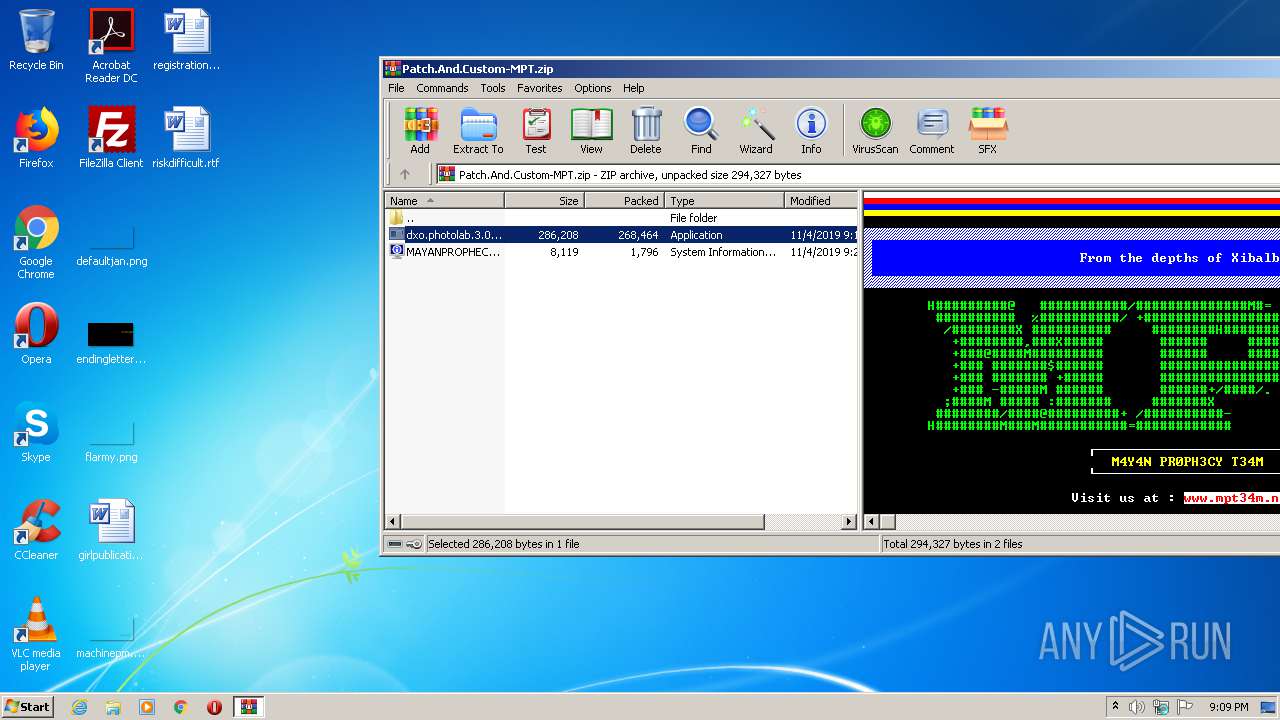
| File name: | Patch.And.Custom-MPT.zip |
| Full analysis: | https://app.any.run/tasks/866458ba-6b80-4cff-9c6b-931c2c50c348 |
| Verdict: | Malicious activity |
| Analysis date: | July 17, 2020, 20:08:48 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | CD2AF80157AB3EC25480FEC5512EC2F1 |
| SHA1: | 9D2BFBB5B4F6A2FF07406C12927D0478EF535EA1 |
| SHA256: | CC7FE81F860E3D311EFB4BB9EB83033203664AAC3F48B545A7A5608F26CF5771 |
| SSDEEP: | 6144:luGY4Lu6RbTlmj0pK7SKPtkq1ngekorlghsF8BfY3O:IGY6Tcf7SQtn1aoOhT23O |
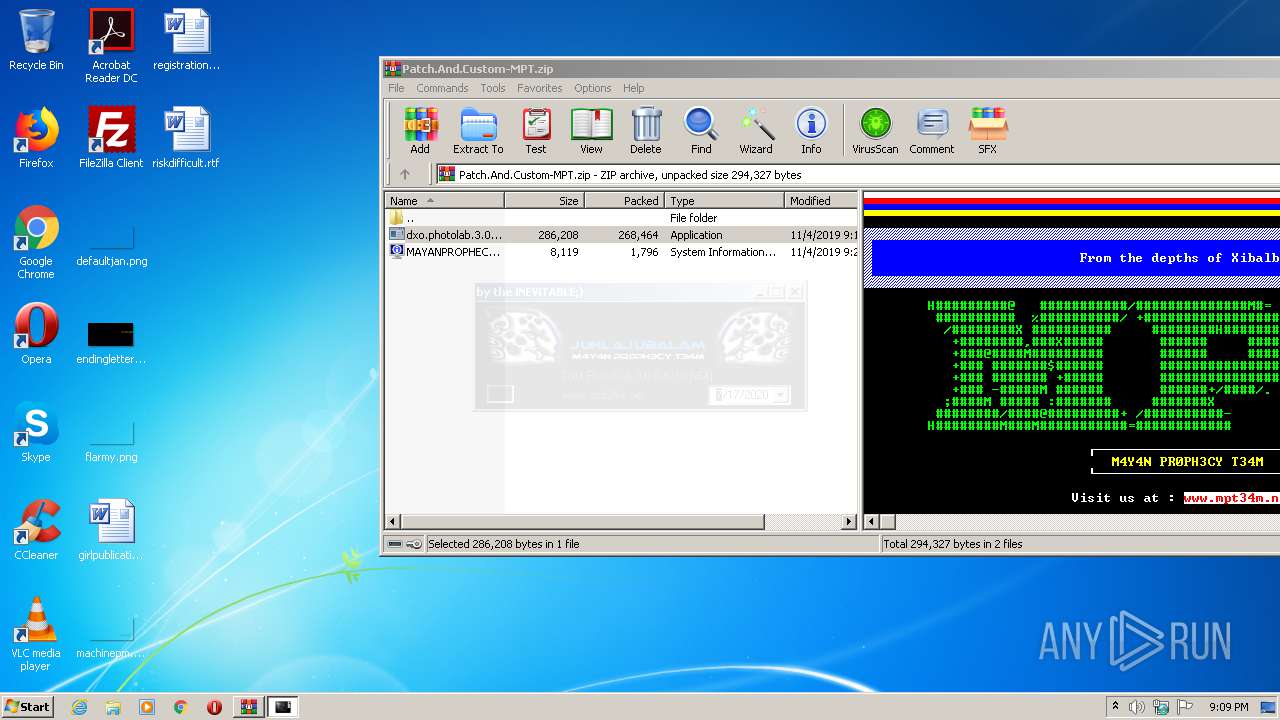
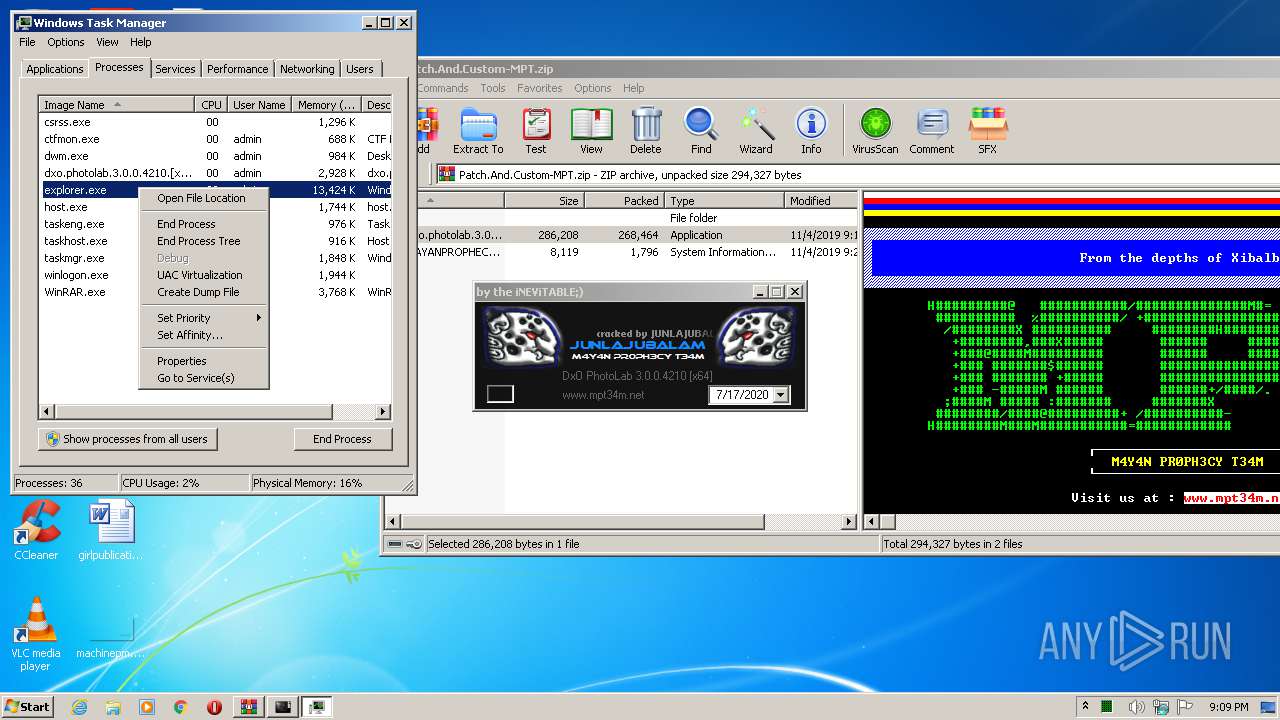
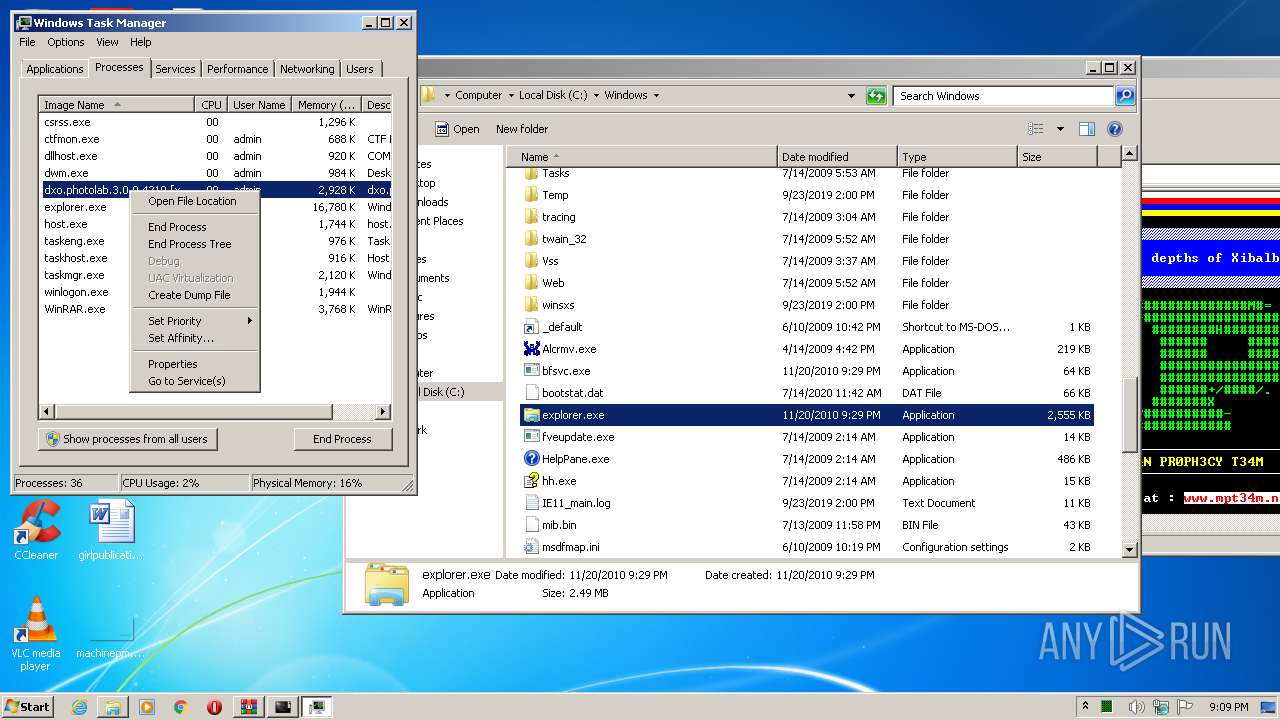
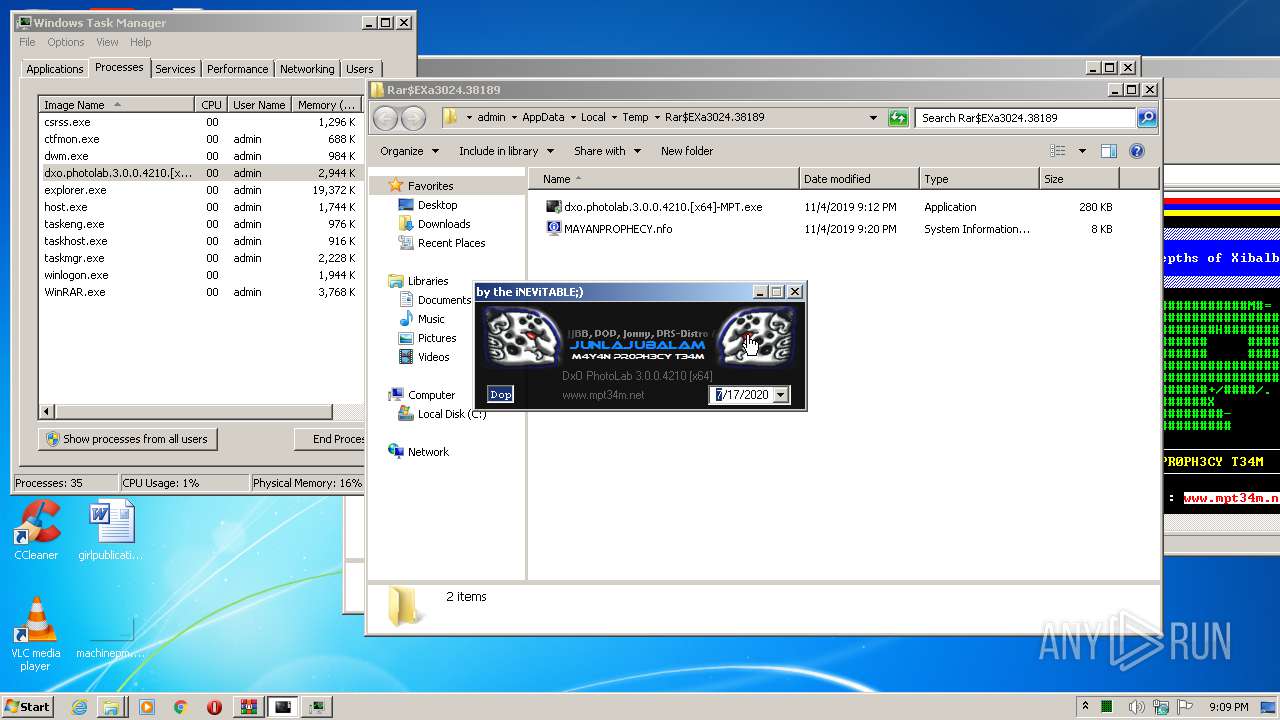
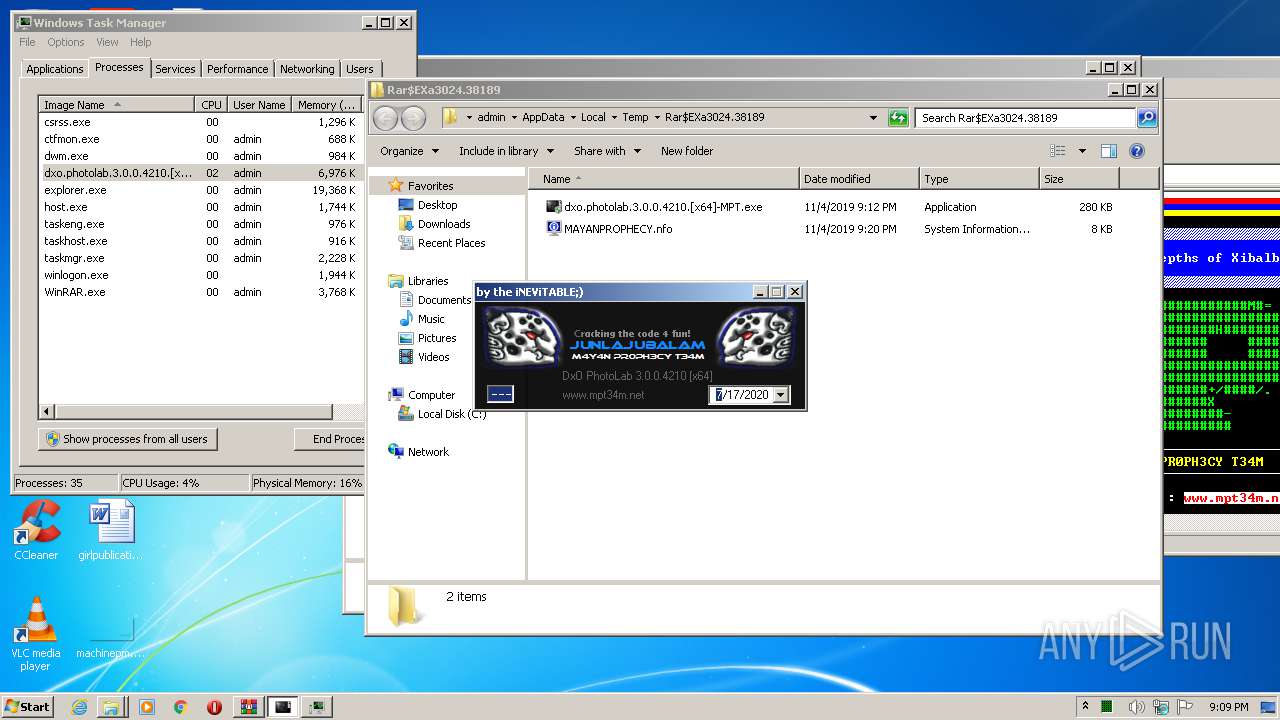
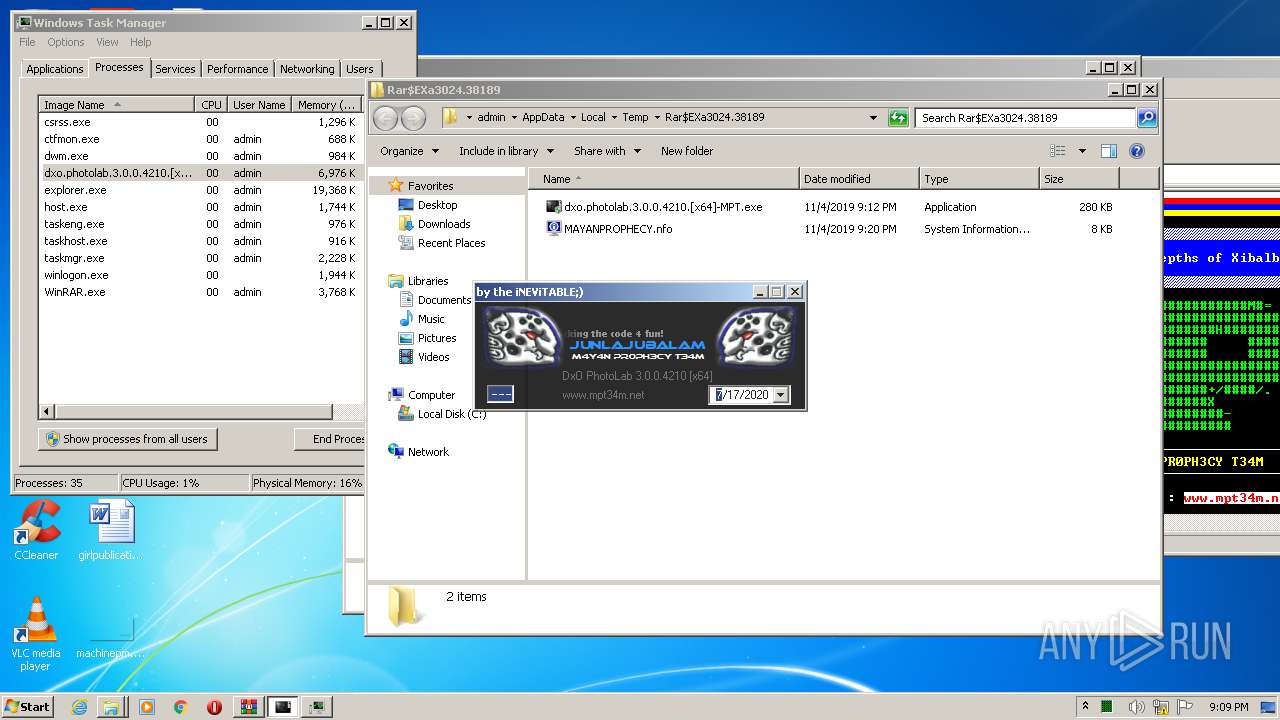
MALICIOUS
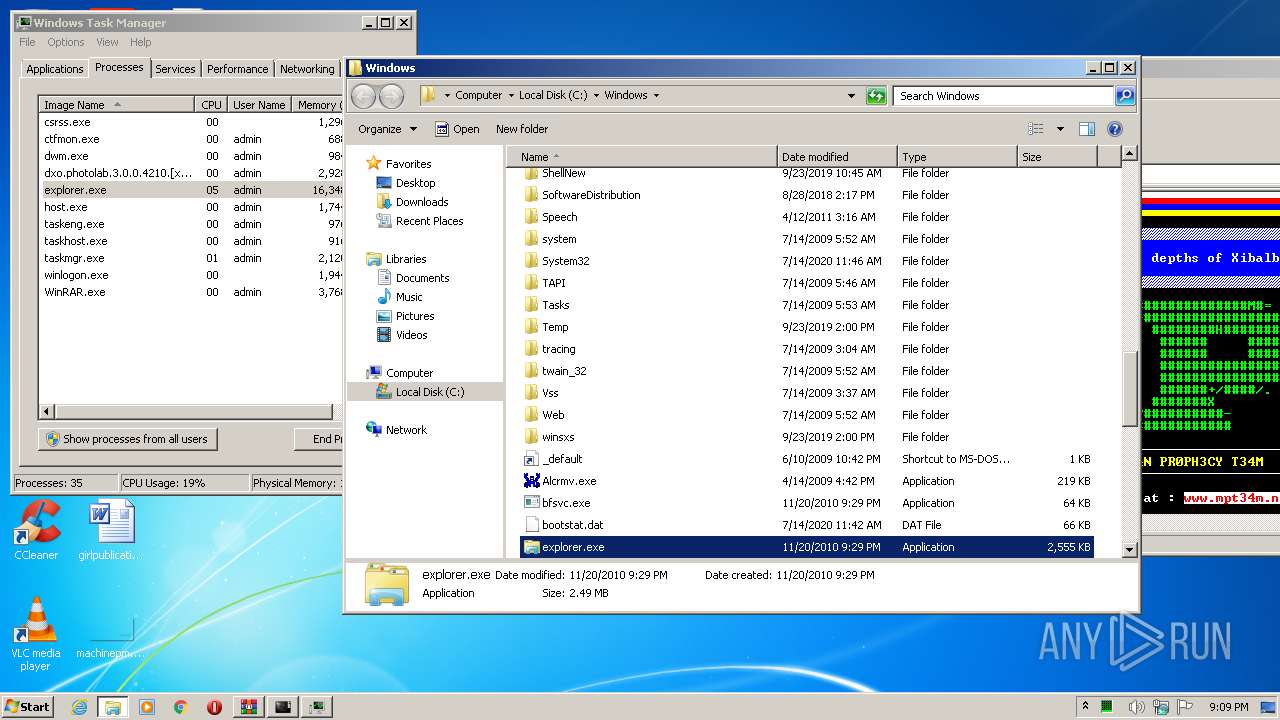
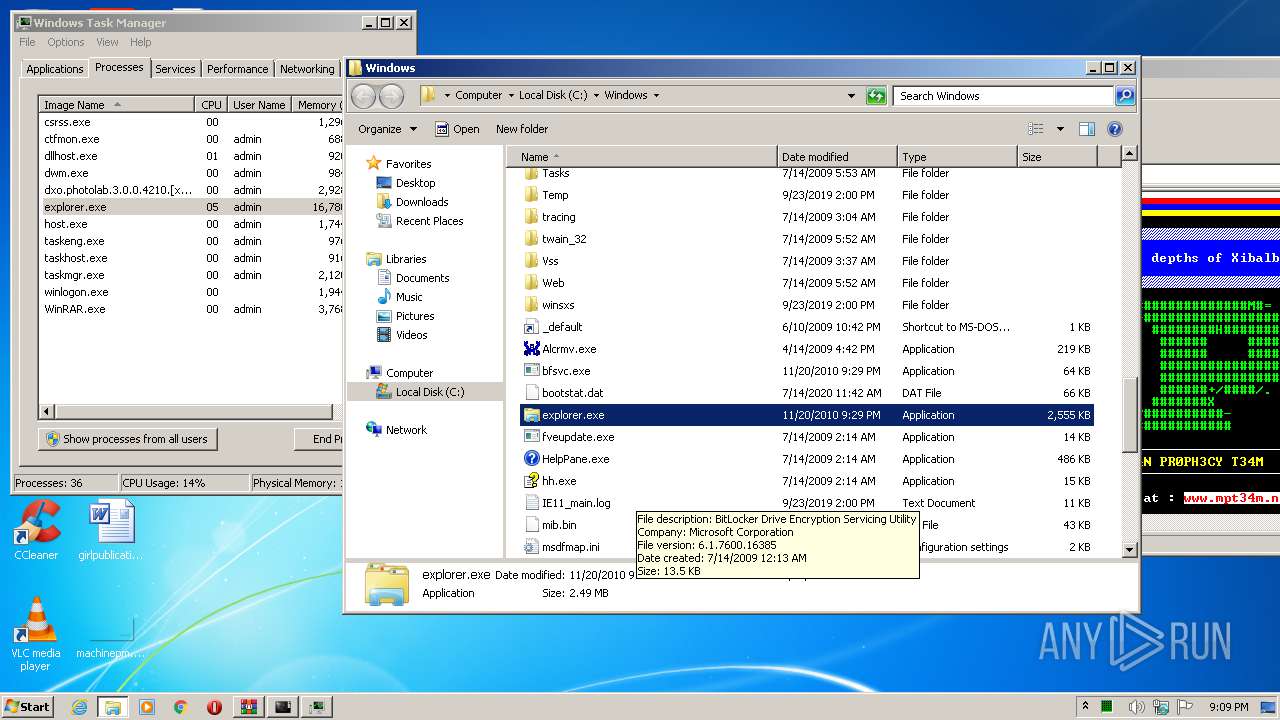
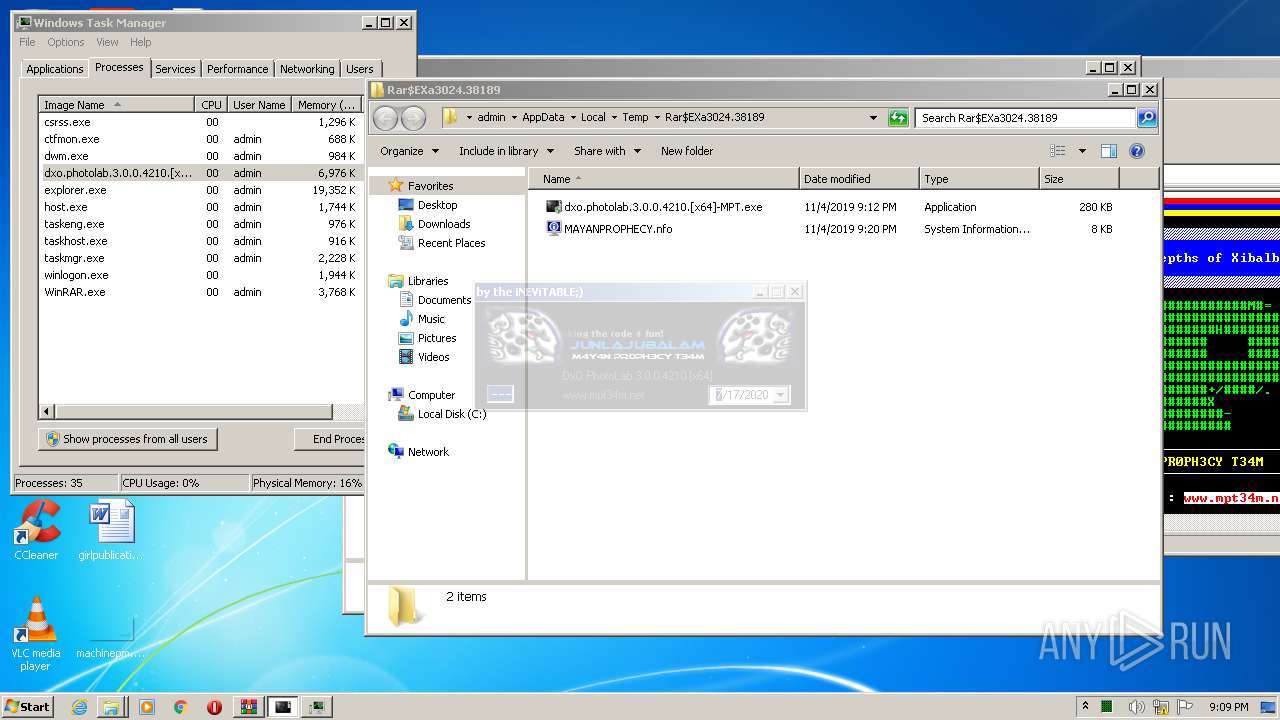
Application was dropped or rewritten from another process
- dxo.photolab.3.0.0.4210.[x64]-MPT.exe (PID: 2084)
- dxo.photolab.3.0.0.4210.[x64]-MPT.exe (PID: 3528)
Loads dropped or rewritten executable
- dxo.photolab.3.0.0.4210.[x64]-MPT.exe (PID: 3528)
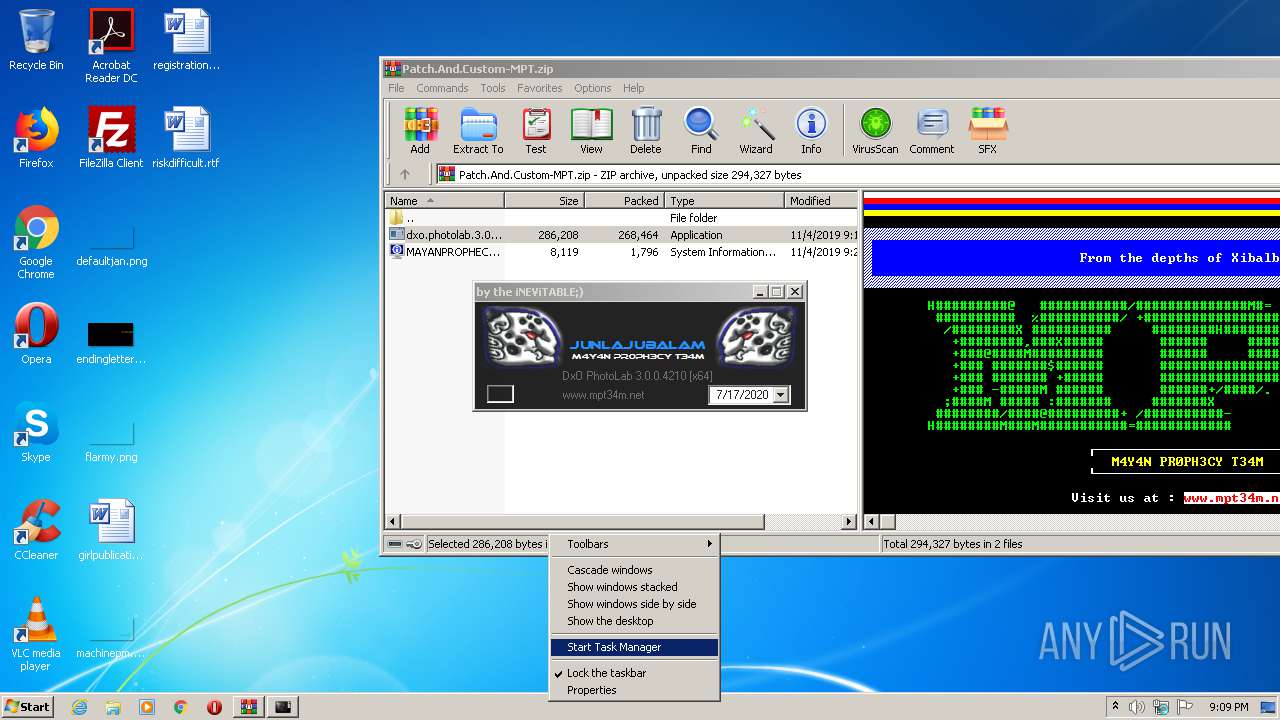
SUSPICIOUS
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3024)
- dxo.photolab.3.0.0.4210.[x64]-MPT.exe (PID: 3528)
Creates files in the program directory
- dxo.photolab.3.0.0.4210.[x64]-MPT.exe (PID: 3528)
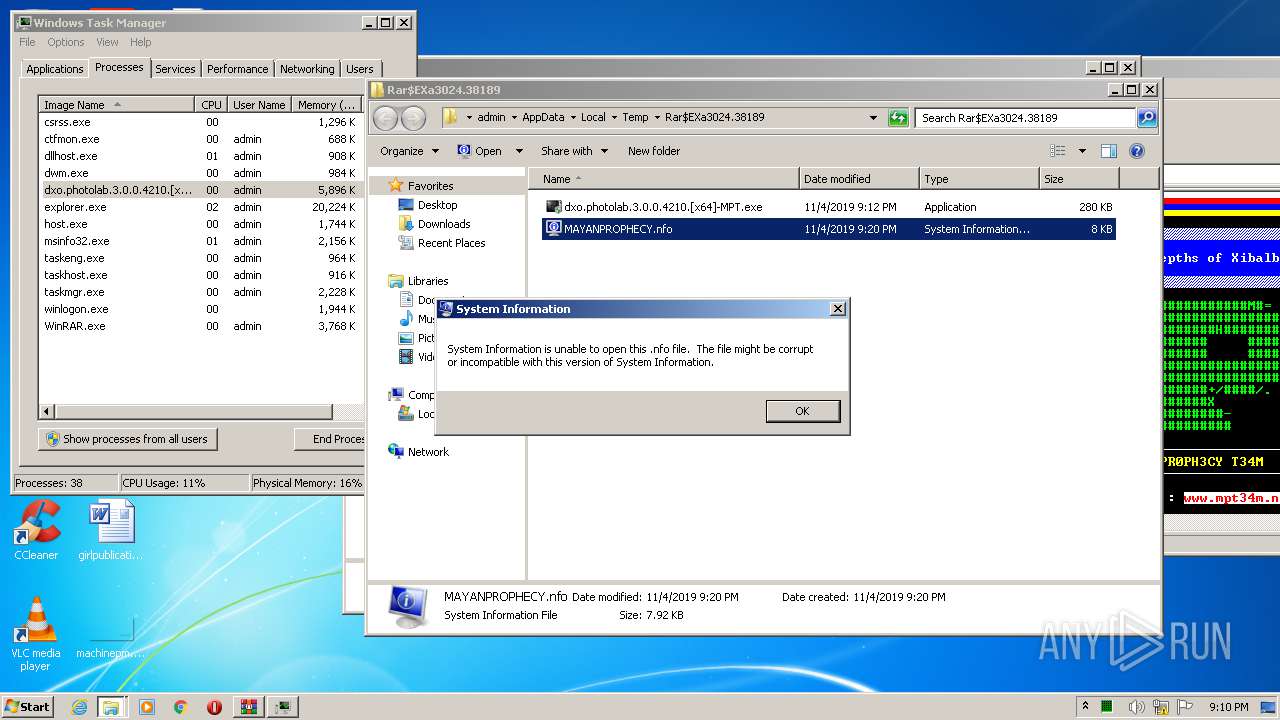
INFO
Manual execution by user
- taskmgr.exe (PID: 3632)
- msinfo32.exe (PID: 3812)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:11:04 22:20:21 |
| ZipCRC: | 0x6e71048a |
| ZipCompressedSize: | 1796 |
| ZipUncompressedSize: | 8119 |
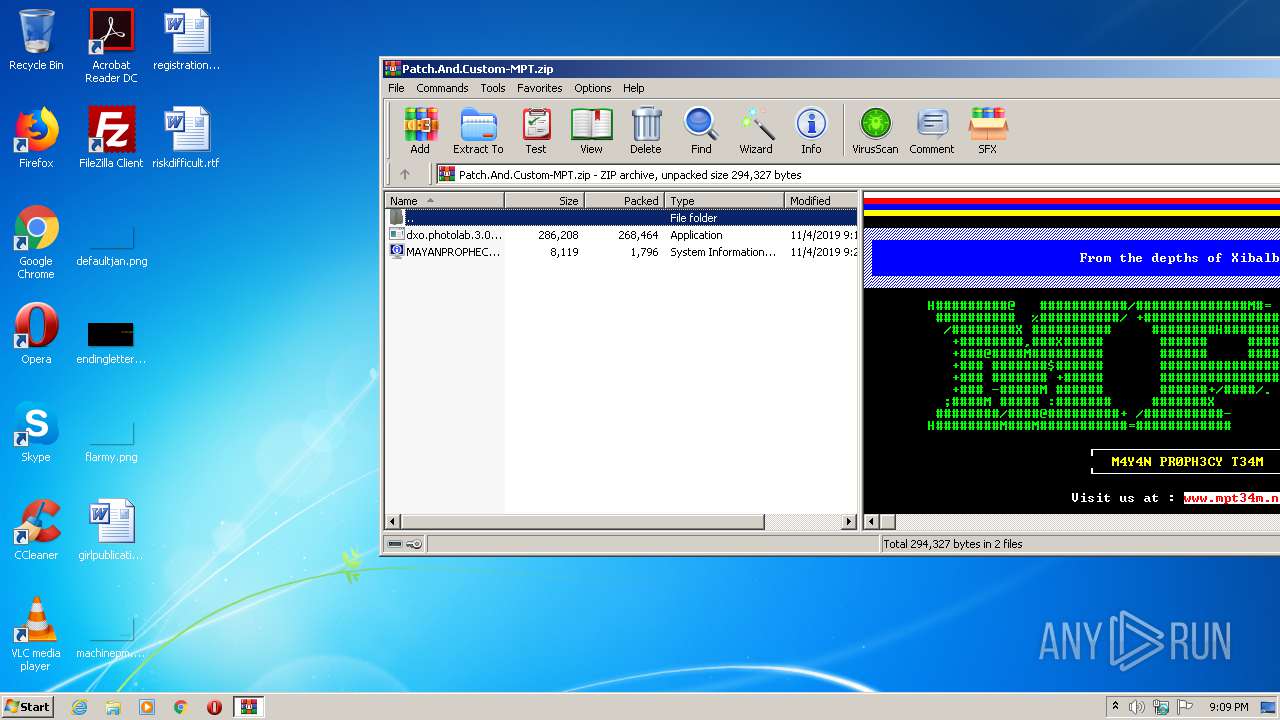
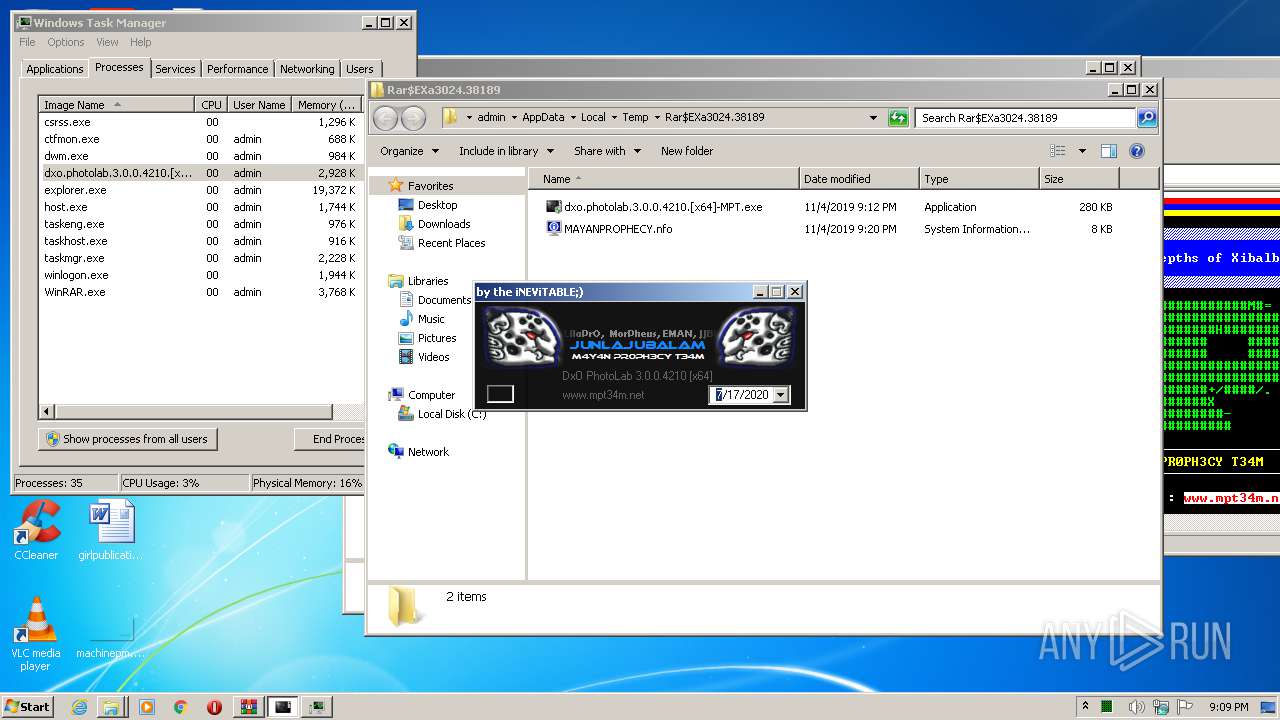
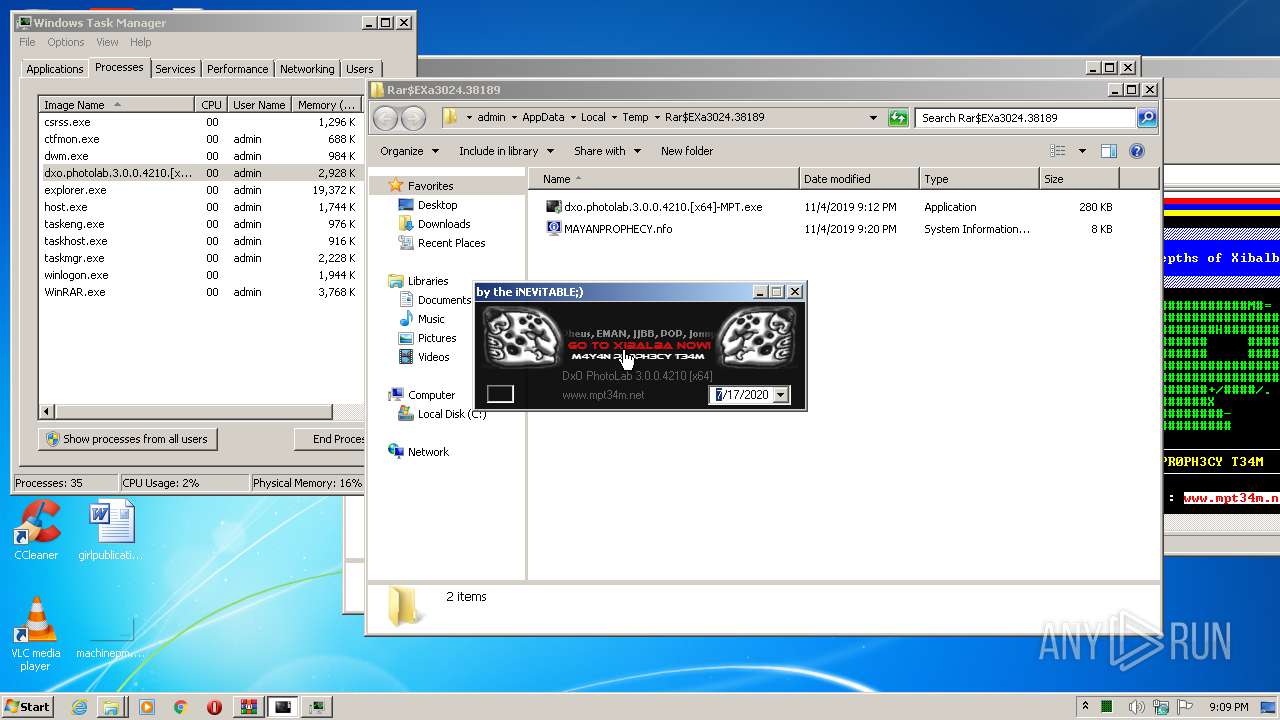
| ZipFileName: | MAYANPROPHECY.nfo |
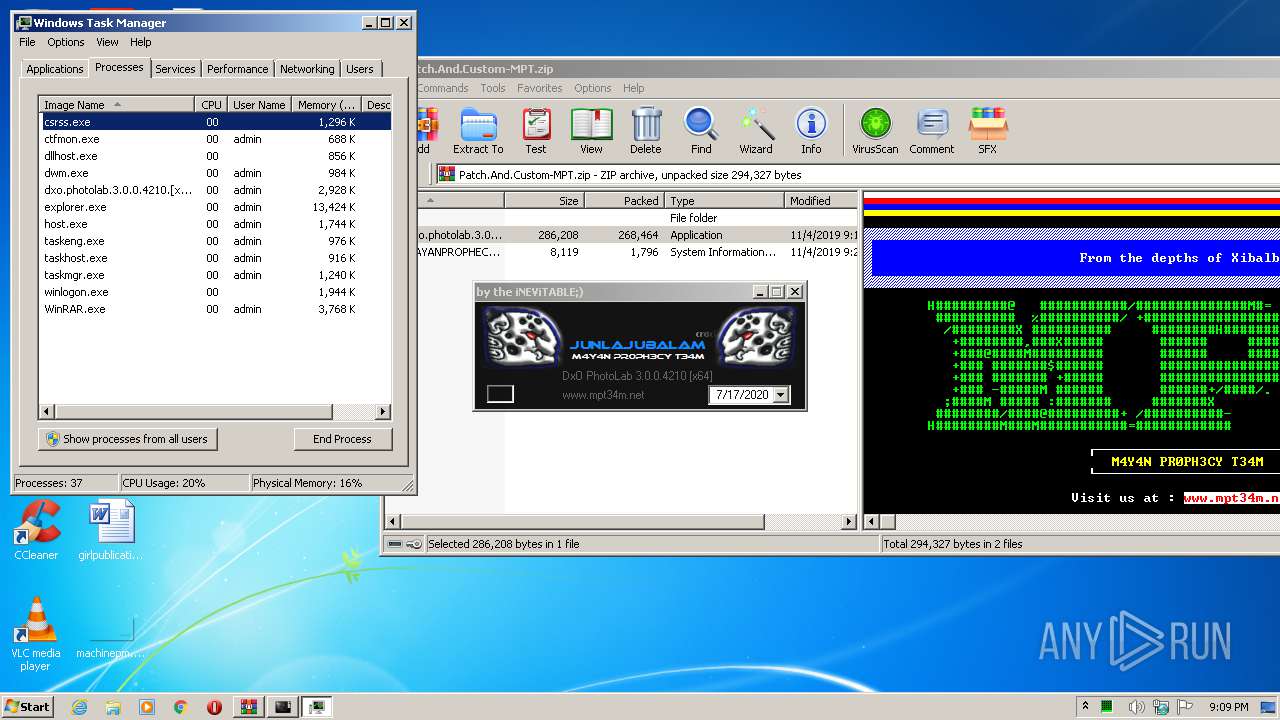
Total processes
46
Monitored processes
5
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
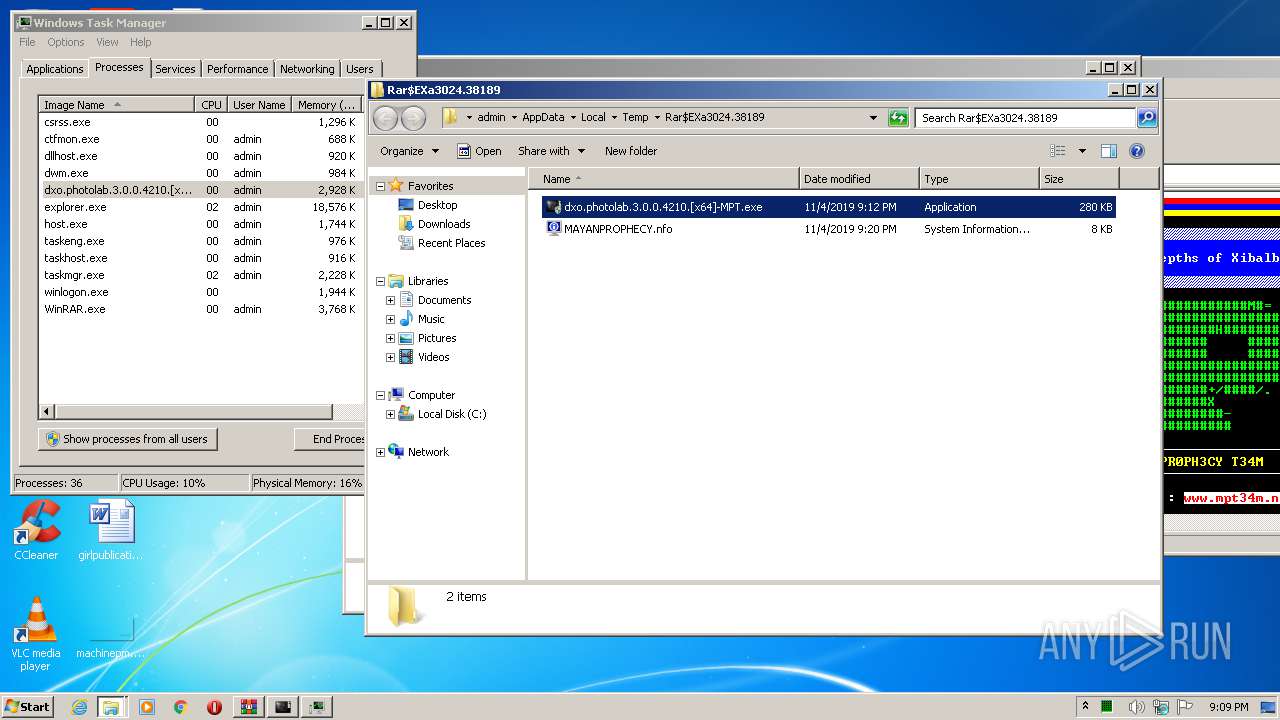
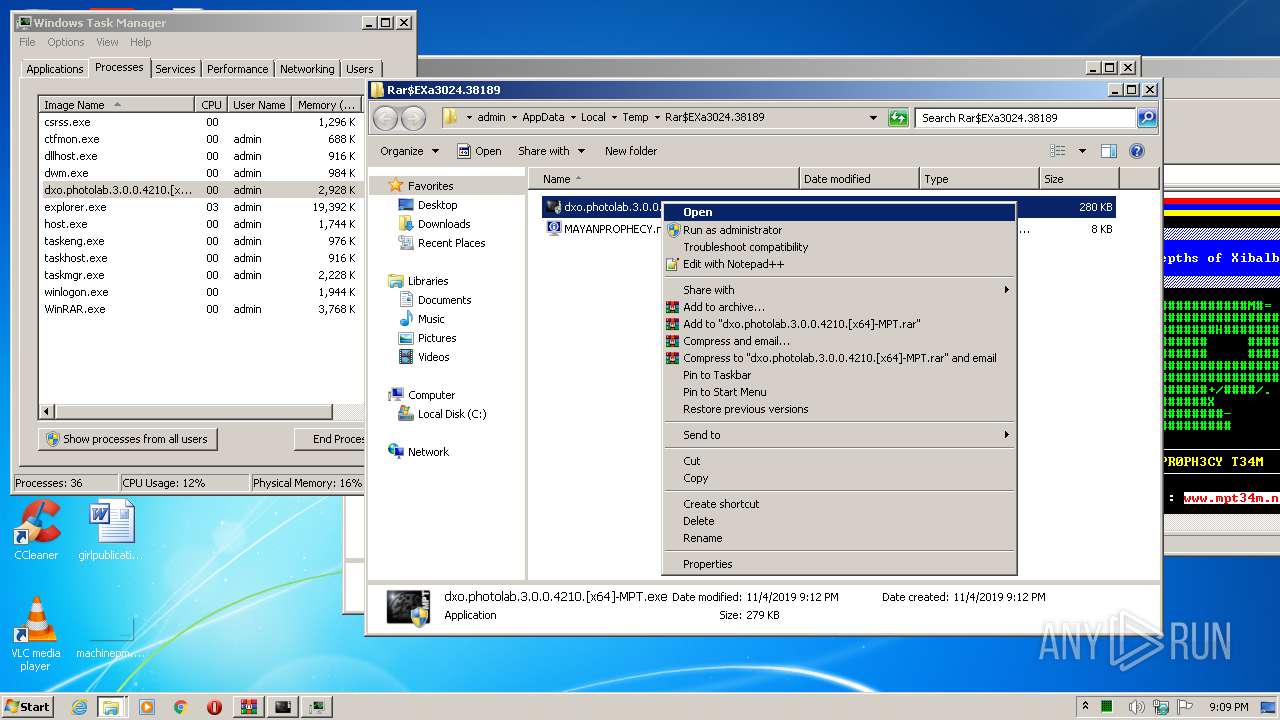
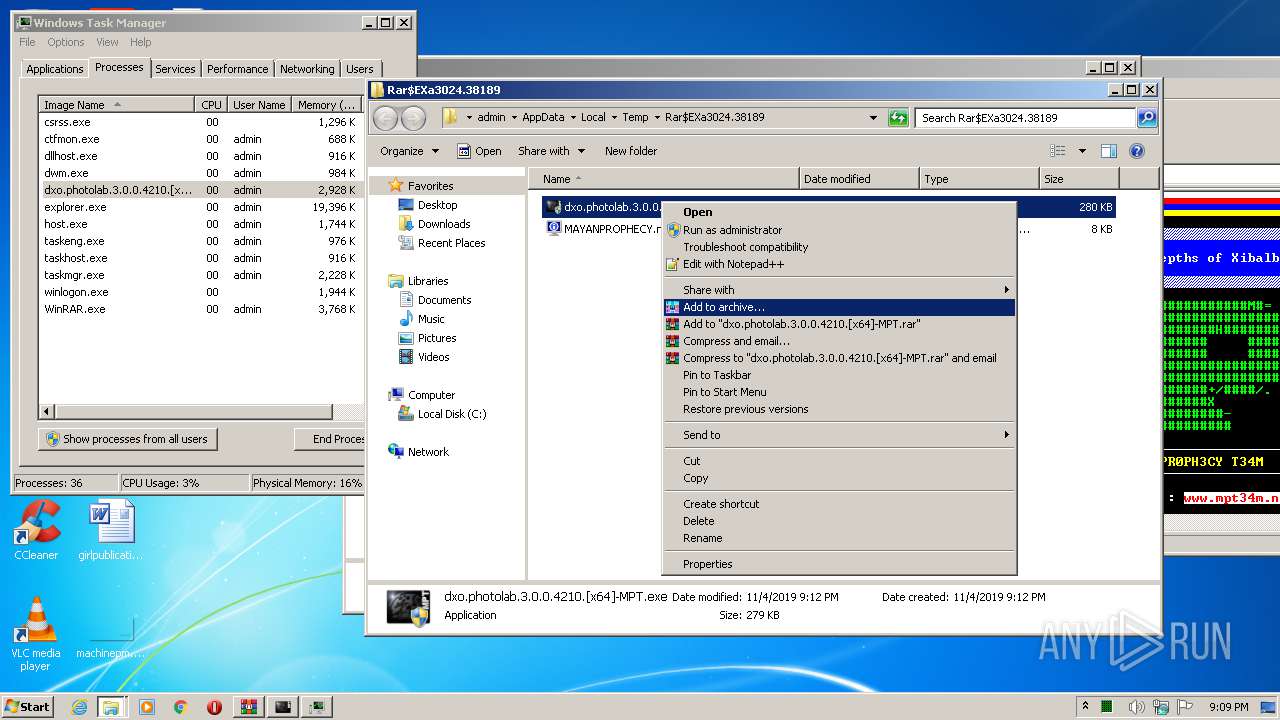
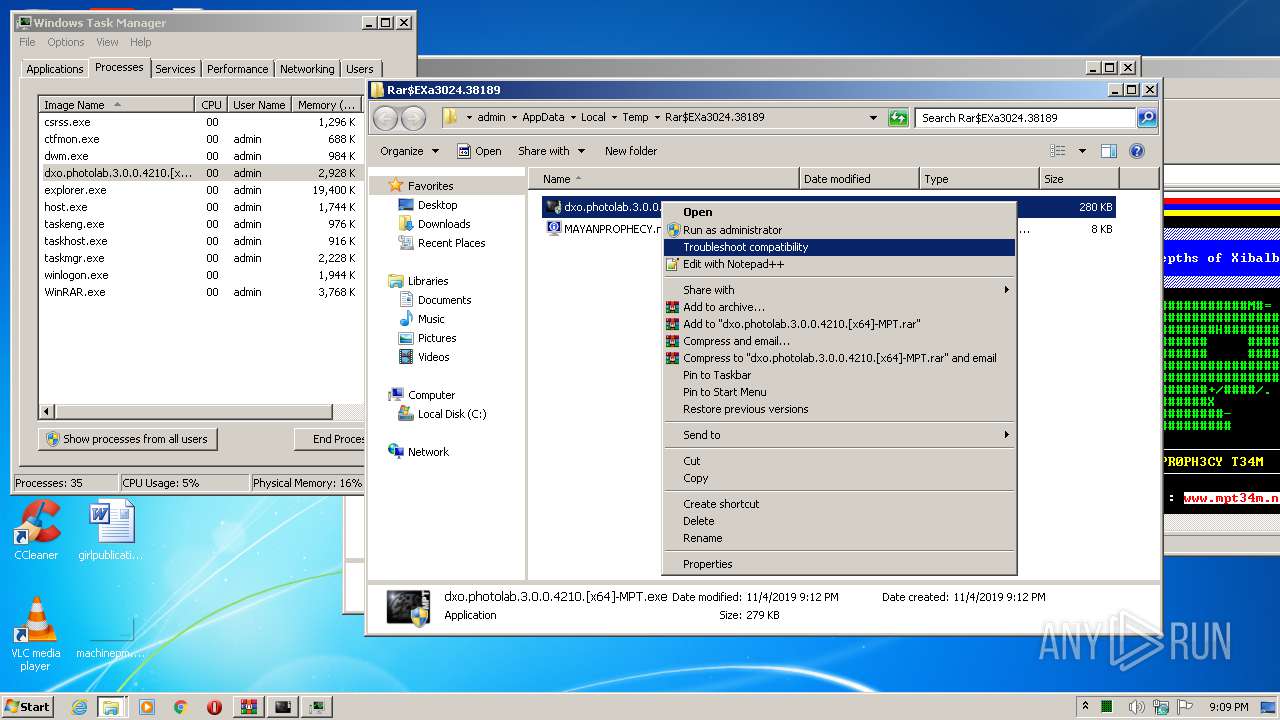
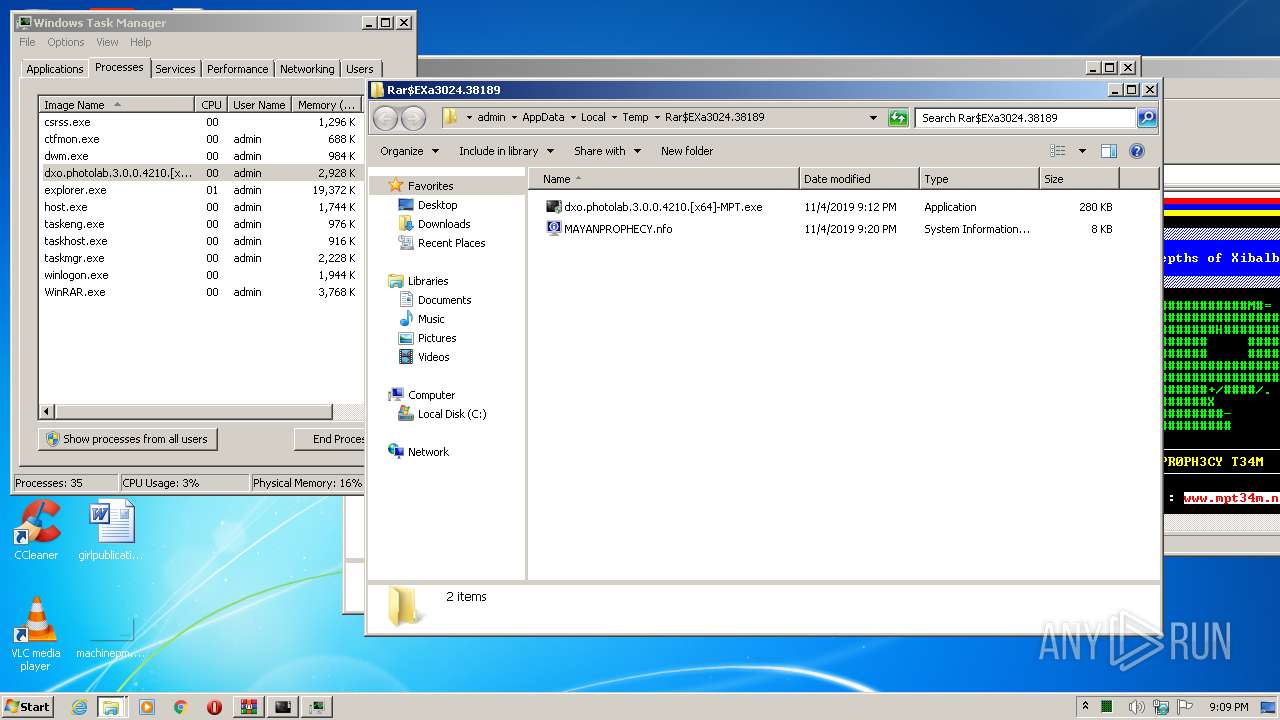
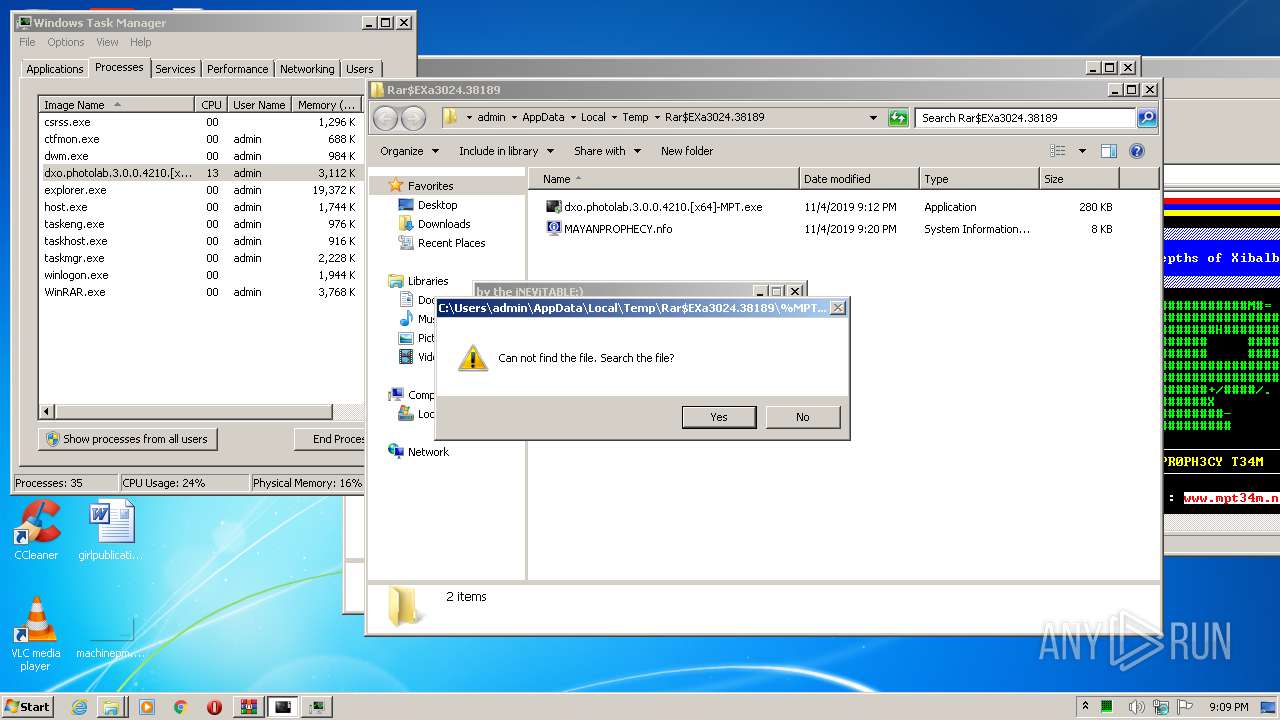
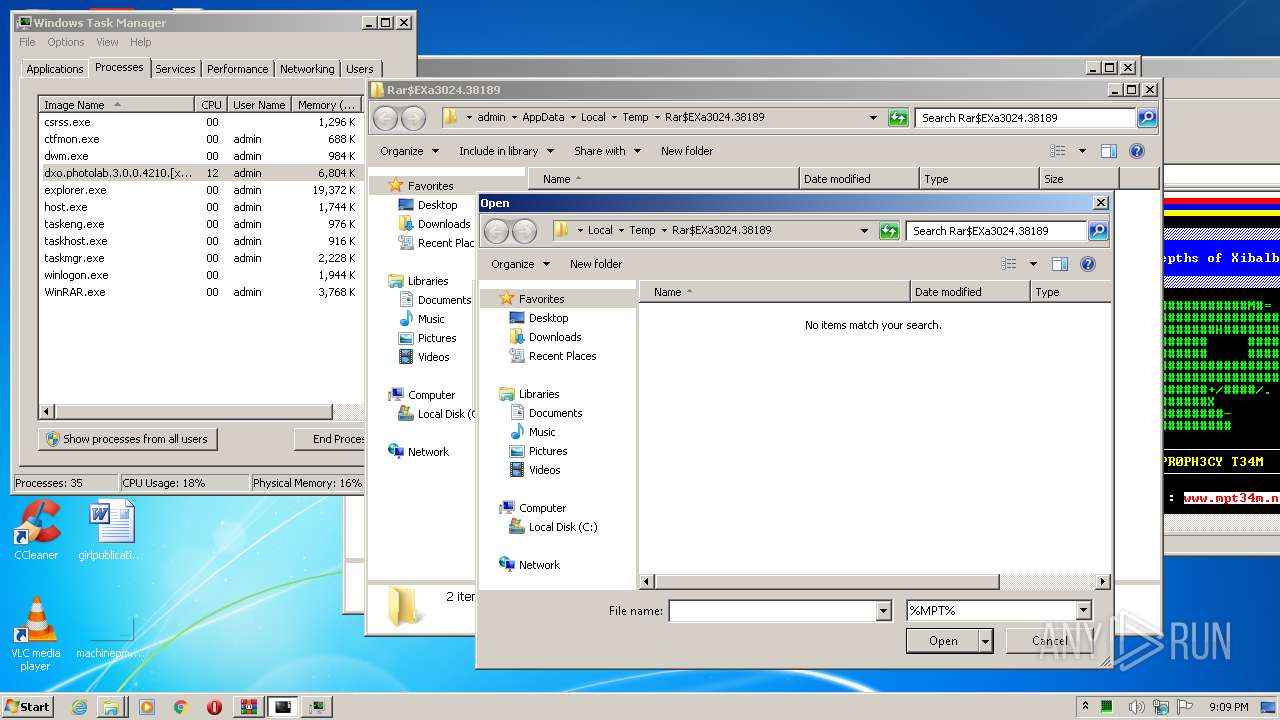
| 2084 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa3024.38189\dxo.photolab.3.0.0.4210.[x64]-MPT.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa3024.38189\dxo.photolab.3.0.0.4210.[x64]-MPT.exe | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
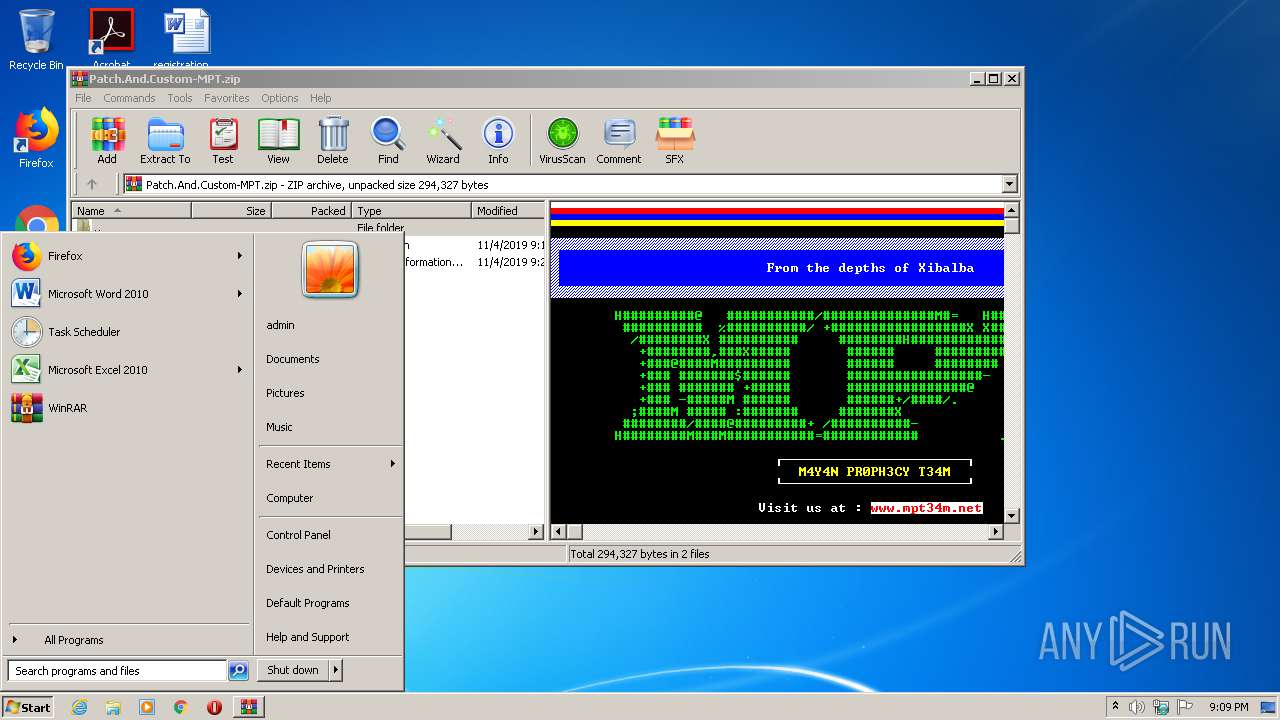
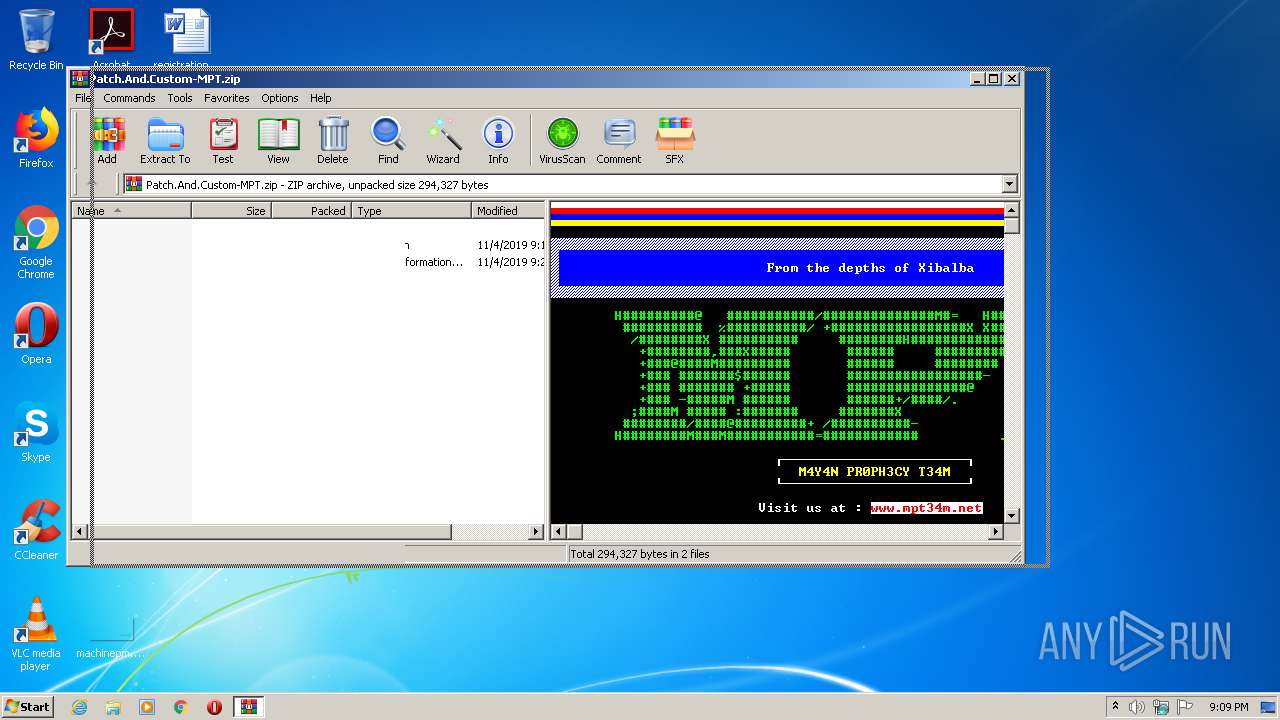
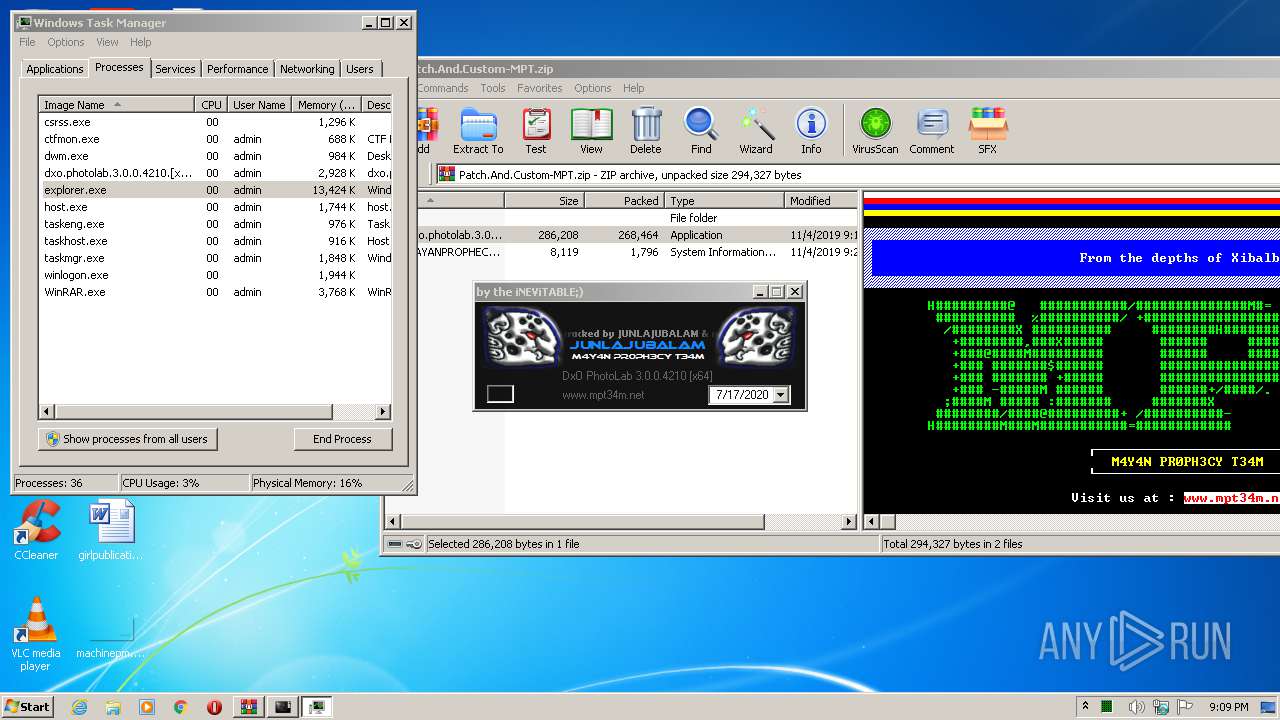
| 3024 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Patch.And.Custom-MPT.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3528 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa3024.38189\dxo.photolab.3.0.0.4210.[x64]-MPT.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa3024.38189\dxo.photolab.3.0.0.4210.[x64]-MPT.exe | WinRAR.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 3221225547 Modules
| |||||||||||||||
| 3632 | "C:\Windows\system32\taskmgr.exe" /4 | C:\Windows\system32\taskmgr.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Task Manager Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3812 | "C:\Windows\system32\msinfo32.exe" "C:\Users\admin\AppData\Local\Temp\Rar$EXa3024.38189\MAYANPROPHECY.nfo" | C:\Windows\system32\msinfo32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: System Information Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 403
Read events
1 353
Write events
49
Delete events
1
Modification events
| (PID) Process: | (3024) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3024) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3024) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\132\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3024) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Patch.And.Custom-MPT.zip | |||
| (PID) Process: | (3024) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3024) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3024) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3024) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3024) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\132\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\msinfo32.exe,-10001 |
Value: System Information File | |||
| (PID) Process: | (3024) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
6
Suspicious files
0
Text files
2
Unknown types
1
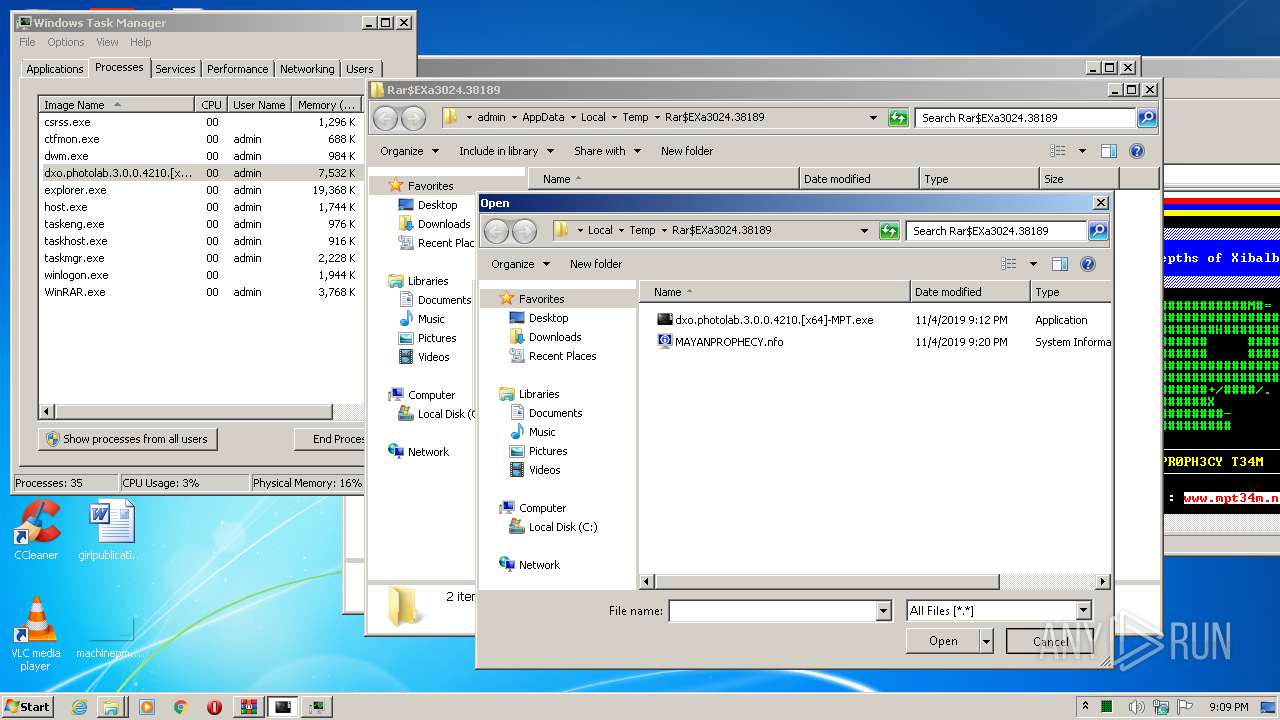
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3024 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3024.38189\MAYANPROPHECY.nfo | text | |
MD5:— | SHA256:— | |||
| 3024 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3024.38189\dxo.photolab.3.0.0.4210.[x64]-MPT.exe | executable | |
MD5:— | SHA256:— | |||
| 3528 | dxo.photolab.3.0.0.4210.[x64]-MPT.exe | C:\ProgramData\DxO Labs\Licenses\dxophotolab3.lic | text | |
MD5:— | SHA256:— | |||
| 3528 | dxo.photolab.3.0.0.4210.[x64]-MPT.exe | C:\Users\admin\AppData\Local\Temp\9CE5948F6F706809AD1DF3709868DF94.dll | executable | |
MD5:459AB623C4848CC699392078368EE335 | SHA256:01778AA8B5C4BB01F823097544520A556D6E623C1E35EC317FD1ECB03E3B69EA | |||
| 3528 | dxo.photolab.3.0.0.4210.[x64]-MPT.exe | C:\Users\admin\AppData\Local\Temp\64F4EA4C8142CAC73E06647D59A699D1.dll | executable | |
MD5:14DD1F05C6BD3CE4ACAB3EBDB9F0903B | SHA256:9A9296A1CC6C243E166B301346C4CD9DEC45028BBC80FDE3903B6C3740C6A239 | |||
| 3528 | dxo.photolab.3.0.0.4210.[x64]-MPT.exe | C:\Users\admin\AppData\Local\Temp\dup2patcher.dll | executable | |
MD5:— | SHA256:— | |||
| 3528 | dxo.photolab.3.0.0.4210.[x64]-MPT.exe | C:\Users\admin\AppData\Local\Temp\7CEB9B2A0E395BD64E74381485A106AF.dll | executable | |
MD5:5AFB011D9DB047BB0400C5C5CA2E450B | SHA256:125FC74E03435B3E0EDE0FF523D625D9C1FBB299286E9E2DBD1442E506150DA6 | |||
| 3528 | dxo.photolab.3.0.0.4210.[x64]-MPT.exe | C:\Users\admin\AppData\Local\Temp\Berlin Sans FB.TTF | odttf | |
MD5:FE2027C27B6A24505F548C6FD2E1076D | SHA256:0B6044C72E67AAAE9C2AE3C8B4BB06D066FDBC02779C68E3883984ACBBE24CB8 | |||
| 3528 | dxo.photolab.3.0.0.4210.[x64]-MPT.exe | C:\Users\admin\AppData\Local\Temp\bassmod.dll | executable | |
MD5:E4EC57E8508C5C4040383EBE6D367928 | SHA256:8AD9E47693E292F381DA42DDC13724A3063040E51C26F4CA8E1F8E2F1DDD547F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report