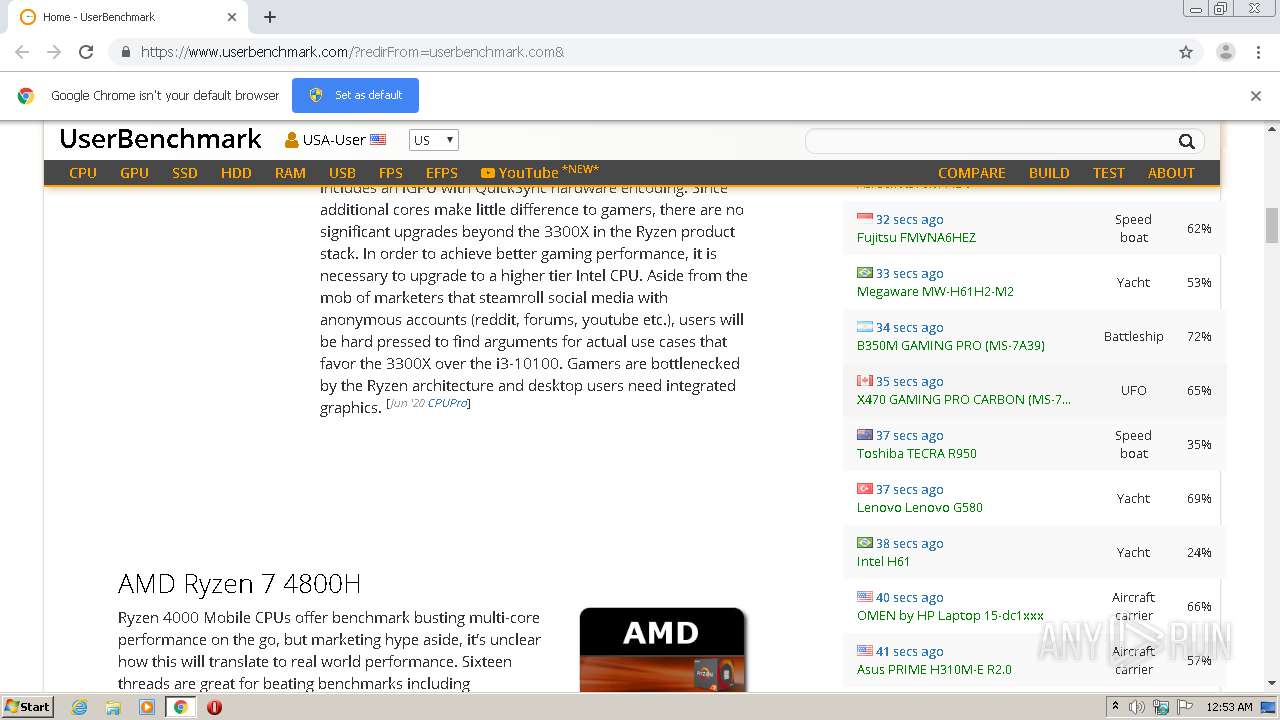
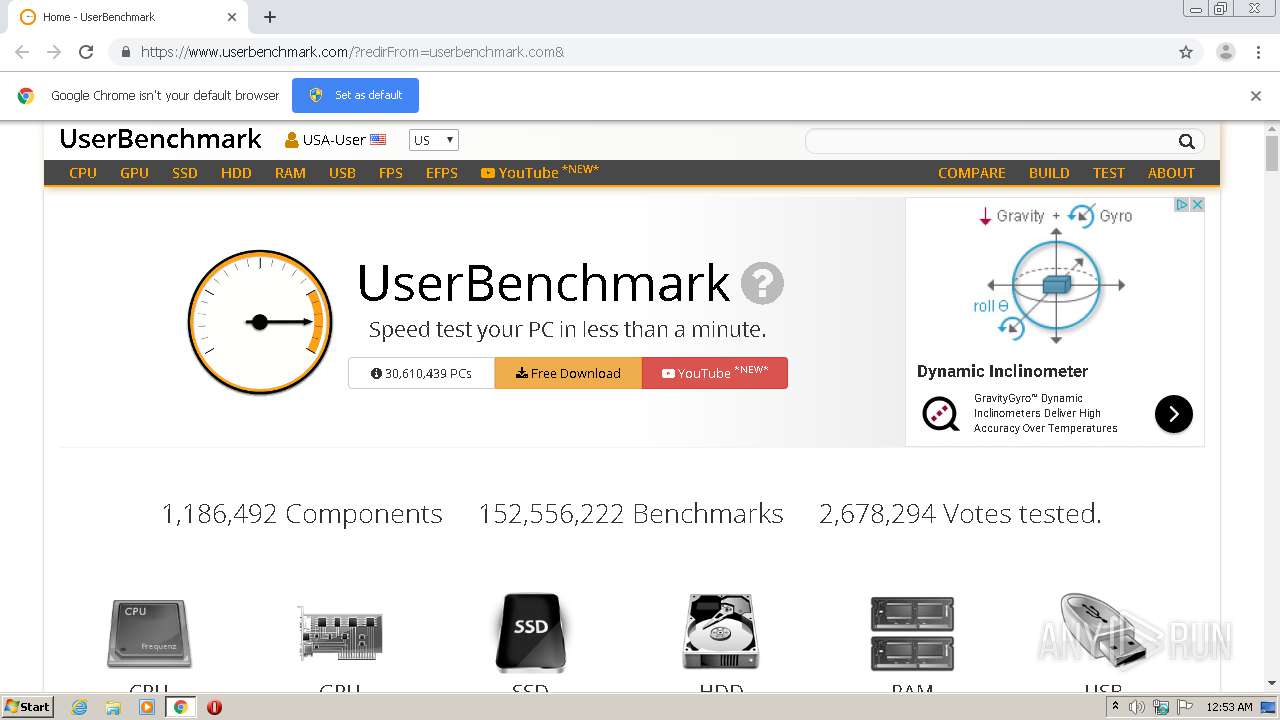
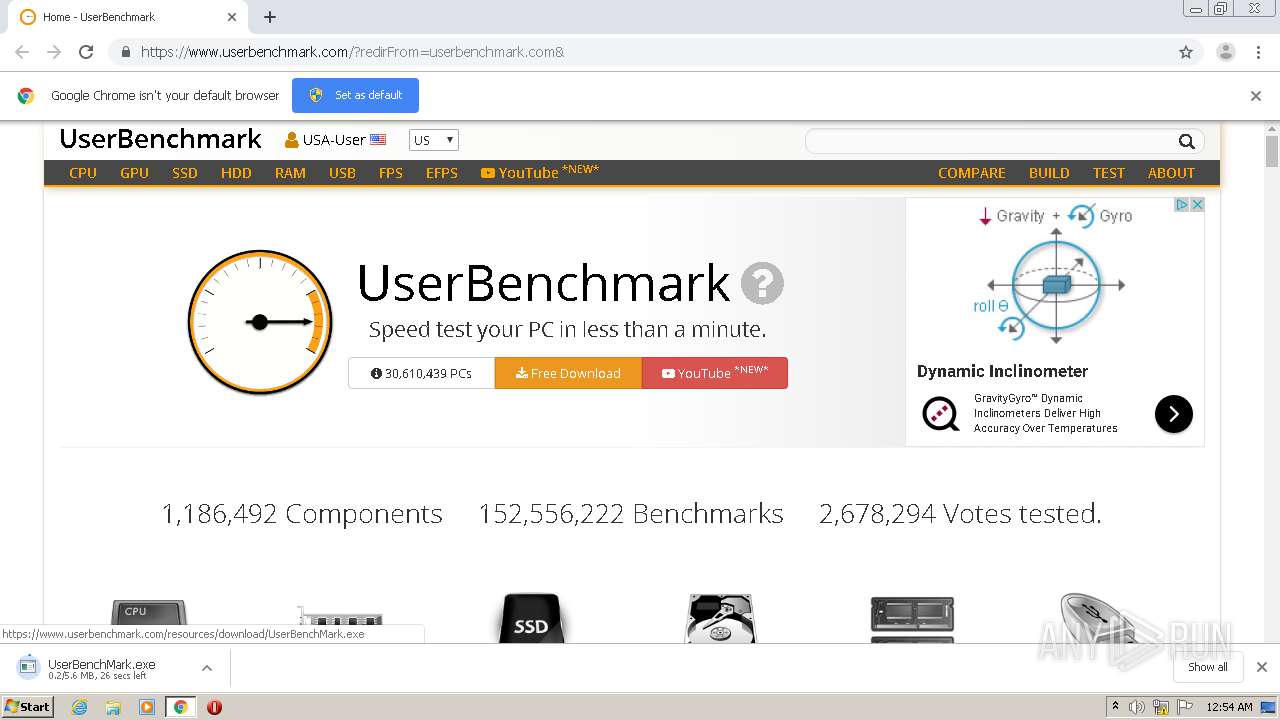
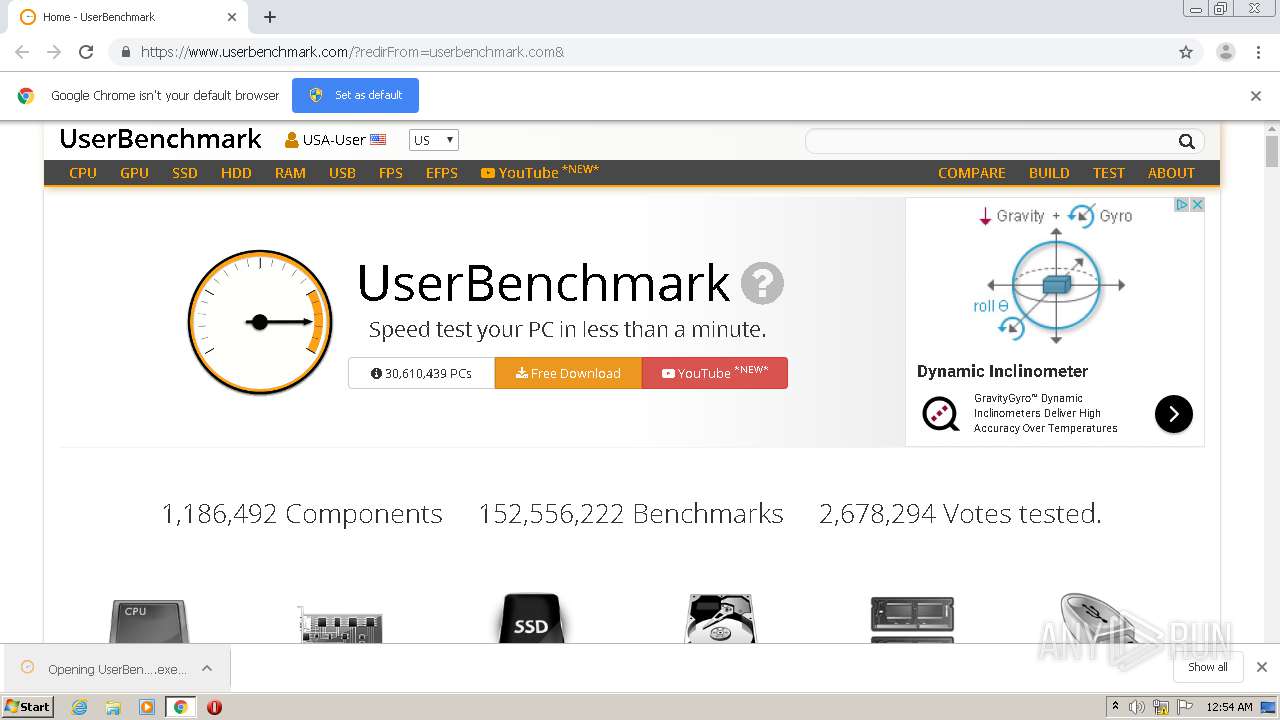
| URL: | https://userbenchmark.com |
| Full analysis: | https://app.any.run/tasks/0741449a-aed1-4c0b-a375-344899731148 |
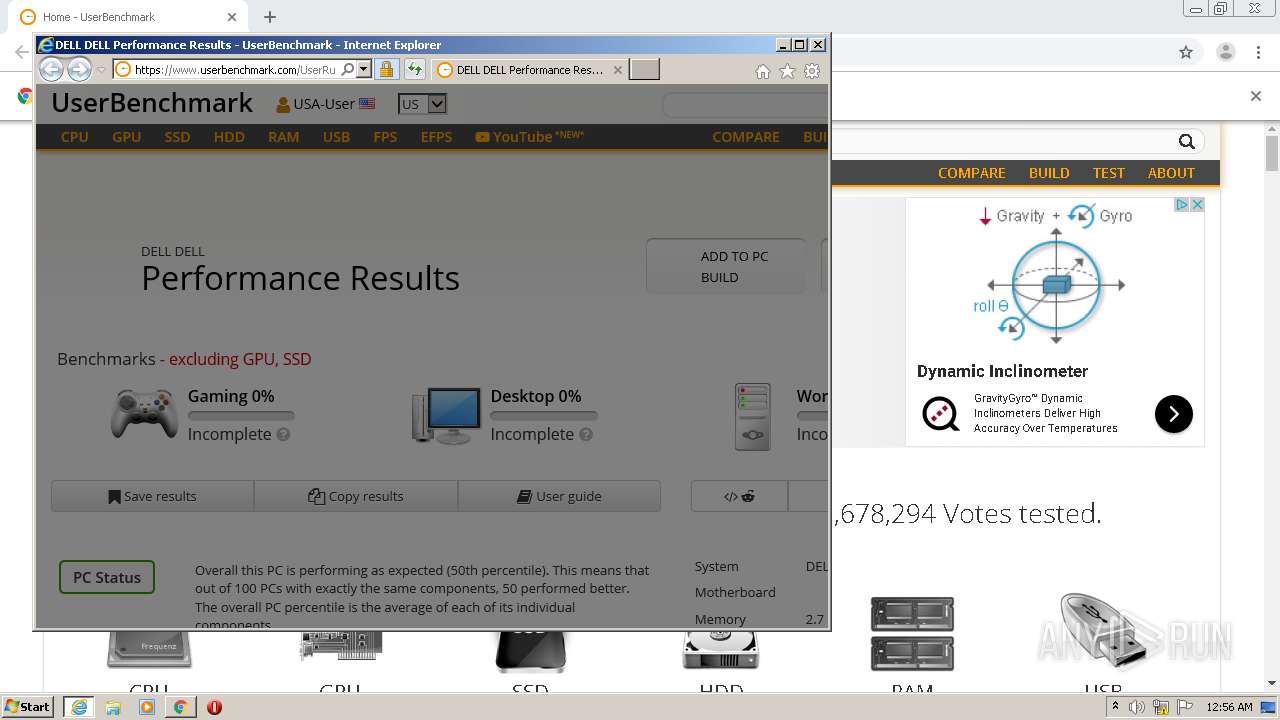
| Verdict: | Malicious activity |
| Analysis date: | July 14, 2020, 23:52:49 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | D4FBD8DE429FB99542B6E9CDCA578436 |
| SHA1: | B46E4F80550C2D888C6E3B93054E95E20B9DB72B |
| SHA256: | CCFD49D2295AF6DFF7C29ABC6AEA2B1963D441F415E9CAA7DA8D7BC450FF9AEF |
| SSDEEP: | 3:N8+a+kdI:2b+b |
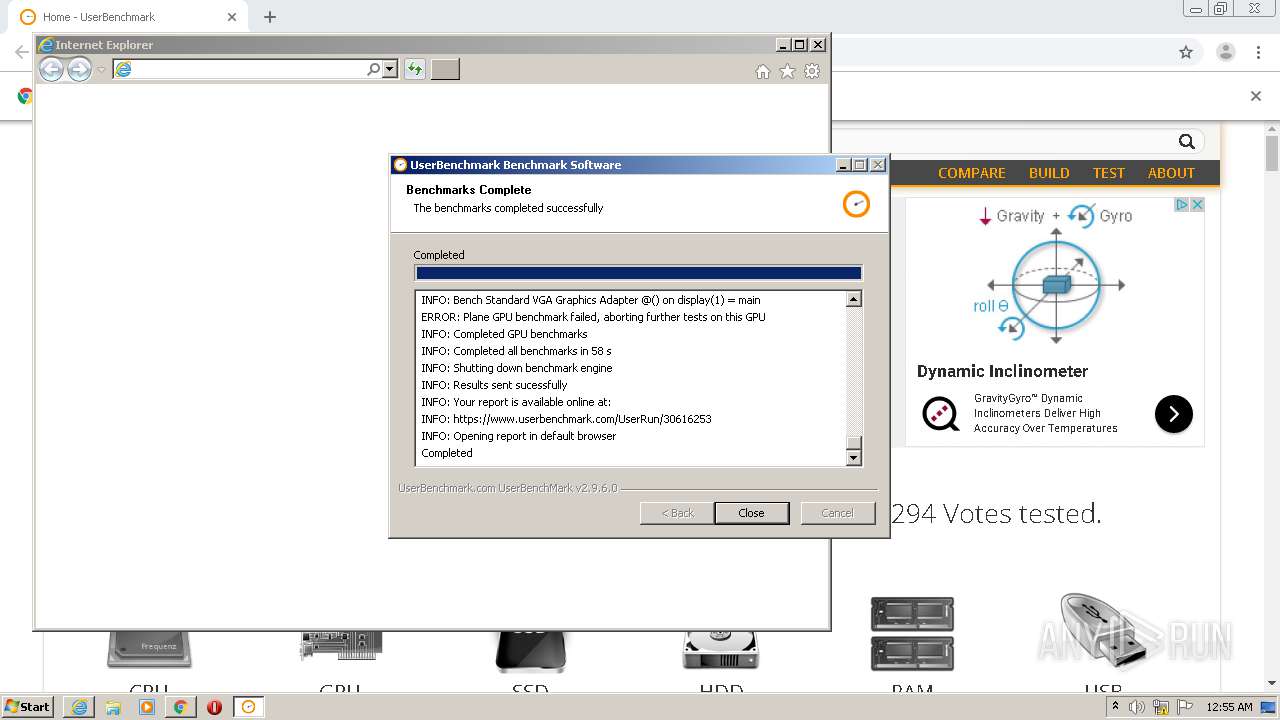
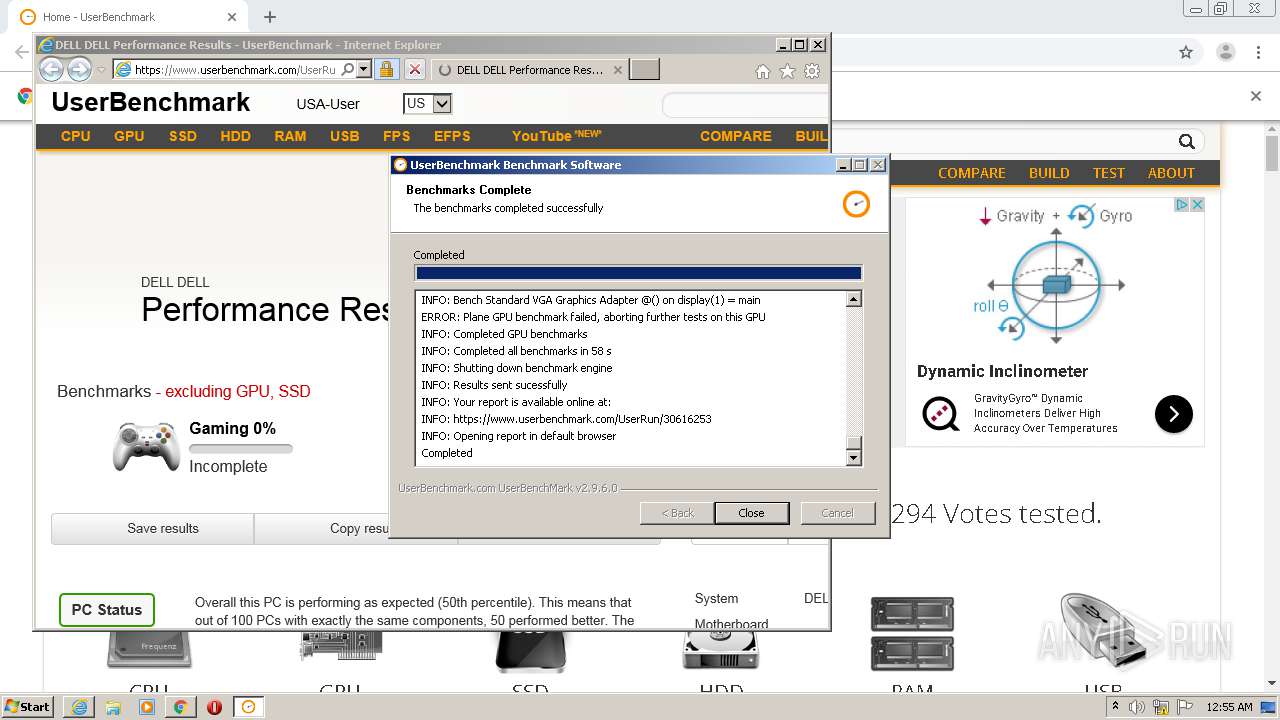
MALICIOUS
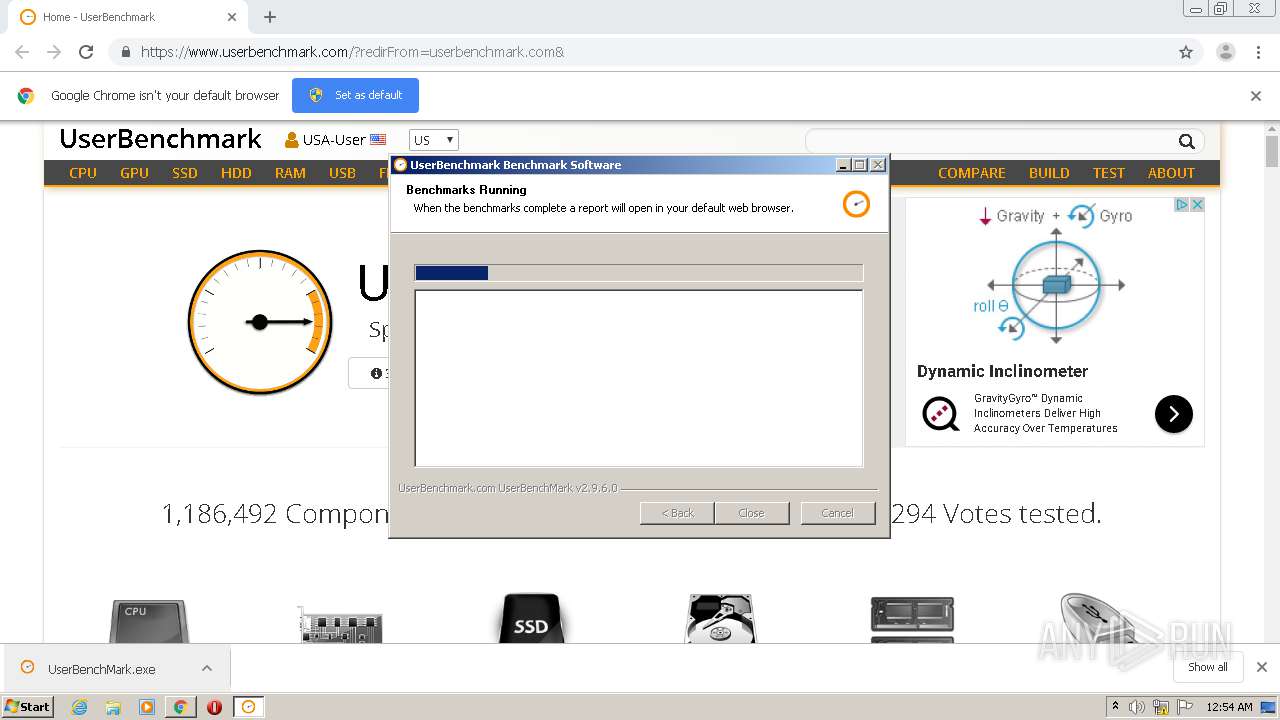
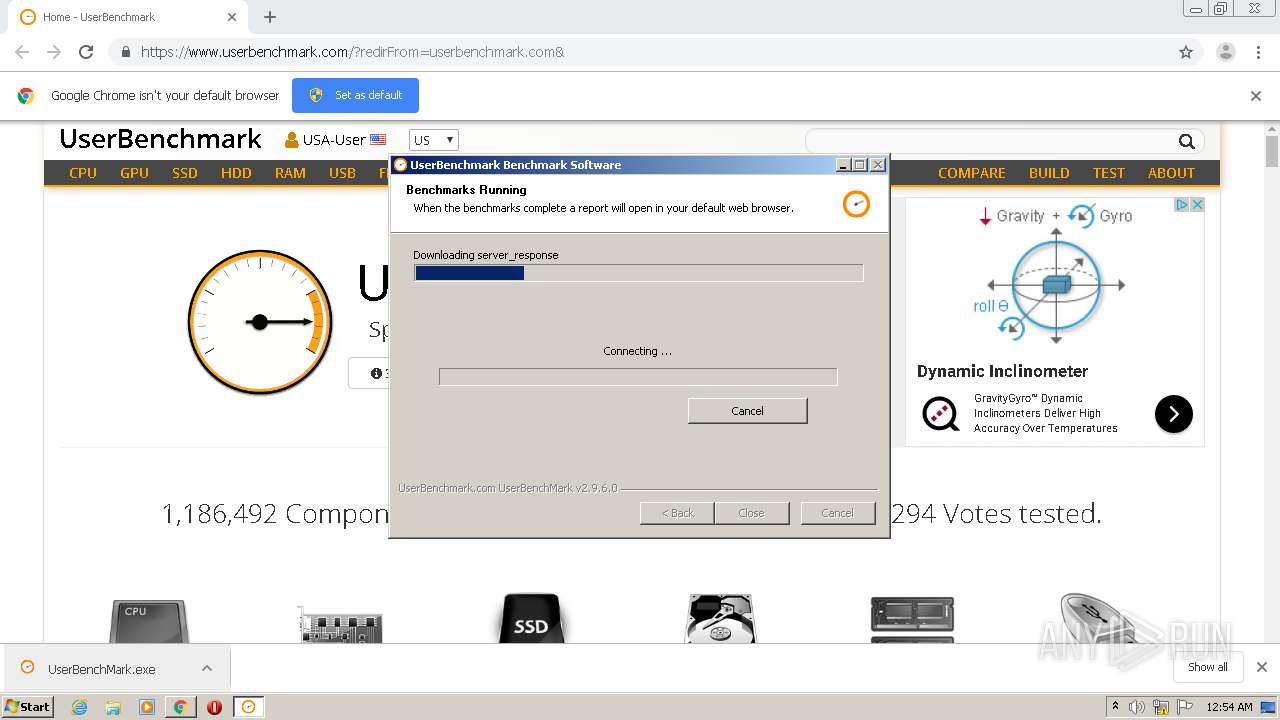
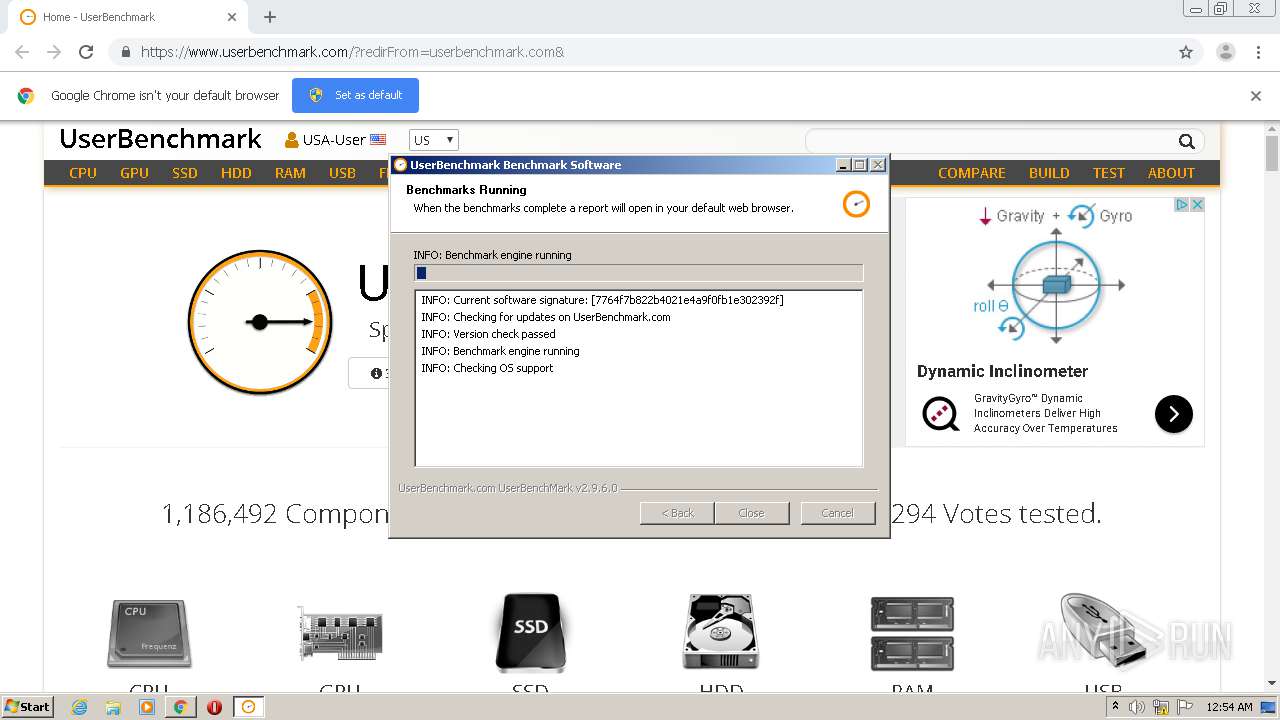
Application was dropped or rewritten from another process
- UserBenchMark.exe (PID: 3024)
- UserBenchMarkRunEngine.exe (PID: 3816)
- UBMCPUBench.exe (PID: 3380)
- UserBenchMark.exe (PID: 988)
- ns5941.tmp (PID: 2068)
- UBMDriveBench.exe (PID: 1076)
- UBMRAMBench.exe (PID: 3800)
- UBMGPUStats.exe (PID: 2064)
- UBMDriveBench.exe (PID: 1776)
- SHADOW.exe (PID: 2840)
Loads dropped or rewritten executable
- UserBenchMark.exe (PID: 3024)
