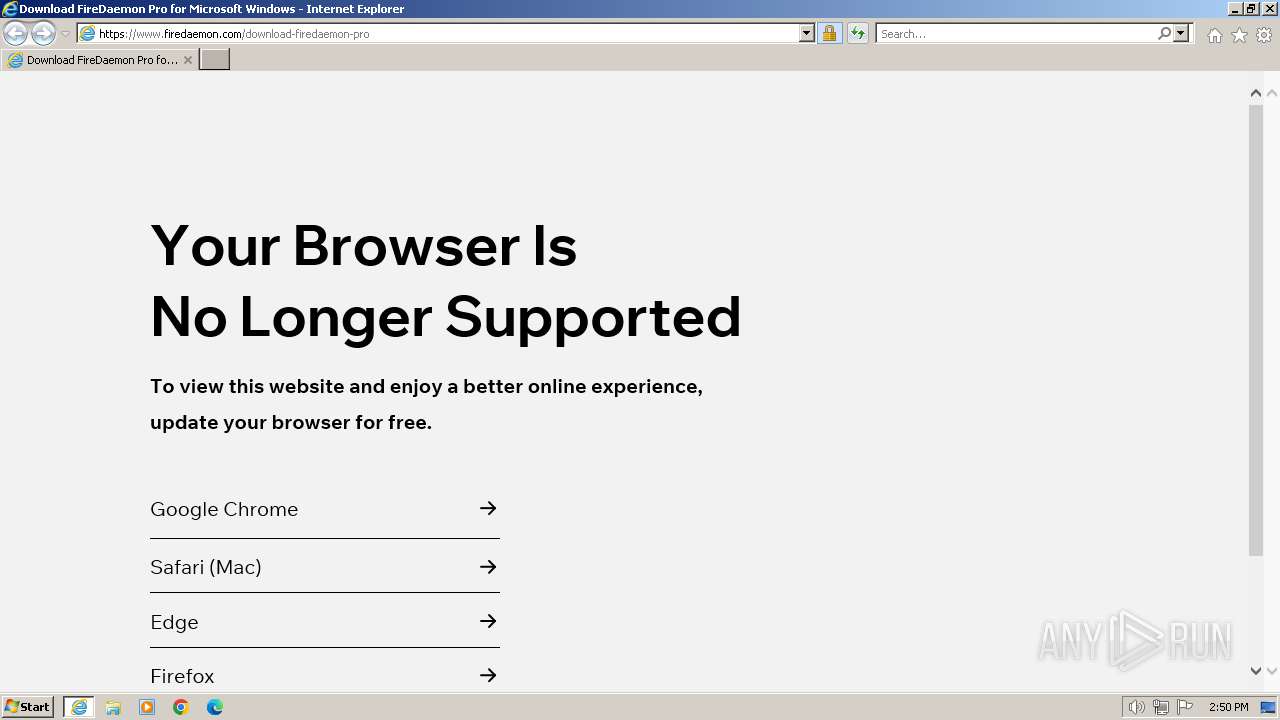
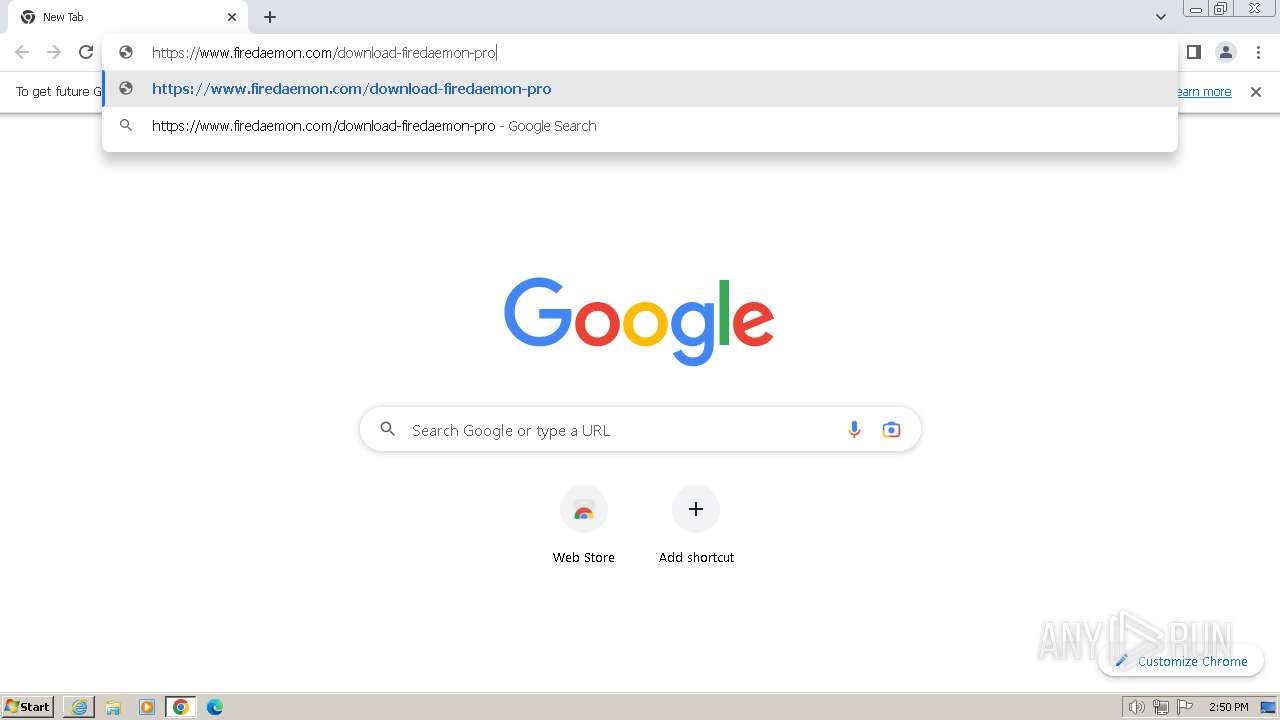
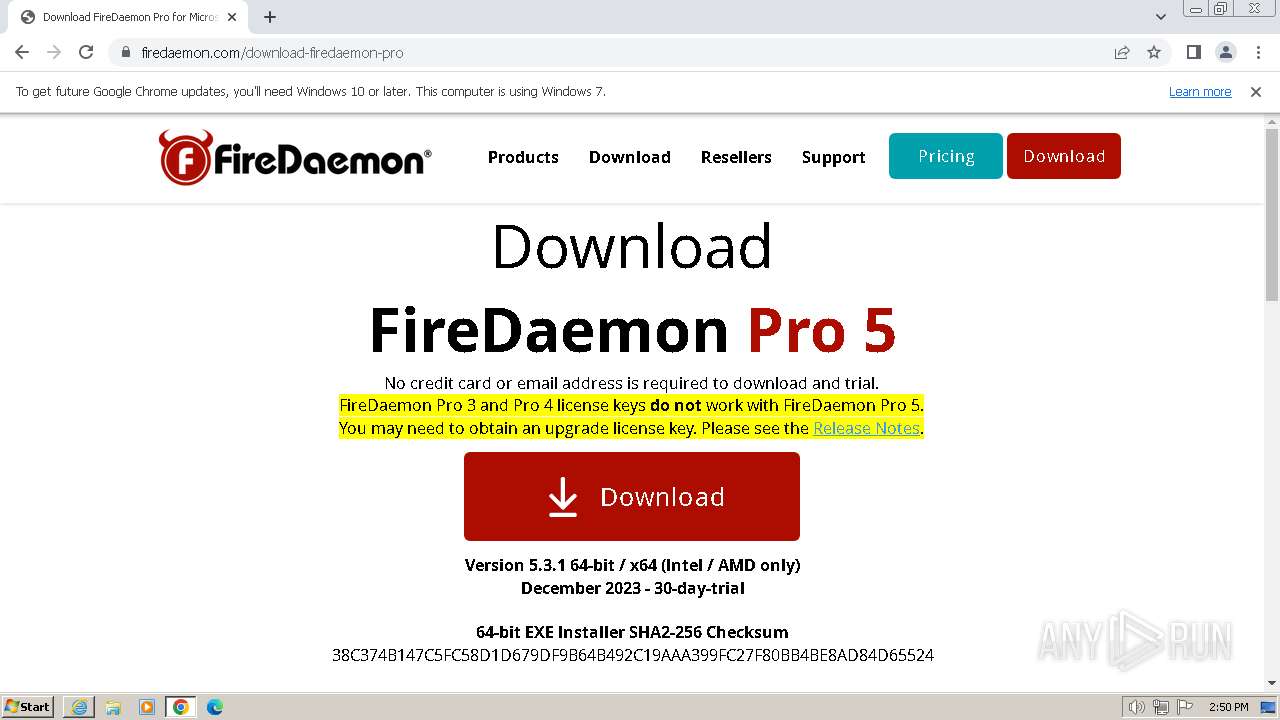
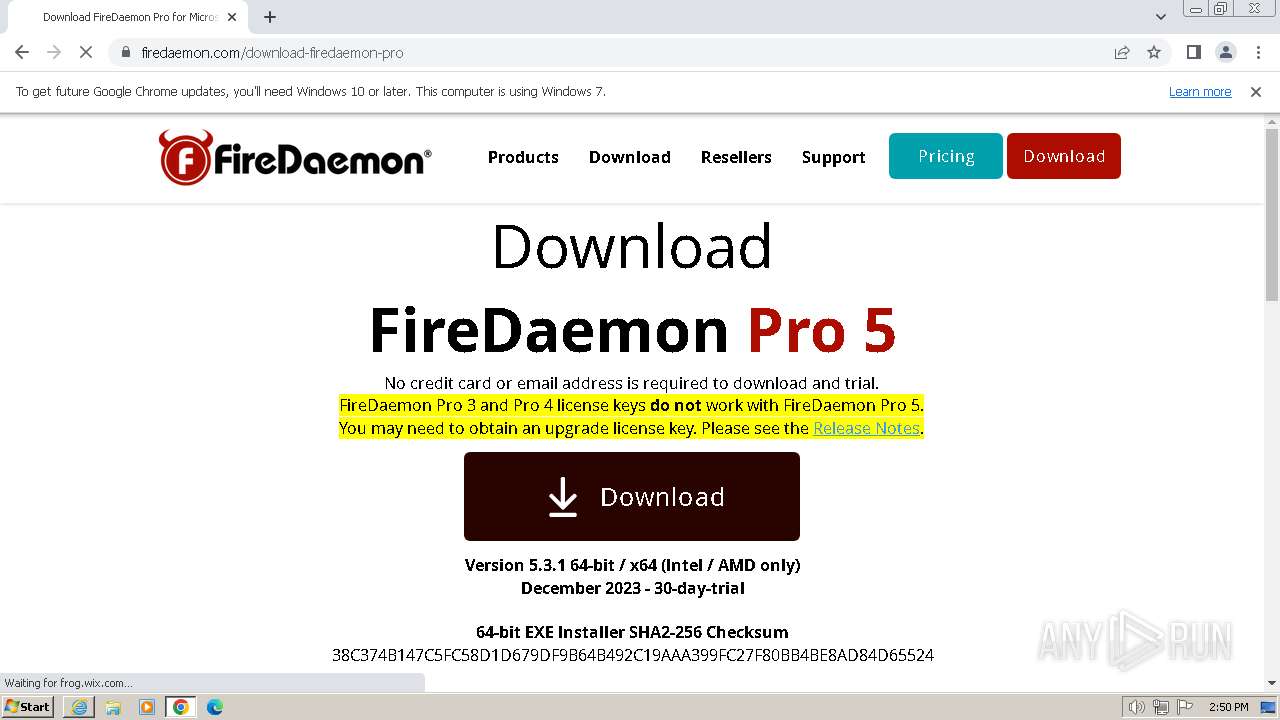
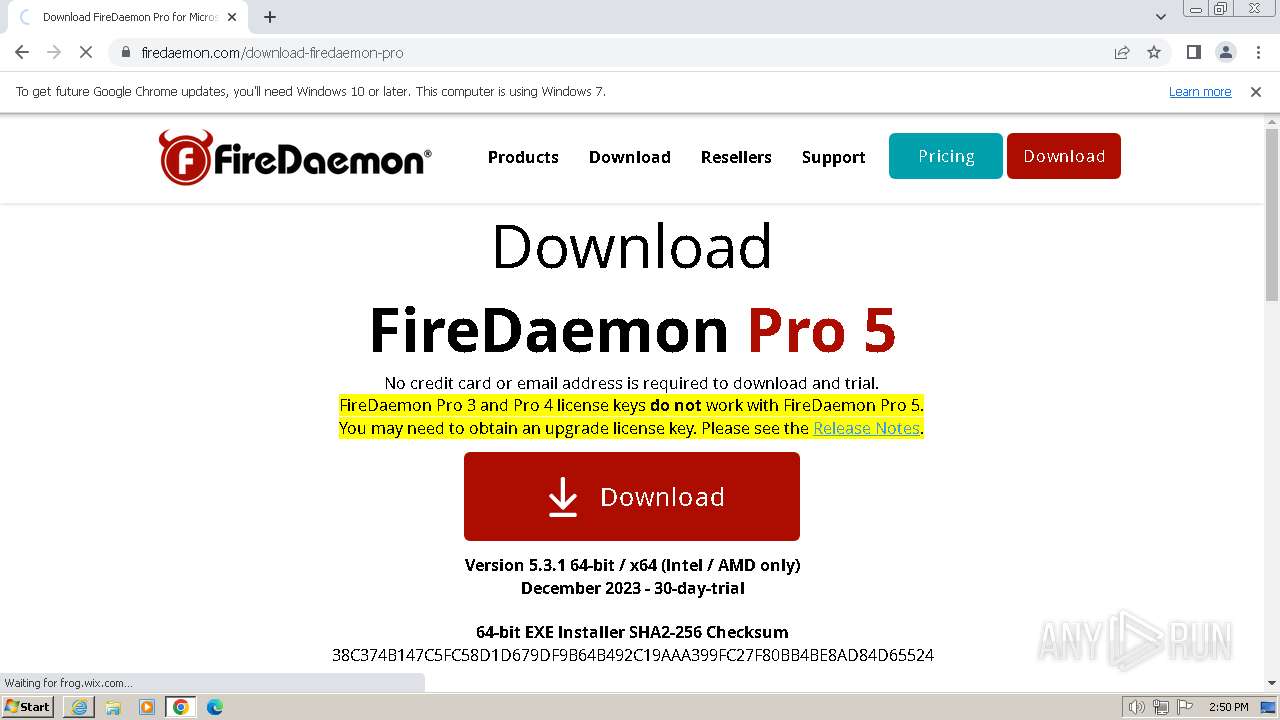
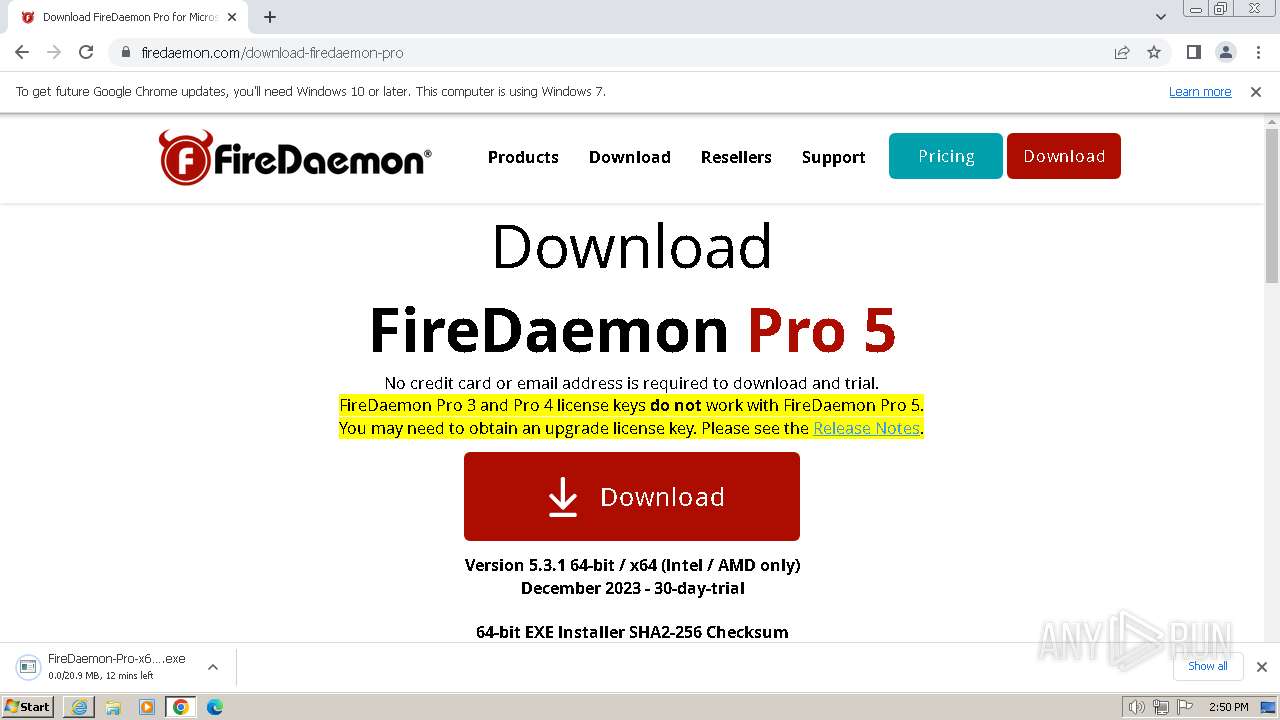
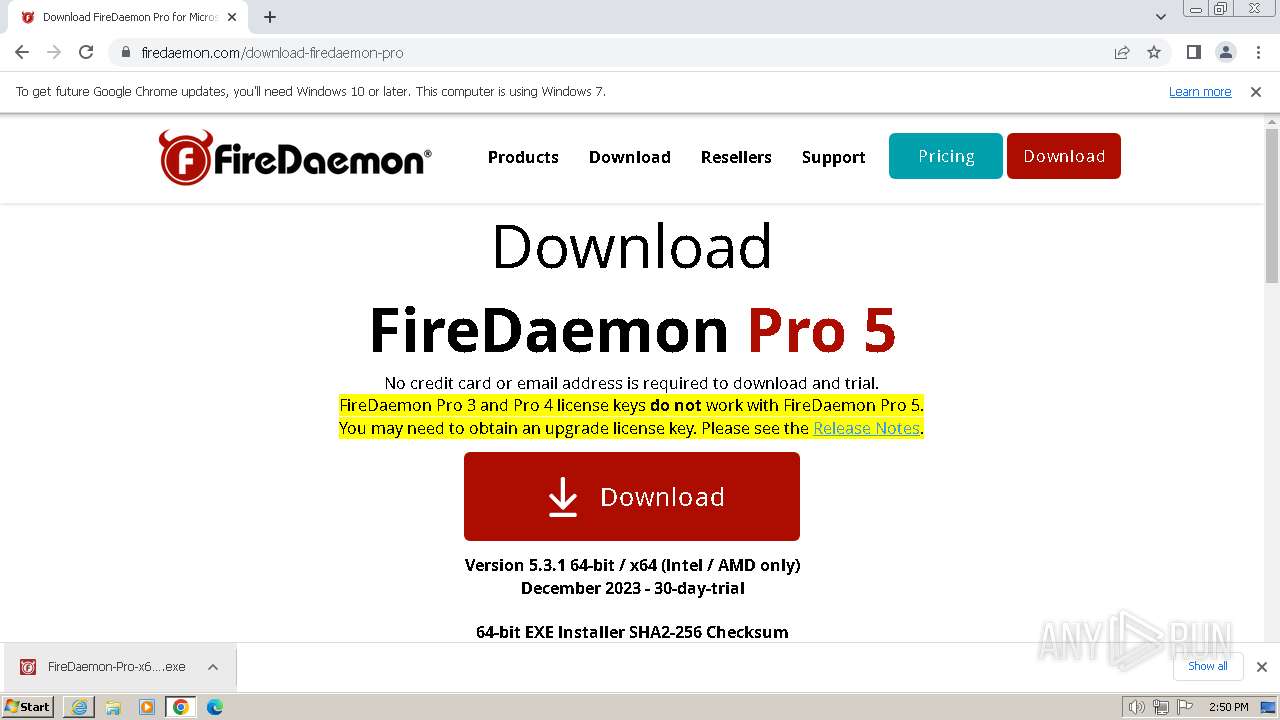
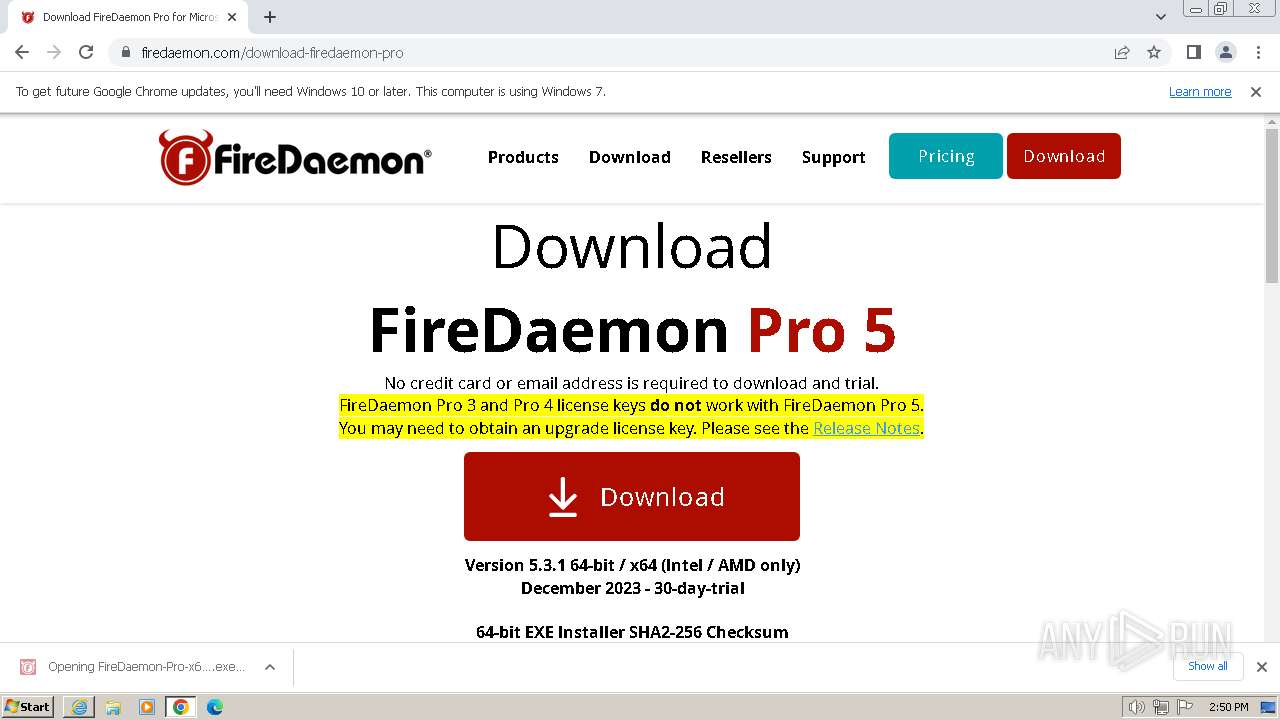
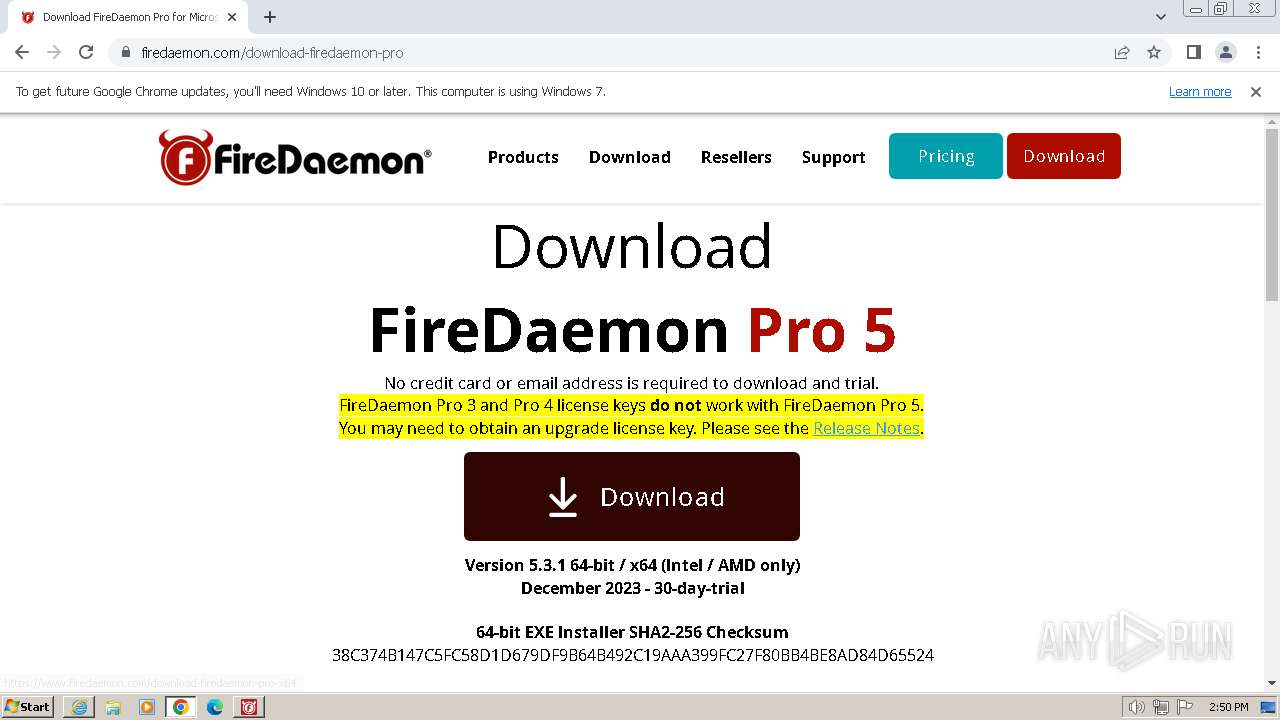
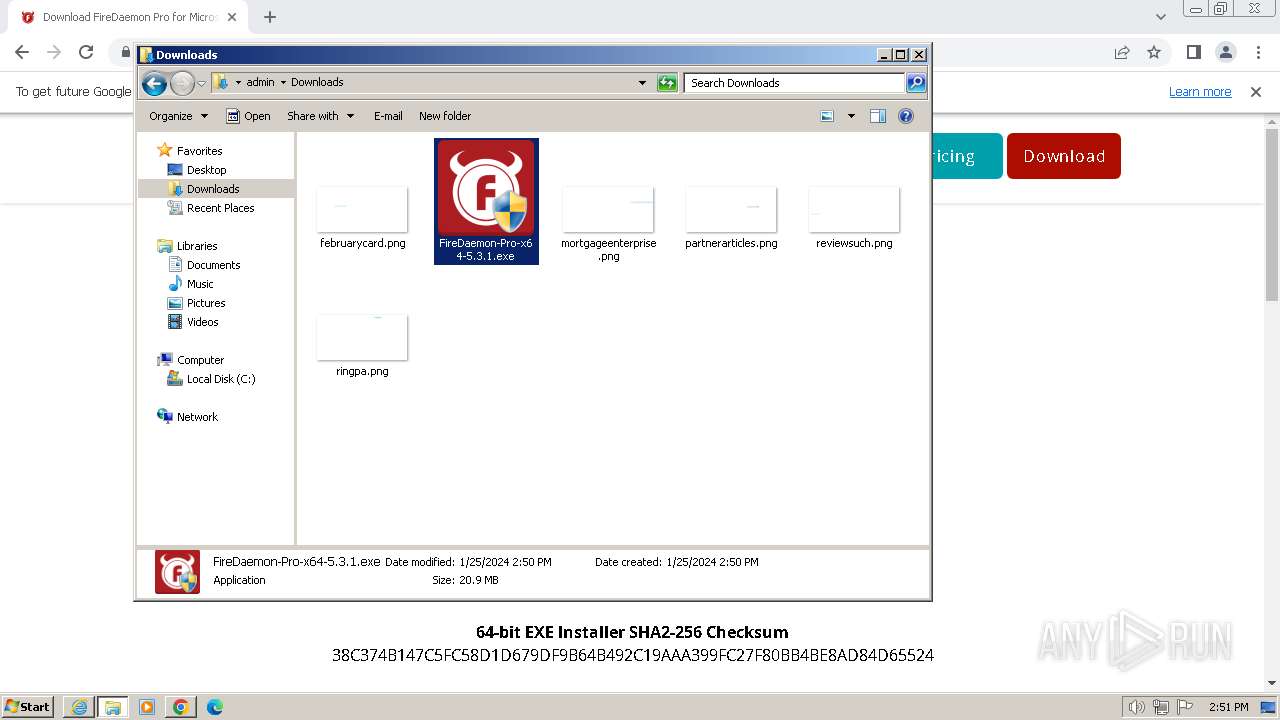
| URL: | https://www.firedaemon.com/download-firedaemon-pro |
| Full analysis: | https://app.any.run/tasks/1204dee9-9f63-4d9f-9a8f-0c98ecddc9a7 |
| Verdict: | Malicious activity |
| Analysis date: | January 25, 2024, 14:49:52 |
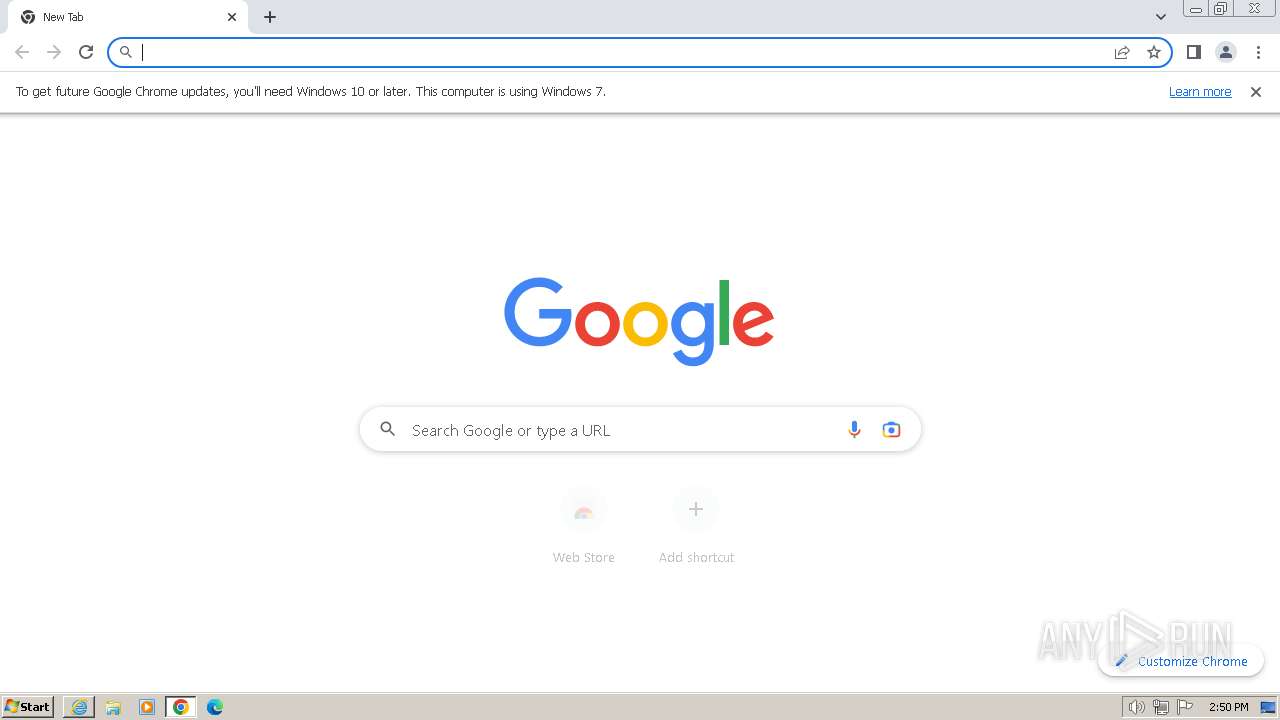
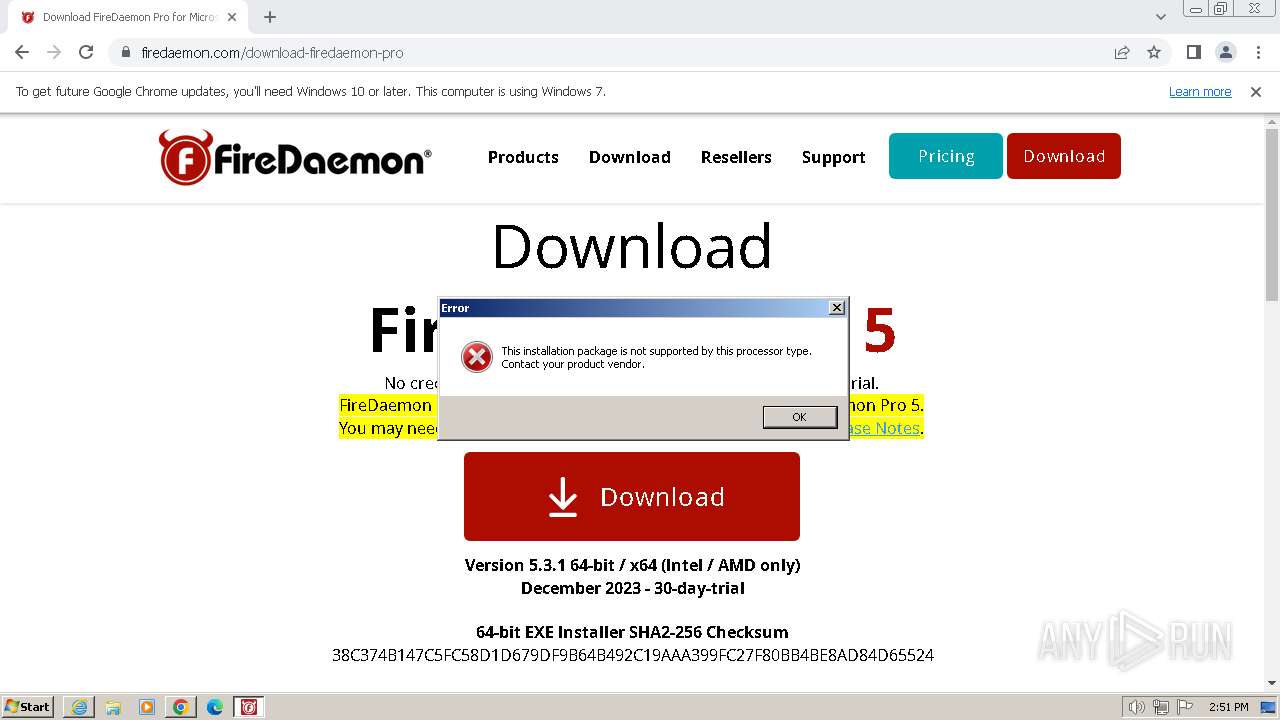
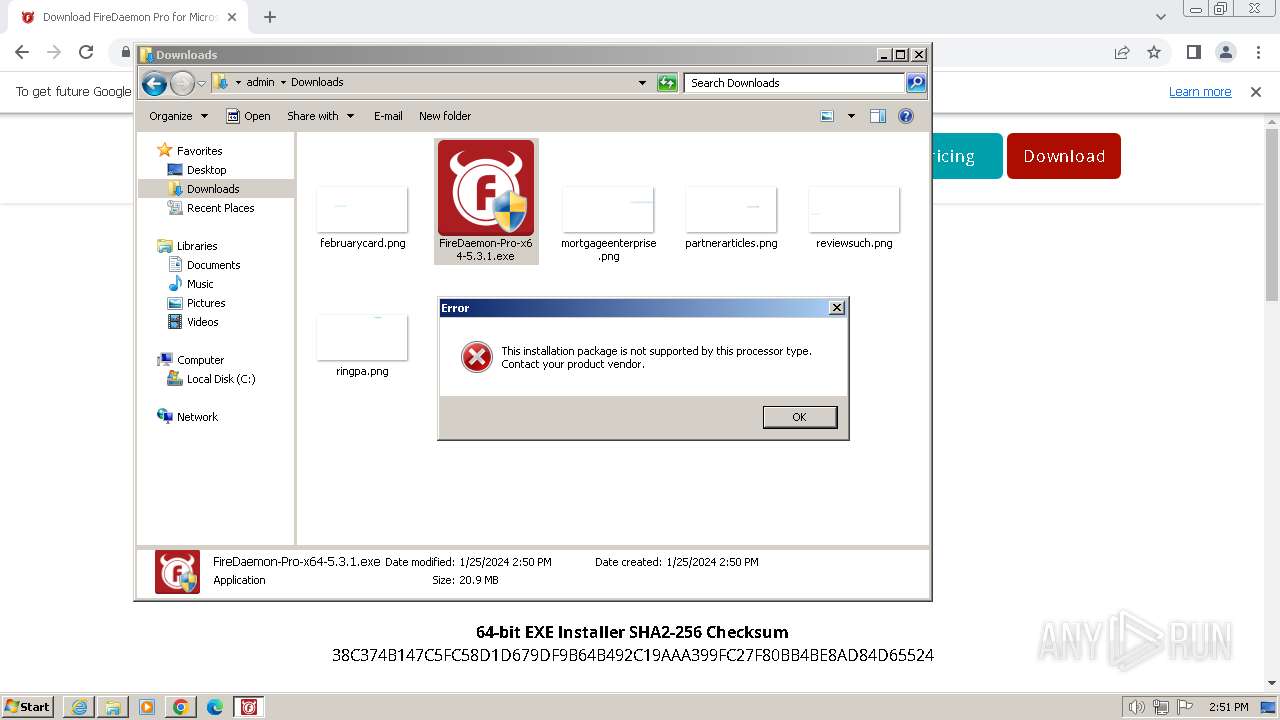
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 400CE9CE8713CB69EBF9CE61ABFCA079 |
| SHA1: | DD058532931350CE1F305475352A1AA537DDB46A |
| SHA256: | CC7016C7F29F2DEC6AC3B01AFADA6704225325B435E254901B1B9F872B8CF70C |
| SSDEEP: | 3:N8DSLQQjLLnKJDS4LIVa:2OLQr4fVa |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads security settings of Internet Explorer
- FireDaemon-Pro-x64-5.3.1.exe (PID: 2208)
- FireDaemon-Pro-x64-5.3.1.exe (PID: 2924)
Checks Windows Trust Settings
- FireDaemon-Pro-x64-5.3.1.exe (PID: 2208)
- FireDaemon-Pro-x64-5.3.1.exe (PID: 2924)
Reads settings of System Certificates
- FireDaemon-Pro-x64-5.3.1.exe (PID: 2208)
- FireDaemon-Pro-x64-5.3.1.exe (PID: 2924)
Reads the Windows owner or organization settings
- FireDaemon-Pro-x64-5.3.1.exe (PID: 2208)
- FireDaemon-Pro-x64-5.3.1.exe (PID: 2924)
Adds/modifies Windows certificates
- FireDaemon-Pro-x64-5.3.1.exe (PID: 2208)
INFO
Application launched itself
- iexplore.exe (PID: 2580)
- chrome.exe (PID: 3076)
Manual execution by a user
- wmpnscfg.exe (PID: 1820)
- chrome.exe (PID: 3076)
- FireDaemon-Pro-x64-5.3.1.exe (PID: 3228)
- explorer.exe (PID: 3928)
- FireDaemon-Pro-x64-5.3.1.exe (PID: 2924)
Reads the computer name
- wmpnscfg.exe (PID: 1820)
- FireDaemon-Pro-x64-5.3.1.exe (PID: 2208)
- FireDaemon-Pro-x64-5.3.1.exe (PID: 2924)
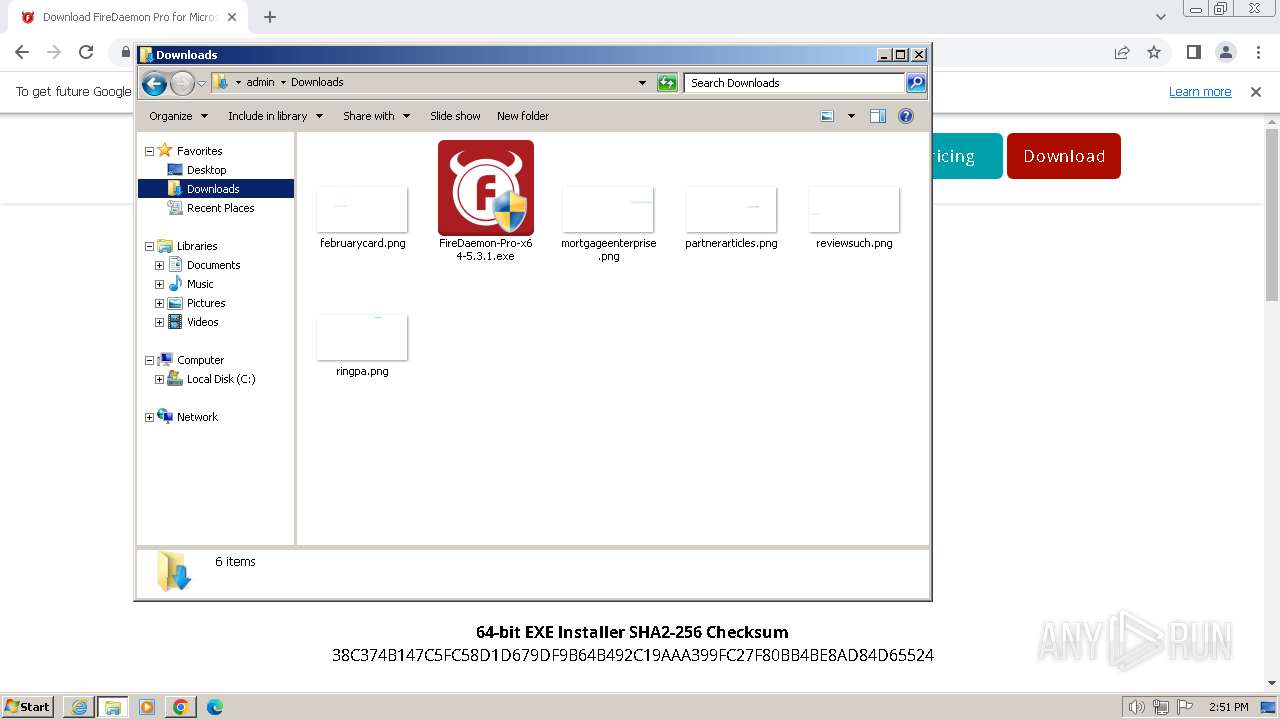
Executable content was dropped or overwritten
- chrome.exe (PID: 2544)
- chrome.exe (PID: 3076)
Checks supported languages
- wmpnscfg.exe (PID: 1820)
- FireDaemon-Pro-x64-5.3.1.exe (PID: 2208)
- FireDaemon-Pro-x64-5.3.1.exe (PID: 2924)
Drops the executable file immediately after the start
- chrome.exe (PID: 3076)
- chrome.exe (PID: 2544)
The process uses the downloaded file
- chrome.exe (PID: 3076)
- chrome.exe (PID: 3768)
Creates files or folders in the user directory
- FireDaemon-Pro-x64-5.3.1.exe (PID: 2208)
- FireDaemon-Pro-x64-5.3.1.exe (PID: 2924)
Create files in a temporary directory
- FireDaemon-Pro-x64-5.3.1.exe (PID: 2208)
- FireDaemon-Pro-x64-5.3.1.exe (PID: 2924)
Reads the machine GUID from the registry
- FireDaemon-Pro-x64-5.3.1.exe (PID: 2208)
- FireDaemon-Pro-x64-5.3.1.exe (PID: 2924)
Reads Environment values
- FireDaemon-Pro-x64-5.3.1.exe (PID: 2208)
- FireDaemon-Pro-x64-5.3.1.exe (PID: 2924)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
76
Monitored processes
29
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 116 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --disable-quic --mojo-platform-channel-handle=3652 --field-trial-handle=1188,i,4882472412169554157,7725998544014425230,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 948 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=109.0.5414.120 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x6a158b38,0x6a158b48,0x6a158b54 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1344 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=1852 --field-trial-handle=1188,i,4882472412169554157,7725998544014425230,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1492 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=3056 --field-trial-handle=1188,i,4882472412169554157,7725998544014425230,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
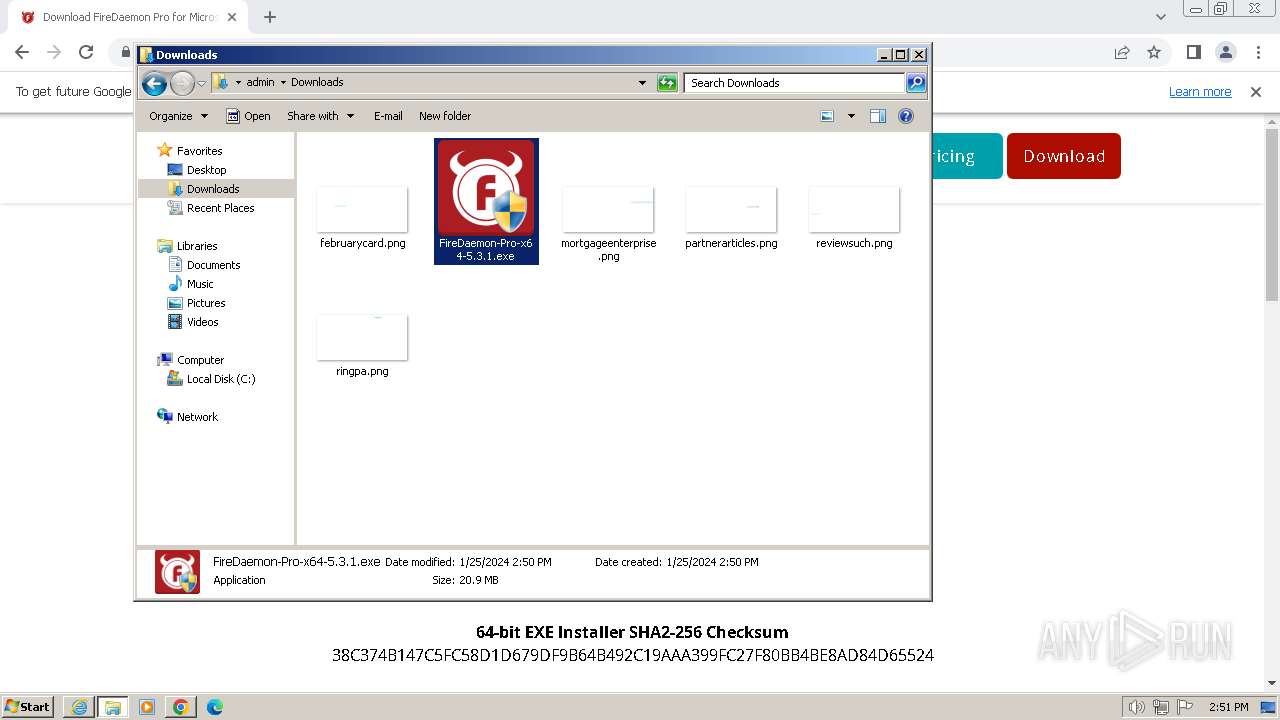
| 1504 | "C:\Users\admin\Downloads\FireDaemon-Pro-x64-5.3.1.exe" | C:\Users\admin\Downloads\FireDaemon-Pro-x64-5.3.1.exe | — | chrome.exe | |||||||||||
User: admin Company: FireDaemon Technologies Limited Integrity Level: MEDIUM Description: FireDaemon Pro Installer Exit code: 3221226540 Version: 5.3.1 Modules
| |||||||||||||||
| 1820 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1840 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --disable-quic --mojo-platform-channel-handle=4216 --field-trial-handle=1188,i,4882472412169554157,7725998544014425230,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1848 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --disable-quic --mojo-platform-channel-handle=4192 --field-trial-handle=1188,i,4882472412169554157,7725998544014425230,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2032 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=944 --field-trial-handle=1188,i,4882472412169554157,7725998544014425230,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2208 | "C:\Users\admin\Downloads\FireDaemon-Pro-x64-5.3.1.exe" | C:\Users\admin\Downloads\FireDaemon-Pro-x64-5.3.1.exe | chrome.exe | ||||||||||||
User: admin Company: FireDaemon Technologies Limited Integrity Level: HIGH Description: FireDaemon Pro Installer Exit code: 3758096389 Version: 5.3.1 Modules
| |||||||||||||||
Total events
31 674
Read events
31 414
Write events
247
Delete events
13
Modification events
| (PID) Process: | (2580) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (2580) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (2580) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (2580) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2580) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2580) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2580) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2580) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2580) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2580) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
7
Suspicious files
149
Text files
57
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2588 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\07CEF2F654E3ED6050FFC9B6EB844250_3431D4C539FB2CFCB781821E9902850D | der | |
MD5:DDDC70946C87D597FCBB22ADC5BCB4E6 | SHA256:95E572A3C0FADC2B820644FF9571D555F3A348C61315E60456D7C50C426BC225 | |||
| 2588 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B2FAF7692FD9FFBD64EDE317E42334BA_D7393C8F62BDE4D4CB606228BC7A711E | binary | |
MD5:B96C3B534558D271640B48EB56927867 | SHA256:82BE95A4AD4321EB63AAA6826538782E47463BEE3440369A8969806B7F766E8E | |||
| 2588 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\7FB5FDE2CD69AA29879D4E02A7B7F46C | der | |
MD5:50B1B0CE3096D27AA0B0F625BD7B77AA | SHA256:B971A2F3F846F80066B83A8EFEC07C2BF8B554EA6AABDB2538EE406592F9E739 | |||
| 2588 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\07CEF2F654E3ED6050FFC9B6EB844250_3431D4C539FB2CFCB781821E9902850D | binary | |
MD5:55AC1512841648C7F2B814CD4D87E09D | SHA256:004725E89F649E7D9EA697AAEDC182A65696123AB8FA20547F2B4CF1E552C412 | |||
| 2588 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:32BB20527AC954E5EC520F690DAE7276 | SHA256:89B74FC6A4CB5D19CC66609CA79B3FB05B86353B677006DB7920B80E45D38456 | |||
| 2588 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\download-firedaemon-pro[1].htm | html | |
MD5:B00F2E33D884F4FC2CF6AC4D397BF91A | SHA256:AE0279BD0D4725FB3F3B33CA1D941A22A7598F1E6891CD61BF1C91F2952B575B | |||
| 2588 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\CCB41FA1CFBF6B72844E88664A397933 | der | |
MD5:E3A693AAA9AA0E501B849A568FDB301C | SHA256:C456E74D9EA78561E610D5BA2BB8155891EB698CD5F35942019956066C22FD4C | |||
| 2588 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\94C18AA77707A64853AFFBE6D6382F75 | der | |
MD5:217691D7CA900939993694EB50DEABA8 | SHA256:4A08BD739A2DF487922A0A94F478578B53F2424F9E1AE1CE1CA52BE03B245EF5 | |||
| 2588 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B2FAF7692FD9FFBD64EDE317E42334BA_D7393C8F62BDE4D4CB606228BC7A711E | der | |
MD5:93780E52B78E85035EC822CBF0DE579F | SHA256:30653A79543A4142C2D300024DC3FEF7AD2CC90E0DB9DD3EF5728F5DD281CED1 | |||
| 2588 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\siteTags.bundle.min[1].js | text | |
MD5:7145D37309F2D1AD0F961C6C0A0DB191 | SHA256:CA3396F3825BB4251AC34B999DDC5F589EF860B95E3667D57EE26E3061503CA8 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
26
TCP/UDP connections
86
DNS requests
63
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2588 | iexplore.exe | GET | 304 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?09ca35c5e0844a72 | unknown | — | — | unknown |
2588 | iexplore.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | unknown | binary | 1.42 Kb | unknown |
2588 | iexplore.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEH1bUSa0droR23QWC7xTDac%3D | unknown | binary | 2.18 Kb | unknown |
2588 | iexplore.exe | GET | 200 | 192.124.249.41:80 | http://crl.starfieldtech.com/sfroot-g2.crl | unknown | binary | 584 b | unknown |
2588 | iexplore.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.sectigo.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRDC9IOTxN6GmyRjyTl2n4yTUczyAQUjYxexFStiuF36Zv5mwXhuAGNYeECEQDY0QqIA4ls560xLfSPYRX5 | unknown | binary | 472 b | unknown |
2588 | iexplore.exe | GET | 200 | 151.101.3.3:80 | http://ocsp.int-r1.certainly.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBQ9Cy058uESb%2B0ddJm5bqXlFvfbcAQUvZed36HYGyWZ4wwEBolkEtdlJMcCEwDbtxRB3HpBe3ZlumyaQ4p4Tjk%3D | unknown | binary | 523 b | unknown |
2588 | iexplore.exe | GET | 304 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?a0aa2a2858c872c9 | unknown | — | — | unknown |
2588 | iexplore.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.sectigo.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRDC9IOTxN6GmyRjyTl2n4yTUczyAQUjYxexFStiuF36Zv5mwXhuAGNYeECEB2cnsgbMqdL5IQNRvg1bHI%3D | unknown | binary | 471 b | unknown |
2588 | iexplore.exe | GET | 200 | 104.18.20.226:80 | http://ocsp2.globalsign.com/rootr3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT1nGh%2FJBjWKnkPdZIzB1bqhelHBwQUj%2FBLf6guRSSuTVD6Y5qL3uLdG7wCEH6HwqMlsnS7%2BryQ1sUoZV4%3D | unknown | binary | 1.40 Kb | unknown |
2588 | iexplore.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.sectigo.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRDC9IOTxN6GmyRjyTl2n4yTUczyAQUjYxexFStiuF36Zv5mwXhuAGNYeECEHgnk5%2FZKEYAQUsEAs4i3T4%3D | unknown | binary | 471 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2588 | iexplore.exe | 34.149.87.45:443 | www.firedaemon.com | GOOGLE | US | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2588 | iexplore.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | EDGECAST | GB | whitelisted |
2588 | iexplore.exe | 172.64.149.23:80 | ocsp.comodoca.com | CLOUDFLARENET | US | unknown |
2588 | iexplore.exe | 104.18.38.233:80 | ocsp.comodoca.com | CLOUDFLARENET | — | shared |
2588 | iexplore.exe | 34.96.106.200:443 | static.parastorage.com | GOOGLE | US | unknown |
2588 | iexplore.exe | 151.101.65.26:443 | polyfill.io | FASTLY | US | unknown |
2588 | iexplore.exe | 99.86.4.79:443 | static.wixstatic.com | AMAZON-02 | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.firedaemon.com |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.comodoca.com |
| whitelisted |
ocsp.usertrust.com |
| whitelisted |
ocsp.sectigo.com |
| whitelisted |
static.parastorage.com |
| shared |
polyfill.io |
| whitelisted |
static.wixstatic.com |
| whitelisted |
crl.starfieldtech.com |
| whitelisted |
ocsp.int-r1.certainly.com |
| unknown |