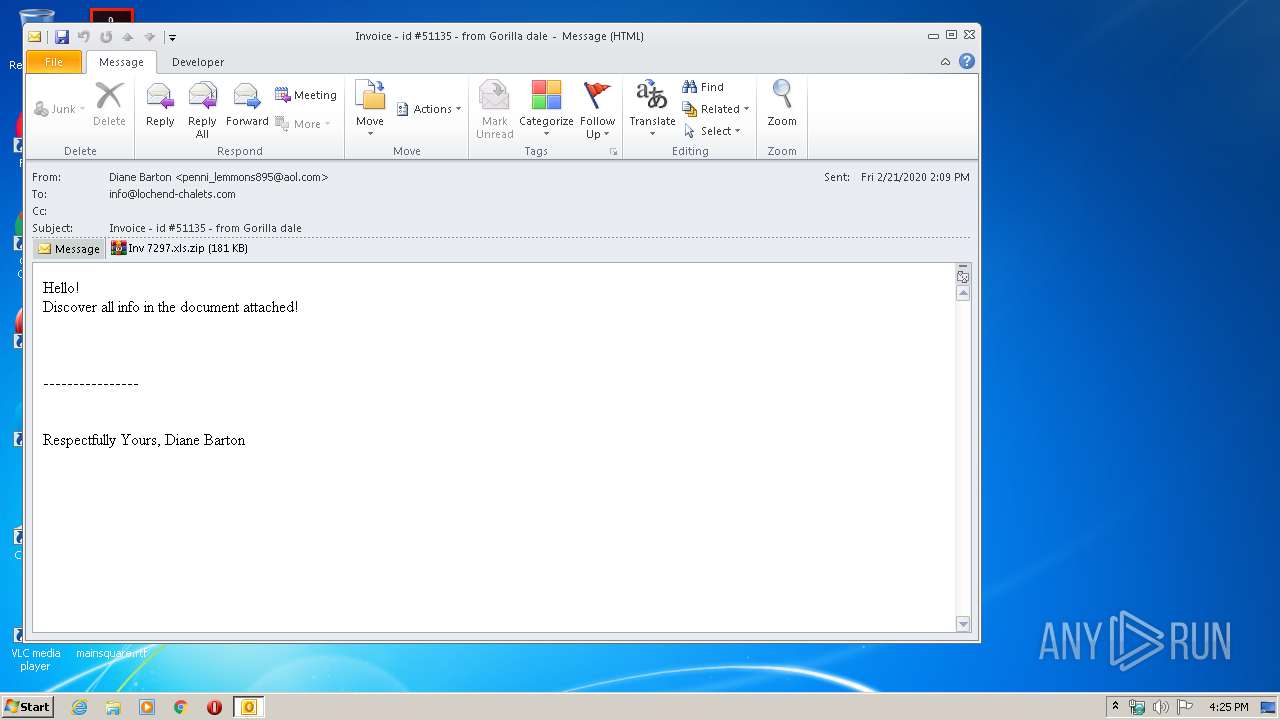
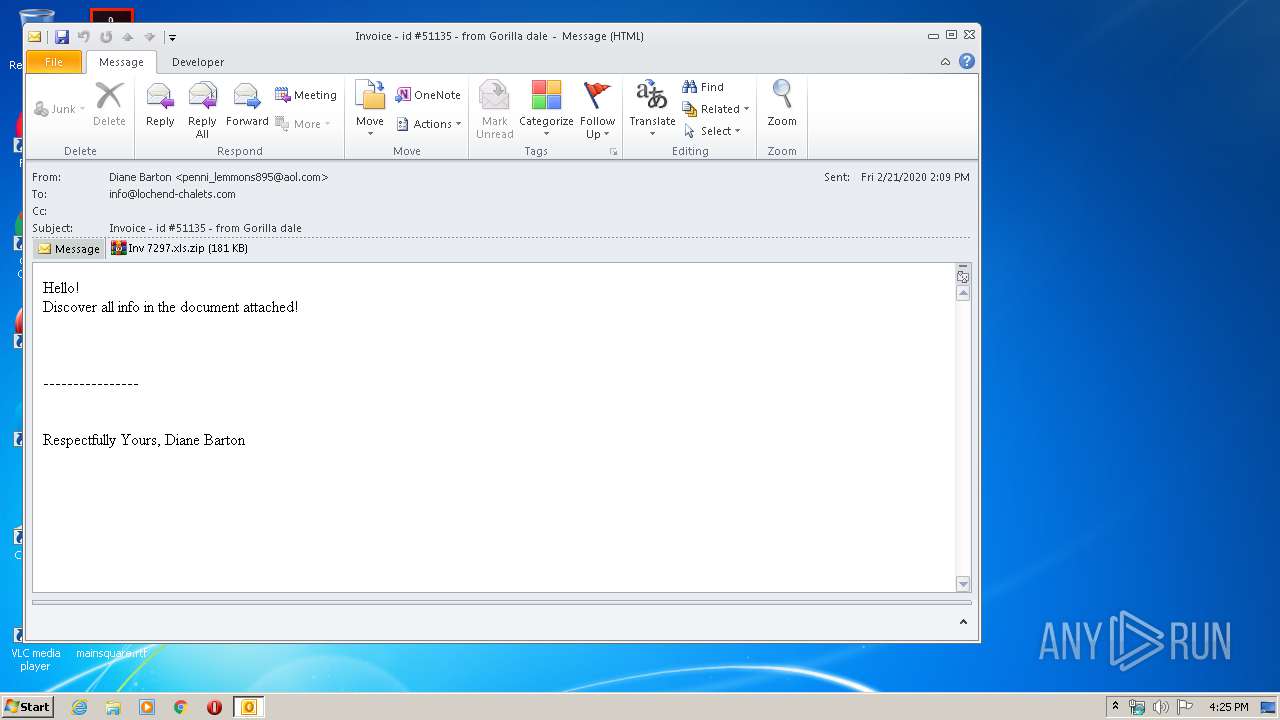
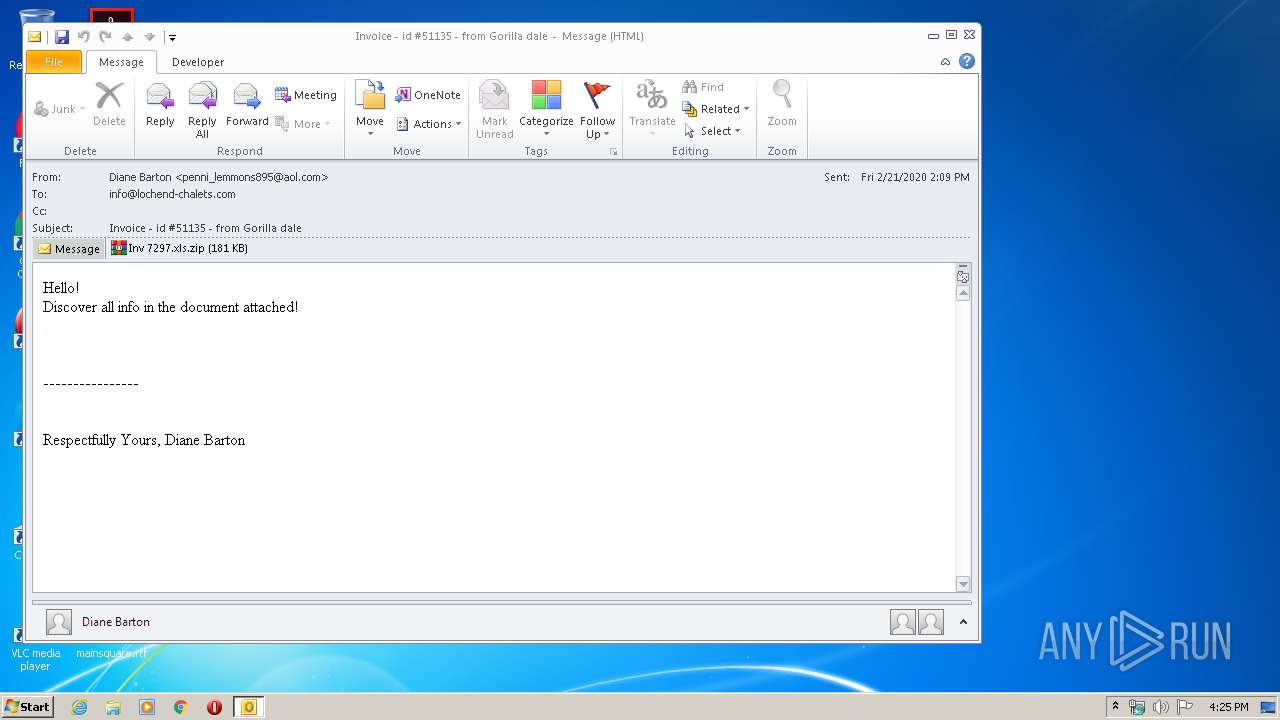
| File name: | Invoice - id #51135 - from Gorilla dale.msg |
| Full analysis: | https://app.any.run/tasks/544931a8-5a17-4b0d-94fe-68f30f1dc0f7 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | February 21, 2020, 16:24:45 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.ms-outlook |
| File info: | CDFV2 Microsoft Outlook Message |
| MD5: | 8D3C7E71334C4F76828258E5603A8CF1 |
| SHA1: | B5810C138C9C6D40D3C65B3F48AD17895A260B5C |
| SHA256: | CD02EF216C0A34B62429A3D7C10BF33E7EEA7FEBED14DBA57C4F961F609FAADA |
| SSDEEP: | 6144:emrbWb2k3hbdlylKsgqopeJBWhZFVE+W2NdDF0ViorNnYgmIl1oH2HU:TbVfrpf1WO |
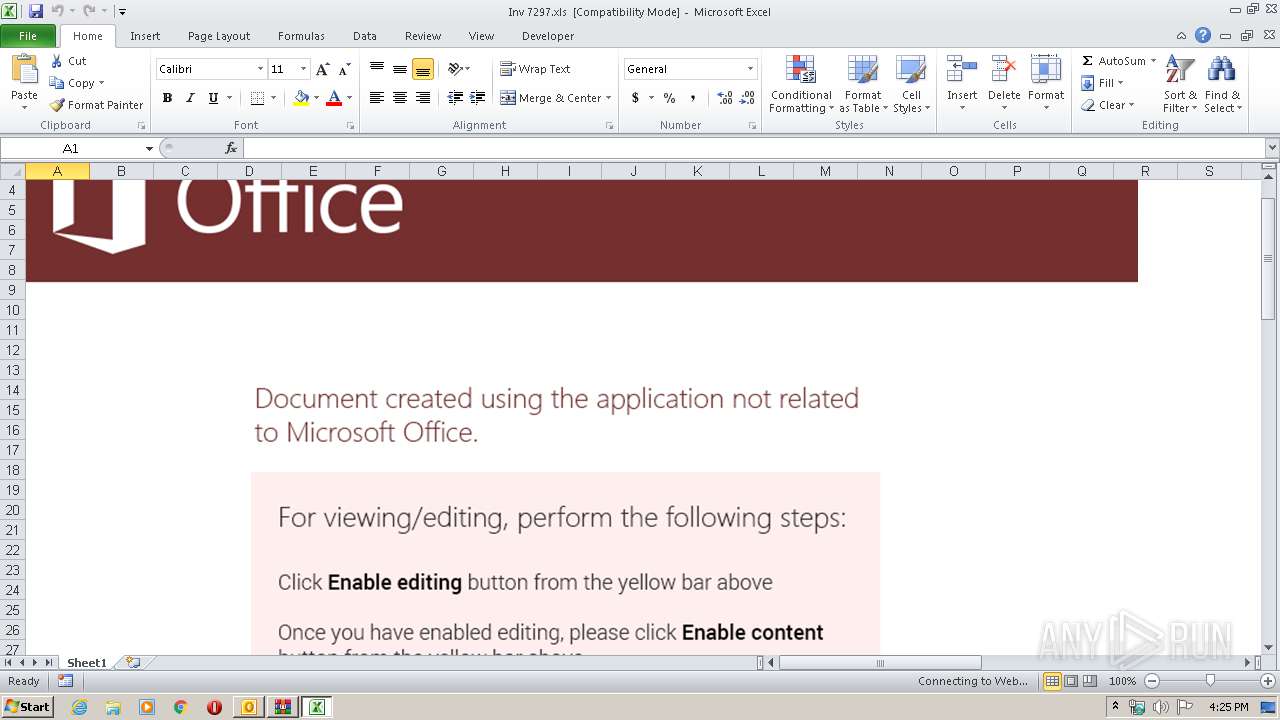
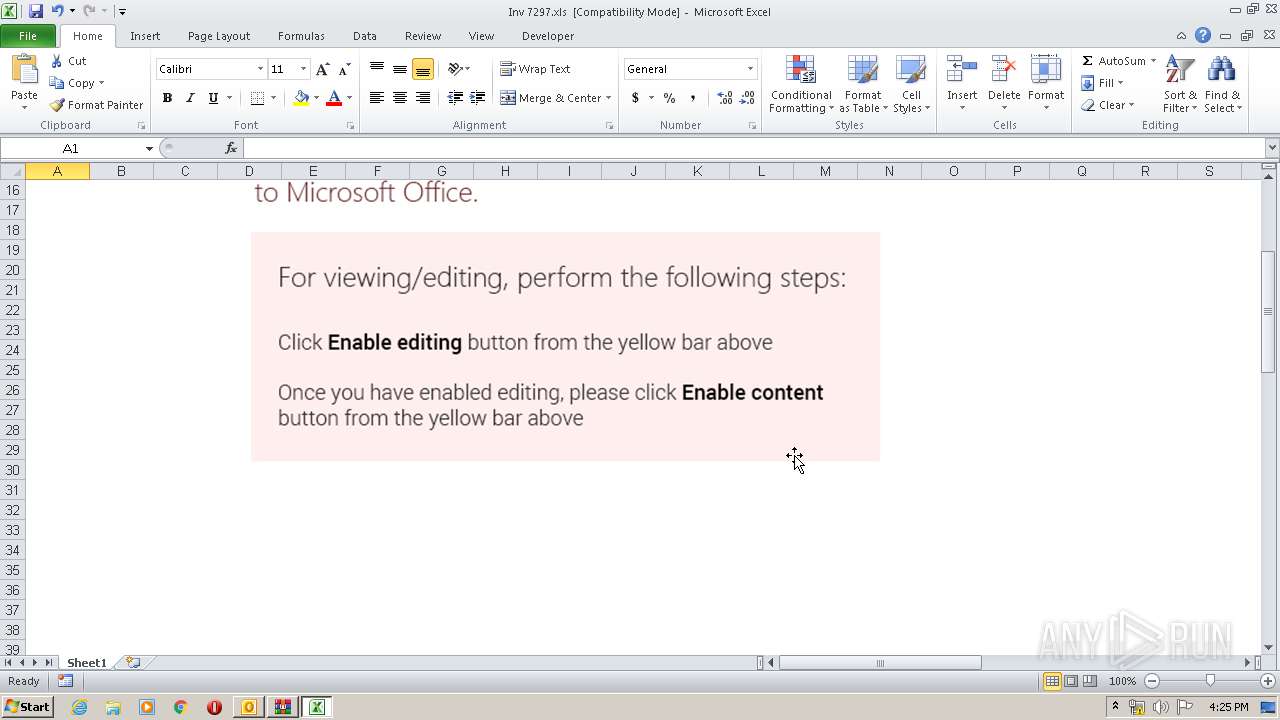
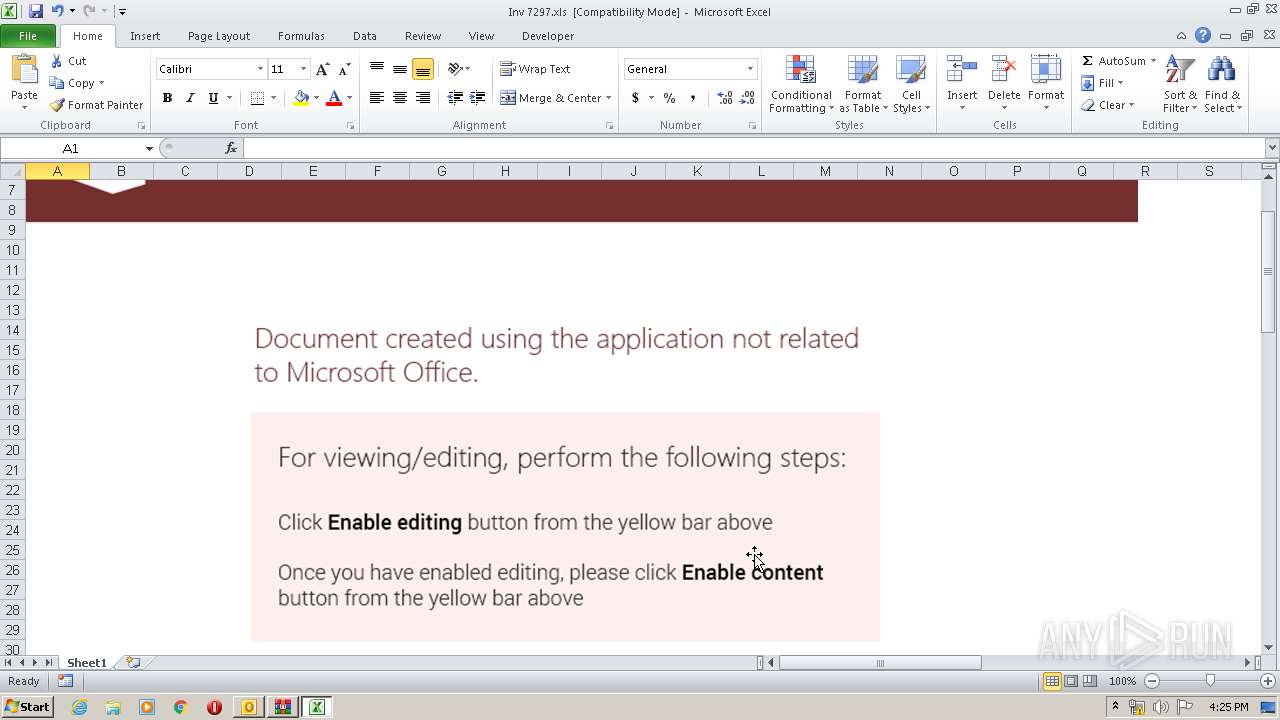
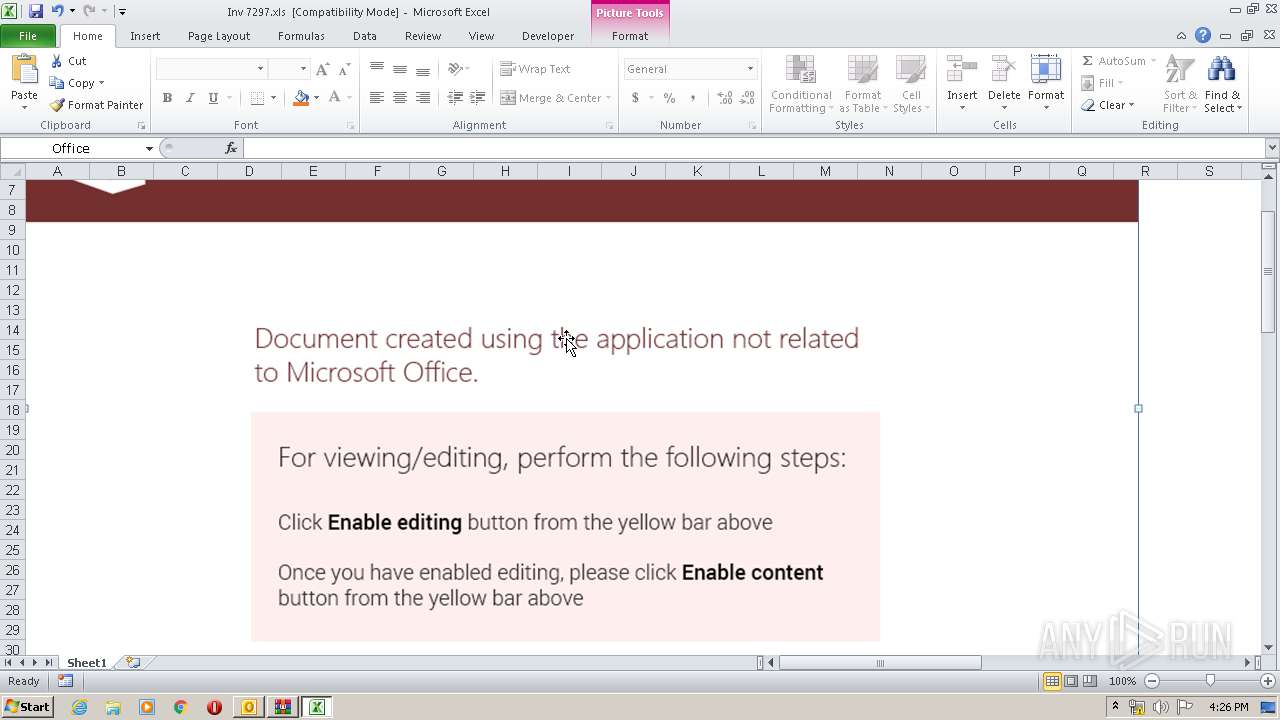
MALICIOUS
Unusual execution from Microsoft Office
- OUTLOOK.EXE (PID: 2952)
SUSPICIOUS
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 2952)
- EXCEL.EXE (PID: 3756)
Creates files in the user directory
- OUTLOOK.EXE (PID: 2952)
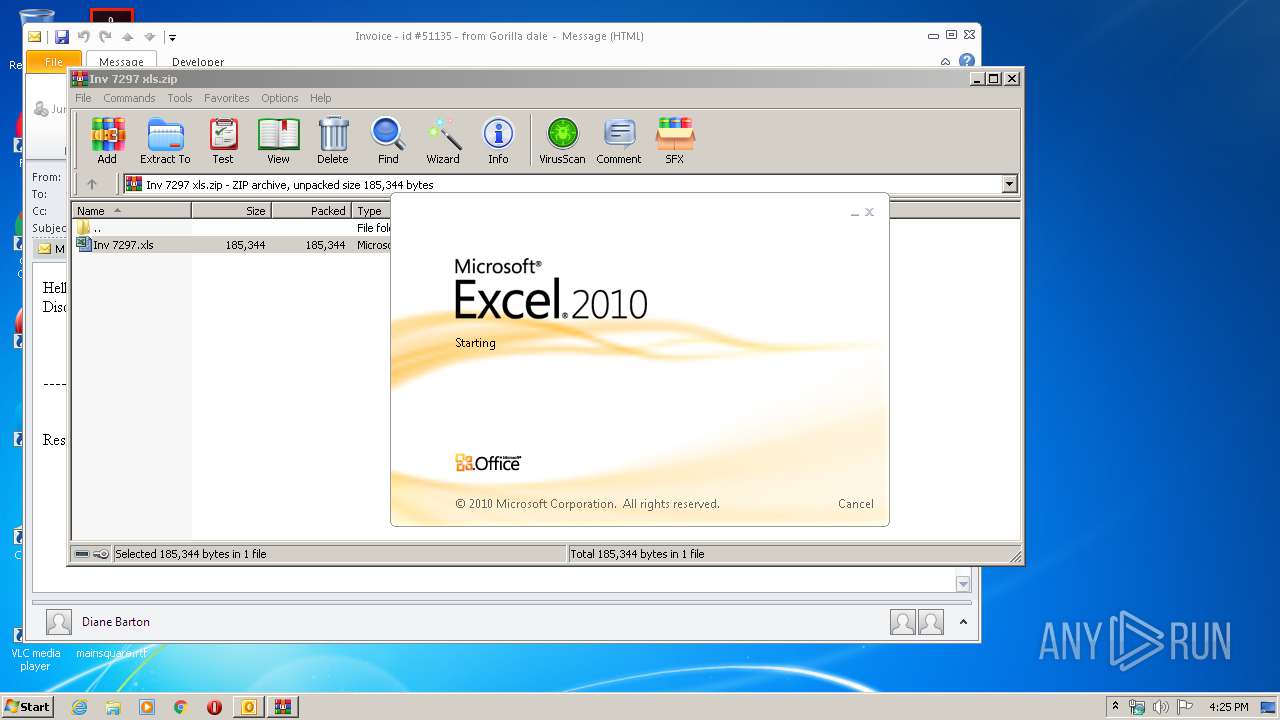
Starts Microsoft Office Application
- WinRAR.exe (PID: 3344)
- EXCEL.EXE (PID: 3756)
Application launched itself
- EXCEL.EXE (PID: 3756)
INFO
Reads Microsoft Office registry keys
- EXCEL.EXE (PID: 3756)
- EXCEL.EXE (PID: 3768)
- OUTLOOK.EXE (PID: 2952)
Creates files in the user directory
- EXCEL.EXE (PID: 3756)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msg | | | Outlook Message (47.1) |
|---|---|---|
| .oft | | | Outlook Form Template (27.5) |
