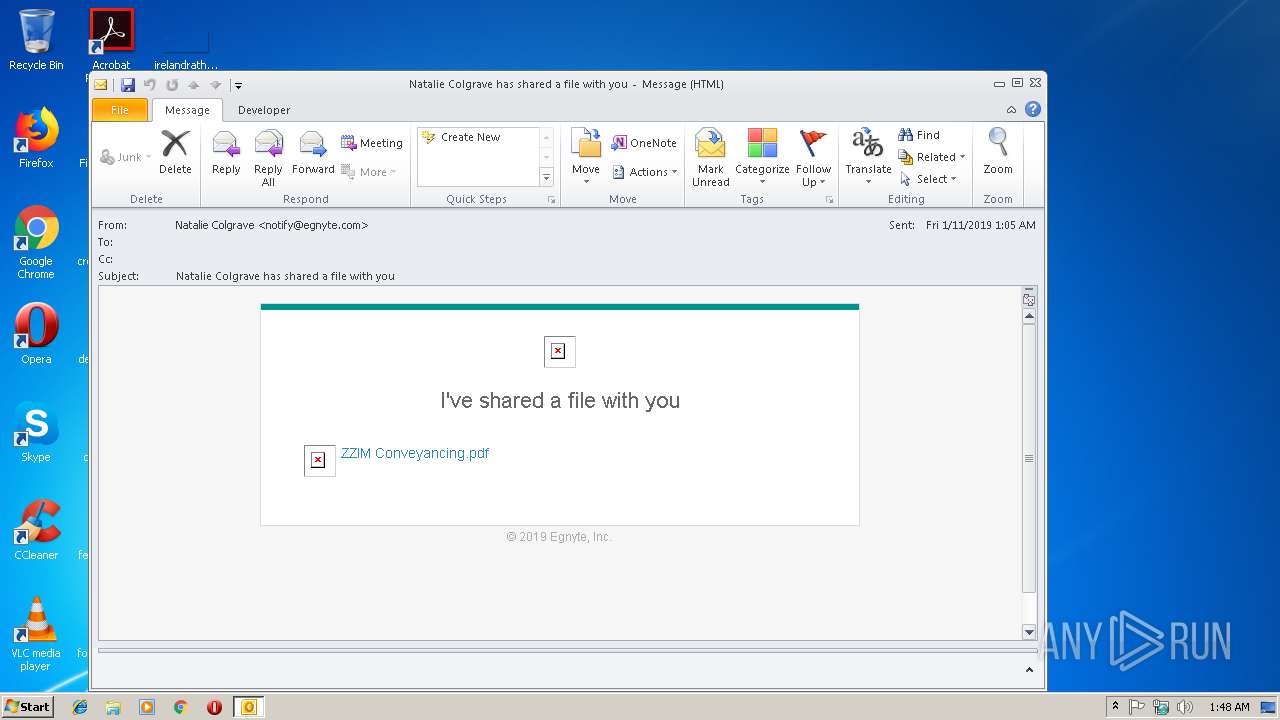
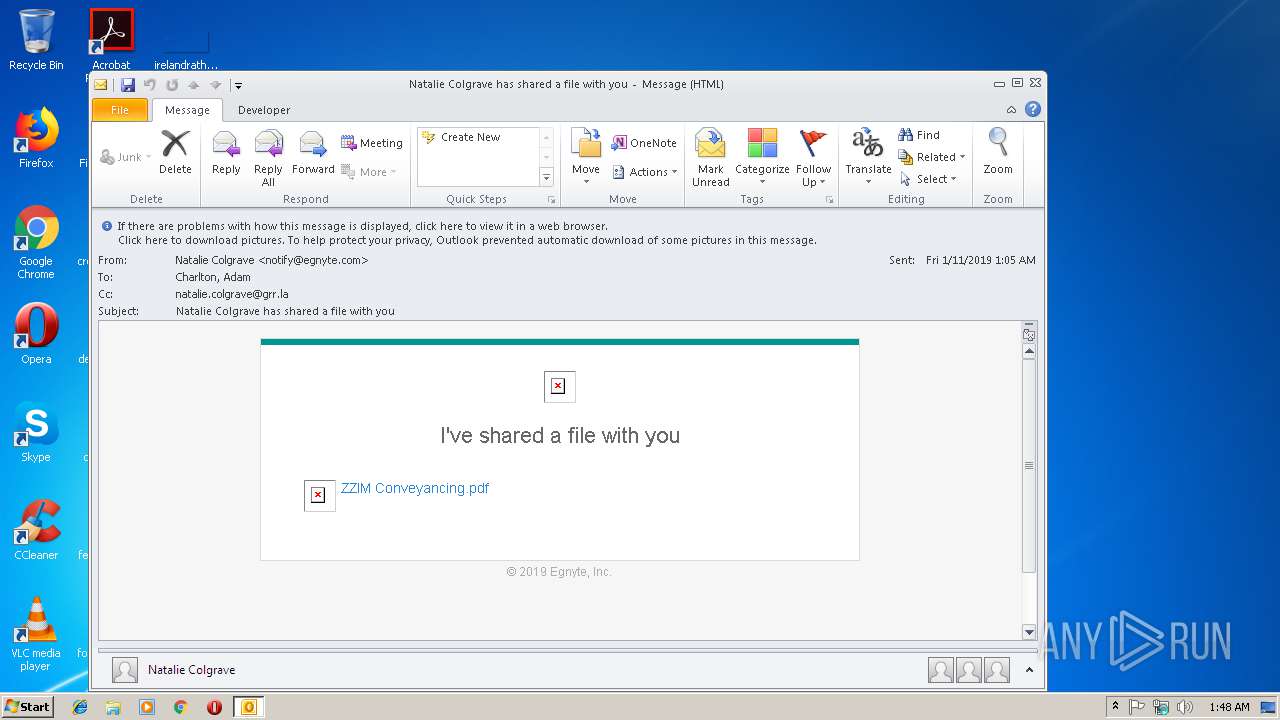
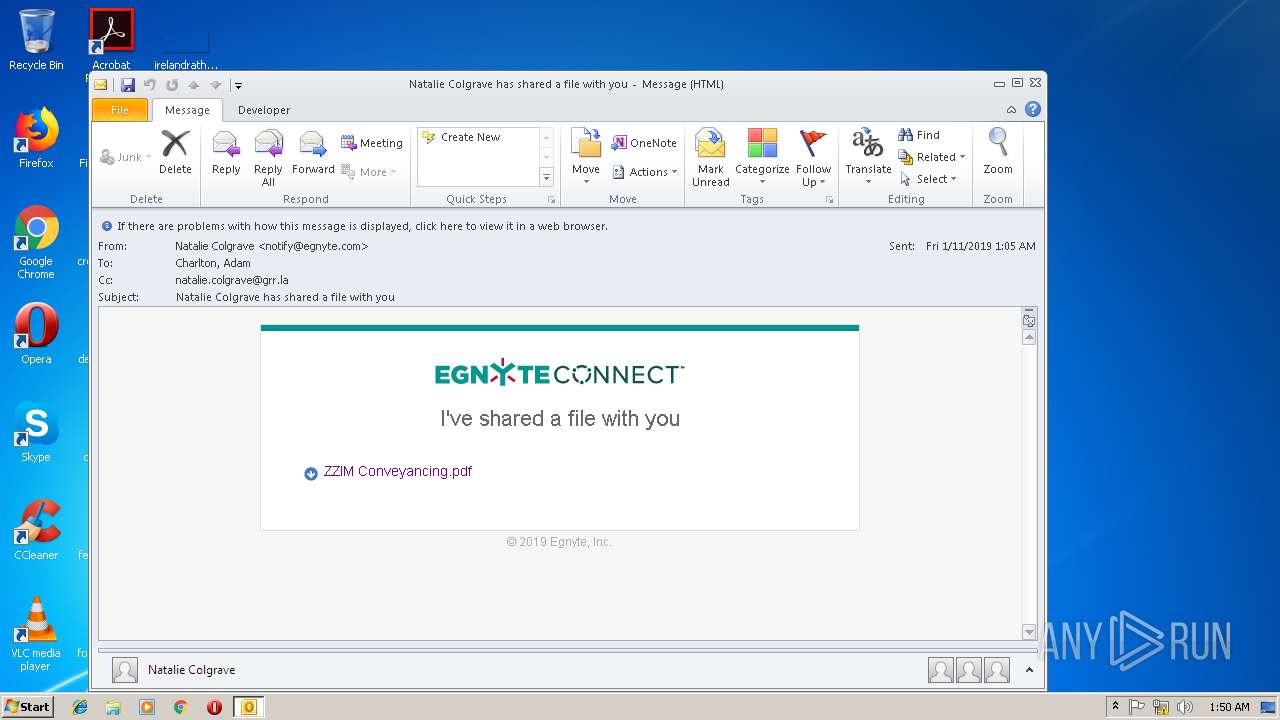
| File name: | Natalie_Colgrave_has_shared_a_file_with_you.eml |
| Full analysis: | https://app.any.run/tasks/104cf749-354b-4c3e-84a2-6840ae8e867f |
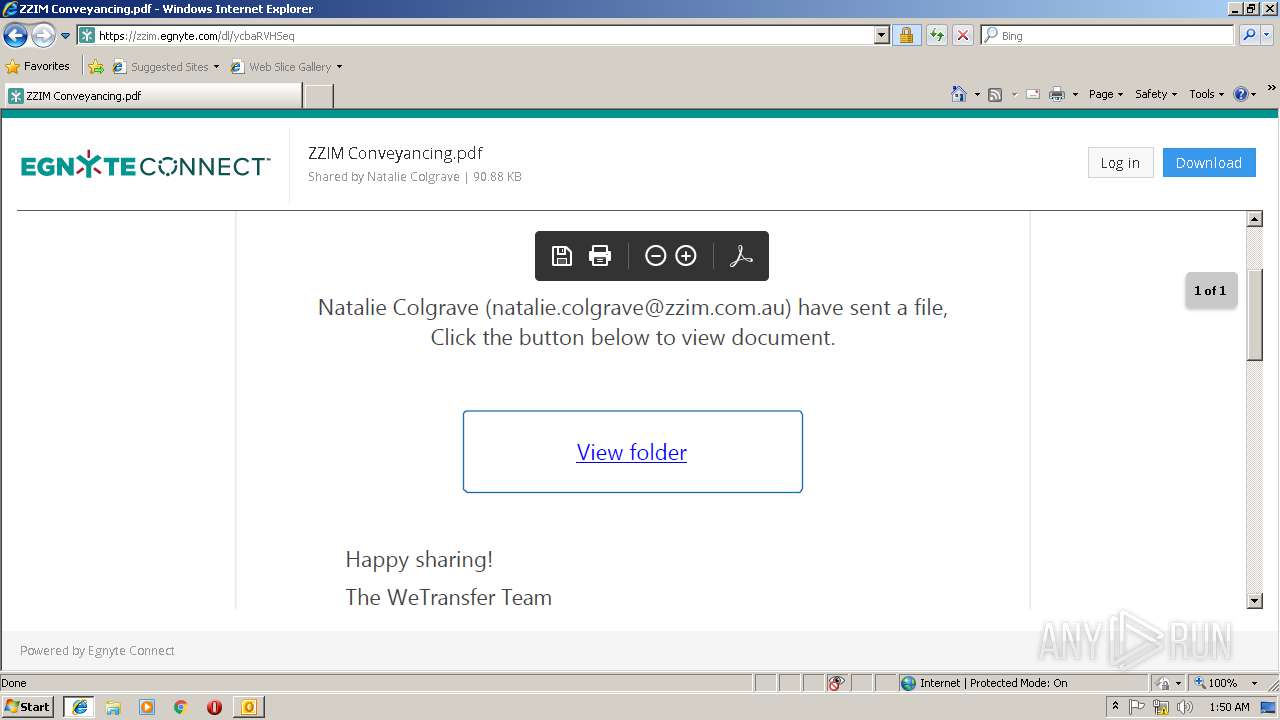
| Verdict: | Malicious activity |
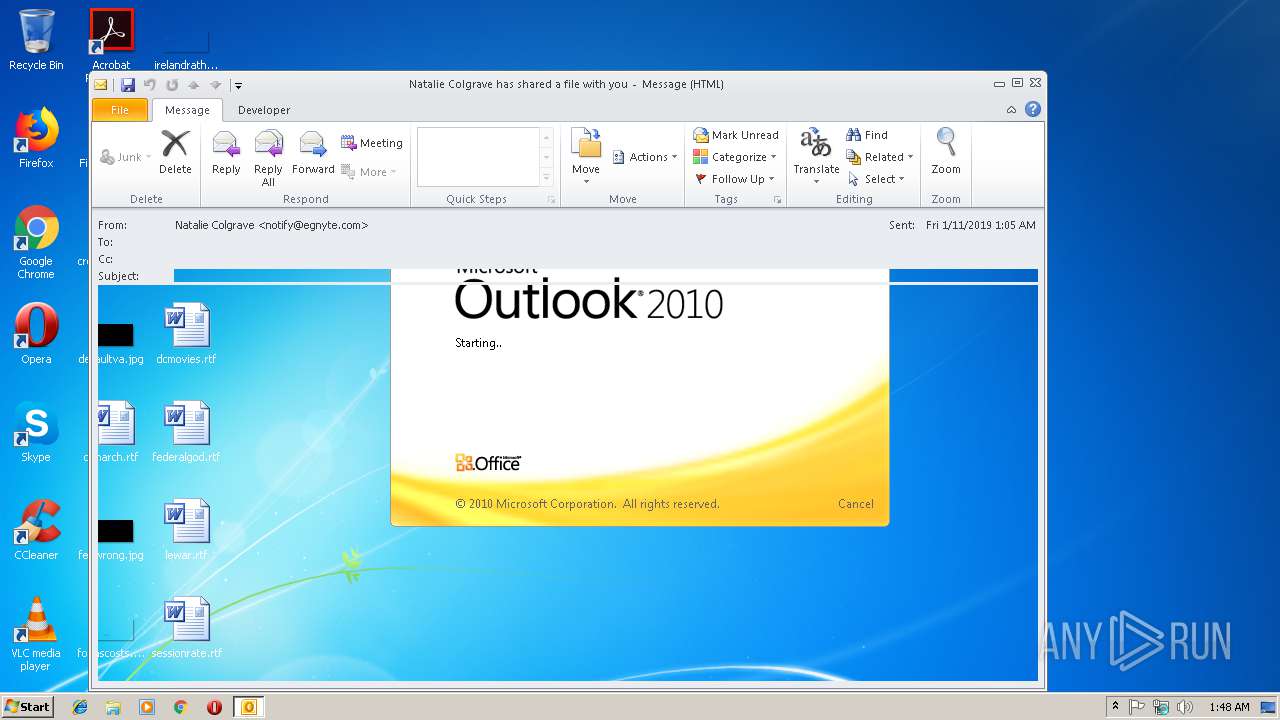
| Analysis date: | January 11, 2019, 01:48:21 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | message/rfc822 |
| File info: | RFC 822 mail, ASCII text, with very long lines, with CRLF line terminators |
| MD5: | 914C8508338772C90039DB82B6C49568 |
| SHA1: | D51F4B509C8B61E2E0C17F82640D9D2A1961F15C |
| SHA256: | CC6E2FBACEF75860C5605FBCFC31731C882EEC2CA575CED76D811B15E6CC9604 |
| SSDEEP: | 192:j95/DeCXa0aH5NelL+m+m4PRWoYzhLmmnAzX0c7KgYFJkMv8Mn0uZC:j9BD4ZIJH+m45kwbXYQE0uA |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 2896)
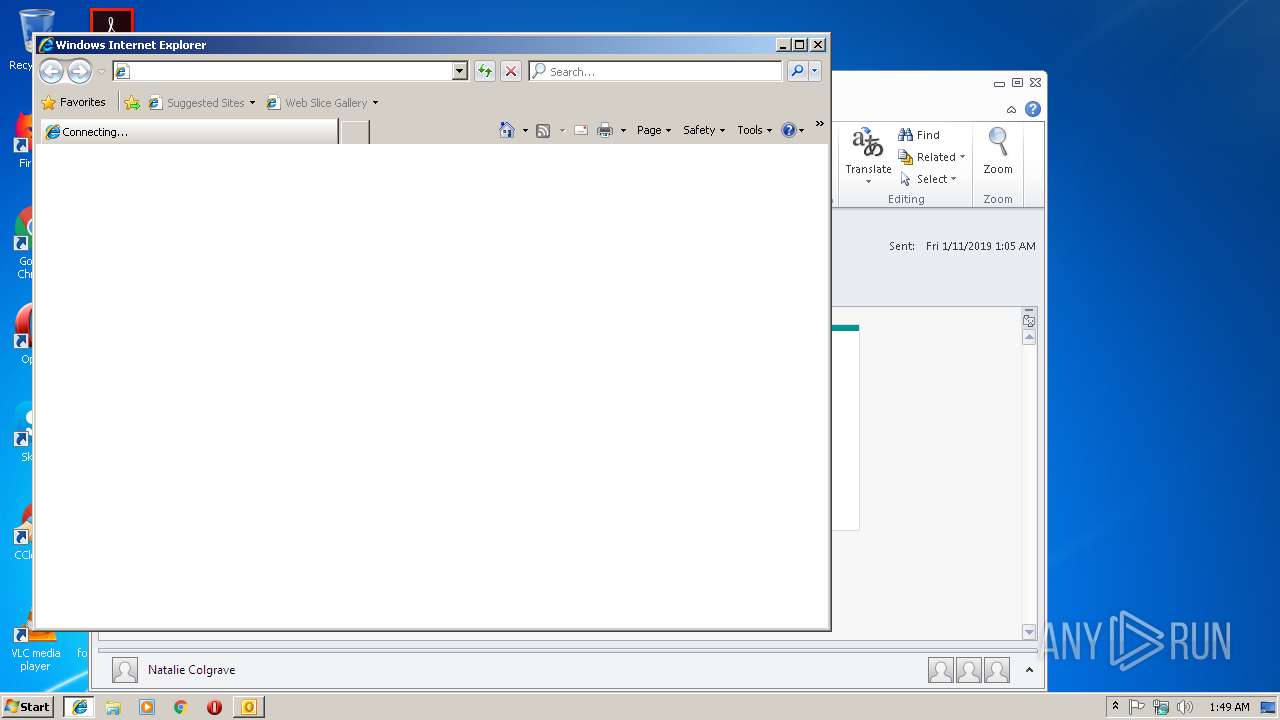
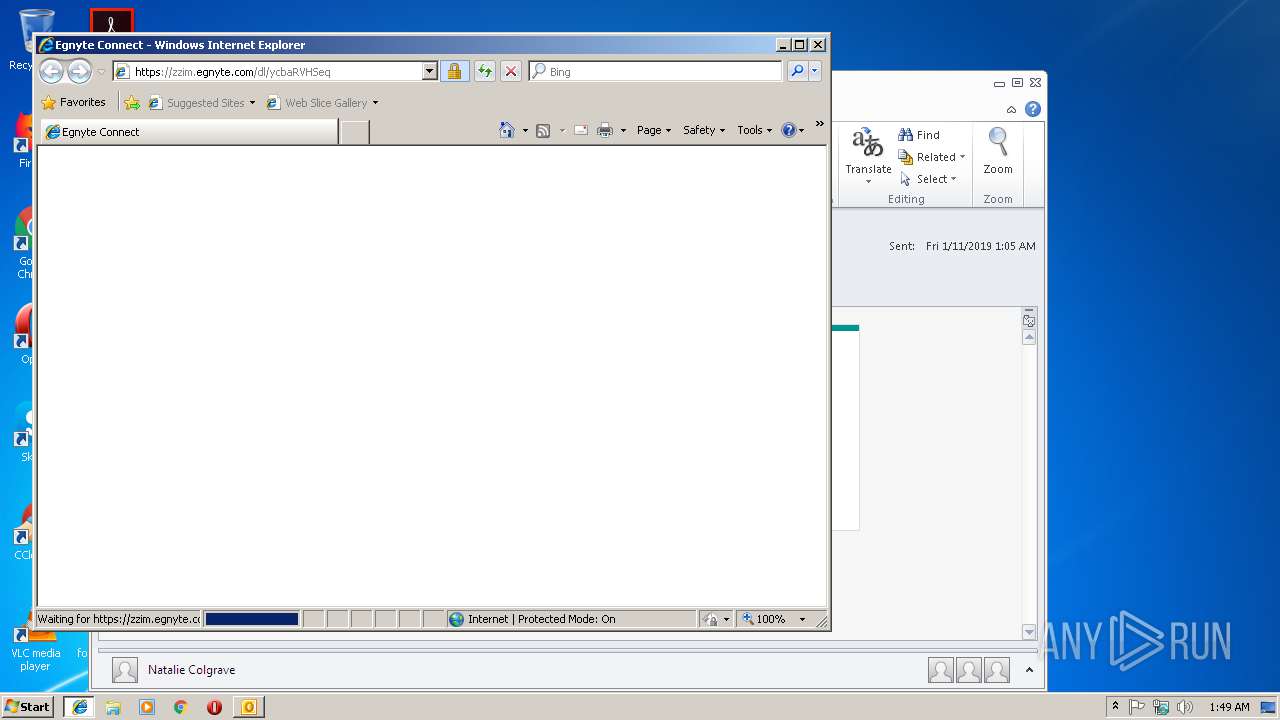
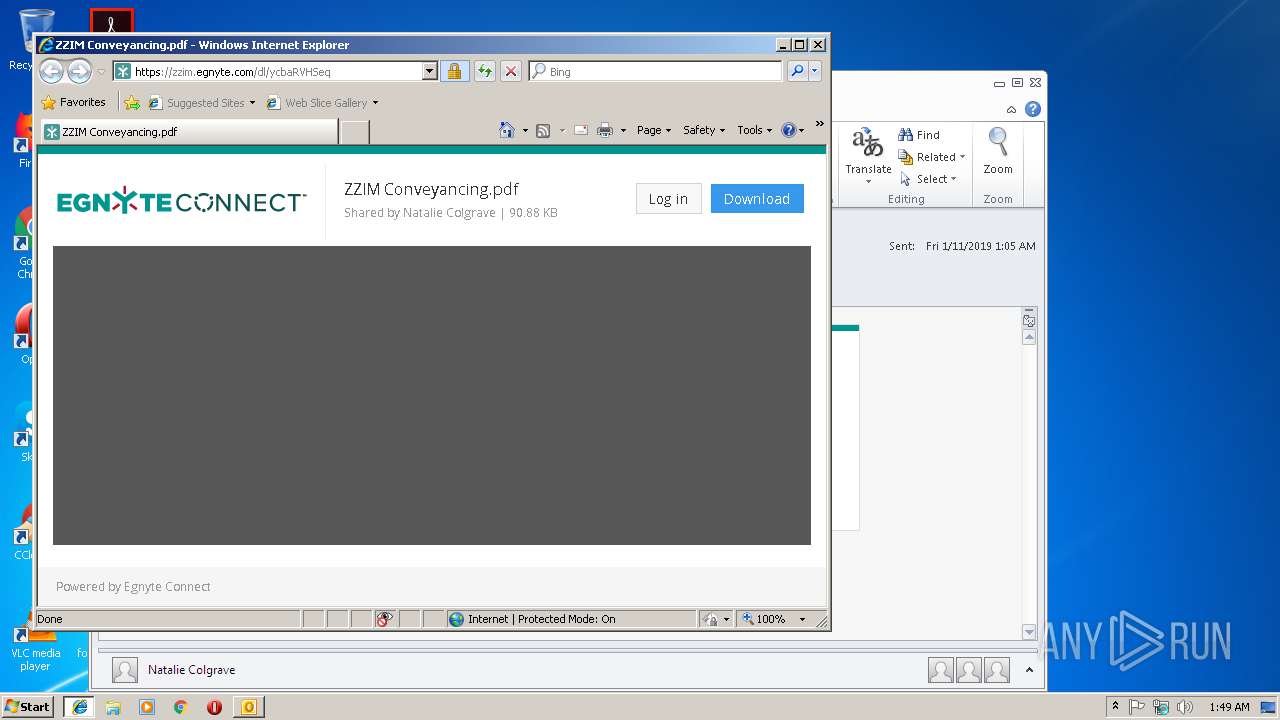
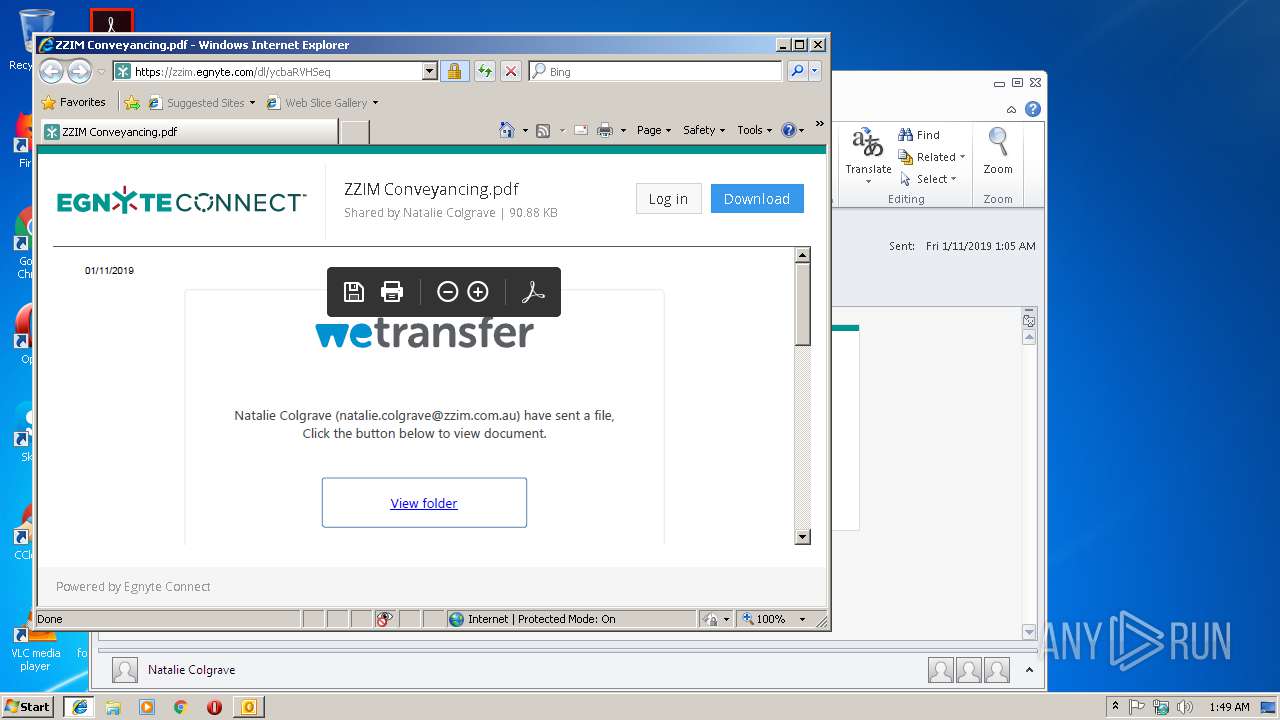
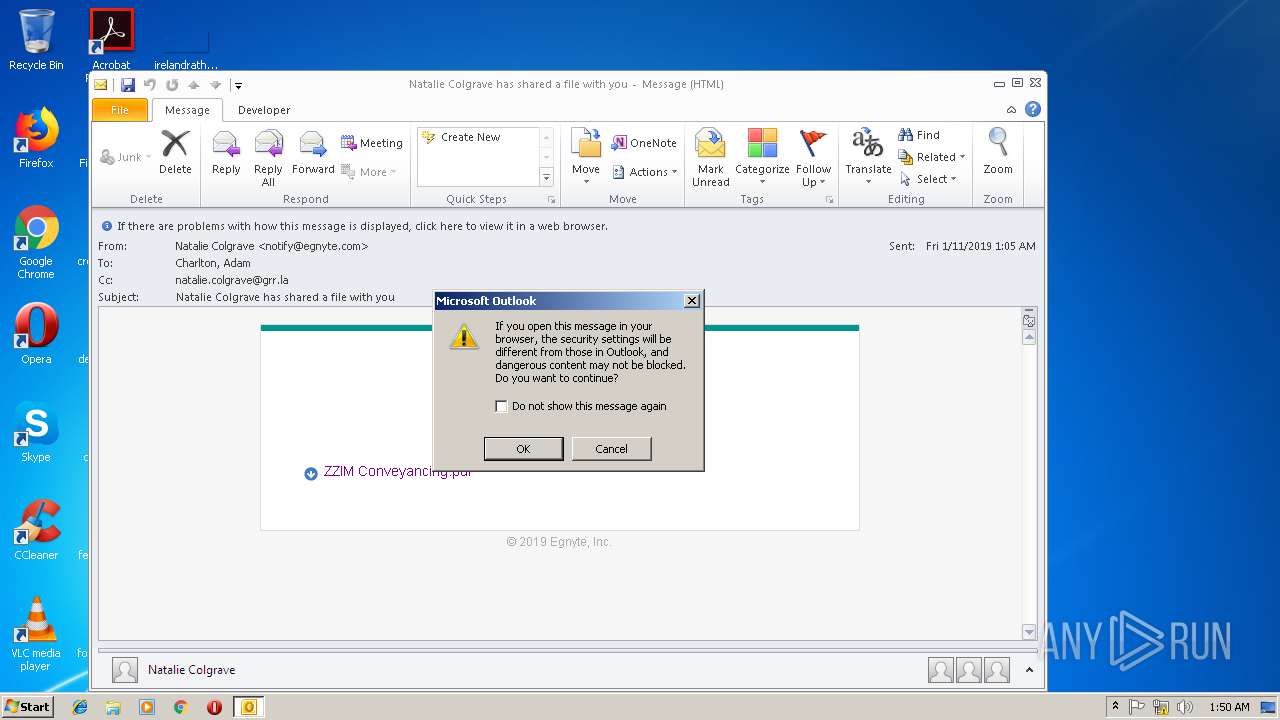
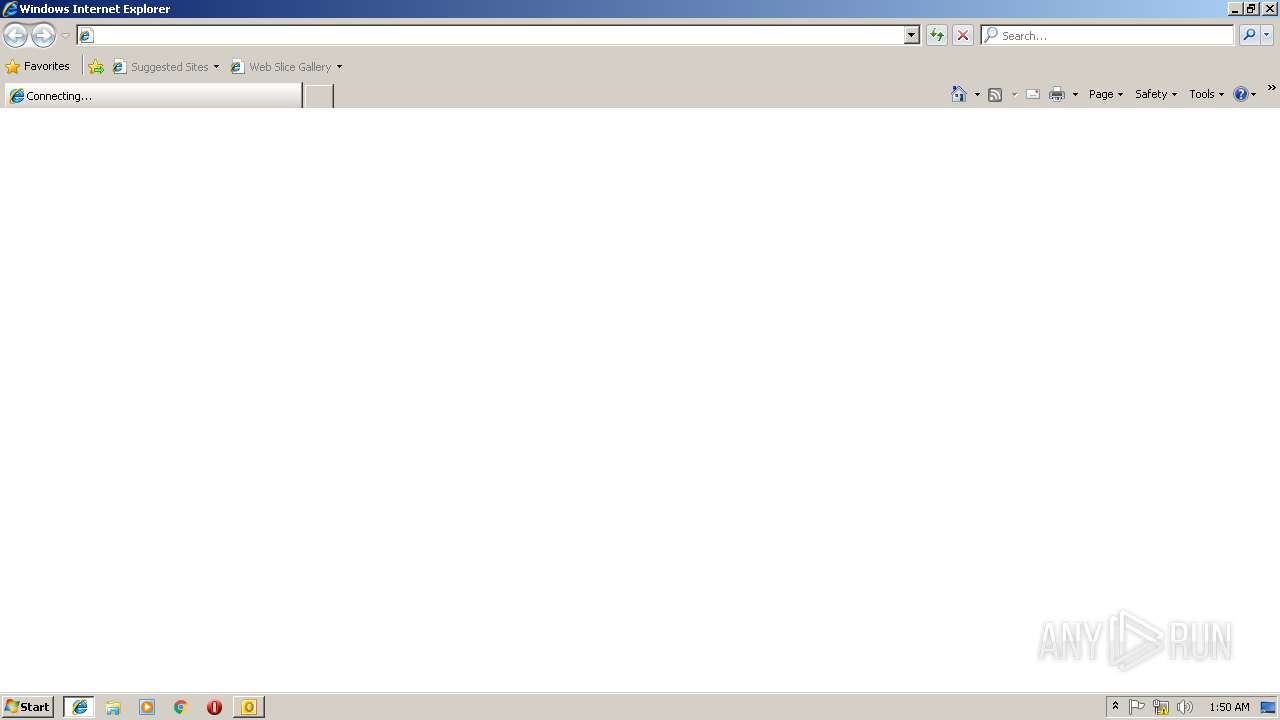
Starts Internet Explorer
- OUTLOOK.EXE (PID: 2896)
Creates files in the user directory
- OUTLOOK.EXE (PID: 2896)
INFO
Reads settings of System Certificates
- OUTLOOK.EXE (PID: 2896)
- iexplore.exe (PID: 2904)
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 2896)
- iexplore.exe (PID: 3276)
Changes internet zones settings
- iexplore.exe (PID: 2904)
- iexplore.exe (PID: 3276)
Application launched itself
- iexplore.exe (PID: 2904)
- RdrCEF.exe (PID: 3188)
- iexplore.exe (PID: 3276)
- AcroRd32.exe (PID: 2712)
Creates files in the user directory
- iexplore.exe (PID: 3660)
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 2908)
- AcroRd32.exe (PID: 2832)
- iexplore.exe (PID: 2904)
- iexplore.exe (PID: 3344)
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 1872)
Reads Internet Cache Settings
- iexplore.exe (PID: 3660)
- iexplore.exe (PID: 3344)
Reads internet explorer settings
- iexplore.exe (PID: 3660)
- iexplore.exe (PID: 3344)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .eml | | | E-Mail message (Var. 5) (100) |
|---|
Total processes
49
Monitored processes
16
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 128 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe" --type=renderer /o /eo /l /b /id 3344 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe | — | AcroRd32.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe Acrobat Reader DC Exit code: 1 Version: 15.23.20070.215641 Modules
| |||||||||||||||
| 1872 | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe -Embedding | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe | — | svchost.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe® Flash® Player Installer/Uninstaller 26.0 r0 Exit code: 0 Version: 26,0,0,131 Modules
| |||||||||||||||
| 2332 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe" --type=renderer /o /eo /l /b /id 3660 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe | — | AcroRd32.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe Acrobat Reader DC Exit code: 1 Version: 15.23.20070.215641 Modules
