| URL: | bing.com |
| Full analysis: | https://app.any.run/tasks/621440ed-501b-4806-bf13-d64f2c98b42e |
| Verdict: | Malicious activity |
| Analysis date: | April 21, 2025, 21:32:08 |
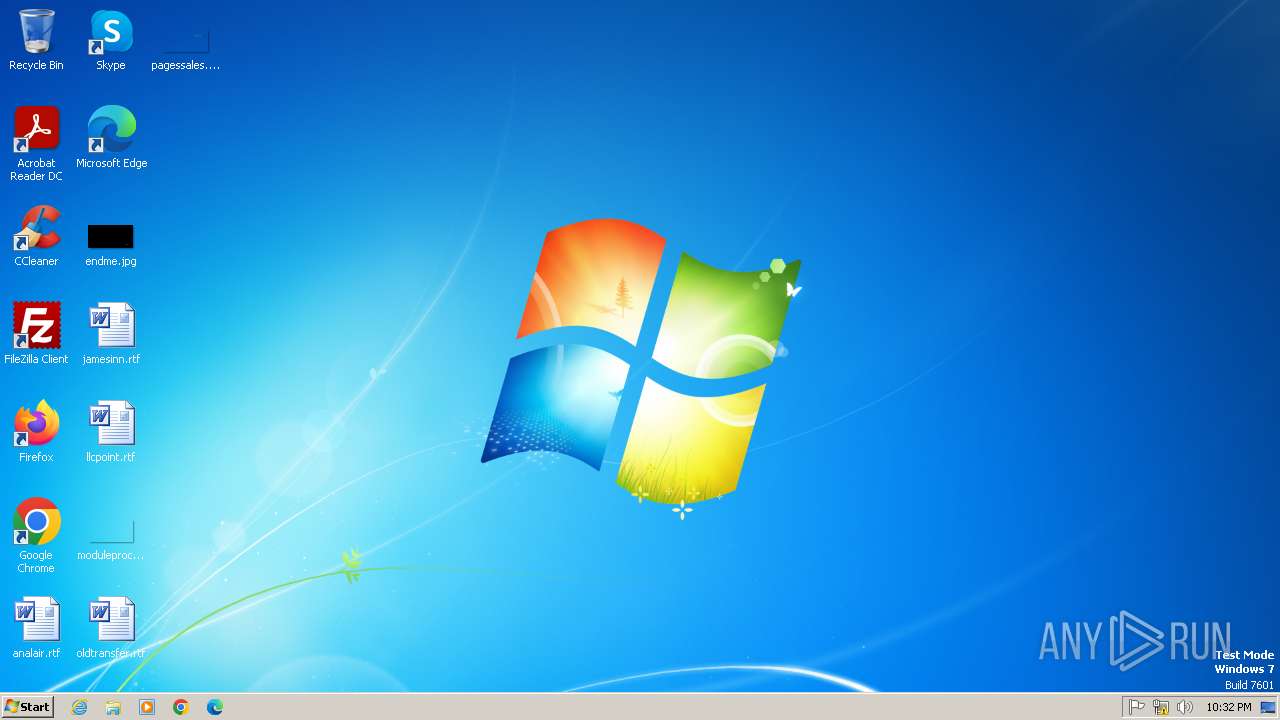
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 477C8C514F4F61EC9981125986B88987 |
| SHA1: | 2F5BF4C8E9FF1478738AF00AF07ACF4AC79B1E25 |
| SHA256: | CCBFCC1A6AF5041E560F737F8F251831E4C45C6024BE0469DE133F7FB3971E1D |
| SSDEEP: | 3:5LK:52 |
MALICIOUS
Executing a file with an untrusted certificate
- curl.exe (PID: 3792)
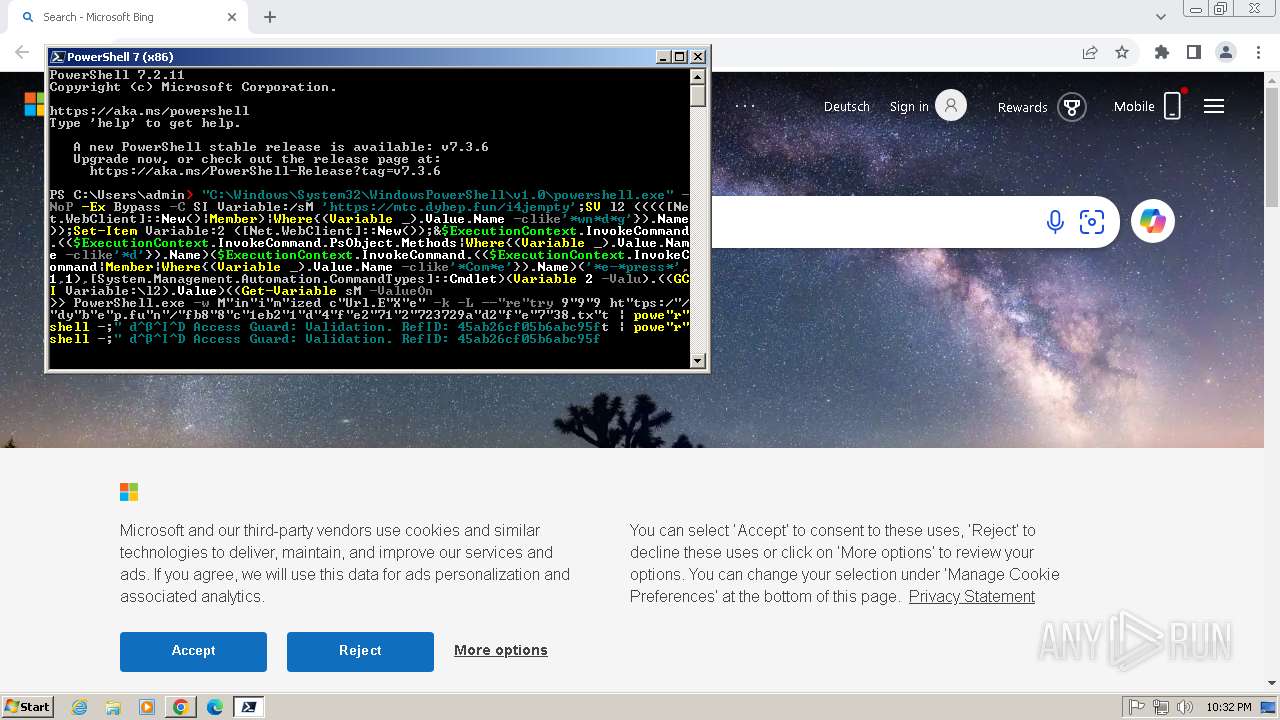
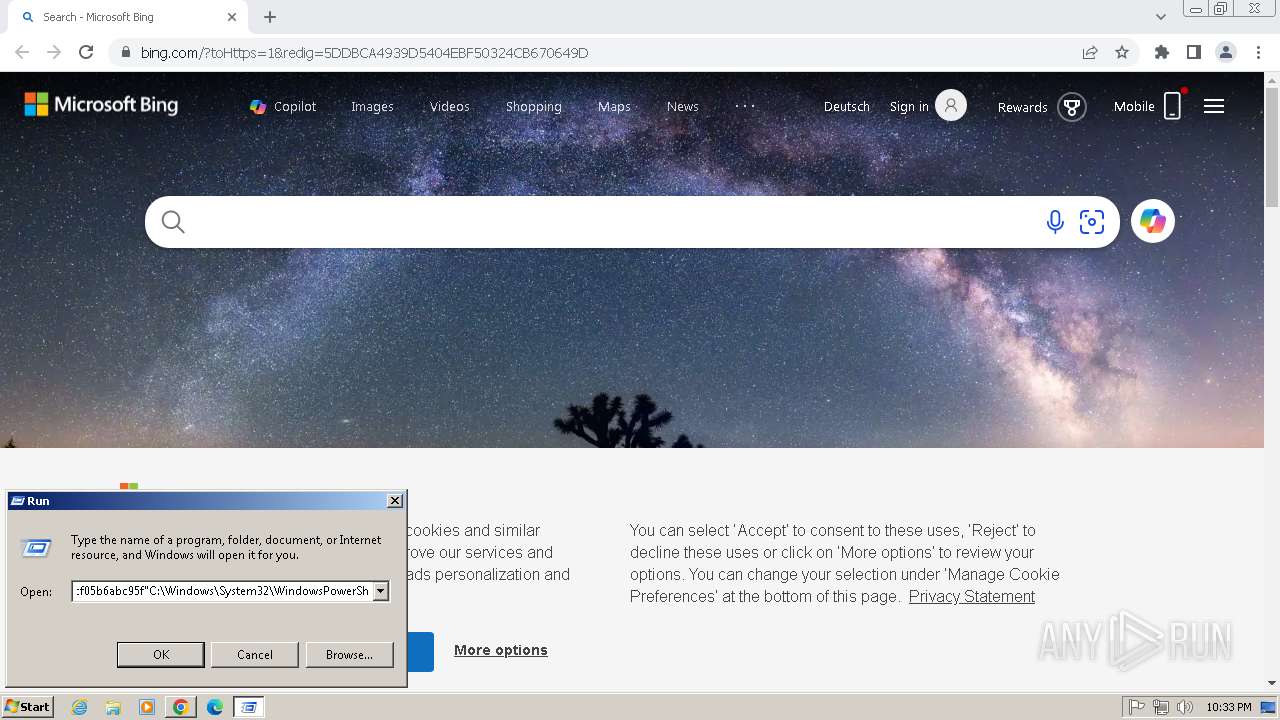
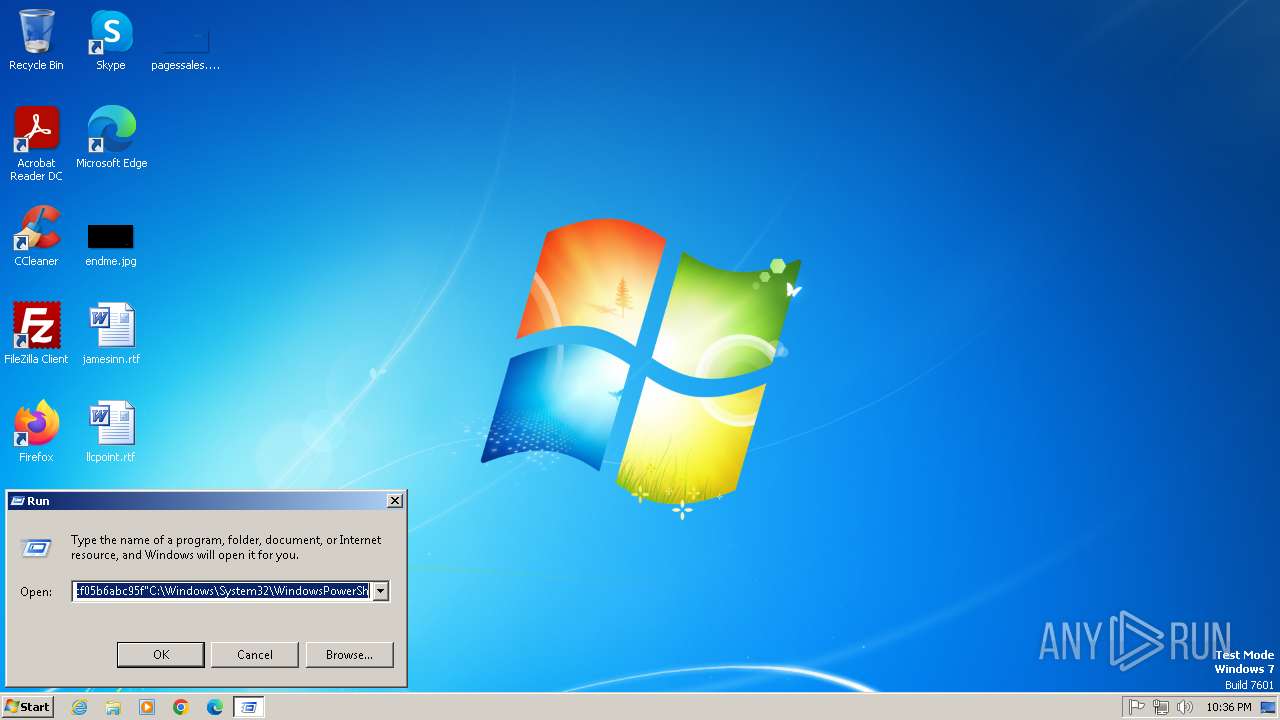
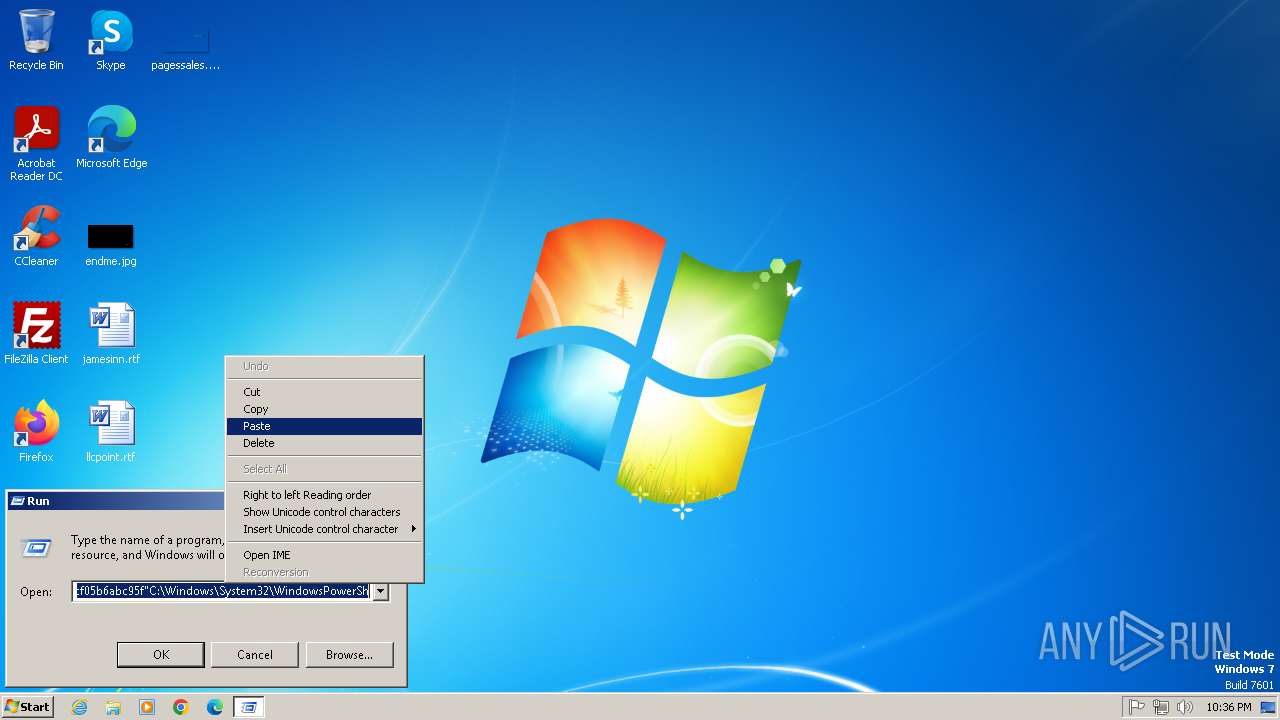
Bypass execution policy to execute commands
- powershell.exe (PID: 3912)
- powershell.exe (PID: 3520)
Changes powershell execution policy (Bypass)
- powershell.exe (PID: 3400)
Script downloads file (POWERSHELL)
- powershell.exe (PID: 3912)
SUSPICIOUS
Reads the date of Windows installation
- pwsh.exe (PID: 2780)
Application launched itself
- powershell.exe (PID: 4024)
- powershell.exe (PID: 3400)
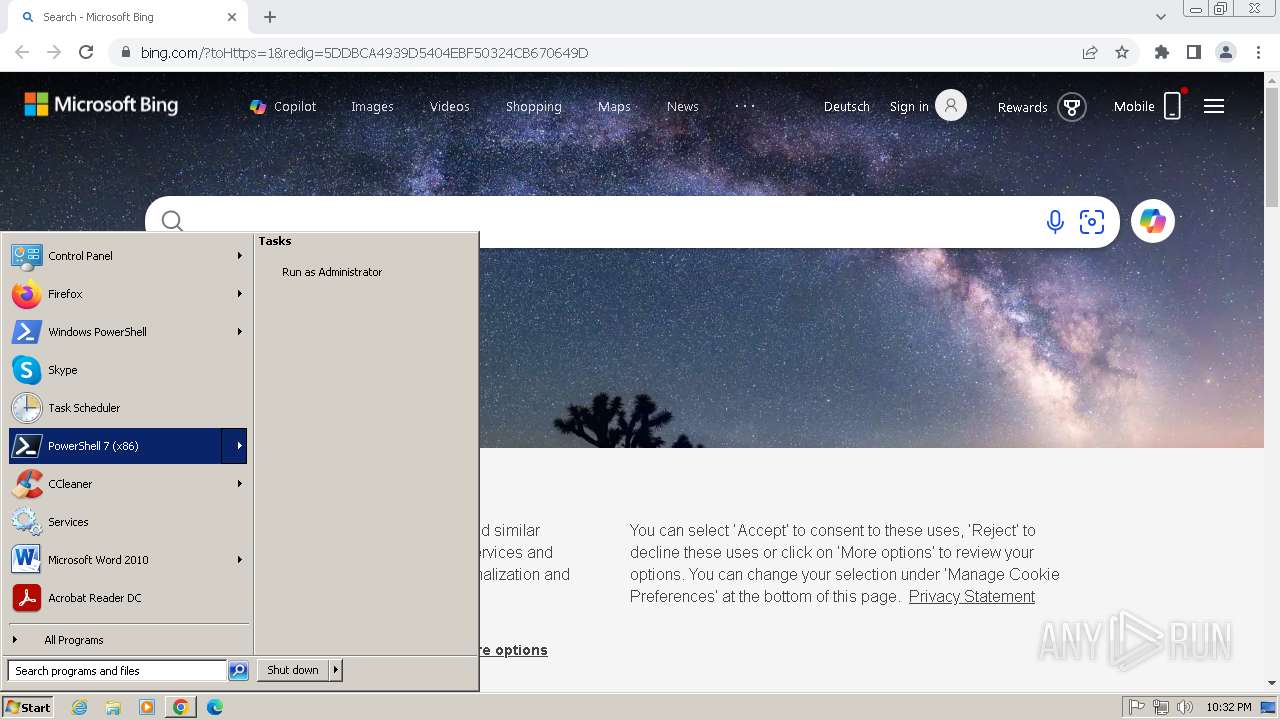
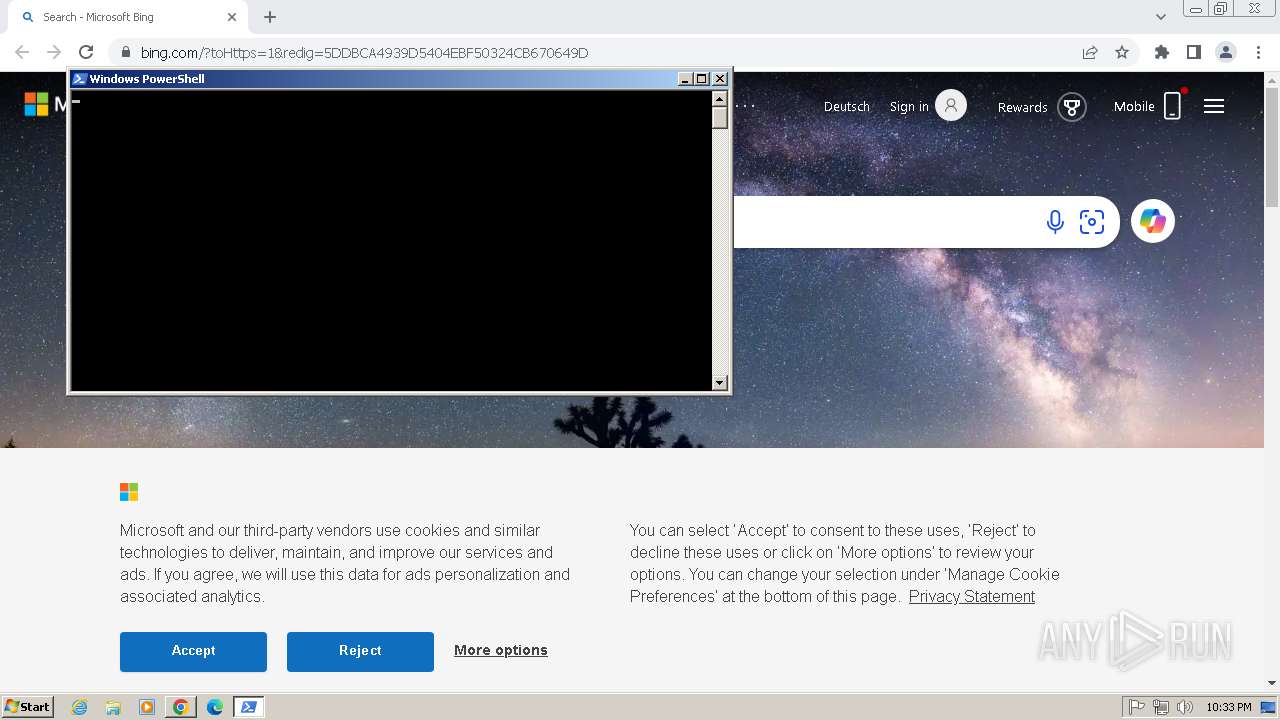
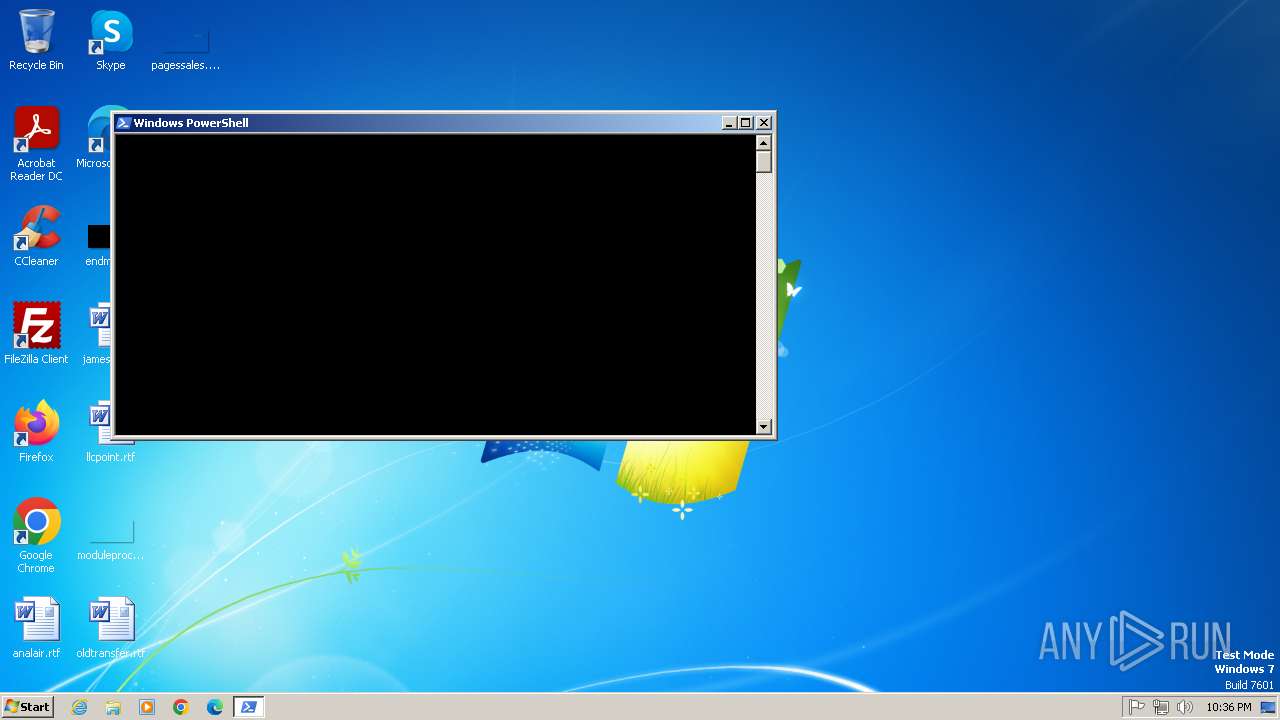
Starts POWERSHELL.EXE for commands execution
- powershell.exe (PID: 4024)
- powershell.exe (PID: 3400)
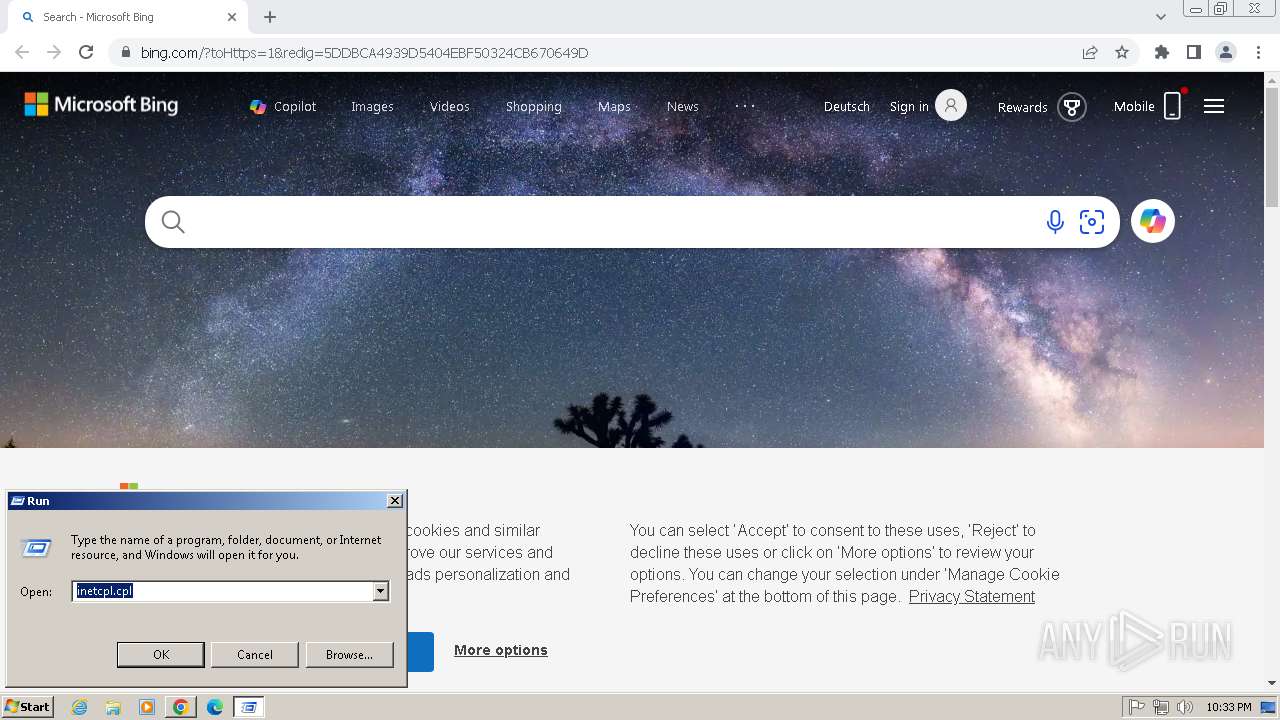
Reads the Internet Settings
- powershell.exe (PID: 3400)
- powershell.exe (PID: 3912)
- powershell.exe (PID: 4024)
Executes script without checking the security policy
- powershell.exe (PID: 3912)
- powershell.exe (PID: 3520)
Using PowerShell to operate with local accounts
- powershell.exe (PID: 4024)
The process bypasses the loading of PowerShell profile settings
- powershell.exe (PID: 3400)
INFO
Application launched itself
- chrome.exe (PID: 2848)
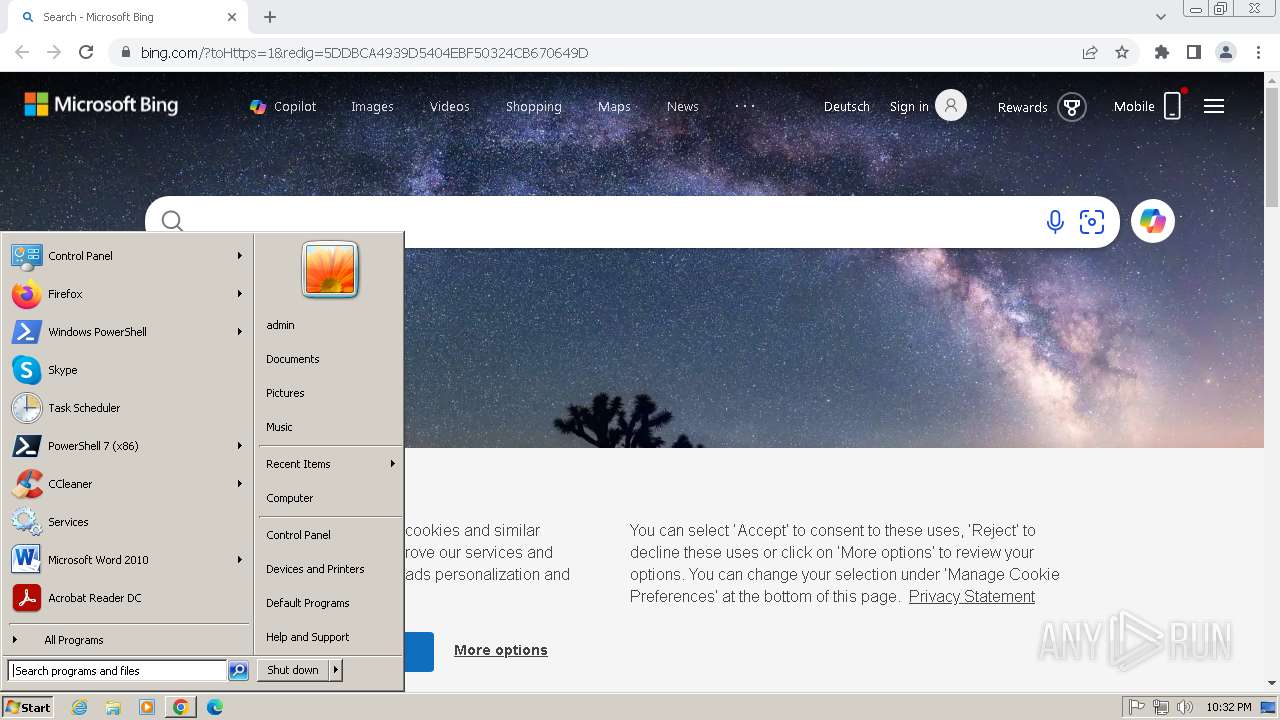
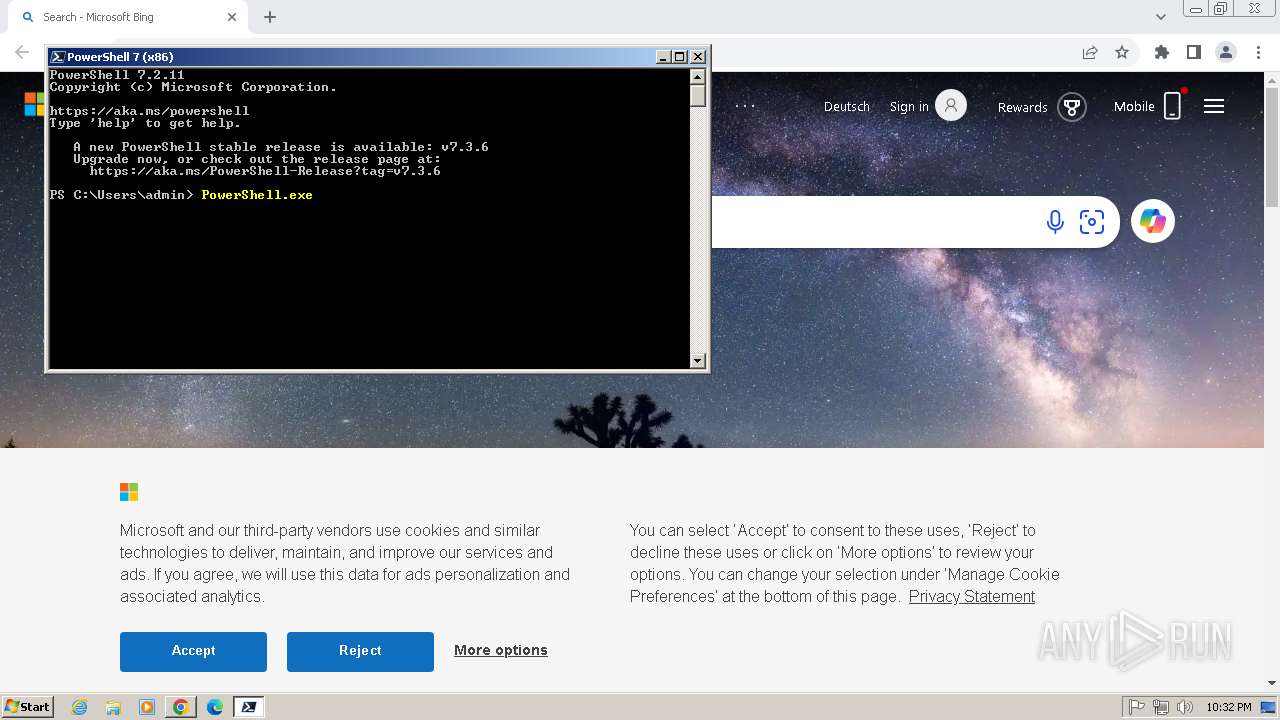
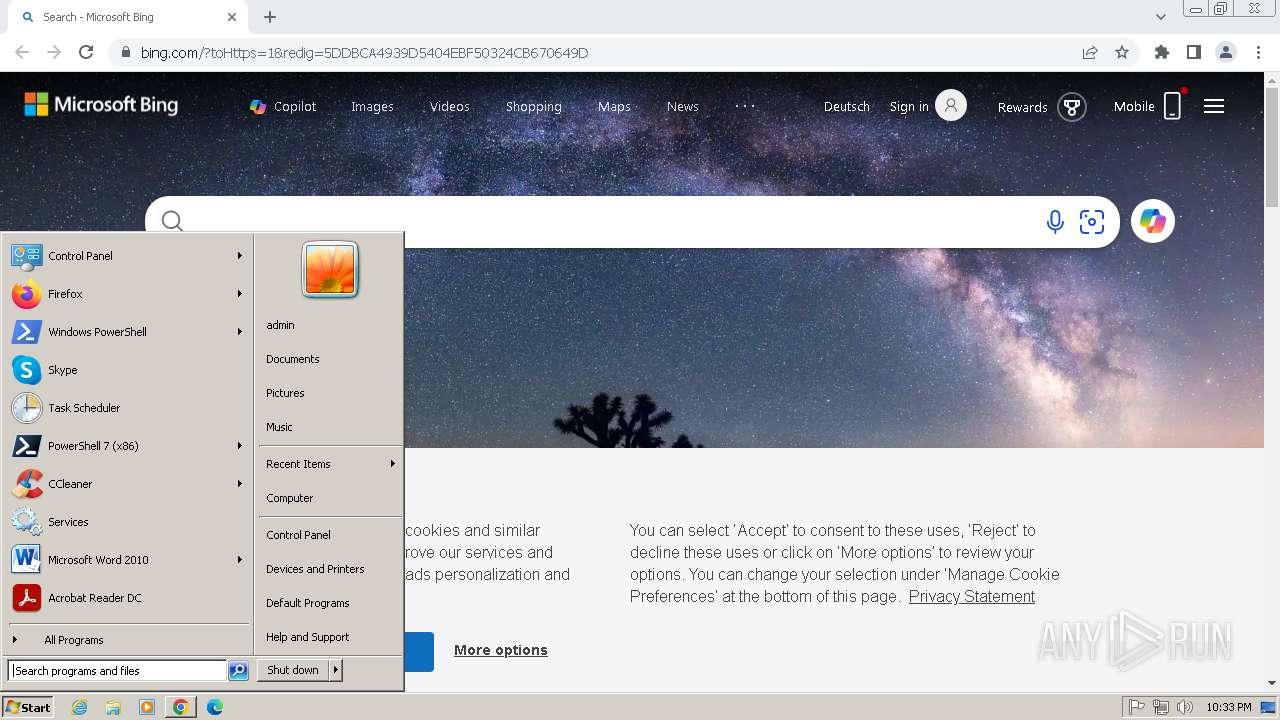
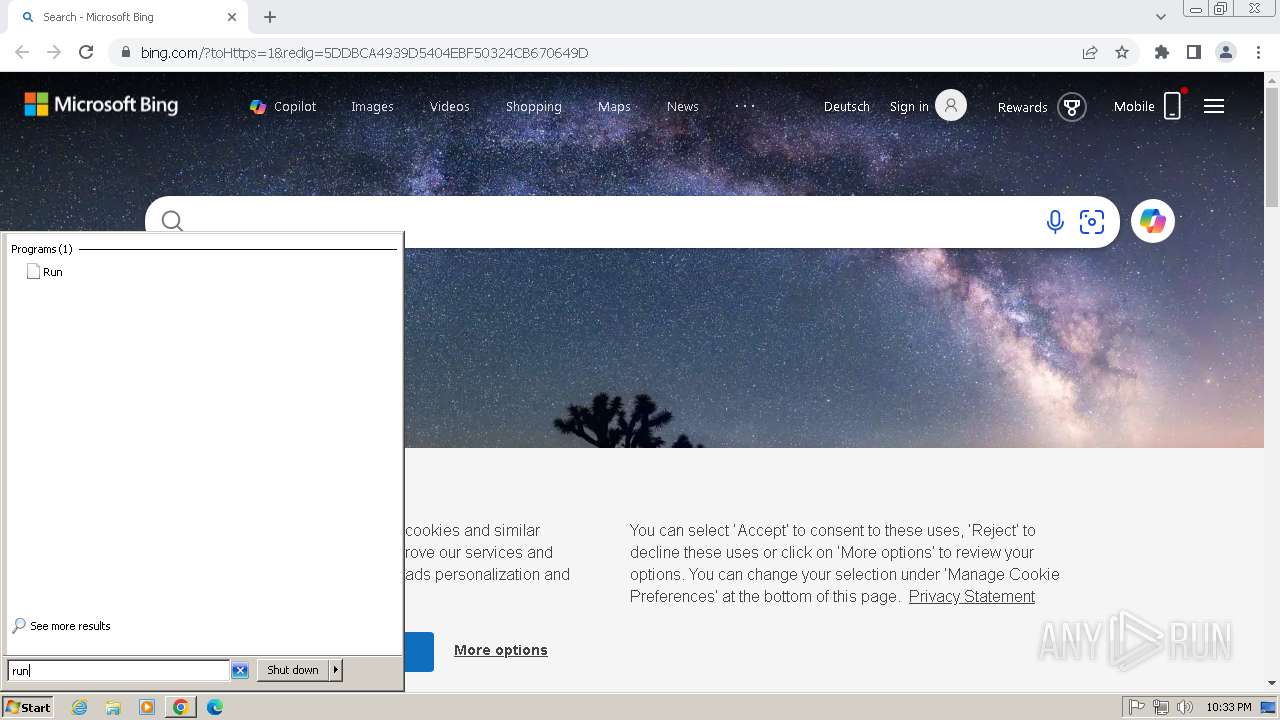
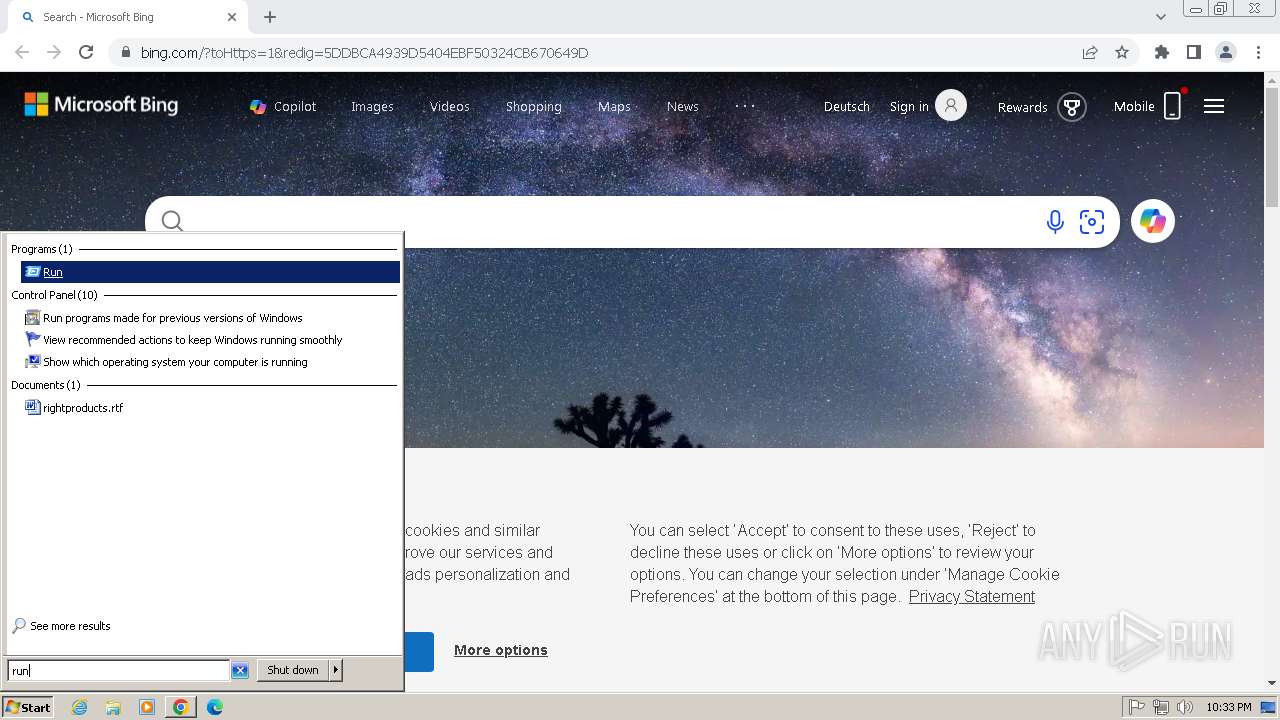
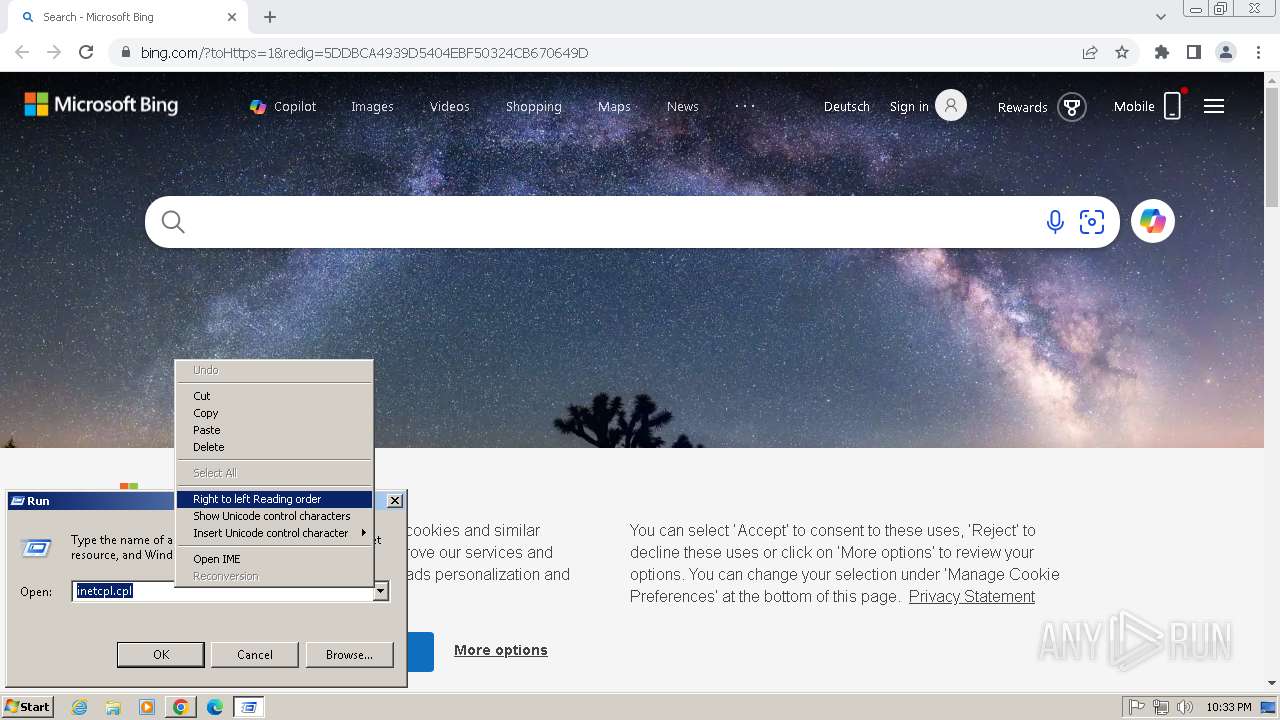
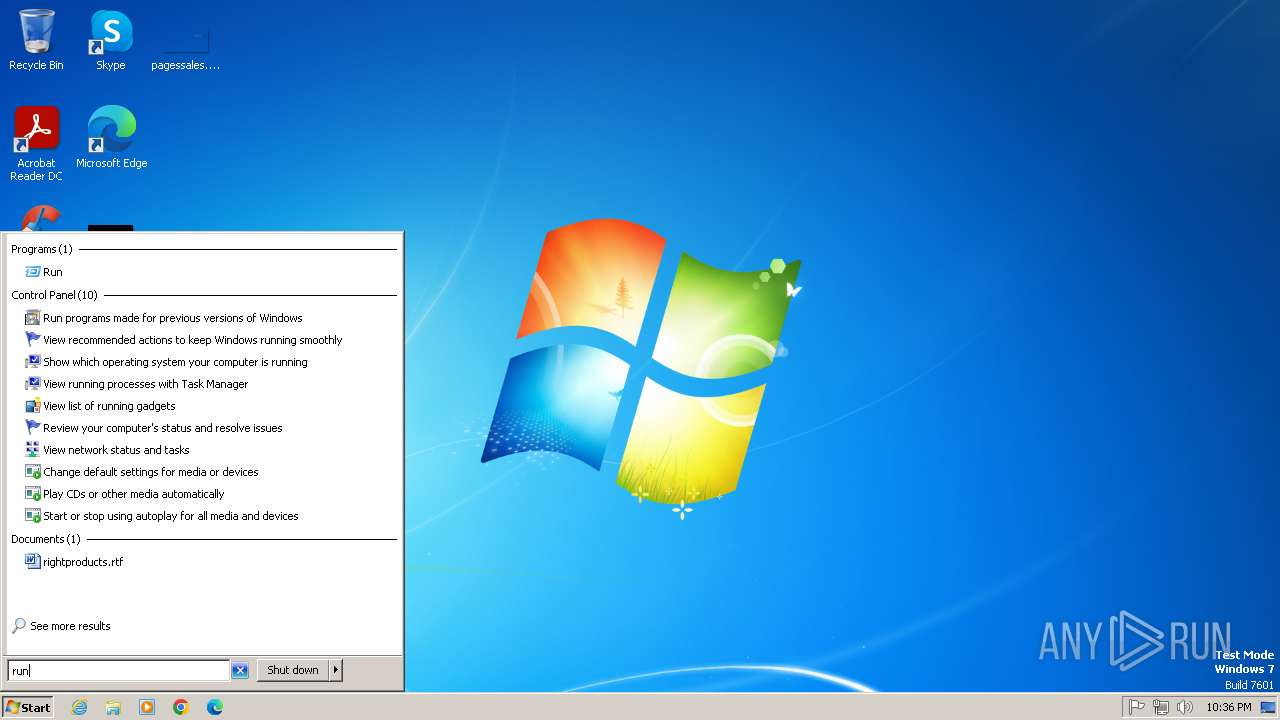
Manual execution by a user
- pwsh.exe (PID: 2780)
- powershell.exe (PID: 4024)
- powershell.exe (PID: 3520)
Checks supported languages
- pwsh.exe (PID: 2780)
- curl.exe (PID: 3792)
Reads the computer name
- pwsh.exe (PID: 2780)
- curl.exe (PID: 3792)
Reads security settings of Internet Explorer
- powershell.exe (PID: 4024)
Execution of CURL command
- powershell.exe (PID: 4024)
Create files in a temporary directory
- powershell.exe (PID: 4024)
Gets data length (POWERSHELL)
- powershell.exe (PID: 3400)
Creates or changes the value of an item property via Powershell
- powershell.exe (PID: 3400)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 4024)
- powershell.exe (PID: 3912)
- powershell.exe (PID: 3520)
Disables trace logs
- powershell.exe (PID: 3912)
The sample compiled with english language support
- chrome.exe (PID: 3840)
Executable content was dropped or overwritten
- chrome.exe (PID: 3840)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
58
Monitored processes
22
Malicious processes
3
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 892 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --extension-process --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --mojo-platform-channel-handle=2904 --field-trial-handle=1136,i,15972800205737465707,3081900770706296168,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 916 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=1852 --field-trial-handle=1136,i,15972800205737465707,3081900770706296168,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1020 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=1032 --field-trial-handle=1136,i,15972800205737465707,3081900770706296168,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1156 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=2036 --field-trial-handle=1136,i,15972800205737465707,3081900770706296168,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1460 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=1300 --field-trial-handle=1136,i,15972800205737465707,3081900770706296168,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1964 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=109.0.5414.120 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x6f578b38,0x6f578b48,0x6f578b54 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2588 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgACAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --mojo-platform-channel-handle=1088 --field-trial-handle=1136,i,15972800205737465707,3081900770706296168,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2612 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=1524 --field-trial-handle=1136,i,15972800205737465707,3081900770706296168,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2780 | "C:\Program Files\PowerShell\7\pwsh.exe" -WorkingDirectory ~ | C:\Program Files\PowerShell\7\pwsh.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: pwsh Exit code: 3221225786 Version: 7.2.11.500 Modules
| |||||||||||||||
| 2848 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking --disable-features=OptimizationGuideModelDownloading,OptimizationHintsFetching,OptimizationTargetPrediction,OptimizationHints "bing.com" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
Total events
19 110
Read events
18 850
Write events
258
Delete events
2
Modification events
| (PID) Process: | (2848) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2848) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2848) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
| (PID) Process: | (2848) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
| (PID) Process: | (2848) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_enableddate |
Value: 0 | |||
| (PID) Process: | (2848) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2848) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2848) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2848) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2848) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
Executable files
4
Suspicious files
116
Text files
42
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2848 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF182e9c.TMP | — | |
MD5:— | SHA256:— | |||
| 2848 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2848 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Variations | binary | |
MD5:961E3604F228B0D10541EBF921500C86 | SHA256:F7B24F2EB3D5EB0550527490395D2F61C3D2FE74BB9CB345197DAD81B58B5FED | |||
| 2848 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 2848 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old | text | |
MD5:A24B909E4573DE480D459FBFBD20D770 | SHA256:E7D33D7AD48DE7D8C150ED0DA355C8ACE856C8C5F7DEE13CD74EE41B13748284 | |||
| 2848 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF182f19.TMP | text | |
MD5:456D3EF989973A7C218E338A6CFFAD25 | SHA256:75631D994431F254B94255C50038A3657BFC45D76FCE9D794D514E57CA678872 | |||
| 2848 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:9F941EA08DBDCA2EB3CFA1DBBBA6F5DC | SHA256:127F71DF0D2AD895D4F293E62284D85971AE047CA15F90B87BF6335898B0B655 | |||
| 2848 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF183544.TMP | — | |
MD5:— | SHA256:— | |||
| 2848 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2848 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old~RF1832b3.TMP | text | |
MD5:FF6BABA737D50E515029C3F3A1305BBC | SHA256:670EED15EAA8E3F1A4F8612B229654EB0C64107AEAF0B1017E4BD45E3F7EED83 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
24
TCP/UDP connections
59
DNS requests
64
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1460 | chrome.exe | GET | 301 | 150.171.28.10:80 | http://bing.com/ | unknown | — | — | whitelisted |
860 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acvebl5hyowh6yyy3wmoaw5wbfpa_4.10.2830.100/oimompecagnajdejgnnjijobebaeigek_4.10.2830.100_win32_acmfn7n2mz6vs4wnlypsmq4uakaq.crx3 | unknown | — | — | whitelisted |
860 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acvebl5hyowh6yyy3wmoaw5wbfpa_4.10.2830.100/oimompecagnajdejgnnjijobebaeigek_4.10.2830.100_win32_acmfn7n2mz6vs4wnlypsmq4uakaq.crx3 | unknown | — | — | whitelisted |
860 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acvebl5hyowh6yyy3wmoaw5wbfpa_4.10.2830.100/oimompecagnajdejgnnjijobebaeigek_4.10.2830.100_win32_acmfn7n2mz6vs4wnlypsmq4uakaq.crx3 | unknown | — | — | whitelisted |
860 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acvebl5hyowh6yyy3wmoaw5wbfpa_4.10.2830.100/oimompecagnajdejgnnjijobebaeigek_4.10.2830.100_win32_acmfn7n2mz6vs4wnlypsmq4uakaq.crx3 | unknown | — | — | whitelisted |
1460 | chrome.exe | GET | 302 | 2.23.227.215:80 | http://www.bing.com/ | unknown | — | — | whitelisted |
860 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acvebl5hyowh6yyy3wmoaw5wbfpa_4.10.2830.100/oimompecagnajdejgnnjijobebaeigek_4.10.2830.100_win32_acmfn7n2mz6vs4wnlypsmq4uakaq.crx3 | unknown | — | — | whitelisted |
860 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acvebl5hyowh6yyy3wmoaw5wbfpa_4.10.2830.100/oimompecagnajdejgnnjijobebaeigek_4.10.2830.100_win32_acmfn7n2mz6vs4wnlypsmq4uakaq.crx3 | unknown | — | — | whitelisted |
860 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acvebl5hyowh6yyy3wmoaw5wbfpa_4.10.2830.100/oimompecagnajdejgnnjijobebaeigek_4.10.2830.100_win32_acmfn7n2mz6vs4wnlypsmq4uakaq.crx3 | unknown | — | — | whitelisted |
860 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acvebl5hyowh6yyy3wmoaw5wbfpa_4.10.2830.100/oimompecagnajdejgnnjijobebaeigek_4.10.2830.100_win32_acmfn7n2mz6vs4wnlypsmq4uakaq.crx3 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | whitelisted |
1460 | chrome.exe | 150.171.28.10:80 | bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2848 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
1460 | chrome.exe | 173.194.76.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
1460 | chrome.exe | 2.23.227.215:80 | www.bing.com | Ooredoo Q.S.C. | QA | whitelisted |
1460 | chrome.exe | 2.23.227.215:443 | www.bing.com | Ooredoo Q.S.C. | QA | whitelisted |
1460 | chrome.exe | 2.16.241.201:443 | r.bing.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
bing.com |
| whitelisted |
accounts.google.com |
| whitelisted |
www.bing.com |
| whitelisted |
r.bing.com |
| whitelisted |
assets.msn.com |
| whitelisted |
www.msn.com |
| whitelisted |
www.google.com |
| whitelisted |
c.msn.com |
| whitelisted |
browser.events.data.msn.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2780 | pwsh.exe | Not Suspicious Traffic | INFO [ANY.RUN] Azure Front Door domain observed in TLS SNI ( .azurefd .net) |
Process | Message |
|---|---|
pwsh.exe | Profiler was prevented from loading notification profiler due to app settings.
Process ID (decimal): 2780. Message ID: [0x2509].
|