- SHADOW.exe (PID: 2840)
Changes settings of System certificates
- UserBenchMark.exe (PID: 3024)
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 2868)
- chrome.exe (PID: 632)
- UserBenchMark.exe (PID: 3024)
Reads Internet Cache Settings
- UserBenchMark.exe (PID: 3024)
Adds / modifies Windows certificates
- UserBenchMark.exe (PID: 3024)
Starts application with an unusual extension
- UserBenchMark.exe (PID: 3024)
Modifies files in Chrome extension folder
- chrome.exe (PID: 2868)
Reads Environment values
- UBMGPUStats.exe (PID: 2064)
INFO
Application launched itself
- chrome.exe (PID: 2868)
Reads the hosts file
- chrome.exe (PID: 632)
- chrome.exe (PID: 2868)
Reads Internet Cache Settings
- chrome.exe (PID: 2868)
- iexplore.exe (PID: 2076)
- iexplore.exe (PID: 3528)
Reads settings of System Certificates
- UserBenchMark.exe (PID: 3024)
- iexplore.exe (PID: 3528)
- iexplore.exe (PID: 2076)
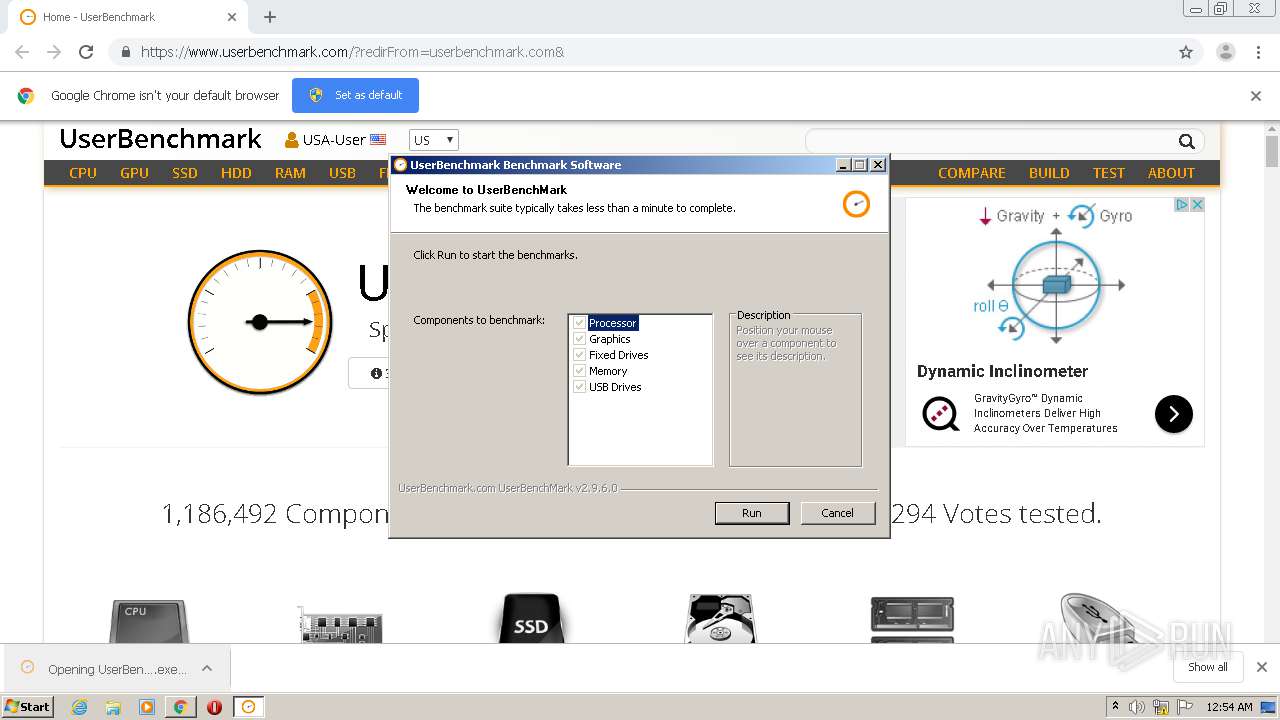
Manual execution by user
- iexplore.exe (PID: 3528)
Changes internet zones settings
- iexplore.exe (PID: 3528)
Creates files in the user directory
- iexplore.exe (PID: 2076)
Reads internet explorer settings
- iexplore.exe (PID: 2076)
Changes settings of System certificates
- iexplore.exe (PID: 3528)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3528)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
88
Monitored processes
46
Malicious processes
3
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 632 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,261042975015532927,9053586626341066999,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=11043183683625515186 --mojo-platform-channel-handle=1556 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 688 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=996,261042975015532927,9053586626341066999,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13137164266095389356 --renderer-client-id=10 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1928 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 752 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=996,261042975015532927,9053586626341066999,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10714386693170542314 --renderer-client-id=9 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2080 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 988 | "C:\Users\admin\Downloads\UserBenchMark.exe" | C:\Users\admin\Downloads\UserBenchMark.exe | — | chrome.exe | |||||||||||
User: admin Company: UserBenchmark.com Integrity Level: MEDIUM Description: Benchmark Software Exit code: 3221226540 Version: 2.9.6.0 Modules
| |||||||||||||||
| 992 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,261042975015532927,9053586626341066999,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=7494187638298166665 --mojo-platform-channel-handle=4744 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1000 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=996,261042975015532927,9053586626341066999,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14735307969506768208 --renderer-client-id=15 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2036 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1076 | UBMDriveBench.exe | C:\Users\admin\AppData\Local\Temp\UserBenchMarkTemp\UBMDriveBench.exe | — | UserBenchMarkRunEngine.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1140 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,261042975015532927,9053586626341066999,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=4927316768601032289 --mojo-platform-channel-handle=4404 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1236 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=996,261042975015532927,9053586626341066999,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=787403523620942138 --renderer-client-id=11 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3432 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1328 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=996,261042975015532927,9053586626341066999,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12082770622368388242 --renderer-client-id=22 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3896 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
2 085
Read events
1 806
Write events
272
Delete events
7
Modification events
| (PID) Process: | (2868) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2868) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2868) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2868) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2868) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2988) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2868-13239244384252750 |
Value: 259 | |||
| (PID) Process: | (2868) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2868) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2868) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
| (PID) Process: | (2868) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
24
Suspicious files
152
Text files
277
Unknown types
58
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2868 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5F0E4560-B34.pma | — | |
MD5:— | SHA256:— | |||
| 2868 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\003b5cf6-f81f-4f2c-9a71-e4ab602fa098.tmp | — | |
MD5:— | SHA256:— | |||
| 2868 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2868 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2868 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\CURRENT | — | |
MD5:— | SHA256:— | |||
| 2868 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old~RF27cbdd.TMP | text | |
MD5:— | SHA256:— | |||
| 2868 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2868 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF27cb60.TMP | text | |
MD5:— | SHA256:— | |||
| 2868 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2868 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF27cd25.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
62
TCP/UDP connections
135
DNS requests
67
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2076 | iexplore.exe | GET | 304 | 205.185.216.10:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | — | — | whitelisted |
2076 | iexplore.exe | GET | 304 | 205.185.216.10:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | — | — | whitelisted |
632 | chrome.exe | GET | 204 | 216.58.212.131:80 | http://www.gstatic.com/generate_204 | US | — | — | whitelisted |
3024 | UserBenchMark.exe | GET | 304 | 2.16.186.56:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | unknown | — | — | whitelisted |
632 | chrome.exe | GET | 302 | 172.217.21.238:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 519 b | whitelisted |
3024 | UserBenchMark.exe | GET | 304 | 2.16.186.56:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | unknown | — | — | whitelisted |
3024 | UserBenchMark.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBReAhtobFzTvhaRmVeJ38QUchY9AwQUu69%2BAj36pvE8hI6t7jiY7NkyMtQCECsuburZdTZsFIpu26N8jAc%3D | US | der | 727 b | whitelisted |
3024 | UserBenchMark.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBR64T7ooMQqLLQoy%2BemBUYZQOKh6QQUkK9qOpRaC9iQ6hJWc99DtDoo2ucCEG5WTfyjWioG40pHbBubPlo%3D | US | der | 471 b | whitelisted |
2076 | iexplore.exe | GET | 200 | 172.217.18.99:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
2076 | iexplore.exe | GET | 200 | 172.217.18.99:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
632 | chrome.exe | 216.58.207.35:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
632 | chrome.exe | 54.39.161.167:443 | userbenchmark.com | OVH SAS | FR | suspicious |
632 | chrome.exe | 2.16.186.81:80 | www.download.windowsupdate.com | Akamai International B.V. | — | whitelisted |
632 | chrome.exe | 216.58.208.35:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
632 | chrome.exe | 216.58.212.131:80 | www.gstatic.com | Google Inc. | US | whitelisted |
632 | chrome.exe | 216.58.206.13:443 | accounts.google.com | Google Inc. | US | whitelisted |
632 | chrome.exe | 172.217.23.130:443 | www.googletagservices.com | Google Inc. | US | whitelisted |
632 | chrome.exe | 172.217.22.4:443 | www.google.com | Google Inc. | US | whitelisted |
632 | chrome.exe | 104.16.133.229:443 | cdnjs.cloudflare.com | Cloudflare Inc | US | suspicious |
632 | chrome.exe | 216.58.207.40:443 | ssl.google-analytics.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
userbenchmark.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.download.windowsupdate.com |
| whitelisted |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
www.userbenchmark.com |
| suspicious |
fonts.googleapis.com |
| whitelisted |
cdnjs.cloudflare.com |
| whitelisted |
Threats
Process | Message |
|---|---|
UserBenchMark.exe | ExecShellAsUser: DLL_PROCESS_ATTACH |
UserBenchMark.exe | ExecShellAsUser: got desktop |
UserBenchMark.exe | ExecShellAsUser: elevated process detected |
UserBenchMark.exe | ExecShellAsUser: NSPIM_UNLOAD wait... |
UserBenchMark.exe | ExecShellAsUser: thread finished |
UserBenchMark.exe | ExecShellAsUser: NSPIM_UNLOAD |
UserBenchMark.exe | ExecShellAsUser: DLL_PROCESS_DETACH |