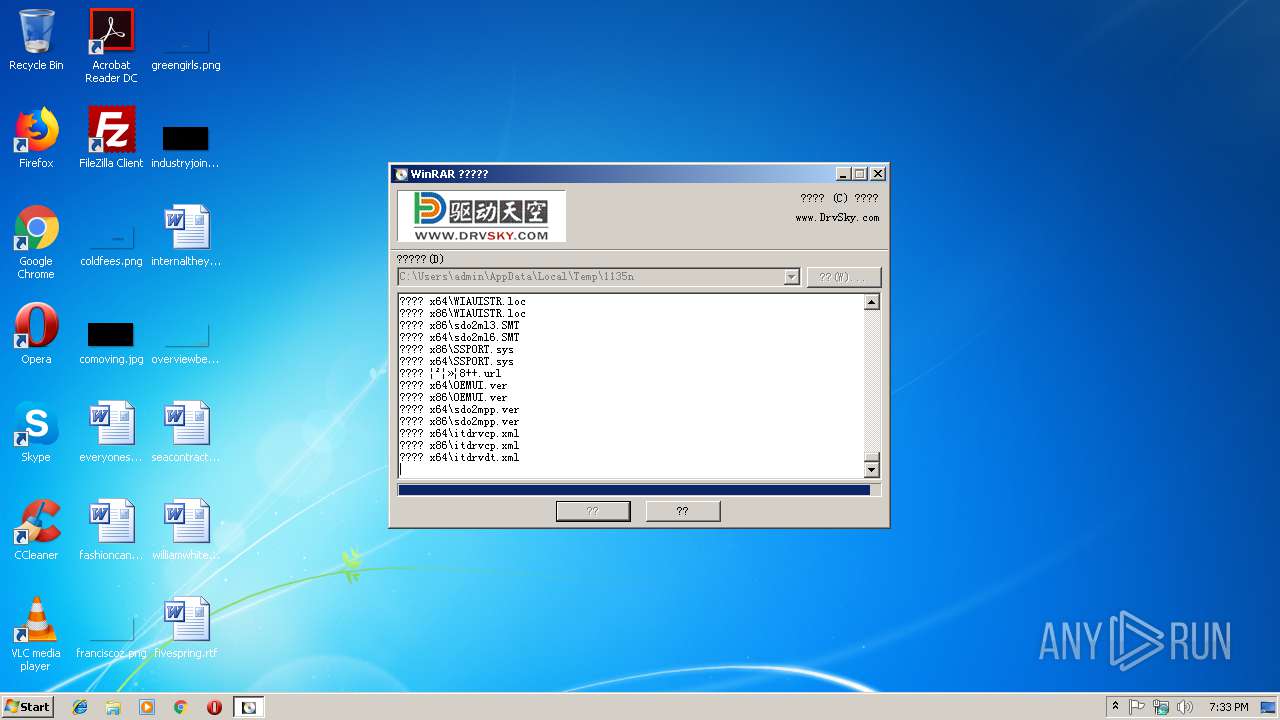
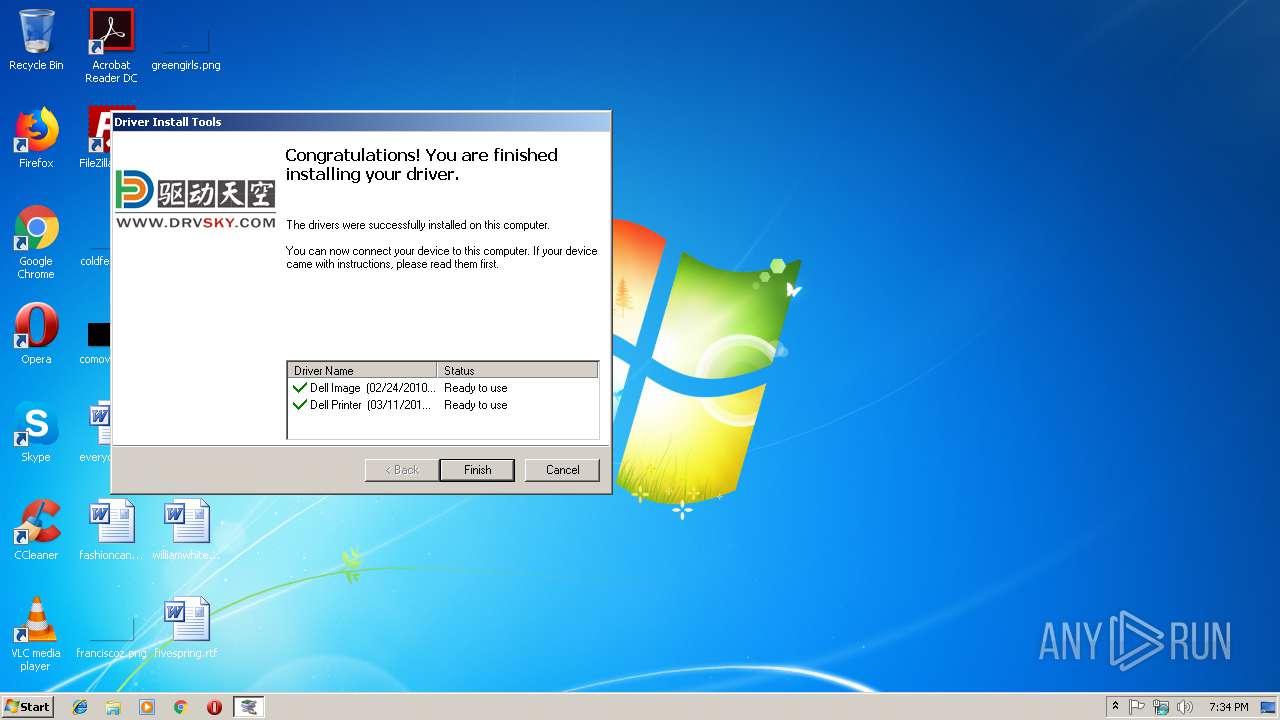
2780 | cd103fd7e6bd4213e3bf138a3b40d77aa2980161bdddd88d0f4b227224d4bcd2.exe | GET | 301 | 47.98.149.187:80 | http://www.drvsky.com/js/winrar.gif | CN | html | 159 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2780 | cd103fd7e6bd4213e3bf138a3b40d77aa2980161bdddd88d0f4b227224d4bcd2.exe | 47.98.149.187:443 | www.drvsky.com | Hangzhou Alibaba Advertising Co.,Ltd. | CN | unknown |
2780 | cd103fd7e6bd4213e3bf138a3b40d77aa2980161bdddd88d0f4b227224d4bcd2.exe | 47.98.149.187:80 | www.drvsky.com | Hangzhou Alibaba Advertising Co.,Ltd. | CN | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.drvsky.com |
| unknown |