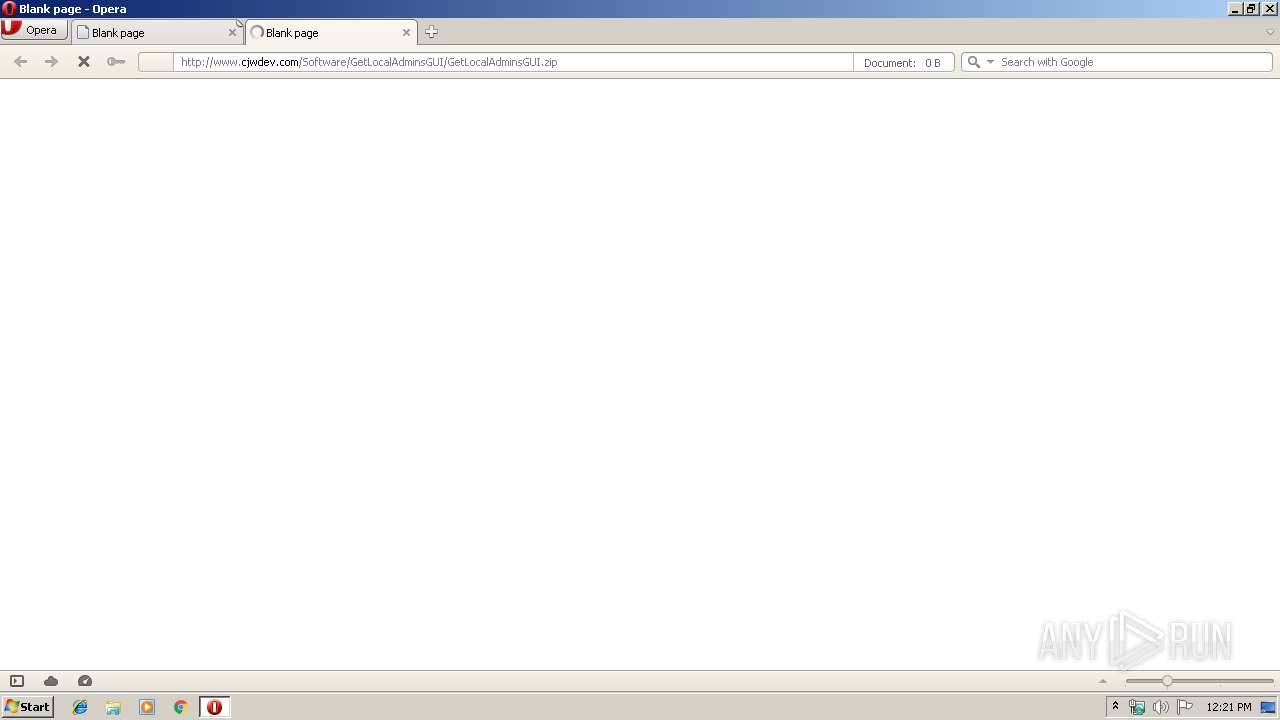
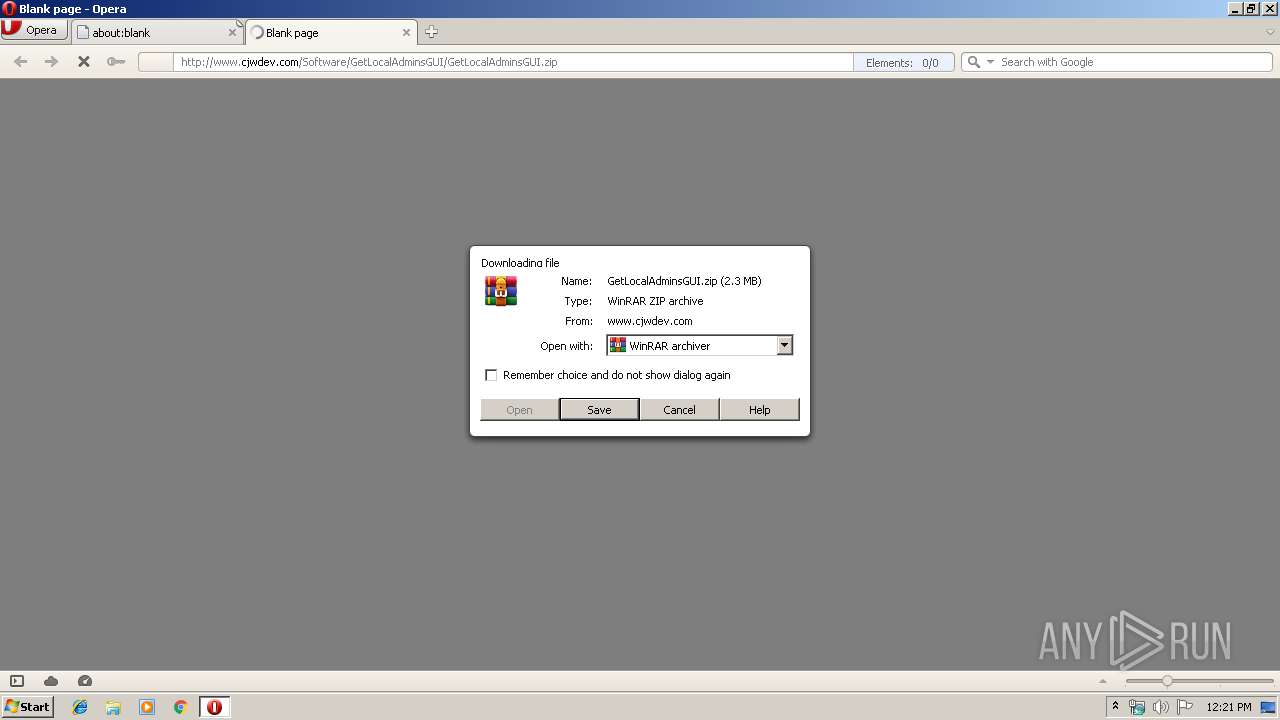
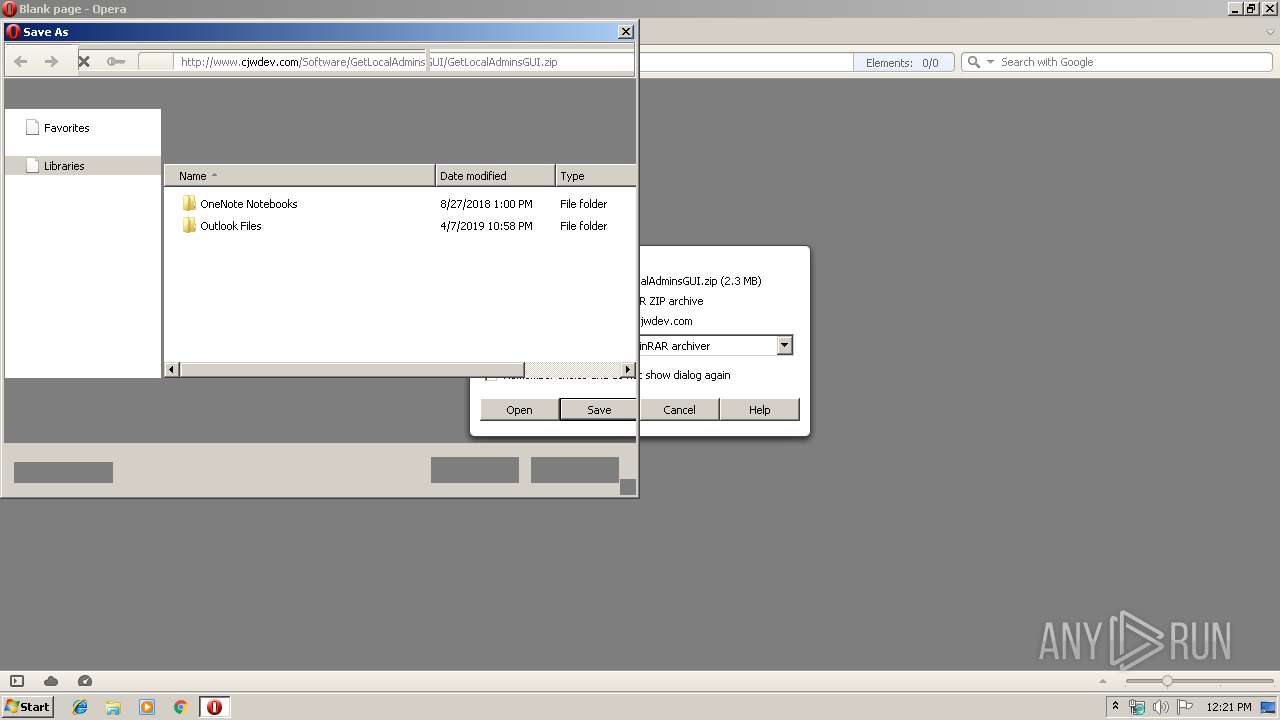
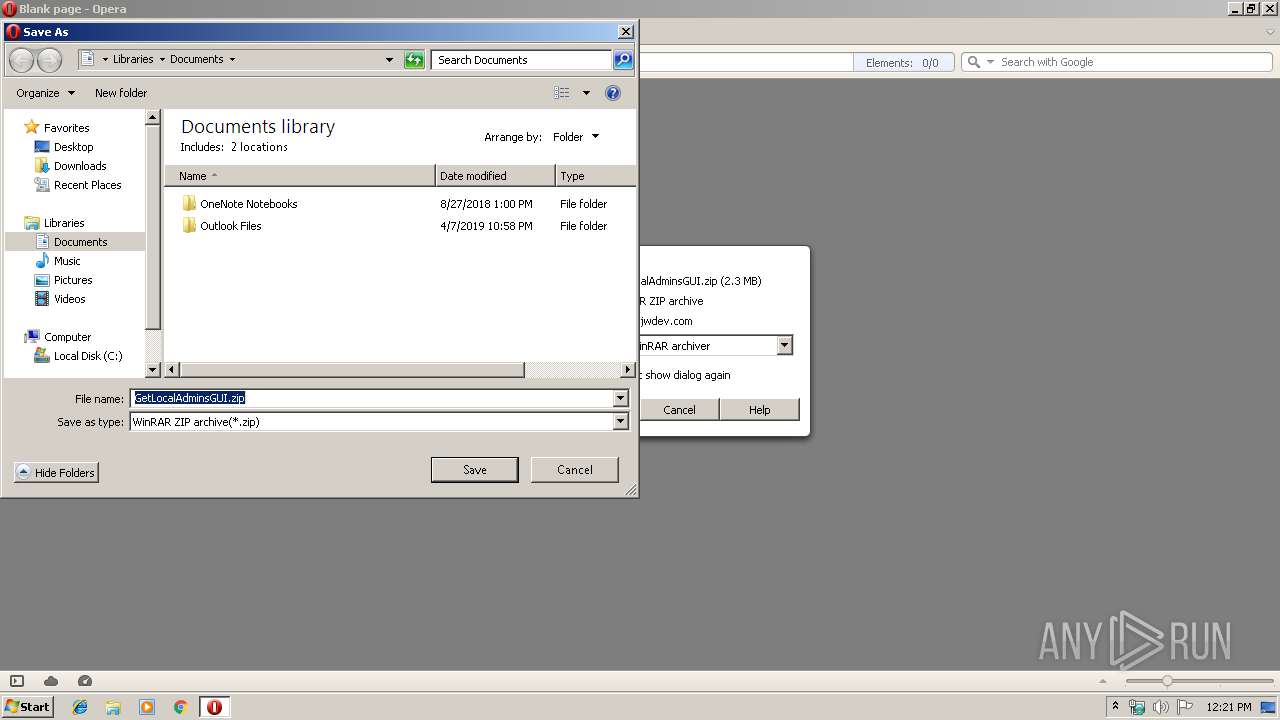
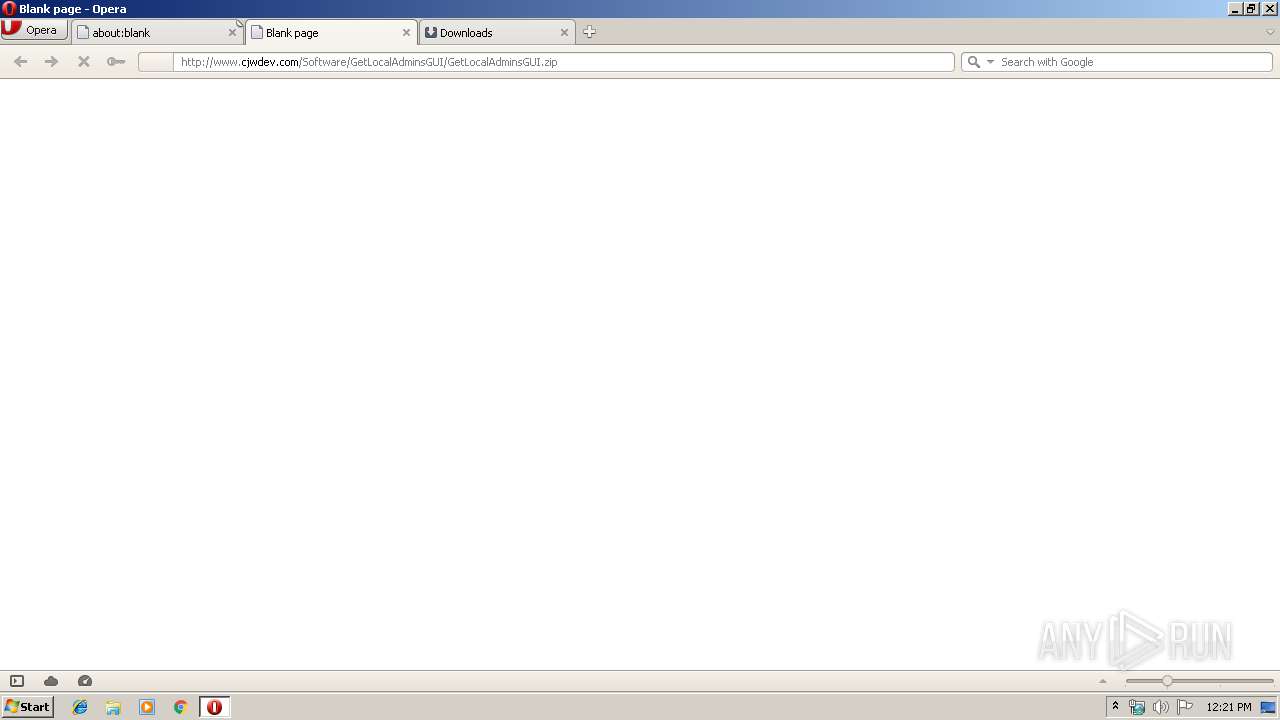
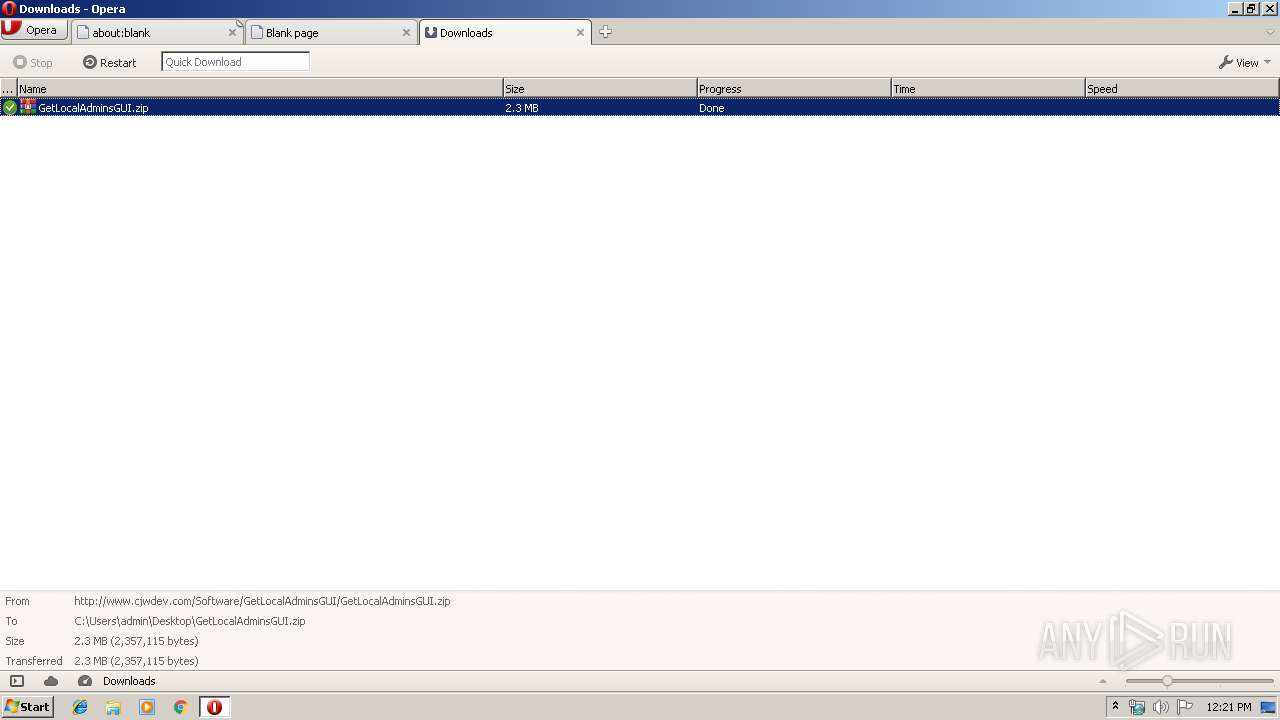
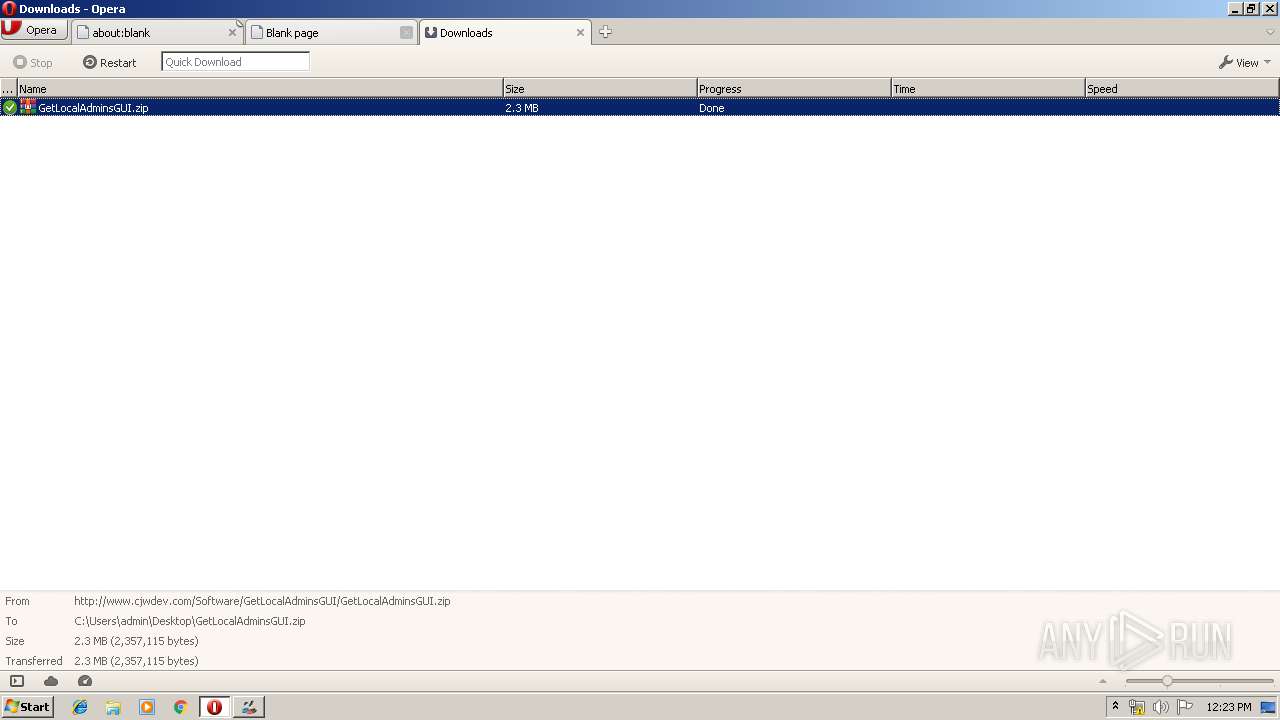
| URL: | http://www.cjwdev.com/Software/GetLocalAdminsGUI/GetLocalAdminsGUI.zip |
| Full analysis: | https://app.any.run/tasks/a33aeb2c-c502-454f-a2cb-8c34f5f8a14f |
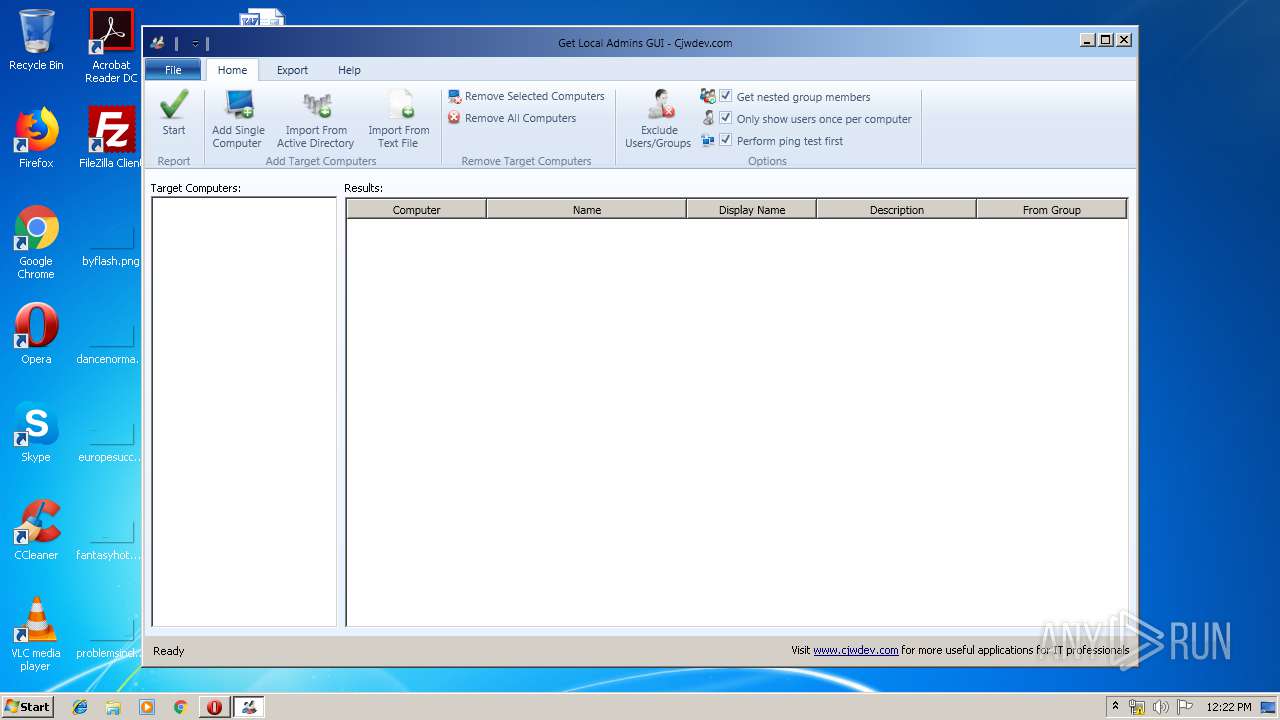
| Verdict: | Malicious activity |
| Analysis date: | June 19, 2019, 11:20:51 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 8E5EEC4D19DC46850F3AC3EDAF519D7B |
| SHA1: | EE50C9771F8A9F24D793814A5FBA89726FC58D71 |
| SHA256: | CC84210F35F467CDAF5830301A58F4CD105080AFD98FB271940F34F5D83C3A1D |
| SSDEEP: | 3:N1KJS4JsRx/YkzLqrSkzLqqc:Cc4JGxNqrXqv |
MALICIOUS
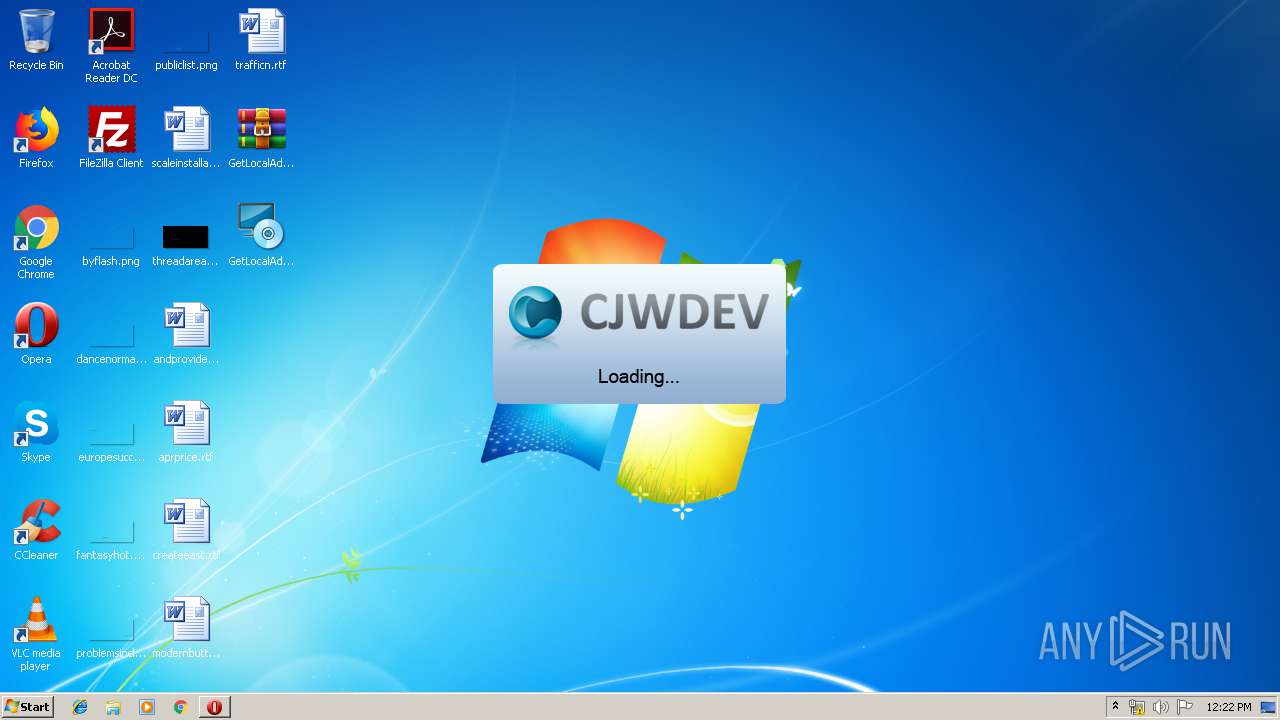
Application was dropped or rewritten from another process
- GetLocalAdminsGUISetup.exe (PID: 3000)
- GetLocalAdminsGUI.exe (PID: 2384)
Loads dropped or rewritten executable
- GetLocalAdminsGUI.exe (PID: 2384)
Loads the Task Scheduler DLL interface
- GetLocalAdminsGUISetup.exe (PID: 3000)
SUSPICIOUS
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2272)
- GetLocalAdminsGUISetup.exe (PID: 3000)
- msiexec.exe (PID: 3728)
Executed as Windows Service
- vssvc.exe (PID: 1508)
Executed via COM
- DrvInst.exe (PID: 3508)
Creates files in the user directory
- GetLocalAdminsGUISetup.exe (PID: 3000)
Reads Environment values
- GetLocalAdminsGUI.exe (PID: 2384)
INFO
Creates files in the user directory
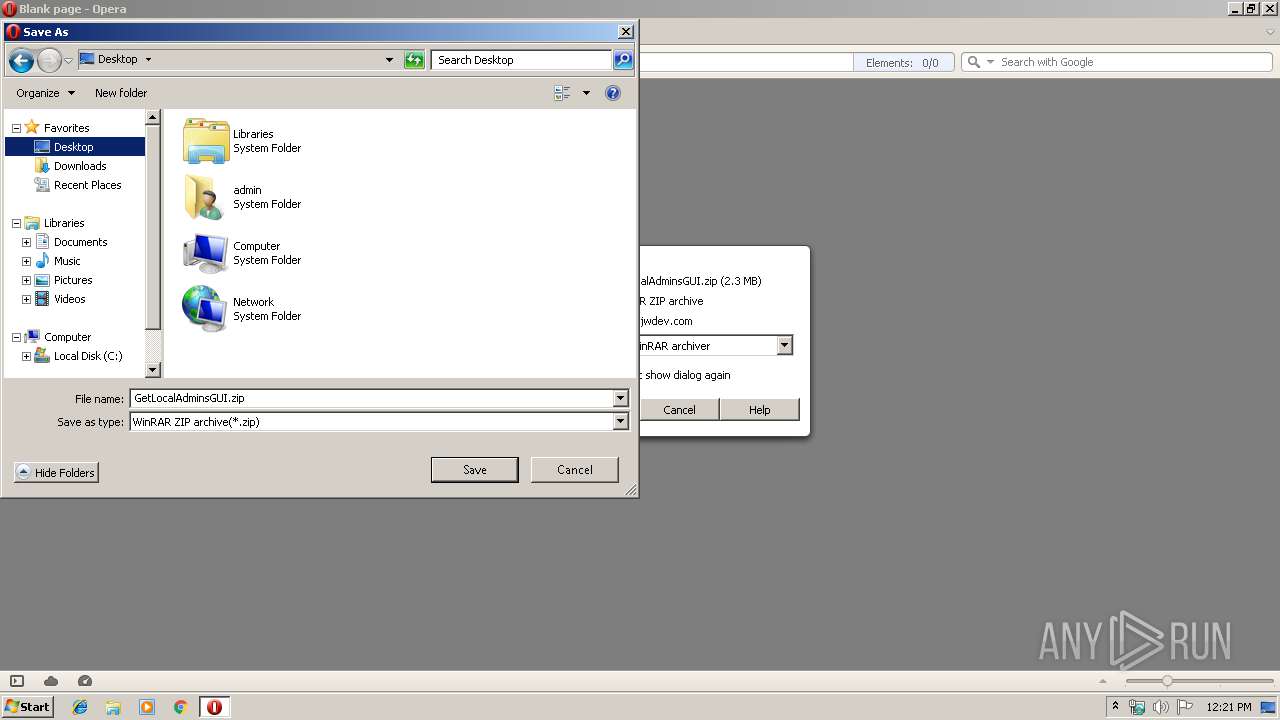
- opera.exe (PID: 2956)
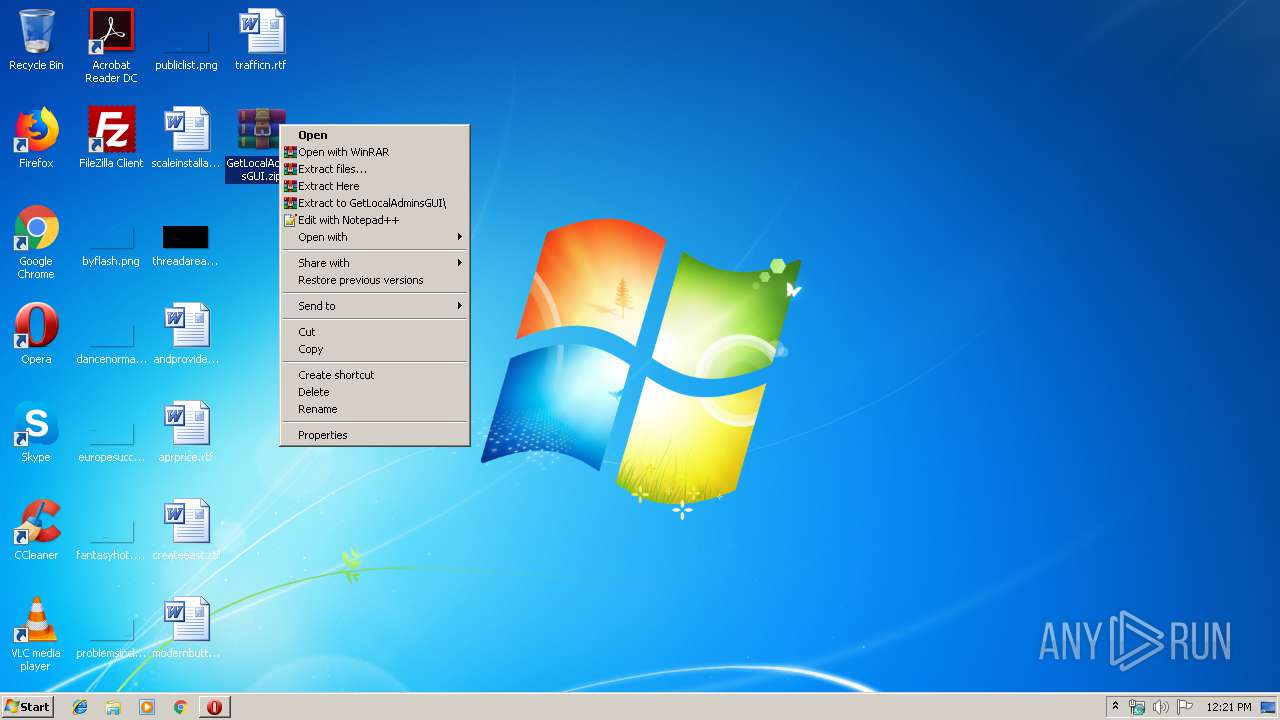
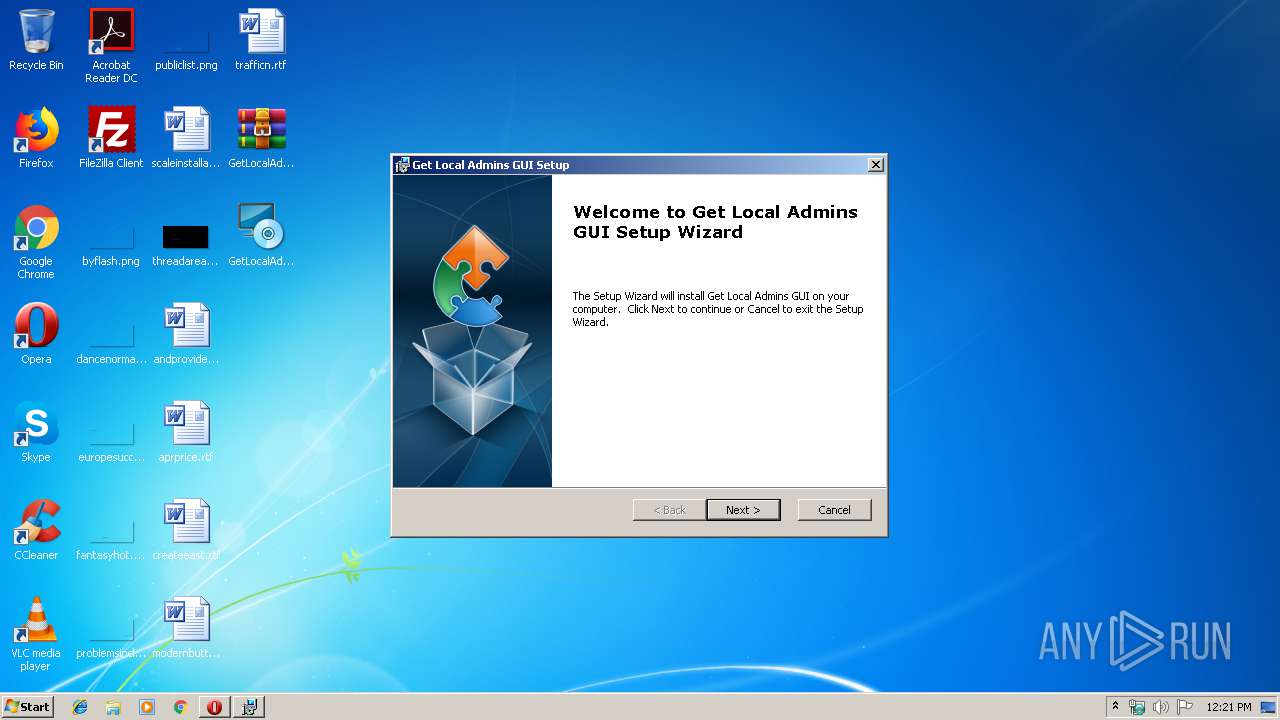
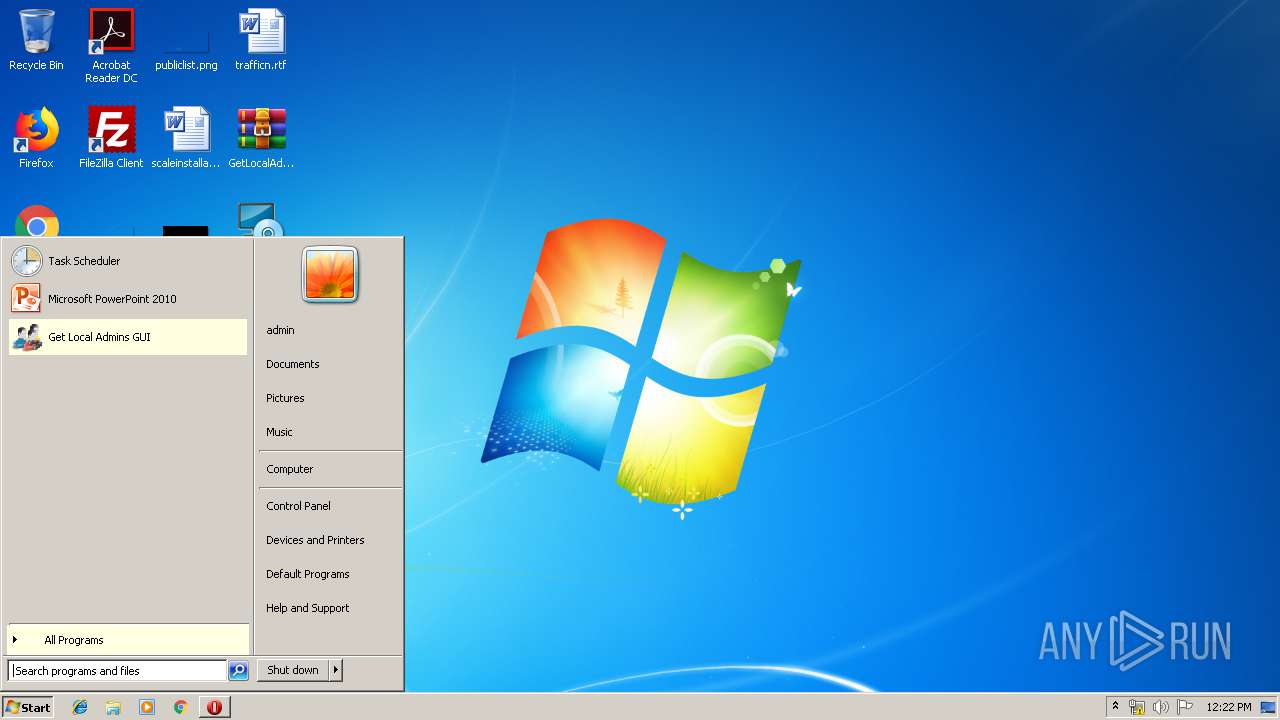
Manual execution by user
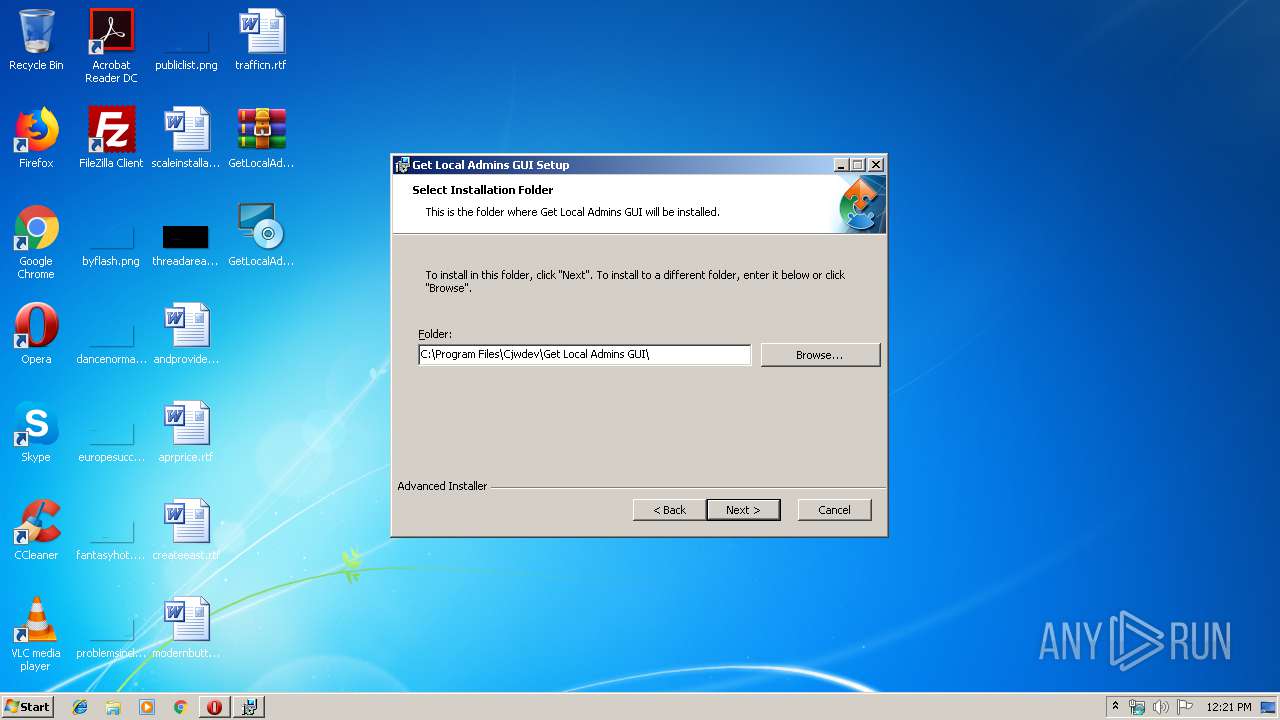
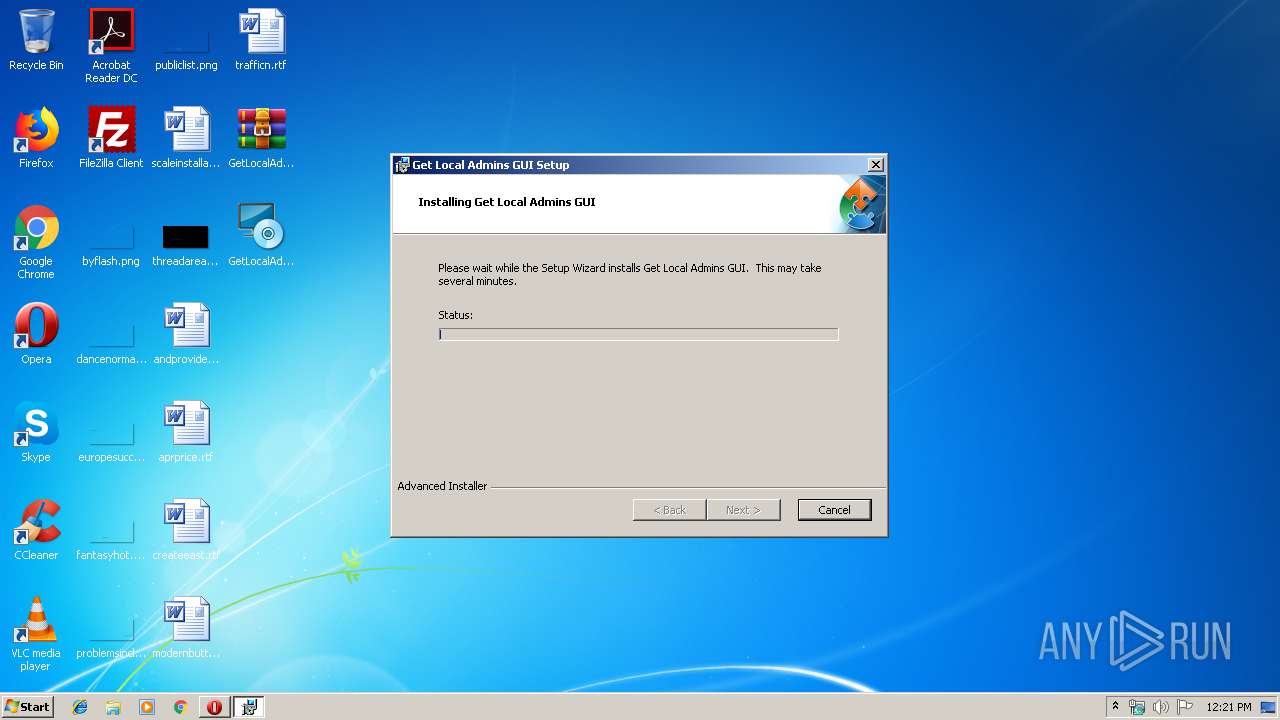
- GetLocalAdminsGUISetup.exe (PID: 3000)
- WinRAR.exe (PID: 2272)
- GetLocalAdminsGUI.exe (PID: 2384)
Searches for installed software
- msiexec.exe (PID: 3728)
Reads Internet Cache Settings
- opera.exe (PID: 2956)
Low-level read access rights to disk partition
- vssvc.exe (PID: 1508)
Changes settings of System certificates
- DrvInst.exe (PID: 3508)
Adds / modifies Windows certificates
- DrvInst.exe (PID: 3508)
Application launched itself
- msiexec.exe (PID: 3728)
Creates files in the program directory
- msiexec.exe (PID: 3728)
Creates a software uninstall entry
- msiexec.exe (PID: 3728)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
47
Monitored processes
10
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1508 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2272 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Desktop\GetLocalAdminsGUI.zip" C:\Users\admin\Desktop\ | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
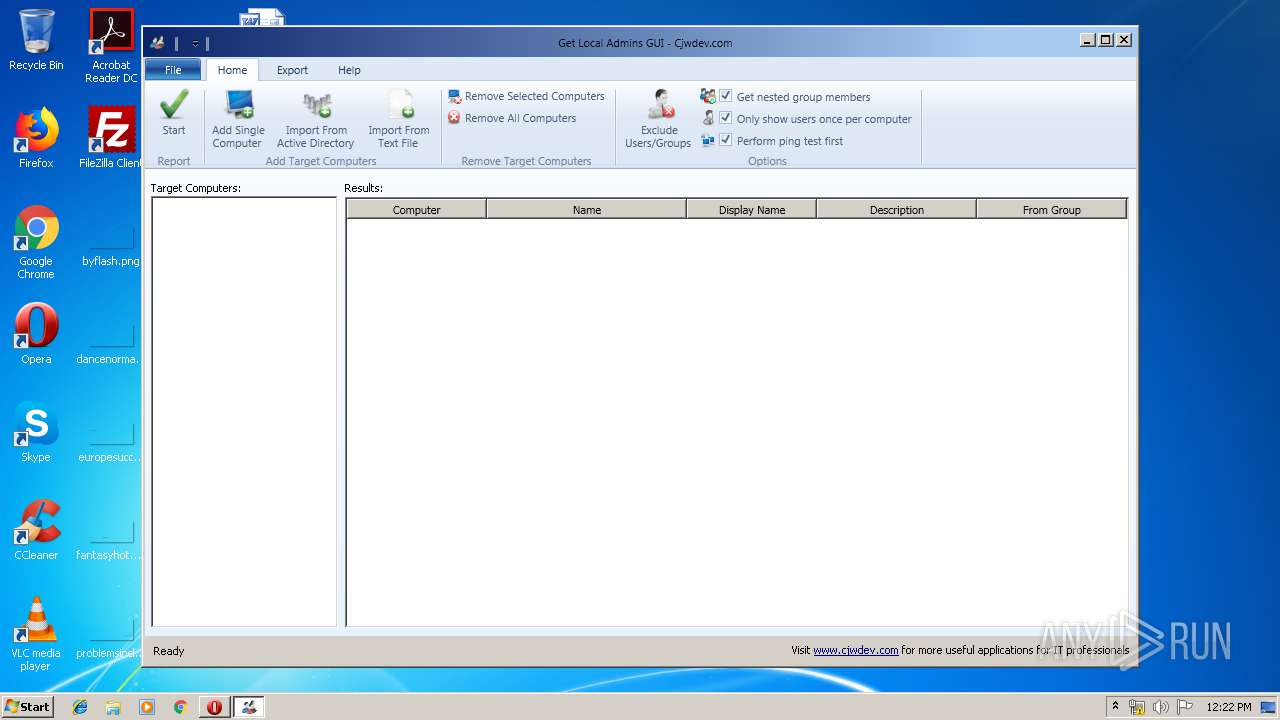
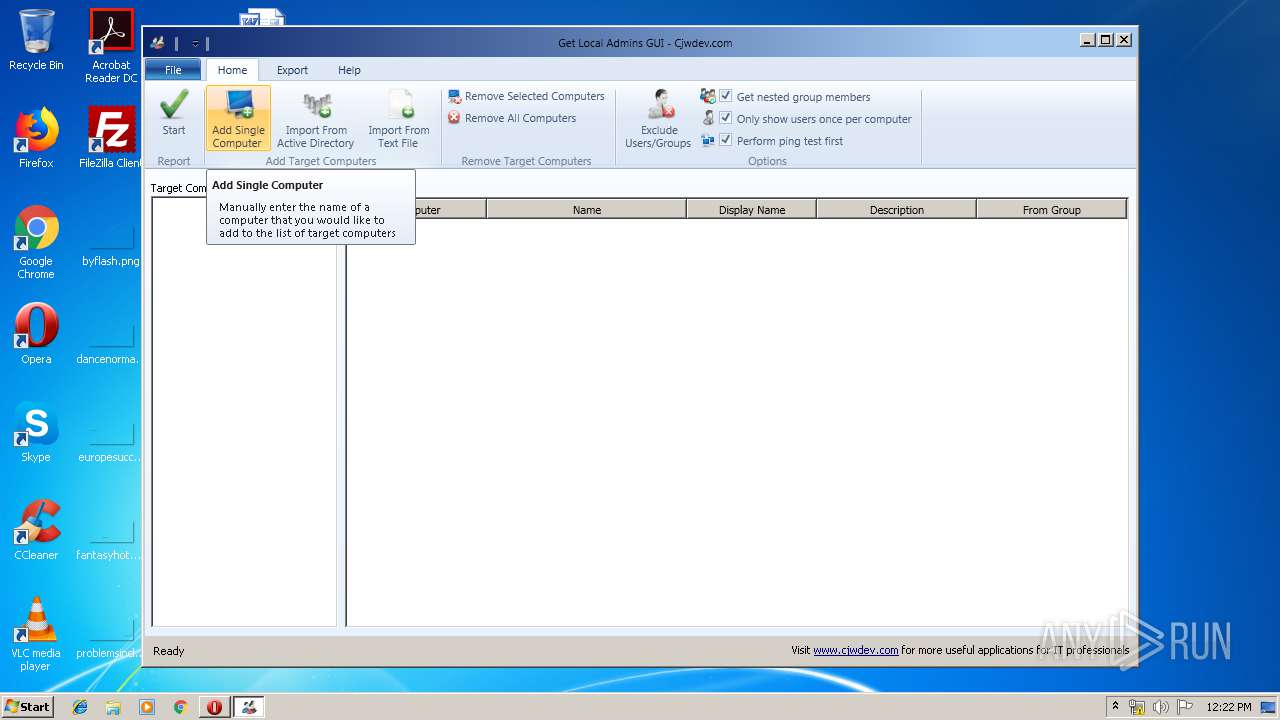
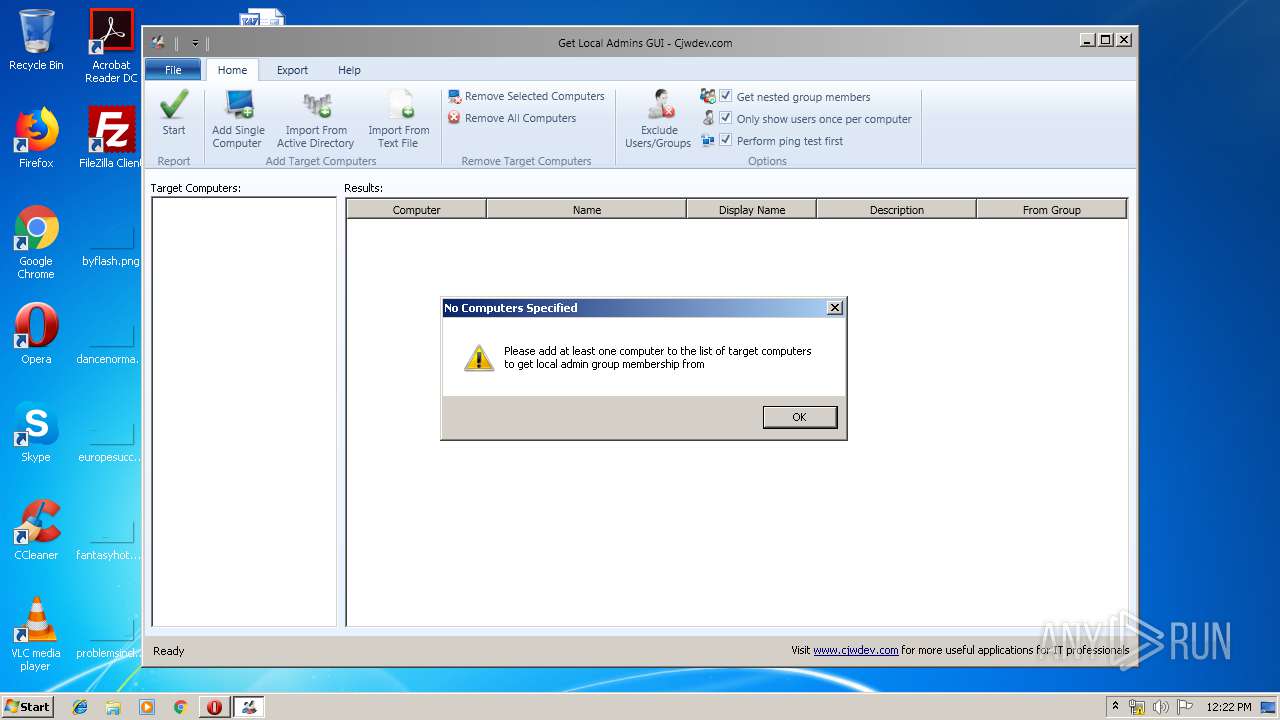
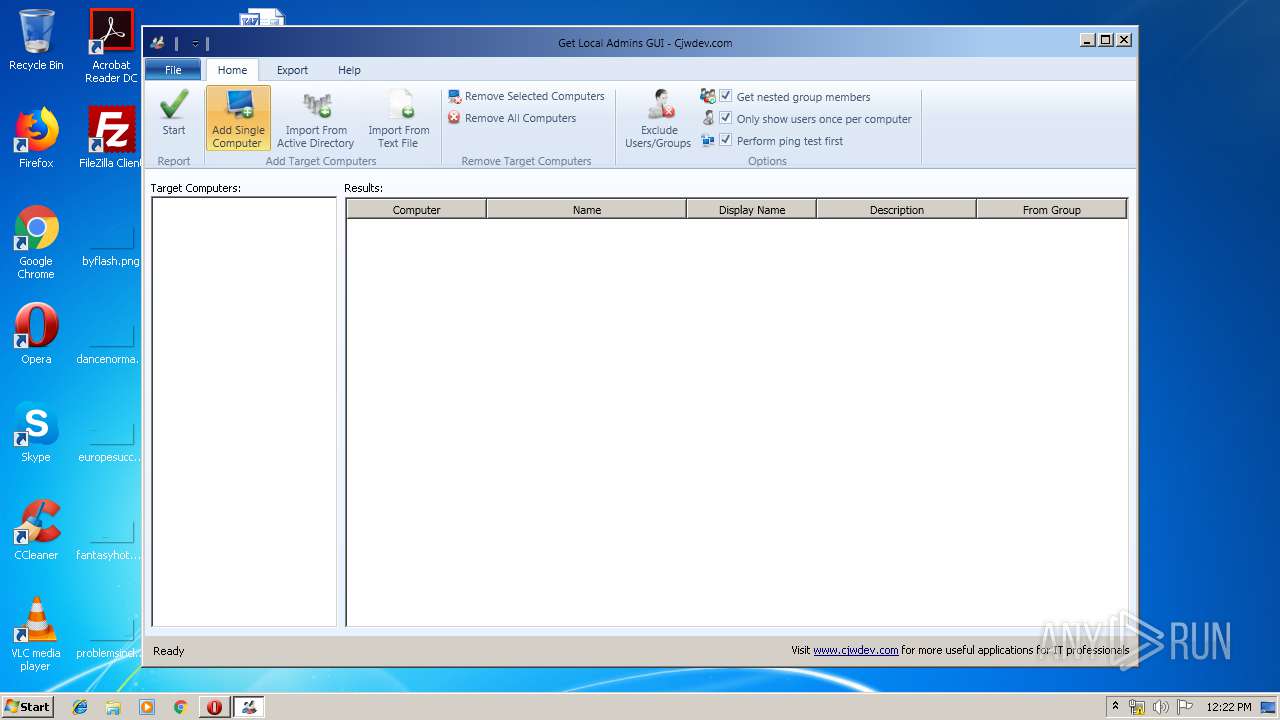
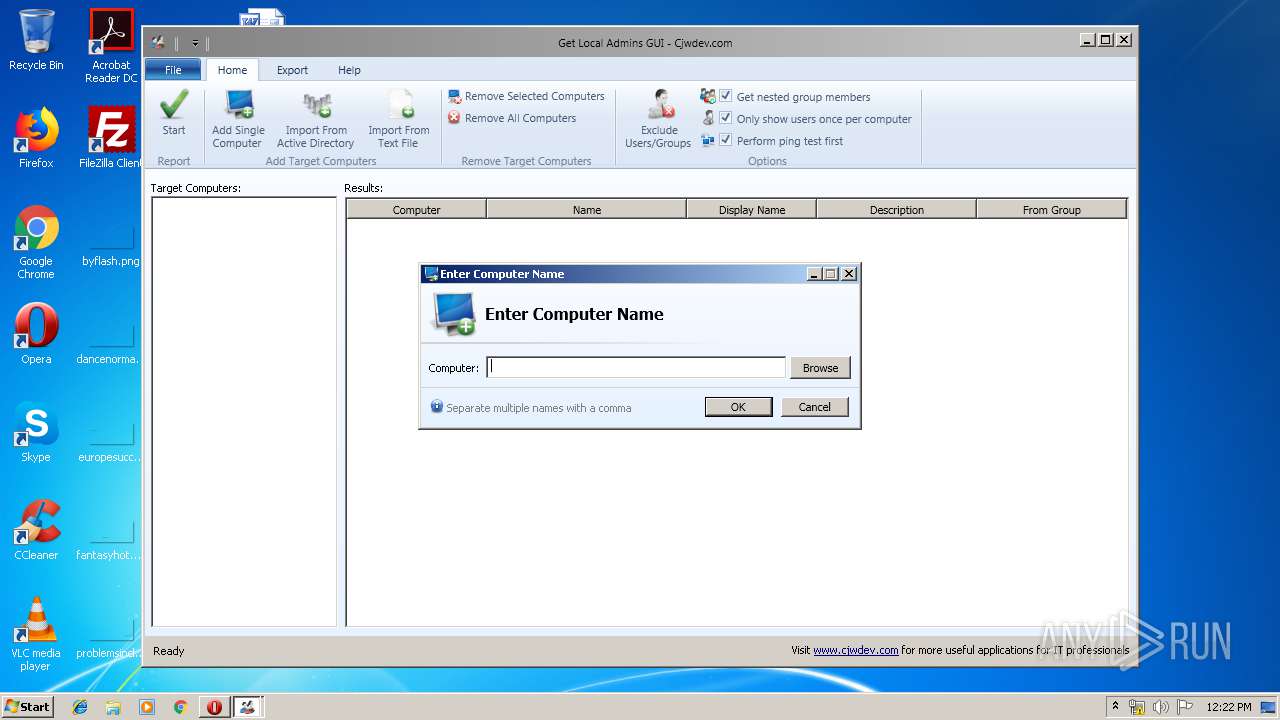
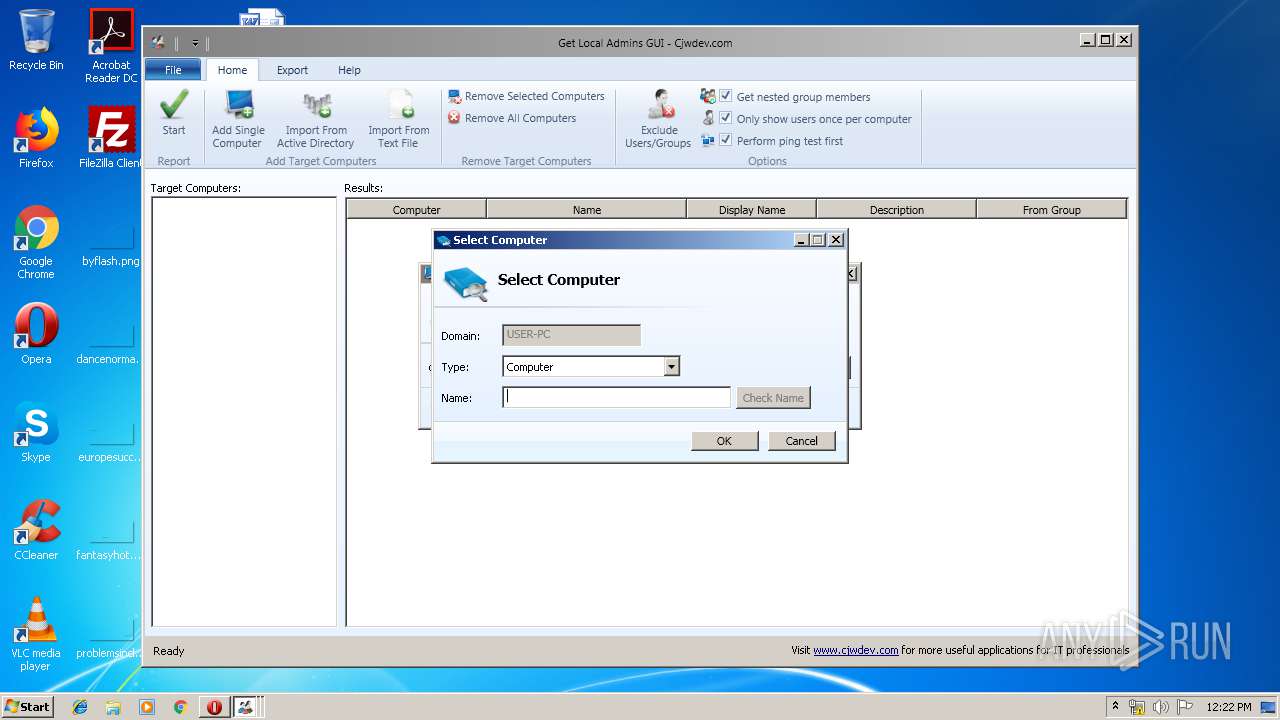
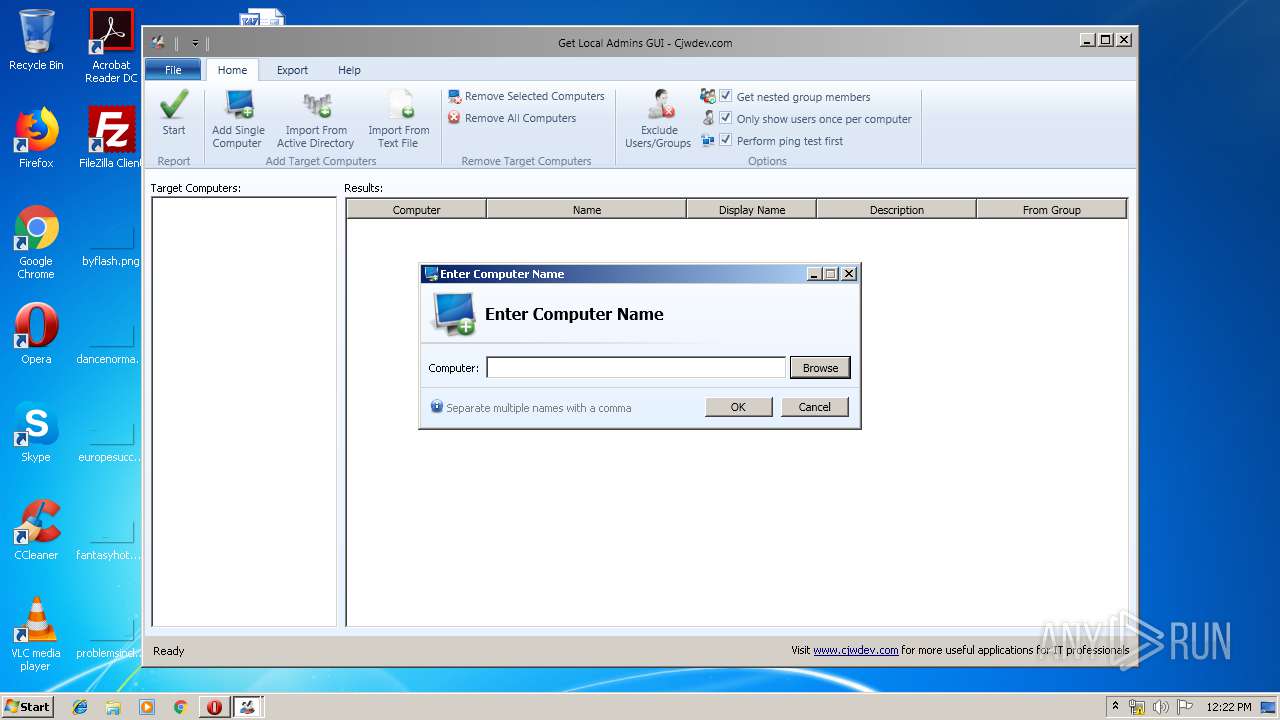
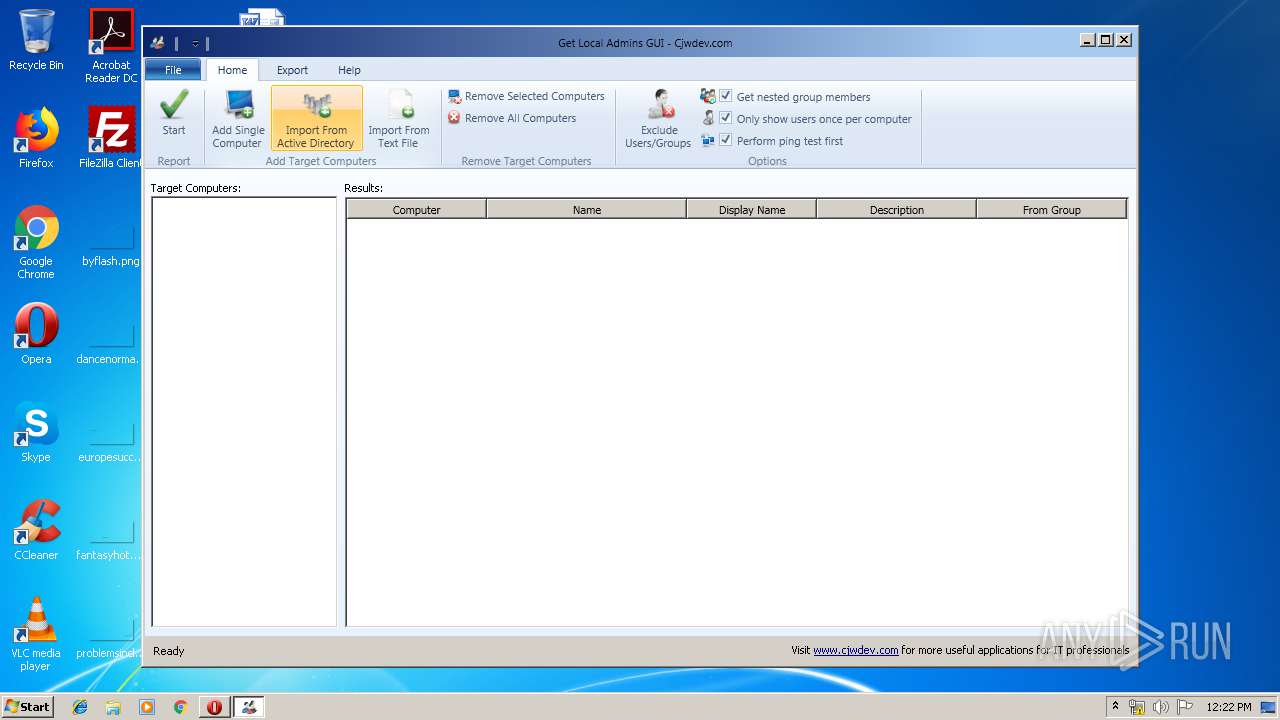
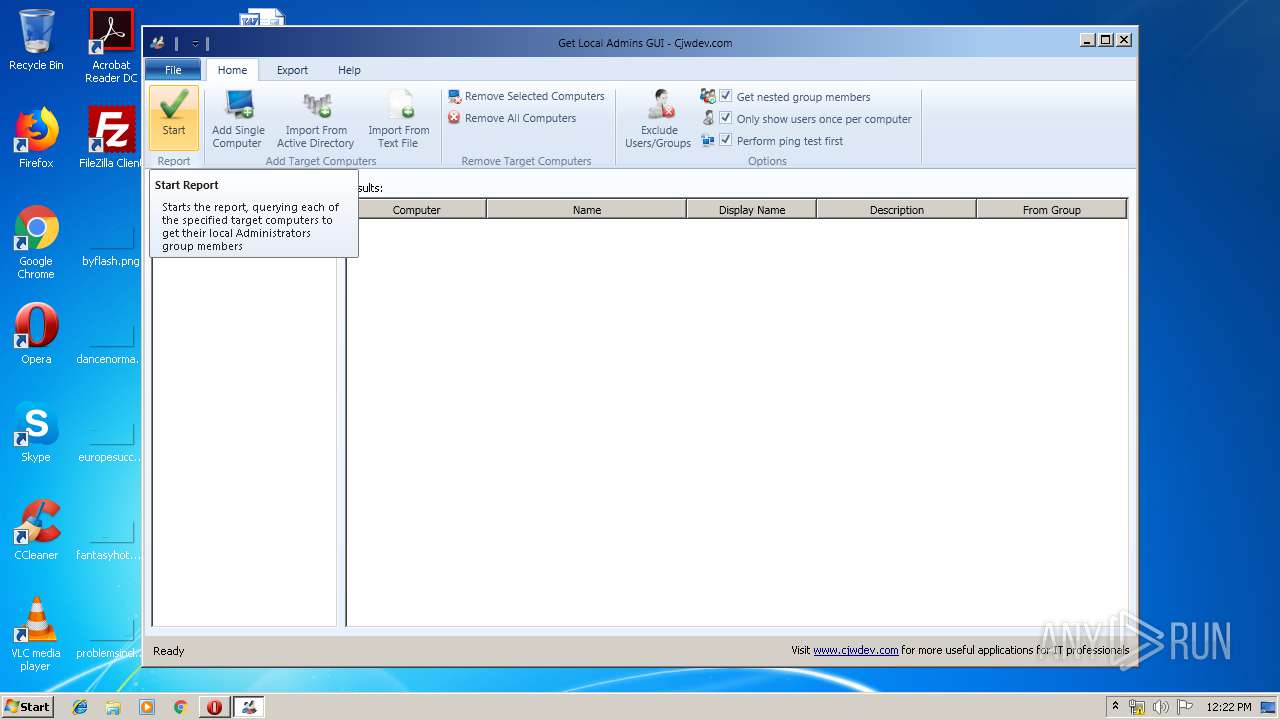
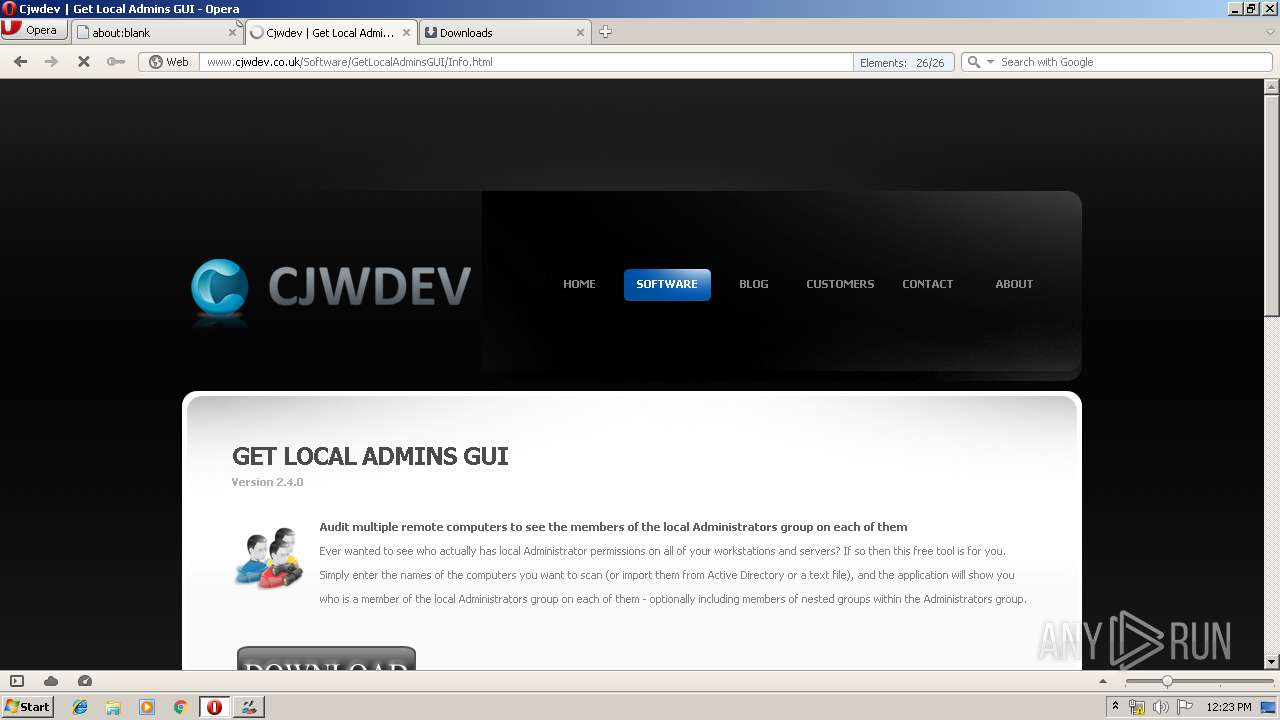
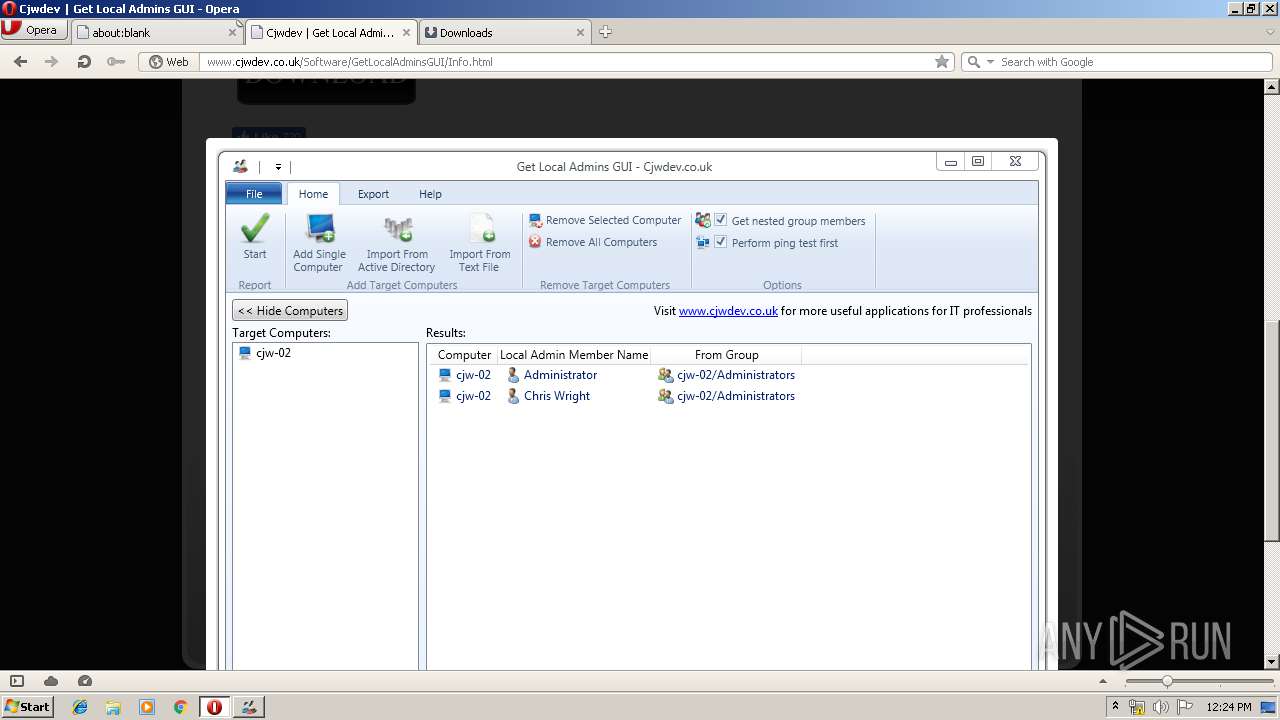
| 2384 | "C:\Program Files\Cjwdev\Get Local Admins GUI\GetLocalAdminsGUI.exe" | C:\Program Files\Cjwdev\Get Local Admins GUI\GetLocalAdminsGUI.exe | explorer.exe | ||||||||||||
User: admin Company: Cjwdev Ltd Integrity Level: MEDIUM Description: Get Local Admins GUI Exit code: 0 Version: 2.4.0.0 Modules
| |||||||||||||||
| 2708 | C:\Windows\system32\MsiExec.exe -Embedding 5E4D43DEF4297D49F376381785DA5E49 | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2956 | "C:\Program Files\Opera\opera.exe" http://www.cjwdev.com/Software/GetLocalAdminsGUI/GetLocalAdminsGUI.zip | C:\Program Files\Opera\opera.exe | explorer.exe | ||||||||||||
User: admin Company: Opera Software Integrity Level: MEDIUM Description: Opera Internet Browser Exit code: 0 Version: 1748 Modules
| |||||||||||||||
| 3000 | "C:\Users\admin\Desktop\GetLocalAdminsGUISetup.exe" | C:\Users\admin\Desktop\GetLocalAdminsGUISetup.exe | explorer.exe | ||||||||||||
User: admin Company: Cjwdev Integrity Level: MEDIUM Description: This installer database contains the logic and data required to install Get Local Admins GUI. Exit code: 0 Version: 2.4.0 Modules
| |||||||||||||||
| 3508 | DrvInst.exe "1" "200" "STORAGE\VolumeSnapshot\HarddiskVolumeSnapshot18" "" "" "6792c44eb" "00000000" "00000390" "000005C4" | C:\Windows\system32\DrvInst.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3724 | C:\Windows\system32\MsiExec.exe -Embedding A015294EFCDF272063F8DDAD56348C30 C | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3728 | C:\Windows\system32\msiexec.exe /V | C:\Windows\system32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 4080 | /i "C:\Users\admin\AppData\Roaming\Cjwdev\Get Local Admins GUI 2.4.0\install\GetLocalAdminsGUISetup.msi" AI_SETUPEXEPATH="C:\Users\admin\Desktop\GetLocalAdminsGUISetup.exe" SETUPEXEDIR="C:\Users\admin\Desktop\" EXE_CMD_LINE="/exenoupdates /exelang 0 /noprereqs " | C:\Windows\system32\msiexec.exe | — | GetLocalAdminsGUISetup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 562
Read events
1 140
Write events
408
Delete events
14
Modification events
| (PID) Process: | (2956) opera.exe | Key: | HKEY_CURRENT_USER\Software\Opera Software |
| Operation: | write | Name: | Last CommandLine v2 |
Value: C:\Program Files\Opera\opera.exe http://www.cjwdev.com/Software/GetLocalAdminsGUI/GetLocalAdminsGUI.zip | |||
| (PID) Process: | (2956) opera.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2956) opera.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 0202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (2956) opera.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 0200000001000000000000000700000006000000030000000500000004000000FFFFFFFF | |||
| (PID) Process: | (2956) opera.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\50\ComDlg |
| Operation: | write | Name: | TV_FolderType |
Value: {FBB3477E-C9E4-4B3B-A2BA-D3F5D3CD46F9} | |||
| (PID) Process: | (2956) opera.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\50\ComDlg |
| Operation: | write | Name: | TV_TopViewID |
Value: {82BA0782-5B7A-4569-B5D7-EC83085F08CC} | |||
| (PID) Process: | (2956) opera.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\50\ComDlg |
| Operation: | write | Name: | TV_TopViewVersion |
Value: 0 | |||
| (PID) Process: | (2956) opera.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\AllFolders\ComDlg\{FBB3477E-C9E4-4B3B-A2BA-D3F5D3CD46F9}\{82BA0782-5B7A-4569-B5D7-EC83085F08CC} |
| Operation: | write | Name: | Mode |
Value: 4 | |||
| (PID) Process: | (2956) opera.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\AllFolders\ComDlg\{FBB3477E-C9E4-4B3B-A2BA-D3F5D3CD46F9}\{82BA0782-5B7A-4569-B5D7-EC83085F08CC} |
| Operation: | write | Name: | LogicalViewMode |
Value: 1 | |||
| (PID) Process: | (2956) opera.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\AllFolders\ComDlg\{FBB3477E-C9E4-4B3B-A2BA-D3F5D3CD46F9}\{82BA0782-5B7A-4569-B5D7-EC83085F08CC} |
| Operation: | write | Name: | FFlags |
Value: 1092616257 | |||
Executable files
14
Suspicious files
54
Text files
138
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2956 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\sessions\oprF098.tmp | — | |
MD5:— | SHA256:— | |||
| 2956 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\oprF0A9.tmp | — | |
MD5:— | SHA256:— | |||
| 2956 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\oprF0E8.tmp | — | |
MD5:— | SHA256:— | |||
| 2956 | opera.exe | C:\Users\admin\AppData\Local\Opera\Opera\cache\sesn\opr00002.tmp | — | |
MD5:— | SHA256:— | |||
| 2956 | opera.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\INWC0XFZ3NND8H4M24DN.temp | — | |
MD5:— | SHA256:— | |||
| 4080 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSI68B6.tmp | — | |
MD5:— | SHA256:— | |||
| 4080 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSI6963.tmp | — | |
MD5:— | SHA256:— | |||
| 4080 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSI6993.tmp | — | |
MD5:— | SHA256:— | |||
| 4080 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSI69A3.tmp | — | |
MD5:— | SHA256:— | |||
| 2956 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\operaprefs.ini | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
45
TCP/UDP connections
47
DNS requests
20
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2956 | opera.exe | GET | — | 94.136.40.103:80 | http://www.cjwdev.com/Software/GetLocalAdminsGUI/GetLocalAdminsGUI.zip | GB | — | — | malicious |
2956 | opera.exe | GET | 200 | 93.184.220.29:80 | http://crl4.digicert.com/DigiCertHighAssuranceEVRootCA.crl | US | der | 543 b | whitelisted |
2956 | opera.exe | GET | 200 | 172.217.23.142:80 | http://clients1.google.com/complete/search?q=get&client=opera-suggest-omnibox&hl=de | US | text | 106 b | whitelisted |
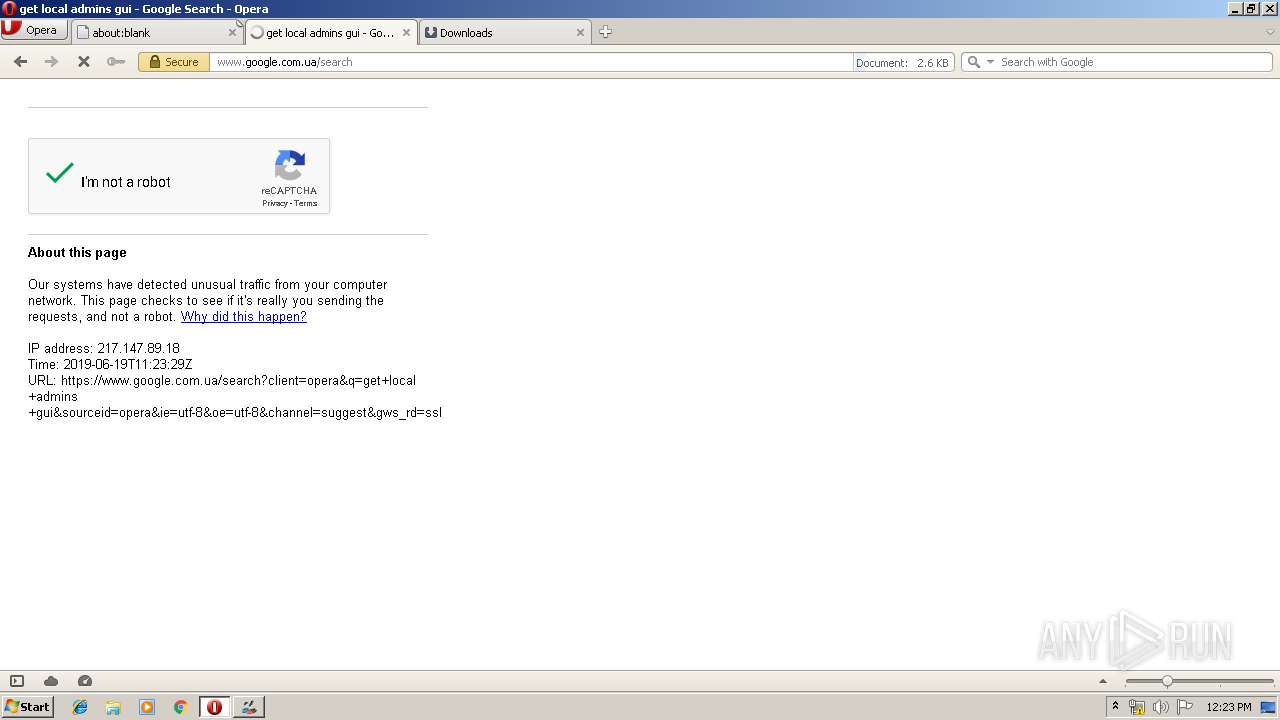
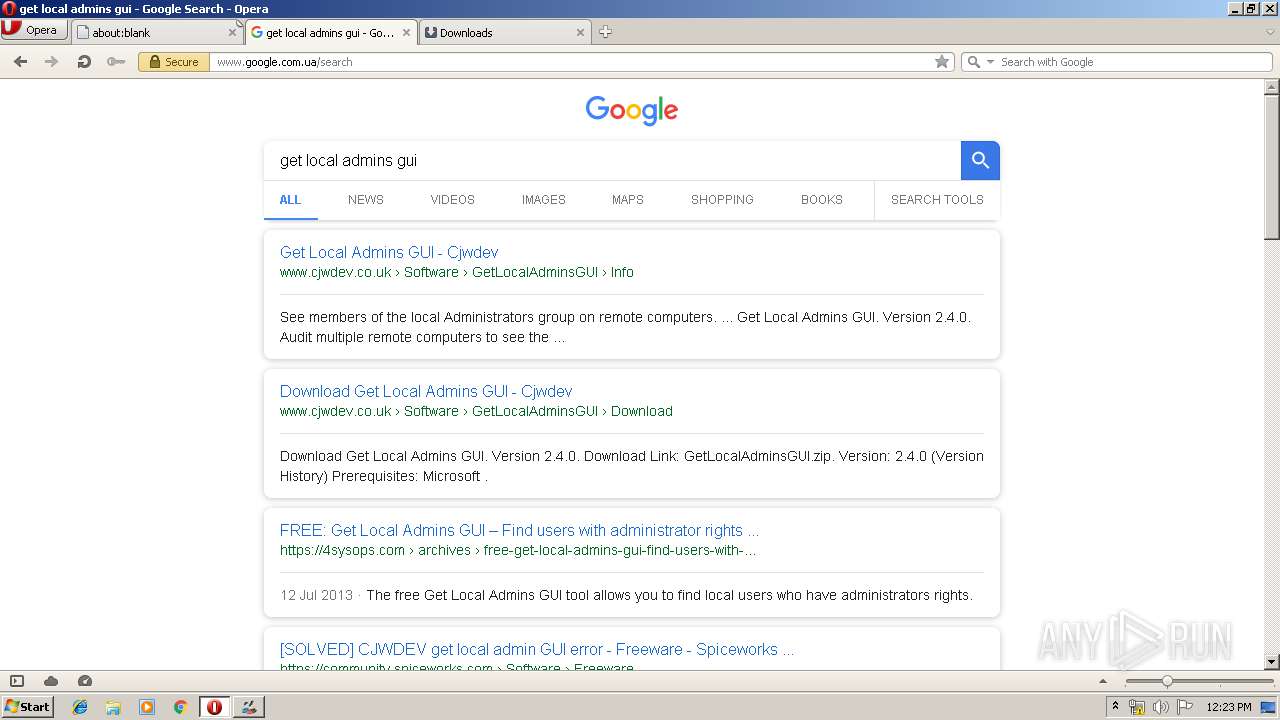
2956 | opera.exe | GET | 302 | 172.217.22.99:80 | http://www.google.com.ua/search?q=get+local+admins+gui&sourceid=opera&ie=utf-8&oe=utf-8&channel=suggest | US | html | 333 b | whitelisted |
2956 | opera.exe | GET | 200 | 172.217.23.142:80 | http://clients1.google.com/complete/search?q=get+local&client=opera-suggest-omnibox&hl=de | US | text | 111 b | whitelisted |
2956 | opera.exe | GET | 200 | 172.217.22.35:80 | http://ocsp.pki.goog/GTSGIAG3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT27bBjYjKBmjX2jXWgnQJKEapsrQQUd8K4UJpndnaxLcKG0IOgfqZ%2BuksCEBbuQj3Mjj5TO95QAIva2XA%3D | US | der | 471 b | whitelisted |
2956 | opera.exe | GET | 200 | 172.217.23.142:80 | http://clients1.google.com/complete/search?q=get+l&client=opera-suggest-omnibox&hl=de | US | text | 109 b | whitelisted |
2956 | opera.exe | GET | 200 | 94.136.40.103:80 | http://www.cjwdev.co.uk/Software/GetLocalAdminsGUI/Info.html | GB | html | 2.15 Kb | malicious |
2956 | opera.exe | GET | 400 | 185.26.182.112:80 | http://sitecheck2.opera.com/?host=www.cjwdev.com&hdn=05mLfJNc6XRzsqaL0iwXXg== | unknown | html | 150 b | whitelisted |
2956 | opera.exe | GET | 200 | 172.217.23.142:80 | http://clients1.google.com/complete/search?q=get+local+admins+gui&client=opera-suggest-omnibox&hl=de | US | text | 64 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2384 | GetLocalAdminsGUI.exe | 94.136.40.103:80 | www.cjwdev.com | Host Europe GmbH | GB | malicious |
2956 | opera.exe | 172.217.22.99:80 | www.google.com.ua | Google Inc. | US | whitelisted |
2956 | opera.exe | 172.217.23.142:80 | clients1.google.com | Google Inc. | US | whitelisted |
2956 | opera.exe | 172.217.22.99:443 | www.google.com.ua | Google Inc. | US | whitelisted |
2956 | opera.exe | 216.58.207.68:443 | www.google.com | Google Inc. | US | whitelisted |
2956 | opera.exe | 172.217.22.35:80 | crl.pki.goog | Google Inc. | US | whitelisted |
2956 | opera.exe | 185.26.182.94:443 | sitecheck2.opera.com | Opera Software AS | — | whitelisted |
2956 | opera.exe | 185.26.182.112:80 | sitecheck2.opera.com | Opera Software AS | — | malicious |
2956 | opera.exe | 93.184.220.29:80 | crl4.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2956 | opera.exe | 172.217.21.227:443 | www.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.cjwdev.com |
| malicious |
sitecheck2.opera.com |
| whitelisted |
certs.opera.com |
| whitelisted |
crl4.digicert.com |
| whitelisted |
clients1.google.com |
| whitelisted |
www.google.com.ua |
| whitelisted |
crl.pki.goog |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
www.google.com |
| malicious |
www.gstatic.com |
| whitelisted |