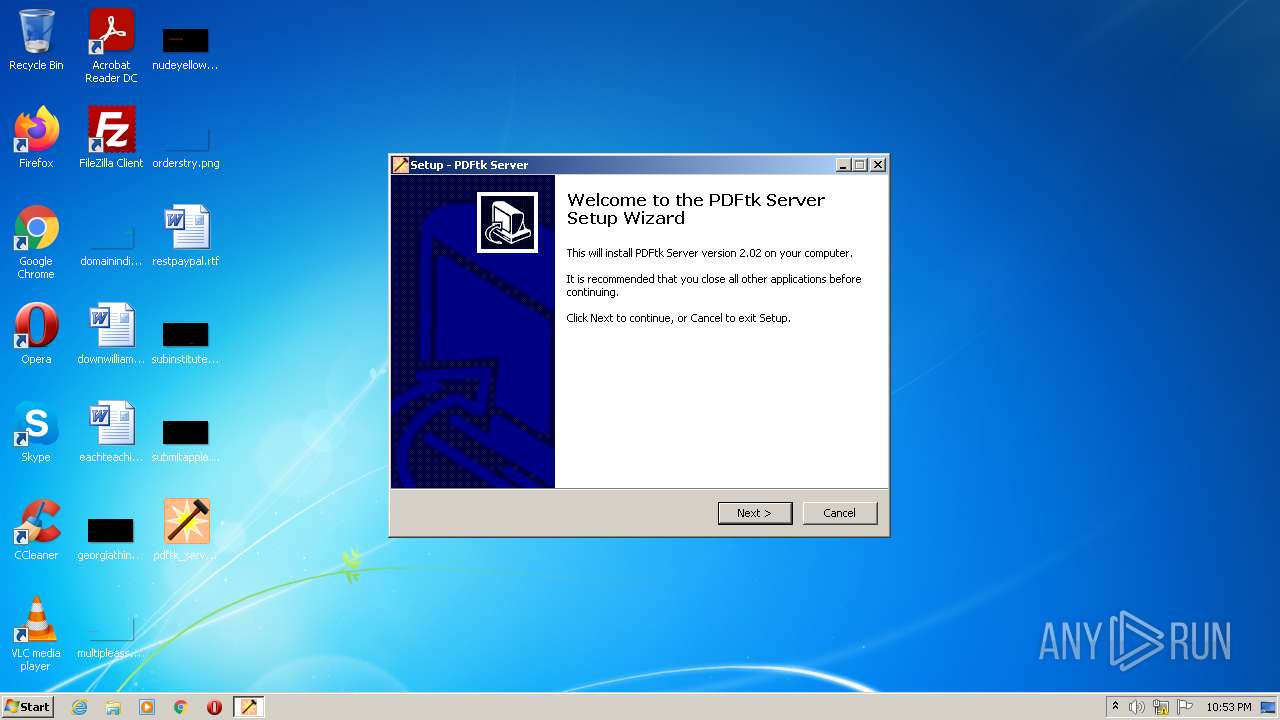
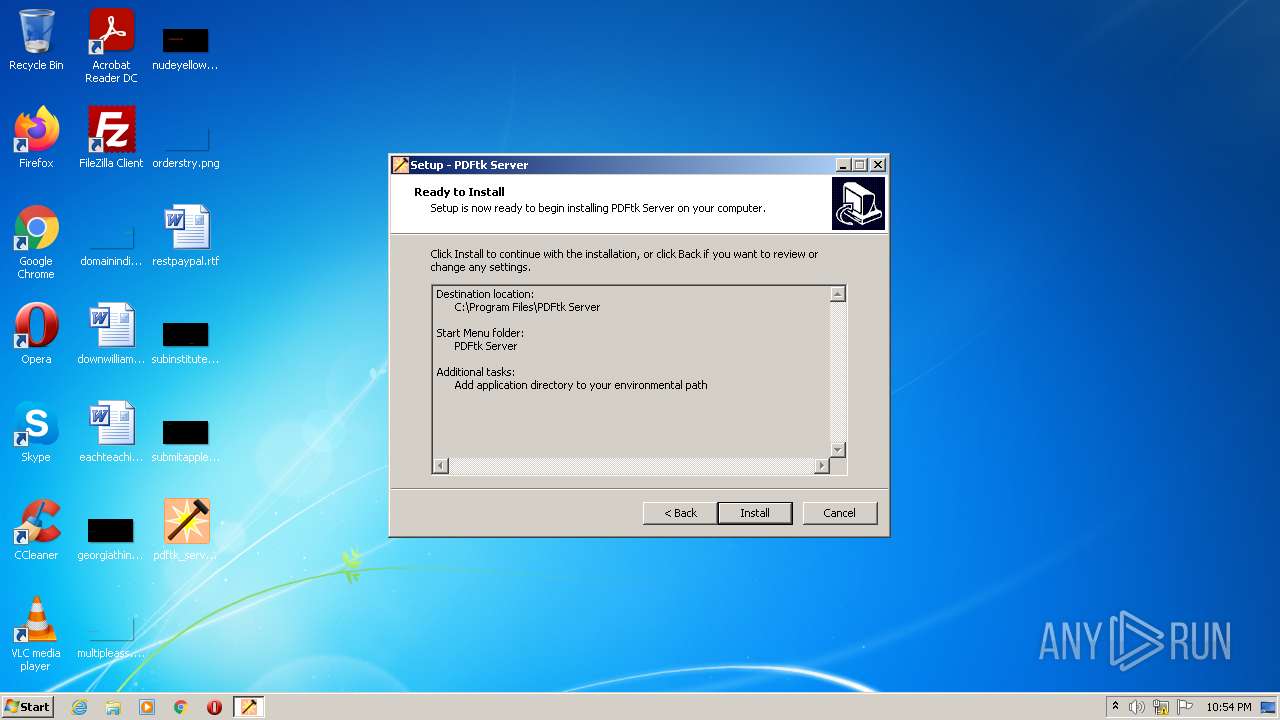
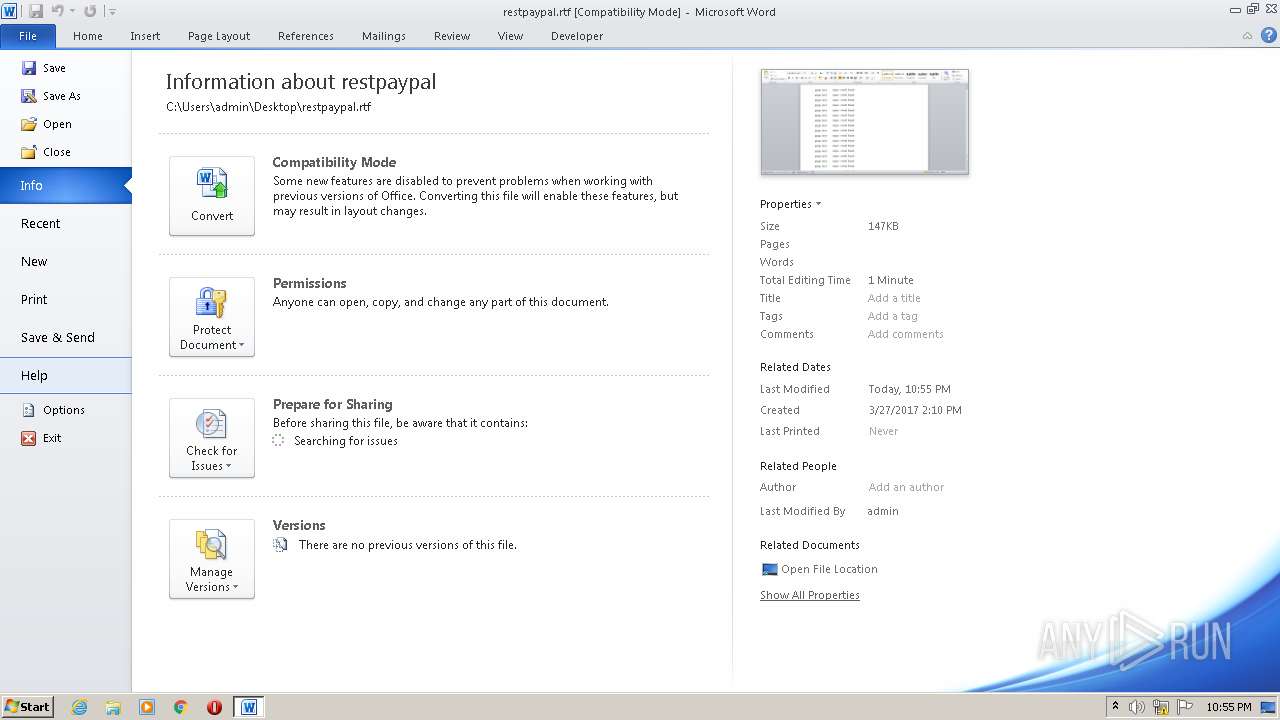
| File name: | pdftk_server-2.02-win-setup.exe |
| Full analysis: | https://app.any.run/tasks/287daa15-9da1-4a93-b036-4f9732f3b72a |
| Verdict: | Malicious activity |
| Analysis date: | August 12, 2022, 21:53:50 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 94A54AF63355C89BBED3C88A8BBFF3F2 |
| SHA1: | FD30F756B3F6279239568EA5C7EA0282DC5FFABE |
| SHA256: | CC8F6A43FC91026BB739AD0AD9A124C24750D6127662FB3638EC1D44403AABD2 |
| SSDEEP: | 49152:5bGUSR40n86Ru3NKNZuF9RTxK5crtjDdxDtRx8vu301sE2hqKLHXnucDr3:cPR4R0uRHRTY54jDDDtIvkqsE20aHXn7 |
MALICIOUS
Drops executable file immediately after starts
- pdftk_server-2.02-win-setup.exe (PID: 2500)
- pdftk_server-2.02-win-setup.exe (PID: 1816)
- pdftk_server-2.02-win-setup.tmp (PID: 2224)
Loads dropped or rewritten executable
- pdftk.exe (PID: 2572)
- pdftk.exe (PID: 3936)
Application was dropped or rewritten from another process
- pdftk.exe (PID: 3936)
- pdftk.exe (PID: 2572)
SUSPICIOUS
Checks supported languages
- pdftk_server-2.02-win-setup.exe (PID: 2500)
- pdftk_server-2.02-win-setup.tmp (PID: 3172)
- pdftk_server-2.02-win-setup.tmp (PID: 2224)
- pdftk_server-2.02-win-setup.exe (PID: 1816)
- cmd.exe (PID: 2344)
- pdftk.exe (PID: 2572)
- pdftk.exe (PID: 3936)
Executable content was dropped or overwritten
- pdftk_server-2.02-win-setup.exe (PID: 2500)
- pdftk_server-2.02-win-setup.exe (PID: 1816)
- pdftk_server-2.02-win-setup.tmp (PID: 2224)
Drops a file with a compile date too recent
- pdftk_server-2.02-win-setup.exe (PID: 2500)
- pdftk_server-2.02-win-setup.exe (PID: 1816)
- pdftk_server-2.02-win-setup.tmp (PID: 2224)
Reads Windows owner or organization settings
- pdftk_server-2.02-win-setup.tmp (PID: 2224)
Reads the computer name
- pdftk_server-2.02-win-setup.tmp (PID: 2224)
- pdftk_server-2.02-win-setup.tmp (PID: 3172)
- pdftk.exe (PID: 2572)
- pdftk.exe (PID: 3936)
Reads the Windows organization settings
- pdftk_server-2.02-win-setup.tmp (PID: 2224)
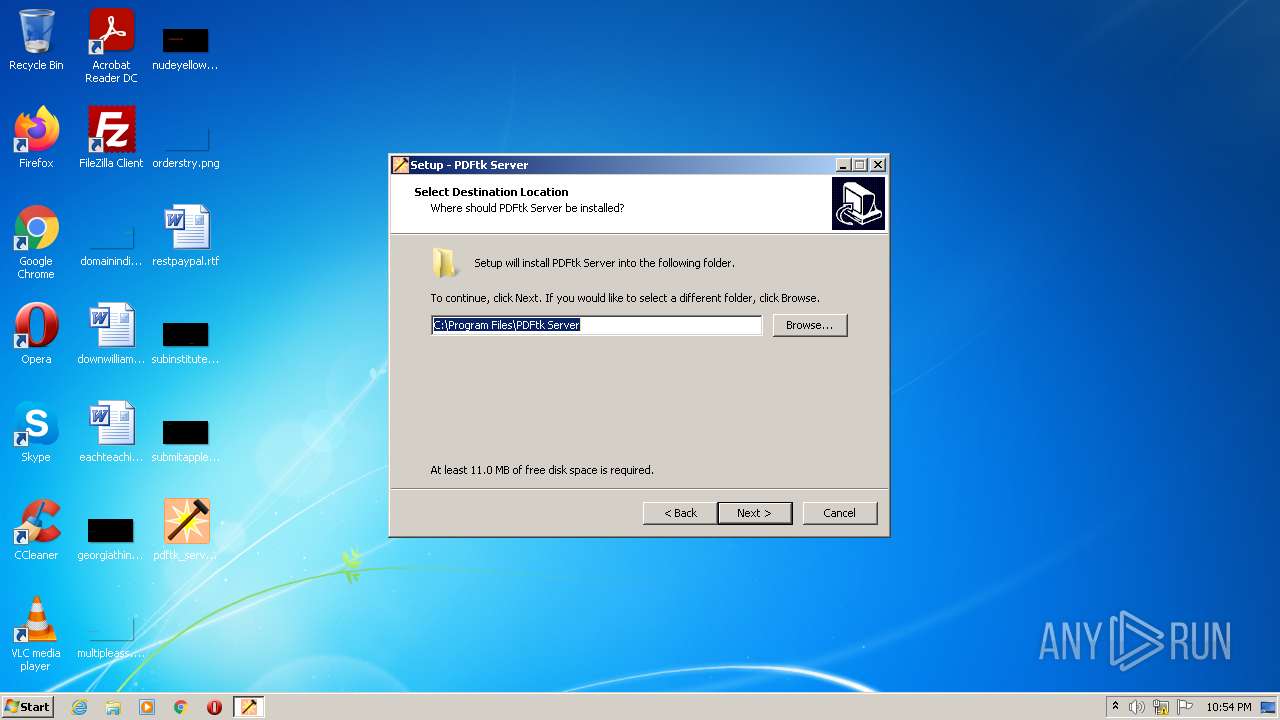
