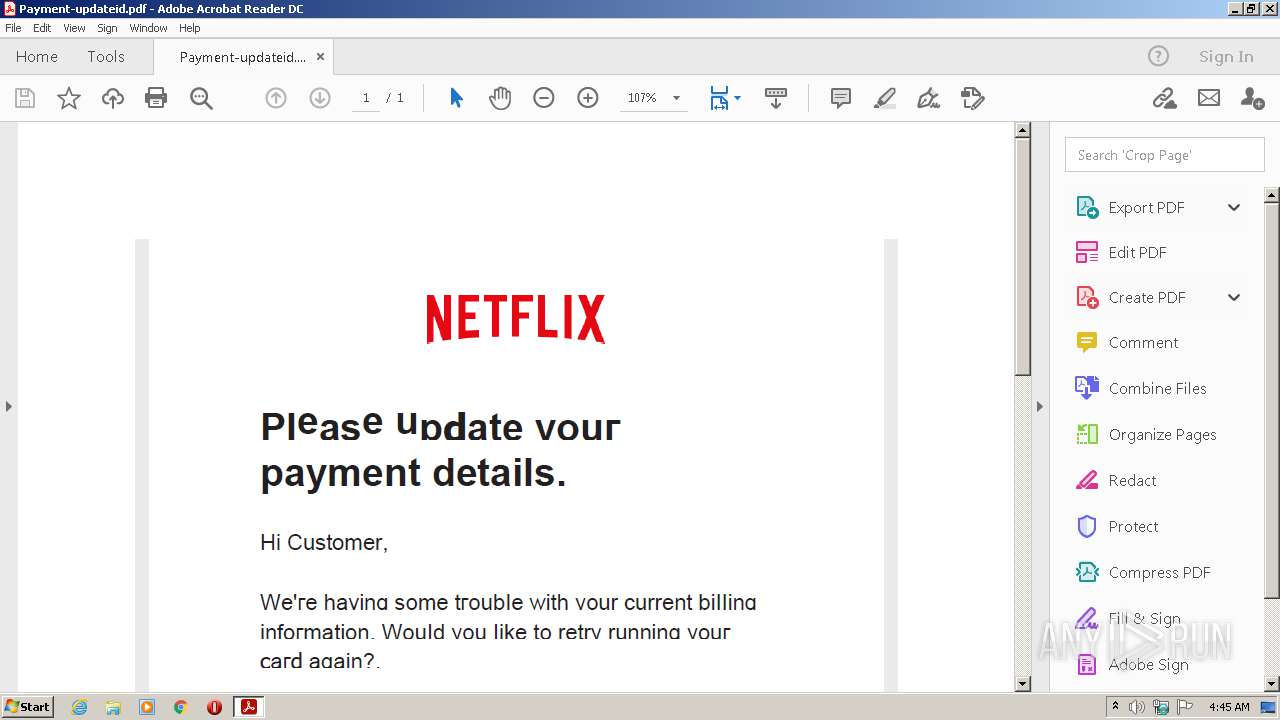
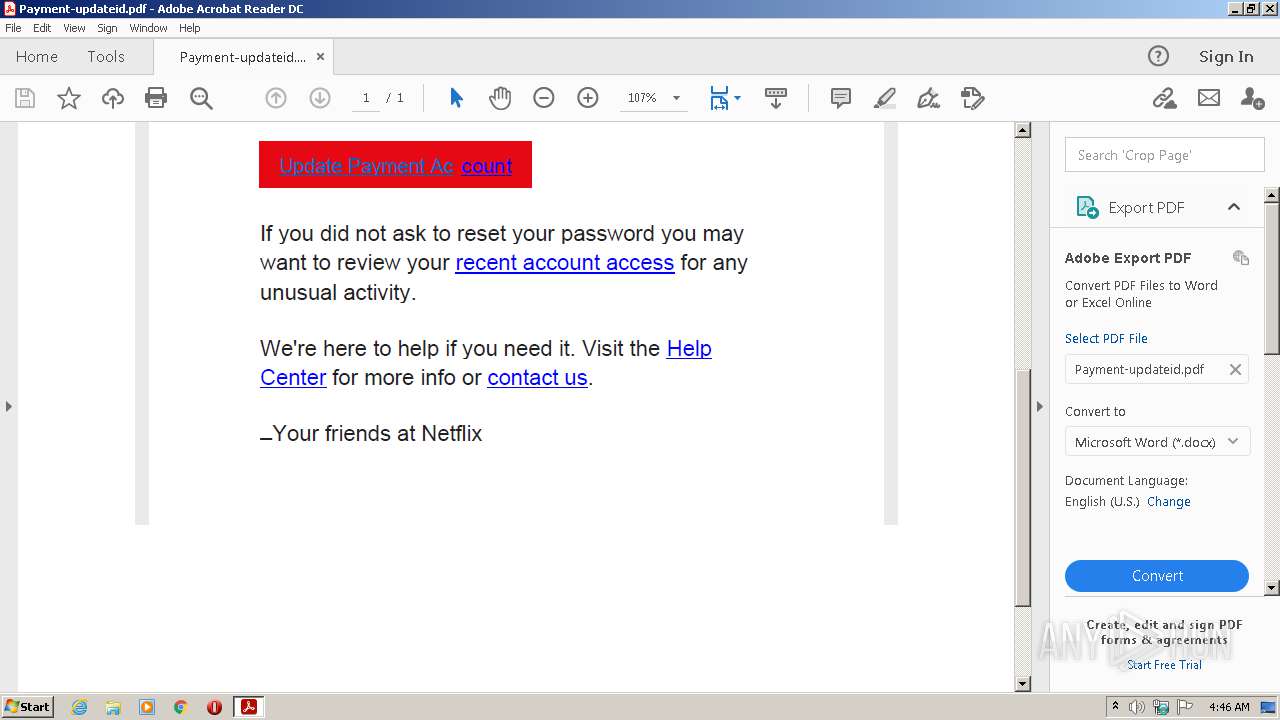
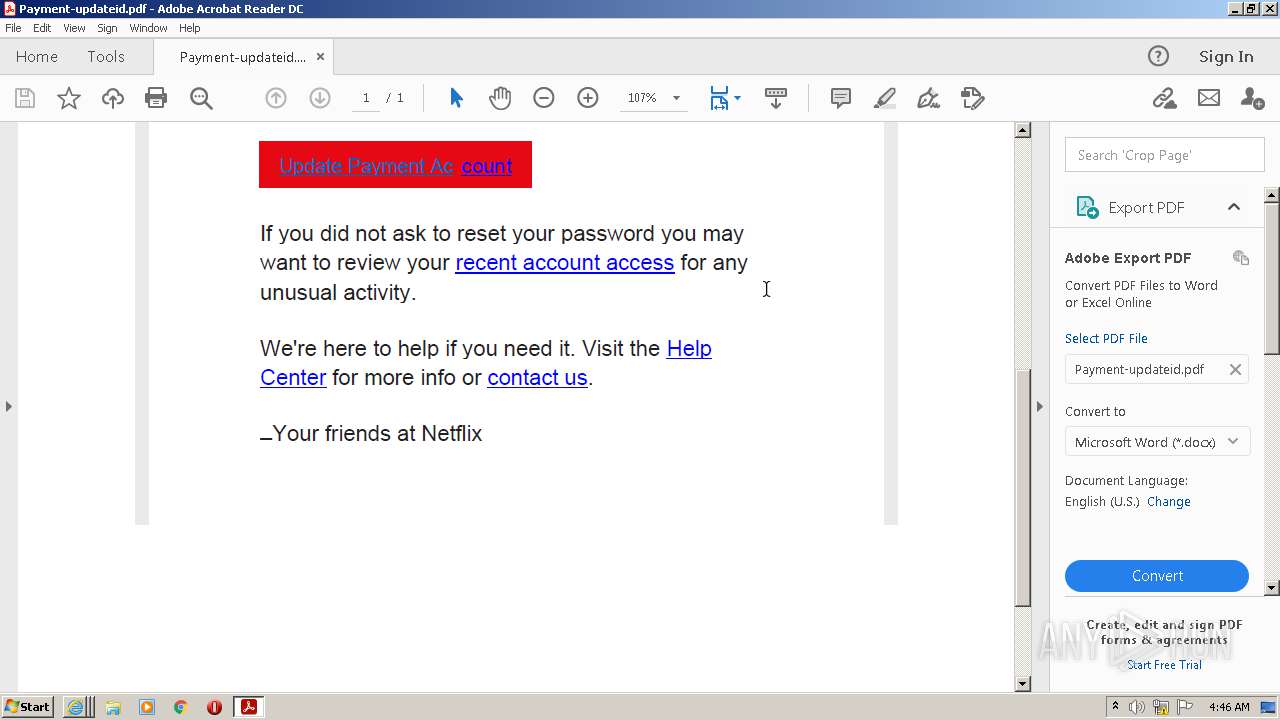
| File name: | Payment-updateid.pdf |
| Full analysis: | https://app.any.run/tasks/8bfd4c58-ec0d-4371-bfeb-52a334b69f59 |
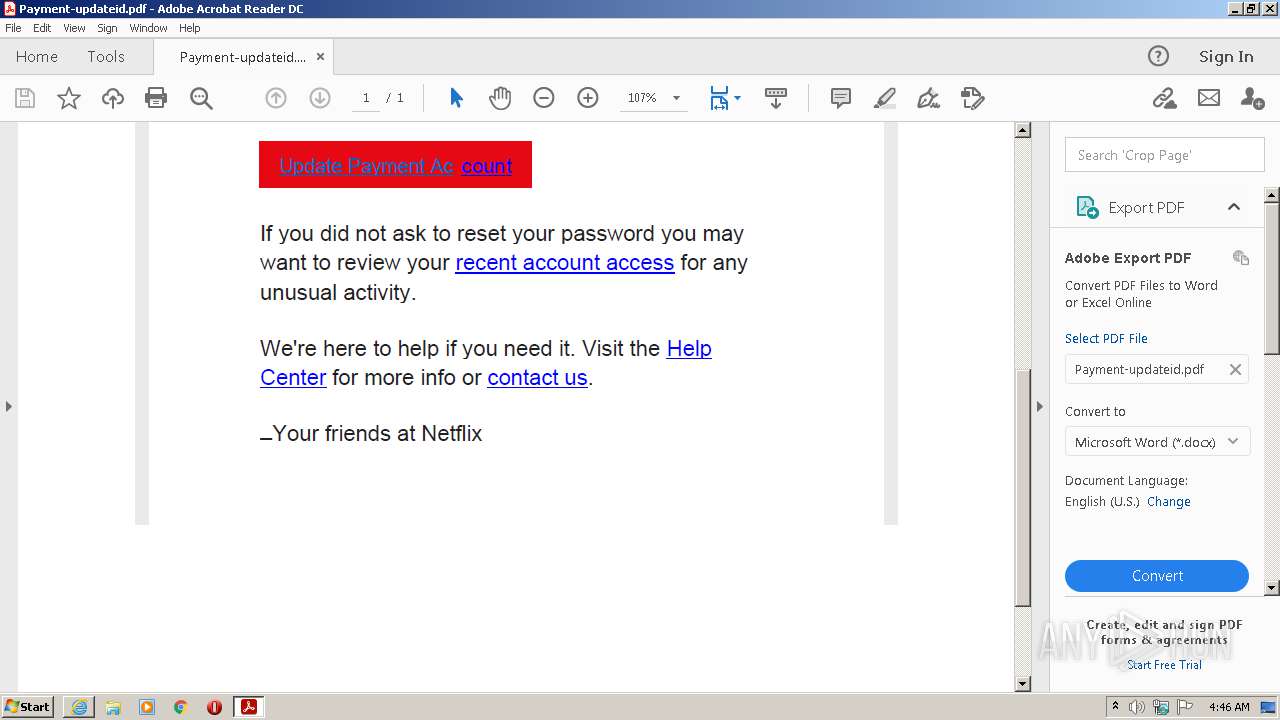
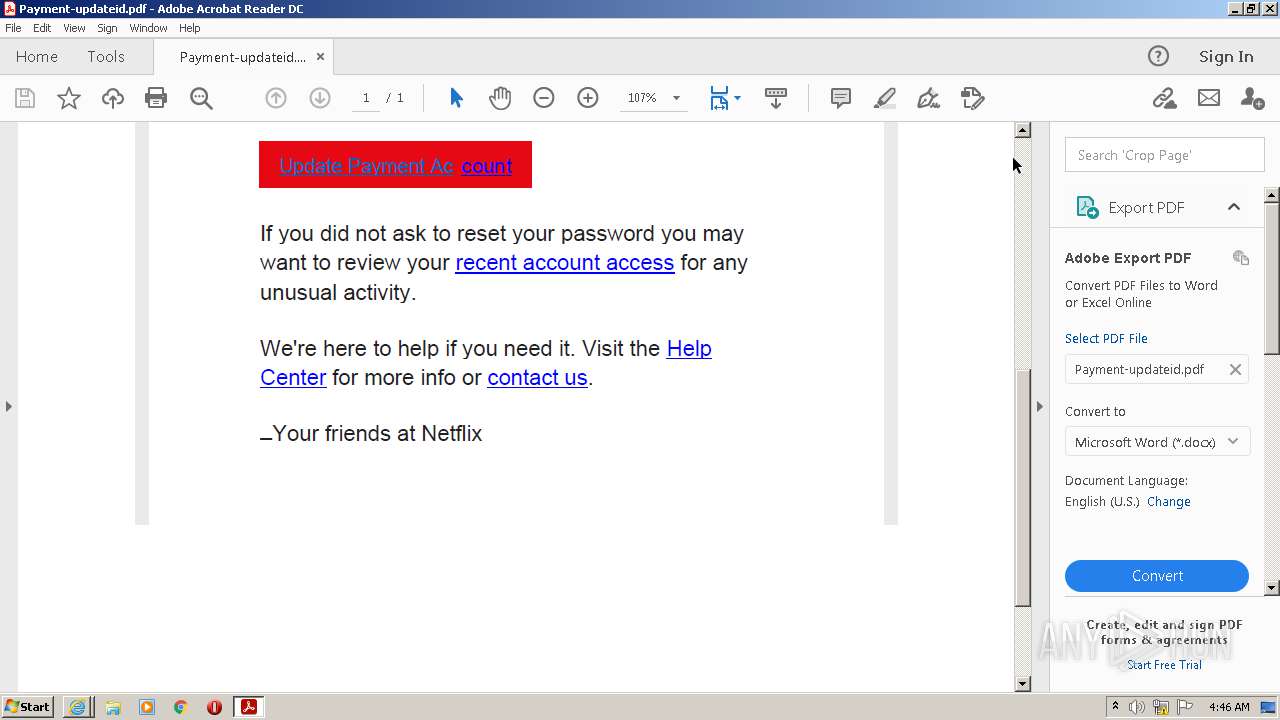
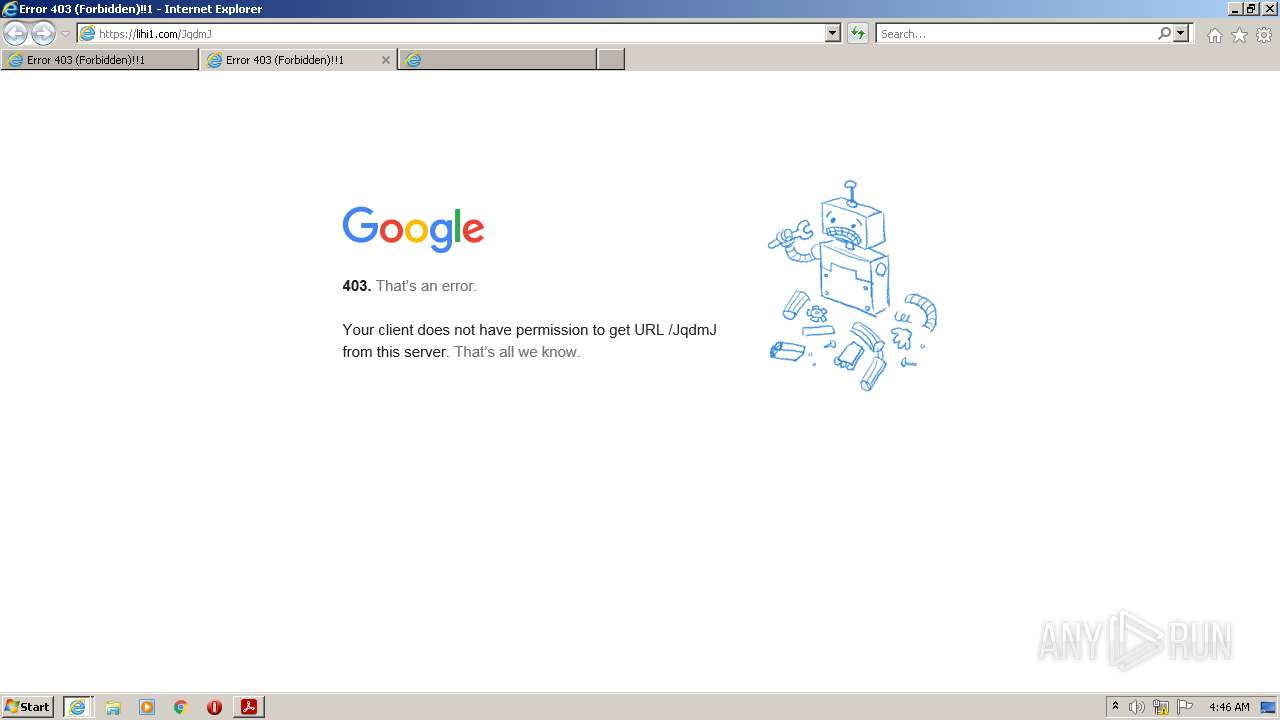
| Verdict: | Suspicious activity |
| Analysis date: | July 22, 2021, 03:45:38 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/pdf |
| File info: | PDF document, version 1.7 |
| MD5: | 4A2775EAE2EBEF41901A3F08D3B857C8 |
| SHA1: | 8B3439F5EA2F20C6BE329C4C6B8EAA9CC439233B |
| SHA256: | CC6F1A04B10BCB168AEEC8D870B97BD7C20FC161E8310B5BCE1AF8ED420E2C24 |
| SSDEEP: | 3072:eiilNpcqF7c/DTmHbARHwHfScBb/jKPNsxcQ0XLN40/yU:piTpcqF7IPmHbGHwHfSEg2xcVXLNP/h |
MALICIOUS
No malicious indicators.SUSPICIOUS
Checks supported languages
- Reader_sl.exe (PID: 1324)
- AdobeARM.exe (PID: 3812)
Reads the computer name
- AdobeARM.exe (PID: 3812)
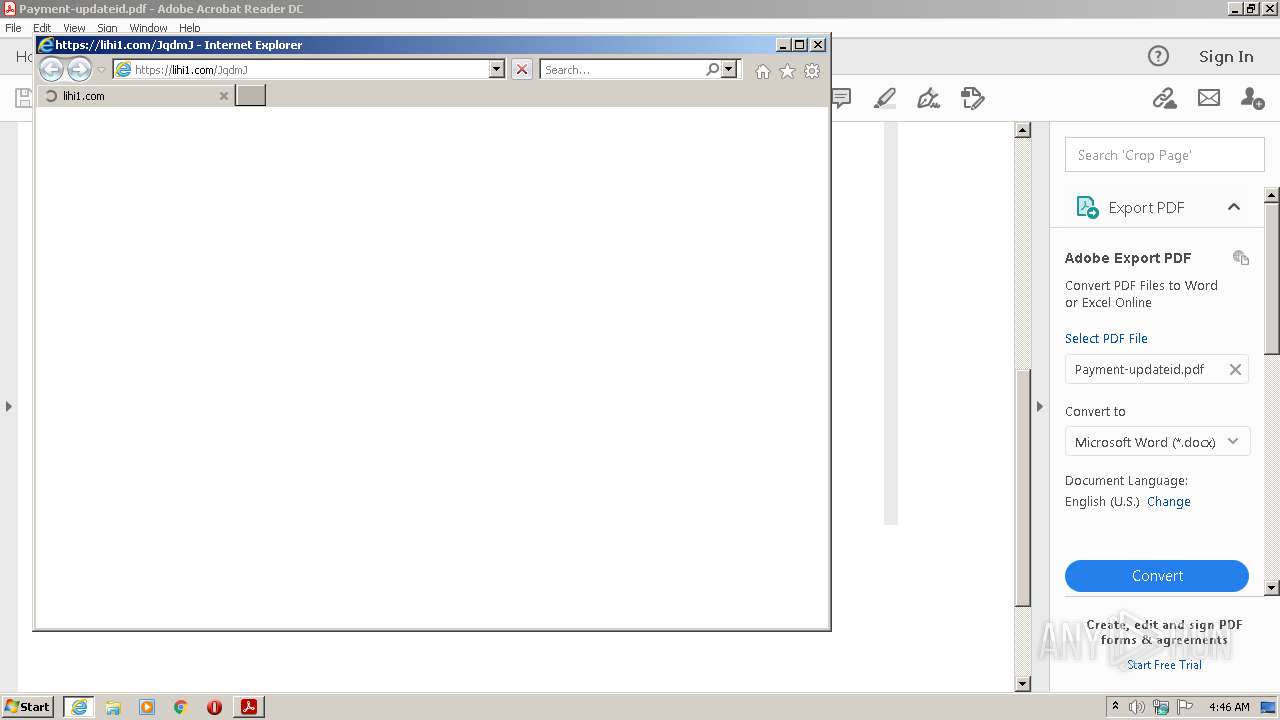
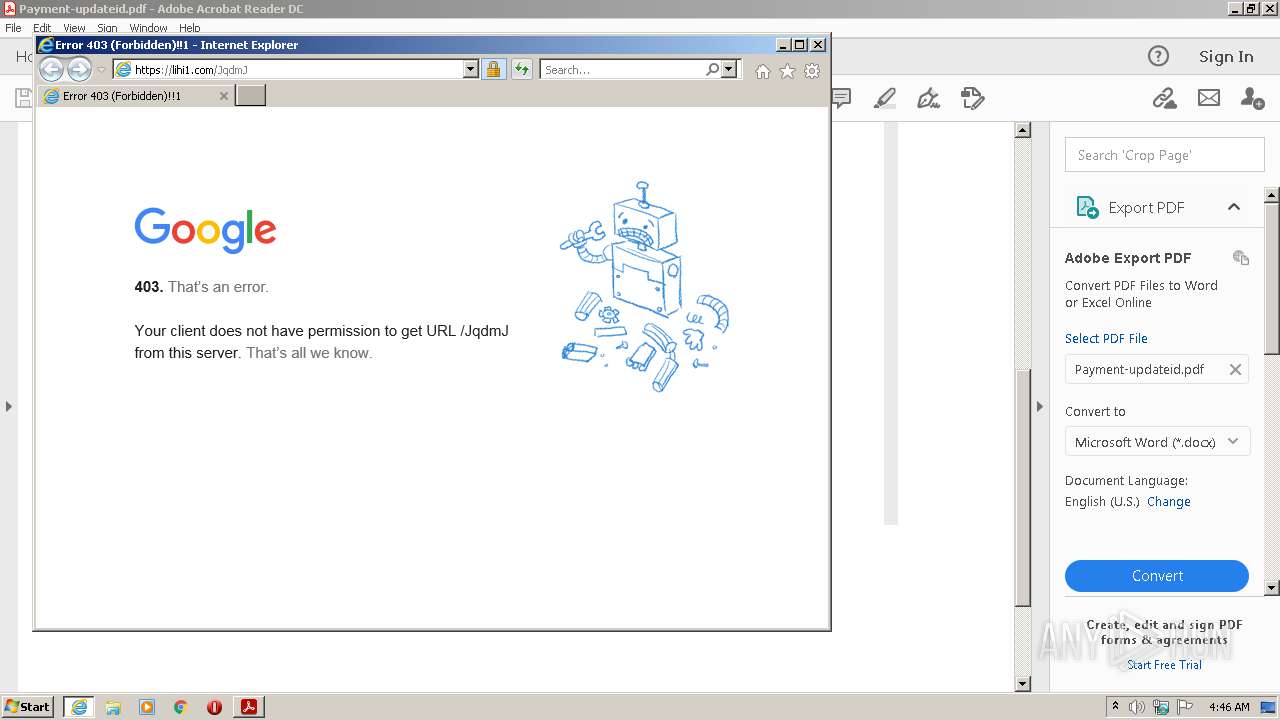
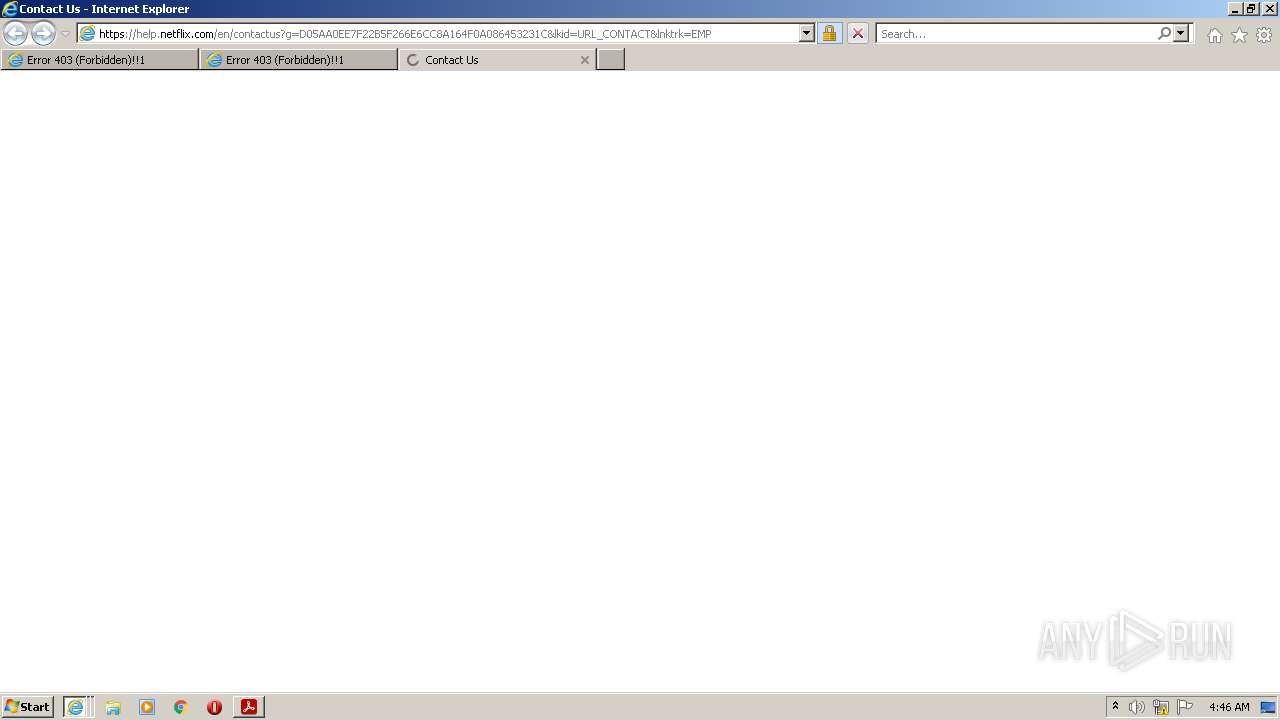
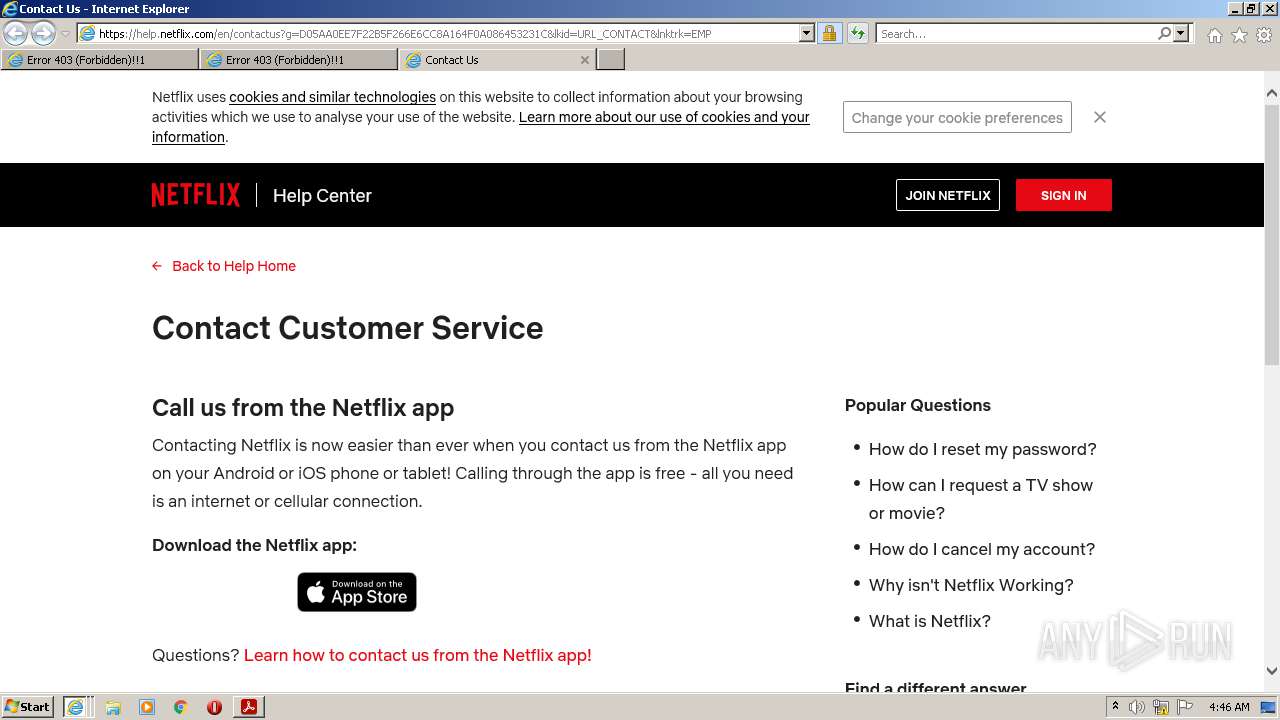
Starts Internet Explorer
- AcroRd32.exe (PID: 2088)
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3004)
- iexplore.exe (PID: 3228)
- iexplore.exe (PID: 980)
Creates files in the program directory
- AdobeARM.exe (PID: 3812)
Executable content was dropped or overwritten
- AdobeARM.exe (PID: 3812)
INFO
Checks supported languages
- AcroRd32.exe (PID: 2088)
- RdrCEF.exe (PID: 384)
- RdrCEF.exe (PID: 2940)
- AcroRd32.exe (PID: 3368)
- RdrCEF.exe (PID: 700)
- RdrCEF.exe (PID: 2304)
- RdrCEF.exe (PID: 3752)
- RdrCEF.exe (PID: 2836)
- RdrCEF.exe (PID: 3176)
- iexplore.exe (PID: 3004)
- iexplore.exe (PID: 1840)
- iexplore.exe (PID: 980)
- RdrCEF.exe (PID: 3600)
- RdrCEF.exe (PID: 2716)
- iexplore.exe (PID: 3228)
Application launched itself
- AcroRd32.exe (PID: 2088)
- RdrCEF.exe (PID: 384)
- iexplore.exe (PID: 1840)
Reads the computer name
- AcroRd32.exe (PID: 2088)
- AcroRd32.exe (PID: 3368)
- RdrCEF.exe (PID: 384)
- iexplore.exe (PID: 3004)
