| File name: | Invision-Free.exe |
| Full analysis: | https://app.any.run/tasks/f278c5b1-bb15-4d56-9e18-d5c1d80a19a9 |
| Verdict: | Malicious activity |
| Analysis date: | January 24, 2022, 15:49:11 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 (stripped to external PDB), for MS Windows |
| MD5: | 6E4E73B54B77E7D5BC66A01DBBB34560 |
| SHA1: | C7F41E25274ADE8387BE9D0D4BB700E42E0D814B |
| SHA256: | CD061B59DC1B8F5F1F95D064BEF7F43402392BB19CA27E220000C66CA7819584 |
| SSDEEP: | 49152:xXwsj9ljg1OpzWI28k7Ly5wD8wnXlVVsIiPAXtHCFgEnojgk:2shljg1OpzWIwy5snXloIIAXAFgEU |
MALICIOUS
Executes PowerShell scripts
- cmd.exe (PID: 1344)
- cmd.exe (PID: 1040)
Drops executable file immediately after starts
- Invision-Free.exe (PID: 488)
Writes to a start menu file
- svchost.exe (PID: 2308)
Application was dropped or rewritten from another process
- staler.exe (PID: 3460)
- dll_loader.exe (PID: 3620)
- svchost.exe (PID: 2308)
- staler_loader.exe (PID: 3020)
Deletes shadow copies
- cmd.exe (PID: 1976)
- cmd.exe (PID: 1536)
Application was injected by another process
- SearchIndexer.exe (PID: 2996)
- svchost.exe (PID: 876)
- svchost.exe (PID: 3456)
- svchost.exe (PID: 332)
- wmiprvse.exe (PID: 1696)
Starts BCDEDIT.EXE to disable recovery
- cmd.exe (PID: 3736)
Runs injected code in another process
- wbadmin.exe (PID: 3224)
Loads the Task Scheduler COM API
- wbengine.exe (PID: 3628)
SUSPICIOUS
Starts CMD.EXE for commands execution
- Invision-Free.exe (PID: 488)
- svchost.exe (PID: 2308)
Checks supported languages
- cmd.exe (PID: 1344)
- cmd.exe (PID: 1040)
- powershell.exe (PID: 2596)
- Invision-Free.exe (PID: 488)
- powershell.exe (PID: 2524)
- cmd.exe (PID: 2380)
- cmd.exe (PID: 2908)
- cmd.exe (PID: 2668)
- cmd.exe (PID: 2200)
- dll_loader.exe (PID: 3620)
- staler_loader.exe (PID: 3020)
- staler.exe (PID: 3460)
- svchost.exe (PID: 2308)
- powershell.exe (PID: 3060)
- cmd.exe (PID: 1976)
- WMIC.exe (PID: 3924)
- cmd.exe (PID: 3736)
- wmiprvse.exe (PID: 1696)
- cmd.exe (PID: 1536)
Drops a file with too old compile date
- Invision-Free.exe (PID: 488)
Reads the computer name
- powershell.exe (PID: 2524)
- powershell.exe (PID: 2596)
- staler_loader.exe (PID: 3020)
- dll_loader.exe (PID: 3620)
- powershell.exe (PID: 3060)
- svchost.exe (PID: 2308)
- WMIC.exe (PID: 3924)
- wmiprvse.exe (PID: 1696)
- staler.exe (PID: 3460)
Executable content was dropped or overwritten
- Invision-Free.exe (PID: 488)
- dll_loader.exe (PID: 3620)
Drops a file with a compile date too recent
- Invision-Free.exe (PID: 488)
- dll_loader.exe (PID: 3620)
Reads Environment values
- staler_loader.exe (PID: 3020)
- staler.exe (PID: 3460)
Creates executable files which already exist in Windows
- dll_loader.exe (PID: 3620)
Creates files in the user directory
- dll_loader.exe (PID: 3620)
- svchost.exe (PID: 2308)
Starts itself from another location
- dll_loader.exe (PID: 3620)
Creates files in the program directory
- SearchIndexer.exe (PID: 2996)
Executed as Windows Service
- vssvc.exe (PID: 2640)
- wbengine.exe (PID: 3628)
- vds.exe (PID: 212)
Creates files in the Windows directory
- wbadmin.exe (PID: 3224)
Executed via COM
- vdsldr.exe (PID: 1248)
INFO
Checks Windows Trust Settings
- powershell.exe (PID: 2524)
- powershell.exe (PID: 2596)
- powershell.exe (PID: 3060)
Reads settings of System Certificates
- powershell.exe (PID: 3060)
- powershell.exe (PID: 2524)
Reads the computer name
- vssadmin.exe (PID: 4032)
- vssvc.exe (PID: 2640)
- svchost.exe (PID: 3456)
- wbadmin.exe (PID: 3224)
- wbengine.exe (PID: 3628)
- vdsldr.exe (PID: 1248)
- vds.exe (PID: 212)
Checks supported languages
- vssvc.exe (PID: 2640)
- svchost.exe (PID: 3456)
- vssadmin.exe (PID: 4032)
- bcdedit.exe (PID: 2780)
- bcdedit.exe (PID: 2796)
- wbadmin.exe (PID: 3224)
- wbengine.exe (PID: 3628)
- vdsldr.exe (PID: 1248)
- vds.exe (PID: 212)
- NOTEPAD.EXE (PID: 2844)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (61.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.6) |
| .exe | | | Win32 Executable (generic) (10) |
| .exe | | | Win16/32 Executable Delphi generic (4.6) |
| .exe | | | Generic Win/DOS Executable (4.4) |
EXIF
EXE
| Subsystem: | Windows GUI |
|---|---|
| SubsystemVersion: | 4 |
| ImageVersion: | - |
| OSVersion: | 4 |
| EntryPoint: | 0x1559 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 3383808 |
| CodeSize: | 2048 |
| LinkerVersion: | 6 |
| PEType: | PE32 |
| TimeStamp: | 0000:00:00 00:00:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 01-Jan-1970 00:00:00 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 01-Jan-1970 00:00:00 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000006F0 | 0x00000800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 4.80236 |
.rdata | 0x00002000 | 0x00339E11 | 0x0033A000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.99799 |
.bss | 0x0033C000 | 0x00000004 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x0033D000 | 0x000001F0 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.81994 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.85064 | 408 | UNKNOWN | English - United States | RT_MANIFEST |
Imports
kernel32.dll |
msvcrt.dll |
Total processes
78
Monitored processes
33
Malicious processes
9
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 212 | C:\Windows\System32\vds.exe | C:\Windows\System32\vds.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Virtual Disk Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 332 | C:\Windows\system32\svchost.exe -k NetworkService | C:\Windows\system32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 488 | "C:\Users\admin\AppData\Local\Temp\Invision-Free.exe" | C:\Users\admin\AppData\Local\Temp\Invision-Free.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 876 | C:\Windows\system32\svchost.exe -k netsvcs | C:\Windows\system32\svchost.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1040 | cmd /c powershell -Command "Add-MpPreference -ExclusionPath @($env:UserProfile,$env:AppData,$env:Temp,$env:SystemRoot,$env:HomeDrive,$env:SystemDrive) -Force" & powershell -Command "Add-MpPreference -ExclusionExtension @('exe','dll') -Force" & exit | C:\Windows\system32\cmd.exe | — | Invision-Free.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1248 | C:\Windows\System32\vdsldr.exe -Embedding | C:\Windows\System32\vdsldr.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Virtual Disk Service Loader Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
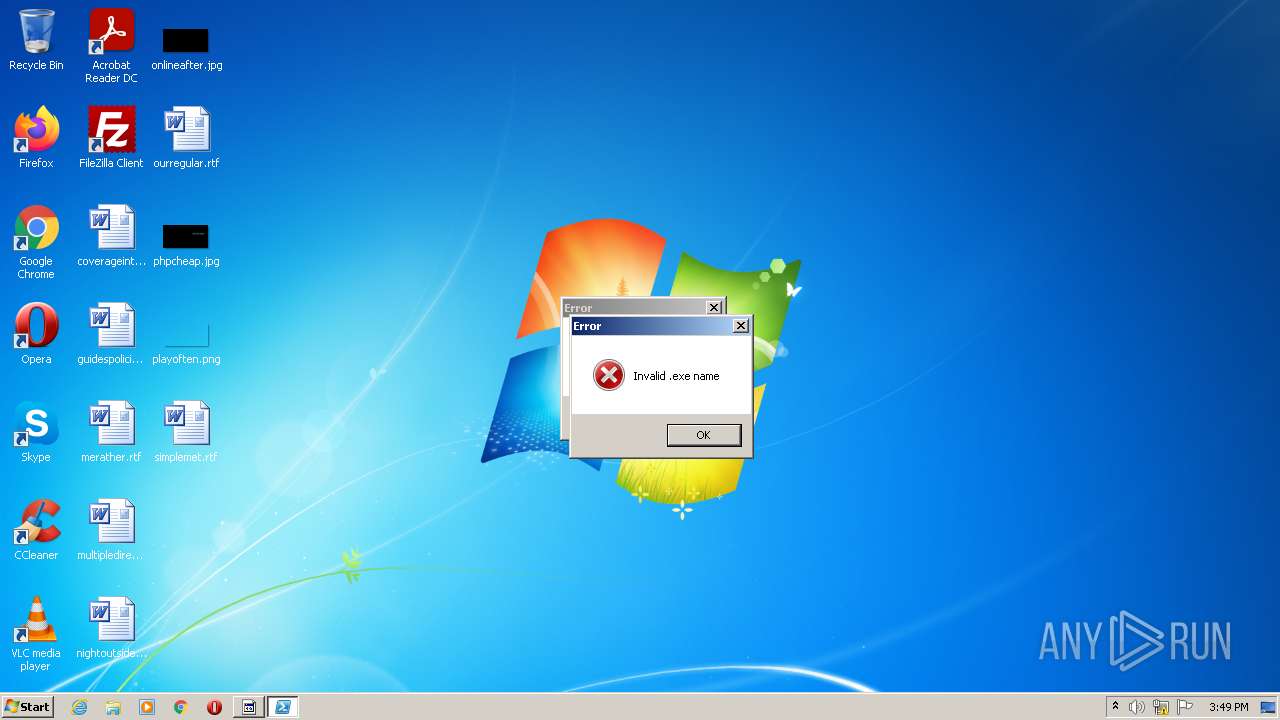
| 1344 | cmd /c powershell -Command "Add-Type -AssemblyName System.Windows.Forms;[System.Windows.Forms.MessageBox]::Show('Invalid .exe name','Error','OK','Error')" | C:\Windows\system32\cmd.exe | — | Invision-Free.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1536 | "C:\Windows\System32\cmd.exe" /C wbadmin delete catalog -quiet | C:\Windows\System32\cmd.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1696 | C:\Windows\system32\wbem\wmiprvse.exe -secured -Embedding | C:\Windows\system32\wbem\wmiprvse.exe | svchost.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: WMI Provider Host Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 1976 | "C:\Windows\System32\cmd.exe" /C vssadmin delete shadows /all /quiet & wmic shadowcopy delete | C:\Windows\System32\cmd.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
20 156
Read events
20 069
Write events
87
Delete events
0
Modification events
| (PID) Process: | (3020) staler_loader.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\staler_loader_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3020) staler_loader.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\staler_loader_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3020) staler_loader.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\staler_loader_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (3460) staler.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\staler_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3460) staler.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\staler_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3460) staler.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\staler_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (3460) staler.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\staler_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (3460) staler.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\staler_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (3460) staler.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\staler_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (3460) staler.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\staler_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
Executable files
5
Suspicious files
11
Text files
98
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 488 | Invision-Free.exe | C:\Users\admin\AppData\Local\Temp\service64-uninstaller.exe | executable | |
MD5:— | SHA256:— | |||
| 3620 | dll_loader.exe | C:\Users\admin\AppData\Roaming\svchost.exe | executable | |
MD5:— | SHA256:— | |||
| 876 | svchost.exe | C:\Windows\appcompat\programs\RecentFileCache.bcf | txt | |
MD5:— | SHA256:— | |||
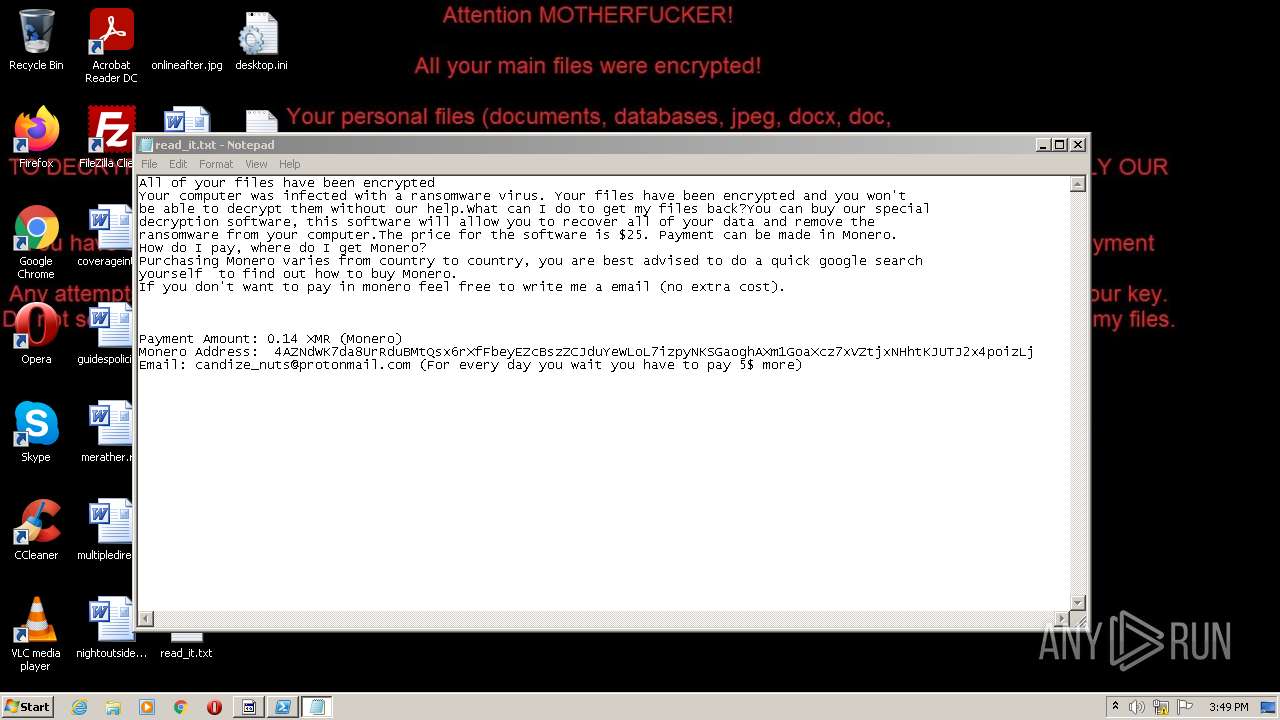
| 2308 | svchost.exe | C:\Users\admin\Links\read_it.txt | text | |
MD5:— | SHA256:— | |||
| 2308 | svchost.exe | C:\Users\admin\Documents\read_it.txt | text | |
MD5:— | SHA256:— | |||
| 2308 | svchost.exe | C:\Users\admin\Documents\OneNote Notebooks\Personal\read_it.txt | text | |
MD5:— | SHA256:— | |||
| 2308 | svchost.exe | C:\Users\admin\Documents\Outlook Files\read_it.txt | text | |
MD5:— | SHA256:— | |||
| 488 | Invision-Free.exe | C:\Users\admin\AppData\Local\Temp\staler_loader.exe | executable | |
MD5:— | SHA256:— | |||
| 2524 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | dbf | |
MD5:446DD1CF97EABA21CF14D03AEBC79F27 | SHA256:A7DE5177C68A64BD48B36D49E2853799F4EBCFA8E4761F7CC472F333DC5F65CF | |||
| 2524 | powershell.exe | C:\Users\admin\AppData\Local\Temp\z105x5ii.xsw.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
5
DNS requests
3
Threats
3
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3020 | staler_loader.exe | 193.122.6.168:80 | checkip.dyndns.org | Oracle Corporation | US | malicious |
3460 | staler.exe | 23.128.64.141:443 | ip4.seeip.org | Joe's Datacenter, LLC | US | suspicious |
3020 | staler_loader.exe | 132.226.8.169:80 | checkip.dyndns.org | Oracle Corporation | US | malicious |
3020 | staler_loader.exe | 193.122.130.0:80 | checkip.dyndns.org | Oracle Corporation | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
checkip.dyndns.org |
| shared |
ip4.seeip.org |
| suspicious |
dns.msftncsi.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Misc activity | ET INFO DYNAMIC_DNS Query to *.dyndns. Domain |
— | — | Misc activity | AV INFO Query to checkip.dyndns. Domain |
1 ETPRO signatures available at the full report