| |||||||||||||||
| 2352 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe" /o /eo /l /b /id 3344 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe | — | iexplore.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe Acrobat Reader DC Exit code: 0 Version: 15.23.20070.215641 Modules
| |||||||||||||||
| 2712 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe" /o /eo /l /b /id 3344 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe | iexplore.exe | ||||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe Acrobat Reader DC Exit code: 1 Version: 15.23.20070.215641 Modules
| |||||||||||||||
| 2716 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe" /o /eo /l /b /id 3660 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe | — | iexplore.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe Acrobat Reader DC Exit code: 0 Version: 15.23.20070.215641 Modules
| |||||||||||||||
| 2724 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe" --type=renderer --disable-3d-apis --disable-databases --disable-direct-npapi-requests --disable-file-system --disable-notifications --disable-shared-workers --disable-direct-write --lang=en-US --lang=en-US --log-severity=disable --product-version="ReaderServices/15.23.20053 Chrome/45.0.2454.85" --device-scale-factor=1 --enable-delegated-renderer --num-raster-threads=2 --gpu-rasterization-msaa-sample-count=8 --content-image-texture-target=3553 --video-image-texture-target=3553 --disable-accelerated-video-decode --disable-webrtc-hw-encoding --disable-gpu-compositing --channel="3188.1.841066505\188086996" --allow-no-sandbox-job /prefetch:673131151 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe | — | RdrCEF.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe RdrCEF Exit code: 0 Version: 15.23.20053.211670 Modules
| |||||||||||||||
| 2832 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe" /o /eo /l /b /id 3660 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe | — | iexplore.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe Acrobat Reader DC Exit code: 1 Version: 15.23.20070.215641 Modules
| |||||||||||||||
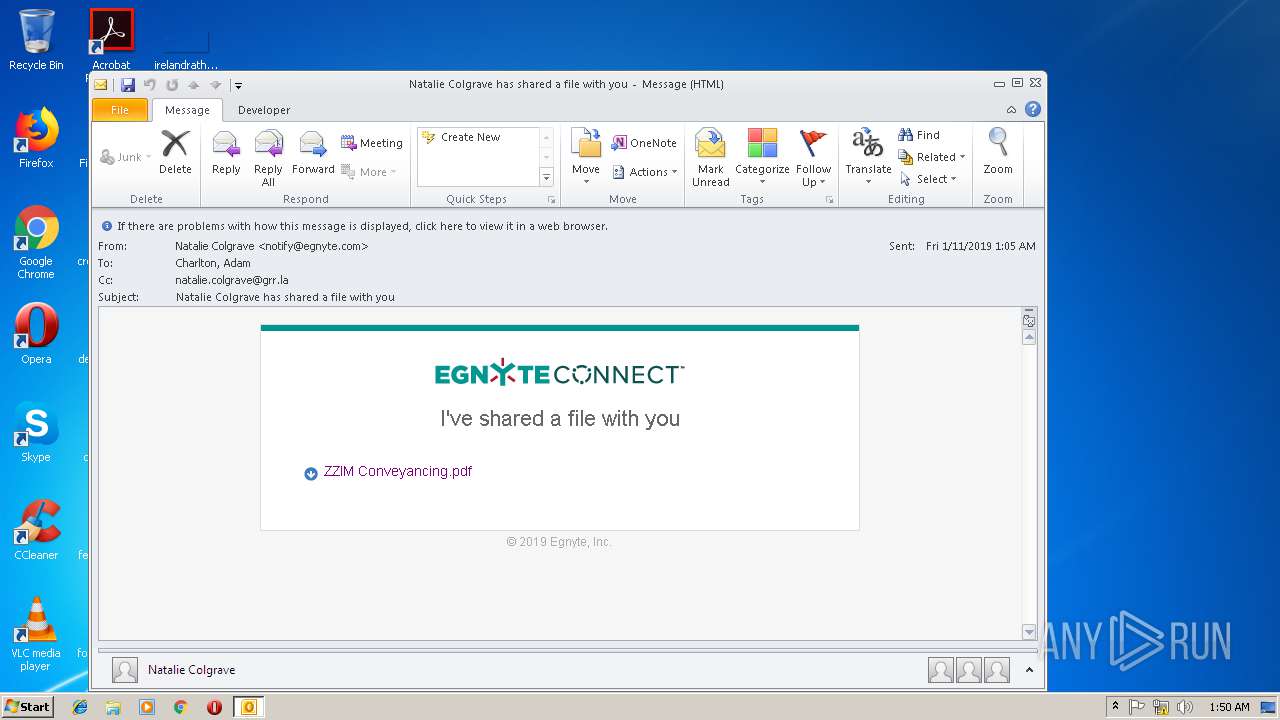
| 2896 | "C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE" /eml "C:\Users\admin\AppData\Local\Temp\Natalie_Colgrave_has_shared_a_file_with_you.eml" | C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
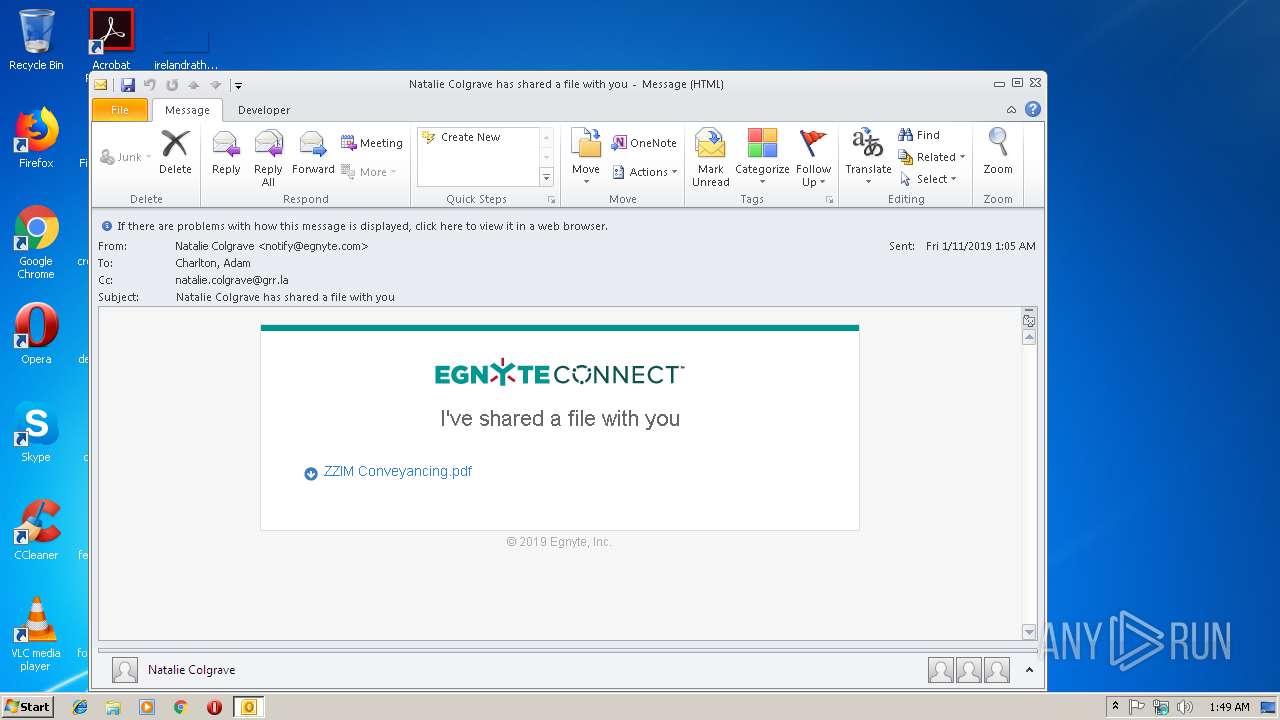
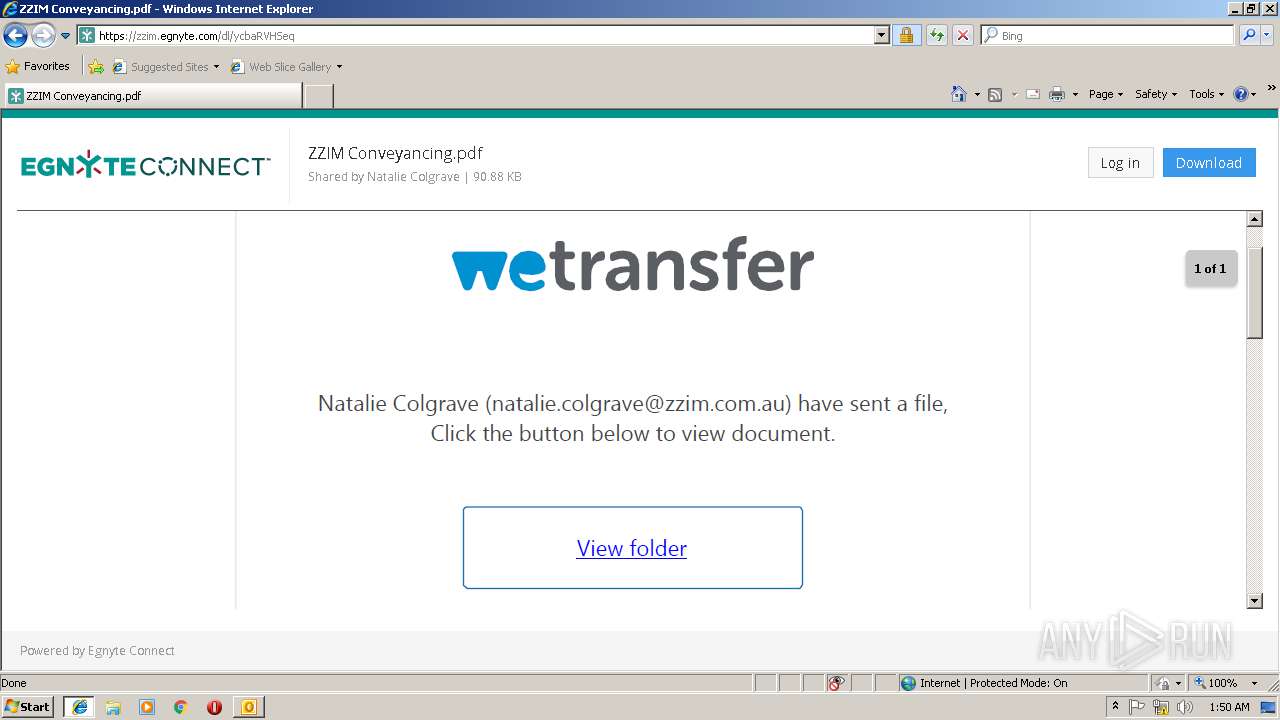
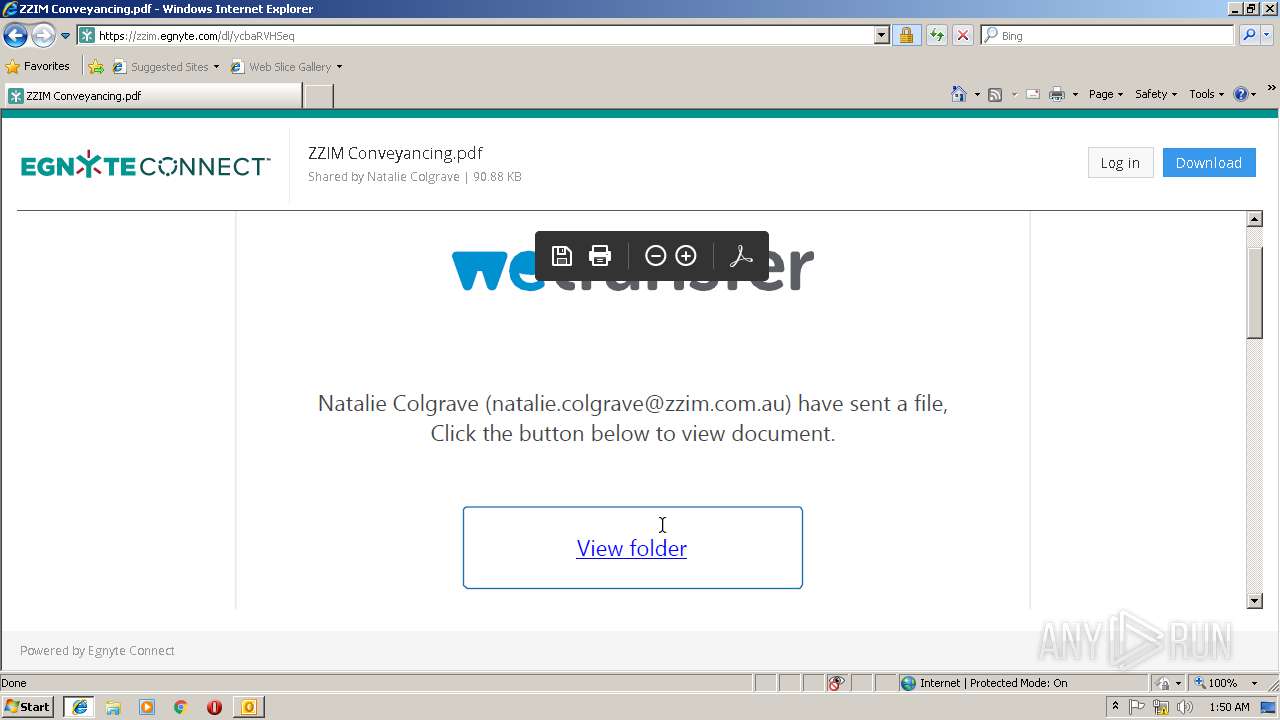
| 2904 | "C:\Program Files\Internet Explorer\iexplore.exe" https://zzim.egnyte.com/dl/ycbaRVHSeq | C:\Program Files\Internet Explorer\iexplore.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
3 003
Read events
2 379
Write events
601
Delete events
23
Modification events
| (PID) Process: | (2896) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2896) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2896) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\Resiliency\StartupItems |
| Operation: | write | Name: | um$ |
Value: 756D2400500B0000010000000000000000000000 | |||
| (PID) Process: | (2896) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook |
| Operation: | write | Name: | MTTT |
Value: 500B0000B011B7CB4FA9D40100000000 | |||
| (PID) Process: | (2896) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionNumber |
Value: 0 | |||
| (PID) Process: | (2896) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionDate |
Value: 219860640 | |||
| (PID) Process: | (2896) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\0a0d020000000000c000000000000046 |
| Operation: | write | Name: | 00030429 |
Value: 03000000 | |||
| (PID) Process: | (2896) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | {ED475418-B0D6-11D2-8C3B-00104B2A6676} |
Value: | |||
| (PID) Process: | (2896) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | LastChangeVer |
Value: 1200000000000000 | |||
| (PID) Process: | (2896) OUTLOOK.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109A10090400000000000F01FEC\Usage |
| Operation: | write | Name: | OutlookMAPI2Intl_1033 |
Value: 1311440917 | |||
Executable files
0
Suspicious files
15
Text files
111
Unknown types
36
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2896 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR99C5.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2904 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\D2YPIJ90\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2904 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3660 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\ycbaRVHSeq[1].txt | — | |
MD5:— | SHA256:— | |||
| 2896 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3660 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\ycbaRVHSeq[1].htm | html | |
MD5:— | SHA256:— | |||
| 2896 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_ContactPrefs_2_9C18D7EA1A94D34EBF1D927853057A5A.dat | xml | |
MD5:BBCF400BD7AE536EB03054021D6A6398 | SHA256:383020065C1F31F4FB09F448599A6D5E532C390AF4E5B8AF0771FE17A23222AD | |||
| 2896 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\{B0152101-97CC-432B-8080-FBF2DF12A856}\{1C306CB1-771E-4B4B-A902-86E897877F5B}.png | image | |
MD5:7D80C0A7E3849818695EAF4989186A3C | SHA256:72DC527D78A8E99331409803811CC2D287E812C008A1C869A6AEA69D7A44B597 | |||
| 2896 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\R9ZEWH8D\download-icon-3[1].png | image | |
MD5:— | SHA256:— | |||
| 2896 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_AvailabilityOptions_2_26B1935A5867644CA18DCE63CFD9A5CD.dat | xml | |
MD5:EEAA832C12F20DE6AAAA9C7B77626E72 | SHA256:C4C9A90F2C961D9EE79CF08FBEE647ED7DE0202288E876C7BAAD00F4CA29CA16 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
71
TCP/UDP connections
61
DNS requests
17
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2896 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
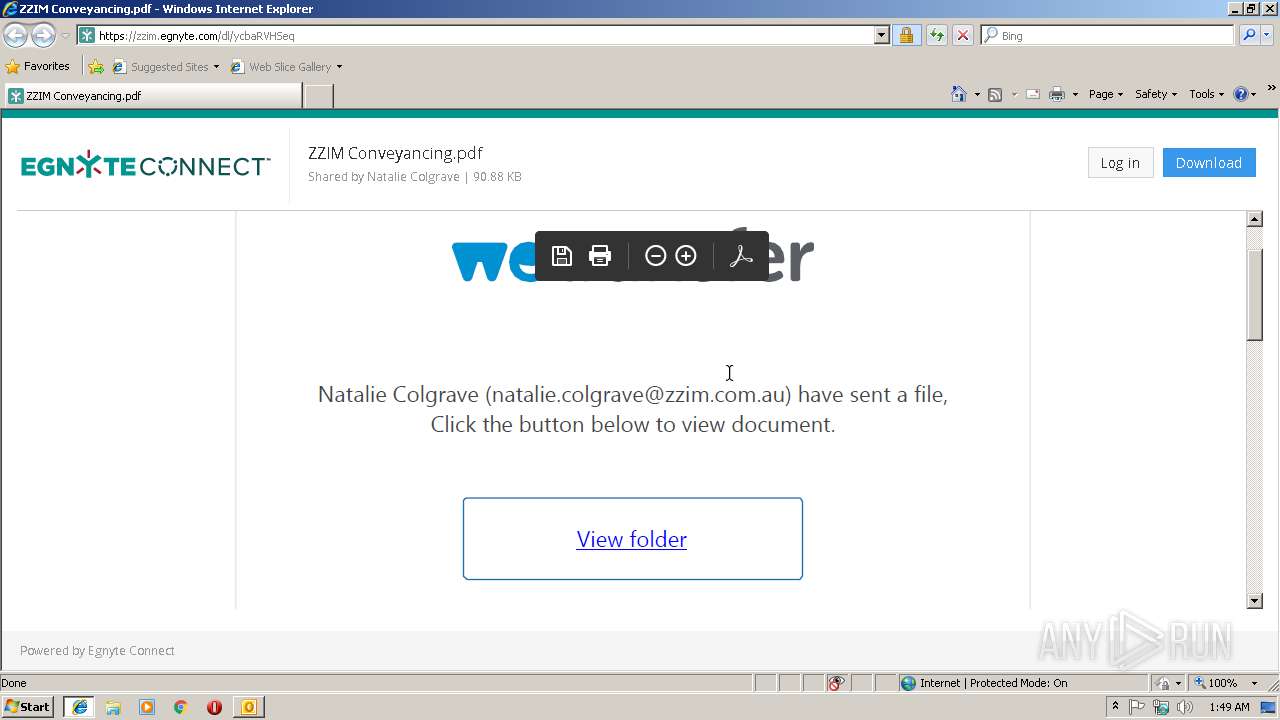
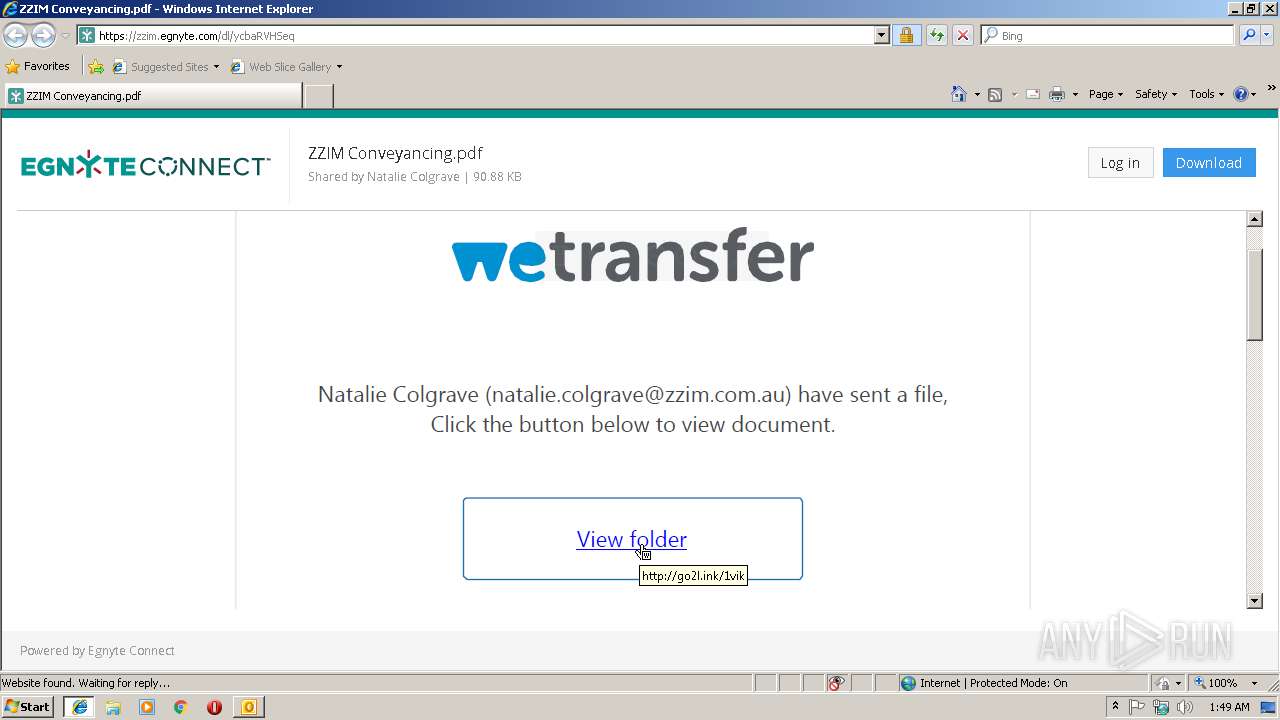
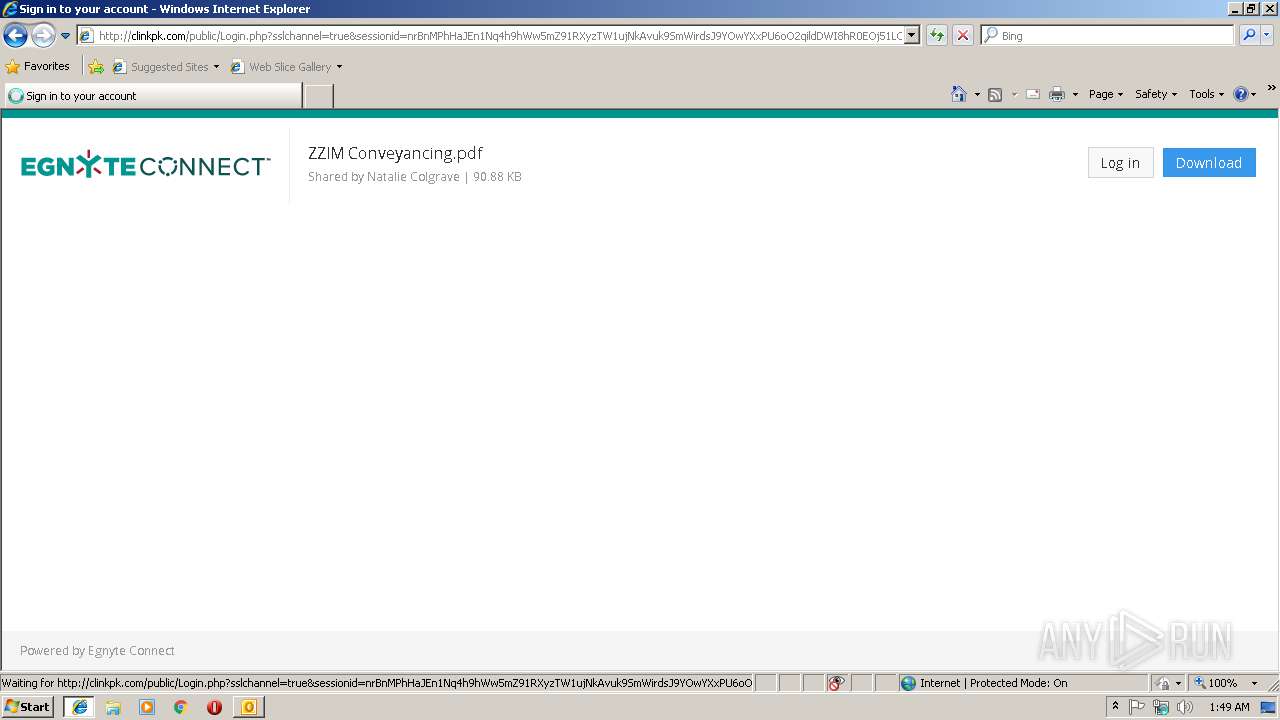
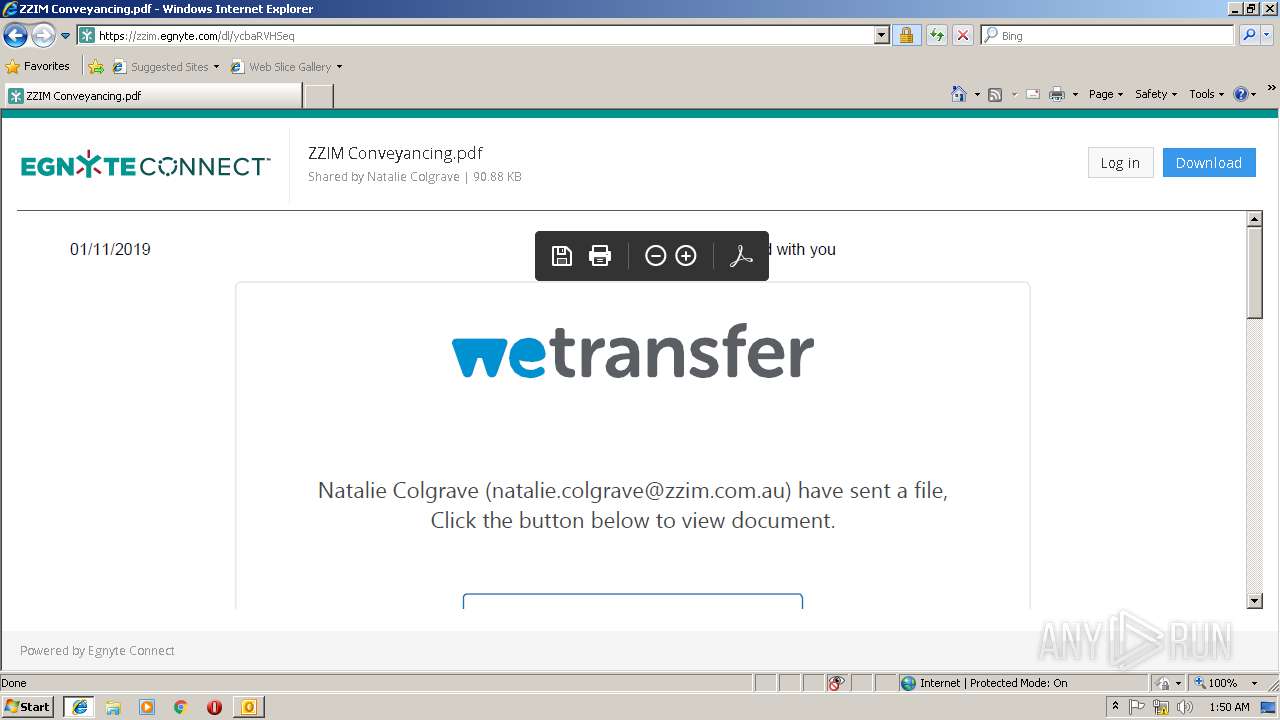
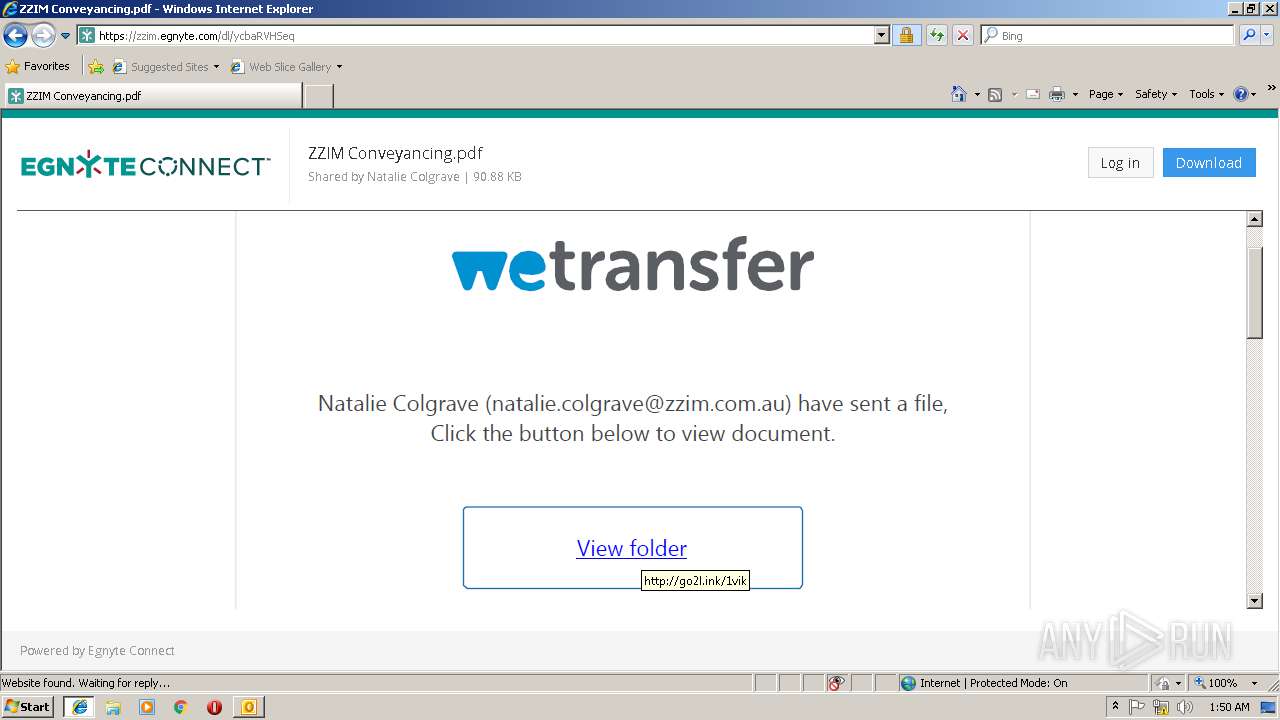
3660 | iexplore.exe | GET | — | 184.168.131.241:80 | http://go2l.ink/1vik | US | — | — | shared |
3660 | iexplore.exe | GET | — | 184.168.131.241:80 | http://go2l.ink/ObhjZ/1vik | US | — | — | shared |
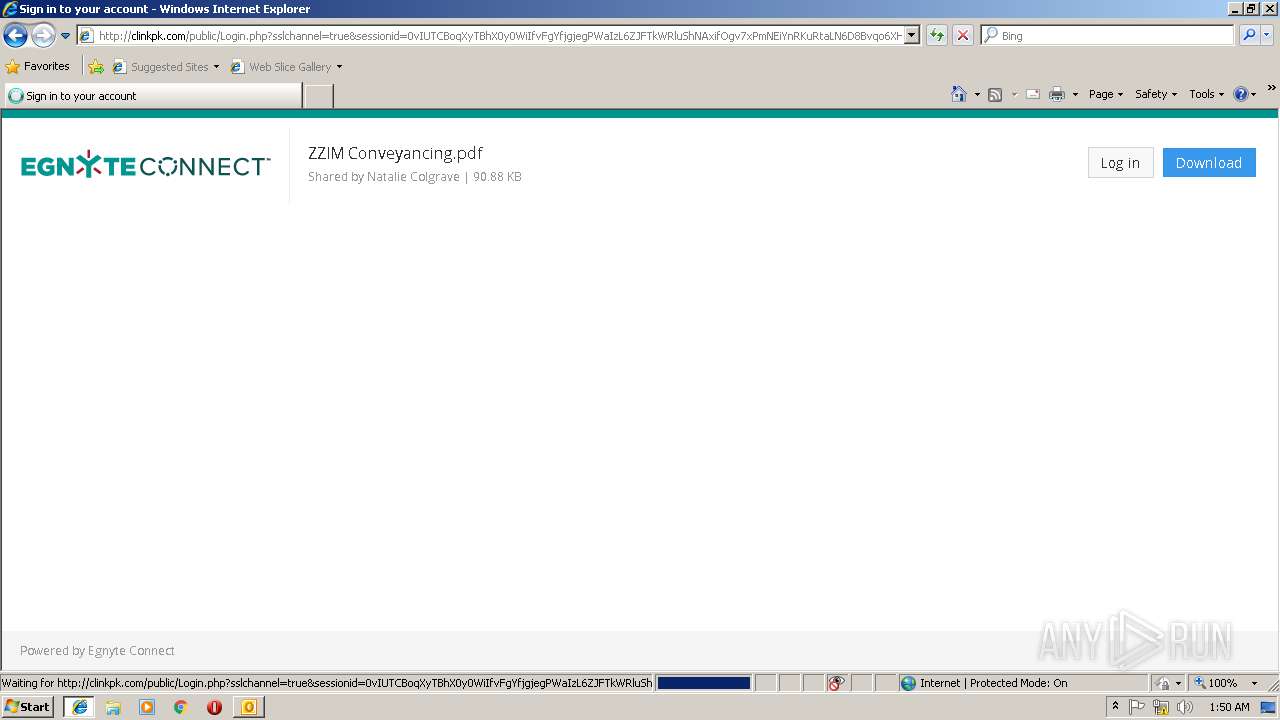
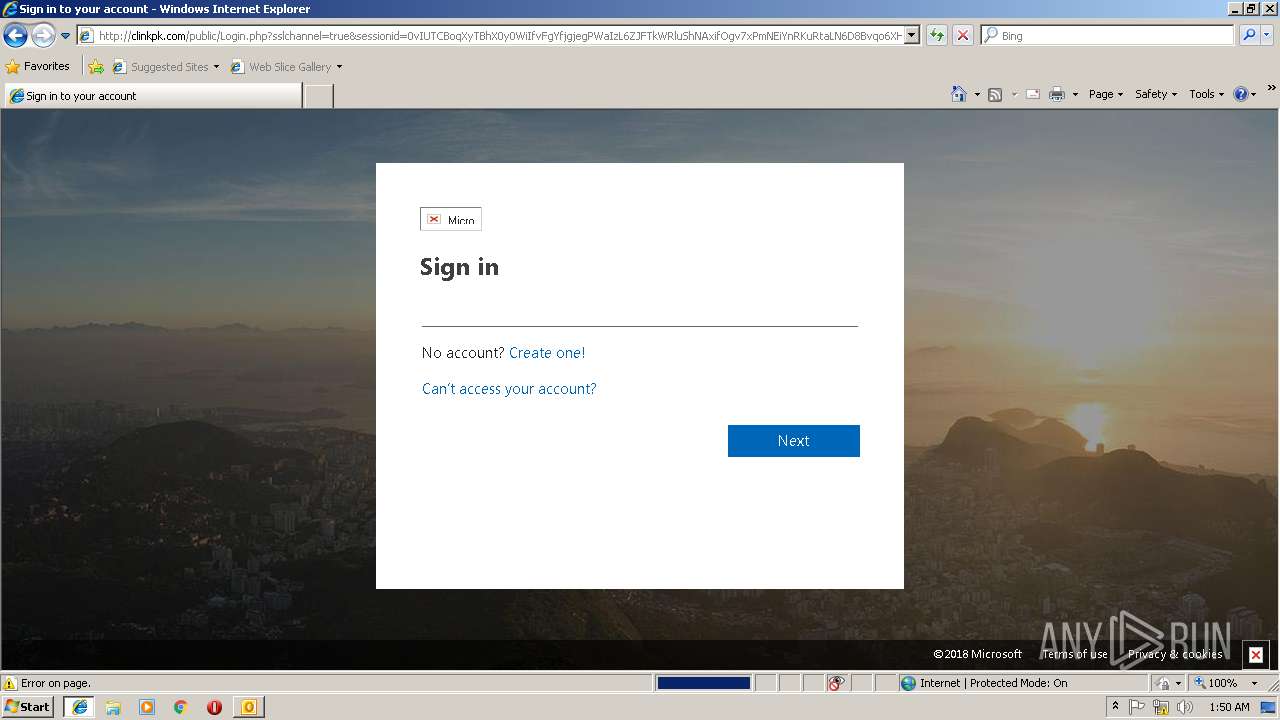
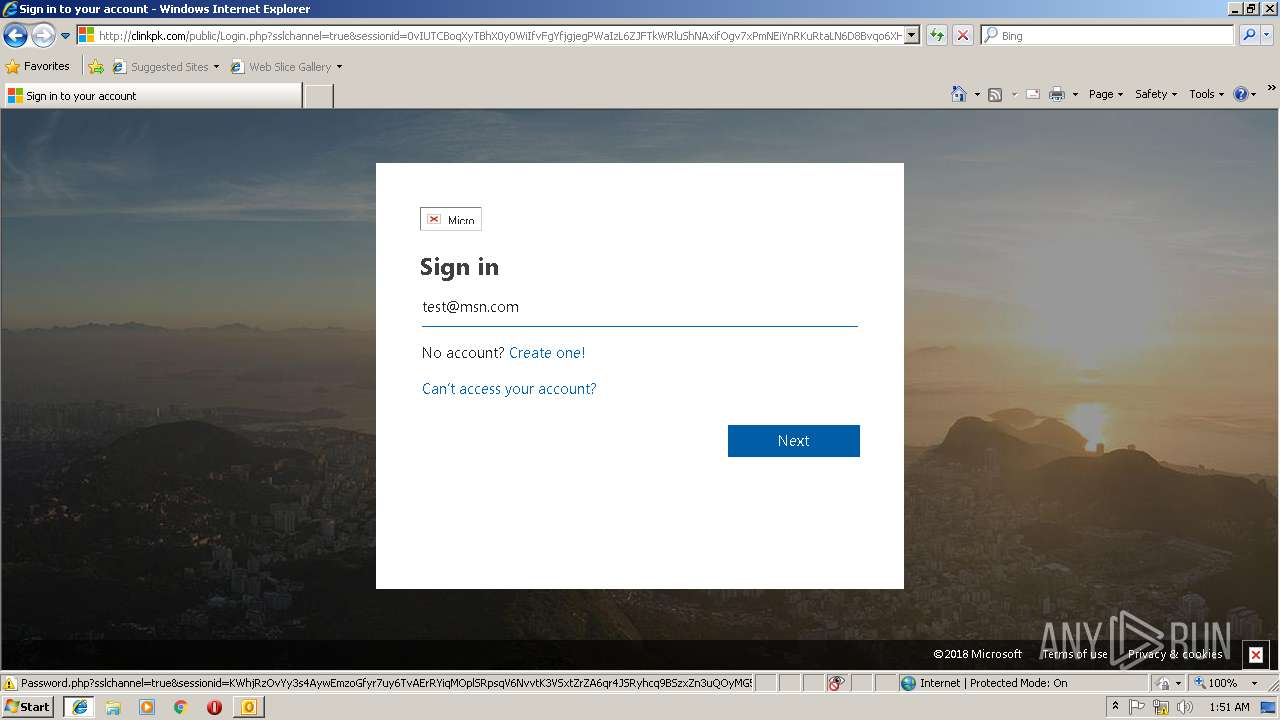
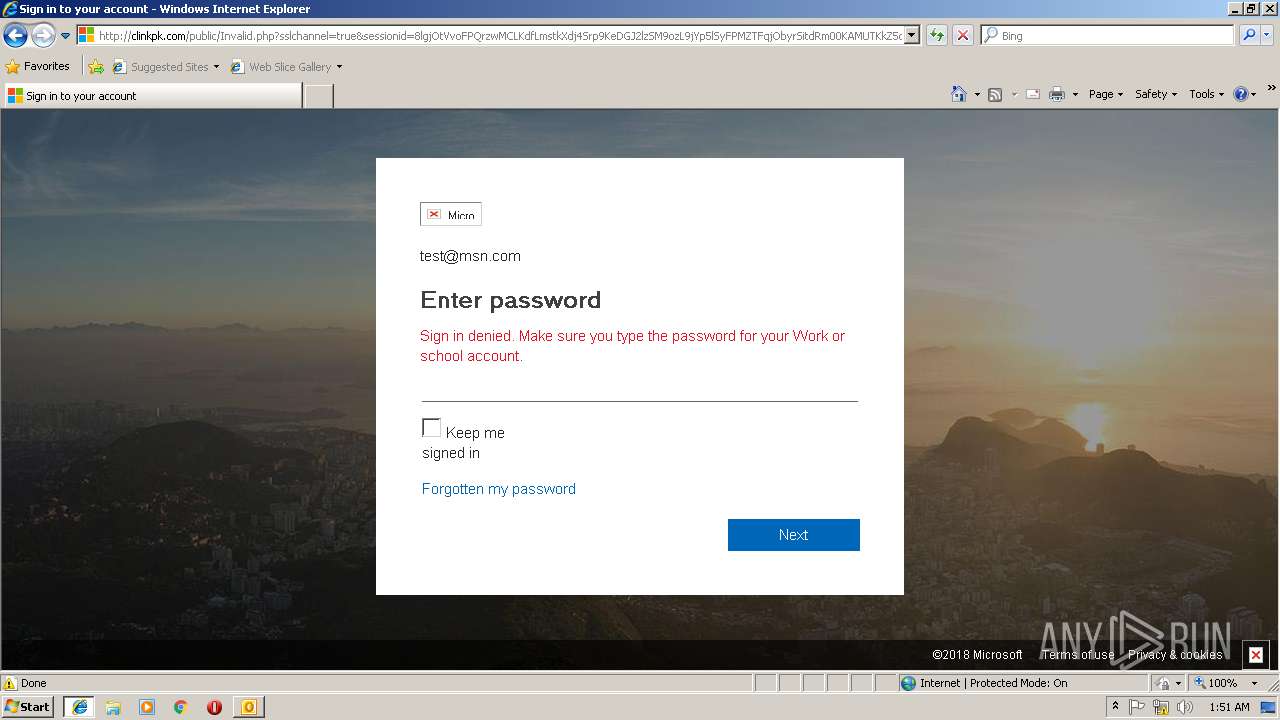
3660 | iexplore.exe | GET | 200 | 216.222.194.40:80 | http://clinkpk.com/public/assets/files/converged.css | US | text | 99.8 Kb | suspicious |
3660 | iexplore.exe | GET | 200 | 216.222.194.40:80 | http://clinkpk.com/public/assets/files/prefetch.htm | US | html | 2.56 Kb | suspicious |
3660 | iexplore.exe | GET | 200 | 216.222.194.40:80 | http://clinkpk.com/public/assets/files/prefetch_data/staticStylesFluent.css | US | text | 41.4 Kb | suspicious |
3660 | iexplore.exe | GET | 200 | 216.222.194.40:80 | http://clinkpk.com/public/assets/files/prefetch_data/prefetch.htm | US | html | 3.23 Kb | suspicious |
3660 | iexplore.exe | GET | 200 | 216.222.194.40:80 | http://clinkpk.com/public/assets/files/prefetch_data/prefetch_data/boot_002.js | US | txt | 647 Kb | suspicious |
3660 | iexplore.exe | GET | 200 | 216.222.194.40:80 | http://clinkpk.com/public/assets/files/prefetch_data/share.htm | US | html | 291 Kb | suspicious |
3660 | iexplore.exe | GET | 200 | 216.222.194.40:80 | http://clinkpk.com/public/assets/files/prefetch_data/prefetch_data/boot_003.js | US | text | 643 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2896 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
2896 | OUTLOOK.EXE | 162.216.250.12:443 | zzim.egnyte.com | Bloomip Inc. | NL | unknown |
3660 | iexplore.exe | 162.216.250.12:443 | zzim.egnyte.com | Bloomip Inc. | NL | unknown |
2904 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2904 | iexplore.exe | 162.216.250.12:443 | zzim.egnyte.com | Bloomip Inc. | NL | unknown |
3660 | iexplore.exe | 162.247.242.20:443 | bam.nr-data.net | New Relic | US | whitelisted |
3660 | iexplore.exe | 151.101.2.110:443 | js-agent.newrelic.com | Fastly | US | suspicious |
3660 | iexplore.exe | 35.186.241.51:443 | api.mixpanel.com | Google Inc. | US | whitelisted |
3660 | iexplore.exe | 184.168.131.241:80 | go2l.ink | GoDaddy.com, LLC | US | shared |
3660 | iexplore.exe | 35.186.235.23:443 | cdn.mxpnl.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
zzim.egnyte.com |
| unknown |
pages.egnyte.com |
| malicious |
www.bing.com |
| whitelisted |
ssl.google-analytics.com |
| whitelisted |
js-agent.newrelic.com |
| whitelisted |
bam.nr-data.net |
| whitelisted |
cdn.mxpnl.com |
| whitelisted |
api.mixpanel.com |
| whitelisted |
go2l.ink |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
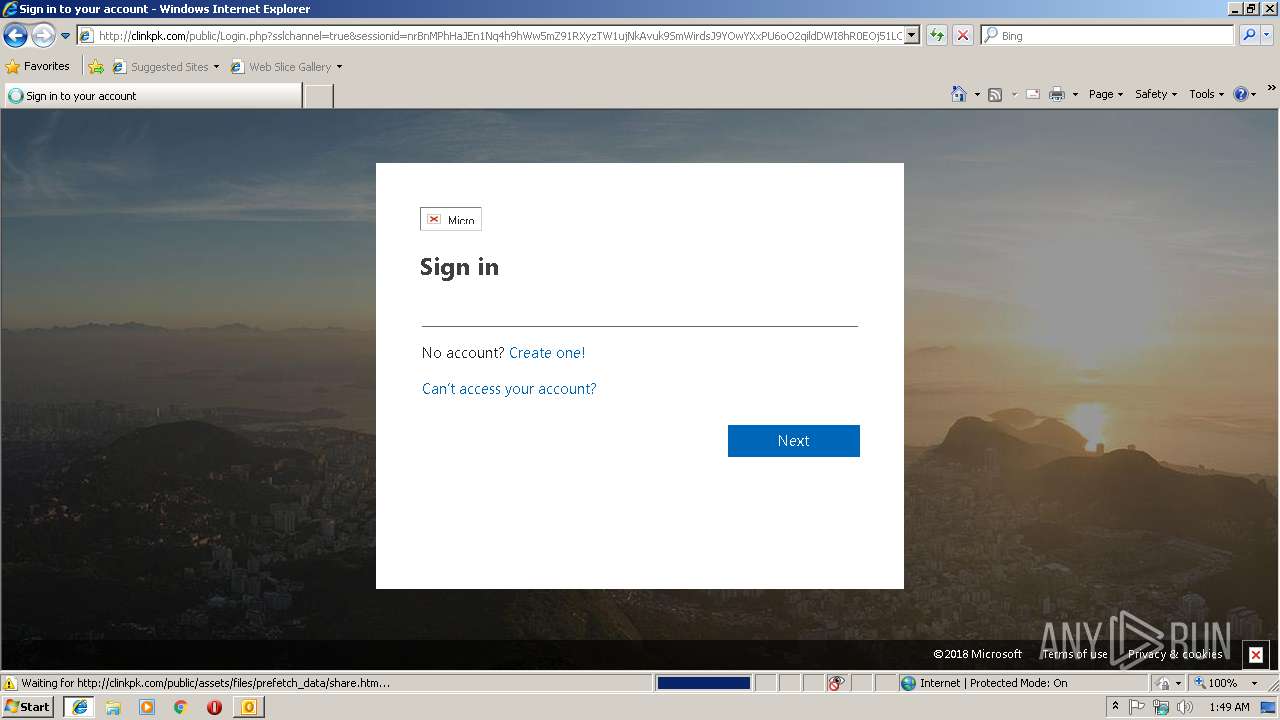
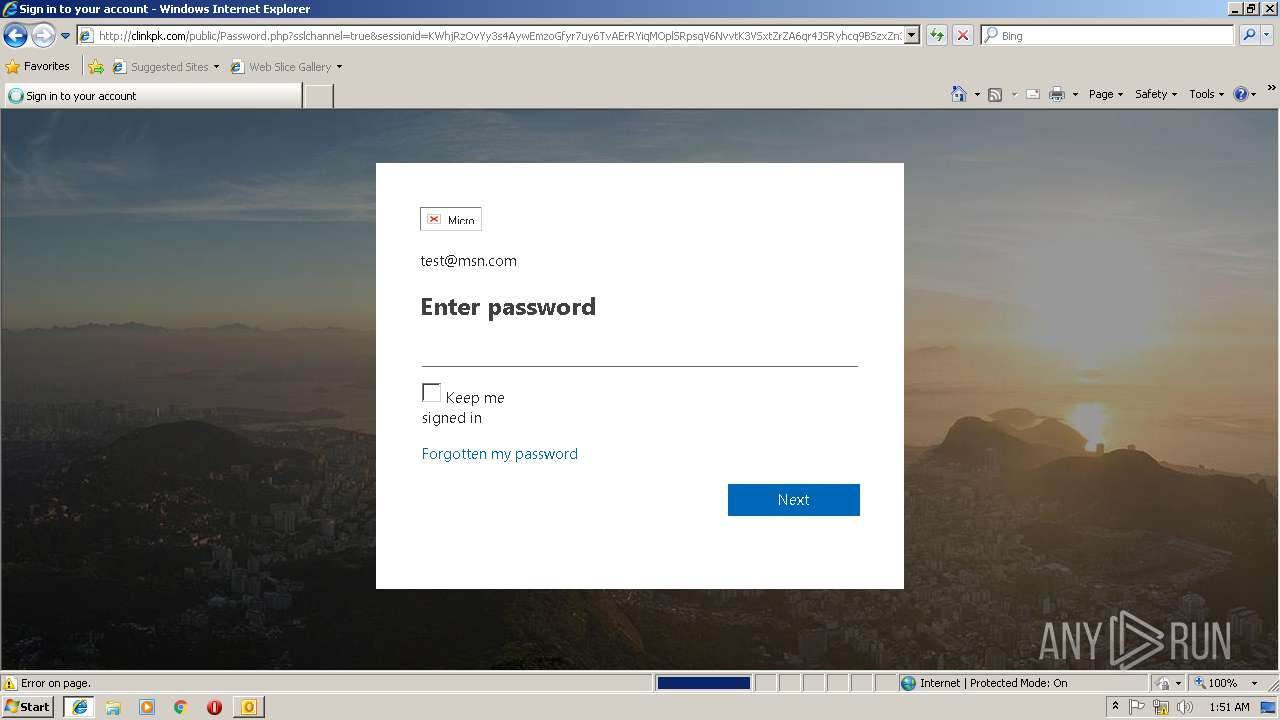
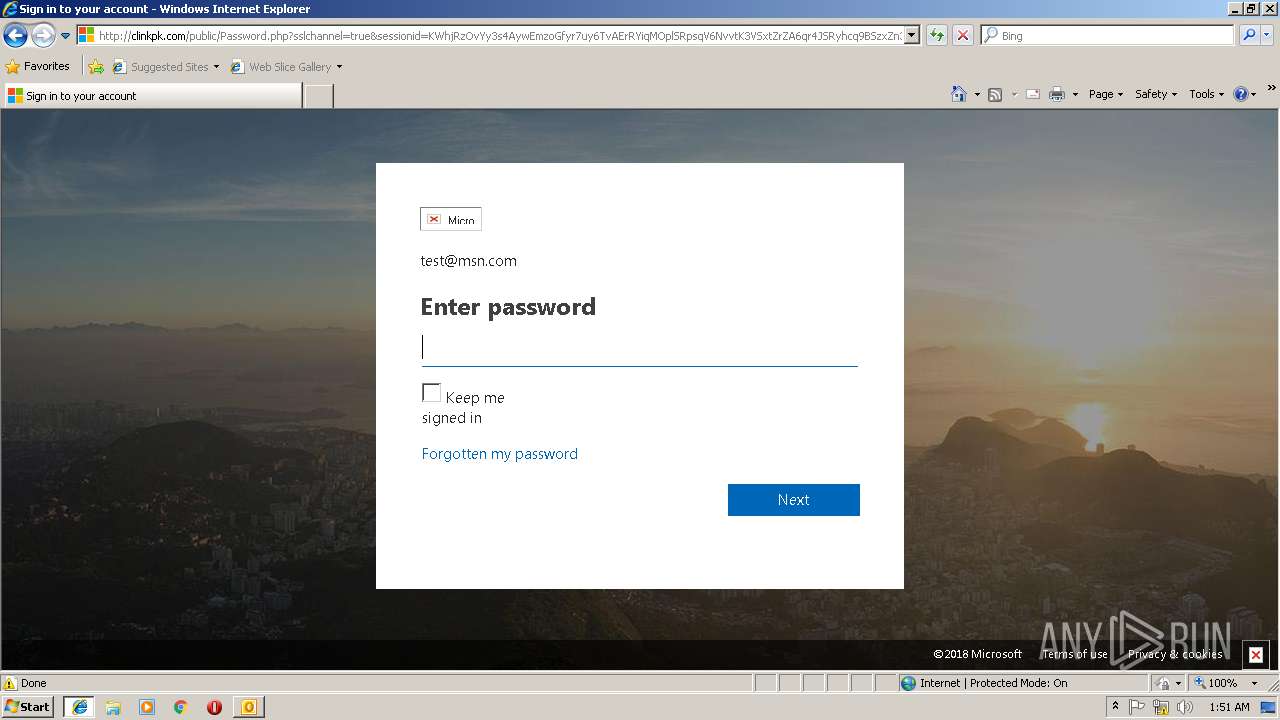
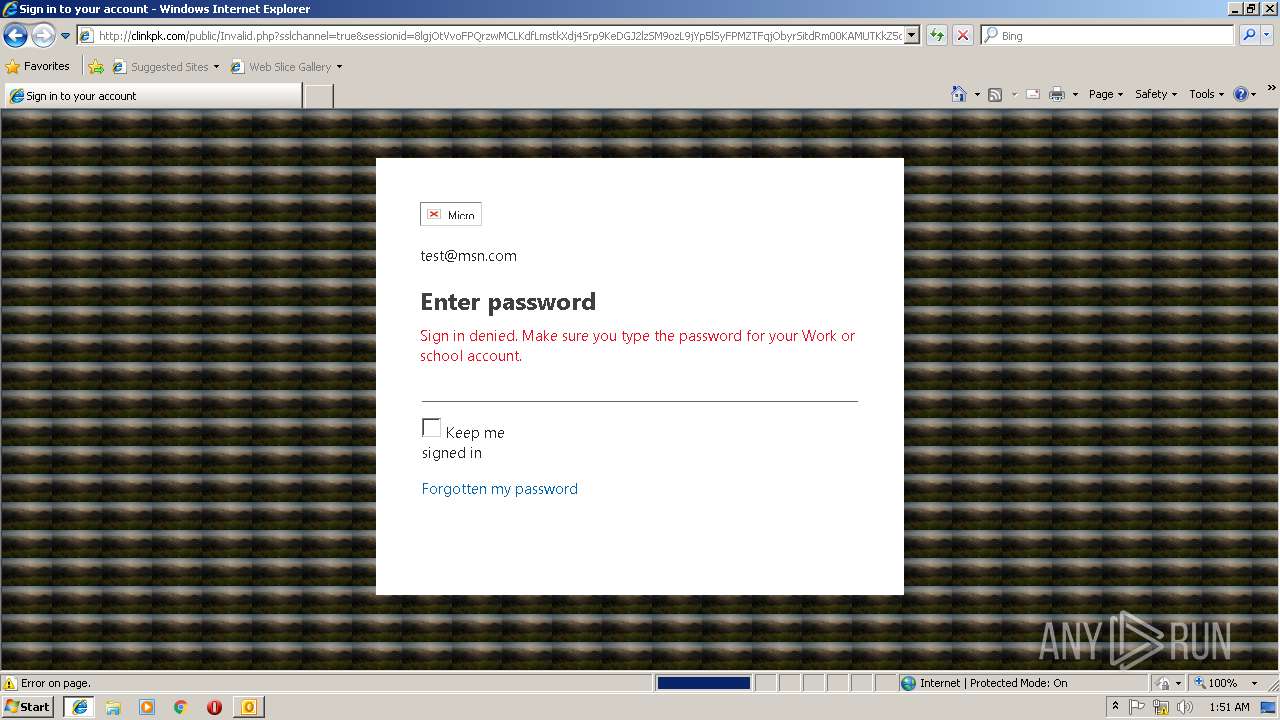
3344 | iexplore.exe | Potential Corporate Privacy Violation | ET POLICY Http Client Body contains passwd= in cleartext |
3344 | iexplore.exe | Potential Corporate Privacy Violation | ET POLICY Http Client Body contains passwd= in cleartext |
4 ETPRO signatures available at the full report