- iexplore.exe (PID: 1840)
- iexplore.exe (PID: 3228)
- iexplore.exe (PID: 980)
Searches for installed software
- AcroRd32.exe (PID: 2088)
- AcroRd32.exe (PID: 3368)
Reads CPU info
- AcroRd32.exe (PID: 3368)
Reads the hosts file
- RdrCEF.exe (PID: 384)
Checks Windows Trust Settings
- AcroRd32.exe (PID: 2088)
- iexplore.exe (PID: 1840)
- iexplore.exe (PID: 3004)
- iexplore.exe (PID: 980)
- AdobeARM.exe (PID: 3812)
- iexplore.exe (PID: 3228)
Reads settings of System Certificates
- AcroRd32.exe (PID: 2088)
- iexplore.exe (PID: 1840)
- iexplore.exe (PID: 3004)
- RdrCEF.exe (PID: 384)
- iexplore.exe (PID: 980)
- iexplore.exe (PID: 3228)
- AdobeARM.exe (PID: 3812)
Changes internet zones settings
- iexplore.exe (PID: 1840)
Reads internet explorer settings
- iexplore.exe (PID: 3004)
- iexplore.exe (PID: 980)
- iexplore.exe (PID: 3228)
Creates files in the user directory
- iexplore.exe (PID: 3228)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| | | Adobe Portable Document Format (100) |
EXIF
XMP
| InstanceID: | uuid:030ACDB2-ADC9-418E-A7B2-460EF9B4119B |
|---|---|
| DocumentID: | uuid:030ACDB2-ADC9-418E-A7B2-460EF9B4119B |
| ModifyDate: | 2021:03:10 19:22:08+08:00 |
| CreateDate: | 2021:03:10 19:22:08+08:00 |
| CreatorTool: | Microsoft® Word 2016 |
| Creator: | PayPaI Support |
| Producer: | Microsoft® Word 2016 |
| XMPToolkit: | 3.1-701 |
| Producer: | Microsoft® Word 2016 |
|---|---|
| ModifyDate: | 2021:03:10 19:22:08+08:00 |
| CreateDate: | 2021:03:10 19:22:08+08:00 |
| Creator: | Microsoft® Word 2016 |
| Author: | PayPaI Support |
| TaggedPDF: | Yes |
| Language: | en-US |
| PageCount: | 1 |
| Linearized: | No |
| PDFVersion: | 1.7 |
Total processes
54
Monitored processes
17
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 384 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe" --backgroundcolor=16514043 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe | AcroRd32.exe | ||||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe RdrCEF Exit code: 0 Version: 20.13.20064.405839 Modules
| |||||||||||||||