| .xls | | | Microsoft Excel sheet (19.9) |
Total processes
42
Monitored processes
4
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2952 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" /f "C:\Users\admin\AppData\Local\Temp\Invoice - id #51135 - from Gorilla dale.msg" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
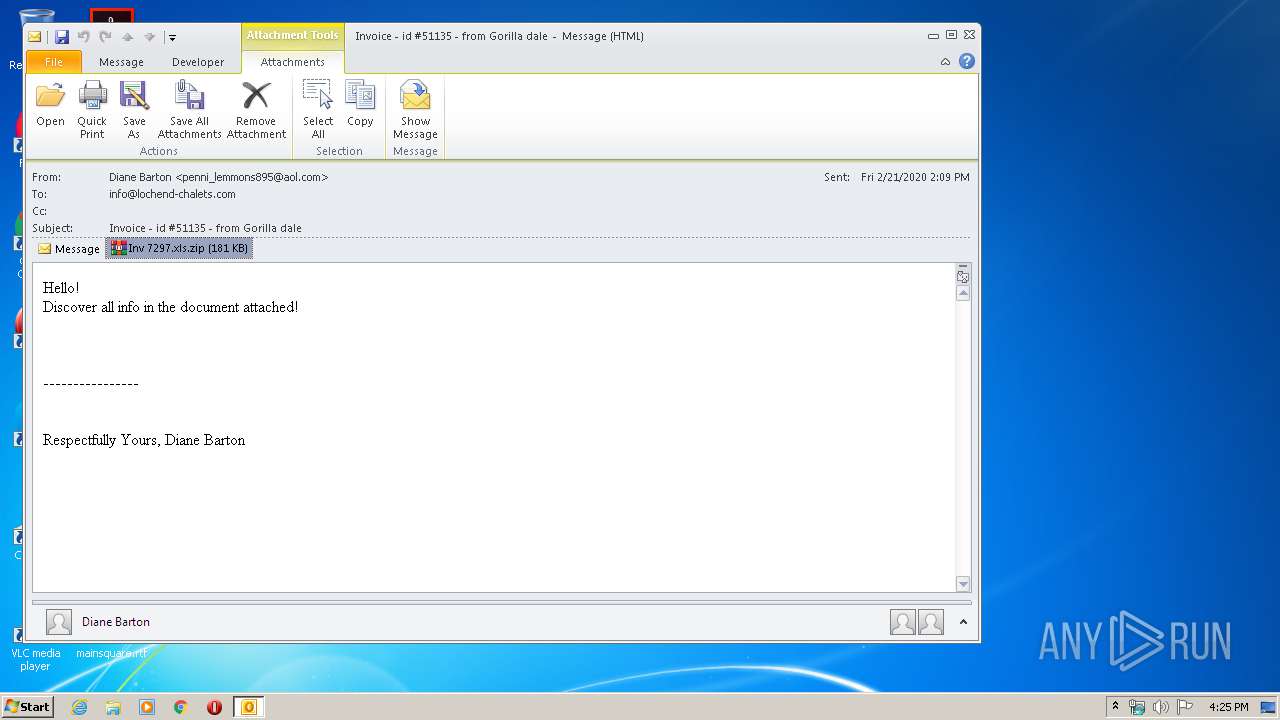
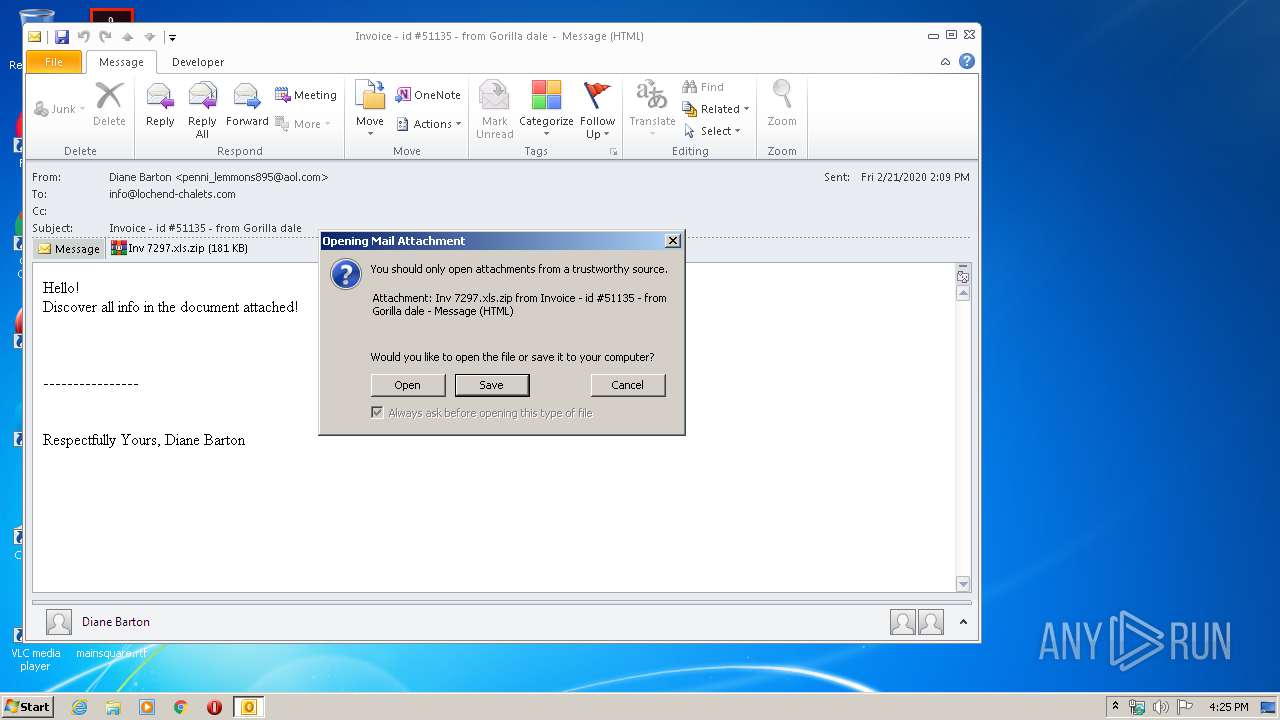
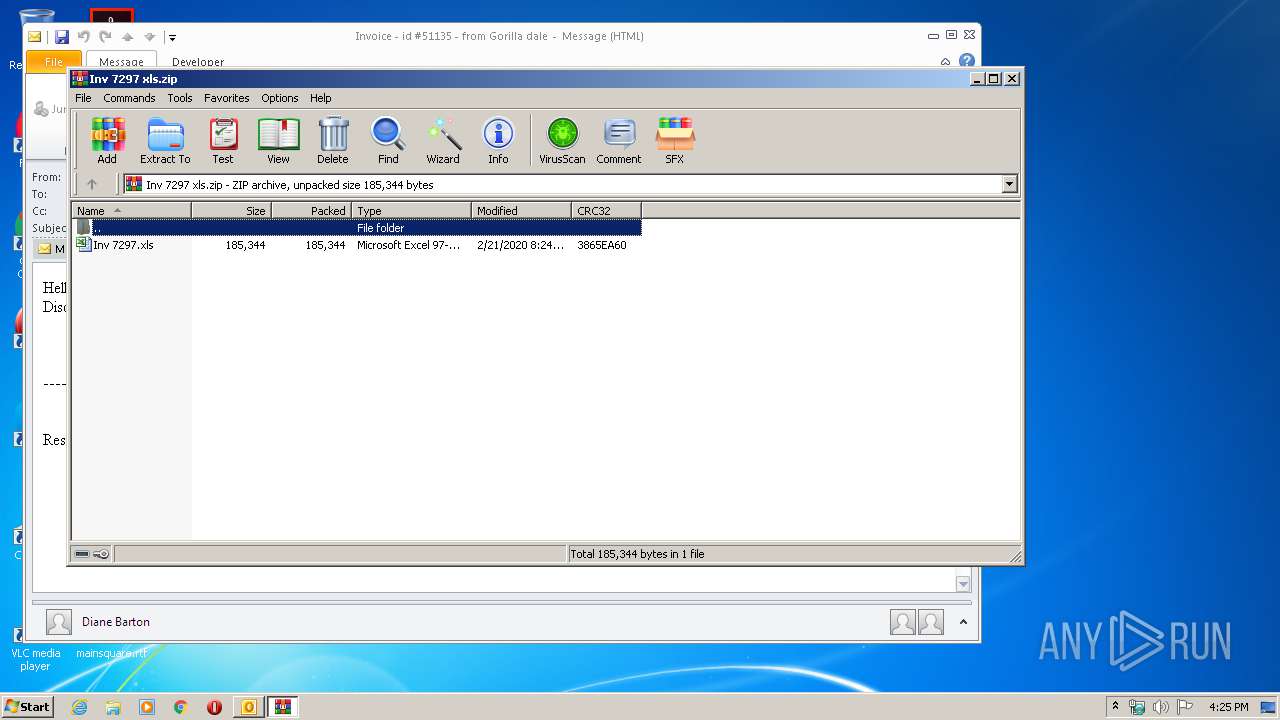
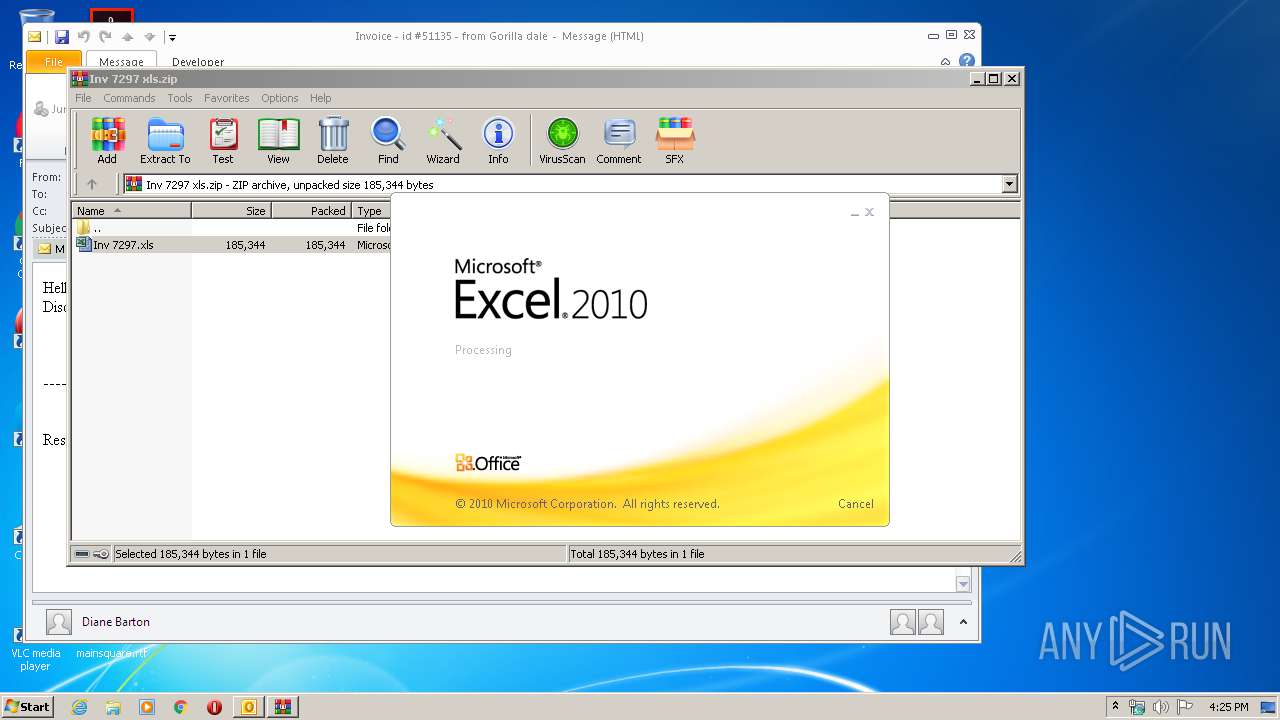
| 3344 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\O7VF9L0V\Inv 7297 xls.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | OUTLOOK.EXE | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
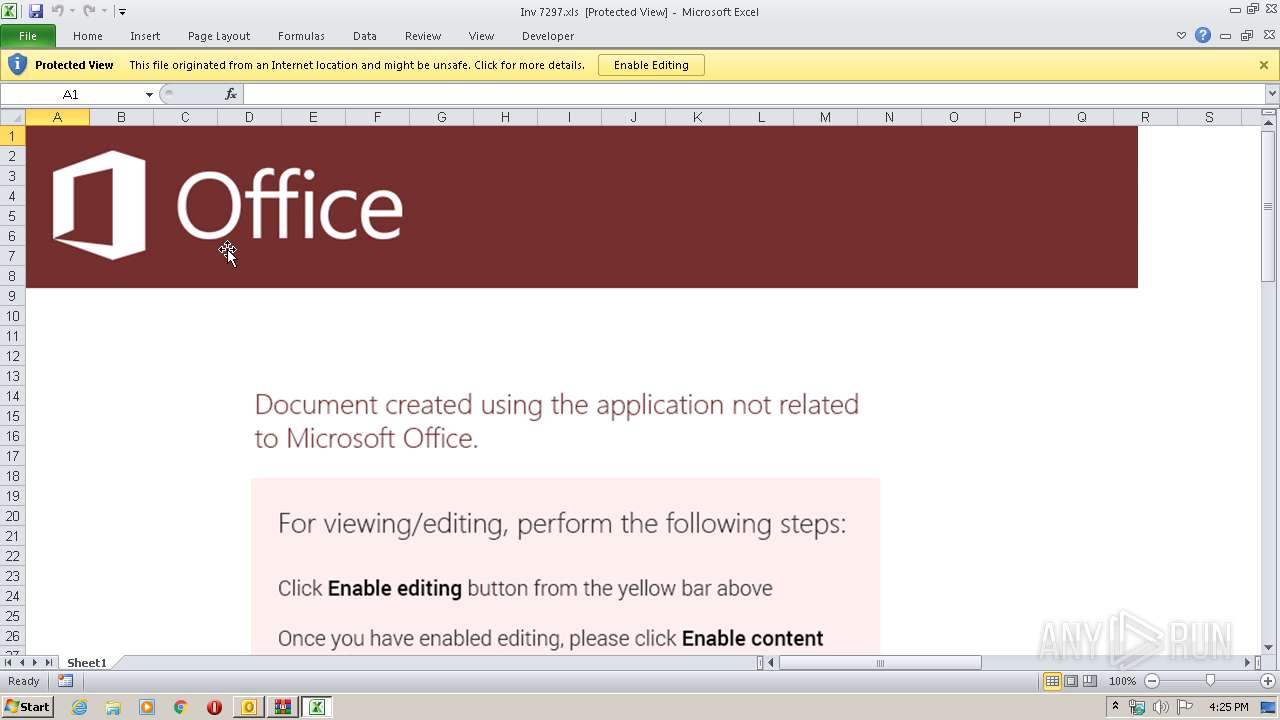
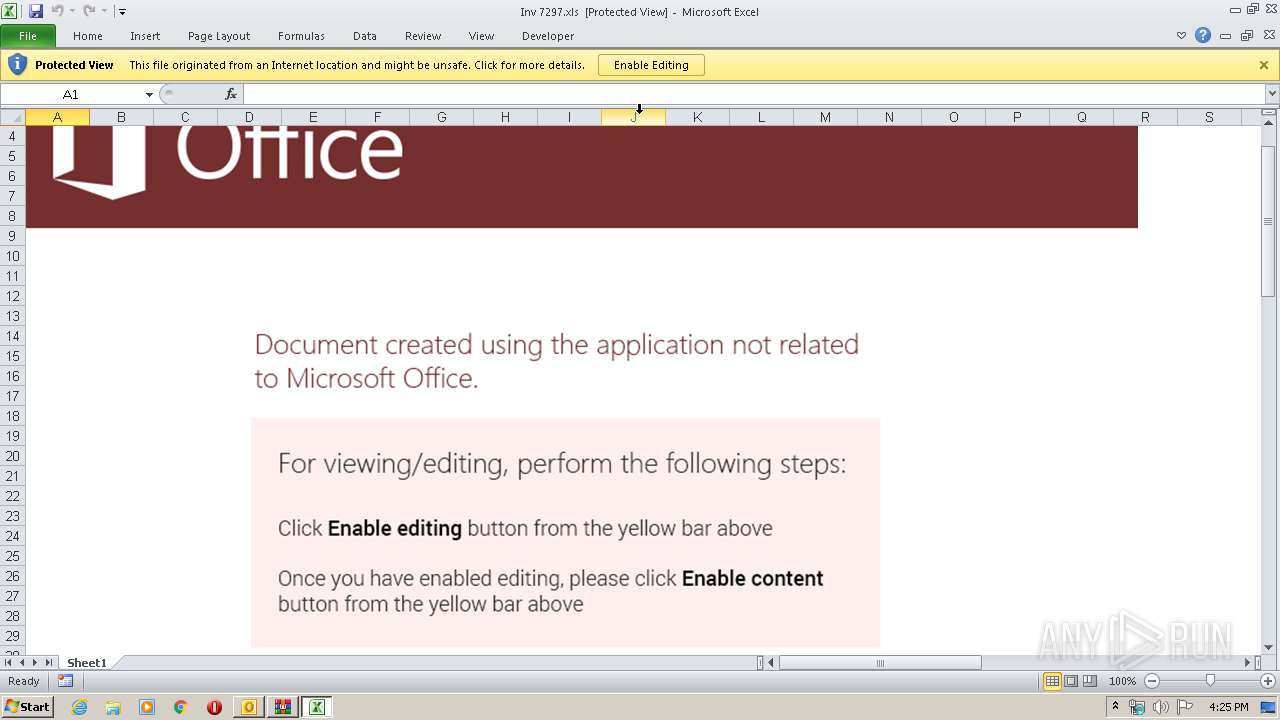
| 3756 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" /dde | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | WinRAR.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3768 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | — | EXCEL.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
3 408
Read events
2 712
Write events
658
Delete events
38
Modification events
| (PID) Process: | (2952) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2952) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2952) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2952) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2952) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2952) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2952) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2952) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2952) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
| (PID) Process: | (2952) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1055 |
Value: Off | |||
Executable files
0
Suspicious files
33
Text files
32
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2952 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR6AF7.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2952 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\O7VF9L0V\Inv 7297 xls (2).zip\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 3756 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVRA456.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3756 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\~DF7E37EEFBBDC3E0B4.TMP | — | |
MD5:— | SHA256:— | |||
| 3756 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\OICE_9C73B888-6E6C-4260-AEAA-31DE23D9224D.0\CF435741.xls\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 2952 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\outlook logging\firstrun.log | text | |
MD5:— | SHA256:— | |||
| 3768 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\OICE_9C73B888-6E6C-4260-AEAA-31DE23D9224D.0\~DFF180F9230D3C10F3.TMP | — | |
MD5:— | SHA256:— | |||
| 3768 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\OICE_9C73B888-6E6C-4260-AEAA-31DE23D9224D.0\~DFF9007422E3C94277.TMP | — | |
MD5:— | SHA256:— | |||
| 2952 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_WorkHours_1_C71056DEF74B014BA1351B690B4A89AD.dat | xml | |
MD5:807EF0FC900FEB3DA82927990083D6E7 | SHA256:4411E7DC978011222764943081500FFF0E43CBF7CCD44264BD1AB6306CA68913 | |||
| 2952 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_RssRule_2_1D79E559D471B545A86E361D8B4F382C.dat | xml | |
MD5:D8B37ED0410FB241C283F72B76987F18 | SHA256:31E68049F6B7F21511E70CD7F2D95B9CF1354CF54603E8F47C1FC40F40B7A114 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
4
DNS requests
4
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2952 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
3756 | EXCEL.EXE | GET | 200 | 2.16.186.11:80 | http://isrg.trustid.ocsp.identrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRv9GhNQxLSSGKBnMArPUcsHYovpgQUxKexpHsscfrb4UuQdf%2FEFWCFiRACEAoBQUIAAAFThXNqC4Xspwg%3D | unknown | der | 1.37 Kb | whitelisted |
3756 | EXCEL.EXE | GET | 200 | 2.16.186.27:80 | http://ocsp.int-x3.letsencrypt.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBR%2B5mrncpqz%2FPiiIGRsFqEtYHEIXQQUqEpqYwR93brm0Tm3pkVl7%2FOo7KECEgNCDwOADzP2LuMtxDEY6Xv2DQ%3D%3D | unknown | der | 527 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2952 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
3756 | EXCEL.EXE | 161.117.177.248:443 | veqejzkb.xyz | — | SG | suspicious |
3756 | EXCEL.EXE | 2.16.186.11:80 | isrg.trustid.ocsp.identrust.com | Akamai International B.V. | — | whitelisted |
3756 | EXCEL.EXE | 2.16.186.27:80 | ocsp.int-x3.letsencrypt.org | Akamai International B.V. | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
veqejzkb.xyz |
| suspicious |
isrg.trustid.ocsp.identrust.com |
| whitelisted |
ocsp.int-x3.letsencrypt.org |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3756 | EXCEL.EXE | Potentially Bad Traffic | ET INFO Observed Let's Encrypt Certificate for Suspicious TLD (.xyz) |