Creates a directory in Program Files
- pdftk_server-2.02-win-setup.tmp (PID: 2224)
INFO
Application was dropped or rewritten from another process
- pdftk_server-2.02-win-setup.tmp (PID: 3172)
- pdftk_server-2.02-win-setup.tmp (PID: 2224)
Loads dropped or rewritten executable
- pdftk_server-2.02-win-setup.tmp (PID: 2224)
Creates files in the program directory
- pdftk_server-2.02-win-setup.tmp (PID: 2224)
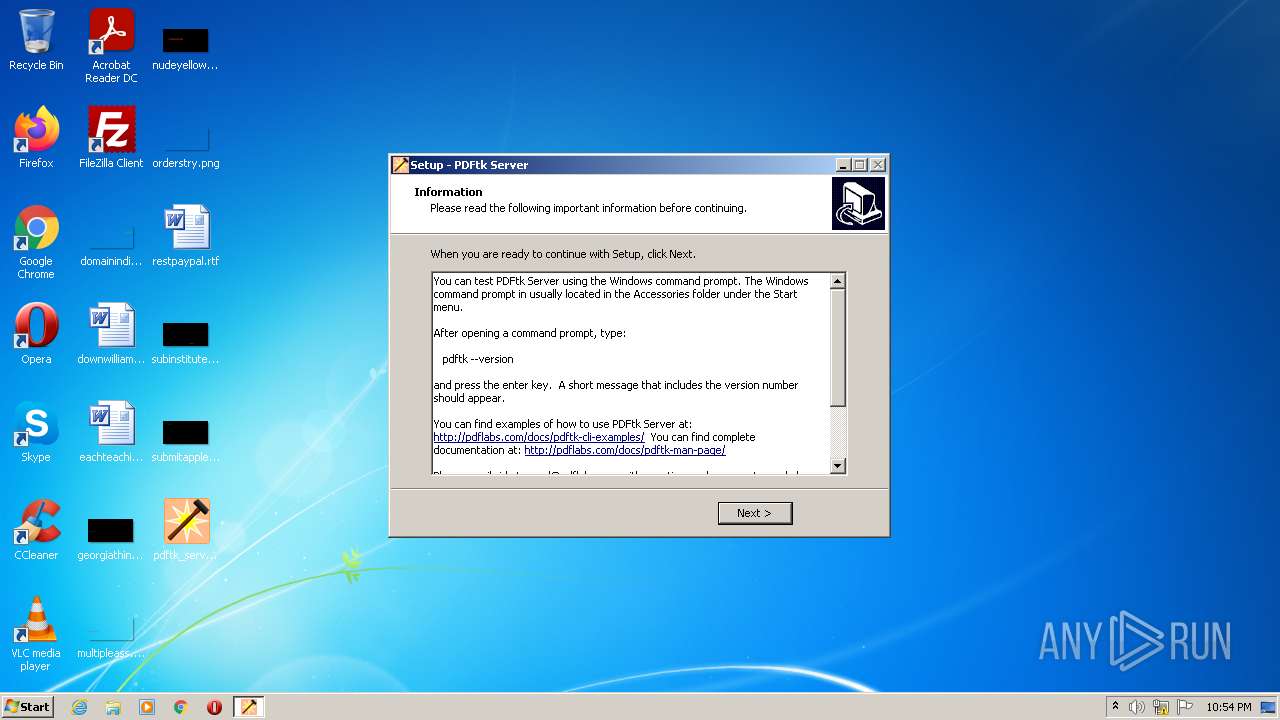
Creates a software uninstall entry
- pdftk_server-2.02-win-setup.tmp (PID: 2224)
Checks supported languages
- WINWORD.EXE (PID: 1992)
- AcroRd32.exe (PID: 2988)
- RdrCEF.exe (PID: 3544)
- RdrCEF.exe (PID: 3016)
- RdrCEF.exe (PID: 3256)
- AcroRd32.exe (PID: 3064)
- RdrCEF.exe (PID: 1136)
- RdrCEF.exe (PID: 1028)
- RdrCEF.exe (PID: 664)
- RdrCEF.exe (PID: 2668)
- RdrCEF.exe (PID: 2768)
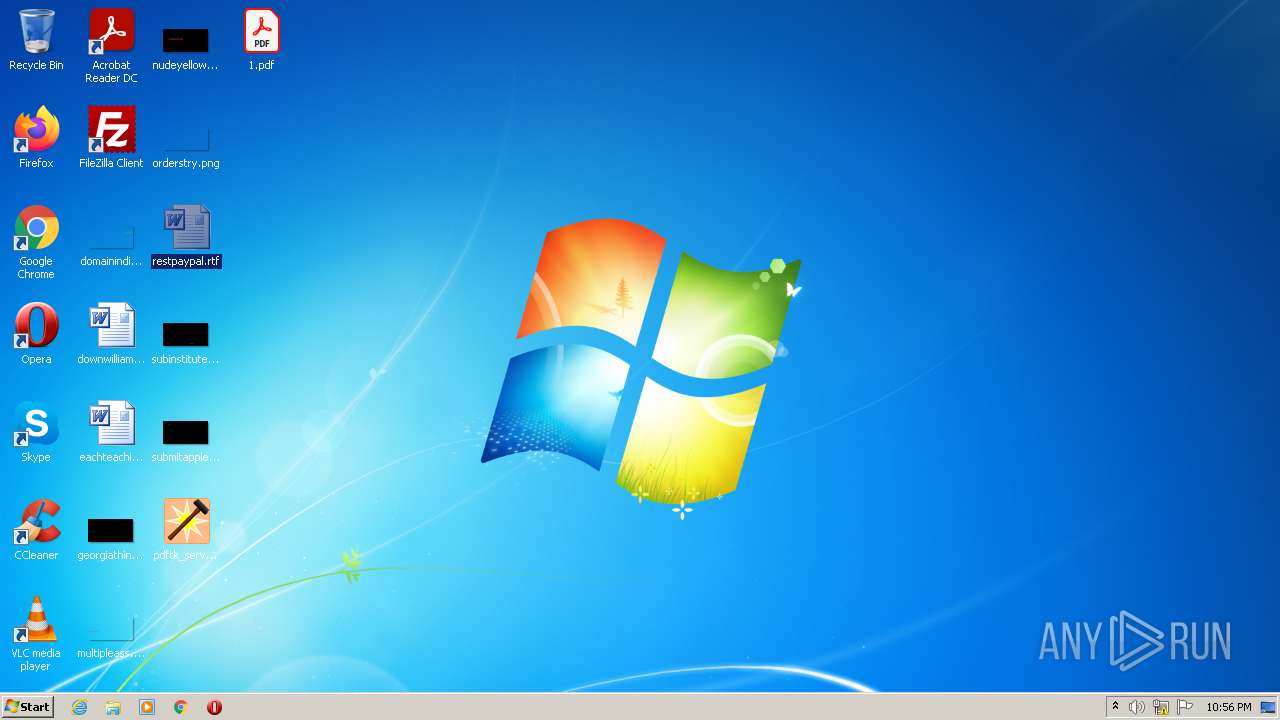
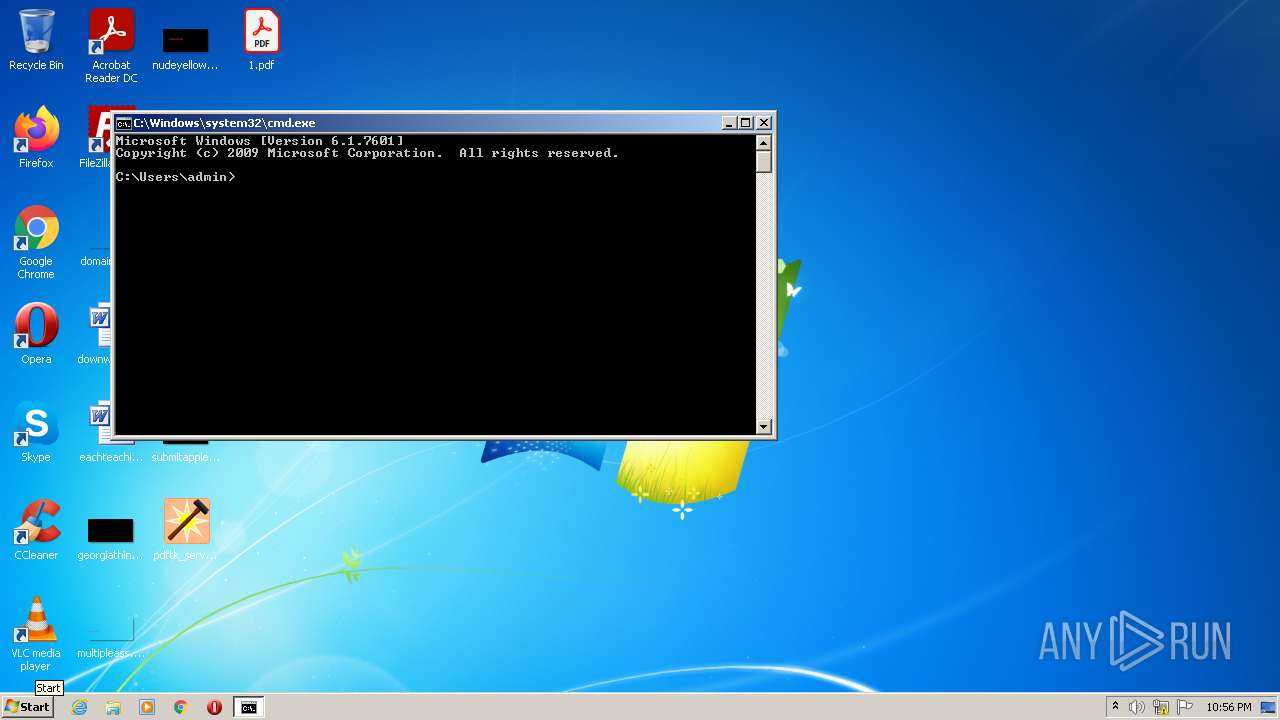
Manual execution by user
- WINWORD.EXE (PID: 1992)
- cmd.exe (PID: 2344)
Application launched itself
- AcroRd32.exe (PID: 2988)
- RdrCEF.exe (PID: 3544)
Reads the computer name
- AcroRd32.exe (PID: 2988)
- WINWORD.EXE (PID: 1992)
- AcroRd32.exe (PID: 3064)
- RdrCEF.exe (PID: 3544)
Searches for installed software
- AcroRd32.exe (PID: 2988)
- AcroRd32.exe (PID: 3064)
Reads CPU info
- AcroRd32.exe (PID: 3064)
Checks Windows Trust Settings
- AcroRd32.exe (PID: 2988)
Reads settings of System Certificates
- AcroRd32.exe (PID: 2988)
- RdrCEF.exe (PID: 3544)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 1992)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Delphi generic (57.2) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (18.2) |
| .exe | | | Win16/32 Executable Delphi generic (8.3) |
| .exe | | | Generic Win/DOS Executable (8) |
| .exe | | | DOS Executable Generic (8) |
EXIF
EXE
| ProductVersion: | 2.02 |
|---|---|
| ProductName: | PDFtk Server |
| LegalCopyright: | Copyright 2003-2013 Steward and Lee, LLC |
| FileVersion: | |
| FileDescription: | PDFtk Server Setup |
| CompanyName: | PDF Labs |
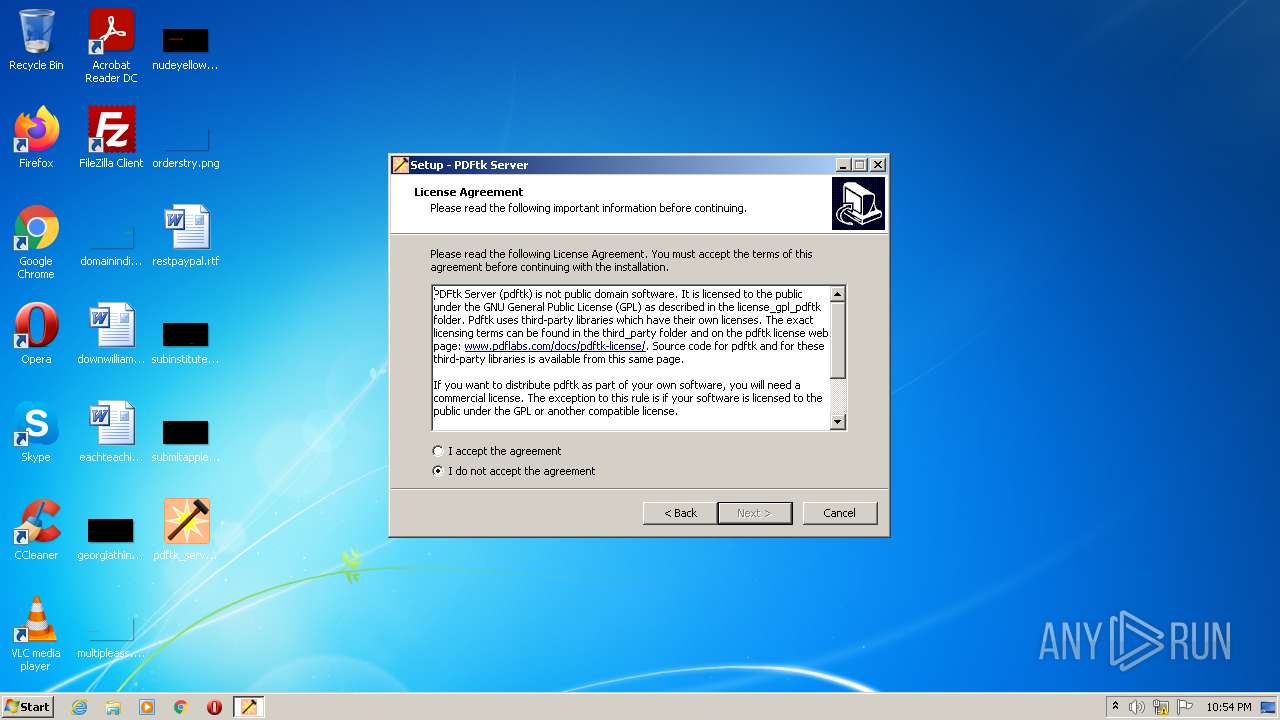
| Comments: | This installation was built with Inno Setup. |
| CharacterSet: | Unicode |
| LanguageCode: | Neutral |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 0.0.0.0 |
| FileVersionNumber: | 0.0.0.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 5 |
| ImageVersion: | 6 |
| OSVersion: | 5 |
| EntryPoint: | 0xf3bc |
| UninitializedDataSize: | - |
| InitializedDataSize: | 266240 |
| CodeSize: | 60416 |
| LinkerVersion: | 2.25 |
| PEType: | PE32 |
| TimeStamp: | 2012:10:09 10:48:22+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 09-Oct-2012 08:48:22 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | PDF Labs |
| FileDescription: | PDFtk Server Setup |
| FileVersion: | - |
| LegalCopyright: | Copyright 2003-2013 Steward and Lee, LLC |
| ProductName: | PDFtk Server |
| ProductVersion: | 2.02 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 09-Oct-2012 08:48:22 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000DE64 | 0x0000E000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.45289 |
.itext | 0x0000F000 | 0x00000B2C | 0x00000C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.68179 |
.data | 0x00010000 | 0x00000C84 | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.23598 |
.bss | 0x00011000 | 0x000056B0 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00017000 | 0x00000DD0 | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.89082 |
.tls | 0x00018000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x00019000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.204488 |
.rsrc | 0x0001A000 | 0x0003F1FC | 0x0003F200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.41113 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.08452 | 1444 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 5.08151 | 7336 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 5.60222 | 3240 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 5.83291 | 1864 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 3.98068 | 204840 | Latin 1 / Western European | English - United States | RT_ICON |
4091 | 2.56031 | 104 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4092 | 3.25287 | 212 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4093 | 3.26919 | 164 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4094 | 3.33268 | 684 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4095 | 3.34579 | 844 | Latin 1 / Western European | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
oleaut32.dll |
user32.dll |
Total processes
61
Monitored processes
18
Malicious processes
5
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 664 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe" --type=renderer --log-file="C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\debug.log" --touch-events=enabled --field-trial-handle=1188,12569236771562159300,1284792434199612626,131072 --disable-features=NetworkService,VizDisplayCompositor --disable-gpu-compositing --lang=en-US --disable-pack-loading --log-file="C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\debug.log" --log-severity=disable --product-version="ReaderServices/20.13.20064 Chrome/80.0.0.0" --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10534915373040682087 --renderer-client-id=7 --mojo-platform-channel-handle=1536 --allow-no-sandbox-job /prefetch:1 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe | — | RdrCEF.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe RdrCEF Exit code: 0 Version: 20.13.20064.405839 Modules
| |||||||||||||||
| 1028 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe" --type=renderer --log-file="C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\debug.log" --touch-events=enabled --field-trial-handle=1188,12569236771562159300,1284792434199612626,131072 --disable-features=NetworkService,VizDisplayCompositor --disable-gpu-compositing --lang=en-US --disable-pack-loading --log-file="C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\debug.log" --log-severity=disable --product-version="ReaderServices/20.13.20064 Chrome/80.0.0.0" --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3417445559051384311 --renderer-client-id=6 --mojo-platform-channel-handle=1520 --allow-no-sandbox-job /prefetch:1 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe | — | RdrCEF.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe RdrCEF Exit code: 0 Version: 20.13.20064.405839 Modules
| |||||||||||||||
| 1136 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe" --type=gpu-process --field-trial-handle=1188,12569236771562159300,1284792434199612626,131072 --disable-features=NetworkService,VizDisplayCompositor --disable-pack-loading --log-file="C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\debug.log" --log-severity=disable --product-version="ReaderServices/20.13.20064 Chrome/80.0.0.0" --lang=en-US --gpu-preferences=KAAAAAAAAADgACAgAQAAAAAAAAAAAGAAAAAAABAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --use-gl=swiftshader-webgl --log-file="C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\debug.log" --service-request-channel-token=9493084791381521854 --mojo-platform-channel-handle=1464 --allow-no-sandbox-job --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe | — | RdrCEF.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe RdrCEF Exit code: 1 Version: 20.13.20064.405839 Modules
| |||||||||||||||
| 1816 | "C:\Users\admin\Desktop\pdftk_server-2.02-win-setup.exe" /SPAWNWND=$1013C /NOTIFYWND=$2012A | C:\Users\admin\Desktop\pdftk_server-2.02-win-setup.exe | pdftk_server-2.02-win-setup.tmp | ||||||||||||
User: admin Company: PDF Labs Integrity Level: HIGH Description: PDFtk Server Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 1992 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\restpaypal.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2224 | "C:\Users\admin\AppData\Local\Temp\is-9OQ3G.tmp\pdftk_server-2.02-win-setup.tmp" /SL5="$2013E,2643659,327680,C:\Users\admin\Desktop\pdftk_server-2.02-win-setup.exe" /SPAWNWND=$1013C /NOTIFYWND=$2012A | C:\Users\admin\AppData\Local\Temp\is-9OQ3G.tmp\pdftk_server-2.02-win-setup.tmp | pdftk_server-2.02-win-setup.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 2344 | "C:\Windows\system32\cmd.exe" | C:\Windows\system32\cmd.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2500 | "C:\Users\admin\Desktop\pdftk_server-2.02-win-setup.exe" | C:\Users\admin\Desktop\pdftk_server-2.02-win-setup.exe | Explorer.EXE | ||||||||||||
User: admin Company: PDF Labs Integrity Level: MEDIUM Description: PDFtk Server Setup Exit code: 0 Version: Modules
| |||||||||||||||
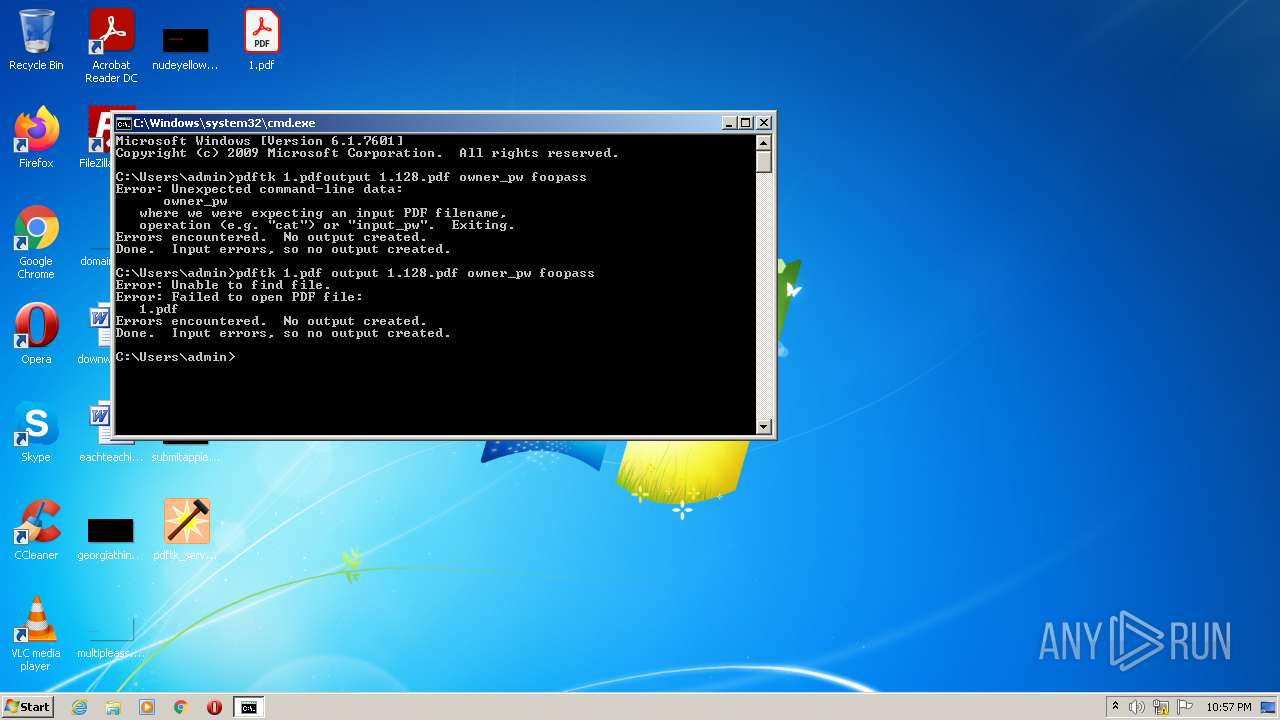
| 2572 | pdftk 1.pdfoutput 1.128.pdf owner_pw foopass | C:\Program Files\PDFtk Server\bin\pdftk.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
| 2668 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe" --type=gpu-process --field-trial-handle=1188,12569236771562159300,1284792434199612626,131072 --disable-features=NetworkService,VizDisplayCompositor --disable-pack-loading --log-file="C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\debug.log" --log-severity=disable --product-version="ReaderServices/20.13.20064 Chrome/80.0.0.0" --lang=en-US --gpu-preferences=KAAAAAAAAADgACAgAQAAAAAAAAAAAGAAAAAAABAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --use-gl=swiftshader-webgl --log-file="C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\debug.log" --service-request-channel-token=12810568363279800801 --mojo-platform-channel-handle=1392 --allow-no-sandbox-job --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe | — | RdrCEF.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe RdrCEF Exit code: 1 Version: 20.13.20064.405839 Modules
| |||||||||||||||
Total events
16 816
Read events
16 122
Write events
512
Delete events
182
Modification events
| (PID) Process: | (2224) pdftk_server-2.02-win-setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: B00800002A6F2E0596AED801 | |||
| (PID) Process: | (2224) pdftk_server-2.02-win-setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: A97A4661ECF7C60B0612E480337E0F731F1220B046080711EB637E1C426C849D | |||
| (PID) Process: | (2224) pdftk_server-2.02-win-setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (2224) pdftk_server-2.02-win-setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFiles0000 |
Value: C:\Program Files\PDFtk Server\bin\libiconv2.dll | |||
| (PID) Process: | (2224) pdftk_server-2.02-win-setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFilesHash |
Value: D7137CB990584188845A4A45FB0F96B0CFB42DC5A77FB8B3C73B9A7965ABF23C | |||
| (PID) Process: | (2224) pdftk_server-2.02-win-setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{E3617D29-6D71-4B5C-B9E2-C927C705E317}_is1 |
| Operation: | write | Name: | Inno Setup: Setup Version |
Value: 5.5.2 (u) | |||
| (PID) Process: | (2224) pdftk_server-2.02-win-setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{E3617D29-6D71-4B5C-B9E2-C927C705E317}_is1 |
| Operation: | write | Name: | Inno Setup: App Path |
Value: C:\Program Files\PDFtk Server | |||
| (PID) Process: | (2224) pdftk_server-2.02-win-setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{E3617D29-6D71-4B5C-B9E2-C927C705E317}_is1 |
| Operation: | write | Name: | InstallLocation |
Value: C:\Program Files\PDFtk Server\ | |||
| (PID) Process: | (2224) pdftk_server-2.02-win-setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{E3617D29-6D71-4B5C-B9E2-C927C705E317}_is1 |
| Operation: | write | Name: | Inno Setup: Icon Group |
Value: PDFtk Server | |||
| (PID) Process: | (2224) pdftk_server-2.02-win-setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{E3617D29-6D71-4B5C-B9E2-C927C705E317}_is1 |
| Operation: | write | Name: | Inno Setup: User |
Value: admin | |||
Executable files
9
Suspicious files
126
Text files
65
Unknown types
11
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2224 | pdftk_server-2.02-win-setup.tmp | C:\Users\admin\AppData\Local\Temp\is-O5LGT.tmp\_isetup\_shfoldr.dll | executable | |
MD5:92DC6EF532FBB4A5C3201469A5B5EB63 | SHA256:9884E9D1B4F8A873CCBD81F8AD0AE257776D2348D027D811A56475E028360D87 | |||
| 2224 | pdftk_server-2.02-win-setup.tmp | C:\Program Files\PDFtk Server\bin\pdftk.exe | executable | |
MD5:84E0D5EC5117114B21F26DC9C1F38B48 | SHA256:5E5CBE817ECC3CC1875369D81119472559C9624D55C7176852C8827750AFA00A | |||
| 2224 | pdftk_server-2.02-win-setup.tmp | C:\Program Files\PDFtk Server\bin\is-Q2KQ0.tmp | executable | |
MD5:84E0D5EC5117114B21F26DC9C1F38B48 | SHA256:5E5CBE817ECC3CC1875369D81119472559C9624D55C7176852C8827750AFA00A | |||
| 2224 | pdftk_server-2.02-win-setup.tmp | C:\Program Files\PDFtk Server\docs\pdftk.1.txt | text | |
MD5:0CB2104C7A6B398F3696D7FCCD5E949D | SHA256:6122CA5A3866B59071CB241CD0A0B2130481A78A0642FB5DD6BE2A4258FE58A0 | |||
| 2224 | pdftk_server-2.02-win-setup.tmp | C:\Program Files\PDFtk Server\docs\pdftk.1.html | html | |
MD5:6D097976D554FFCA6754D5DE8188D07E | SHA256:02FD039AA624B14FDA7DC41478D3E43D05F96E15589D5E832CFFAAB558CB6649 | |||
| 1816 | pdftk_server-2.02-win-setup.exe | C:\Users\admin\AppData\Local\Temp\is-9OQ3G.tmp\pdftk_server-2.02-win-setup.tmp | executable | |
MD5:252227BFF84AB95ED76BFA44C429B413 | SHA256:E98710DD1E98F0D086F725F38B7F547141F940B0D111A9B07633172A7C2BA2CA | |||
| 2500 | pdftk_server-2.02-win-setup.exe | C:\Users\admin\AppData\Local\Temp\is-5JBTI.tmp\pdftk_server-2.02-win-setup.tmp | executable | |
MD5:252227BFF84AB95ED76BFA44C429B413 | SHA256:E98710DD1E98F0D086F725F38B7F547141F940B0D111A9B07633172A7C2BA2CA | |||
| 2224 | pdftk_server-2.02-win-setup.tmp | C:\Program Files\PDFtk Server\docs\changelog.html | html | |
MD5:5B79763C2CAC31D30F1682552AF5D3A3 | SHA256:4ECE09694BB1700CF8043A67466034A40858ADFCA83A19D2659D2EC191585B3B | |||
| 2224 | pdftk_server-2.02-win-setup.tmp | C:\Program Files\PDFtk Server\docs\is-BIDMG.tmp | text | |
MD5:FDC30ED4F4EF6B71265F3745207DA7E2 | SHA256:DA919FDBA0B52C24FACD532A71CEEA30BF8647865D8A6D28DEB12283FC1EC54C | |||
| 2224 | pdftk_server-2.02-win-setup.tmp | C:\Program Files\PDFtk Server\bin\is-DSI1Q.tmp | executable | |
MD5:FD1DC6C680299A2ED1EEDCC3EABDA601 | SHA256:CB016E794D3311C71F21D87803E10A0E1133995F62A485EB37B321CD9B9E1087 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
3
DNS requests
2
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3544 | RdrCEF.exe | 23.35.236.137:443 | geo2.adobe.com | Zayo Bandwidth Inc | US | suspicious |
3544 | RdrCEF.exe | 107.22.247.231:443 | p13n.adobe.io | Amazon.com, Inc. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
geo2.adobe.com |
| whitelisted |
p13n.adobe.io |
| whitelisted |