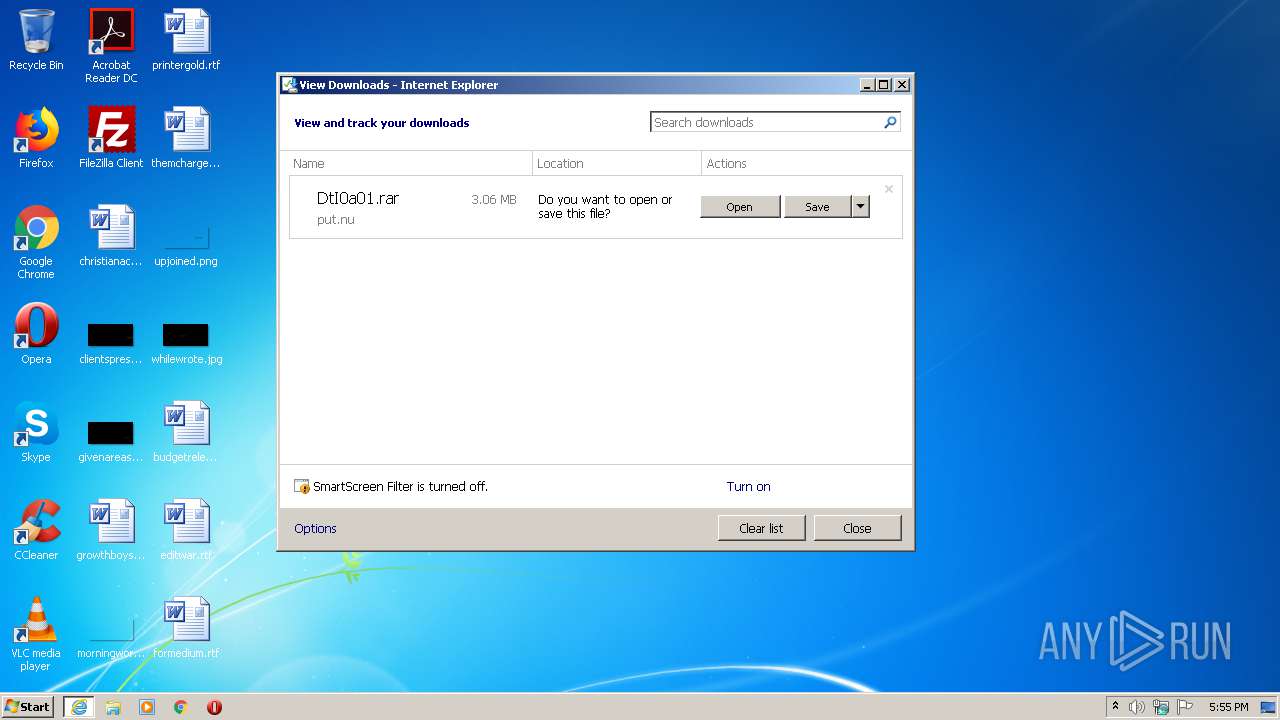
| URL: | http://put.nu/files/DtI0a01.rar |
| Full analysis: | https://app.any.run/tasks/2f4422dd-0f53-4025-a073-e4068ce39d5e |
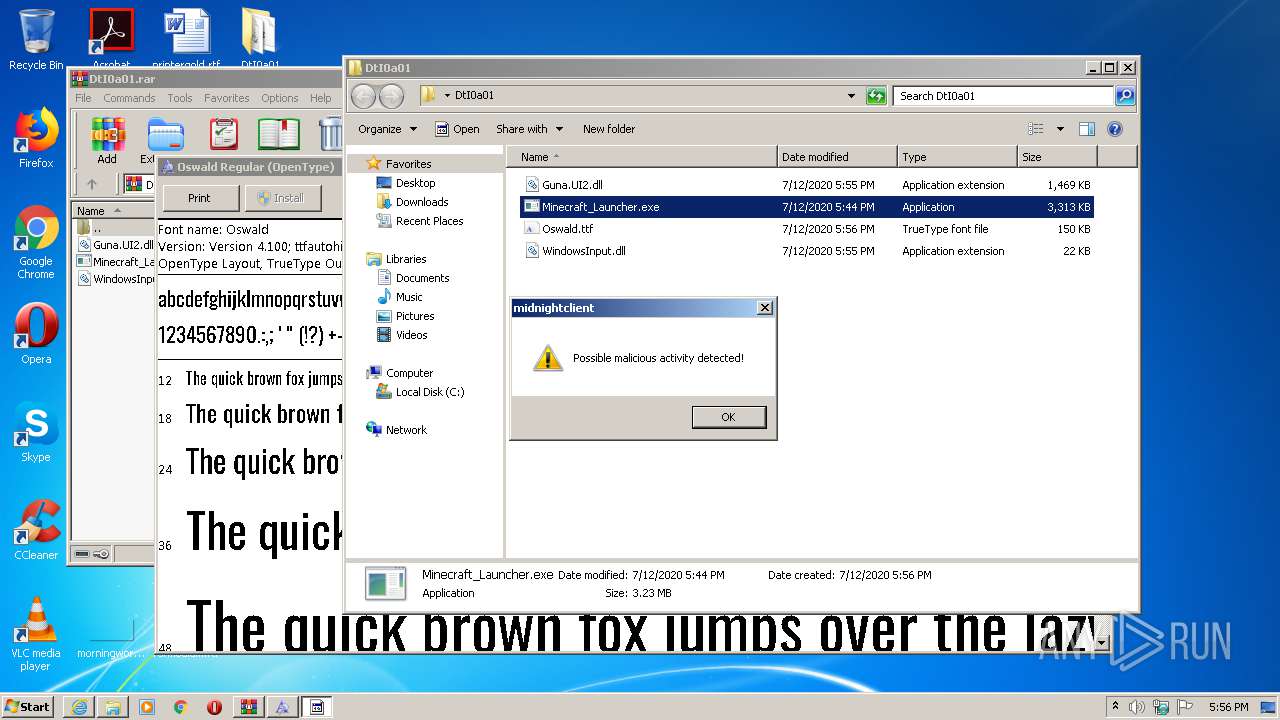
| Verdict: | Malicious activity |
| Analysis date: | July 12, 2020, 16:55:34 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 3C39D600F984792A1C9197B6A96928FA |
| SHA1: | 14EC785B556D3A17A52EFA8E47053AD9FD2F50DA |
| SHA256: | CCAAD1D75B234E6A4F31C729A1B0314194626CC21FB910EE072BACC9FA5FC474 |
| SSDEEP: | 3:N1KOQRDzHsQX:COuDsQX |
MALICIOUS
Application was dropped or rewritten from another process
- Minecraft_Launcher.exe (PID: 1752)
- Minecraft_Launcher.exe (PID: 1568)
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 532)
- Minecraft_Launcher.exe (PID: 1752)
SUSPICIOUS
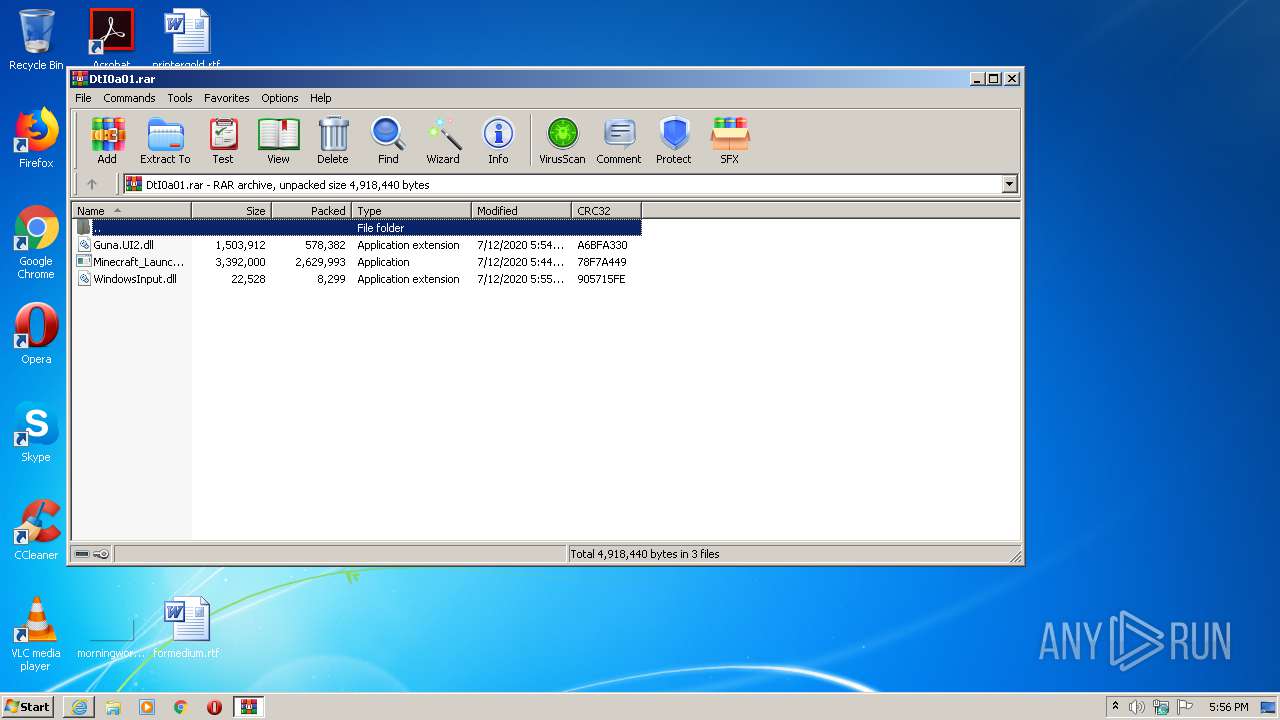
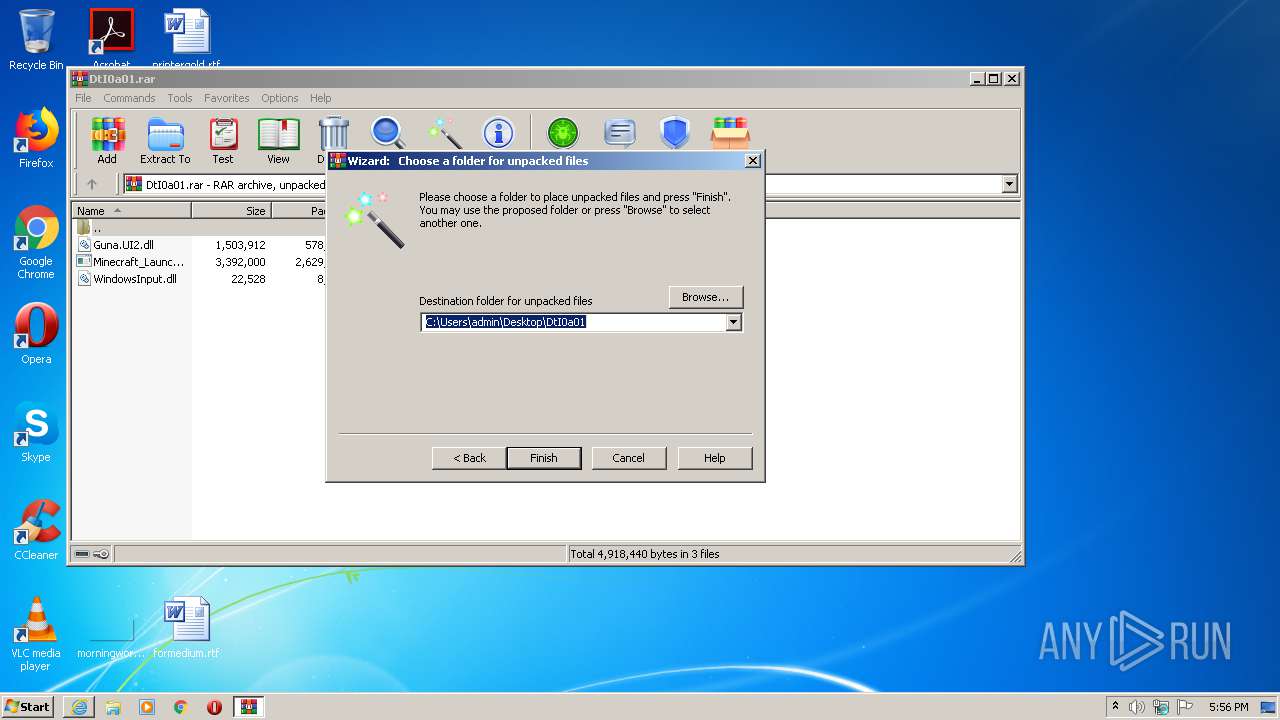
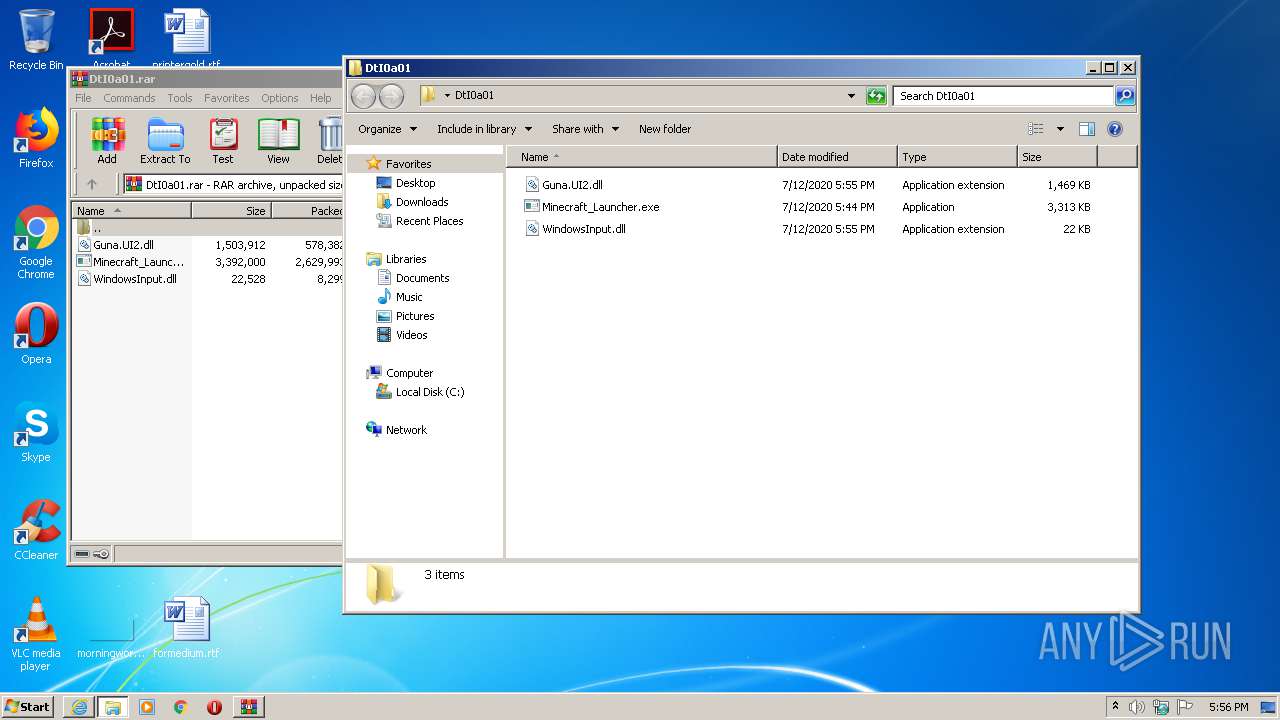
Executable content was dropped or overwritten
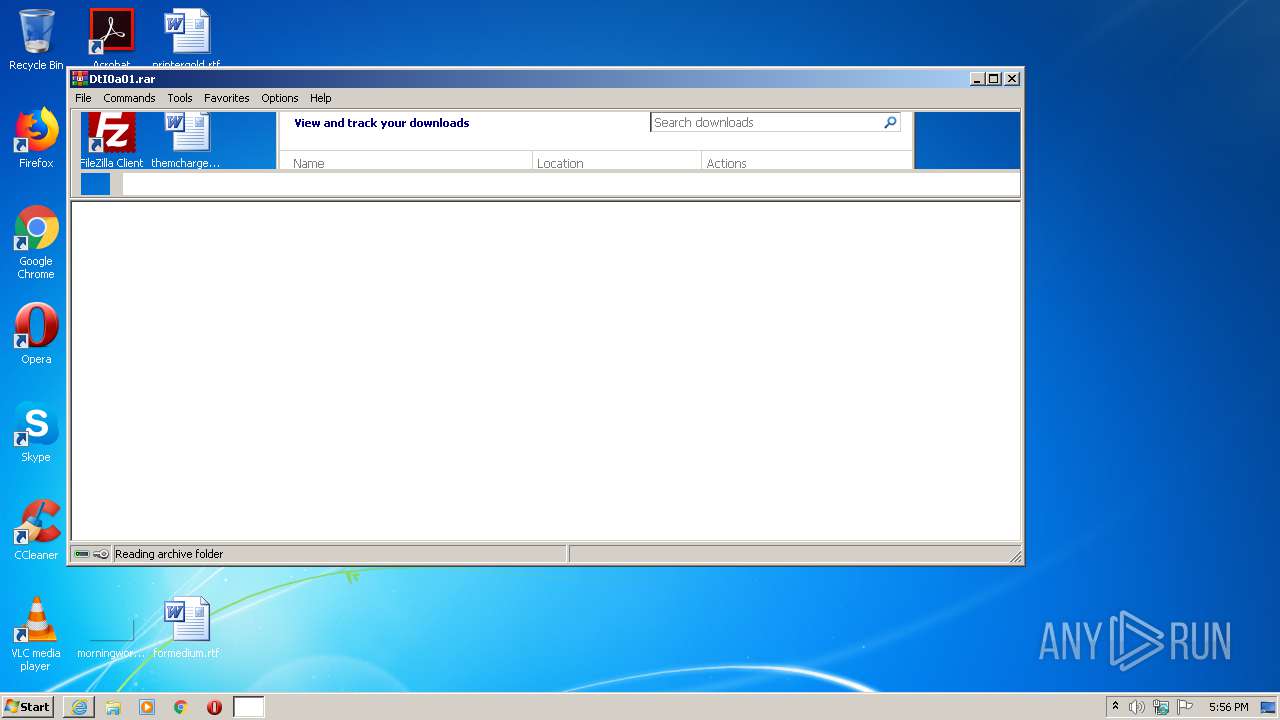
- WinRAR.exe (PID: 1088)
Executed via COM
- DllHost.exe (PID: 3912)
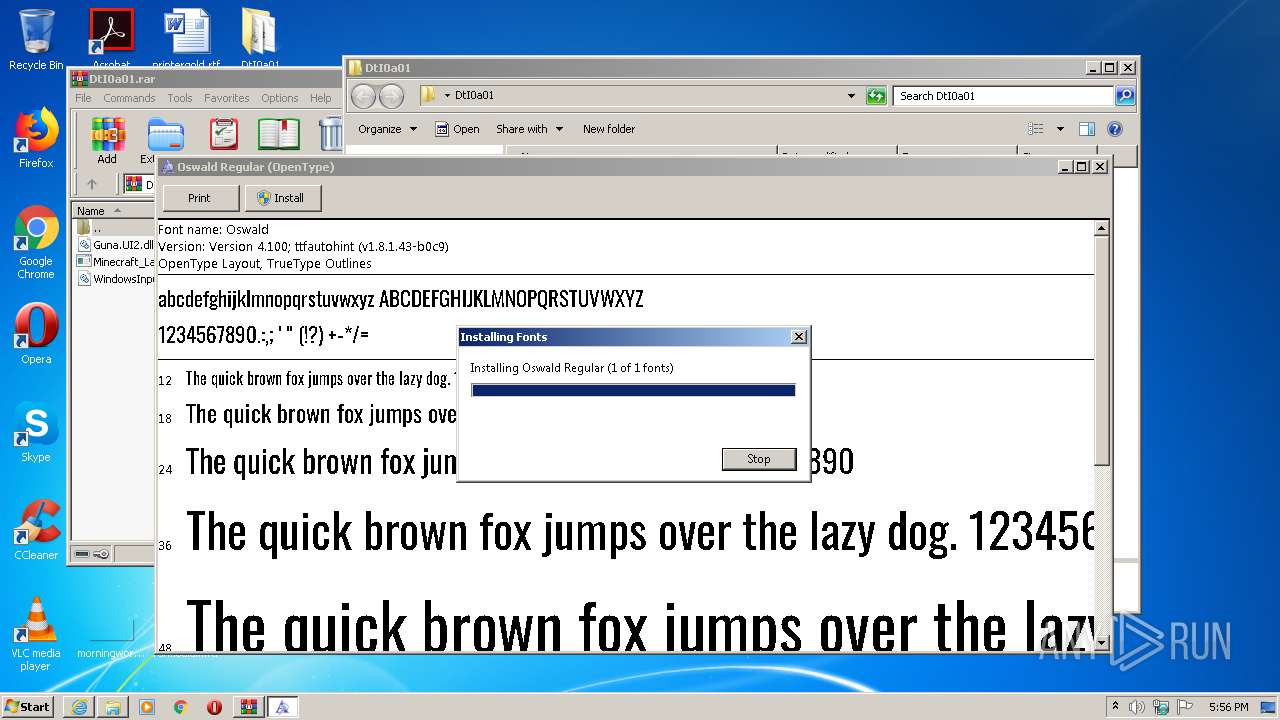
Creates files in the Windows directory
- DllHost.exe (PID: 3912)
INFO
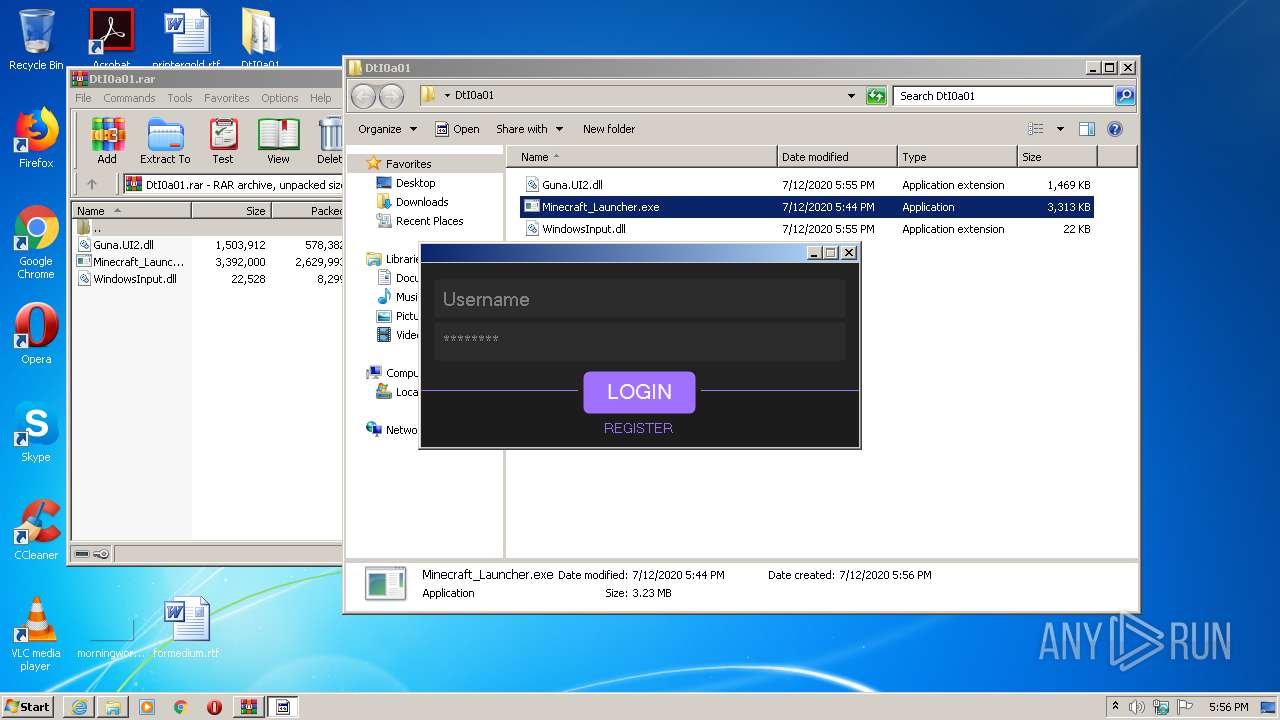
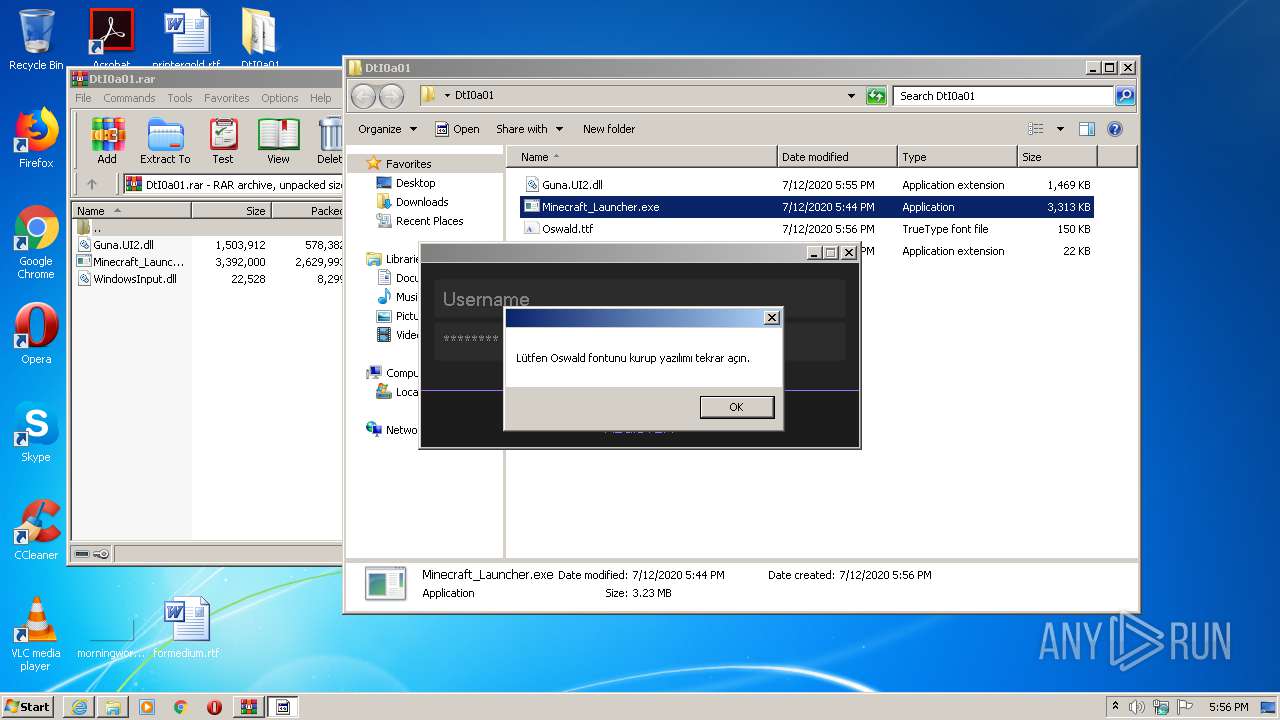
Manual execution by user
- Minecraft_Launcher.exe (PID: 1752)
- Minecraft_Launcher.exe (PID: 1568)
Application launched itself
- iexplore.exe (PID: 632)
Modifies the phishing filter of IE
- iexplore.exe (PID: 632)
Reads Internet Cache Settings
- iexplore.exe (PID: 632)
- iexplore.exe (PID: 1888)
Changes internet zones settings
- iexplore.exe (PID: 632)
Reads the hosts file
- Minecraft_Launcher.exe (PID: 1752)
- Minecraft_Launcher.exe (PID: 1568)
Reads settings of System Certificates
- iexplore.exe (PID: 632)
Changes settings of System certificates
- iexplore.exe (PID: 632)
Adds / modifies Windows certificates
- iexplore.exe (PID: 632)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
58
Monitored processes
16
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 532 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe2_ Global\UsGthrCtrlFltPipeMssGthrPipe2 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 604 | "C:\Windows\System32\arp.exe" -a | C:\Windows\System32\arp.exe | — | Minecraft_Launcher.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Arp Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 632 | "C:\Program Files\Internet Explorer\iexplore.exe" http://put.nu/files/DtI0a01.rar | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 912 | "C:\Windows\System32\arp.exe" -a | C:\Windows\System32\arp.exe | — | Minecraft_Launcher.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Arp Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 952 | "C:\Windows\System32\arp.exe" -a | C:\Windows\System32\arp.exe | — | Minecraft_Launcher.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Arp Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
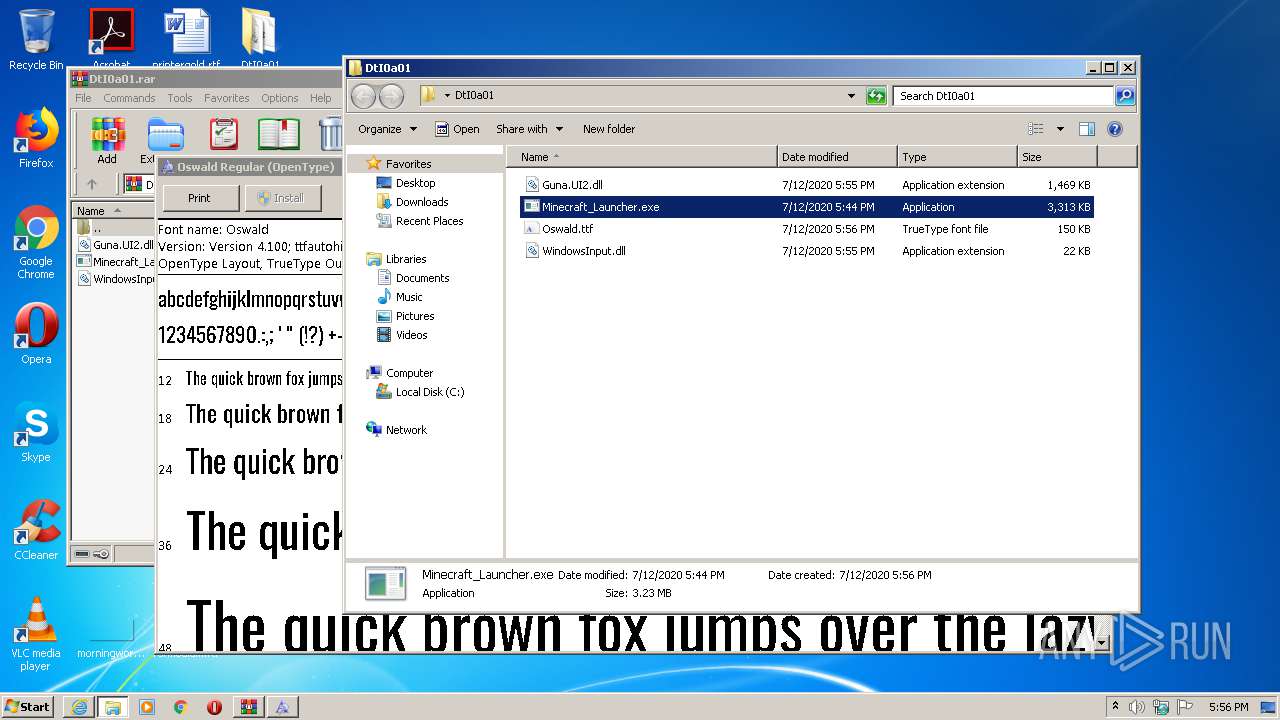
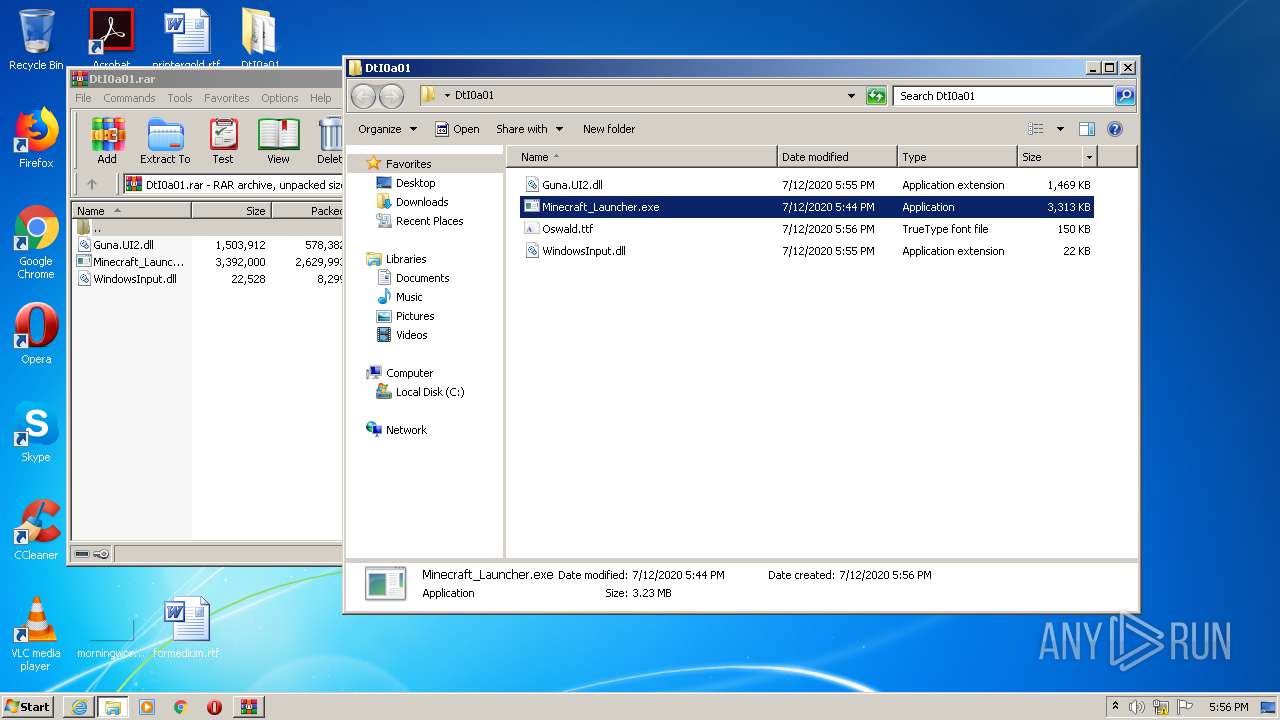
| 1088 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\DtI0a01.rar" | C:\Program Files\WinRAR\WinRAR.exe | iexplore.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
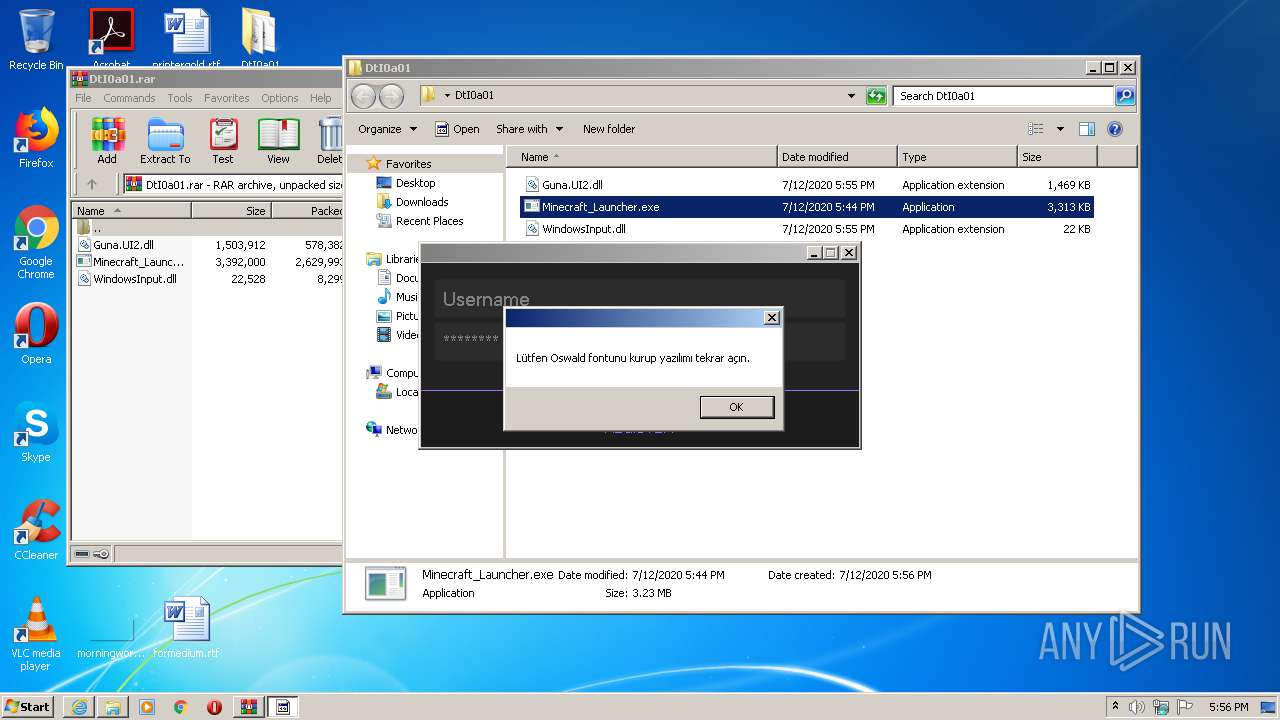
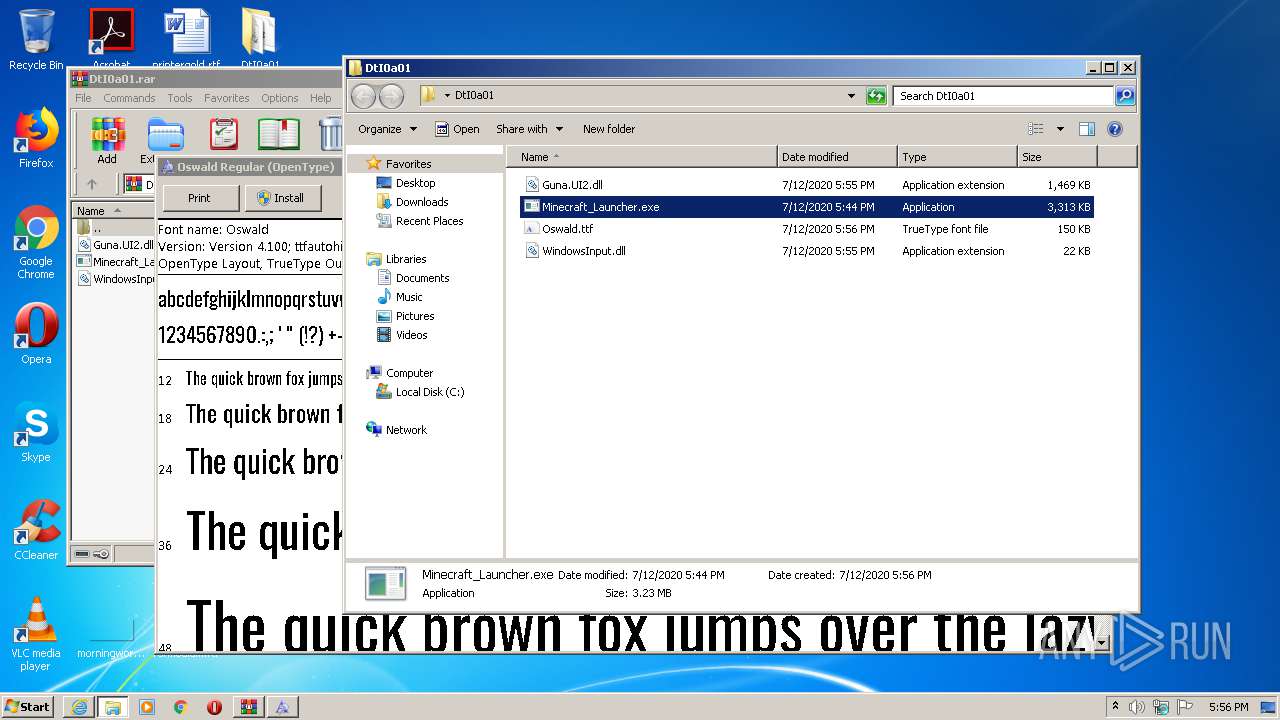
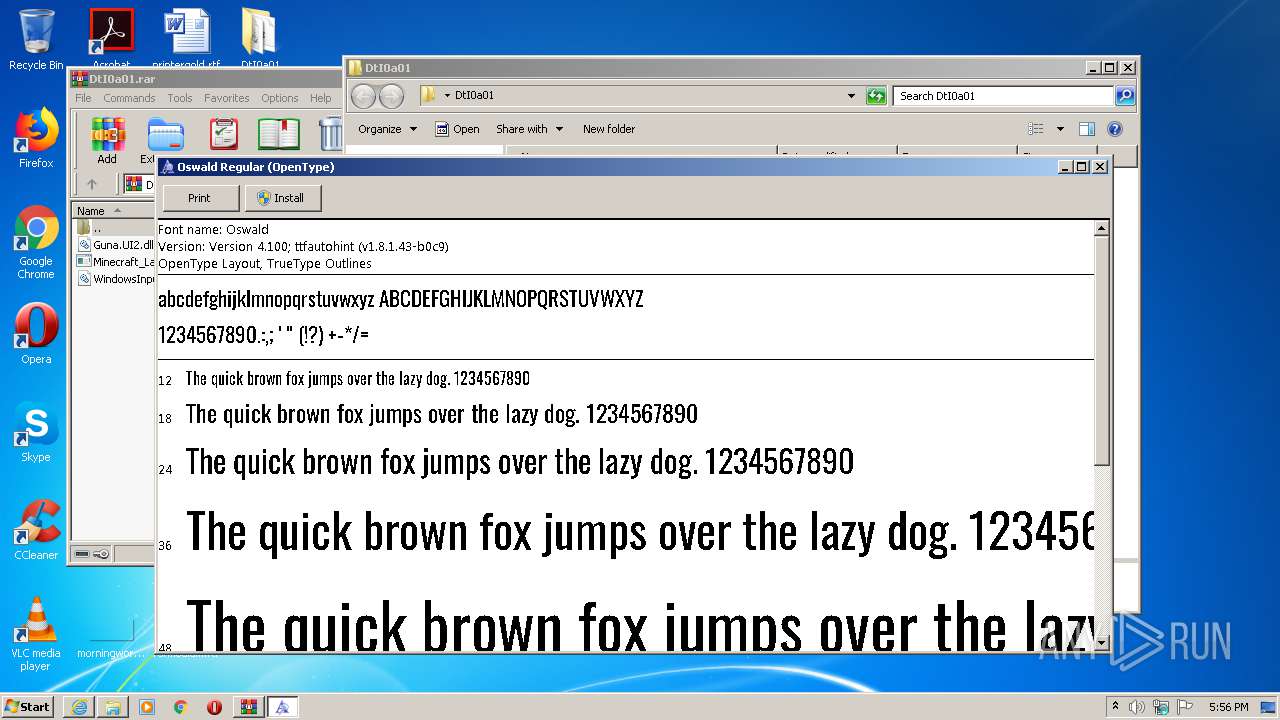
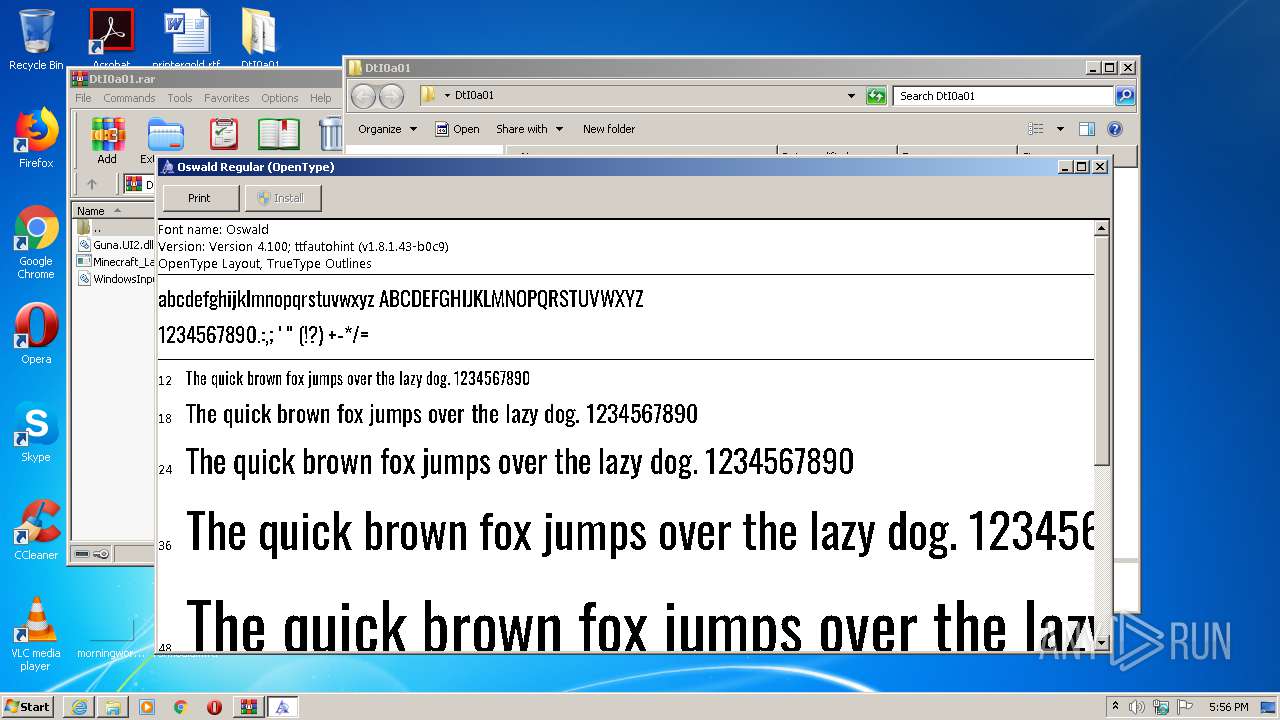
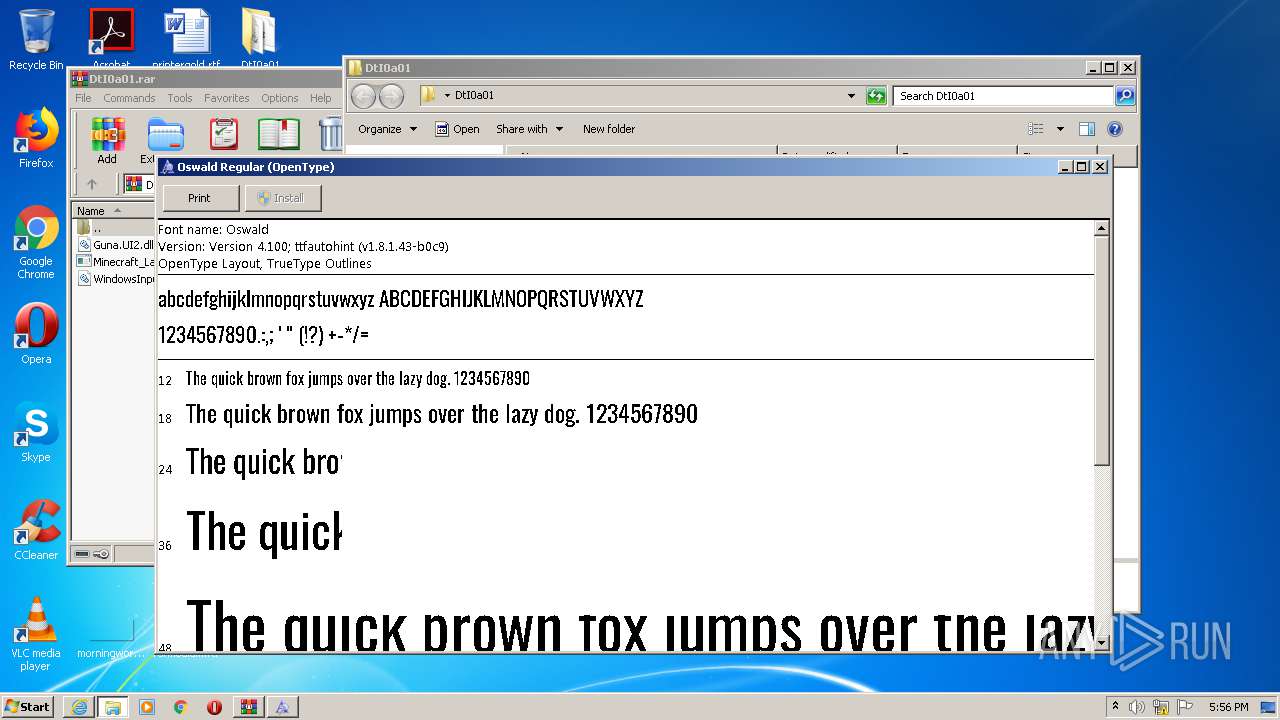
| 1488 | "C:\Windows\System32\fontview.exe" C:\Users\admin\Desktop\DtI0a01\Oswald.ttf | C:\Windows\System32\fontview.exe | — | Minecraft_Launcher.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Font Viewer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
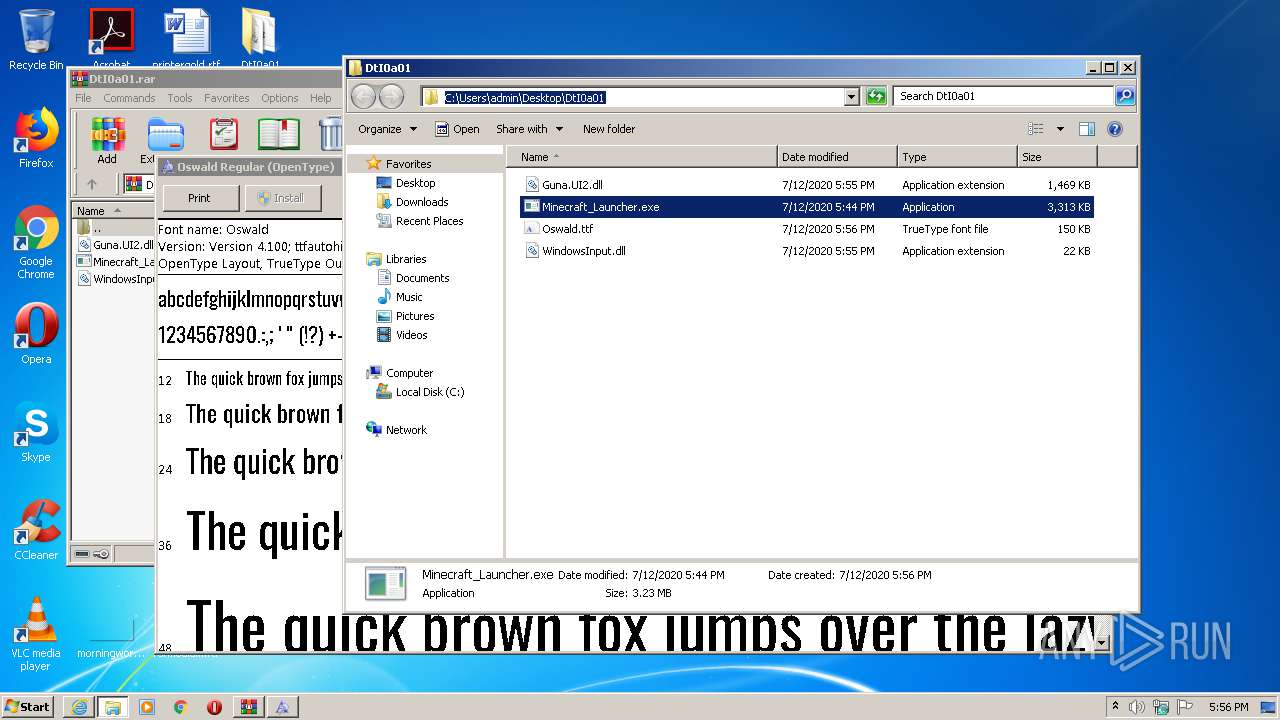
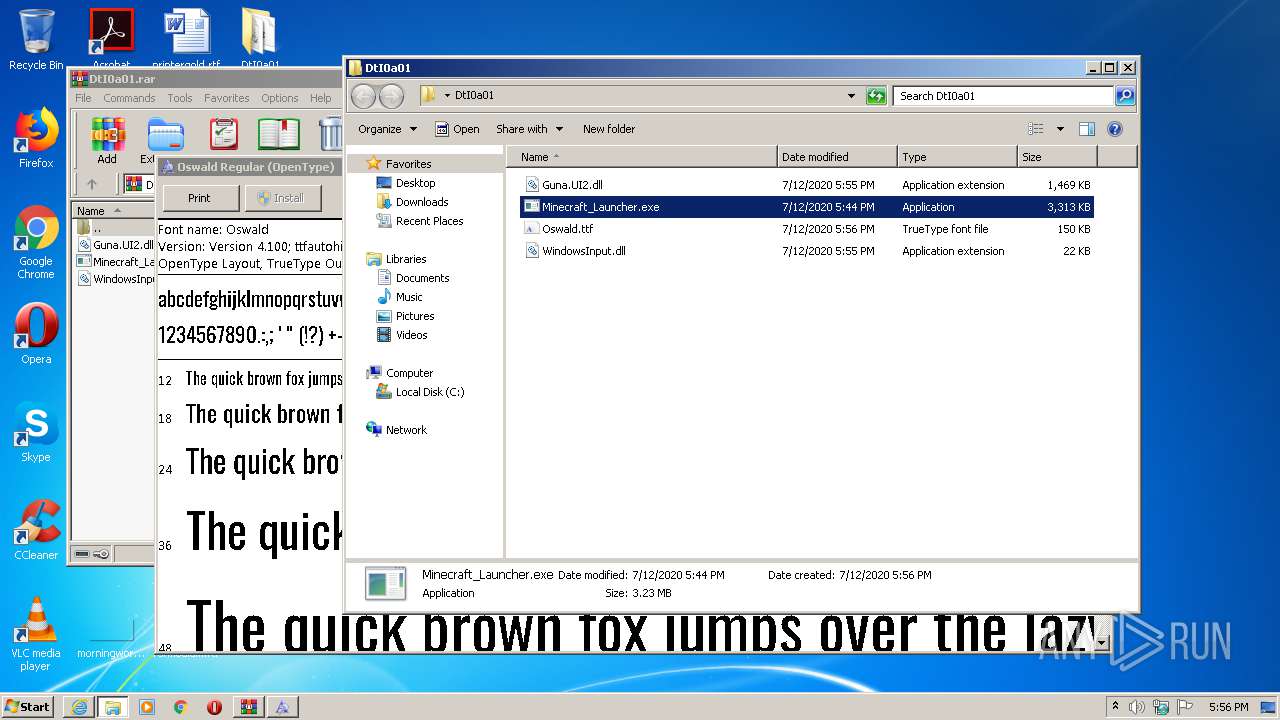
| 1568 | "C:\Users\admin\Desktop\DtI0a01\Minecraft_Launcher.exe" | C:\Users\admin\Desktop\DtI0a01\Minecraft_Launcher.exe | explorer.exe | ||||||||||||
User: admin Company: Mojang Integrity Level: MEDIUM Description: Minecraft Launcher Exit code: 4294967295 Version: 0.0.0.0 Modules
| |||||||||||||||
| 1588 | "C:\Windows\System32\arp.exe" -a | C:\Windows\System32\arp.exe | — | Minecraft_Launcher.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Arp Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1752 | "C:\Users\admin\Desktop\DtI0a01\Minecraft_Launcher.exe" | C:\Users\admin\Desktop\DtI0a01\Minecraft_Launcher.exe | explorer.exe | ||||||||||||
User: admin Company: Mojang Integrity Level: MEDIUM Description: Minecraft Launcher Exit code: 0 Version: 0.0.0.0 Modules
| |||||||||||||||
Total events
9 294
Read events
2 498
Write events
4 553
Delete events
2 243
Modification events
| (PID) Process: | (1888) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\LowCache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1888) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\LowCache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1888) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\LowCache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (632) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 1561782128 | |||
| (PID) Process: | (632) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30824557 | |||
| (PID) Process: | (632) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (632) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (632) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (632) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (632) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
Executable files
3
Suspicious files
11
Text files
2
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 632 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF385AB9CC75768B8F.TMP | — | |
MD5:— | SHA256:— | |||
| 632 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\DtI0a01.rar.db1w1g5.partial:Zone.Identifier | — | |
MD5:— | SHA256:— | |||
| 632 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Cab9E7F.tmp | — | |
MD5:— | SHA256:— | |||
| 632 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Tar9E80.tmp | — | |
MD5:— | SHA256:— | |||
| 632 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\VersionManager\ver9EC0.tmp | — | |
MD5:— | SHA256:— | |||
| 1888 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\DtI0a01.rar.db1w1g5.partial | compressed | |
MD5:— | SHA256:— | |||
| 632 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\DtI0a01.rar | compressed | |
MD5:— | SHA256:— | |||
| 632 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{88D5E48B-C460-11EA-B03F-5254004A04AF}.dat | binary | |
MD5:— | SHA256:— | |||
| 1888 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\DtI0a01[1].rar | compressed | |
MD5:— | SHA256:— | |||
| 632 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\DtI0a01.rar:Zone.Identifier | text | |
MD5:FBCCF14D504B7B2DBCB5A5BDA75BD93B | SHA256:EACD09517CE90D34BA562171D15AC40D302F0E691B439F91BE1B6406E25F5913 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
11
DNS requests
8
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1888 | iexplore.exe | GET | 200 | 52.70.201.25:80 | http://put.nu/files/DtI0a01.rar | US | compressed | 3.07 Mb | suspicious |
632 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
632 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
632 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1888 | iexplore.exe | 52.70.201.25:80 | put.nu | Amazon.com, Inc. | US | suspicious |
— | — | 52.70.201.25:80 | put.nu | Amazon.com, Inc. | US | suspicious |
1752 | Minecraft_Launcher.exe | 104.24.111.151:443 | api.auth.gg | Cloudflare Inc | US | shared |
632 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1752 | Minecraft_Launcher.exe | 162.159.133.233:443 | cdn.discordapp.com | Cloudflare Inc | — | shared |
632 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1568 | Minecraft_Launcher.exe | 104.24.111.151:443 | api.auth.gg | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
put.nu |
| suspicious |
api.auth.gg |
| whitelisted |
cdn.discordapp.com |
| shared |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |