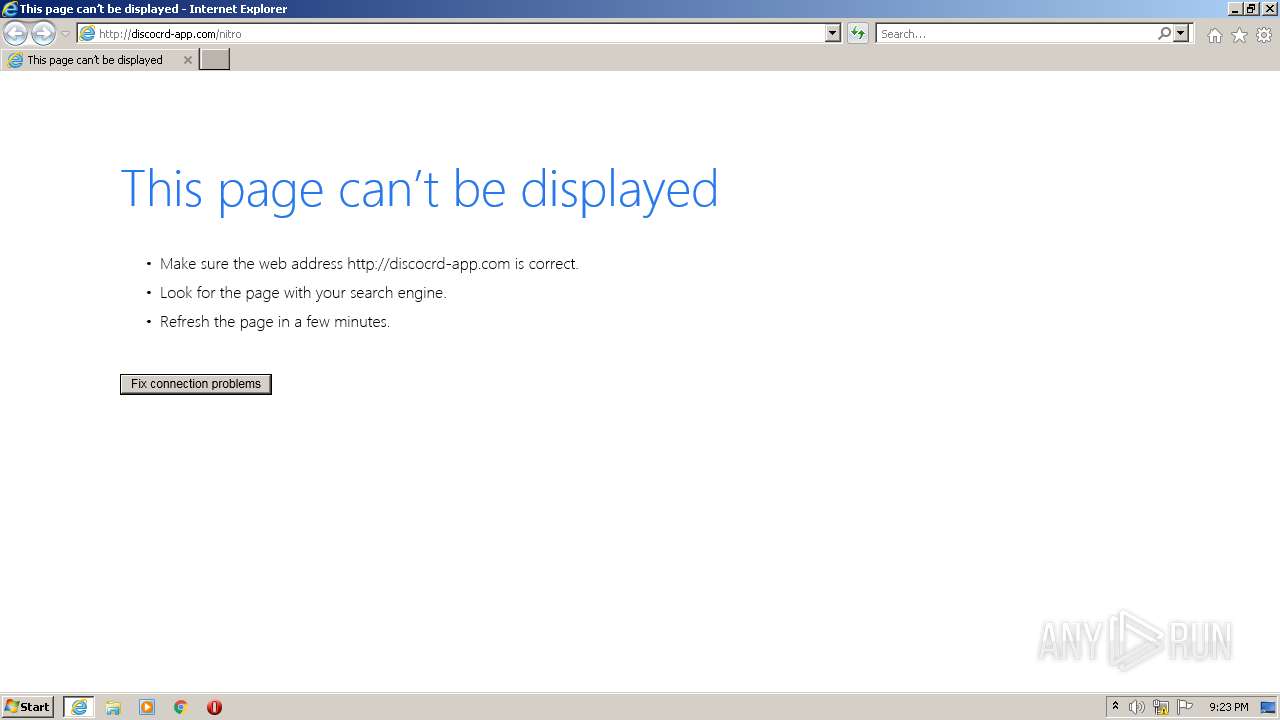
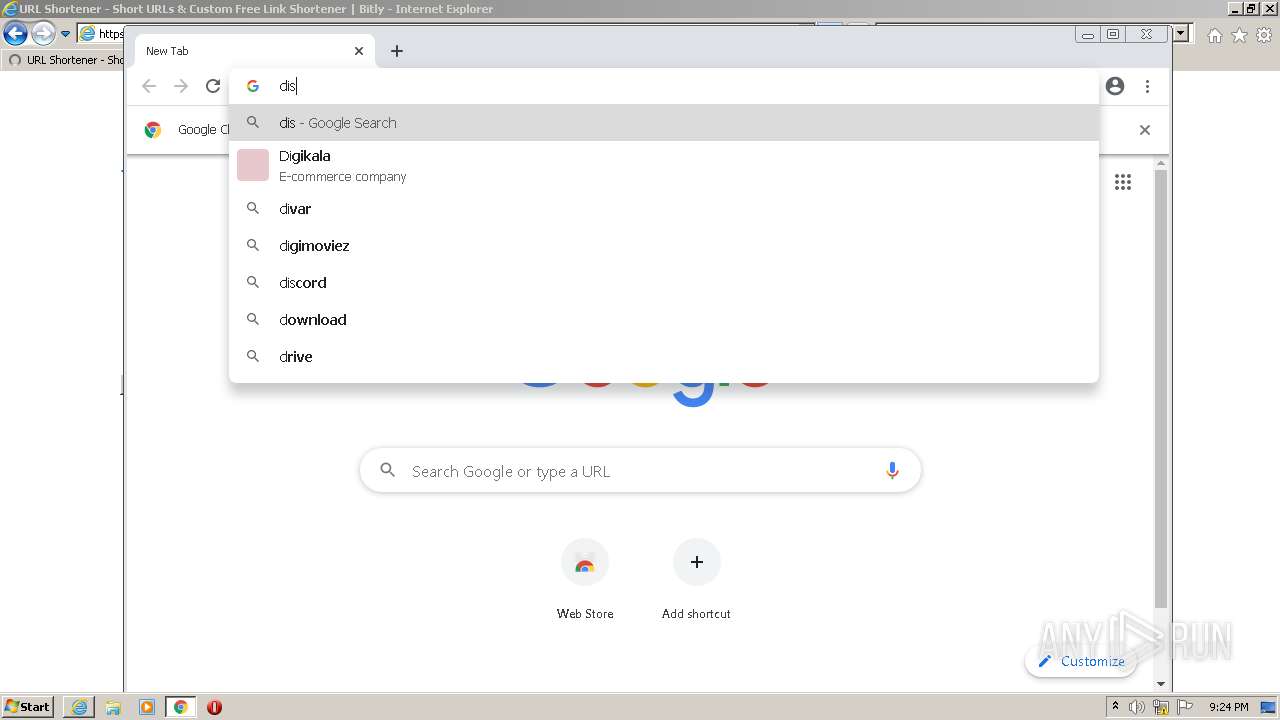
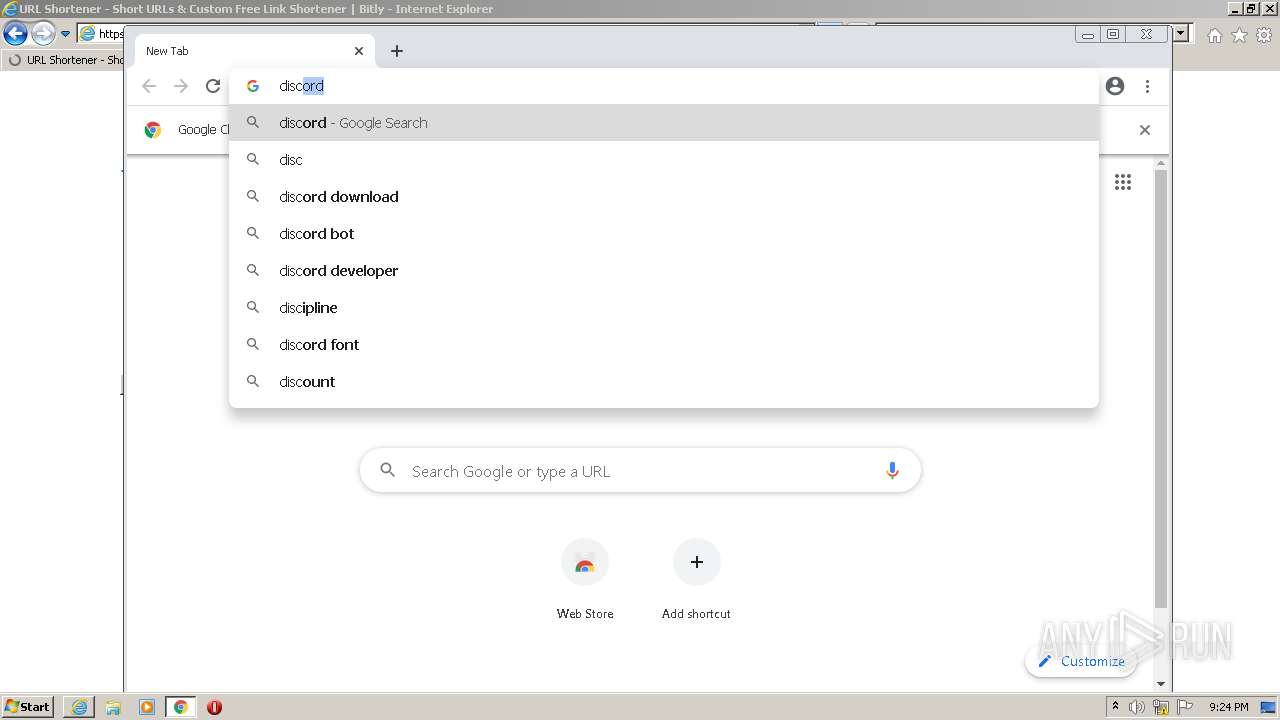
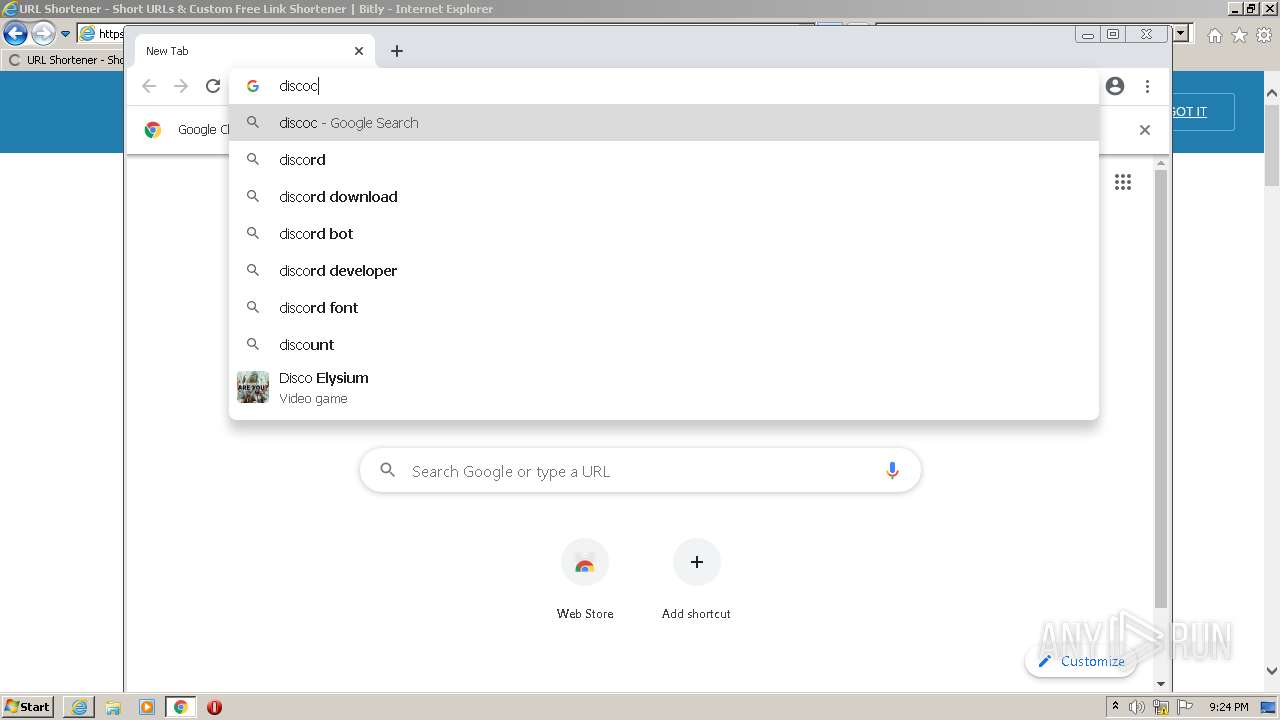
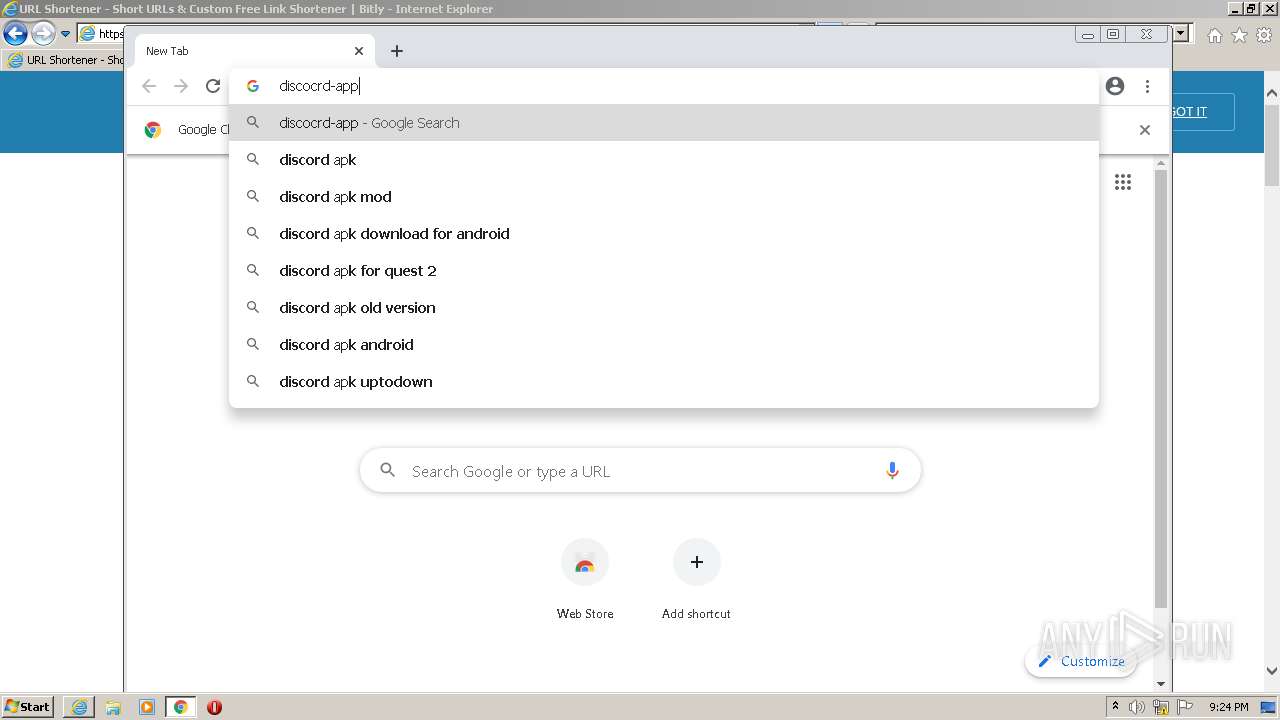
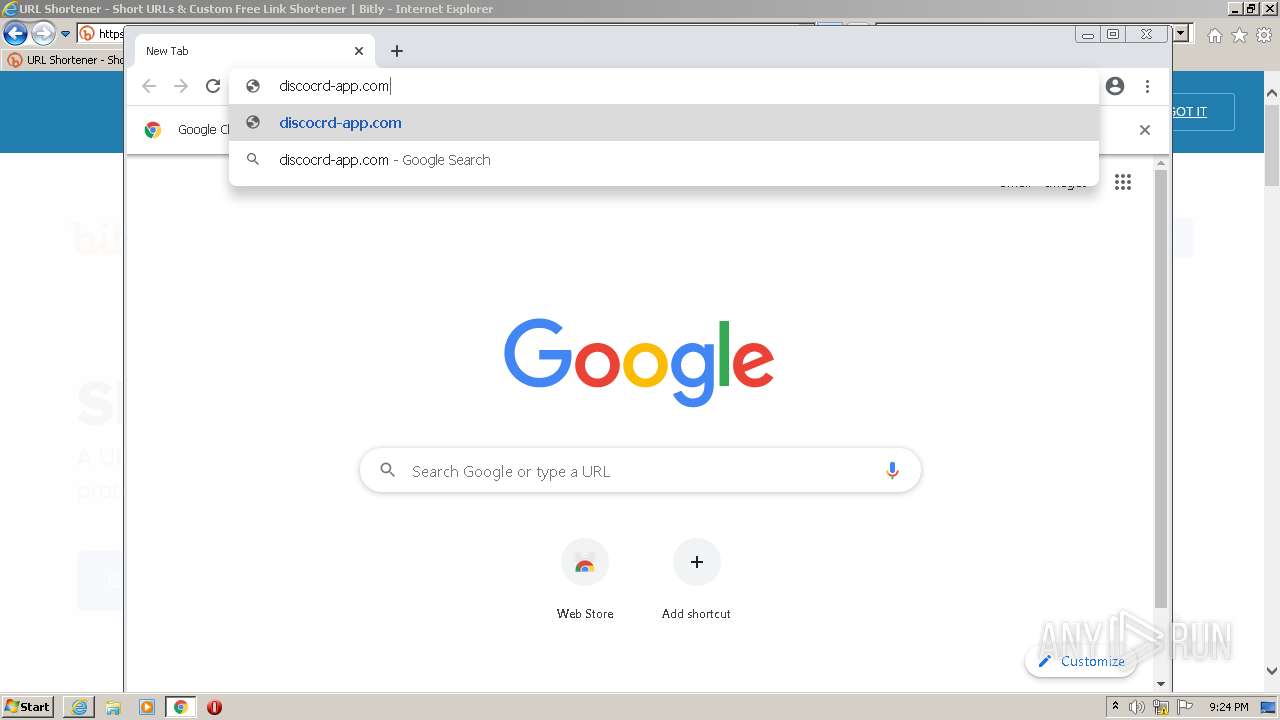
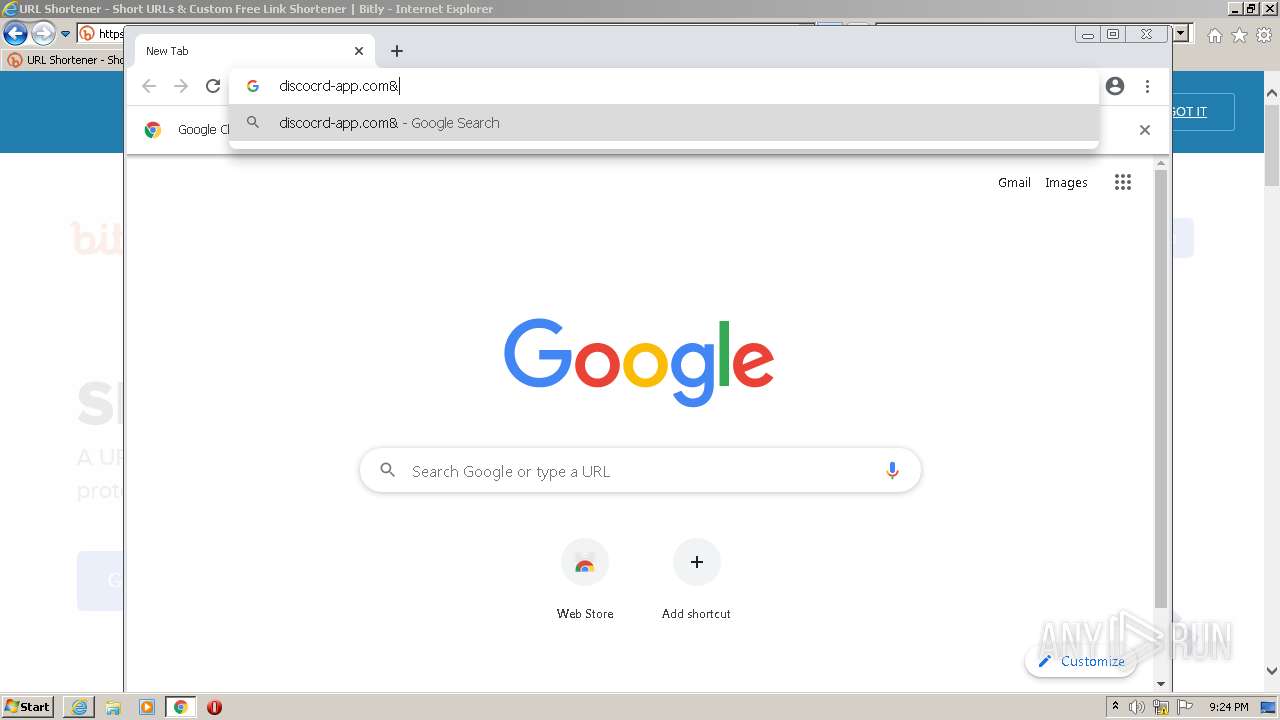
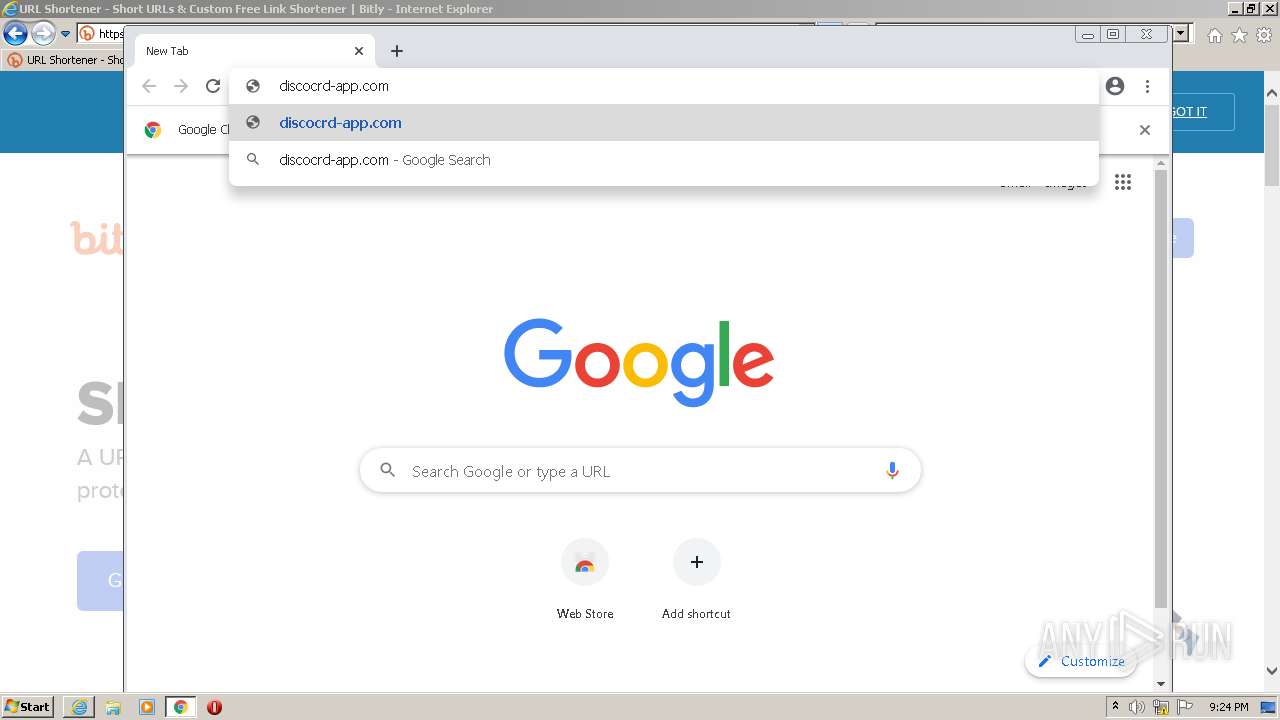
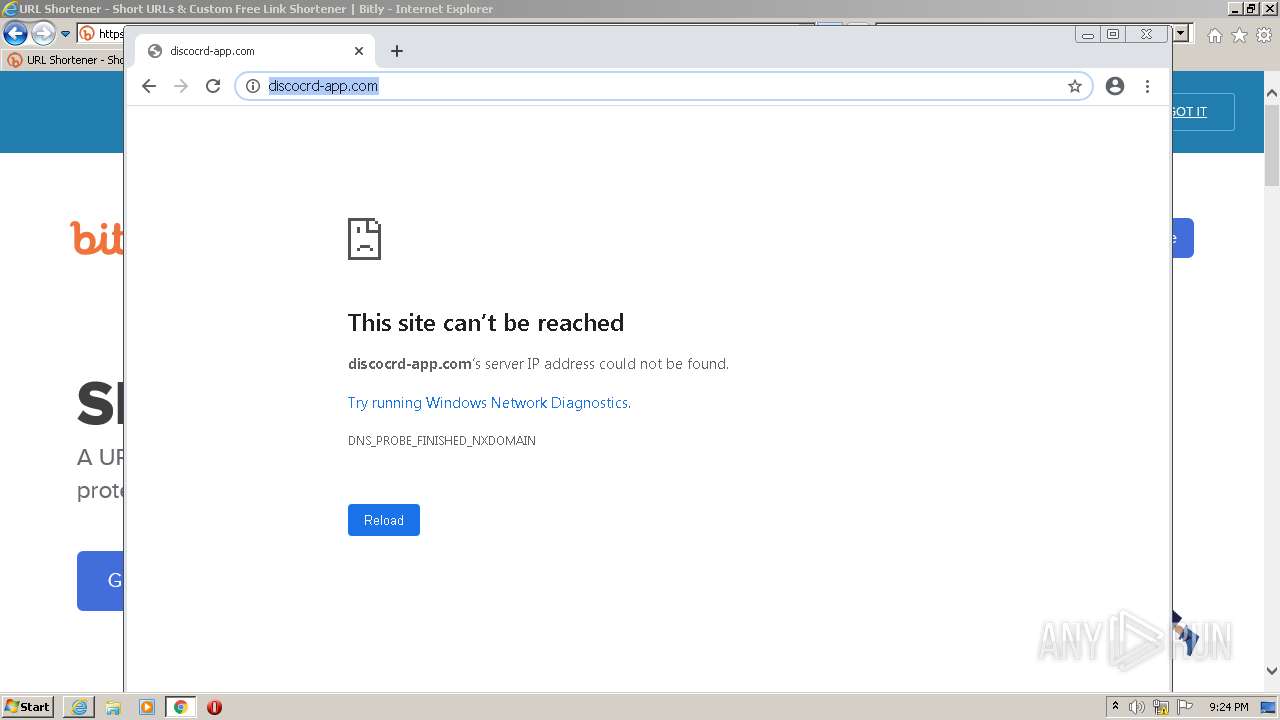
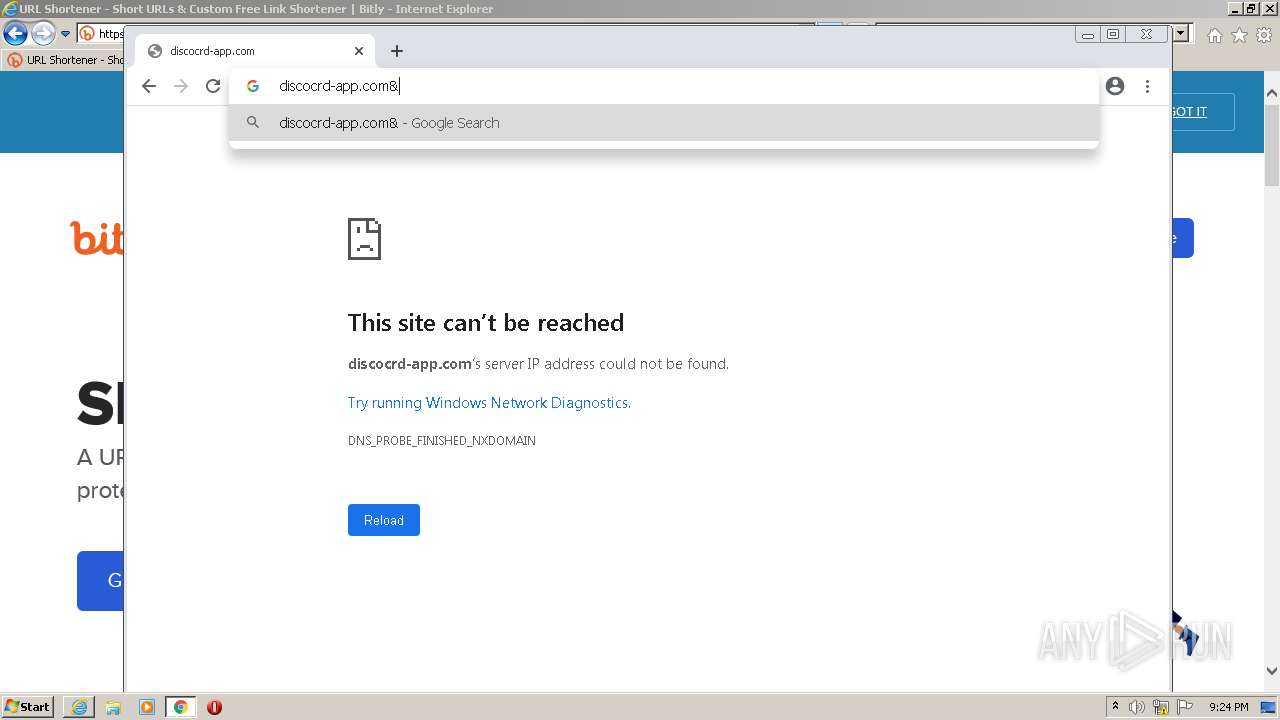
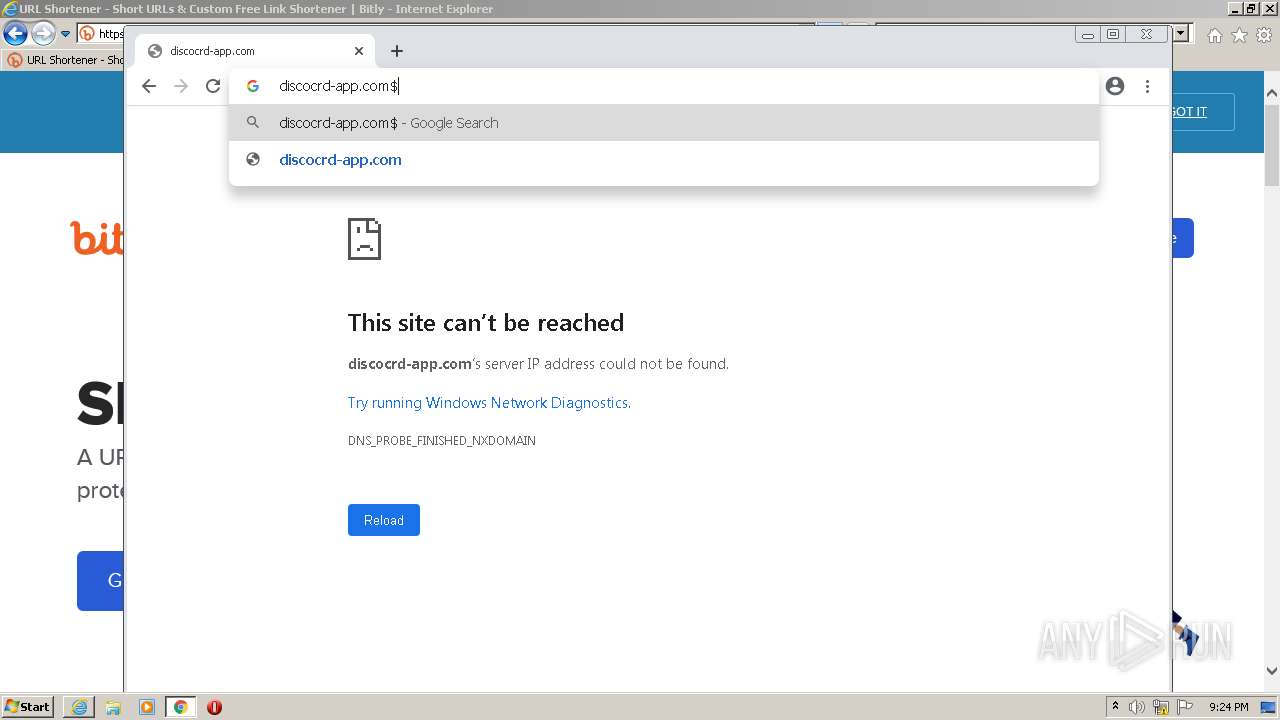
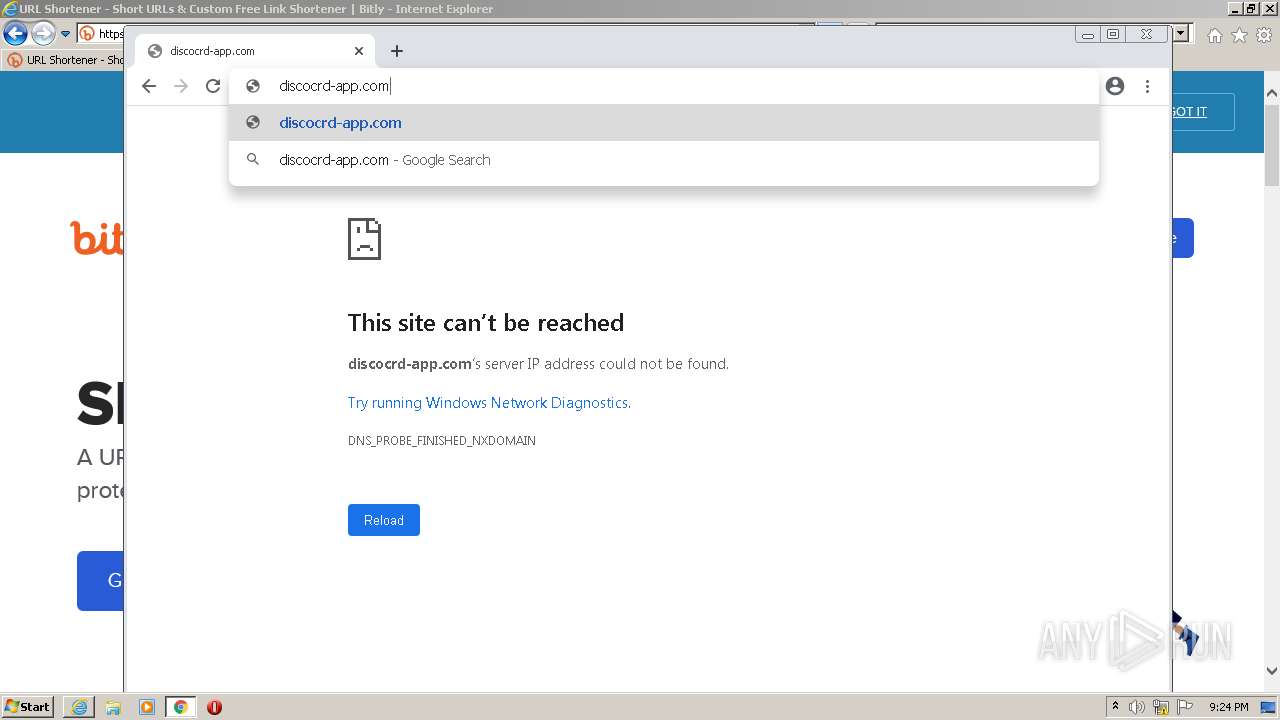
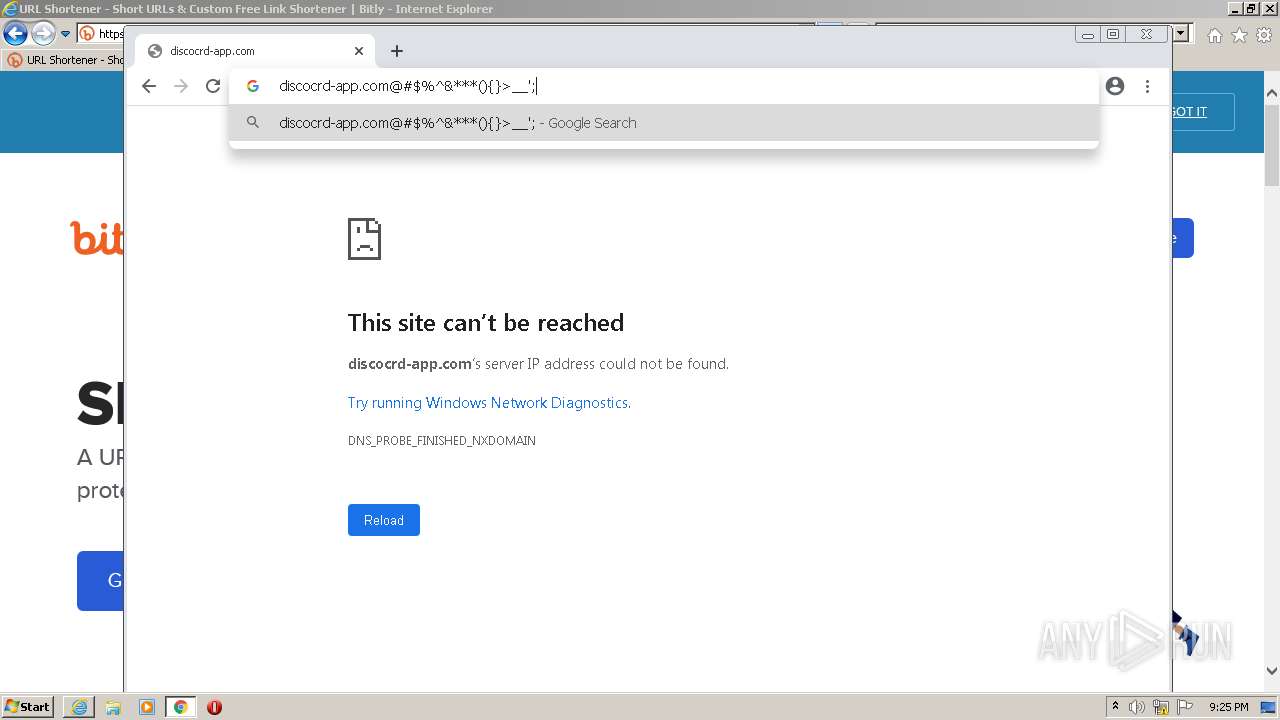
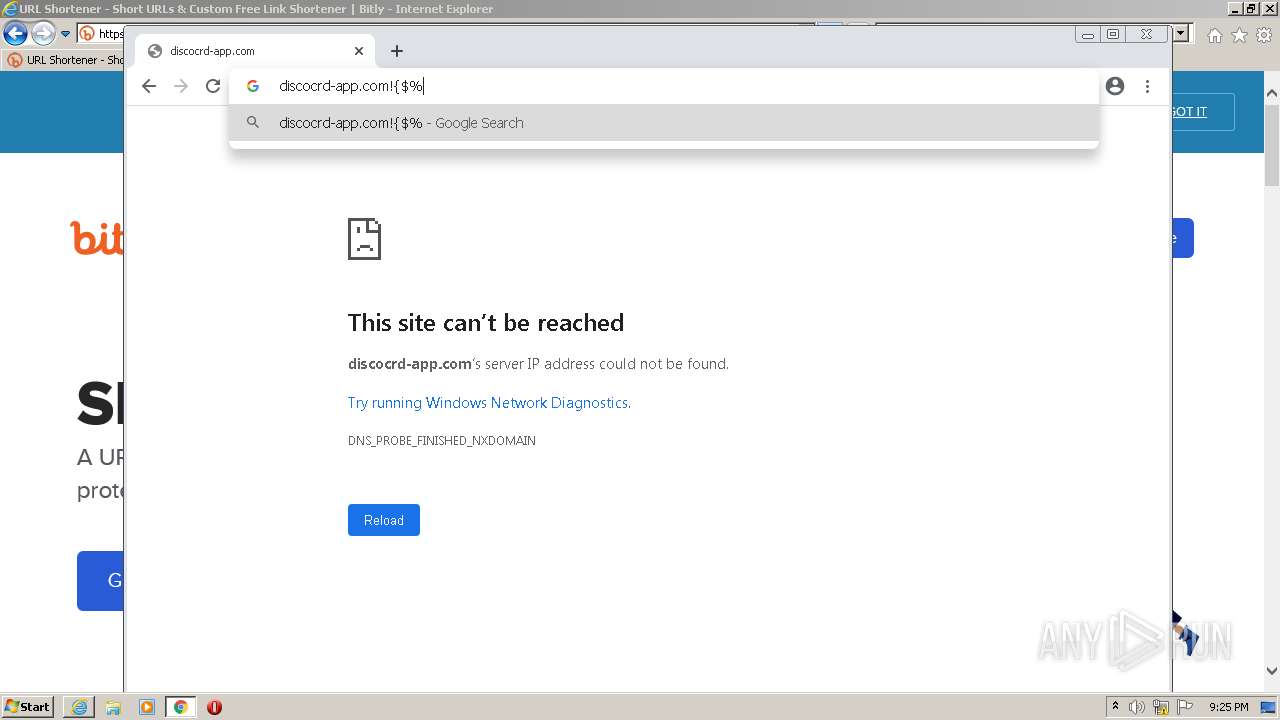
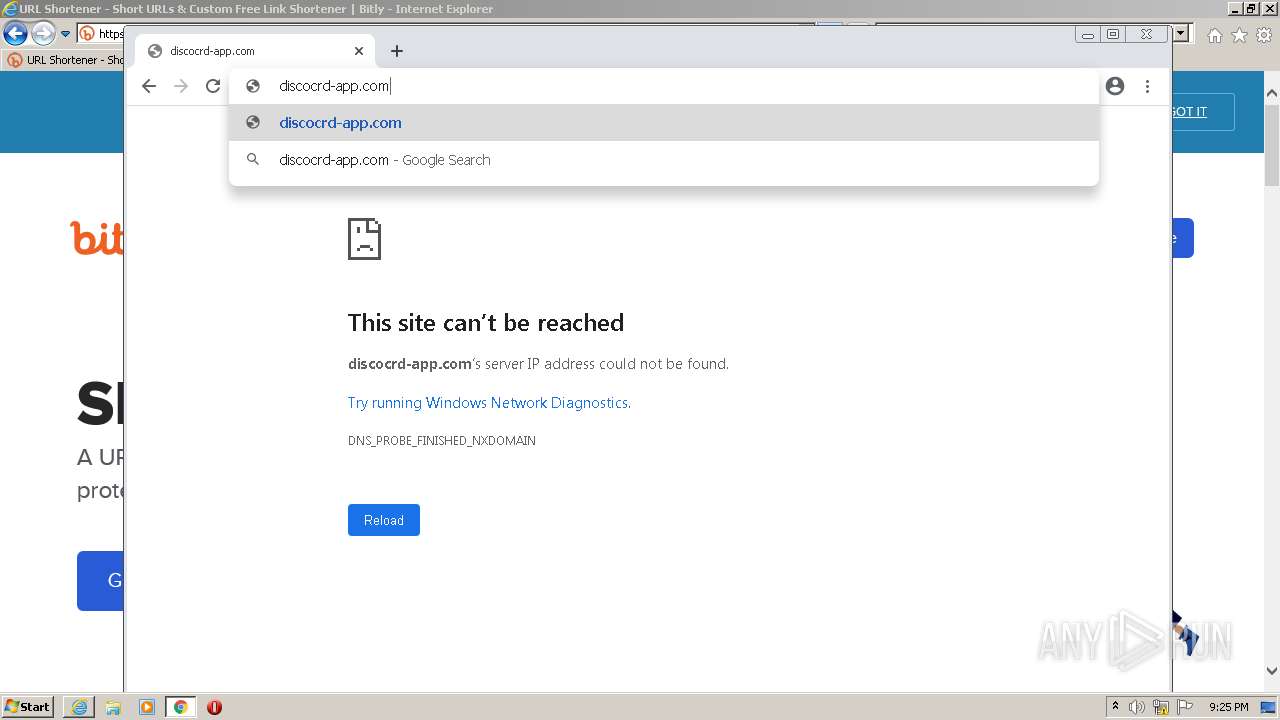
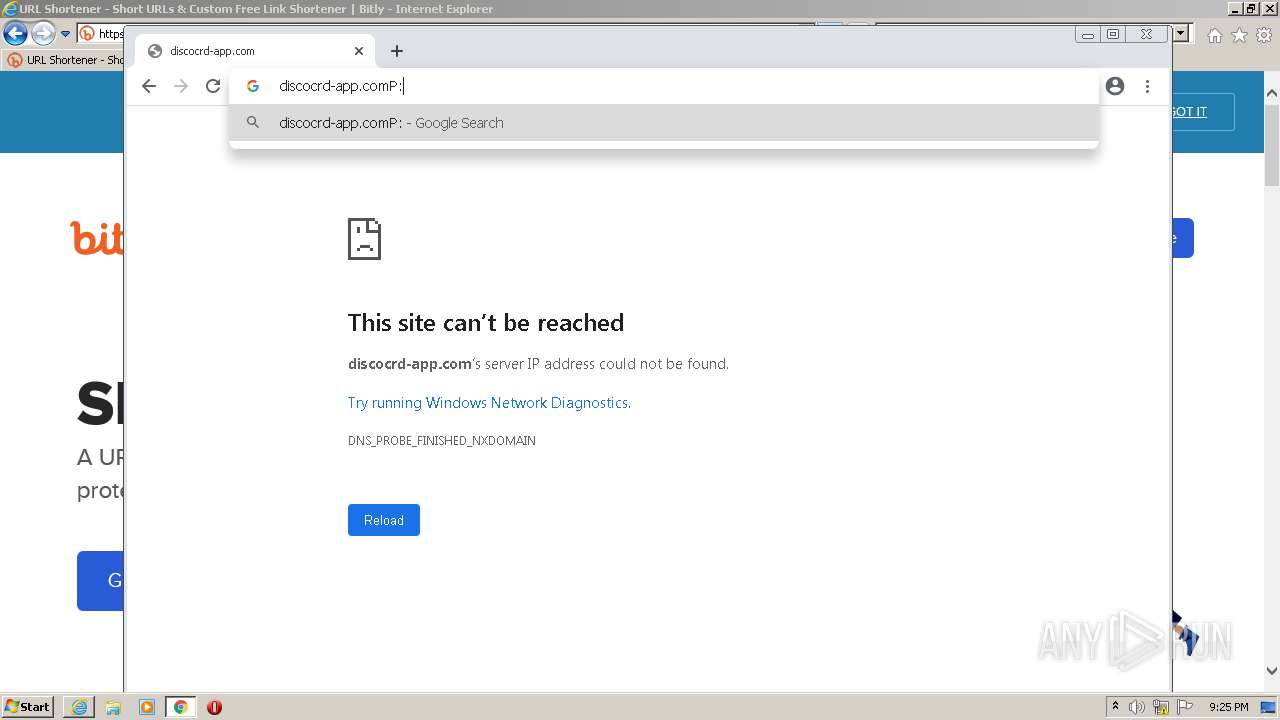
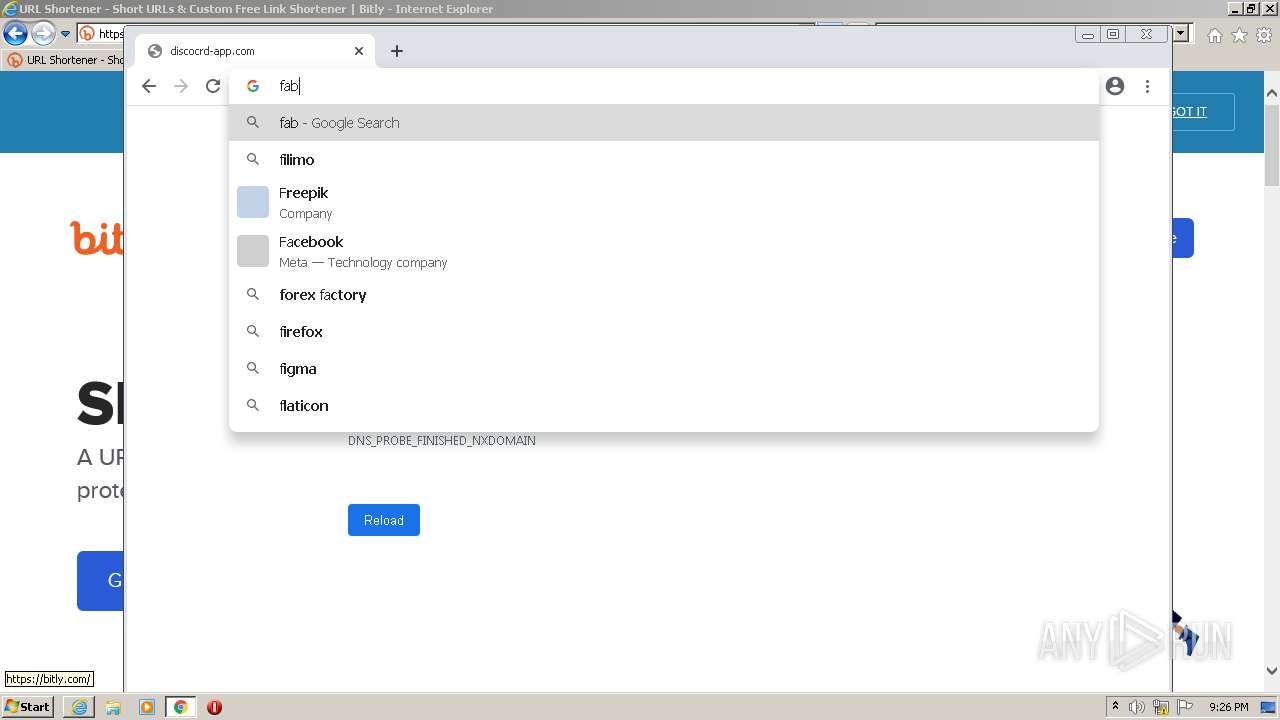
| URL: | http://discocrd-app.com/nitro |
| Full analysis: | https://app.any.run/tasks/5993af2d-bda4-4d9a-b01b-2d8a78b88df1 |
| Verdict: | Malicious activity |
| Analysis date: | July 06, 2022, 20:23:49 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 62336F466D9C167BE2B995BC95D272D0 |
| SHA1: | 3999F6466747B4397021FC1E2FE23E598F3B416A |
| SHA256: | CC8C52F26A898545B510A7B58B92D3B4F788BDDD314074F6636FA65C0E46AFAA |
| SSDEEP: | 3:N1KaMWdGRdua:CaXEXua |
MALICIOUS
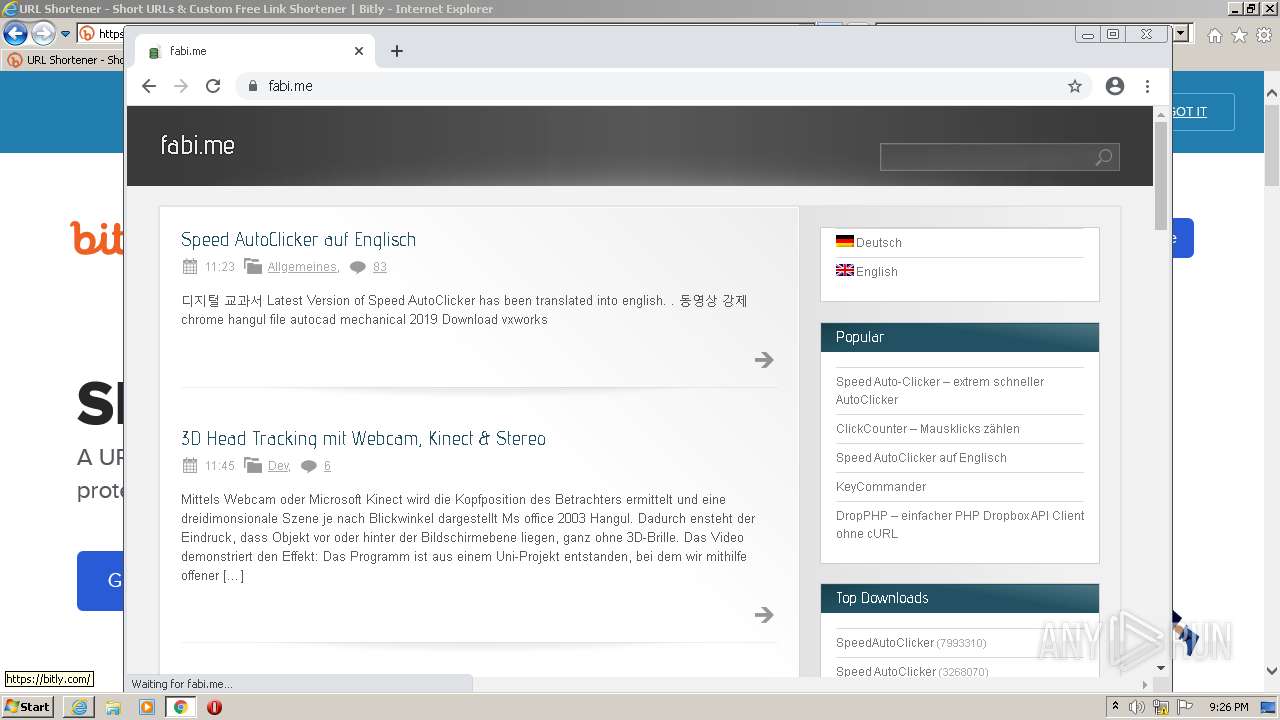
Drops executable file immediately after starts
- chrome.exe (PID: 3896)
SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3332)
Modifies files in Chrome extension folder
- chrome.exe (PID: 2660)
Drops a file with a compile date too recent
- chrome.exe (PID: 3896)
Executable content was dropped or overwritten
- chrome.exe (PID: 3896)
INFO
Checks supported languages
- iexplore.exe (PID: 2876)
- iexplore.exe (PID: 3332)
- chrome.exe (PID: 2660)
- chrome.exe (PID: 3428)
- chrome.exe (PID: 2020)
- chrome.exe (PID: 3904)
- chrome.exe (PID: 4064)
- chrome.exe (PID: 2116)
- chrome.exe (PID: 2132)
- chrome.exe (PID: 1968)
- chrome.exe (PID: 3416)
- chrome.exe (PID: 3988)
- chrome.exe (PID: 3540)
- chrome.exe (PID: 1828)
- chrome.exe (PID: 3004)
- chrome.exe (PID: 3136)
- chrome.exe (PID: 2712)
- chrome.exe (PID: 2076)
- chrome.exe (PID: 3396)
- chrome.exe (PID: 1928)
- chrome.exe (PID: 1884)
- chrome.exe (PID: 1856)
- chrome.exe (PID: 2980)
- chrome.exe (PID: 1596)
- chrome.exe (PID: 2800)
- chrome.exe (PID: 2544)
- chrome.exe (PID: 3004)
- chrome.exe (PID: 1856)
- chrome.exe (PID: 2712)
- chrome.exe (PID: 3180)
- chrome.exe (PID: 2012)
- chrome.exe (PID: 3768)
- chrome.exe (PID: 2832)
- chrome.exe (PID: 2756)
- chrome.exe (PID: 2752)
- chrome.exe (PID: 3896)
- chrome.exe (PID: 2348)
- chrome.exe (PID: 2524)
- chrome.exe (PID: 2848)
- chrome.exe (PID: 1000)
- chrome.exe (PID: 2096)
- chrome.exe (PID: 672)
- chrome.exe (PID: 2552)
- chrome.exe (PID: 2376)
- chrome.exe (PID: 2108)
- chrome.exe (PID: 3020)
- chrome.exe (PID: 3644)
- chrome.exe (PID: 3536)
- chrome.exe (PID: 3292)