| 700 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe" --type=gpu-process --field-trial-handle=1168,7591836415733672309,12079850928672664693,131072 --disable-features=NetworkService,VizDisplayCompositor --disable-pack-loading --log-file="C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\debug.log" --log-severity=disable --product-version="ReaderServices/20.13.20064 Chrome/80.0.0.0" --lang=en-US --gpu-preferences=KAAAAAAAAADgACAgAQAAAAAAAAAAAGAAAAAAABAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --use-gl=swiftshader-webgl --log-file="C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\debug.log" --service-request-channel-token=12672341032049197402 --mojo-platform-channel-handle=1204 --allow-no-sandbox-job --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe | — | RdrCEF.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe RdrCEF Exit code: 1 Version: 20.13.20064.405839 Modules
| |||||||||||||||
| 980 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1840 CREDAT:2954506 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1324 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\Reader_sl.exe" | C:\Program Files\Adobe\Acrobat Reader DC\Reader\Reader_sl.exe | — | AdobeARM.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe Acrobat SpeedLauncher Exit code: 0 Version: 20.12.20041.394260 Modules
| |||||||||||||||
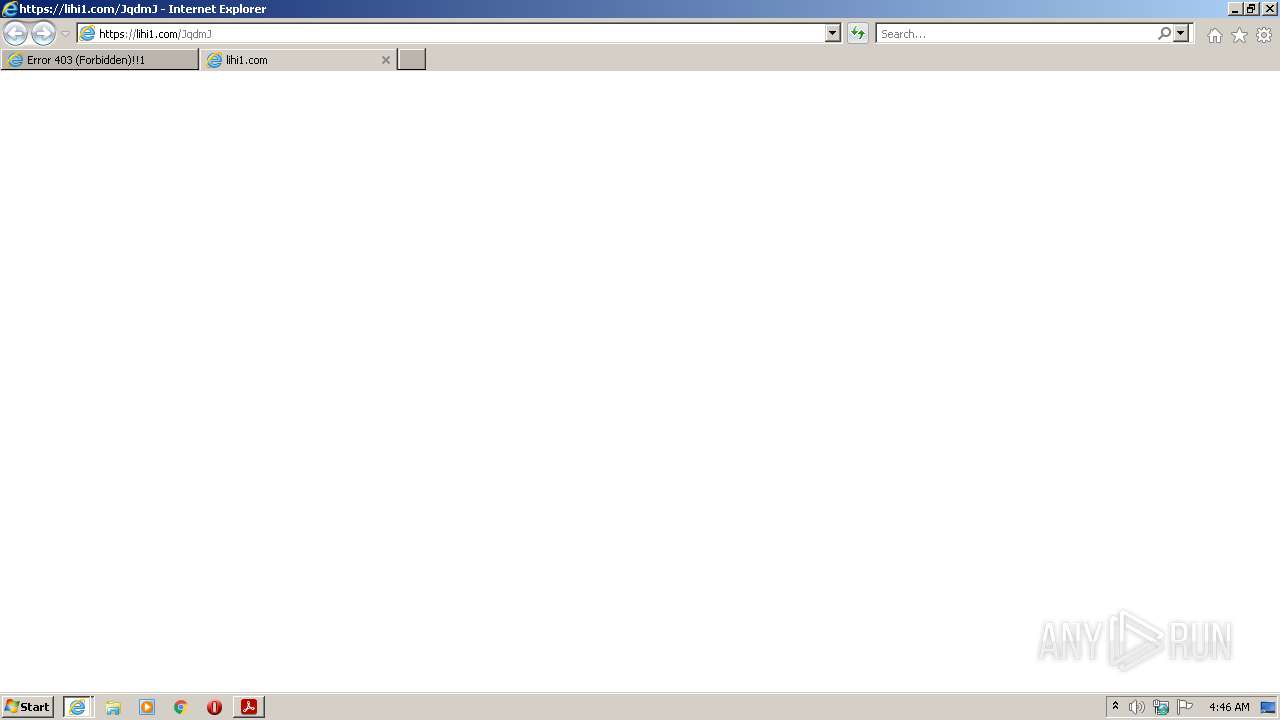
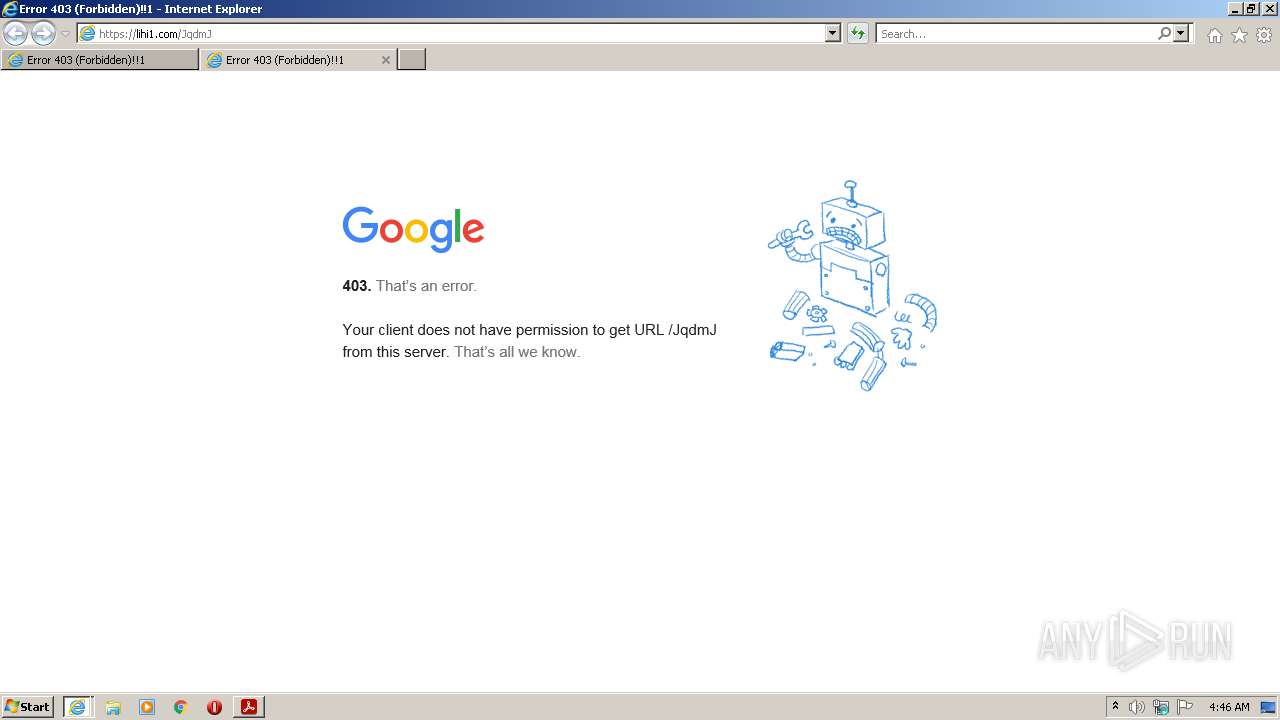
| 1840 | "C:\Program Files\Internet Explorer\iexplore.exe" https://lihi1.com/JqdmJ | C:\Program Files\Internet Explorer\iexplore.exe | AcroRd32.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2088 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe" "C:\Users\admin\AppData\Local\Temp\Payment-updateid.pdf" | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe | Explorer.EXE | ||||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe Acrobat Reader DC Exit code: 0 Version: 20.13.20064.405839 Modules
| |||||||||||||||
| 2304 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe" --type=gpu-process --field-trial-handle=1168,7591836415733672309,12079850928672664693,131072 --disable-features=NetworkService,VizDisplayCompositor --disable-pack-loading --log-file="C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\debug.log" --log-severity=disable --product-version="ReaderServices/20.13.20064 Chrome/80.0.0.0" --lang=en-US --gpu-preferences=KAAAAAAAAADgACAgAQAAAAAAAAAAAGAAAAAAABAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --use-gl=swiftshader-webgl --log-file="C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\debug.log" --service-request-channel-token=10575153964859758781 --mojo-platform-channel-handle=1436 --allow-no-sandbox-job --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe | — | RdrCEF.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe RdrCEF Exit code: 1 Version: 20.13.20064.405839 Modules
| |||||||||||||||
| 2716 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe" --type=renderer --log-file="C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\debug.log" --touch-events=enabled --field-trial-handle=1168,7591836415733672309,12079850928672664693,131072 --disable-features=NetworkService,VizDisplayCompositor --disable-gpu-compositing --lang=en-US --disable-pack-loading --log-file="C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\debug.log" --log-severity=disable --product-version="ReaderServices/20.13.20064 Chrome/80.0.0.0" --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6964770023774670834 --renderer-client-id=9 --mojo-platform-channel-handle=2812 --allow-no-sandbox-job /prefetch:1 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe | — | RdrCEF.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe RdrCEF Exit code: 0 Version: 20.13.20064.405839 Modules
| |||||||||||||||
| 2836 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe" --type=renderer --log-file="C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\debug.log" --touch-events=enabled --field-trial-handle=1168,7591836415733672309,12079850928672664693,131072 --disable-features=NetworkService,VizDisplayCompositor --disable-gpu-compositing --lang=en-US --disable-pack-loading --log-file="C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\debug.log" --log-severity=disable --product-version="ReaderServices/20.13.20064 Chrome/80.0.0.0" --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12676222956628829893 --renderer-client-id=6 --mojo-platform-channel-handle=1524 --allow-no-sandbox-job /prefetch:1 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe | — | RdrCEF.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe RdrCEF Exit code: 0 Version: 20.13.20064.405839 Modules
| |||||||||||||||
| 2940 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe" --type=renderer --log-file="C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\debug.log" --touch-events=enabled --field-trial-handle=1168,7591836415733672309,12079850928672664693,131072 --disable-features=NetworkService,VizDisplayCompositor --disable-gpu-compositing --lang=en-US --disable-pack-loading --log-file="C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\debug.log" --log-severity=disable --product-version="ReaderServices/20.13.20064 Chrome/80.0.0.0" --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8013581315742284950 --renderer-client-id=2 --mojo-platform-channel-handle=1176 --allow-no-sandbox-job /prefetch:1 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe | — | RdrCEF.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe RdrCEF Exit code: 0 Version: 20.13.20064.405839 Modules
| |||||||||||||||
Total events
44 050
Read events
43 787
Write events
258
Delete events
5
Modification events
| (PID) Process: | (3368) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\Acrobat Reader\DC\ExitSection |
| Operation: | write | Name: | bLastExitNormal |
Value: 0 | |||
| (PID) Process: | (3368) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\Acrobat Reader\DC\AVGeneral |
| Operation: | write | Name: | iNumReaderLaunches |
Value: 2 | |||
| (PID) Process: | (3368) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\Acrobat Reader\DC\FTEDialog |
| Operation: | write | Name: | bShowUpdateFTE |
Value: 1 | |||
| (PID) Process: | (3368) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\Acrobat Reader\DC\HomeWelcome |
| Operation: | write | Name: | bIsAcrobatUpdated |
Value: 1 | |||
| (PID) Process: | (3368) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\Acrobat Reader\DC\HomeWelcomeFirstMileReader |
| Operation: | write | Name: | iCardCountShown |
Value: 2 | |||
| (PID) Process: | (3368) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\Acrobat Reader\DC\FTEDialog |
| Operation: | delete value | Name: | iLastCardShown |
Value: 0 | |||
| (PID) Process: | (2088) AcroRd32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3368) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\Acrobat Reader\DC\SessionManagement |
| Operation: | write | Name: | bNormalExit |
Value: 0 | |||
| (PID) Process: | (3368) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\Acrobat Reader\DC\SessionManagement\cWindowsCurrent\cWin0 |
| Operation: | write | Name: | iTabCount |
Value: 0 | |||
| (PID) Process: | (3368) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\Acrobat Reader\DC\SessionManagement\cWindowsCurrent |
| Operation: | write | Name: | iWinCount |
Value: 1 | |||
Executable files
1
Suspicious files
192
Text files
39
Unknown types
22
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 384 | RdrCEF.exe | C:\Users\admin\AppData\LocalLow\Adobe\AcroCef\DC\Acrobat\Cache\Code Cache\js\8e417e79df3bf0e9_0 | binary | |
MD5:52B096AF16B282B1F7D3E277E09B06EC | SHA256:6A7E59341C59F74F0D25B35D7D6D72526F14D99820237E19E4CDD1A696ADD371 | |||
| 384 | RdrCEF.exe | C:\Users\admin\AppData\LocalLow\Adobe\AcroCef\DC\Acrobat\Cache\Code Cache\js\2a426f11fd8ebe18_0 | binary | |
MD5:C5FBE9CF3E266B1724F0237C27CFCEB6 | SHA256:45499967B41AE4C7F013230FE0BF31C67BB61E10FA22849CB989F145A92E8E41 | |||
| 384 | RdrCEF.exe | C:\Users\admin\AppData\LocalLow\Adobe\AcroCef\DC\Acrobat\Cache\Code Cache\js\983b7a3da8f39a46_0 | binary | |
MD5:951F3055103F759C10767CC6C0F603C5 | SHA256:A24625B5CF8A956C033D16BC2A99E5DAFECE9DD4A0D16D4130123B6C5D5205B7 | |||
| 384 | RdrCEF.exe | C:\Users\admin\AppData\LocalLow\Adobe\AcroCef\DC\Acrobat\Cache\Code Cache\js\72d9f526d2e2e7c8_0 | binary | |
MD5:D18E8BC89292E603927CAE09AC59E2C5 | SHA256:C5666F19310705F5CDBEF2137A8783AAD0C4D7E81B582DEA1008A56DF8F0C431 | |||
| 384 | RdrCEF.exe | C:\Users\admin\AppData\LocalLow\Adobe\AcroCef\DC\Acrobat\Cache\Code Cache\js\86b8040b7132b608_0 | binary | |
MD5:CA7C0BF20401633220CA4041C3E82E02 | SHA256:75E5B26EA5772F1FAE32EE41D30CF5D8CCECD8ABED95A9B5E3F7C4AE67FBD911 | |||
| 384 | RdrCEF.exe | C:\Users\admin\AppData\LocalLow\Adobe\AcroCef\DC\Acrobat\Cache\Code Cache\js\aba6710fde0876af_0 | binary | |
MD5:4922ACE4A18AC56FC6519909545B2E97 | SHA256:7454DFE635C1EF2483448551DEAE20AD393CA900903487E327B4A94AA3587F03 | |||
| 384 | RdrCEF.exe | C:\Users\admin\AppData\LocalLow\Adobe\AcroCef\DC\Acrobat\Cache\Code Cache\js\4a0e94571d979b3c_0 | binary | |
MD5:C6AA7C893FF567AE144F918E7A947F50 | SHA256:FCC43615578EEEB0EFF8102D5B7A29241FD21ECD0355D2182F9AABAFE13CA70B | |||
| 384 | RdrCEF.exe | C:\Users\admin\AppData\LocalLow\Adobe\AcroCef\DC\Acrobat\Cache\Code Cache\js\8c84d92a9dbce3e0_0 | binary | |
MD5:CBD514EF253957330B13C1224F9A115B | SHA256:71EDE1D90E71FD0BD20C057B94B690E6EEFFDD607996693D500D68C7AE783CA1 | |||
| 384 | RdrCEF.exe | C:\Users\admin\AppData\LocalLow\Adobe\AcroCef\DC\Acrobat\Cache\Code Cache\js\92c56fa2a6c4d5ba_0 | binary | |
MD5:31AC9C0326771748E4C0231F59A9C01E | SHA256:DC2E75B863311603441CE0BB665D9CFBE98470A1502327843119880E1E3C34A3 | |||
| 384 | RdrCEF.exe | C:\Users\admin\AppData\LocalLow\Adobe\AcroCef\DC\Acrobat\Cache\Code Cache\js\946896ee27df7947_0 | binary | |
MD5:F6AE937992BAE68AD3915A24F8924C79 | SHA256:D79516C0FFB7B0AFCC592DF4B999171D8C03239C2ECF5AEB1A5B4E612DD911DD | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
14
TCP/UDP connections
41
DNS requests
20
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3004 | iexplore.exe | GET | 200 | 142.250.185.99:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | der | 1.41 Kb | whitelisted |
3004 | iexplore.exe | GET | 200 | 142.250.185.99:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | der | 724 b | whitelisted |
3228 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
1840 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTk45WiKdPUwcMf8JgMC07ACYqr2AQUt2ui6qiqhIx56rTaD5iyxZV2ufQCEAR0EZoNvunUwrmTBH4rTZQ%3D | US | der | 471 b | whitelisted |
1840 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTk45WiKdPUwcMf8JgMC07ACYqr2AQUt2ui6qiqhIx56rTaD5iyxZV2ufQCEAdRQDADRylZtXCMIQXiK1w%3D | US | der | 471 b | whitelisted |
2088 | AcroRd32.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?08ade5d469414fee | US | compressed | 4.70 Kb | whitelisted |
2088 | AcroRd32.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?d5063663891e2cd5 | US | compressed | 4.70 Kb | whitelisted |
1840 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
3004 | iexplore.exe | GET | 200 | 142.250.185.99:80 | http://ocsp.pki.goog/gts1d4/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBSMBFDqU0NJQdZdEGU3bkhj0FoRrQQUJeIYDrJXkZQq5dRdhpCD3lOzuJICEQCWl4Oza3g9wAoAAAAA7Wd1 | US | der | 472 b | whitelisted |
1840 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAo1CNVcKSsBffitZcAP9%2BQ%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3228 | iexplore.exe | 104.20.184.68:443 | geolocation.onetrust.com | Cloudflare Inc | US | shared |
1840 | iexplore.exe | 45.57.90.1:443 | assets.nflxext.com | Netflix Streaming Services Inc. | US | suspicious |
384 | RdrCEF.exe | 2.18.233.74:443 | geo2.adobe.com | Akamai International B.V. | — | whitelisted |
384 | RdrCEF.exe | 3.233.129.217:443 | p13n.adobe.io | — | US | unknown |
2088 | AcroRd32.exe | 2.16.107.24:443 | acroipm2.adobe.com | Akamai International B.V. | — | malicious |
2088 | AcroRd32.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2088 | AcroRd32.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3004 | iexplore.exe | 35.244.149.249:443 | lihi1.com | — | US | unknown |
3004 | iexplore.exe | 142.250.185.99:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
3004 | iexplore.exe | 142.250.186.132:443 | www.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
geo2.adobe.com |
| whitelisted |
p13n.adobe.io |
| whitelisted |
armmf.adobe.com |
| whitelisted |
acroipm2.adobe.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
lihi1.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
www.google.com |
| malicious |
api.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1776 | svchost.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |