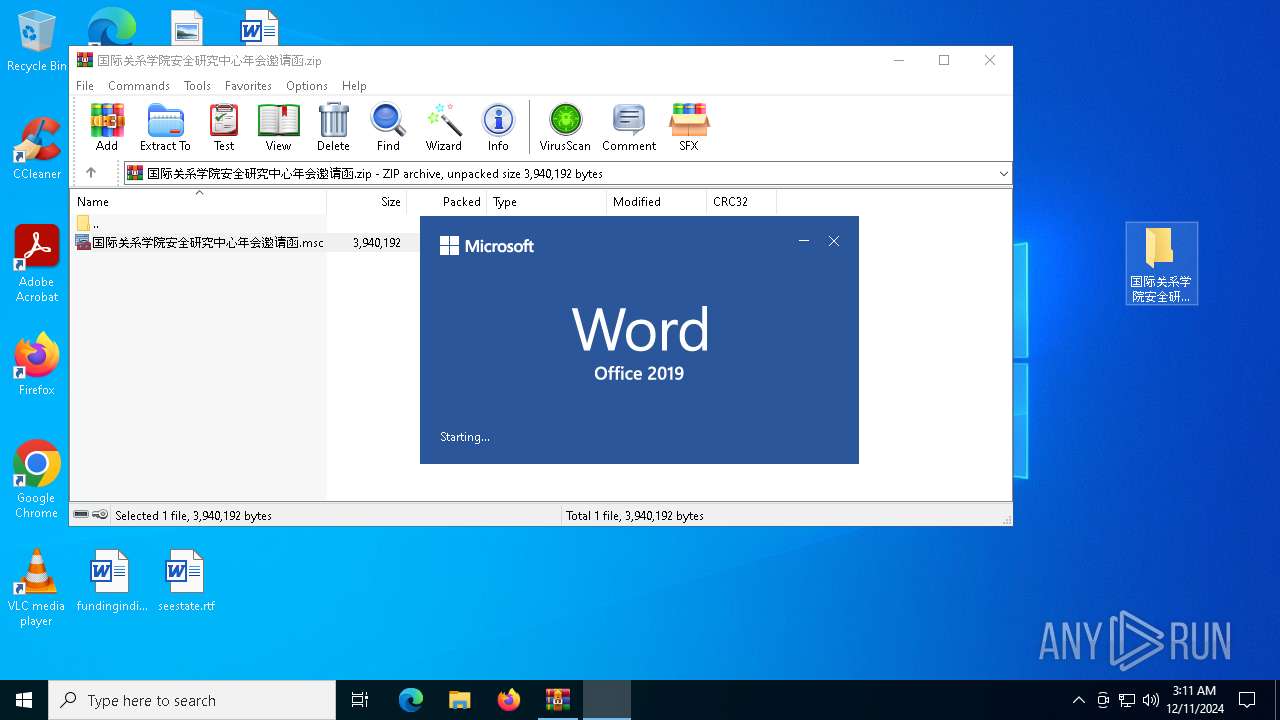
| File name: | 国际关系学院安全研究中心年会邀请函.zip |
| Full analysis: | https://app.any.run/tasks/b03d89bf-175a-4b4e-a9b7-3519ab87daec |
| Verdict: | Malicious activity |
| Analysis date: | December 11, 2024, 03:11:08 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | 529B207EE067CA0B369D1120CAB04E19 |
| SHA1: | 8B248E7BC2275FAFA299F92989A4A178D9A945D7 |
| SHA256: | CC7F5FF0CD0E5E8BBA2FFEF5928D143006DABED0E17054F4DB8F577B7989A898 |
| SSDEEP: | 49152:fxyIrM5zH+zHlXiyCFidRFCyvD8wXGm1DV64XUbUPsd9/wBbixlKcTbPVbj4tkTM:fxyP5D+zHlitFQRMO1XGUo4XUbUSuBb1 |
MALICIOUS
Creates a new folder (SCRIPT)
- mmc.exe (PID: 7064)
Detects the decoding of a binary file from Base64 (SCRIPT)
- mmc.exe (PID: 7064)
GRIMRESOURCES has been detected (YARA)
- mmc.exe (PID: 7064)
Uses base64 encoding (SCRIPT)
- mmc.exe (PID: 7064)
SUSPICIOUS
Reads Microsoft Outlook installation path
- mmc.exe (PID: 7064)
Reads Internet Explorer settings
- mmc.exe (PID: 7064)
Creates FileSystem object to access computer's file system (SCRIPT)
- mmc.exe (PID: 7064)
Creates a Stream, which may work with files, input/output devices, pipes, or TCP/IP sockets (SCRIPT)
- mmc.exe (PID: 7064)
Writes binary data to a Stream object (SCRIPT)
- mmc.exe (PID: 7064)
Runs shell command (SCRIPT)
- mmc.exe (PID: 7064)
Sets XML DOM element text (SCRIPT)
- mmc.exe (PID: 7064)
Saves data to a binary file (SCRIPT)
- mmc.exe (PID: 7064)
Reads security settings of Internet Explorer
- XunJie.exe (PID: 6032)
Executable content was dropped or overwritten
- mmc.exe (PID: 7064)
Checks Windows Trust Settings
- XunJie.exe (PID: 6032)
INFO
Manual execution by a user
- mmc.exe (PID: 6996)
- mmc.exe (PID: 7064)
Reads security settings of Internet Explorer
- mmc.exe (PID: 7064)
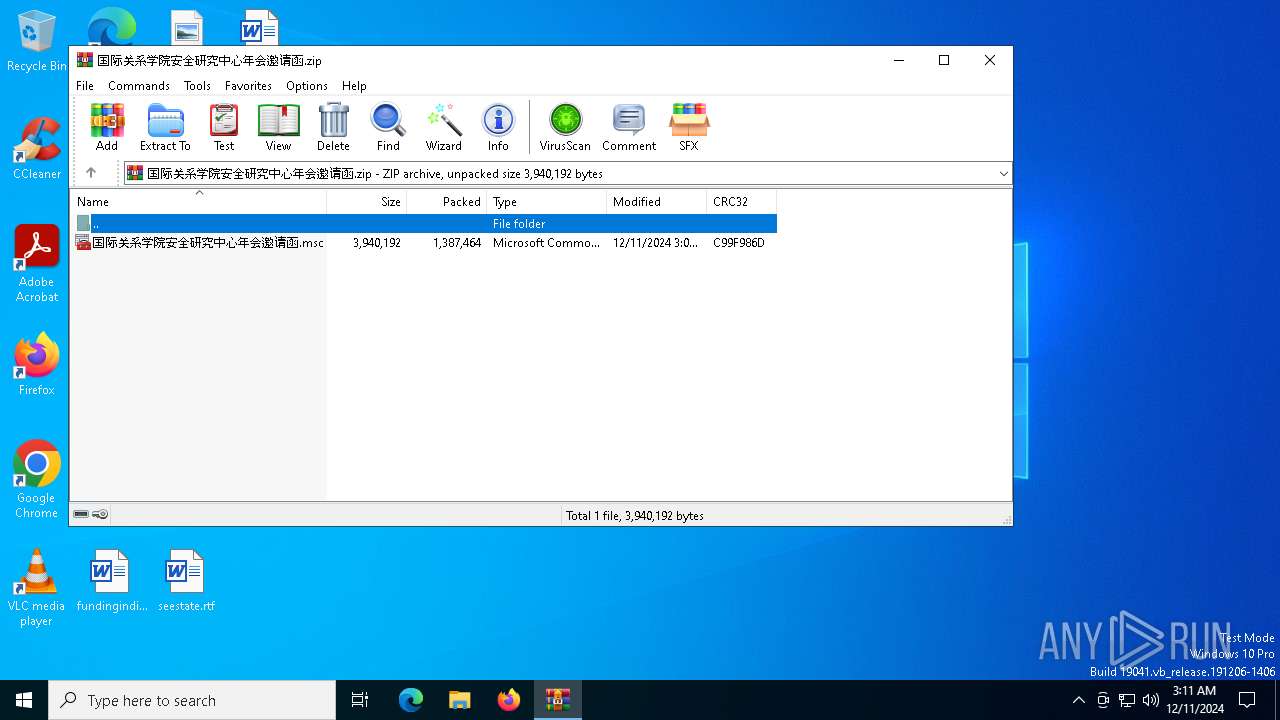
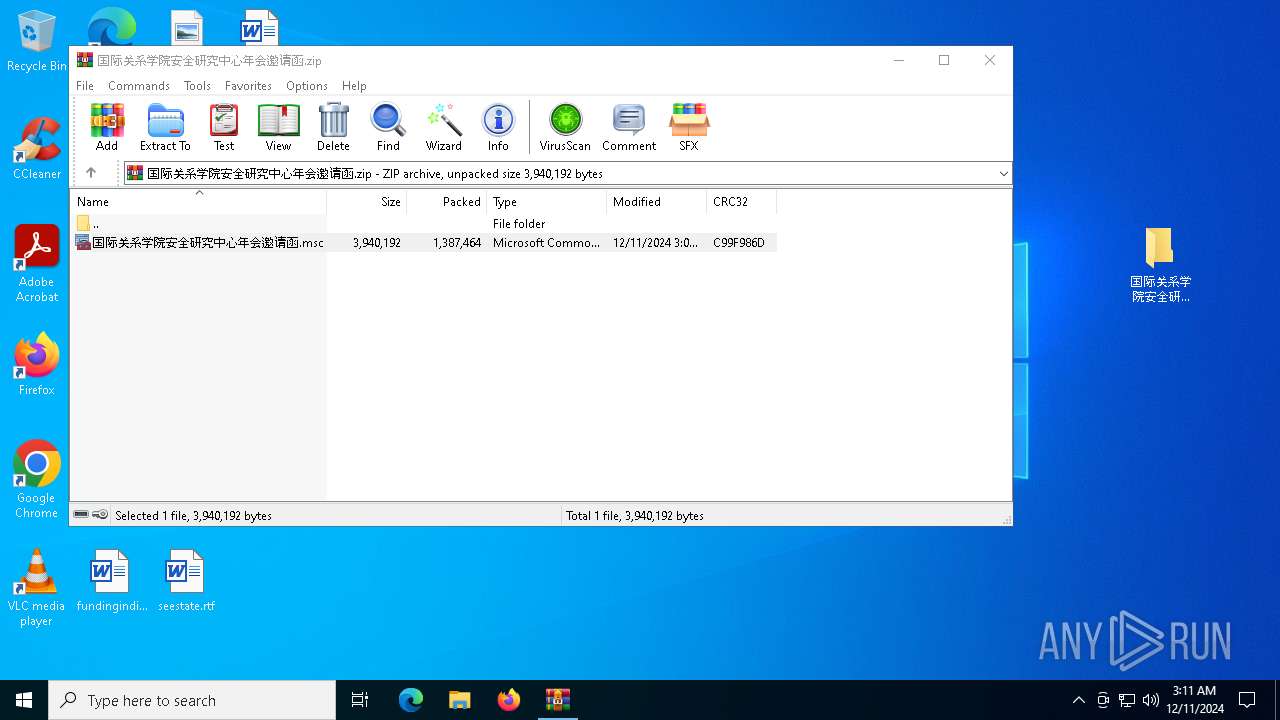
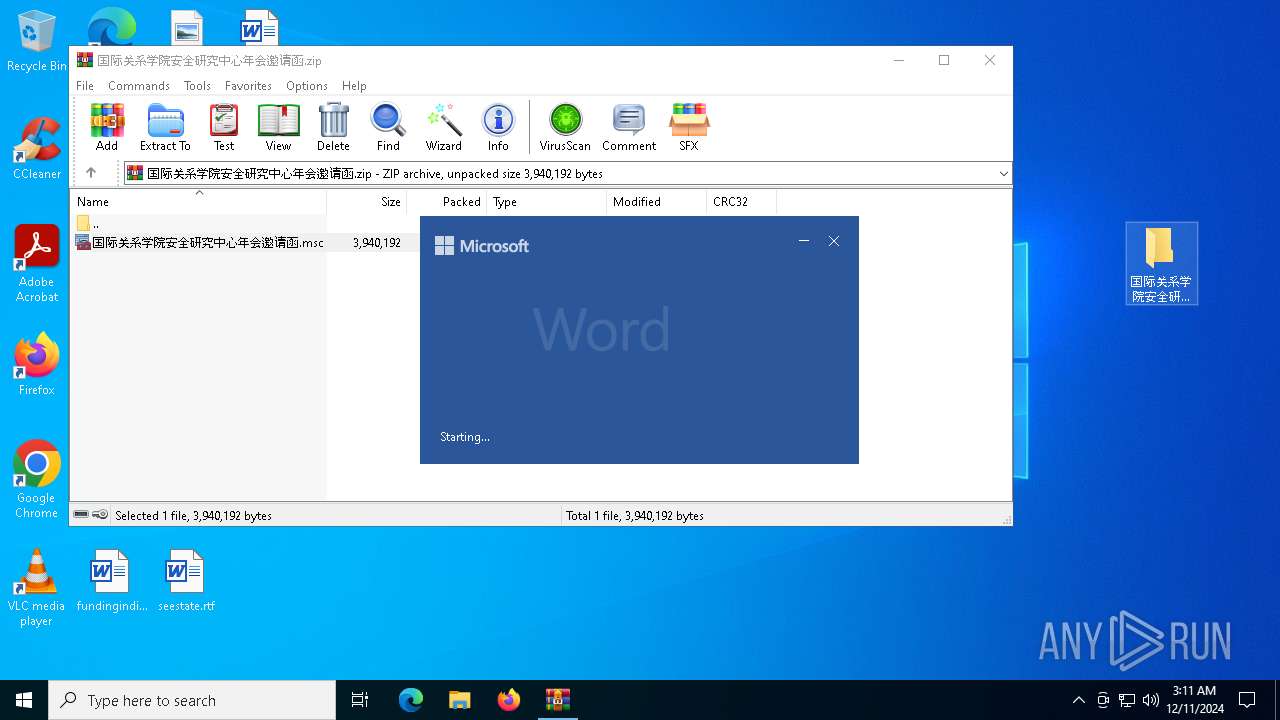
The process uses the downloaded file
- WinRAR.exe (PID: 6280)
- mmc.exe (PID: 7064)
- WINWORD.EXE (PID: 6156)
Creates files or folders in the user directory
- mmc.exe (PID: 7064)
Checks proxy server information
- mmc.exe (PID: 7064)
- XunJie.exe (PID: 6032)
Create files in a temporary directory
- mmc.exe (PID: 7064)
Reads Microsoft Office registry keys
- mmc.exe (PID: 7064)
Creates files in the program directory
- mmc.exe (PID: 7064)
Checks supported languages
- XunJie.exe (PID: 6032)
Drops encrypted VBS script (Microsoft Script Encoder)
- WINWORD.EXE (PID: 6156)
Sends debugging messages
- WINWORD.EXE (PID: 6156)
Reads the machine GUID from the registry
- XunJie.exe (PID: 6032)
Reads the computer name
- XunJie.exe (PID: 6032)
Potential modification of remote process state (Base64 Encoded 'SetThreadContext')
- mmc.exe (PID: 7064)
The sample compiled with english language support
- mmc.exe (PID: 7064)
Potential library load (Base64 Encoded 'LoadLibrary')
- mmc.exe (PID: 7064)
Potential access to remote process (Base64 Encoded 'OpenProcess')
- mmc.exe (PID: 7064)
Potential dynamic function import (Base64 Encoded 'GetProcAddress')
- mmc.exe (PID: 7064)
Reads the software policy settings
- XunJie.exe (PID: 6032)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0808 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2024:12:11 11:07:46 |
| ZipCRC: | 0xc99f986d |
| ZipCompressedSize: | 1387464 |
| ZipUncompressedSize: | 3940192 |
| ZipFileName: | 国际关系学院安全研究中心年会邀请函.msc |
Total processes
138
Monitored processes
7
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3876 | "C:\Program Files\Microsoft Office\root\VFS\ProgramFilesCommonX64\Microsoft Shared\OFFICE16\ai.exe" "BFD860DD-3823-4A73-A44D-254B3FD59040" "96C73DFB-8CBA-4C91-970E-43303486C2C5" "6156" | C:\Program Files\Microsoft Office\root\VFS\ProgramFilesCommonX64\Microsoft Shared\OFFICE16\ai.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Artificial Intelligence (AI) Host for the Microsoft® Windows® Operating System and Platform x64. Version: 0.12.2.0 Modules
| |||||||||||||||
| 6016 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | XunJie.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6032 | "C:\Program Files\XunJie\XunJie.exe" upgrade | C:\Program Files\XunJie\XunJie.exe | mmc.exe | ||||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 6156 | "C:\Program Files\Microsoft Office\Root\Office16\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\国际关系学院安全研究中心年会邀请函.docx" /o "" | C:\Program Files\Microsoft Office\root\Office16\WINWORD.EXE | mmc.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Word Version: 16.0.16026.20146 Modules
| |||||||||||||||
| 6280 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\国际关系学院安全研究中心年会邀请函.zip | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 6996 | "C:\WINDOWS\system32\mmc.exe" "C:\Users\admin\Desktop\国际关系学院安全研究中心年会邀请函.msc" | C:\Windows\System32\mmc.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Management Console Exit code: 3221226540 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7064 | "C:\WINDOWS\system32\mmc.exe" "C:\Users\admin\Desktop\国际关系学院安全研究中心年会邀请函.msc" | C:\Windows\System32\mmc.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Management Console Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
20 470
Read events
20 046
Write events
395
Delete events
29
Modification events
| (PID) Process: | (6280) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (6280) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (6280) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (6280) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\国际关系学院安全研究中心年会邀请函.zip | |||
| (PID) Process: | (6280) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6280) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6280) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6280) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6280) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {7A80E4A8-8005-11D2-BCF8-00C04F72C717} {000214FA-0000-0000-C000-000000000046} 0xFFFF |
Value: 01000000000000002B6832567A4BDB01 | |||
| (PID) Process: | (7064) mmc.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
Executable files
17
Suspicious files
123
Text files
40
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7064 | mmc.exe | C:\Program Files\XunJie\libgcc_s_dw2-1.dll | executable | |
MD5:043B39434829CE93637B1801D57B2082 | SHA256:4D2E2D408D399D066B0AAEF2047F7A33515C13C589832DE0D9F1BA87A530C394 | |||
| 7064 | mmc.exe | C:\Program Files\XunJie\libwinpthread-1.dll | executable | |
MD5:1F4411C1F66C9CDF96CA9D7F9CAF52D9 | SHA256:B5FE4D6408EF2BAABDD168F4C7250900606468E9AEB24C71E0C833D3D715AE65 | |||
| 6156 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\FontCache\4\CloudFonts\SimHei\33134363409.ttf | — | |
MD5:— | SHA256:— | |||
| 6280 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6280.48892\国际关系学院安全研究中心年会邀请函.msc | xml | |
MD5:D4DCFB3B7C833872A20F05CC5A144D66 | SHA256:823C7D02275CD226D7746BAD12155C8933499709F1000094683A3E8F90C4D209 | |||
| 7064 | mmc.exe | C:\Users\admin\AppData\Local\Temp\国际关系学院安全研究中心年会邀请函.docx | document | |
MD5:B57320D4BED84F59324263B8736044A5 | SHA256:BE93B65C3D22FE3FED3FAA9446C94BBA55F66614E4B9883F4518DA883F1EA6D4 | |||
| 6156 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\FontCache\4\CloudFonts\DengXian\54497409372.ttf | — | |
MD5:— | SHA256:— | |||
| 7064 | mmc.exe | C:\Program Files\XunJie\XunJie.exe | executable | |
MD5:A71070F0C6A45470927C908293750428 | SHA256:5FDBE93608742410E4697B359DBEE18CA6D1DF42744CB13C62E591A5417964D5 | |||
| 6156 | WINWORD.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\E2C6CBAF0AF08CF203BA74BF0D0AB6D5_CBDCCBFE4F7A916411C1E69BDD97BB04 | binary | |
MD5:B8A4F15F008F13E02D55DB531694BEDC | SHA256:A0D56EDA9D47B435B4F98ECDBADD7F81E305C30DB6EB287E0C0A028928D4E2A2 | |||
| 6156 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$关系学院安全研究中心年会邀请函.docx | pgc | |
MD5:4A43A155F848489FF5C40289F8414AAA | SHA256:03556E1AC1E78033BC6325D6614A79EBD333B2FBFC14E5BFBC9AF934BEDB6065 | |||
| 6156 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\TokenBroker\Cache\56a61aeb75d8f5be186c26607f4bb213abe7c5ec.tbres | binary | |
MD5:A5CF70386988BA5D25C3ED49A54A48C9 | SHA256:A07E3A9896A9011DD6EB6669603E500DDFC839684E60A04BADFD68B6A8192E56 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
16
TCP/UDP connections
97
DNS requests
31
Threats
22
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6068 | svchost.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6068 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6156 | WINWORD.EXE | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA77flR%2B3w%2FxBpruV2lte6A%3D | unknown | — | — | whitelisted |
6504 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
6156 | WINWORD.EXE | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | unknown | — | — | whitelisted |
6156 | WINWORD.EXE | GET | 200 | 2.16.164.49:80 | http://crl.microsoft.com/pki/crl/products/MicCodSigPCA_08-31-2010.crl | unknown | — | — | whitelisted |
6156 | WINWORD.EXE | GET | 200 | 2.16.164.49:80 | http://crl.microsoft.com/pki/crl/products/microsoftrootcert.crl | unknown | — | — | whitelisted |
6156 | WINWORD.EXE | GET | 200 | 2.16.164.49:80 | http://crl.microsoft.com/pki/crl/products/MicrosoftTimeStampPCA.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6068 | svchost.exe | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
6068 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5064 | SearchApp.exe | 104.126.37.179:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
5064 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1176 | svchost.exe | 40.126.32.68:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1176 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
officeclient.microsoft.com |
| whitelisted |
roaming.officeapps.live.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6032 | XunJie.exe | Misc activity | ET INFO Observed ZeroSSL SSL/TLS Certificate |
6032 | XunJie.exe | Misc activity | ET INFO Observed ZeroSSL SSL/TLS Certificate |
6032 | XunJie.exe | Misc activity | ET INFO Observed ZeroSSL SSL/TLS Certificate |
6032 | XunJie.exe | Misc activity | ET INFO Observed ZeroSSL SSL/TLS Certificate |
6032 | XunJie.exe | Misc activity | ET INFO Observed ZeroSSL SSL/TLS Certificate |
6032 | XunJie.exe | Misc activity | ET INFO Observed ZeroSSL SSL/TLS Certificate |
6032 | XunJie.exe | Misc activity | ET INFO Observed ZeroSSL SSL/TLS Certificate |
6032 | XunJie.exe | Misc activity | ET INFO Observed ZeroSSL SSL/TLS Certificate |
6032 | XunJie.exe | Misc activity | ET INFO Observed ZeroSSL SSL/TLS Certificate |
6032 | XunJie.exe | Misc activity | ET INFO Observed ZeroSSL SSL/TLS Certificate |
Process | Message |
|---|---|
WINWORD.EXE | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|
WINWORD.EXE | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|
WINWORD.EXE | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|