- chrome.exe (PID: 1600)
- chrome.exe (PID: 3156)
- chrome.exe (PID: 1836)
- chrome.exe (PID: 1848)
- chrome.exe (PID: 3836)
Reads the computer name
- iexplore.exe (PID: 2876)
- iexplore.exe (PID: 3332)
- chrome.exe (PID: 2660)
- chrome.exe (PID: 2020)
- chrome.exe (PID: 3904)
- chrome.exe (PID: 2132)
- chrome.exe (PID: 3396)
- chrome.exe (PID: 1596)
- chrome.exe (PID: 3004)
- chrome.exe (PID: 2800)
- chrome.exe (PID: 1848)
Application launched itself
- iexplore.exe (PID: 2876)
- chrome.exe (PID: 2660)
Changes internet zones settings
- iexplore.exe (PID: 2876)
Reads settings of System Certificates
- iexplore.exe (PID: 3332)
- chrome.exe (PID: 3904)
- iexplore.exe (PID: 2876)
Reads internet explorer settings
- iexplore.exe (PID: 3332)
Manual execution by user
- chrome.exe (PID: 2660)
Reads the hosts file
- chrome.exe (PID: 2660)
- chrome.exe (PID: 3904)
Checks Windows Trust Settings
- iexplore.exe (PID: 3332)
- iexplore.exe (PID: 2876)
Creates files in the user directory
- iexplore.exe (PID: 3332)
- iexplore.exe (PID: 2876)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2876)
Changes settings of System certificates
- iexplore.exe (PID: 2876)
Reads the date of Windows installation
- chrome.exe (PID: 3004)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
91
Monitored processes
54
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 672 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1020,17775649781548946282,4093554849767185399,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3380 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1000 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1020,17775649781548946282,4093554849767185399,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2964 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1596 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1020,17775649781548946282,4093554849767185399,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=1828 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1600 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,17775649781548946282,4093554849767185399,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=48 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3740 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1828 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1020,17775649781548946282,4093554849767185399,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2856 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1836 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,17775649781548946282,4093554849767185399,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=49 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2828 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1848 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1020,17775649781548946282,4093554849767185399,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=2240 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1856 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,17775649781548946282,4093554849767185399,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=19 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2172 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1856 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,17775649781548946282,4093554849767185399,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=23 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1716 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1884 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,17775649781548946282,4093554849767185399,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=18 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2816 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
30 966
Read events
30 545
Write events
409
Delete events
12
Modification events
| (PID) Process: | (2876) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (2876) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (2876) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30970230 | |||
| (PID) Process: | (2876) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (2876) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30970230 | |||
| (PID) Process: | (2876) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2876) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2876) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2876) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2876) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
1
Suspicious files
208
Text files
318
Unknown types
55
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3332 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 3332 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | binary | |
MD5:— | SHA256:— | |||
| 3332 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\007DGE43.txt | text | |
MD5:— | SHA256:— | |||
| 3332 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | der | |
MD5:— | SHA256:— | |||
| 3332 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\N02F2OM6.txt | text | |
MD5:— | SHA256:— | |||
| 3332 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\MLO7IULD.txt | text | |
MD5:— | SHA256:— | |||
| 3332 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\0QGHIG4S.txt | text | |
MD5:— | SHA256:— | |||
| 3332 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\Q4Z6RJMF.txt | text | |
MD5:— | SHA256:— | |||
| 3332 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\RG7LWWDI.txt | text | |
MD5:— | SHA256:— | |||
| 3332 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\RH8CX3MS.txt | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
76
TCP/UDP connections
159
DNS requests
79
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3332 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
3332 | iexplore.exe | GET | 200 | 65.9.58.231:80 | http://o.ss2.us//MEowSDBGMEQwQjAJBgUrDgMCGgUABBSLwZ6EW5gdYc9UaSEaaLjjETNtkAQUv1%2B30c7dH4b0W1Ws3NcQwg6piOcCCQCnDkpMNIK3fw%3D%3D | US | der | 1.70 Kb | whitelisted |
3332 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
3332 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEATh56TcXPLzbcArQrhdFZ8%3D | US | der | 471 b | whitelisted |
2876 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
3332 | iexplore.exe | GET | 200 | 142.250.185.195:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | der | 724 b | whitelisted |
3332 | iexplore.exe | GET | 200 | 142.250.185.195:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | der | 1.41 Kb | whitelisted |
3332 | iexplore.exe | GET | 200 | 142.250.185.195:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIAjrICMzZli2TN25s%3D | US | der | 724 b | whitelisted |
3332 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAH9o%2BtuynXIiEOLckvPvJE%3D | US | der | 471 b | whitelisted |
3332 | iexplore.exe | GET | 200 | 142.250.185.195:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEGH3yVmK41sICps0i8Jf%2BP4%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3904 | chrome.exe | 142.250.185.110:443 | clients2.google.com | Google Inc. | US | whitelisted |
3904 | chrome.exe | 142.250.185.109:443 | accounts.google.com | Google Inc. | US | suspicious |
3904 | chrome.exe | 172.217.18.99:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3904 | chrome.exe | 216.58.212.161:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
3332 | iexplore.exe | 143.204.214.48:443 | docrdsfx76ssb.cloudfront.net | — | US | unknown |
— | — | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
2876 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
3332 | iexplore.exe | 13.107.5.80:443 | api.bing.com | Microsoft Corporation | US | whitelisted |
3332 | iexplore.exe | 41.63.96.0:80 | ctldl.windowsupdate.com | Limelight Networks, Inc. | ZA | suspicious |
3332 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
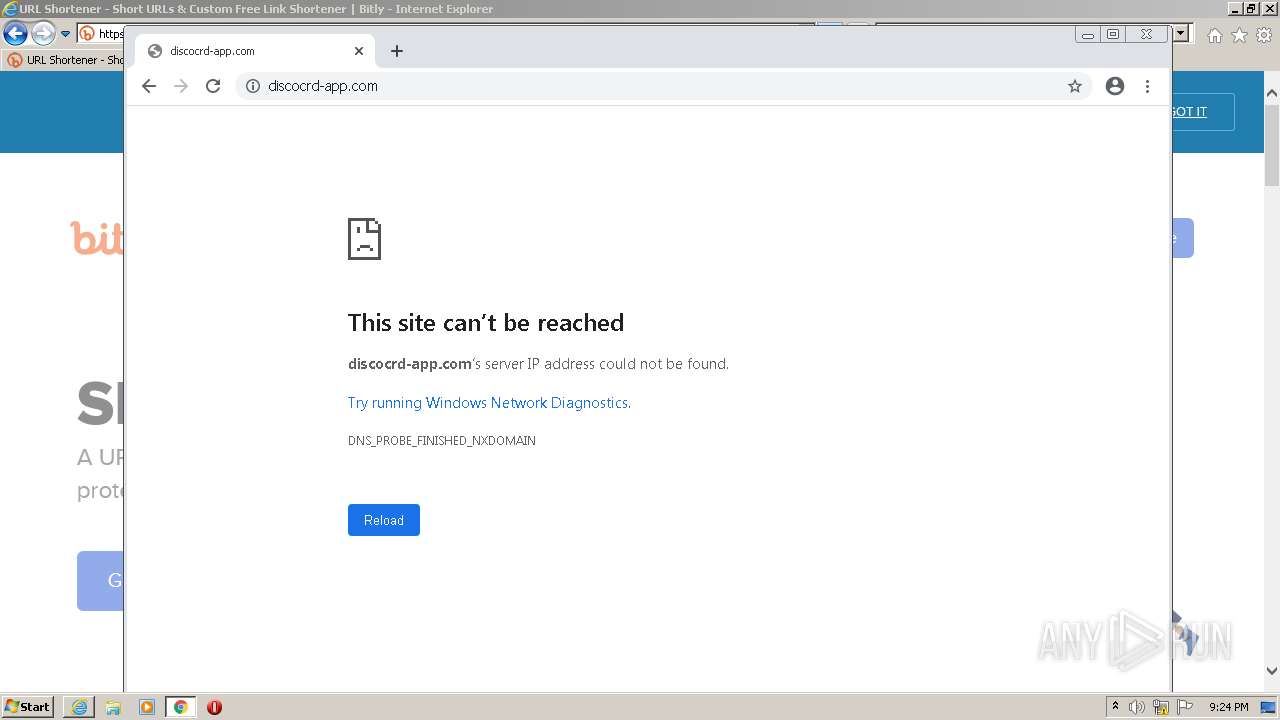
discocrd-app.com |
| unknown |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
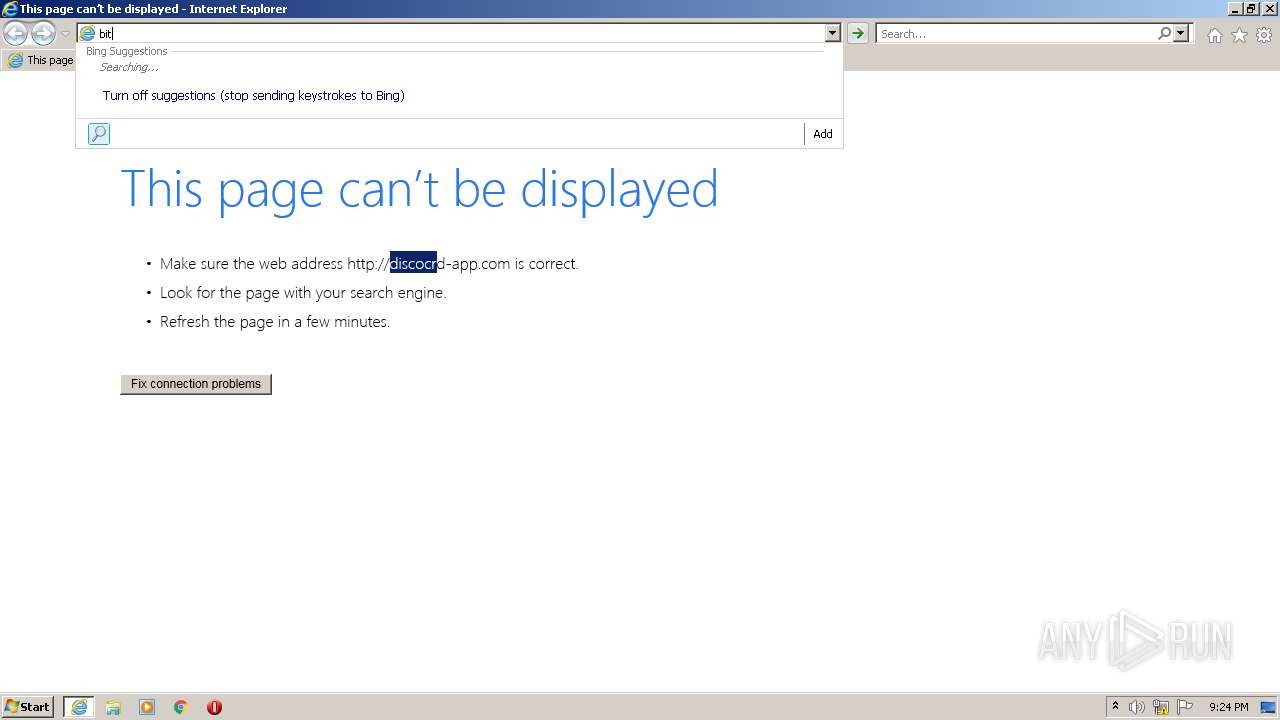
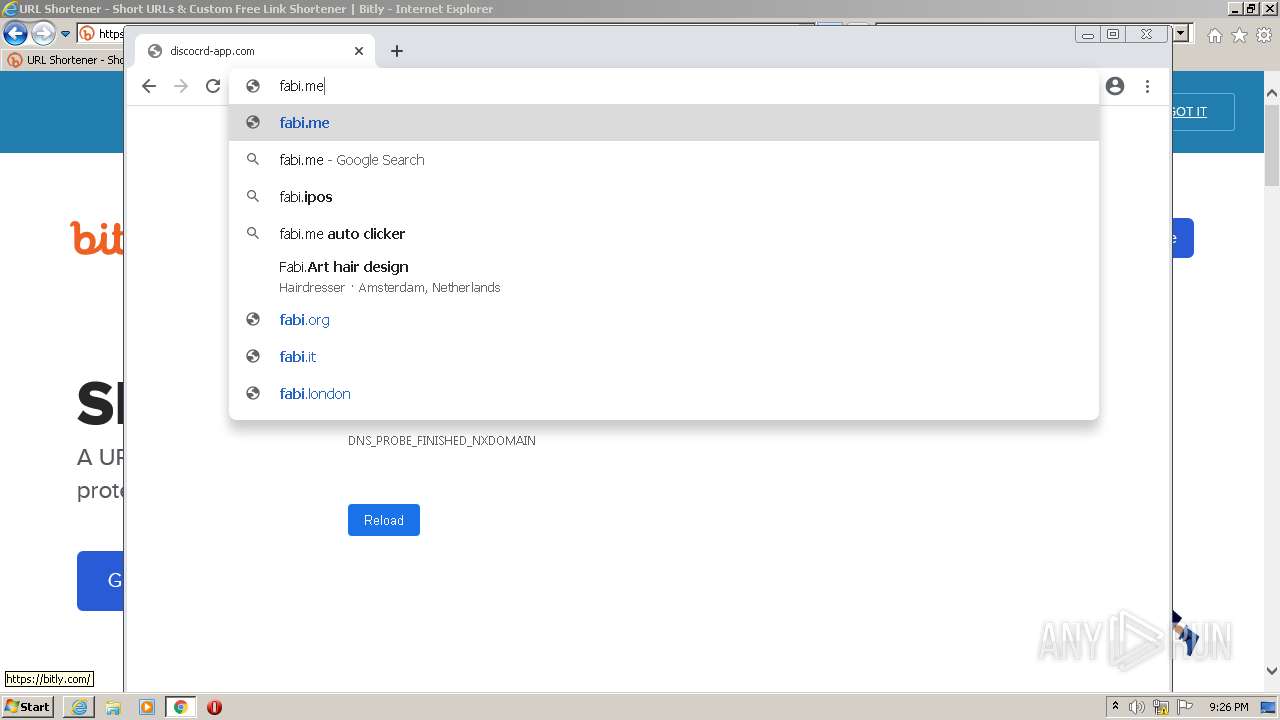
bit.ly |
| shared |
bitly.com |
| shared |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3332 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
3332 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
3332 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
3332 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |