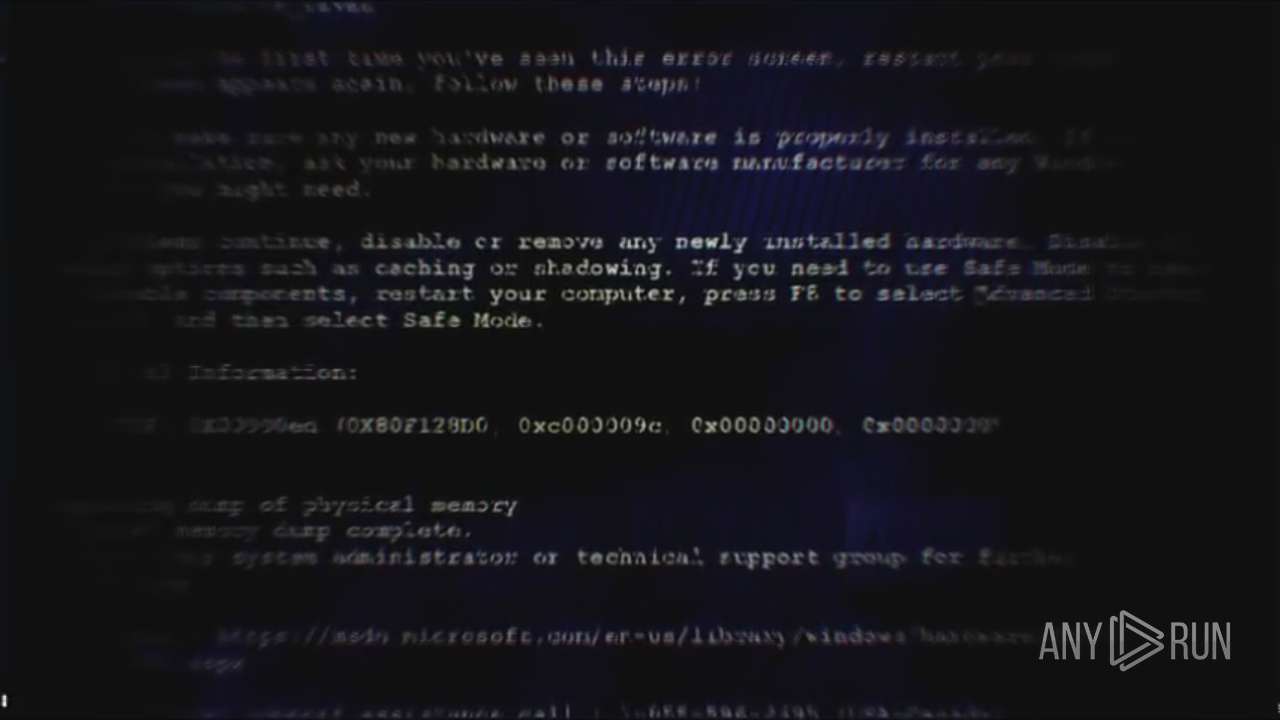
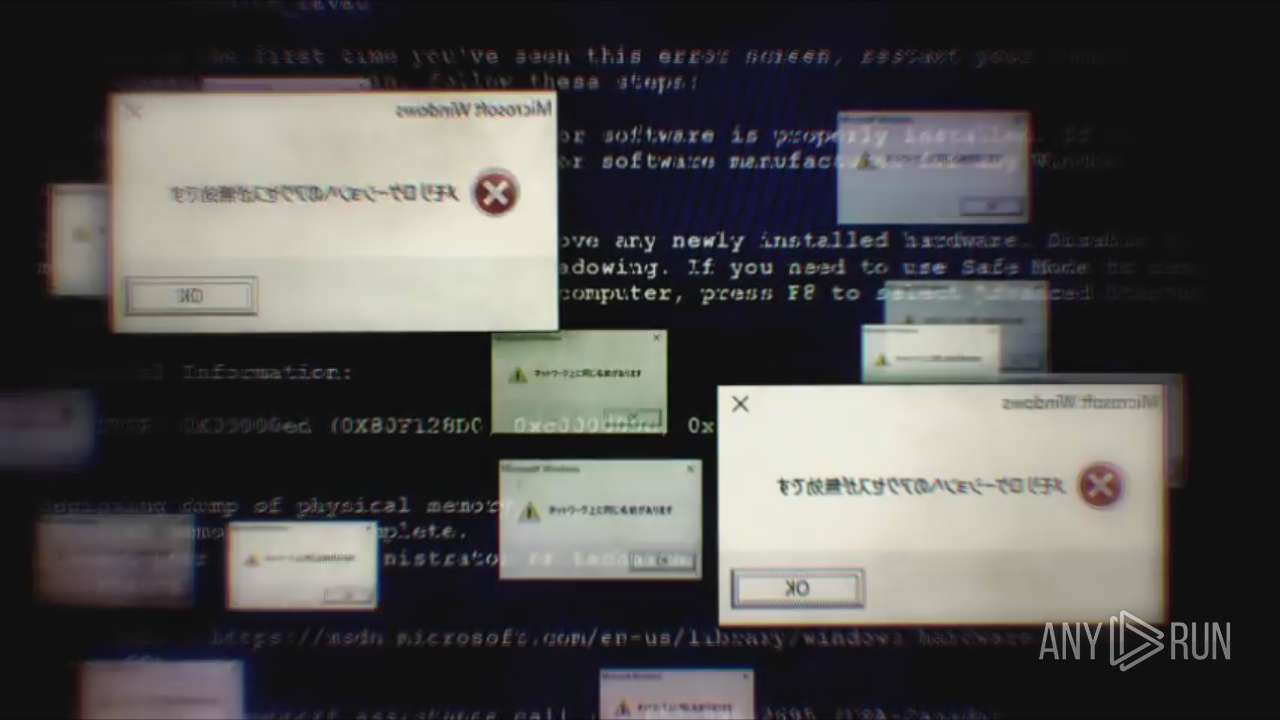
| File name: | Endermanch@ChilledWindows.exe |
| Full analysis: | https://app.any.run/tasks/09b44b6d-b28e-45ce-9799-d41c94e3cc74 |
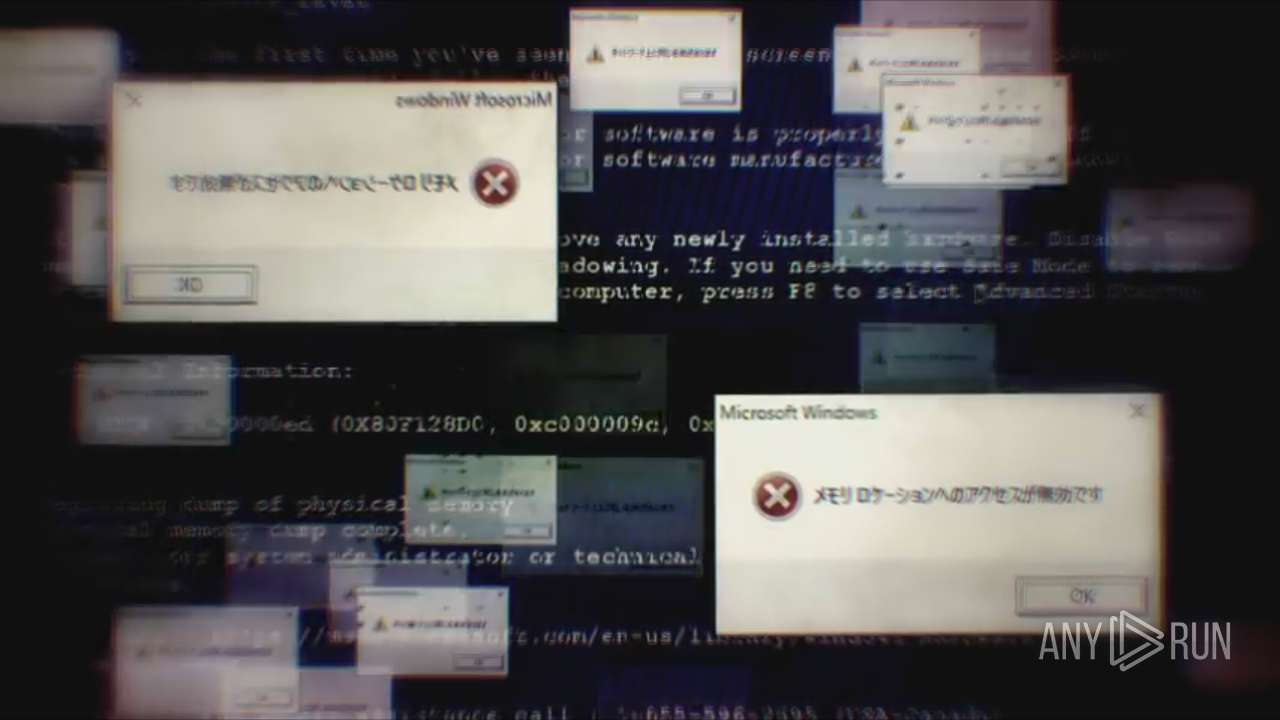
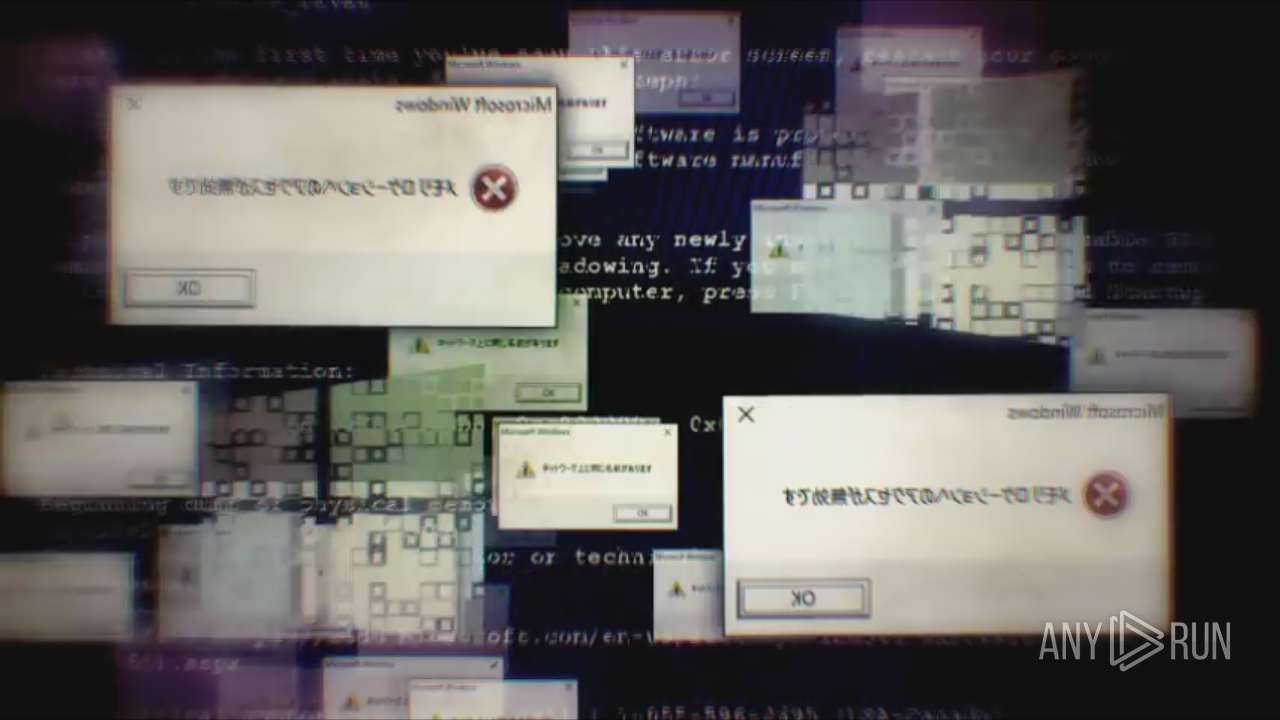
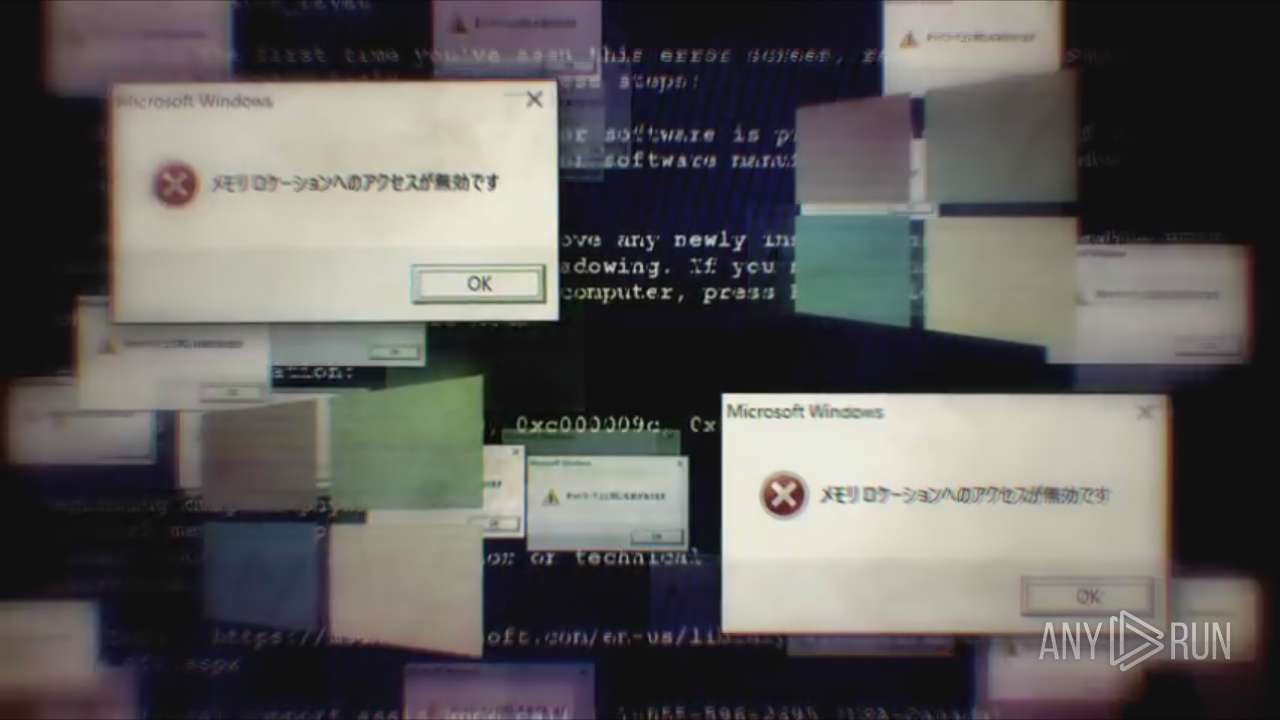
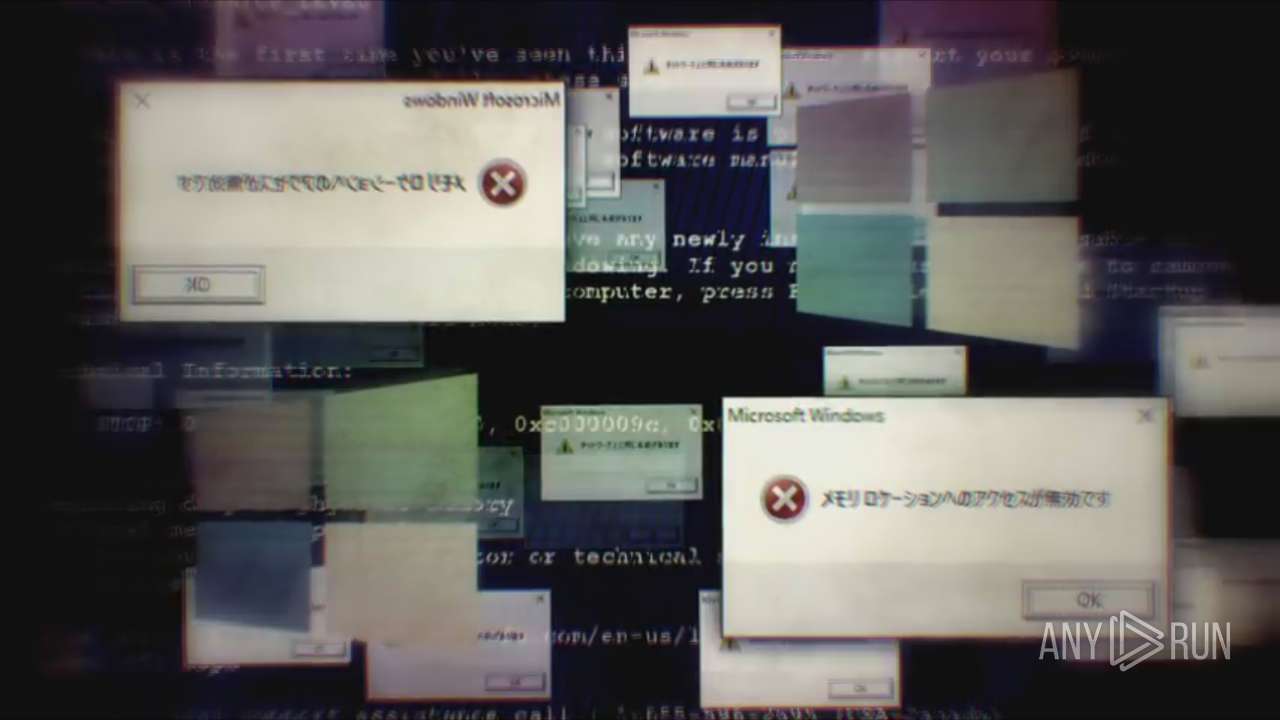
| Verdict: | Malicious activity |
| Analysis date: | April 27, 2023, 12:47:47 |
| OS: | Windows 11 Professional (build: 22000, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 6A4853CD0584DC90067E15AFB43C4962 |
| SHA1: | AE59BBB123E98DC8379D08887F83D7E52B1B47FC |
| SHA256: | CCB9502BF8BA5BECF8B758CA04A5625C30B79E2D10D2677CC43AE4253E1288EC |
| SSDEEP: | 98304:XyDt6K4MJVnjOobt/JN1LA5elHc+S4fRp5UvluKo:XyDtK8bbxn+IHcBEV/F |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads the Internet Settings
- Endermanch@ChilledWindows.exe (PID: 3760)
INFO
Reads the machine GUID from the registry
- Endermanch@ChilledWindows.exe (PID: 3760)
Reads the computer name
- Endermanch@ChilledWindows.exe (PID: 3760)
Checks supported languages
- Endermanch@ChilledWindows.exe (PID: 3760)
The process checks LSA protection
- Endermanch@ChilledWindows.exe (PID: 3760)
Checks proxy server information
- Endermanch@ChilledWindows.exe (PID: 3760)
Create files in a temporary directory
- Endermanch@ChilledWindows.exe (PID: 3760)
Creates files or folders in the user directory
- Endermanch@ChilledWindows.exe (PID: 3760)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (82.9) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (7.4) |
| .exe | | | Win32 Executable (generic) (5.1) |
| .exe | | | Generic Win/DOS Executable (2.2) |
| .exe | | | DOS Executable Generic (2.2) |
EXIF
EXE
| AssemblyVersion: | 1.0.0.0 |
|---|---|
| ProductVersion: | 1.0.0.0 |
| ProductName: | ChilledWindows |
| OriginalFileName: | ChilledWindows.exe |
| LegalTrademarks: | - |
| LegalCopyright: | Copyright © GAMELASTER 2016 |
| InternalName: | ChilledWindows.exe |
| FileVersion: | 1.0.0.0 |
| FileDescription: | ChilledWindows |
| CompanyName: | GAMELASTER |
| Comments: | - |
| CharacterSet: | Unicode |
| LanguageCode: | Neutral |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 1.0.0.0 |
| FileVersionNumber: | 1.0.0.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 4 |
| ImageVersion: | - |
| OSVersion: | 4 |
| EntryPoint: | 0x4340c6 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 177664 |
| CodeSize: | 4400128 |
| LinkerVersion: | 48 |
| PEType: | PE32 |
| ImageFileCharacteristics: | Executable, Large address aware |
| TimeStamp: | 2016:09:10 17:32:23+00:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 10-Sep-2016 17:32:23 |
| Debug artifacts: |
|
| Comments: | - |
| CompanyName: | GAMELASTER |
| FileDescription: | ChilledWindows |
| FileVersion: | 1.0.0.0 |
| InternalName: | ChilledWindows.exe |
| LegalCopyright: | Copyright © GAMELASTER 2016 |
| LegalTrademarks: | - |
| OriginalFilename: | ChilledWindows.exe |
| ProductName: | ChilledWindows |
| ProductVersion: | 1.0.0.0 |
| Assembly Version: | 1.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 10-Sep-2016 17:32:23 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x00432324 | 0x00432400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 7.95766 |
.rsrc | 0x00436000 | 0x0002B214 | 0x0002B400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.96489 |
.reloc | 0x00462000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.10191 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.00112 | 490 | UNKNOWN | UNKNOWN | RT_MANIFEST |
2 | 4.63399 | 67624 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 4.93809 | 21640 | UNKNOWN | UNKNOWN | RT_ICON |
4 | 4.9209 | 16936 | UNKNOWN | UNKNOWN | RT_ICON |
5 | 5.15216 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
6 | 5.33886 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
7 | 5.5223 | 2440 | UNKNOWN | UNKNOWN | RT_ICON |
8 | 5.55064 | 1128 | UNKNOWN | UNKNOWN | RT_ICON |
32512 | 2.97961 | 118 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
mscoree.dll |
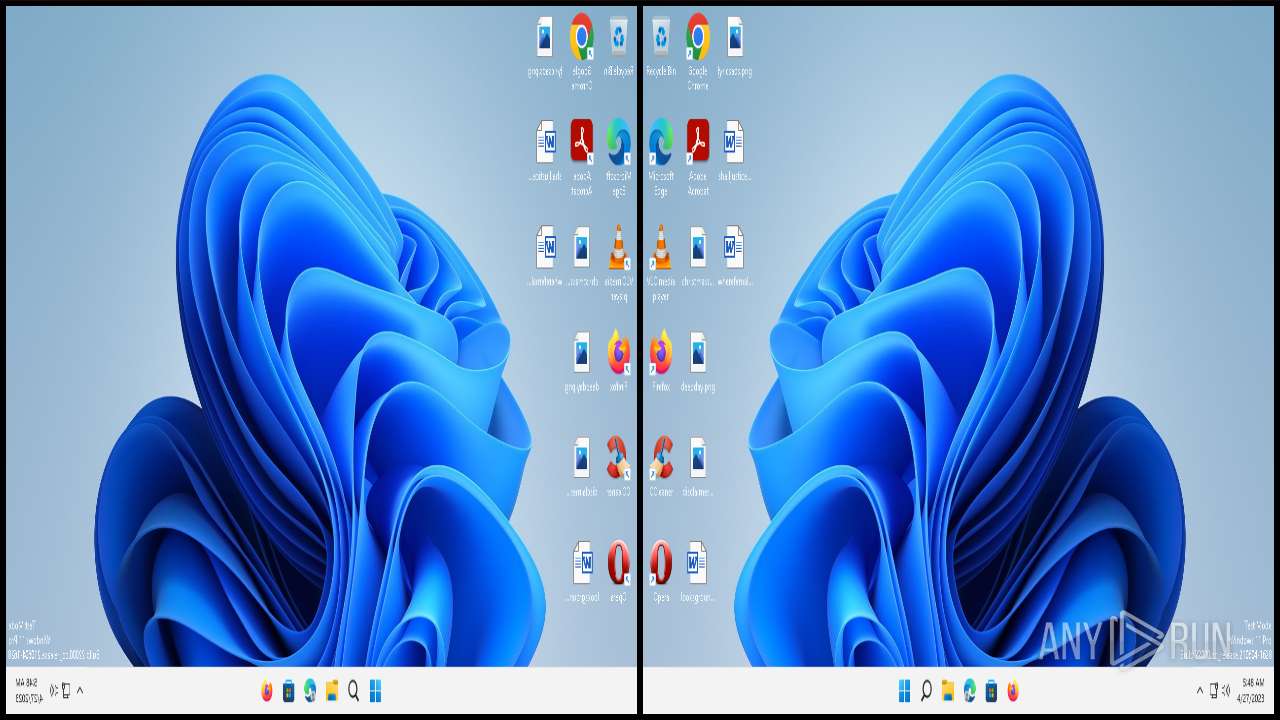
Total processes
126
Monitored processes
1
Malicious processes
1
Suspicious processes
0
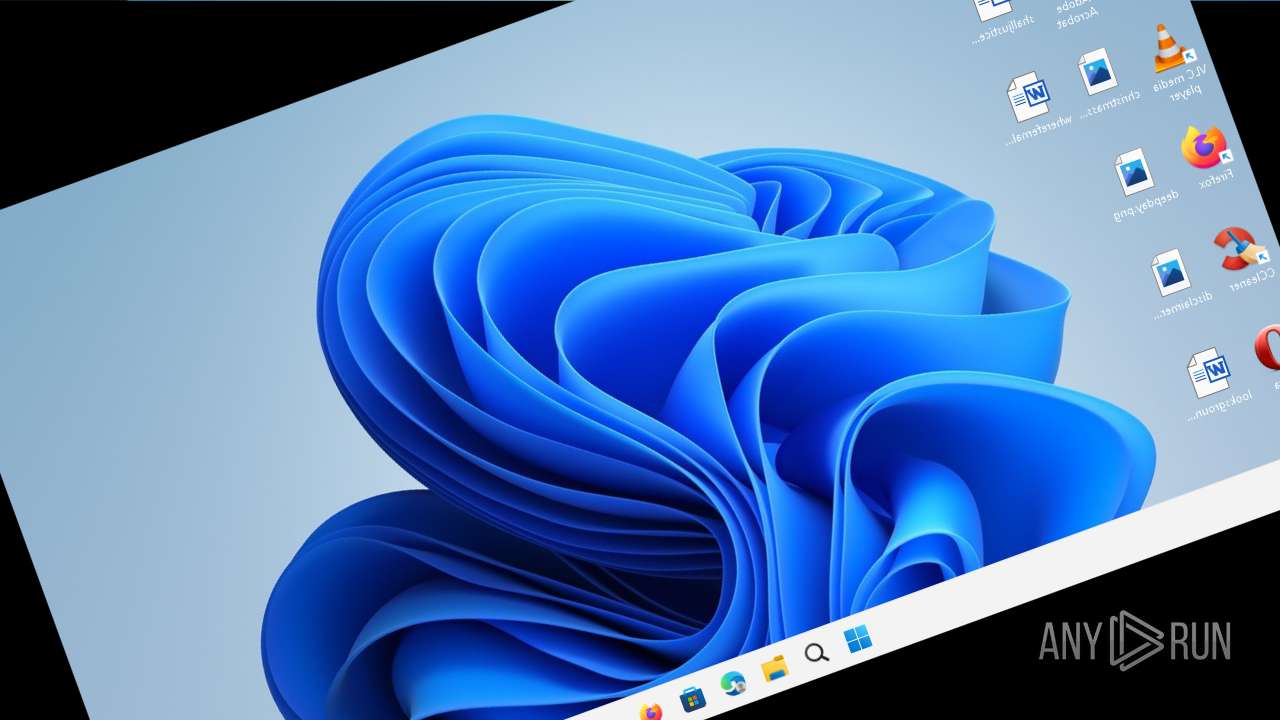
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3760 | "C:\Users\admin\AppData\Local\Temp\Endermanch@ChilledWindows.exe" | C:\Users\admin\AppData\Local\Temp\Endermanch@ChilledWindows.exe | — | explorer.exe | |||||||||||
User: admin Company: GAMELASTER Integrity Level: MEDIUM Description: ChilledWindows Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
5 200
Read events
5 120
Write events
76
Delete events
4
Modification events
| (PID) Process: | (3760) Endermanch@ChilledWindows.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\MediaPlayer\Player\Settings |
| Operation: | delete value | Name: | Client ID |
Value: {CC5EFE1D-FE39-40E9-B76C-5933DFF4D93D} | |||
| (PID) Process: | (3760) Endermanch@ChilledWindows.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3760) Endermanch@ChilledWindows.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3760) Endermanch@ChilledWindows.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3760) Endermanch@ChilledWindows.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3760) Endermanch@ChilledWindows.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\MediaPlayer\Preferences |
| Operation: | write | Name: | MediaLibraryCreateNewDatabase |
Value: 1 | |||
| (PID) Process: | (3760) Endermanch@ChilledWindows.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\MediaPlayer\Preferences |
| Operation: | write | Name: | MLSChangeIndexList |
Value: 0 | |||
| (PID) Process: | (3760) Endermanch@ChilledWindows.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\MediaPlayer\Preferences |
| Operation: | write | Name: | MLSChangeIndexList |
Value: 1 | |||
| (PID) Process: | (3760) Endermanch@ChilledWindows.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\MediaPlayer\Preferences |
| Operation: | write | Name: | MLSChangeIndexList |
Value: 2 | |||
| (PID) Process: | (3760) Endermanch@ChilledWindows.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\MediaPlayer\Preferences |
| Operation: | write | Name: | MLSChangeIndexList |
Value: 3 | |||
Executable files
0
Suspicious files
6
Text files
10
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3760 | Endermanch@ChilledWindows.exe | C:\Users\admin\AppData\Local\Microsoft\Windows Media\12.0\WMSDKNS.DTD | xml | |
MD5:90BE2701C8112BEBC6BD58A7DE19846E | SHA256:644FBCDC20086E16D57F31C5BAD98BE68D02B1C061938D2F5F91CBE88C871FBF | |||
| 3760 | Endermanch@ChilledWindows.exe | C:\Users\admin\AppData\Local\Microsoft\Media Player\CurrentDatabase_400.wmdb | binary | |
MD5:76DDD4D368E11ED3DF0C58A44264E159 | SHA256:6B98EF4D74FE075A763A275F38A6ACC4FBF3263502830A8FAEFB4BA36895A40D | |||
| 3760 | Endermanch@ChilledWindows.exe | C:\Users\admin\AppData\Local\Microsoft\Windows Media\12.0\WMSDKNS.XML.bak | text | |
MD5:7050D5AE8ACFBE560FA11073FEF8185D | SHA256:CB87767C4A384C24E4A0F88455F59101B1AE7B4FB8DE8A5ADB4136C5F7EE545B | |||
| 3760 | Endermanch@ChilledWindows.exe | C:\Users\admin\AppData\Local\Microsoft\Windows Media\12.0\WMSDKNSD.XML | text | |
MD5:A9B5DA9AEC61657B32393D96217165F0 | SHA256:9F4611369CF65B33D886489B2486FCA7B1E83E0DC998D35B15B3AA4C8478A28D | |||
| 3760 | Endermanch@ChilledWindows.exe | C:\Users\admin\AppData\Local\Microsoft\Windows Media\12.0\WMSDKNS.XML | text | |
MD5:5433EAB10C6B5C6D55B7CBD302426A39 | SHA256:23DBF7014E99E93AF5F2760F18EE1370274F06A453145C8D539B66D798DAD131 | |||
| 3760 | Endermanch@ChilledWindows.exe | C:\Users\admin\AppData\Local\Microsoft\CLR_v4.0\UsageLogs\Endermanch@ChilledWindows.exe.log | text | |
MD5:17D526F688147F1B4B8F8979D08D67F4 | SHA256:9E283734B566C2609701BF7820B0C649CF6548F5F36C2A38E8B95196B33F3ECA | |||
| 3760 | Endermanch@ChilledWindows.exe | C:\Users\admin\AppData\Local\Microsoft\Media Player\LocalMLS_3.wmdb | binary | |
MD5:6F3834289B14F549BC538197971CE4A1 | SHA256:F683491DF8D7DD3A8CE583F42263780AA08F9DE24F70ED7E97C62C88BFA540B0 | |||
| 3760 | Endermanch@ChilledWindows.exe | C:\Users\admin\AppData\Local\Temp\chilledwindows.mp4 | binary | |
MD5:698DDCAEC1EDCF1245807627884EDF9C | SHA256:CDE975F975D21EDB2E5FAA505205AB8A2C5A565BA1FF8585D1F0E372B2A1D78B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
11
DNS requests
9
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1480 | svchost.exe | GET | 200 | 13.107.4.52:80 | http://www.msftconnecttest.com/connecttest.txt | US | text | 22 b | whitelisted |
6316 | svchost.exe | GET | 304 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?768cd3bb4549d192 | US | — | — | whitelisted |
6316 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5596 | svchost.exe | 2.19.229.151:443 | fs.microsoft.com | AKAMAI-AS | FR | suspicious |
1480 | svchost.exe | 13.107.4.52:80 | www.msftconnecttest.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6316 | svchost.exe | 40.126.31.67:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6316 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
6316 | svchost.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | EDGECAST | GB | whitelisted |
— | — | 40.126.31.67:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4536 | msedge.exe | 204.79.197.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
fs.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
www.msftconnecttest.com |
| whitelisted |
time.windows.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1480 | svchost.exe | Misc activity | ET INFO Microsoft Connection Test |