| File name: | cd026d398b3677675bfa4f28a51aeb44b684ef261d9e1f3a2957cae42bc14b62 |
| Full analysis: | https://app.any.run/tasks/651ea927-7205-4da3-ae7d-e716190af37b |
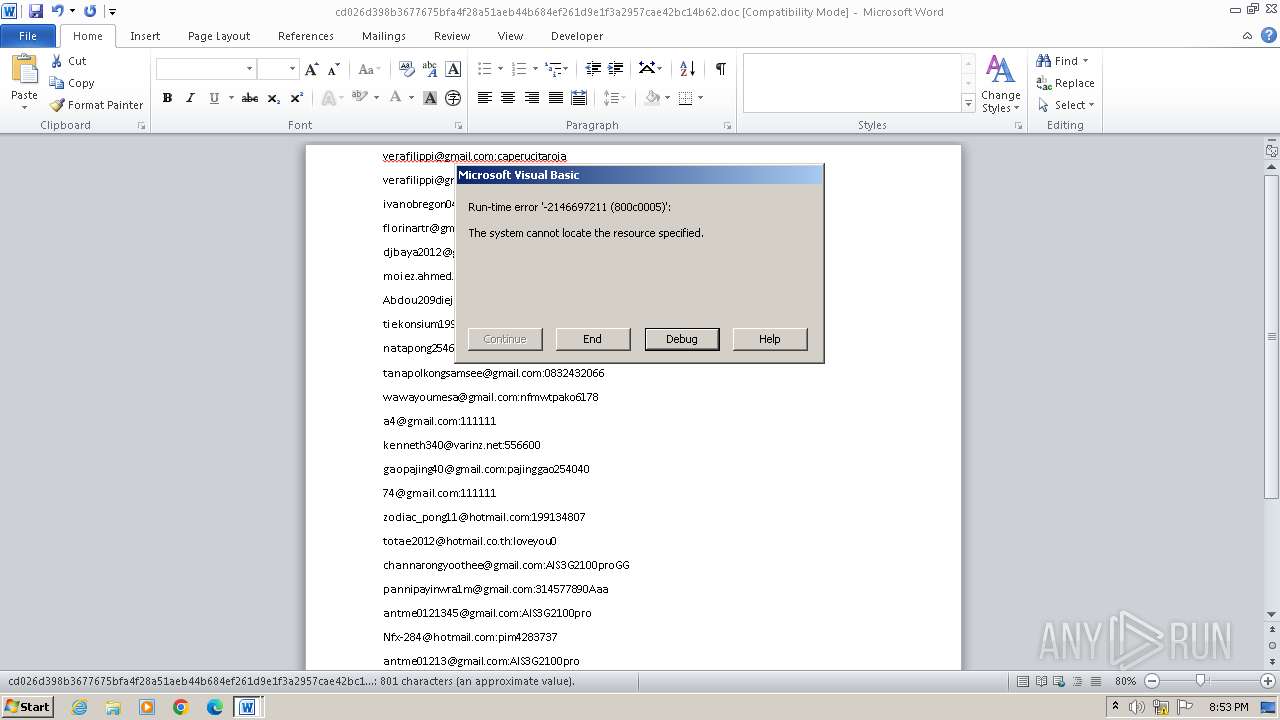
| Verdict: | Malicious activity |
| Analysis date: | December 02, 2023, 20:53:16 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| MIME: | application/msword |
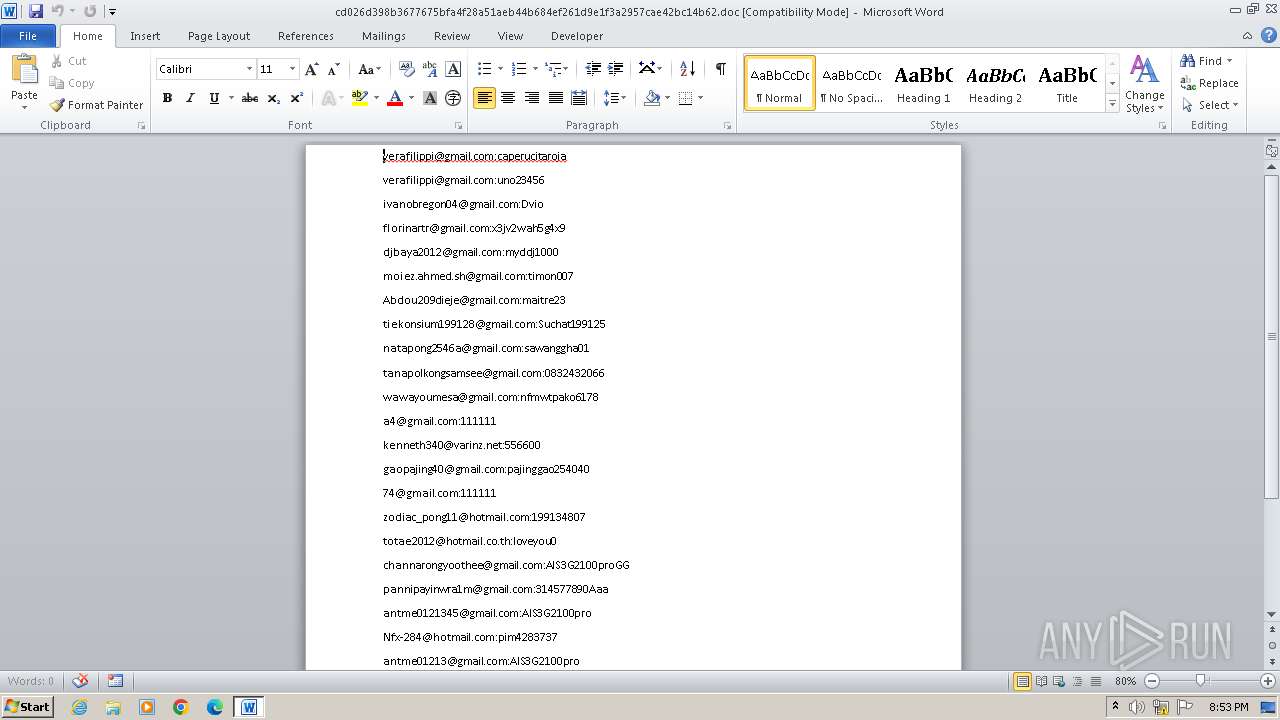
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 10.0, Code page: 1252, Author: KKK, Template: Normal.dotm, Last Saved By: KKK, Revision Number: 19, Name of Creating Application: Microsoft Office Word, Total Editing Time: 01:50:00, Create Time/Date: Thu Nov 9 18:29:00 2023, Last Saved Time/Date: Wed Nov 15 01:30:00 2023, Number of Pages: 1, Number of Words: 145, Number of Characters: 827, Security: 0 |
| MD5: | B365F2F500DA5C175168B03E00AC0F9F |
| SHA1: | 18A0519F99DF057CE414343DB2A85FB249A83EC7 |
| SHA256: | CD026D398B3677675BFA4F28A51AEB44B684EF261D9E1F3A2957CAE42BC14B62 |
| SSDEEP: | 384:aR6DLNSeqrYoHZdNKgoZGuc5/9rQyeU/ec0ja2rKStU:aRxN52a/rZSKStU |
MALICIOUS
Creates internet connection object (SCRIPT)
- WINWORD.EXE (PID: 844)
Sends HTTP request (SCRIPT)
- WINWORD.EXE (PID: 844)
Opens an HTTP connection (SCRIPT)
- WINWORD.EXE (PID: 844)
Connection from MS Office application
- WINWORD.EXE (PID: 844)
SUSPICIOUS
No suspicious indicators.INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Identification: | Word 8.0 |
|---|---|
| LanguageCode: | English (US) |
| DocFlags: | 1Table, ExtChar |
| System: | Windows |
| Word97: | No |
| Title: | - |
| Subject: | - |
| Author: | KKK |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | KKK |
| Software: | Microsoft Office Word |
| CreateDate: | 2023:11:09 18:29:00 |
| ModifyDate: | 2023:11:15 01:30:00 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| CharCountWithSpaces: | 971 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
| LastPrinted: | 0000:00:00 00:00:00 |
| RevisionNumber: | 19 |
| TotalEditTime: | 1.8 hours |
| Words: | 145 |
| Characters: | 827 |
| Pages: | 1 |
| Paragraphs: | 1 |
| Lines: | 6 |
Total processes
38
Monitored processes
1
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 844 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\cd026d398b3677675bfa4f28a51aeb44b684ef261d9e1f3a2957cae42bc14b62.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
3 066
Read events
2 600
Write events
341
Delete events
125
Modification events
| (PID) Process: | (844) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (844) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: On | |||
| (PID) Process: | (844) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: On | |||
| (PID) Process: | (844) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: On | |||
| (PID) Process: | (844) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: On | |||
| (PID) Process: | (844) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: On | |||
| (PID) Process: | (844) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: On | |||
| (PID) Process: | (844) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: On | |||
| (PID) Process: | (844) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: On | |||
| (PID) Process: | (844) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1055 |
Value: On | |||
Executable files
0
Suspicious files
2
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 844 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR8428.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 844 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\UProof\ExcludeDictionaryEN0409.lex | text | |
MD5:F3B25701FE362EC84616A93A45CE9998 | SHA256:B3D510EF04275CA8E698E5B3CBB0ECE3949EF9252F0CDC839E9EE347409A2209 | |||
| 844 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$026d398b3677675bfa4f28a51aeb44b684ef261d9e1f3a2957cae42bc14b62.doc | binary | |
MD5:45F2000DCA530F2571F47F3FC3F267A3 | SHA256:3B29C7F3C2D961C5CCDC73ED7257F140ED08488D39EEF1A079290985EBC80542 | |||
| 844 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | binary | |
MD5:70DD82C86891327DCDC681C8A683DEF0 | SHA256:40E7084FB5E74BDA5D614CF874D7048089BEB9737FD2927A7C775E74095A8F5E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
5
DNS requests
2
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
868 | svchost.exe | 23.35.228.137:80 | armmf.adobe.com | AKAMAI-AS | DE | unknown |
844 | WINWORD.EXE | 162.125.66.18:443 | www.dropbox.com | DROPBOX | DE | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.dropbox.com |
| shared |
armmf.adobe.com |
| whitelisted |