| File name: | cc838a9df5f5d9b135944f6fa9de2b6dcb61191ded33d9d27abc01b0e3ad46f2 |
| Full analysis: | https://app.any.run/tasks/0a81deb7-c894-4f9d-9d3b-e479efde02a2 |
| Verdict: | Malicious activity |
| Analysis date: | July 27, 2023, 06:54:06 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | C71307553BB15AAF77FB7A91C8336B27 |
| SHA1: | 1A2A74B4FBD01364F6C560BCE8C77DEACA6F0C9E |
| SHA256: | CC838A9DF5F5D9B135944F6FA9DE2B6DCB61191DED33D9D27ABC01B0E3AD46F2 |
| SSDEEP: | 98304:bnsmtk2a9QLJQtFx5TOLX3xZy5trnkUf1wa6cODx3yCRGKBv5SGSidQ6JS7aLOMO:DLGQLJQ95TUSPkUf2a/uG253SiZhaj |
MALICIOUS
Connects to the CnC server
- Synaptics.exe (PID: 988)
Application was dropped or rewritten from another process
- Synaptics.exe (PID: 988)
- ._cache_cc838a9df5f5d9b135944f6fa9de2b6dcb61191ded33d9d27abc01b0e3ad46f2.exe (PID: 2576)
- ._cache_cc838a9df5f5d9b135944f6fa9de2b6dcb61191ded33d9d27abc01b0e3ad46f2.exe (PID: 3704)
SUSPICIOUS
Reads the Internet Settings
- cc838a9df5f5d9b135944f6fa9de2b6dcb61191ded33d9d27abc01b0e3ad46f2.exe (PID: 1456)
- Synaptics.exe (PID: 988)
Executable content was dropped or overwritten
- cc838a9df5f5d9b135944f6fa9de2b6dcb61191ded33d9d27abc01b0e3ad46f2.exe (PID: 1456)
INFO
Create files in a temporary directory
- cc838a9df5f5d9b135944f6fa9de2b6dcb61191ded33d9d27abc01b0e3ad46f2.exe (PID: 1456)
Checks supported languages
- cc838a9df5f5d9b135944f6fa9de2b6dcb61191ded33d9d27abc01b0e3ad46f2.exe (PID: 1456)
- ._cache_cc838a9df5f5d9b135944f6fa9de2b6dcb61191ded33d9d27abc01b0e3ad46f2.exe (PID: 3704)
- Synaptics.exe (PID: 988)
The process checks LSA protection
- cc838a9df5f5d9b135944f6fa9de2b6dcb61191ded33d9d27abc01b0e3ad46f2.exe (PID: 1456)
- ._cache_cc838a9df5f5d9b135944f6fa9de2b6dcb61191ded33d9d27abc01b0e3ad46f2.exe (PID: 3704)
- Synaptics.exe (PID: 988)
Creates files in the program directory
- cc838a9df5f5d9b135944f6fa9de2b6dcb61191ded33d9d27abc01b0e3ad46f2.exe (PID: 1456)
- Synaptics.exe (PID: 988)
Reads the computer name
- cc838a9df5f5d9b135944f6fa9de2b6dcb61191ded33d9d27abc01b0e3ad46f2.exe (PID: 1456)
- ._cache_cc838a9df5f5d9b135944f6fa9de2b6dcb61191ded33d9d27abc01b0e3ad46f2.exe (PID: 3704)
- Synaptics.exe (PID: 988)
Reads the machine GUID from the registry
- cc838a9df5f5d9b135944f6fa9de2b6dcb61191ded33d9d27abc01b0e3ad46f2.exe (PID: 1456)
- ._cache_cc838a9df5f5d9b135944f6fa9de2b6dcb61191ded33d9d27abc01b0e3ad46f2.exe (PID: 3704)
- Synaptics.exe (PID: 988)
Checks proxy server information
- Synaptics.exe (PID: 988)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Borland Delphi 7 (92.7) |
|---|---|---|
| .exe | | | UPX compressed Win32 Executable (3.7) |
| .exe | | | Win32 Executable Delphi generic (1.9) |
| .exe | | | Win32 Executable (generic) (0.6) |
| .exe | | | Win16/32 Executable Delphi generic (0.2) |
EXIF
EXE
| Comments: | - |
|---|---|
| ProductVersion: | 1.0.0.0 |
| ProductName: | Synaptics Pointing Device Driver |
| OriginalFileName: | - |
| LegalTrademarks: | - |
| LegalCopyright: | - |
| InternalName: | - |
| FileVersion: | 1.0.0.4 |
| FileDescription: | Synaptics Pointing Device Driver |
| CompanyName: | Synaptics |
| CharacterSet: | Windows, Turkish |
| LanguageCode: | Turkish |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 1.0.0.4 |
| FileVersionNumber: | 1.0.0.4 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 4 |
| ImageVersion: | - |
| OSVersion: | 4 |
| EntryPoint: | 0x9ab80 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 5334016 |
| CodeSize: | 629760 |
| LinkerVersion: | 2.25 |
| PEType: | PE32 |
| ImageFileCharacteristics: | Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| TimeStamp: | 1992:06:19 22:22:17+00:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-1992 22:22:17 |
| Detected languages: |
|
| CompanyName: | Synaptics |
| FileDescription: | Synaptics Pointing Device Driver |
| FileVersion: | 1.0.0.4 |
| InternalName: | - |
| LegalCopyright: | - |
| LegalTrademarks: | - |
| OriginalFilename: | - |
| ProductName: | Synaptics Pointing Device Driver |
| ProductVersion: | 1.0.0.0 |
| Comments: | - |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 19-Jun-1992 22:22:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 0x00001000 | 0x00099BEC | 0x00099C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.57296 |
DATA | 0x0009B000 | 0x00002E54 | 0x00003000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.85462 |
BSS | 0x0009E000 | 0x000011E5 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x000A0000 | 0x00002A42 | 0x00002C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.91933 |
.tls | 0x000A3000 | 0x00000010 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x000A4000 | 0x00000039 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.78462 |
.reloc | 0x000A5000 | 0x0000A980 | 0x0000AA00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 6.67412 |
.rsrc | 0x000B0000 | 0x00505AB0 | 0x00505C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 7.90105 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.22416 | 772 | Latin 1 / Western European | Turkish - Turkey | RT_VERSION |
2 | 2.80231 | 308 | Latin 1 / Western European | UNKNOWN | RT_CURSOR |
3 | 3.00046 | 308 | Latin 1 / Western European | UNKNOWN | RT_CURSOR |
4 | 2.56318 | 308 | Latin 1 / Western European | UNKNOWN | RT_CURSOR |
5 | 2.6949 | 308 | Latin 1 / Western European | UNKNOWN | RT_CURSOR |
6 | 2.62527 | 308 | Latin 1 / Western European | UNKNOWN | RT_CURSOR |
7 | 2.91604 | 308 | Latin 1 / Western European | UNKNOWN | RT_CURSOR |
4073 | 3.23351 | 856 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4074 | 3.23989 | 1064 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4075 | 3.15413 | 932 | Latin 1 / Western European | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
gdi32.dll |
kernel32.dll |
netapi32.dll |
ole32.dll |
oleaut32.dll |
shell32.dll |
user32.dll |
version.dll |
Total processes
42
Monitored processes
4
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 988 | "C:\ProgramData\Synaptics\Synaptics.exe" InjUpdate | C:\ProgramData\Synaptics\Synaptics.exe | cc838a9df5f5d9b135944f6fa9de2b6dcb61191ded33d9d27abc01b0e3ad46f2.exe | ||||||||||||
User: admin Company: Synaptics Integrity Level: HIGH Description: Synaptics Pointing Device Driver Exit code: 0 Version: 1.0.0.4 Modules
| |||||||||||||||
| 1456 | "C:\Users\admin\AppData\Local\Temp\cc838a9df5f5d9b135944f6fa9de2b6dcb61191ded33d9d27abc01b0e3ad46f2.exe" | C:\Users\admin\AppData\Local\Temp\cc838a9df5f5d9b135944f6fa9de2b6dcb61191ded33d9d27abc01b0e3ad46f2.exe | explorer.exe | ||||||||||||
User: admin Company: Synaptics Integrity Level: MEDIUM Description: Synaptics Pointing Device Driver Exit code: 0 Version: 1.0.0.4 Modules
| |||||||||||||||
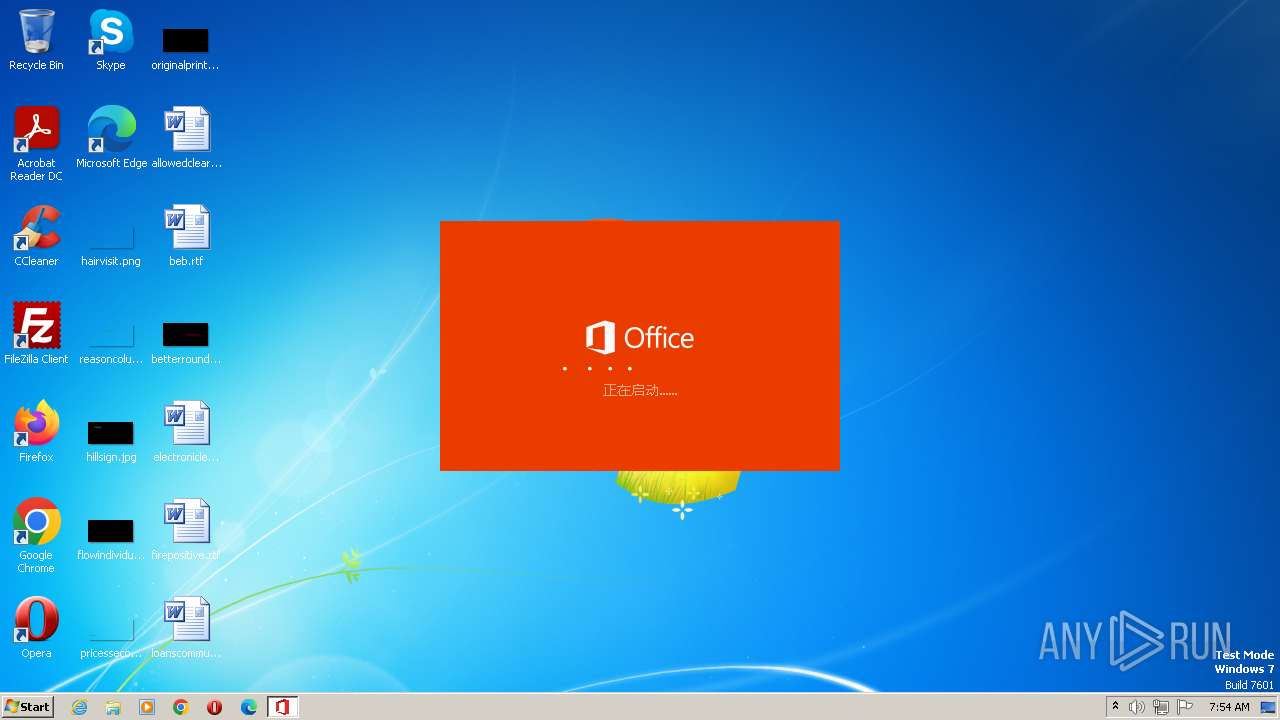
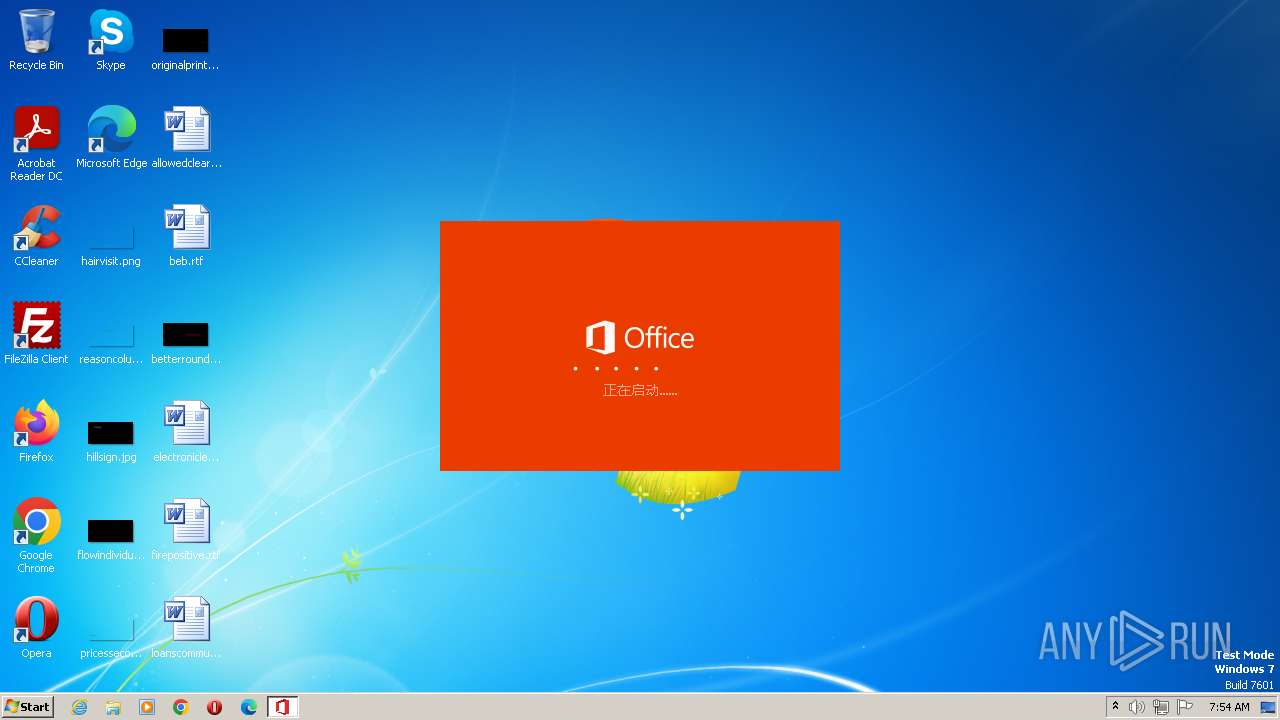
| 2576 | "C:\Users\admin\AppData\Local\Temp\._cache_cc838a9df5f5d9b135944f6fa9de2b6dcb61191ded33d9d27abc01b0e3ad46f2.exe" | C:\Users\admin\AppData\Local\Temp\._cache_cc838a9df5f5d9b135944f6fa9de2b6dcb61191ded33d9d27abc01b0e3ad46f2.exe | — | cc838a9df5f5d9b135944f6fa9de2b6dcb61191ded33d9d27abc01b0e3ad46f2.exe | |||||||||||
User: admin Company: Beijing Yundong Zhixiao Network Technology Co. , Ltd. Integrity Level: MEDIUM Description: Microsoft Office Exit code: 3221226540 Version: 4.3.4.20 Modules
| |||||||||||||||
| 3704 | "C:\Users\admin\AppData\Local\Temp\._cache_cc838a9df5f5d9b135944f6fa9de2b6dcb61191ded33d9d27abc01b0e3ad46f2.exe" | C:\Users\admin\AppData\Local\Temp\._cache_cc838a9df5f5d9b135944f6fa9de2b6dcb61191ded33d9d27abc01b0e3ad46f2.exe | cc838a9df5f5d9b135944f6fa9de2b6dcb61191ded33d9d27abc01b0e3ad46f2.exe | ||||||||||||
User: admin Company: Beijing Yundong Zhixiao Network Technology Co. , Ltd. Integrity Level: HIGH Description: Microsoft Office Exit code: 0 Version: 4.3.4.20 Modules
| |||||||||||||||
Total events
1 982
Read events
1 908
Write events
74
Delete events
0
Modification events
| (PID) Process: | (1456) cc838a9df5f5d9b135944f6fa9de2b6dcb61191ded33d9d27abc01b0e3ad46f2.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1456) cc838a9df5f5d9b135944f6fa9de2b6dcb61191ded33d9d27abc01b0e3ad46f2.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1456) cc838a9df5f5d9b135944f6fa9de2b6dcb61191ded33d9d27abc01b0e3ad46f2.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1456) cc838a9df5f5d9b135944f6fa9de2b6dcb61191ded33d9d27abc01b0e3ad46f2.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (1456) cc838a9df5f5d9b135944f6fa9de2b6dcb61191ded33d9d27abc01b0e3ad46f2.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\178\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (988) Synaptics.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (988) Synaptics.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000049010000090000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A8016B000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (988) Synaptics.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (988) Synaptics.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (988) Synaptics.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
Executable files
4
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1456 | cc838a9df5f5d9b135944f6fa9de2b6dcb61191ded33d9d27abc01b0e3ad46f2.exe | C:\ProgramData\Synaptics\Synaptics.exe | executable | |
MD5:C71307553BB15AAF77FB7A91C8336B27 | SHA256:CC838A9DF5F5D9B135944F6FA9DE2B6DCB61191DED33D9D27ABC01B0E3AD46F2 | |||
| 1456 | cc838a9df5f5d9b135944f6fa9de2b6dcb61191ded33d9d27abc01b0e3ad46f2.exe | C:\ProgramData\Synaptics\RCXBB82.tmp | executable | |
MD5:A9817F10E99F8F8AE92D4EDBFE795F07 | SHA256:05750EFB196C2F48EEBB0C619DC6A3A7B3AC8EAF3CBE7FB39F5AA50274A84DCB | |||
| 1456 | cc838a9df5f5d9b135944f6fa9de2b6dcb61191ded33d9d27abc01b0e3ad46f2.exe | C:\Users\admin\AppData\Local\Temp\._cache_cc838a9df5f5d9b135944f6fa9de2b6dcb61191ded33d9d27abc01b0e3ad46f2.exe | executable | |
MD5:790874E0C2E059D55C231A0AFA422E76 | SHA256:08C89253934A32EA1C504CCE45ACD34F22C2B512598BCA1397BE19EAFCB5C8F0 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
13
DNS requests
4
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3704 | ._cache_cc838a9df5f5d9b135944f6fa9de2b6dcb61191ded33d9d27abc01b0e3ad46f2.exe | GET | — | 116.62.9.230:80 | http://officev2.zhuazi.com/office/log/log/configStartReq/cache_cc838a9df5f5d9b135944f6fa9de2b6dcb61191ded33d9d27abc01b0e3ad46f2/WX_4.3.4.20/Windows7/1da8e2ba355cc359fef25b2e6a6bd9b7 | CN | — | — | suspicious |
3704 | ._cache_cc838a9df5f5d9b135944f6fa9de2b6dcb61191ded33d9d27abc01b0e3ad46f2.exe | GET | — | 116.62.9.230:80 | http://officev2.zhuazi.com/office/log/log/bannerListStartReq/cache_cc838a9df5f5d9b135944f6fa9de2b6dcb61191ded33d9d27abc01b0e3ad46f2/WX_4.3.4.20/Windows7/1da8e2ba355cc359fef25b2e6a6bd9b7 | CN | — | — | suspicious |
988 | Synaptics.exe | GET | — | 174.128.246.100:80 | http://freedns.afraid.org/api/?action=getdyndns&sha=a30fa98efc092684e8d1c5cff797bcc613562978 | US | — | — | malicious |
3704 | ._cache_cc838a9df5f5d9b135944f6fa9de2b6dcb61191ded33d9d27abc01b0e3ad46f2.exe | POST | — | 116.62.9.230:80 | http://officev2.zhuazi.com/office/Index/config/cache_cc838a9df5f5d9b135944f6fa9de2b6dcb61191ded33d9d27abc01b0e3ad46f2-Windows7-32-1280*720/4.3.4.20/cache_cc838a9df5f5d9b135944f6fa9de2b6dcb61191ded33d9d27abc01b0e3ad46f2/1da8e2ba355cc359fef25b2e6a6bd9b7 | CN | — | — | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3704 | ._cache_cc838a9df5f5d9b135944f6fa9de2b6dcb61191ded33d9d27abc01b0e3ad46f2.exe | 116.62.9.230:80 | officev2.zhuazi.com | Hangzhou Alibaba Advertising Co.,Ltd. | CN | suspicious |
988 | Synaptics.exe | 174.128.246.100:80 | freedns.afraid.org | ST-BGP | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
officev2.zhuazi.com |
| suspicious |
xred.mooo.com |
| suspicious |
freedns.afraid.org |
| malicious |
dns.msftncsi.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1084 | svchost.exe | Misc activity | ET INFO DYNAMIC_DNS Query to Abused Domain *.mooo.com |
3 ETPRO signatures available at the full report
Process | Message |
|---|---|
._cache_cc838a9df5f5d9b135944f6fa9de2b6dcb61191ded33d9d27abc01b0e3ad46f2.exe | QObject::connect: Cannot connect (null)::aboutToQuit() to QNativeWifiEngine::closeHandle()
|
._cache_cc838a9df5f5d9b135944f6fa9de2b6dcb61191ded33d9d27abc01b0e3ad46f2.exe | QEventLoop: Cannot be used without QApplication
|