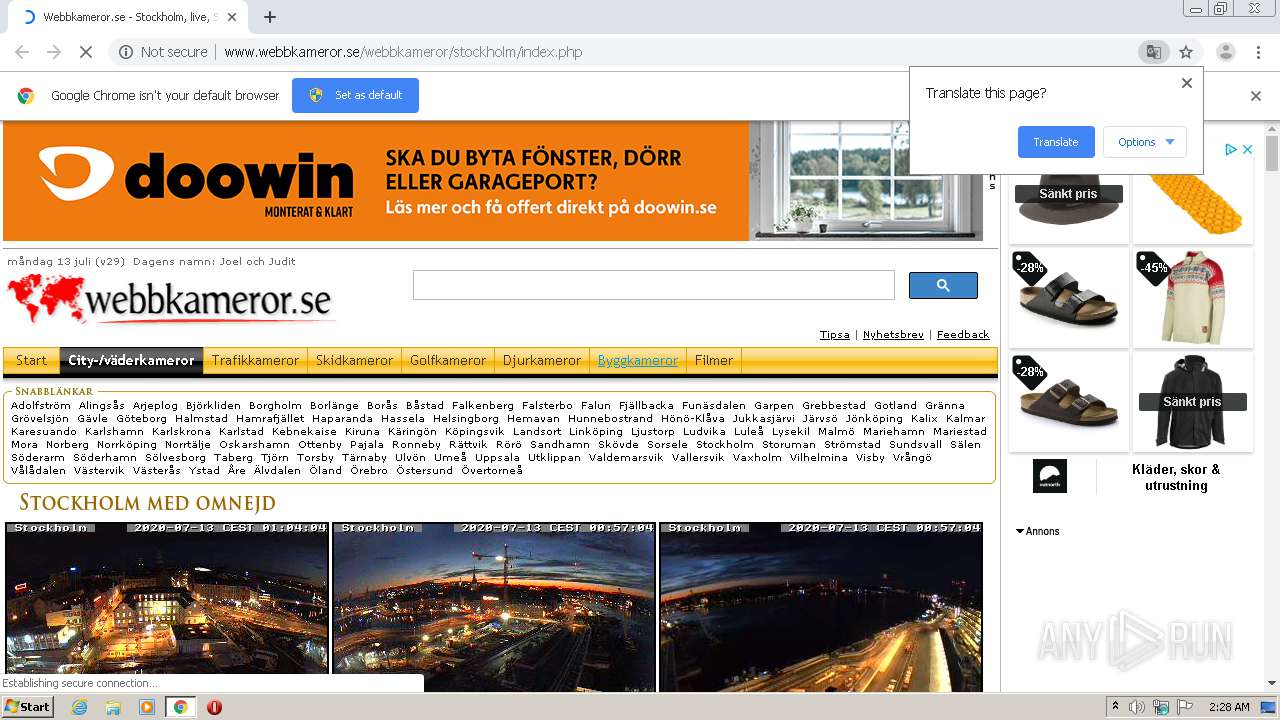
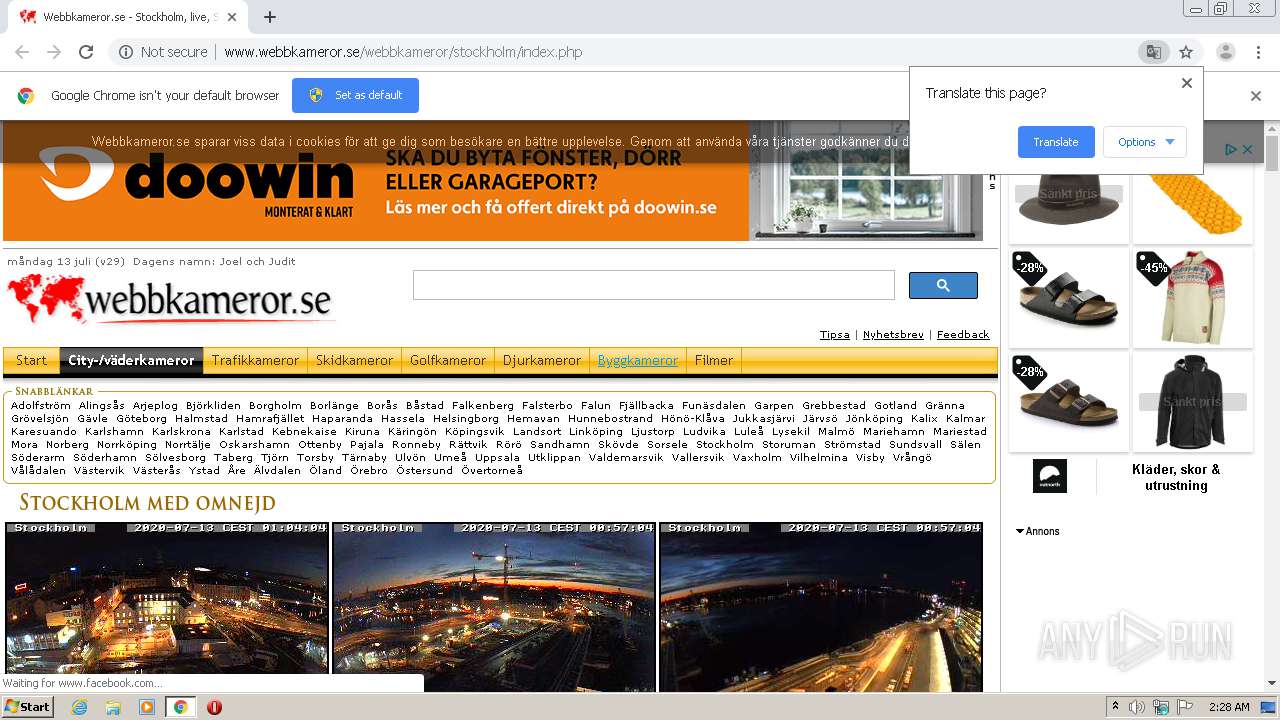
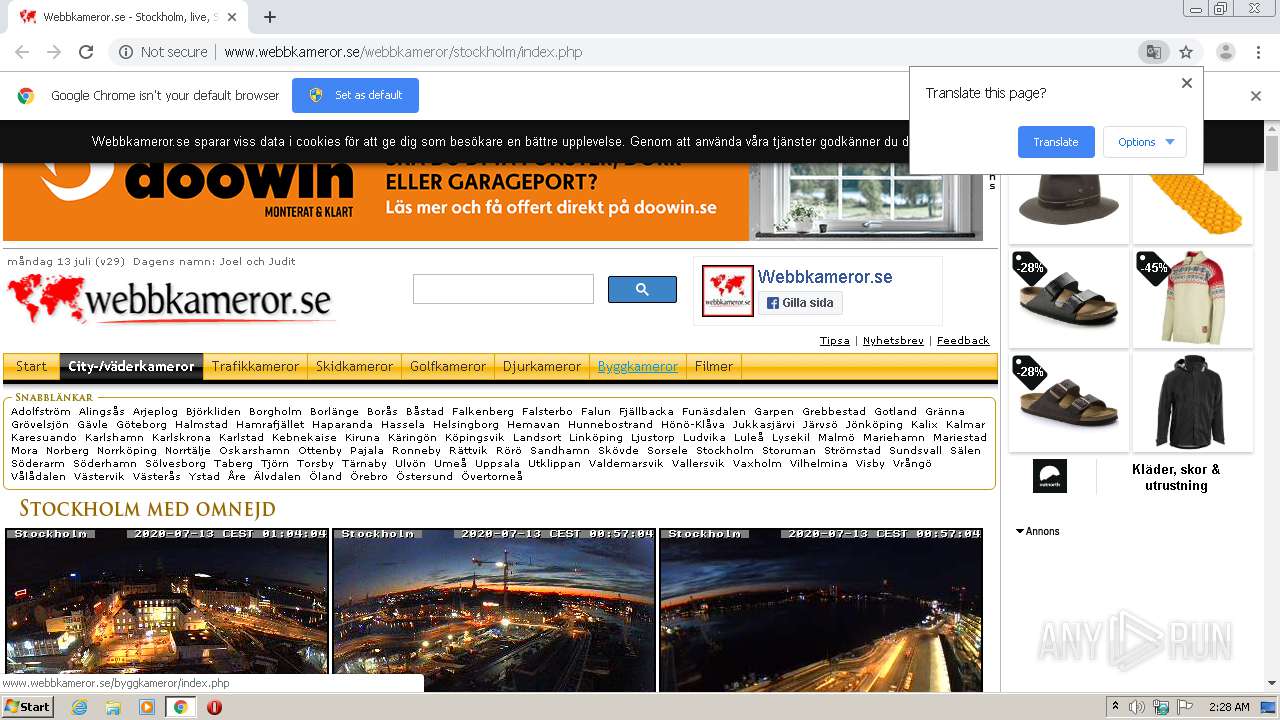
| URL: | http://www.webbkameror.se/webbkameror/stockholm/index.php |
| Full analysis: | https://app.any.run/tasks/7f4a328a-e4c8-4ebc-9c3e-53bbc5d10ef5 |
| Verdict: | Malicious activity |
| Analysis date: | July 13, 2020, 01:28:11 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | CF8BABD8F96D937AAD2DA805C2CA4399 |
| SHA1: | 41B946EB895EE62BDE4DDDE50DFA16127099E36D |
| SHA256: | CCCF4CE2829DF3F8EAFA464393CCB1A81E61F74EAD4BD092131138039D353937 |
| SSDEEP: | 3:N1KJS4TcAcLpHEIAcKIJa2bHn:Cc4oAcLpHEIAcRa2bHn |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 2280)
INFO
Reads the hosts file
- chrome.exe (PID: 2280)
- chrome.exe (PID: 3968)
Application launched itself
- chrome.exe (PID: 2280)
Reads settings of System Certificates
- chrome.exe (PID: 3968)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
64
Monitored processes
29
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 740 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,646910005326375733,12376315652985572013,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=18406145224173051478 --renderer-client-id=26 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5240 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 988 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,646910005326375733,12376315652985572013,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9302781607914822578 --mojo-platform-channel-handle=4912 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1012 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,646910005326375733,12376315652985572013,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8958640579598063861 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3308 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1360 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,646910005326375733,12376315652985572013,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4126090248522606466 --renderer-client-id=10 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3988 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1500 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,646910005326375733,12376315652985572013,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10355053163659842855 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2276 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1740 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,646910005326375733,12376315652985572013,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12304805133475499550 --renderer-client-id=17 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4620 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1936 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2260 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2080 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1012,646910005326375733,12376315652985572013,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=6894951463727935838 --mojo-platform-channel-handle=4160 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2136 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,646910005326375733,12376315652985572013,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15777771697434568016 --mojo-platform-channel-handle=5212 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2280 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "http://www.webbkameror.se/webbkameror/stockholm/index.php" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
739
Read events
647
Write events
87
Delete events
5
Modification events
| (PID) Process: | (2280) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2280) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2280) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2280) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1936) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2280-13239077305354750 |
Value: 259 | |||
| (PID) Process: | (2280) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2280) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2280) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2280) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
| (PID) Process: | (2280) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
79
Text files
298
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2280 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5F0BB8BA-8E8.pma | — | |
MD5:— | SHA256:— | |||
| 2280 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2280 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\a335cdfc-a583-4d0f-aa46-5a252b24a4aa.tmp | — | |
MD5:— | SHA256:— | |||
| 2280 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2280 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2280 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RFf697e.TMP | text | |
MD5:— | SHA256:— | |||
| 2280 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2280 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RFf6950.TMP | text | |
MD5:— | SHA256:— | |||
| 2280 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2280 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RFf6b34.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
120
TCP/UDP connections
134
DNS requests
62
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3968 | chrome.exe | GET | 200 | 87.237.210.145:80 | http://www.webbkameror.se/webbkameror/stockholm/index.php | SE | html | 13.5 Kb | whitelisted |
3968 | chrome.exe | GET | 200 | 18.194.52.173:80 | http://18.194.52.173/ImageHarvester/Images/6612copyright!!-slussen_3_320.jpg | DE | image | 14.3 Kb | unknown |
3968 | chrome.exe | GET | 200 | 87.237.210.145:80 | http://www.webbkameror.se/bilder/linje_horisontell_20.gif | SE | image | 53 b | whitelisted |
3968 | chrome.exe | GET | 200 | 87.237.210.145:80 | http://webbkameror.se/bilder/annons_pil_v.jpg | SE | image | 855 b | whitelisted |
3968 | chrome.exe | GET | 200 | 87.237.210.145:80 | http://www.webbkameror.se/webkameror.css | SE | text | 868 b | whitelisted |
3968 | chrome.exe | GET | 200 | 172.217.23.98:80 | http://pagead2.googlesyndication.com/pagead/js/adsbygoogle.js | US | text | 41.0 Kb | whitelisted |
3968 | chrome.exe | GET | 200 | 18.194.52.173:80 | http://18.194.52.173/ImageHarvester/Images/6612copyright!!-slussen_1_320.jpg | DE | image | 18.8 Kb | unknown |
3968 | chrome.exe | GET | 404 | 87.237.210.145:80 | http://87.237.210.145/~checkpoi/webcam/stureplan/webkamera_stureplan_320.jpg | SE | html | 1.80 Kb | whitelisted |
3968 | chrome.exe | GET | 200 | 87.237.210.145:80 | http://www.webbkameror.se/bilder/txt-stockholm_m_omnejd.jpg | SE | image | 11.9 Kb | whitelisted |
3968 | chrome.exe | GET | 404 | 87.237.210.145:80 | http://www.webbkameror.se/webbkameror/webkameror.css | SE | html | 1.88 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3968 | chrome.exe | 87.237.210.145:80 | www.webbkameror.se | TELE2 | SE | unknown |
3968 | chrome.exe | 172.217.21.238:80 | www.google-analytics.com | Google Inc. | US | whitelisted |
3968 | chrome.exe | 195.74.38.129:80 | webcamsallad.com | Binero AB | SE | suspicious |
3968 | chrome.exe | 195.74.38.175:80 | liveevents.nu | Binero AB | SE | suspicious |
3968 | chrome.exe | 195.74.38.149:80 | liveevent.se | Binero AB | SE | suspicious |
3968 | chrome.exe | 195.74.38.125:80 | www.liveevent.nu | Binero AB | SE | suspicious |
3968 | chrome.exe | 216.58.207.67:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3968 | chrome.exe | 216.58.207.66:443 | adservice.google.pl | Google Inc. | US | whitelisted |
3968 | chrome.exe | 195.74.38.69:80 | live24.nu | Binero AB | SE | suspicious |
3968 | chrome.exe | 89.18.104.15:80 | — | RB Communication AB | SE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
www.webbkameror.se |
| unknown |
accounts.google.com |
| shared |
chs03.cookie-script.com |
| unknown |
pagead2.googlesyndication.com |
| whitelisted |
webbkameror.se |
| whitelisted |
www.googletagservices.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
webcamsallad.com |
| suspicious |
nks.webcamsallad.com |
| suspicious |