| File name: | buhsrv1.rdp |
| Full analysis: | https://app.any.run/tasks/4f6f5b86-d856-43e4-a772-f7a86d83f359 |
| Verdict: | Malicious activity |
| Analysis date: | April 04, 2025, 05:06:38 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/plain |
| File info: | Unicode text, UTF-16, little-endian text, with very long lines (5074), with CRLF line terminators |
| MD5: | 95E6FD77AD7A0BFC8C3D1F3D2FD8A283 |
| SHA1: | 2418177DC2D64A85C99C93FAF9DF3D819E8DF153 |
| SHA256: | CCA25DB9EF9D7108AAD35BE9E394B268A561A78DD9B789E658000CDCAB271B4F |
| SSDEEP: | 192:Z0FMWRw31vLguo4rWl873jCIHFE1tGLl6nsCtF7F08oFC3ZAWLZ+65YxhHV:zWR4Uuo43mIlE3UcztpNoI3ZA2Wl |
MALICIOUS
No malicious indicators.SUSPICIOUS
There is functionality for taking screenshot (YARA)
- vlc.exe (PID: 300)
Potential Corporate Privacy Violation
- mstsc.exe (PID: 680)
Reads the history of recent RDP connections
- mstsc.exe (PID: 680)
- mstsc.exe (PID: 6576)
INFO
Checks supported languages
- vlc.exe (PID: 300)
Reads the software policy settings
- mstsc.exe (PID: 680)
- mstsc.exe (PID: 6576)
Reads the computer name
- vlc.exe (PID: 300)
The process uses Lua
- vlc.exe (PID: 300)
Manual execution by a user
- mstsc.exe (PID: 6576)
- mstsc.exe (PID: 680)
Reads security settings of Internet Explorer
- mstsc.exe (PID: 6576)
- mstsc.exe (PID: 680)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
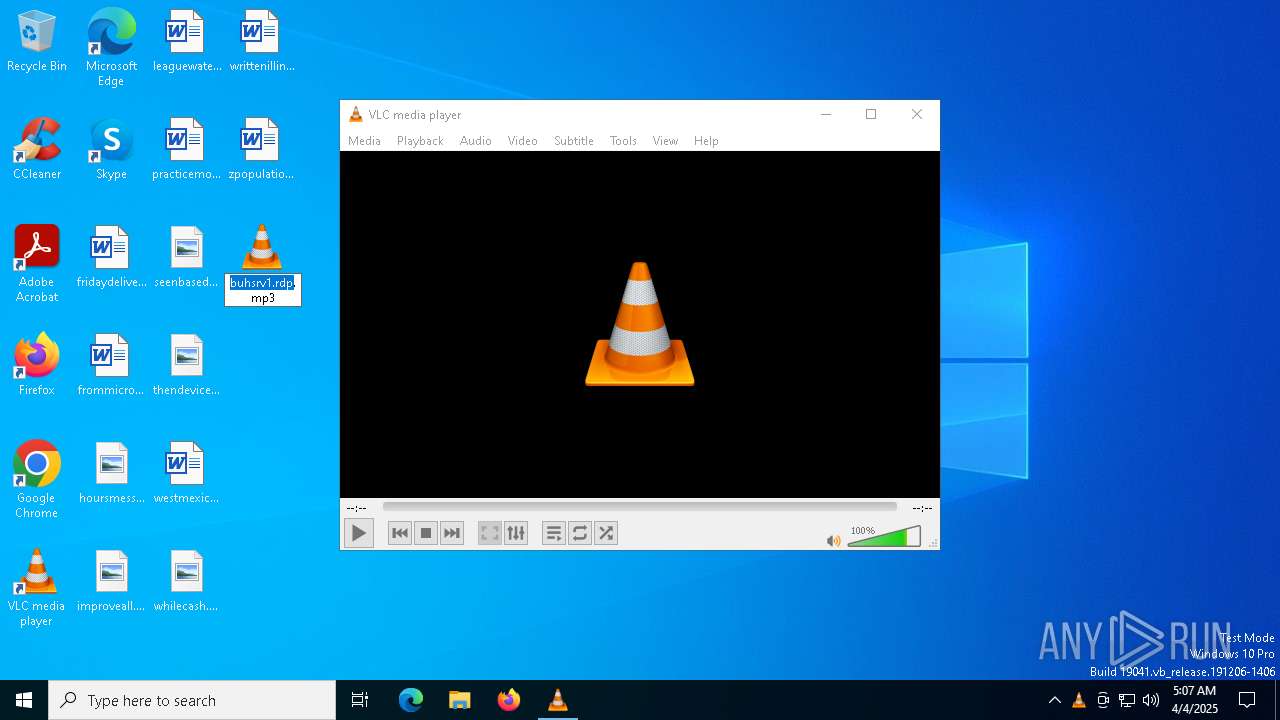
TRiD
| .rdp | | | Remote Desktop Connection Settings (Unicode) (99.1) |
|---|---|---|
| .txt | | | Text - UTF-16 (LE) encoded (0.5) |
| .mp3 | | | MP3 audio (0.2) |
Total processes
131
Monitored processes
5
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
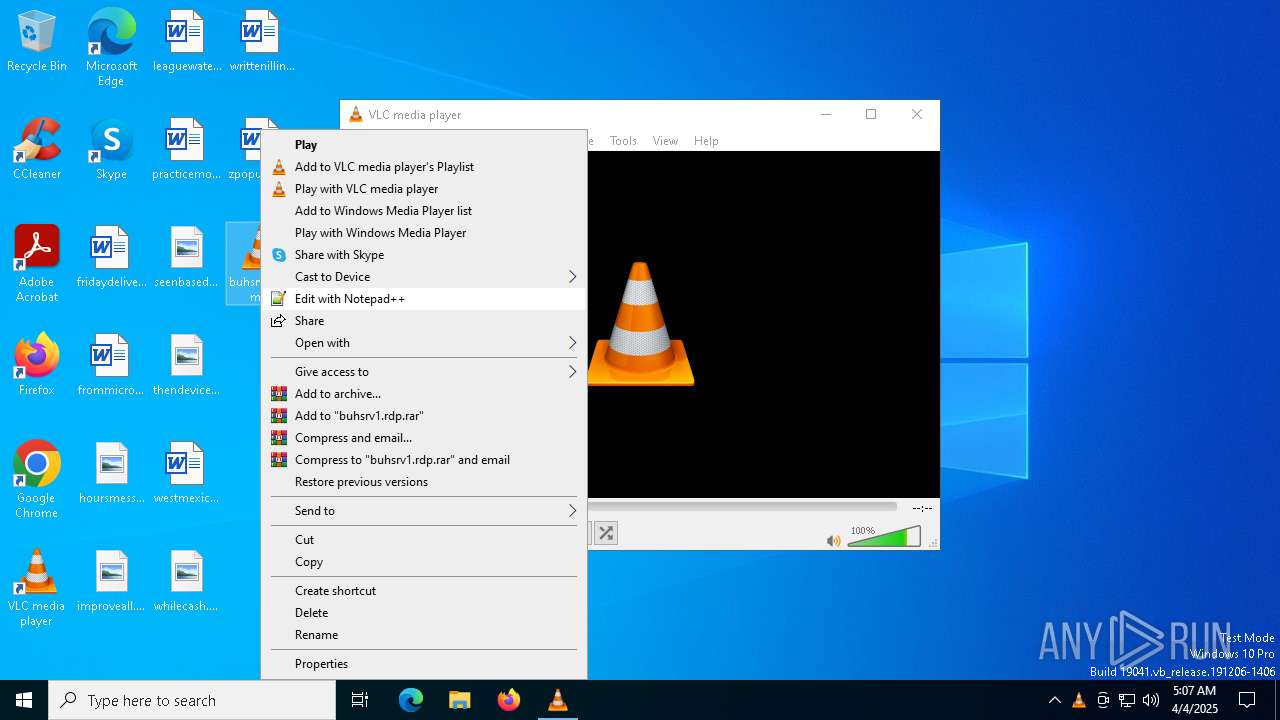
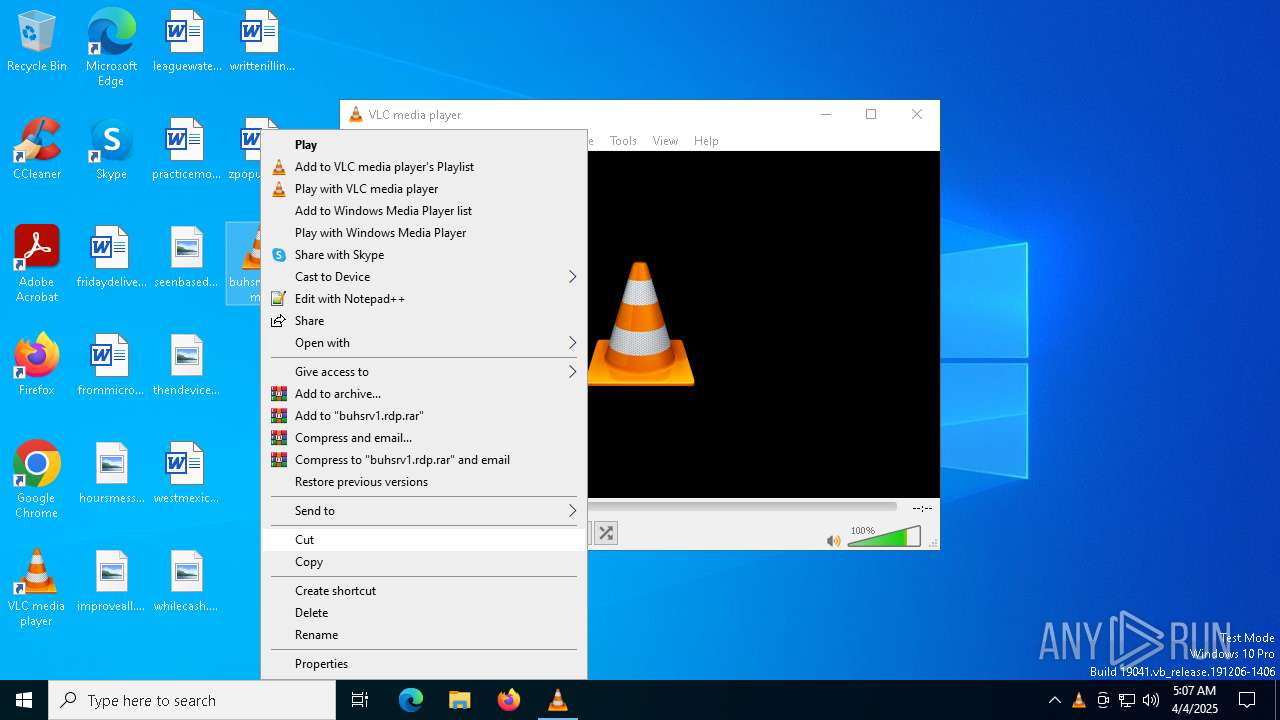
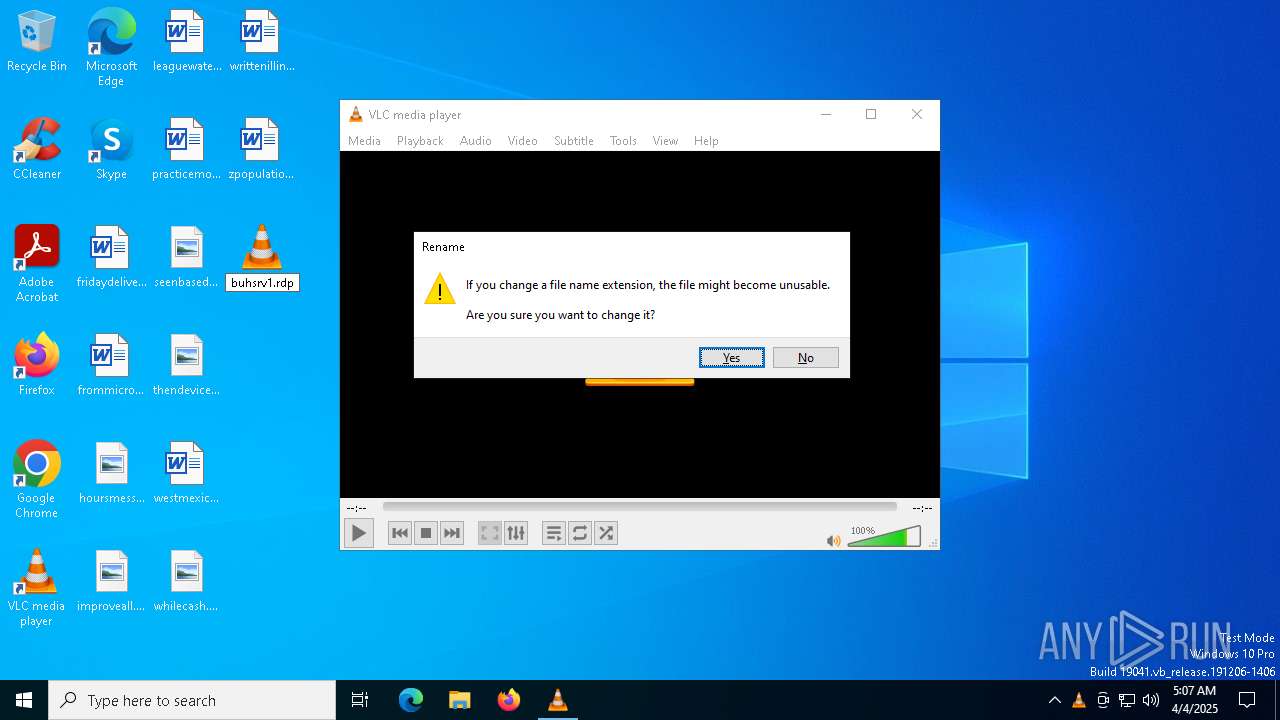
| 300 | "C:\Program Files\VideoLAN\VLC\vlc.exe" --started-from-file C:\Users\admin\Desktop\buhsrv1.rdp.mp3 | C:\Program Files\VideoLAN\VLC\vlc.exe | — | explorer.exe | |||||||||||
User: admin Company: VideoLAN Integrity Level: MEDIUM Description: VLC media player Exit code: 0 Version: 3.0.11 Modules
| |||||||||||||||
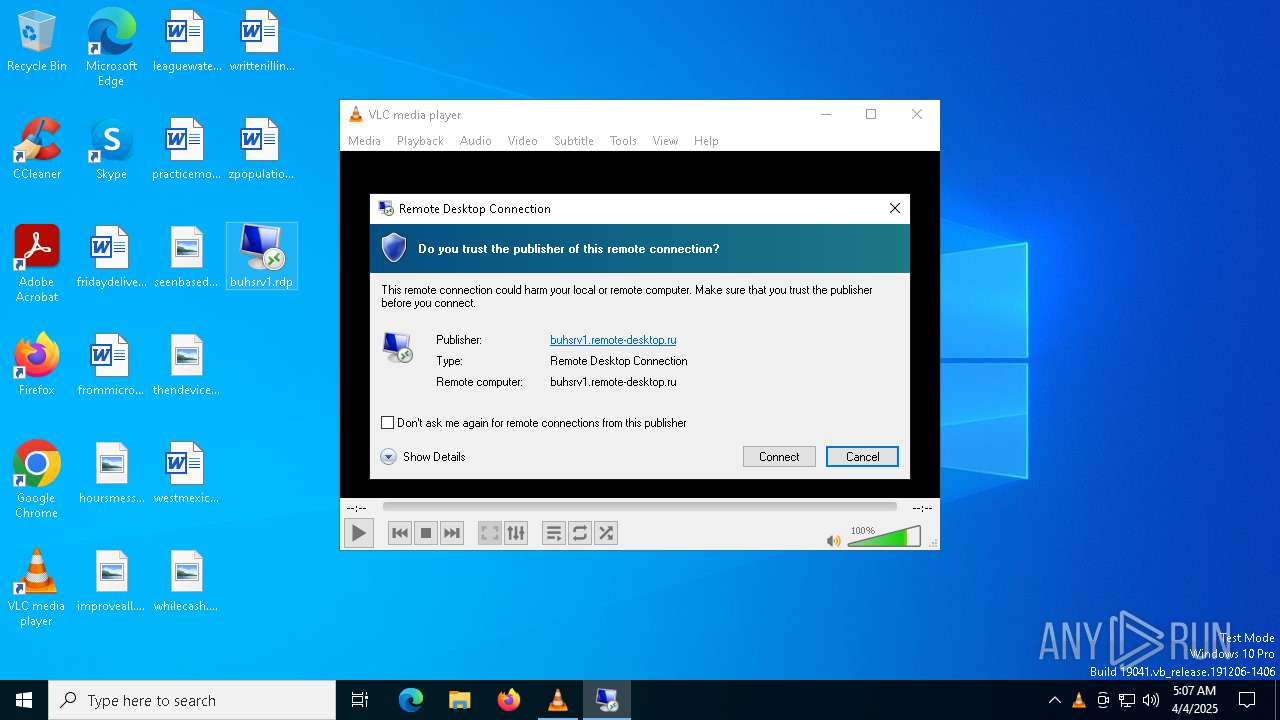
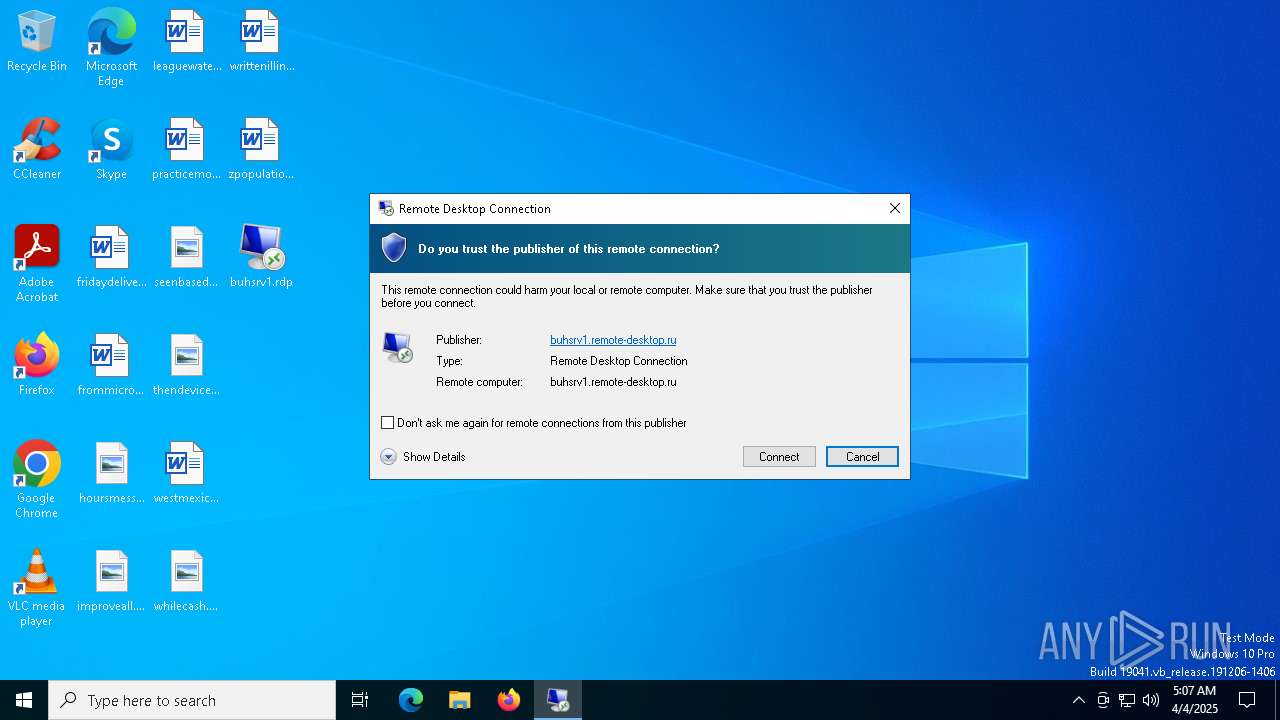
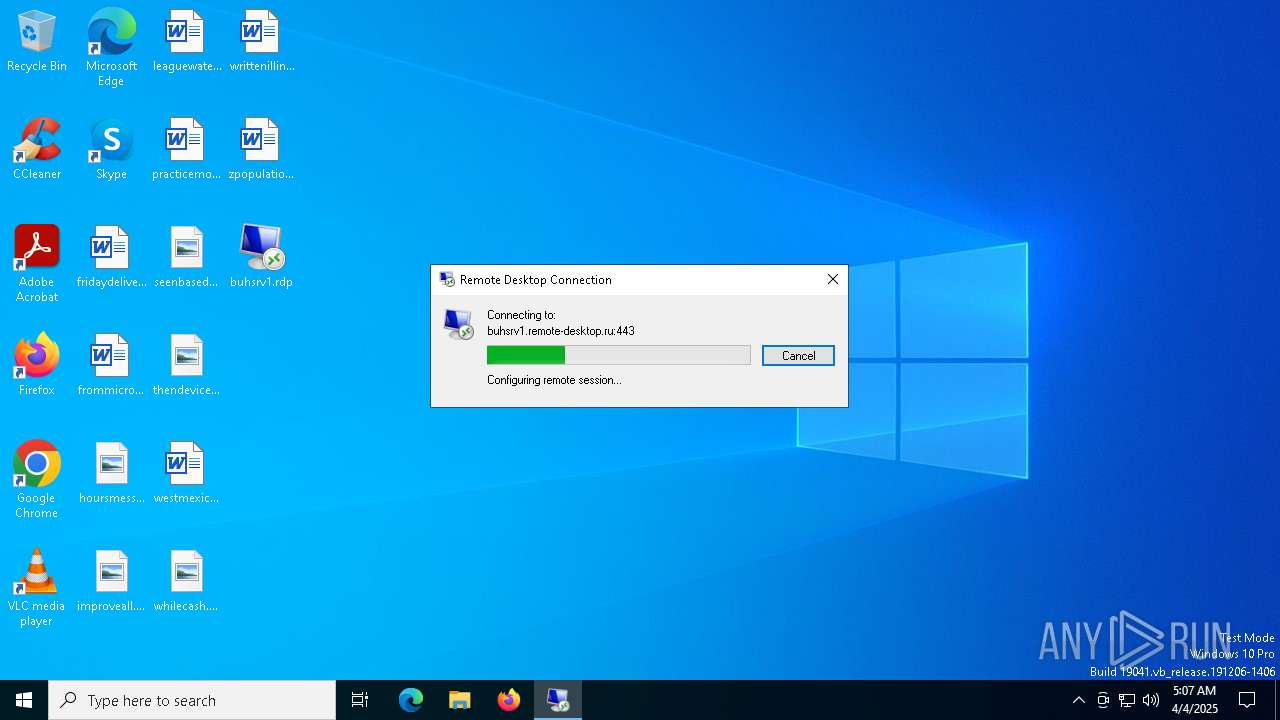
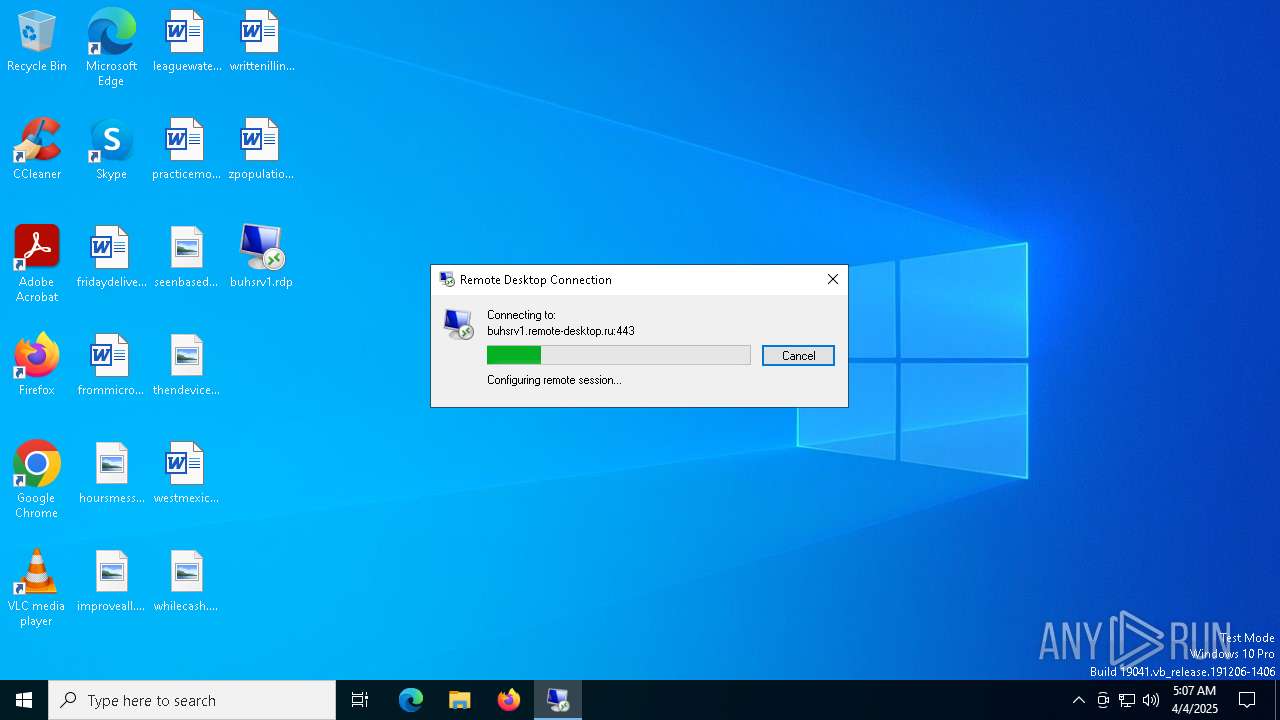
| 680 | "mstsc.exe" "C:\Users\admin\Desktop\buhsrv1.rdp" | C:\Windows\System32\mstsc.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Remote Desktop Connection Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4652 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6392 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | — | SppExtComObj.Exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6576 | "mstsc.exe" "C:\Users\admin\Desktop\buhsrv1.rdp" | C:\Windows\System32\mstsc.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Remote Desktop Connection Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
10 259
Read events
10 258
Write events
1
Delete events
0
Modification events
| (PID) Process: | (680) mstsc.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Terminal Server Client\PublisherBypassList |
| Operation: | write | Name: | C29BB19C5F37E8A8887750FB13C5489CE77FD27100 |
Value: 69 | |||
Executable files
4
Suspicious files
0
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 300 | vlc.exe | — | ||
MD5:— | SHA256:— | |||
| 300 | vlc.exe | C:\Users\admin\AppData\Roaming\vlc\vlc-qt-interface.ini.JXX300 | text | |
MD5:E32BAB2C0A1D850ED3BC5401F749CFE7 | SHA256:A59406D335C05D703F60510AFFFB251470109AA28D161734C781827CDE220839 | |||
| 300 | vlc.exe | C:\Users\admin\AppData\Roaming\vlc\ml.xspf.tmp300 | xml | |
MD5:781602441469750C3219C8C38B515ED4 | SHA256:81970DBE581373D14FBD451AC4B3F96E5F69B79645F1EE1CA715CFF3AF0BF20D | |||
| 300 | vlc.exe | C:\Users\admin\AppData\Roaming\vlc\vlc-qt-interface.ini.lock | text | |
MD5:35895C9F17BDE6474F1A866AB8770FFB | SHA256:688C8A7569E119B79704C4067425C9C307BB02FA965349443B03B19DAB5785CB | |||
| 300 | vlc.exe | C:\Users\admin\AppData\Roaming\vlc\ml.xspf | xml | |
MD5:781602441469750C3219C8C38B515ED4 | SHA256:81970DBE581373D14FBD451AC4B3F96E5F69B79645F1EE1CA715CFF3AF0BF20D | |||
| 300 | vlc.exe | C:\Users\admin\AppData\Roaming\vlc\vlc-qt-interface.ini.oXL300 | text | |
MD5:FDF960177BAE8D6D100AEF43865ECECB | SHA256:91B1E2C6168C135ADF6BE83696933C4DCC3DFF349E7F0B3A32420AA23E5FB5B7 | |||
| 300 | vlc.exe | C:\Users\admin\AppData\Roaming\vlc\vlc-qt-interface.ini | text | |
MD5:E32BAB2C0A1D850ED3BC5401F749CFE7 | SHA256:A59406D335C05D703F60510AFFFB251470109AA28D161734C781827CDE220839 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
21
DNS requests
13
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.25:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4300 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
4300 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2104 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.216.77.25:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
3216 | svchost.exe | 172.172.255.218:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6544 | svchost.exe | 40.126.31.3:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
2112 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2104 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
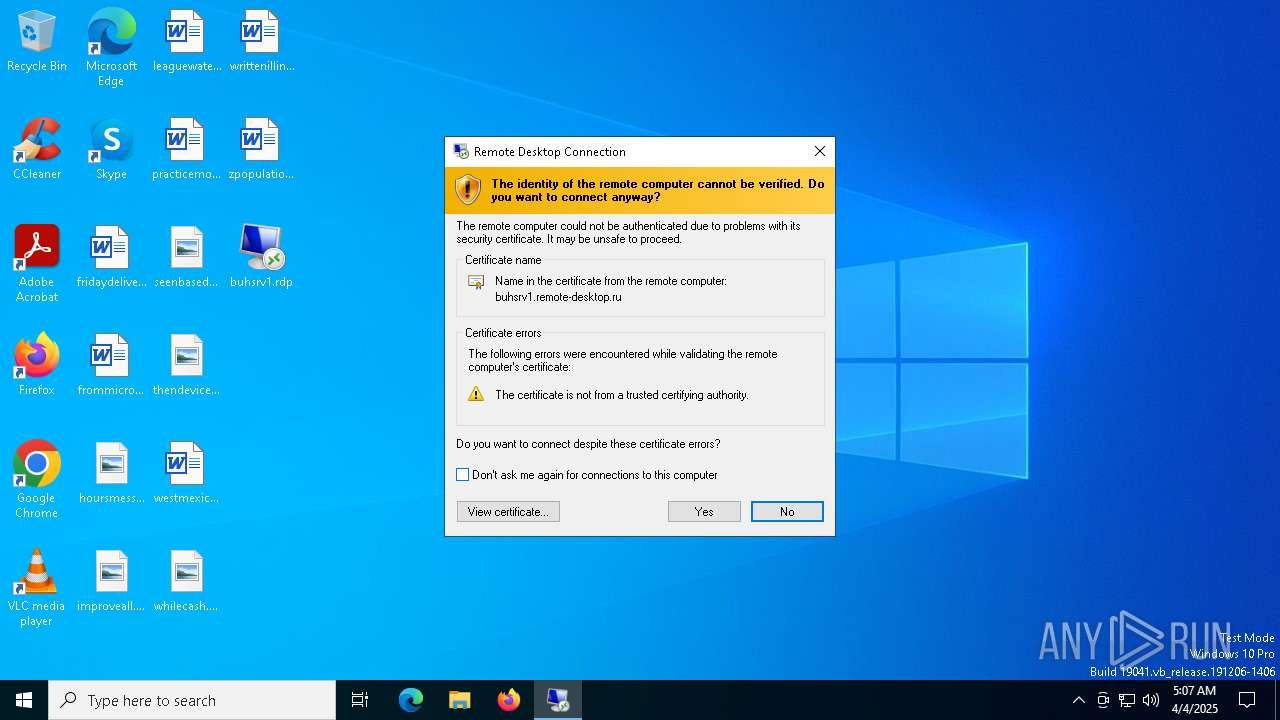
buhsrv1.remote-desktop.ru |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
680 | mstsc.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 29 |
680 | mstsc.exe | Potential Corporate Privacy Violation | POLICY [ANY.RUN] RDP protocol for remote access (TPKT Header) |
680 | mstsc.exe | Potential Corporate Privacy Violation | POLICY [ANY.RUN] RDP protocol for remote access (TPKT Header) |